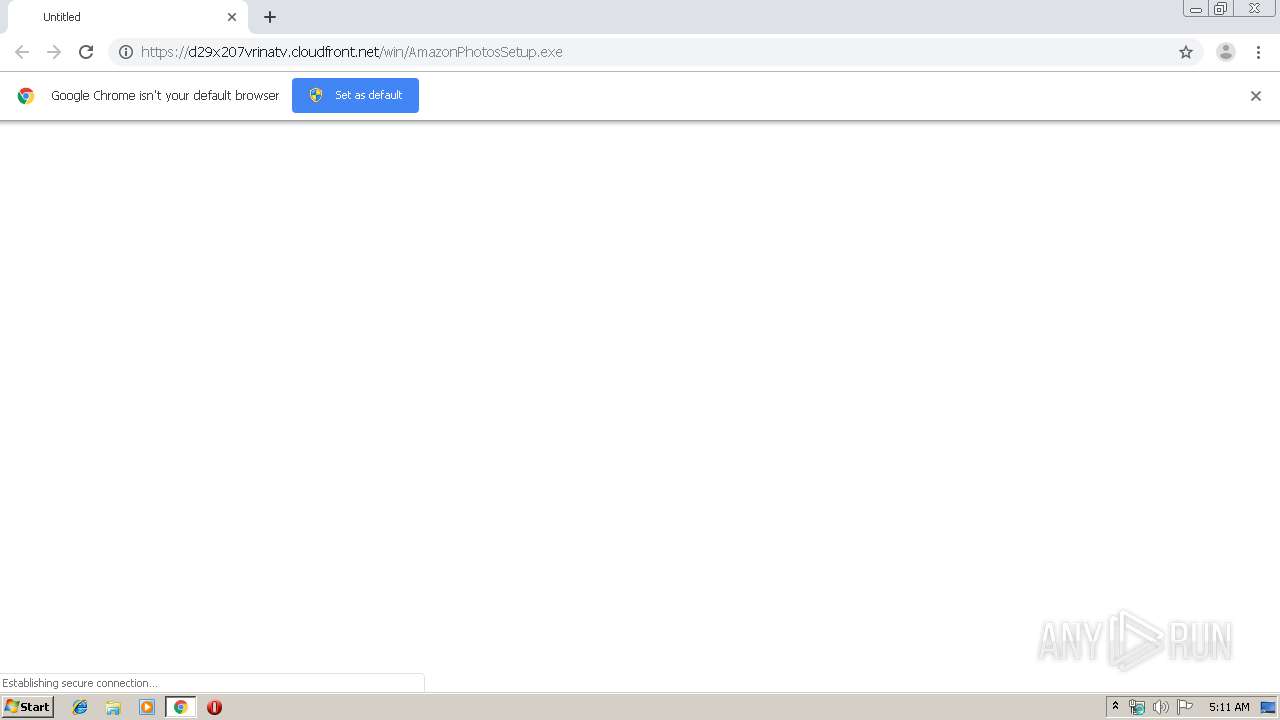
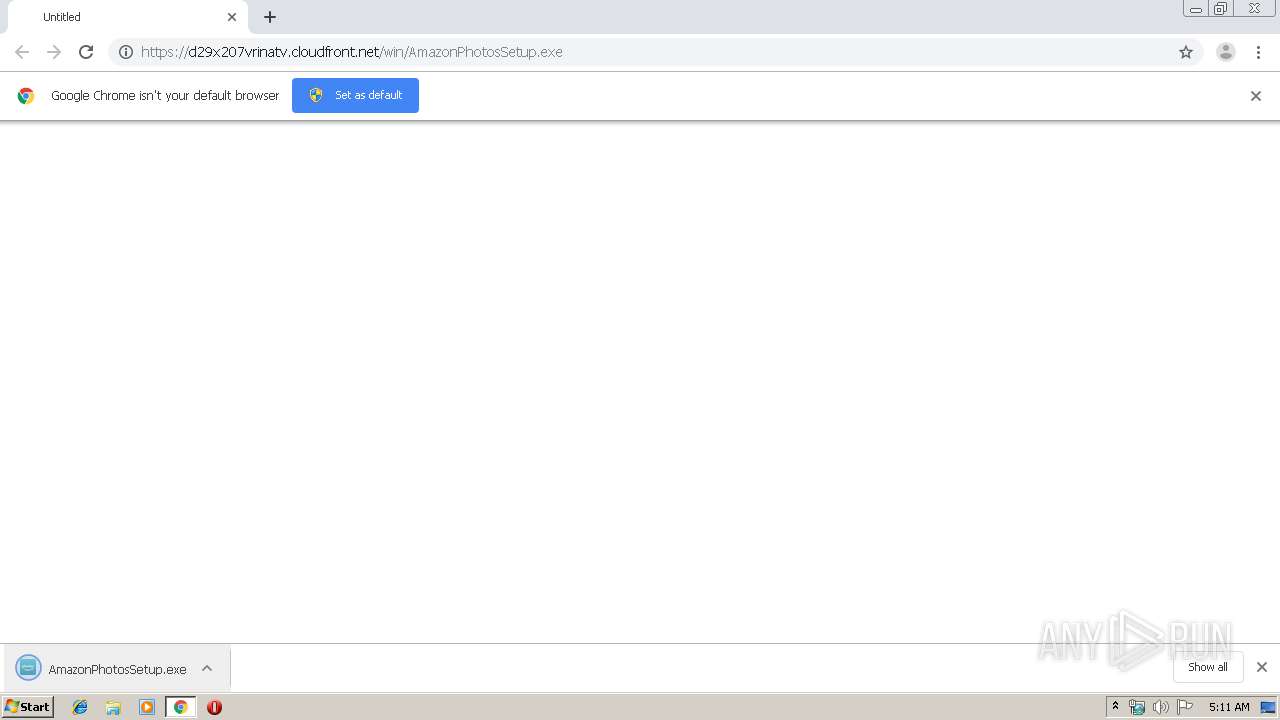
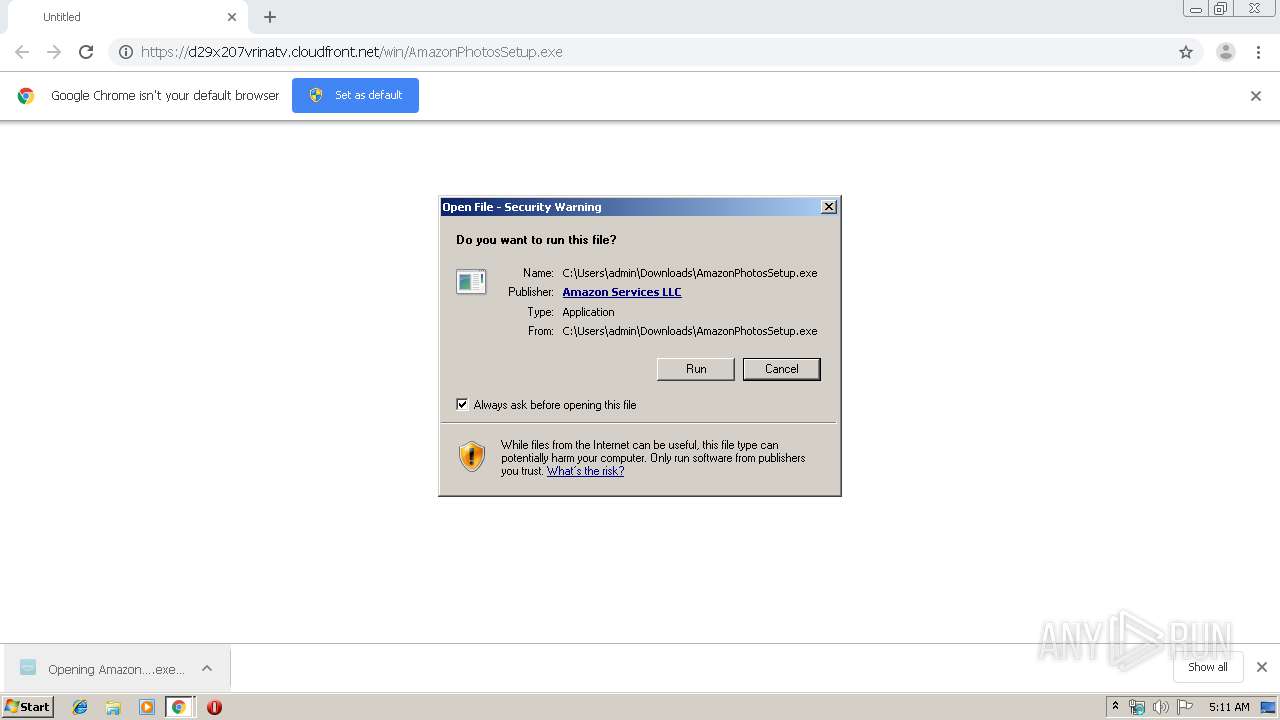
| URL: | https://d29x207vrinatv.cloudfront.net/win/AmazonPhotosSetup.exe |
| Full analysis: | https://app.any.run/tasks/2741488e-5c7a-4c95-8767-269f8a6bab34 |
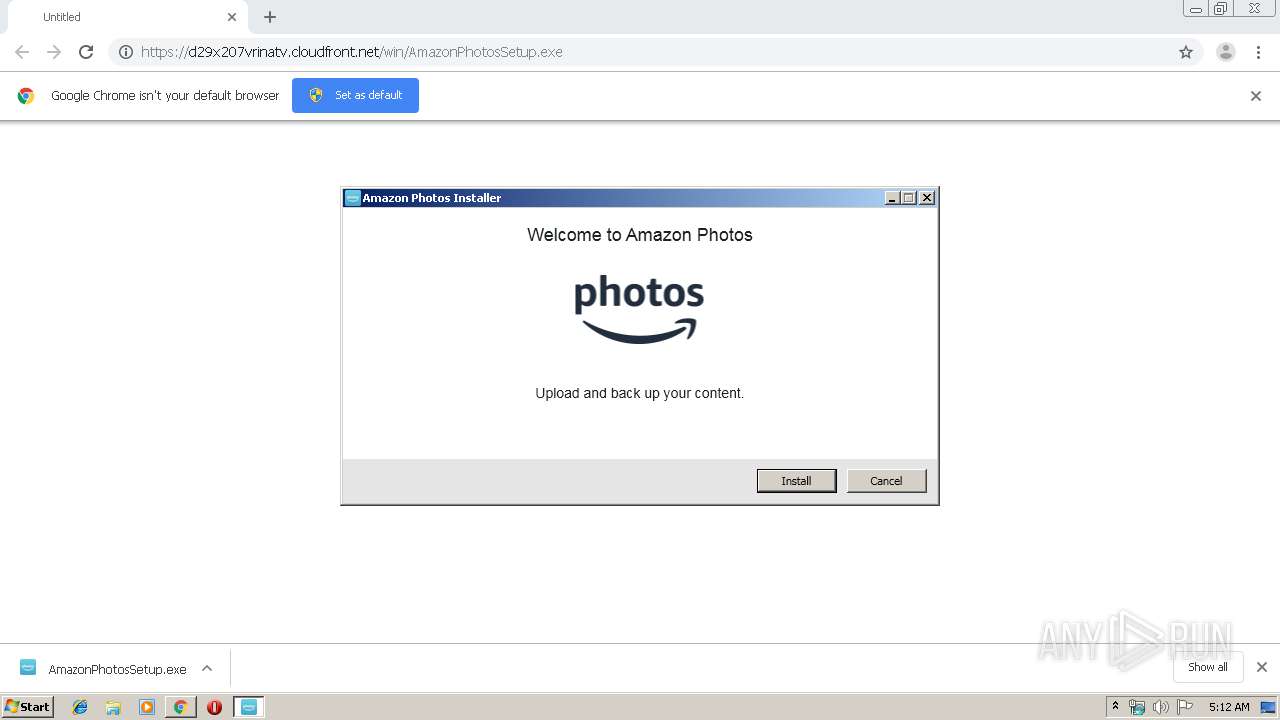
| Verdict: | Malicious activity |
| Analysis date: | January 18, 2020, 05:11:36 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | BE184B13D29EB0ED74615EEC409BF045 |
| SHA1: | 8D63D8BF273A4471D394856C4D45F9D5A0868F95 |
| SHA256: | DD6091CC5839C5260CCB5ACE657620D59421AC951FBE87D4B5BAA91CF86679F8 |
| SSDEEP: | 3:N8P2IKUGJ0l/0C+kI2gYsxAvA:2ONfvRrYs6A |
MALICIOUS
Changes settings of System certificates
- AmazonPhotosSetup.exe (PID: 3456)
Loads dropped or rewritten executable
- AmazonPhotosSetupQ.exe (PID: 3196)
- AmazonPhotos.exe (PID: 4060)
Changes the autorun value in the registry
- AmazonPhotosSetupQ.exe (PID: 3196)
Application was dropped or rewritten from another process
- AmazonPhotos.exe (PID: 4060)
- AmazonPhotosSetup.exe (PID: 3456)
- AmazonPhotosSetupQ.exe (PID: 3196)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2368)
- chrome.exe (PID: 1972)
- AmazonPhotosSetupQ.exe (PID: 3196)
- AmazonPhotosSetup.exe (PID: 3456)
Reads Environment values
- AmazonPhotosSetup.exe (PID: 3456)
- AmazonPhotos.exe (PID: 4060)
Creates files in the program directory
- AmazonPhotosSetup.exe (PID: 3456)
- AmazonPhotos.exe (PID: 4060)
Creates a software uninstall entry
- AmazonPhotosSetupQ.exe (PID: 3196)
Creates files in the user directory
- AmazonPhotosSetupQ.exe (PID: 3196)
- AmazonPhotos.exe (PID: 4060)
- AmazonPhotosSetup.exe (PID: 3456)
Changes IE settings (feature browser emulation)
- AmazonPhotosSetupQ.exe (PID: 3196)
Reads Internet Cache Settings
- AmazonPhotos.exe (PID: 4060)
Reads internet explorer settings
- AmazonPhotos.exe (PID: 4060)
Reads the machine GUID from the registry
- AmazonPhotosSetup.exe (PID: 3456)
INFO
Reads the hosts file
- chrome.exe (PID: 1972)
- chrome.exe (PID: 2368)
Reads Internet Cache Settings
- chrome.exe (PID: 2368)
Application launched itself
- chrome.exe (PID: 2368)
Changes settings of System certificates
- chrome.exe (PID: 2368)
Reads settings of System Certificates
- AmazonPhotos.exe (PID: 4060)
- AmazonPhotosSetup.exe (PID: 3456)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
49
Monitored processes
14
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,13414990043362372438,13216414154305691942,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17913439659776262701 --mojo-platform-channel-handle=488 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 896 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,13414990043362372438,13216414154305691942,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=9283058272879515065 --mojo-platform-channel-handle=4276 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1048 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,13414990043362372438,13216414154305691942,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=12655342641307997473 --mojo-platform-channel-handle=656 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13414990043362372438,13216414154305691942,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=262252432934773925 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2236 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1756 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1020,13414990043362372438,13216414154305691942,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2688865722745345868 --mojo-platform-channel-handle=1040 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1972 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1020,13414990043362372438,13216414154305691942,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=10273954328952910070 --mojo-platform-channel-handle=1632 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2104 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13414990043362372438,13216414154305691942,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12649638801948570887 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2260 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2368 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "https://d29x207vrinatv.cloudfront.net/win/AmazonPhotosSetup.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2420 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1020,13414990043362372438,13216414154305691942,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17496062741063895007 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2480 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
2 102
Read events
1 944
Write events
155
Delete events
3
Modification events
| (PID) Process: | (2400) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2368-13223797910856500 |
Value: 259 | |||
| (PID) Process: | (2368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2368) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (2368) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
158
Suspicious files
16
Text files
91
Unknown types
13
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\34c65cd0-7082-4529-820c-b1ef1a178f63.tmp | — | |
MD5:— | SHA256:— | |||
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old~RF39a95a.TMP | text | |
MD5:— | SHA256:— | |||
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RF39a8fc.TMP | text | |
MD5:— | SHA256:— | |||
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF39a8fc.TMP | text | |
MD5:— | SHA256:— | |||
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:— | SHA256:— | |||
| 2368 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\MANIFEST-000001 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
50
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4060 | AmazonPhotos.exe | GET | — | 8.253.207.108:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
3456 | AmazonPhotosSetup.exe | POST | 204 | 52.71.114.218:80 | http://fls-na.amazon.com/1/clouddrive-photos/1/OE | US | — | — | shared |
3456 | AmazonPhotosSetup.exe | POST | 204 | 52.71.114.218:80 | http://fls-na.amazon.com/1/clouddrive-photos/1/OE | US | — | — | shared |
3456 | AmazonPhotosSetup.exe | POST | 204 | 18.209.233.89:80 | http://fls-na.amazon.com/1/clouddrive-photos/1/OE | US | — | — | shared |
3456 | AmazonPhotosSetup.exe | GET | 200 | 23.37.43.27:80 | http://s2.symcb.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCED141%2Fl2SWCyYX308B7Khio%3D | NL | der | 1.71 Kb | whitelisted |
3456 | AmazonPhotosSetup.exe | GET | 200 | 23.37.43.27:80 | http://sv.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQe6LNDJdqx%2BJOp7hVgTeaGFJ%2FCQgQUljtT8Hkzl699g%2B8uK8zKt4YecmYCEDlPLCJizC25K%2F6uIFk78XQ%3D | NL | der | 1.57 Kb | shared |
4060 | AmazonPhotos.exe | GET | — | 8.253.207.108:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
3456 | AmazonPhotosSetup.exe | POST | 204 | 18.209.233.89:80 | http://fls-na.amazon.com/1/clouddrive-photos/1/OE | US | — | — | shared |
3456 | AmazonPhotosSetup.exe | POST | 204 | 18.209.233.89:80 | http://fls-na.amazon.com/1/clouddrive-photos/1/OE | US | — | — | shared |
2368 | chrome.exe | GET | 200 | 93.184.220.29:80 | http://sv.symcb.com/sv.crt | US | der | 1.34 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1972 | chrome.exe | 216.58.205.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
1972 | chrome.exe | 172.217.16.173:443 | accounts.google.com | Google Inc. | US | whitelisted |
1972 | chrome.exe | 143.204.208.102:443 | d29x207vrinatv.cloudfront.net | — | US | unknown |
— | — | 172.217.18.4:443 | www.google.com | Google Inc. | US | whitelisted |
1972 | chrome.exe | 216.58.207.78:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2368 | chrome.exe | 93.184.220.29:80 | sv.symcb.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3456 | AmazonPhotosSetup.exe | 143.204.208.163:443 | d29x207vrinatv.cloudfront.net | — | US | whitelisted |
3456 | AmazonPhotosSetup.exe | 176.32.98.79:443 | det-ta-g7g.amazon.com | Amazon.com, Inc. | US | unknown |
3456 | AmazonPhotosSetup.exe | 52.71.114.218:80 | fls-na.amazon.com | Amazon.com, Inc. | US | unknown |
3456 | AmazonPhotosSetup.exe | 52.119.196.28:443 | det-ta-g7g.amazon.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
d29x207vrinatv.cloudfront.net |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| malicious |
sv.symcb.com |
| whitelisted |
fls-na.amazon.com |
| shared |
det-ta-g7g.amazon.com |
| unknown |
ssl.gstatic.com |
| whitelisted |
s2.symcb.com |
| whitelisted |