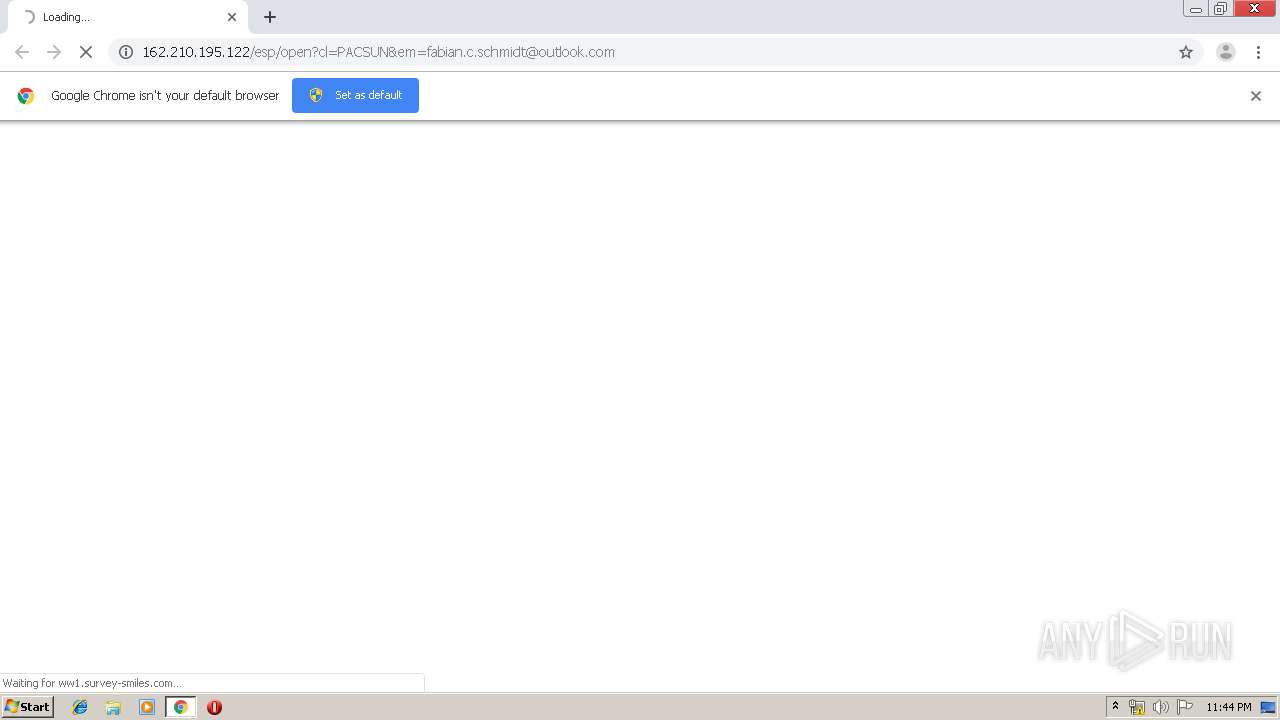
| URL: | http://162.210.195.122/esp/open?cl=PACSUN&em=fabian.c.schmidt@outlook.com |
| Full analysis: | https://app.any.run/tasks/a4f0e833-3bc0-4999-9a31-516f9a5005cb |
| Verdict: | Malicious activity |
| Analysis date: | July 11, 2019, 22:44:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 741B7888CD873A5ED4D9EFE31F4678AE |
| SHA1: | 9477A7B5C5FCE70AD1F97858AFA619E2ABEE9498 |
| SHA256: | DD5891F306086C96F3A27ED5C6C88B3E6A1072DCF5BF7CFB2CE289032ABD14E0 |
| SSDEEP: | 3:N1KrgrGRw25uDiYWGhXRjkGT:CK89ClRjb |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3320)
INFO
Application launched itself
- chrome.exe (PID: 3320)
Reads settings of System Certificates
- chrome.exe (PID: 2780)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
22
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,1950797460820085351,3372199184442401014,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12822135864262241147 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2456 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1400 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1016,1950797460820085351,3372199184442401014,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=15472820735844316360 --mojo-platform-channel-handle=1032 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,1950797460820085351,3372199184442401014,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16350545858118770304 --mojo-platform-channel-handle=3416 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,1950797460820085351,3372199184442401014,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2844727965206604143 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2524 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1016,1950797460820085351,3372199184442401014,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=10735741928492415211 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3212 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,1950797460820085351,3372199184442401014,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=5655182838350588117 --mojo-platform-channel-handle=2916 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,1950797460820085351,3372199184442401014,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=5038835102445226726 --mojo-platform-channel-handle=1448 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2980 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,1950797460820085351,3372199184442401014,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10123213732908063511 --mojo-platform-channel-handle=3632 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1016,1950797460820085351,3372199184442401014,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7674257278267396108 --mojo-platform-channel-handle=3812 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3220 --on-initialized-event-handle=312 --parent-handle=316 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
623
Read events
530
Write events
88
Delete events
5
Modification events
| (PID) Process: | (3320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3160) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3320-13207358665373500 |
Value: 259 | |||
| (PID) Process: | (3320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3320) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 1512-13197841398593750 |
Value: 0 | |||
| (PID) Process: | (3320) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
9
Text files
192
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ec6040c0-aa98-41ad-b5e2-f2457b375fa0.tmp | — | |
MD5:— | SHA256:— | |||
| 3320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000020.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old~RFcdca9.TMP | text | |
MD5:— | SHA256:— | |||
| 3320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RFcdc3c.TMP | text | |
MD5:— | SHA256:— | |||
| 3320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFcdc3c.TMP | text | |
MD5:— | SHA256:— | |||
| 3320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3320 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
20
TCP/UDP connections
27
DNS requests
17
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2780 | chrome.exe | GET | 200 | 2.16.186.64:80 | http://i4.cdn-image.com/__media__/js/min.js?v2.2 | unknown | text | 2.97 Kb | whitelisted |
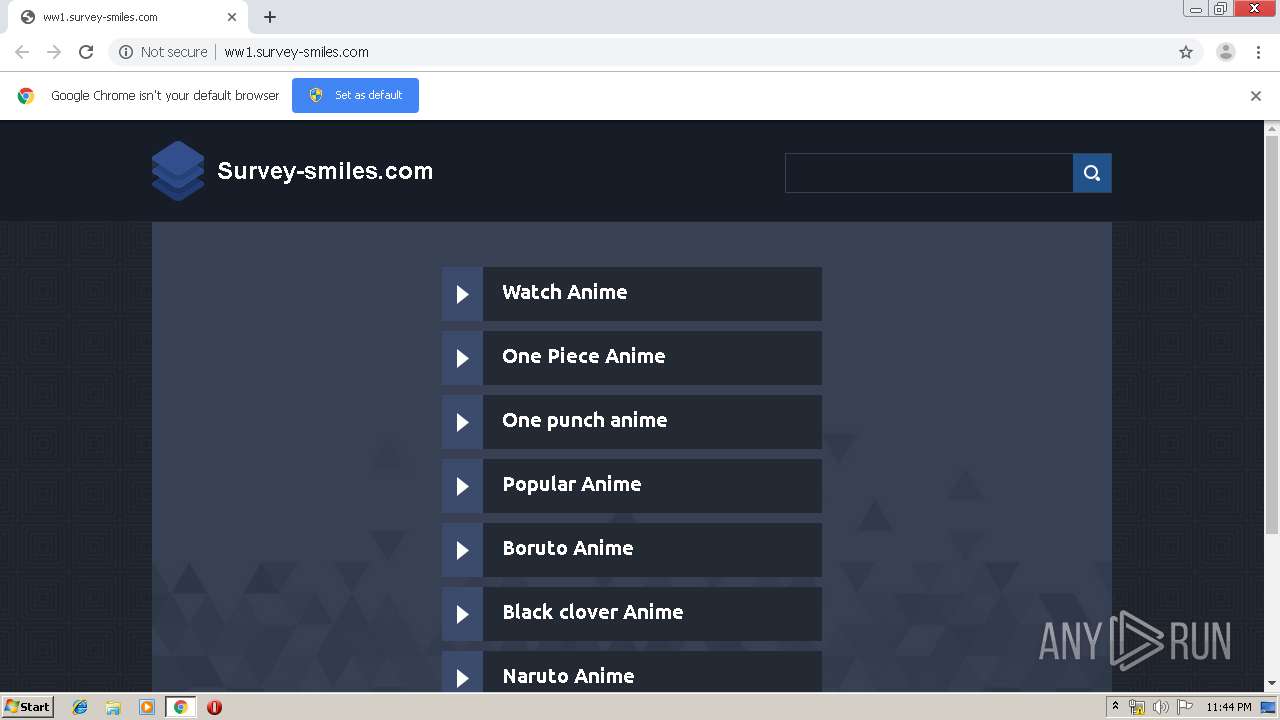
2780 | chrome.exe | GET | 200 | 208.91.196.145:80 | http://ww1.survey-smiles.com/?fp=728O9CQIXb8FBSmtk41qTbu46G9jfMIXF7Nll17wngcSRiocdgf%2FF3pY0fJg78o1sdmbYa1ot0UZU47WMv1OhMohUqr47NY5gYElHAppGecprJoA0wd54gnlRLw39TGUv5noL%2B3k0aedeKHReF4x5bipLSqcIm9aHMNbHLWqXkwTEDadNSSgVob9dXYn4g%2Bg&prvtof=%2B4Ax9eb9Vfg86YqFf4bhL8CbOfqzEAc8DdBVbuvGvfM%3D&poru=YDnzwvZOg1X7ZlRmmZGhBWqRzIKbRrTbTxav1tRwo%2BPetMVavbhPUfANgqxyxnrL& | VG | html | 4.81 Kb | malicious |
2780 | chrome.exe | GET | 200 | 208.91.196.145:80 | http://ww1.survey-smiles.com/px.js?ch=1 | VG | text | 346 b | malicious |
2780 | chrome.exe | GET | 200 | 2.16.186.106:80 | http://i3.cdn-image.com/__media__/pics/12471/libg.png | unknown | image | 1.07 Kb | whitelisted |
2780 | chrome.exe | GET | 302 | 216.58.208.46:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOWVmQUFXS041NV9ZVXlJVWwxbGc5TUM4dw/7519.422.0.3_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 515 b | whitelisted |
2780 | chrome.exe | GET | 200 | 2.16.186.106:80 | http://i3.cdn-image.com/__media__/pics/12471/arrow.png | unknown | image | 1.04 Kb | whitelisted |
2780 | chrome.exe | GET | 200 | 2.16.186.106:80 | http://i2.cdn-image.com/__media__/fonts/ubuntu-b/ubuntu-b.woff | unknown | woff | 37.0 Kb | whitelisted |
2780 | chrome.exe | GET | 200 | 2.16.186.106:80 | http://i3.cdn-image.com/__media__/pics/12471/bodybg.png | unknown | image | 94.9 Kb | whitelisted |
2780 | chrome.exe | GET | 200 | 2.16.186.106:80 | http://i1.cdn-image.com/__media__/pics/12471/logo.png | unknown | image | 3.86 Kb | whitelisted |
2780 | chrome.exe | GET | 200 | 2.16.186.64:80 | http://i4.cdn-image.com/__media__/pics/12471/libgh.png | unknown | image | 1.06 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2780 | chrome.exe | 162.210.195.122:80 | — | Leaseweb USA, Inc. | US | malicious |
2780 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2780 | chrome.exe | 5.79.68.107:80 | survey-smiles.com | LeaseWeb Netherlands B.V. | NL | malicious |
2780 | chrome.exe | 172.217.23.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
2780 | chrome.exe | 2.16.186.106:80 | i4.cdn-image.com | Akamai International B.V. | — | whitelisted |
— | — | 172.217.18.1:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
2780 | chrome.exe | 208.91.196.145:80 | ww1.survey-smiles.com | Confluence Networks Inc | VG | malicious |
— | — | 216.58.208.46:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
2780 | chrome.exe | 172.217.22.46:443 | clients2.google.com | Google Inc. | US | whitelisted |
2780 | chrome.exe | 216.58.205.227:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
survey-smiles.com |
| whitelisted |
ww1.survey-smiles.com |
| malicious |
i4.cdn-image.com |
| whitelisted |
i3.cdn-image.com |
| whitelisted |
i1.cdn-image.com |
| whitelisted |
clients1.google.com |
| whitelisted |
i2.cdn-image.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2780 | chrome.exe | Generic Protocol Command Decode | SURICATA HTTP unable to match response to request |