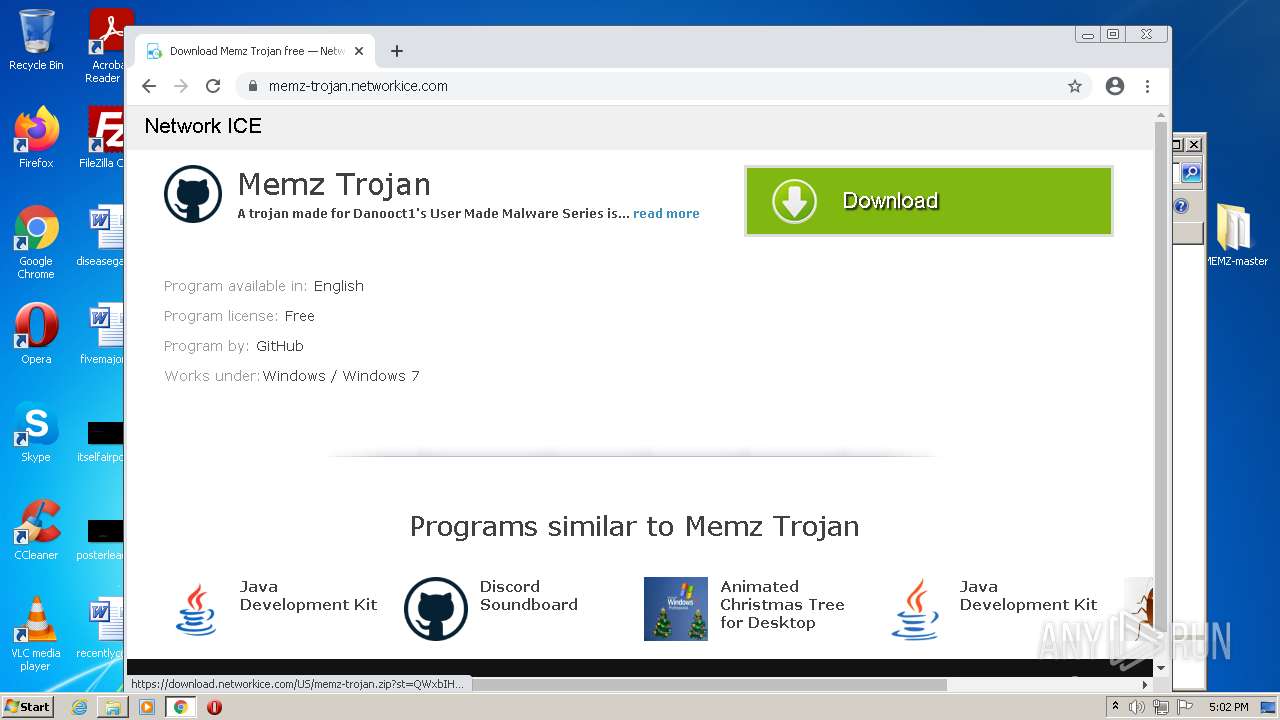
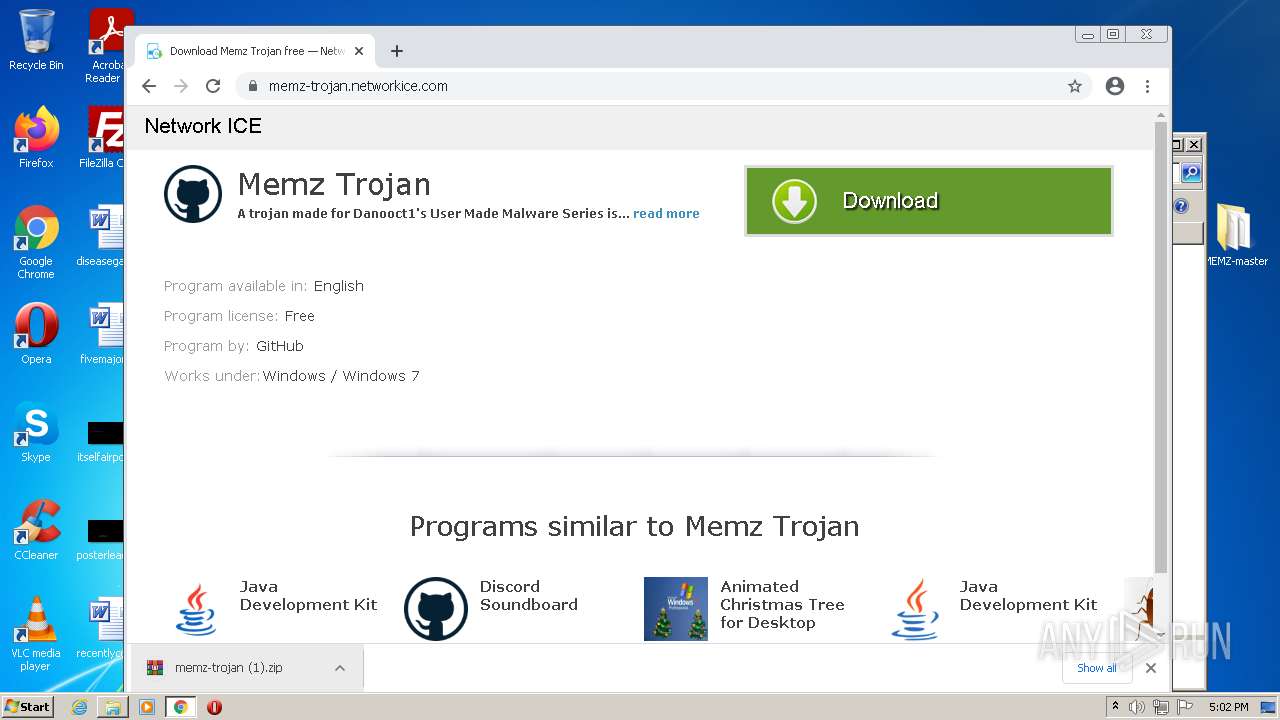
| download: | download |
| Full analysis: | https://app.any.run/tasks/d3ea043a-1f71-4c6b-ad1a-09f93c1104d6 |
| Verdict: | Malicious activity |
| Analysis date: | April 27, 2022, 16:00:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, UTF-8 Unicode text, with very long lines |
| MD5: | EEF5AF60F4E4B06F1A575933CCA573AA |
| SHA1: | B4A1EDB6295539DB713A7D527A8A6268D69A187A |
| SHA256: | DD5293B6B702EB771ECED3964D6AE31B46B93EF92F98A2B85EE08CEFC5E1F602 |
| SSDEEP: | 768:y07ULDMgvL/zZyqt8l8dik3dtFdp3a9w3jU9Ns2l1ITE8ElV09NVsj:ELDMgzr0qWl8di6dfT3In8Epj |
MALICIOUS
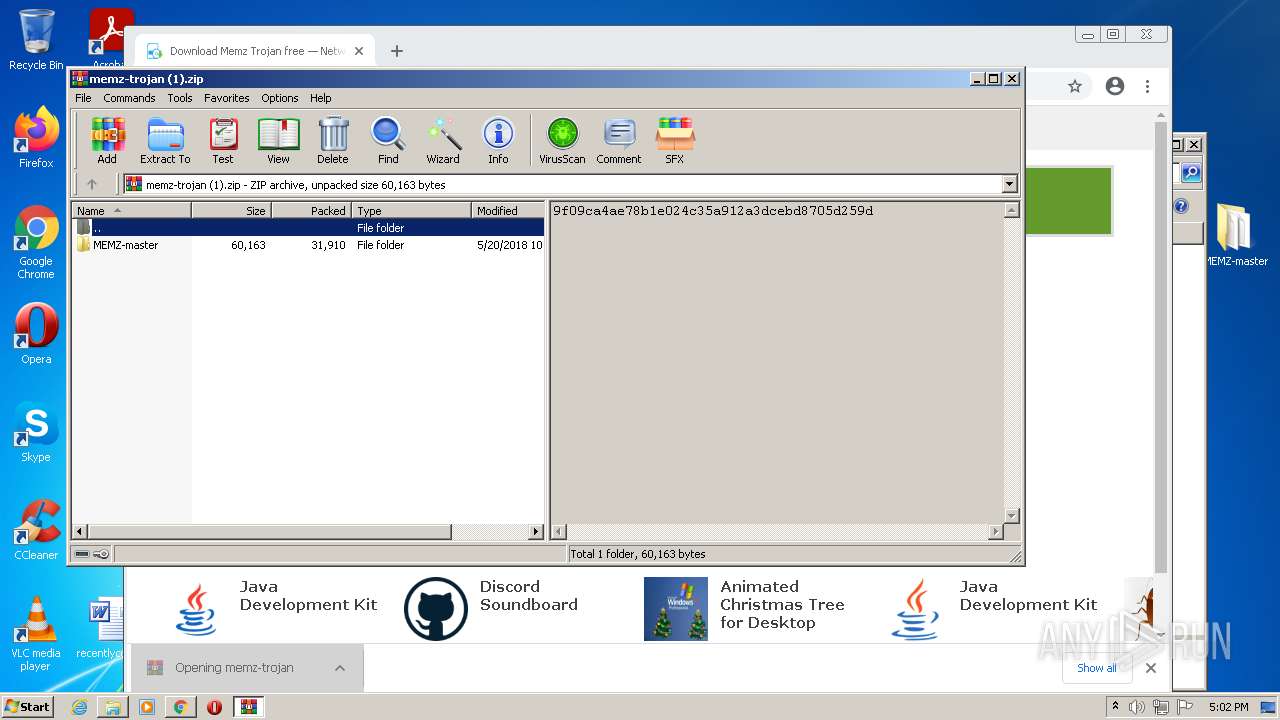
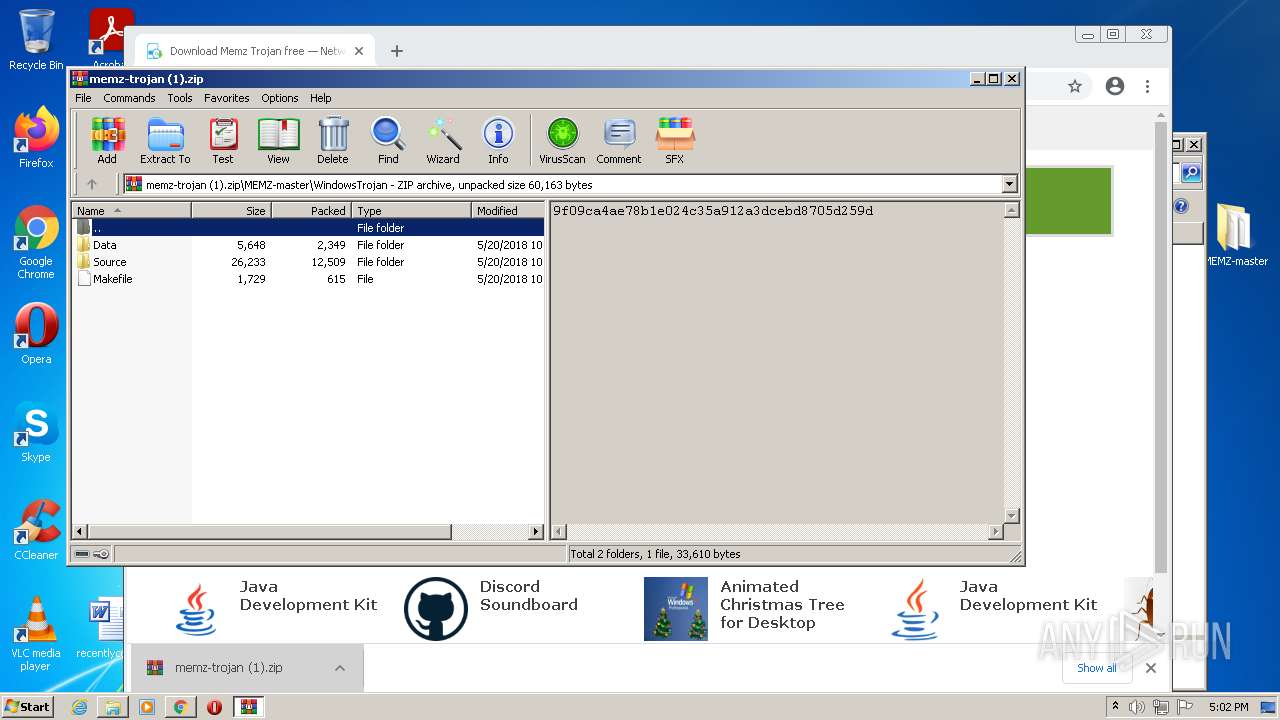
Drops executable file immediately after starts
- chrome.exe (PID: 1936)
SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 1936)
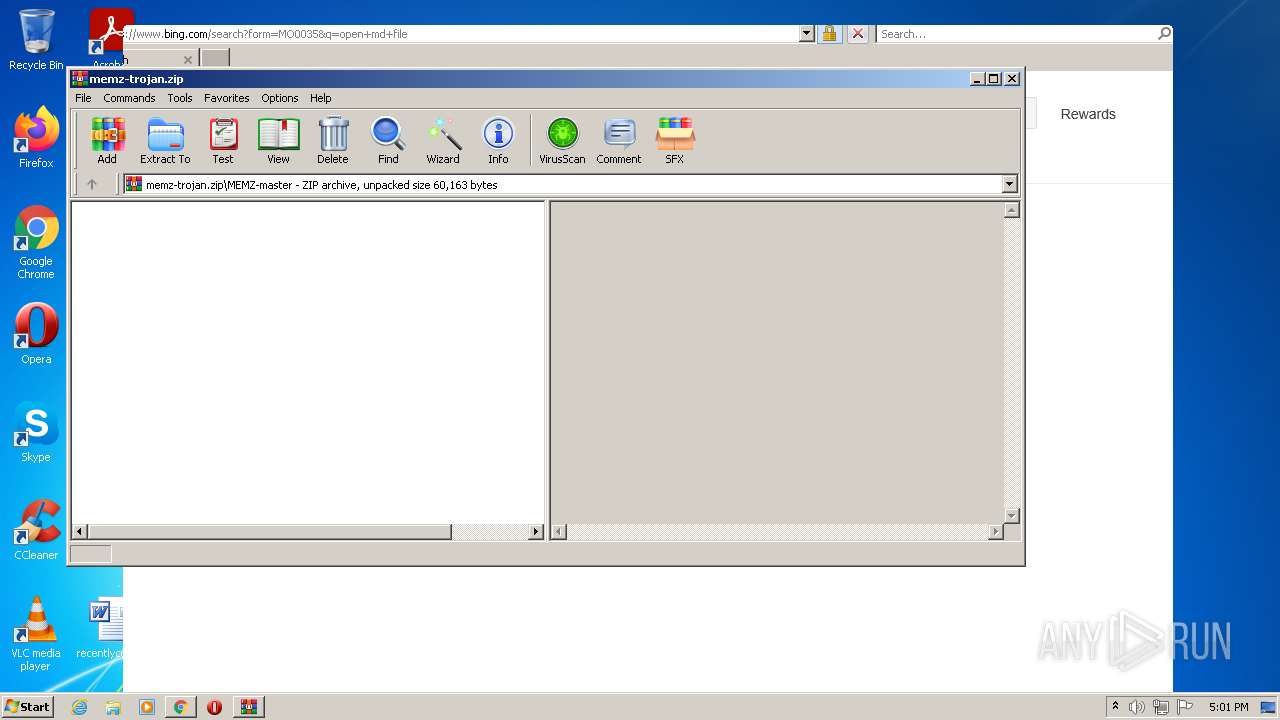
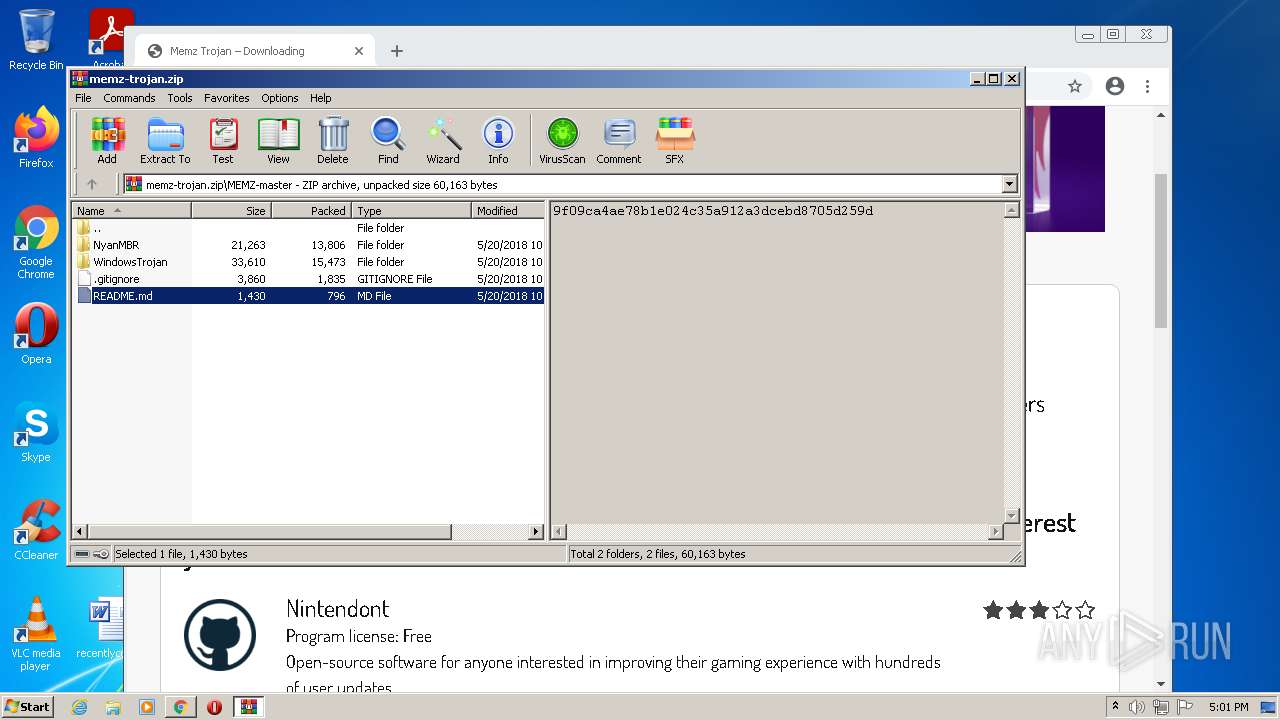
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 3096)
Checks supported languages
- WinRAR.exe (PID: 3096)
- WinRAR.exe (PID: 2332)
Reads the computer name
- WinRAR.exe (PID: 3096)
- WinRAR.exe (PID: 2332)
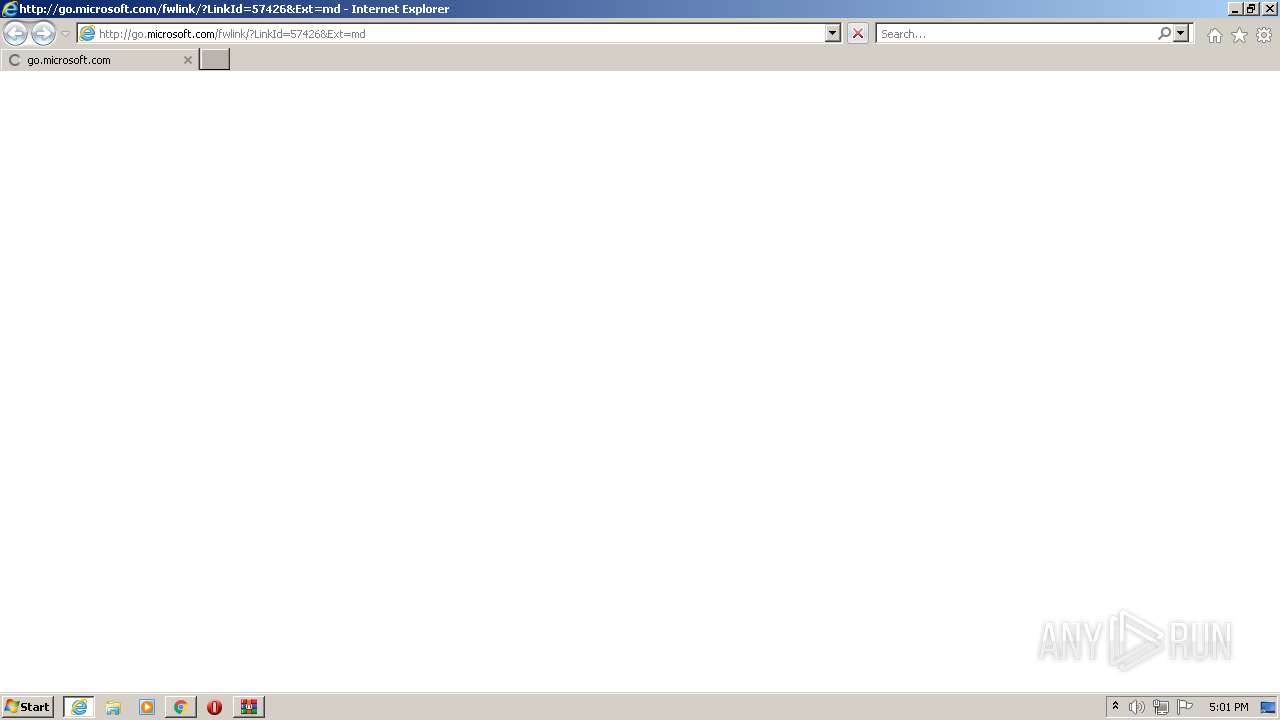
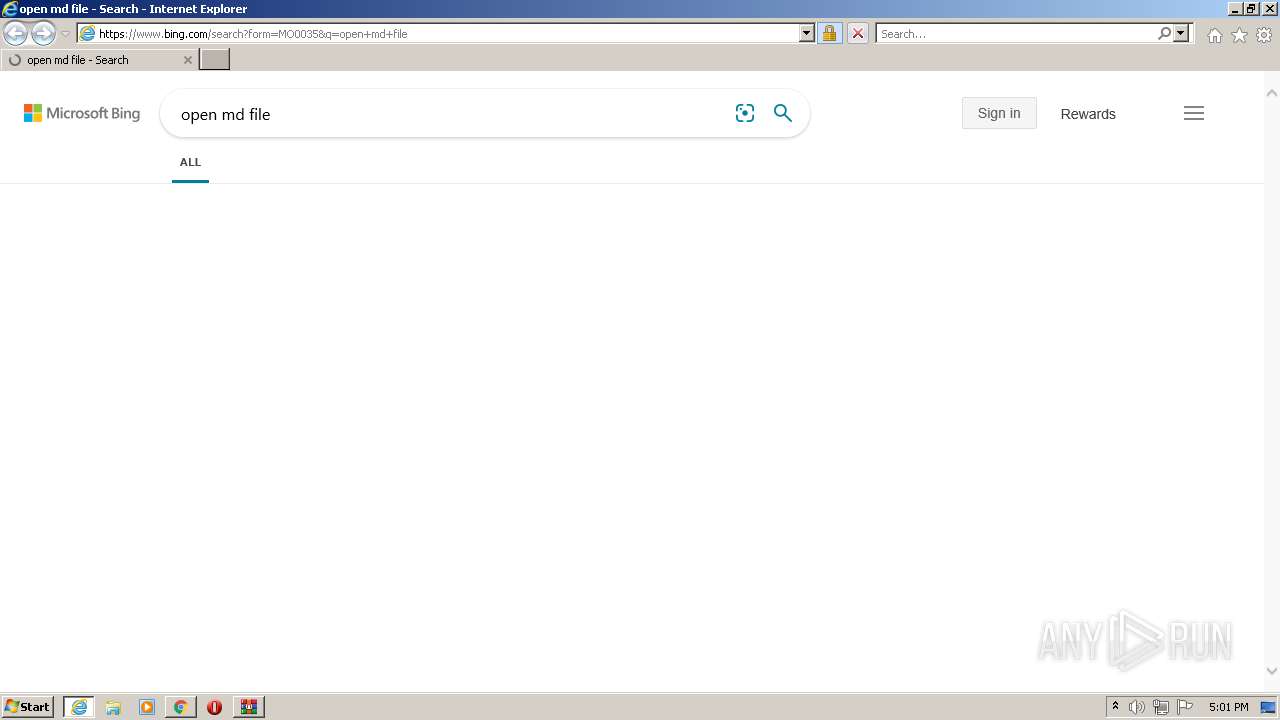
Starts Internet Explorer
- rundll32.exe (PID: 1792)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2440)
Drops a file with a compile date too recent
- chrome.exe (PID: 1936)
INFO
Reads the computer name
- rundll32.exe (PID: 956)
- chrome.exe (PID: 1936)
- chrome.exe (PID: 3368)
- chrome.exe (PID: 3396)
- chrome.exe (PID: 3648)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 2384)
- chrome.exe (PID: 3600)
- chrome.exe (PID: 3176)
- rundll32.exe (PID: 1792)
- iexplore.exe (PID: 2028)
- chrome.exe (PID: 2828)
- iexplore.exe (PID: 2440)
- chrome.exe (PID: 856)
- rundll32.exe (PID: 1972)
- chrome.exe (PID: 3140)
- chrome.exe (PID: 560)
Checks supported languages
- chrome.exe (PID: 1936)
- rundll32.exe (PID: 956)
- chrome.exe (PID: 188)
- chrome.exe (PID: 3396)
- chrome.exe (PID: 3368)
- chrome.exe (PID: 3648)
- chrome.exe (PID: 2376)
- chrome.exe (PID: 1100)
- chrome.exe (PID: 568)
- chrome.exe (PID: 3656)
- chrome.exe (PID: 2976)
- chrome.exe (PID: 3004)
- chrome.exe (PID: 2668)
- chrome.exe (PID: 2132)
- chrome.exe (PID: 2752)
- chrome.exe (PID: 2852)
- chrome.exe (PID: 2420)
- chrome.exe (PID: 2372)
- chrome.exe (PID: 1164)
- chrome.exe (PID: 2812)
- chrome.exe (PID: 1912)
- chrome.exe (PID: 3136)
- chrome.exe (PID: 3472)
- chrome.exe (PID: 3140)
- chrome.exe (PID: 4060)
- chrome.exe (PID: 3228)
- chrome.exe (PID: 3580)
- chrome.exe (PID: 2448)
- chrome.exe (PID: 2908)
- chrome.exe (PID: 2384)
- chrome.exe (PID: 2532)
- chrome.exe (PID: 3624)
- chrome.exe (PID: 2784)
- chrome.exe (PID: 2932)
- chrome.exe (PID: 3048)
- chrome.exe (PID: 3600)
- chrome.exe (PID: 3176)
- rundll32.exe (PID: 1792)
- iexplore.exe (PID: 2028)
- iexplore.exe (PID: 2440)
- chrome.exe (PID: 3780)
- chrome.exe (PID: 2828)
- rundll32.exe (PID: 268)
- chrome.exe (PID: 472)
- chrome.exe (PID: 3156)
- chrome.exe (PID: 3408)
- chrome.exe (PID: 1228)
- chrome.exe (PID: 2476)
- chrome.exe (PID: 3756)
- chrome.exe (PID: 4004)
- chrome.exe (PID: 3664)
- chrome.exe (PID: 1640)
- chrome.exe (PID: 856)
- rundll32.exe (PID: 1972)
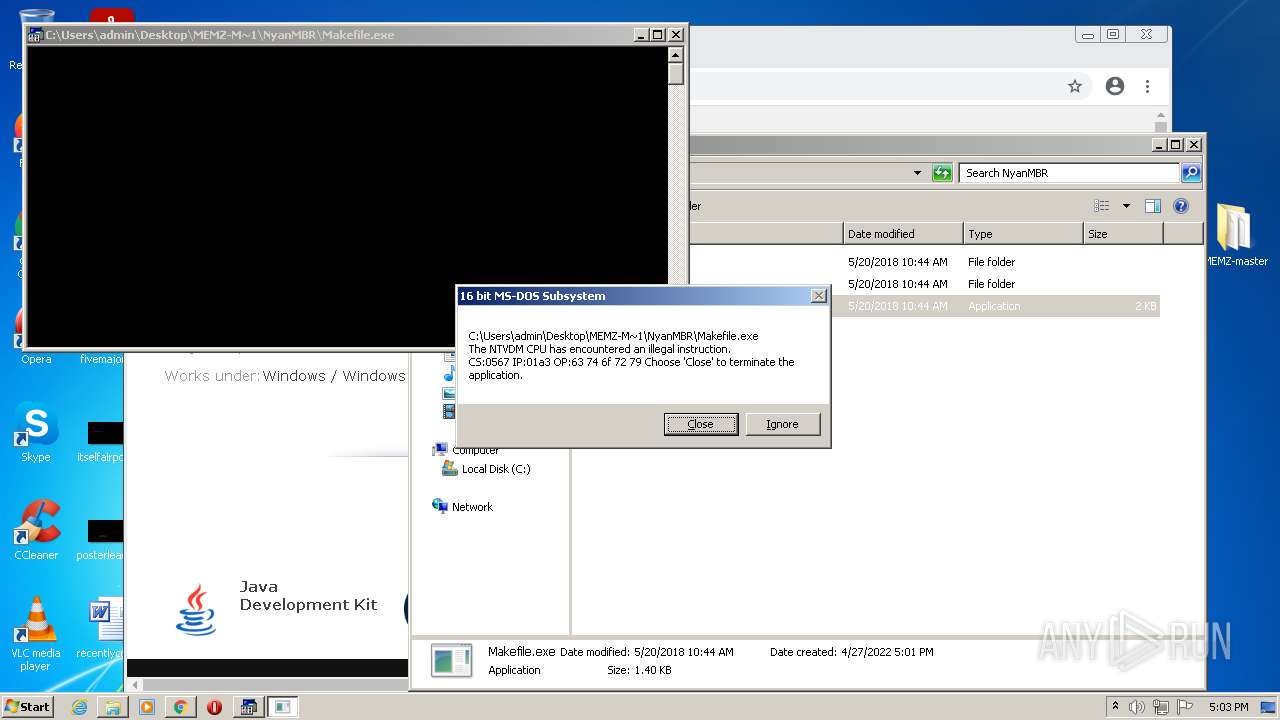
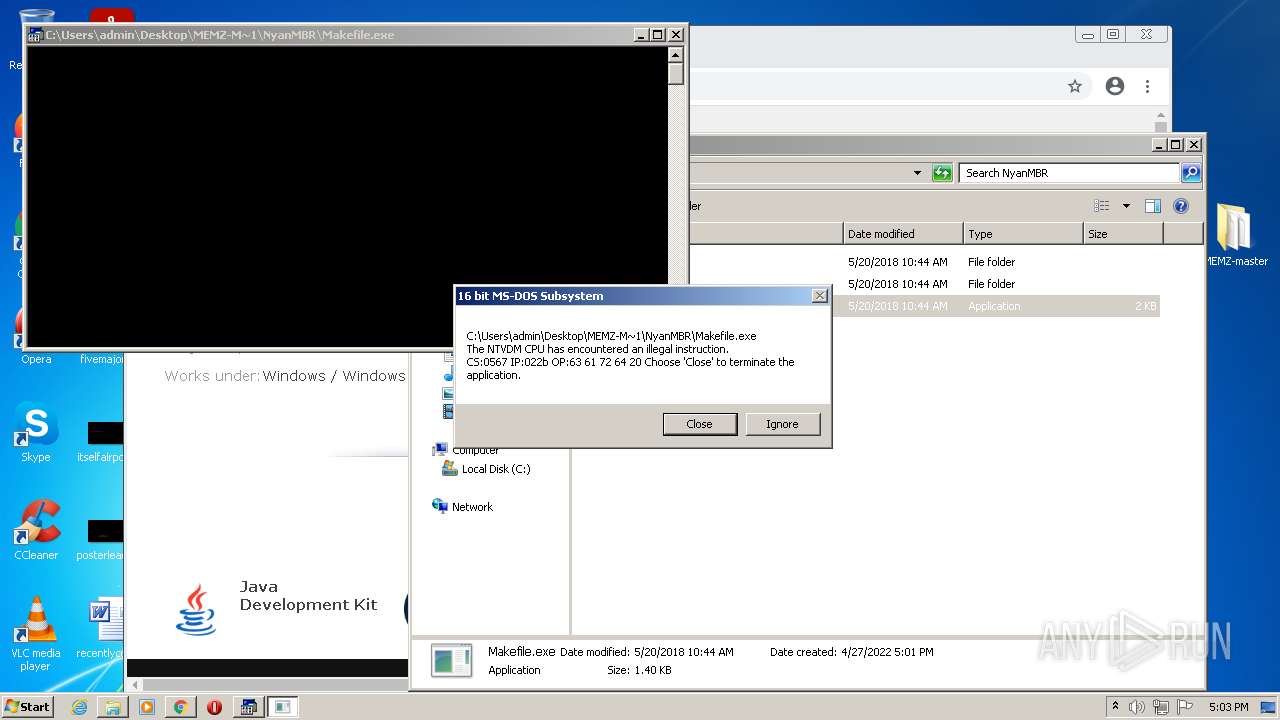
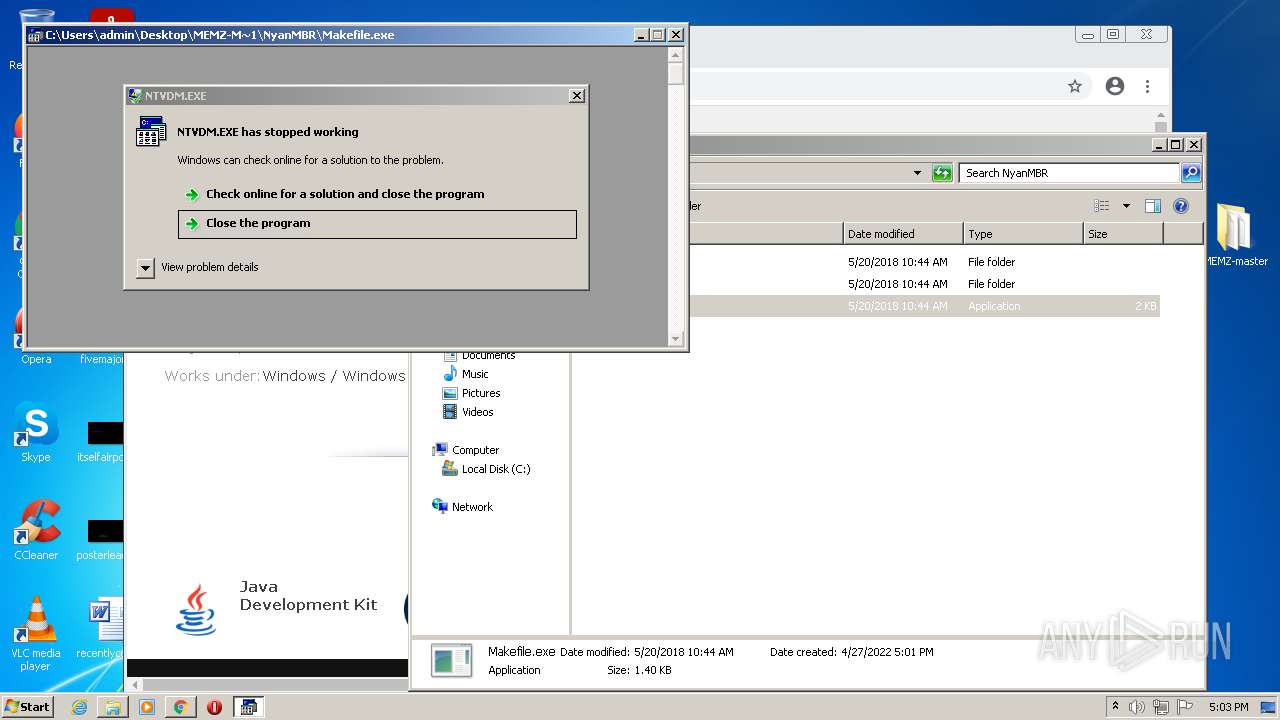
- ntvdm.exe (PID: 1852)
- chrome.exe (PID: 2284)
- chrome.exe (PID: 2576)
- chrome.exe (PID: 2724)
- chrome.exe (PID: 668)
- ntvdm.exe (PID: 2692)
- ntvdm.exe (PID: 1968)
- chrome.exe (PID: 2712)
- chrome.exe (PID: 3888)
- chrome.exe (PID: 3020)
- chrome.exe (PID: 2480)
- chrome.exe (PID: 2996)
- chrome.exe (PID: 2736)
- chrome.exe (PID: 3140)
- chrome.exe (PID: 560)
- chrome.exe (PID: 3052)
- chrome.exe (PID: 3584)
- chrome.exe (PID: 3964)
- chrome.exe (PID: 2156)
- chrome.exe (PID: 3000)
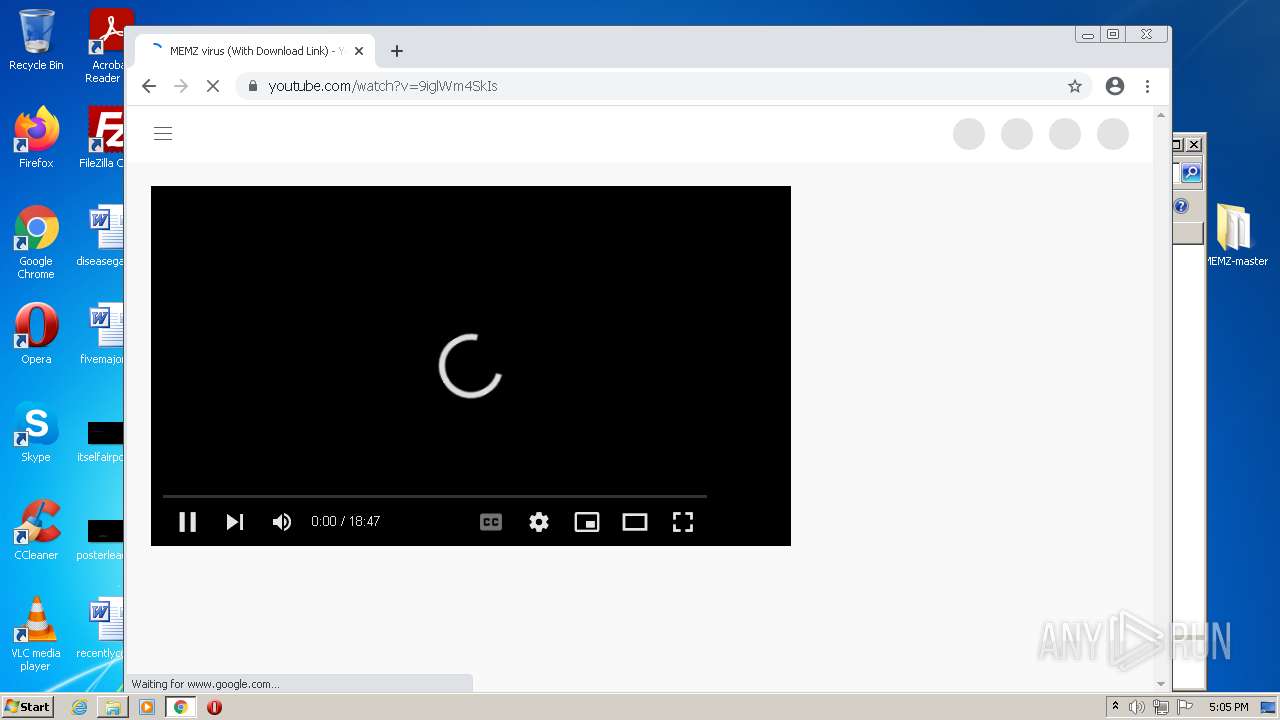
Manual execution by user
- chrome.exe (PID: 1936)
- rundll32.exe (PID: 268)
- rundll32.exe (PID: 1972)
- ntvdm.exe (PID: 1852)
- ntvdm.exe (PID: 2692)
- ntvdm.exe (PID: 1968)
Reads the hosts file
- chrome.exe (PID: 1936)
- chrome.exe (PID: 3396)
Reads settings of System Certificates
- chrome.exe (PID: 3396)
- iexplore.exe (PID: 2440)
Application launched itself
- chrome.exe (PID: 1936)
- iexplore.exe (PID: 2028)
Reads the date of Windows installation
- chrome.exe (PID: 3600)
- iexplore.exe (PID: 2028)
Changes internet zones settings
- iexplore.exe (PID: 2028)
Creates files in the user directory
- iexplore.exe (PID: 2440)
Checks Windows Trust Settings
- iexplore.exe (PID: 2440)
Reads internet explorer settings
- iexplore.exe (PID: 2440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
HTML
| themeColor: | #1a7dff |
|---|---|
| referrer: | no-referrer-when-downgrade |
| cconsentContentSelector: | <p class='cc_message'>es.download.it uses its own and third-party cookies to show personalized content and ads on its properties and other sites, and to analyze how its services are used. By closing this notice, by scrolling this page, by clicking on any element outside of this notice you accept their use. <a href='https://www.iubenda.com/privacy-policy/61913038/cookie-policy' target='_blank'>Cookie Policy</a> <a href='https://www.iubenda.com/privacy-policy/61913038' target='_blank'>Privacy Policy</a></p> |
| cconsentLang: | es |
| cconsentPolicyUrl: | https://www.iubenda.com/privacy-policy/61913038/cookie-policy |
| cconsentDomain: | es.download.it |
| HTTPEquivXUACompatible: | ie=edge |
| viewport: | width=device-width, initial-scale=1, shrink-to-fit=no |
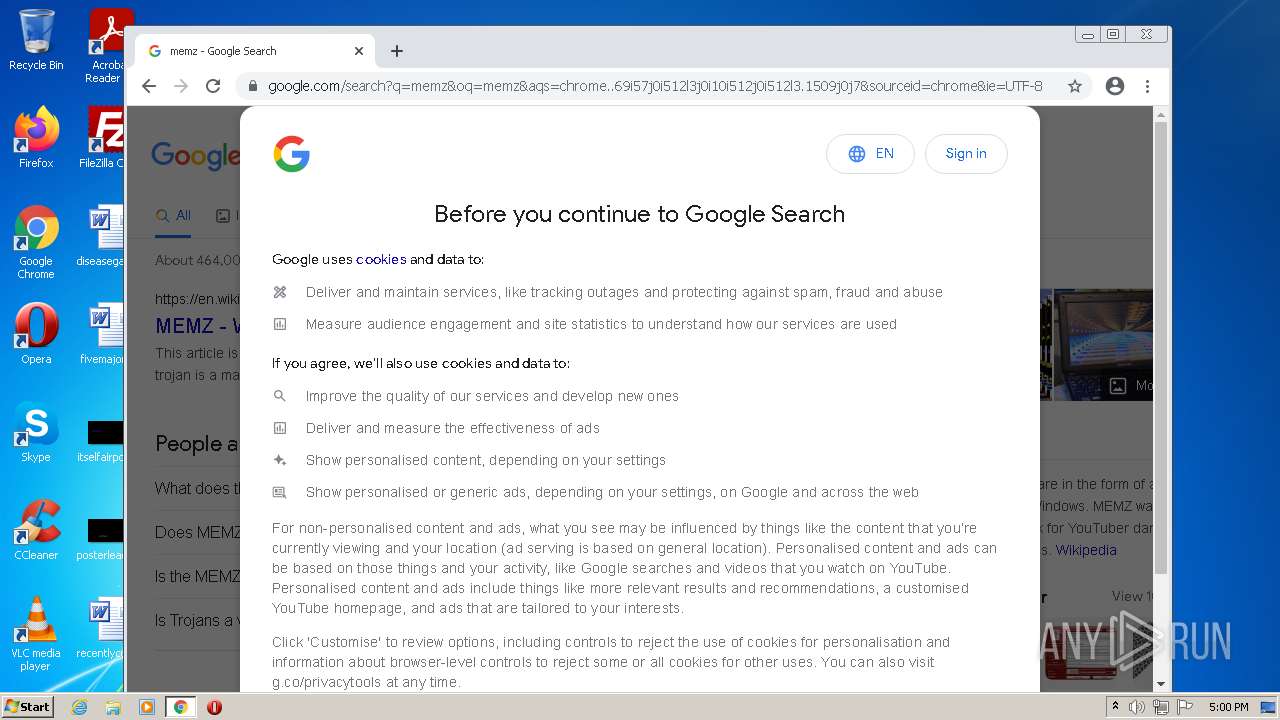
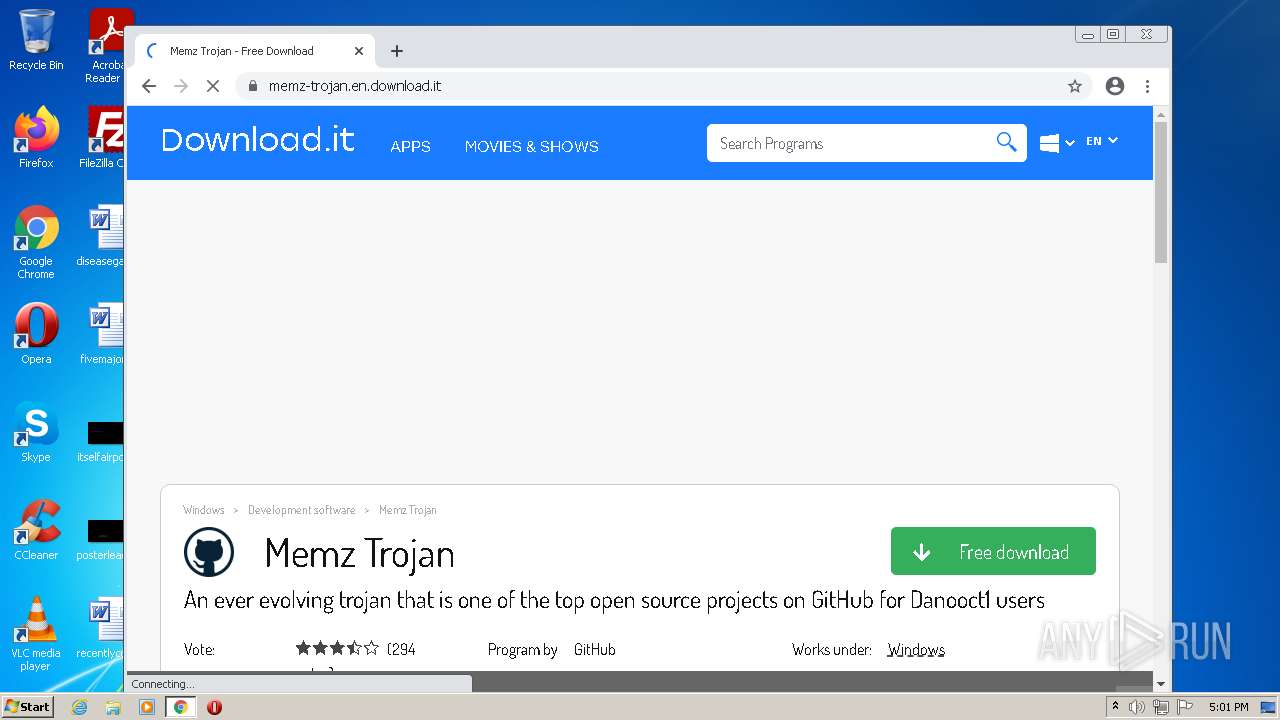
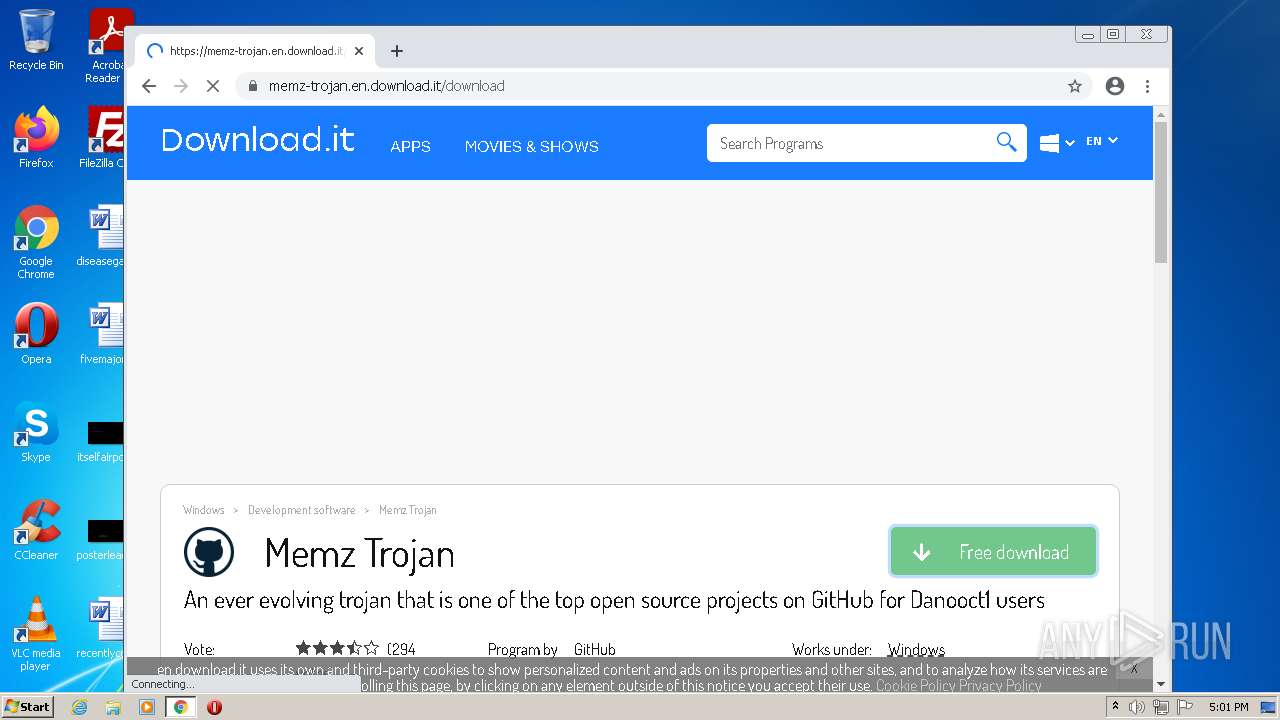
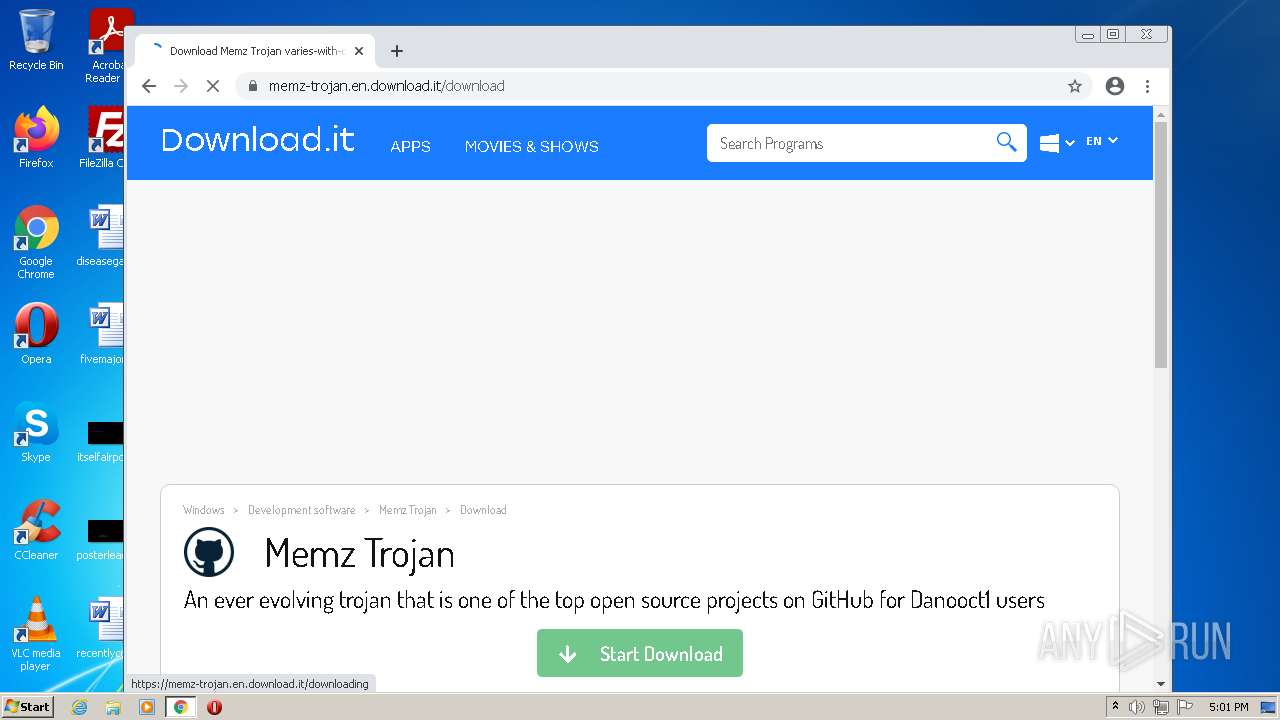
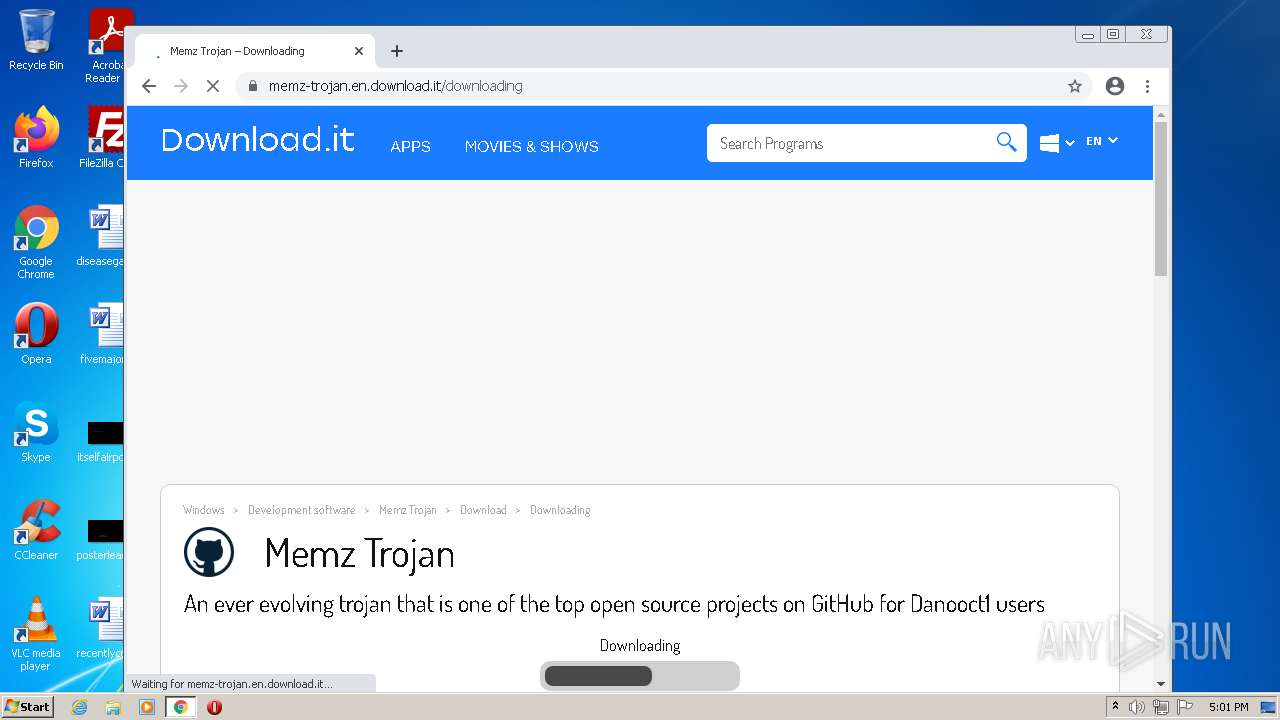
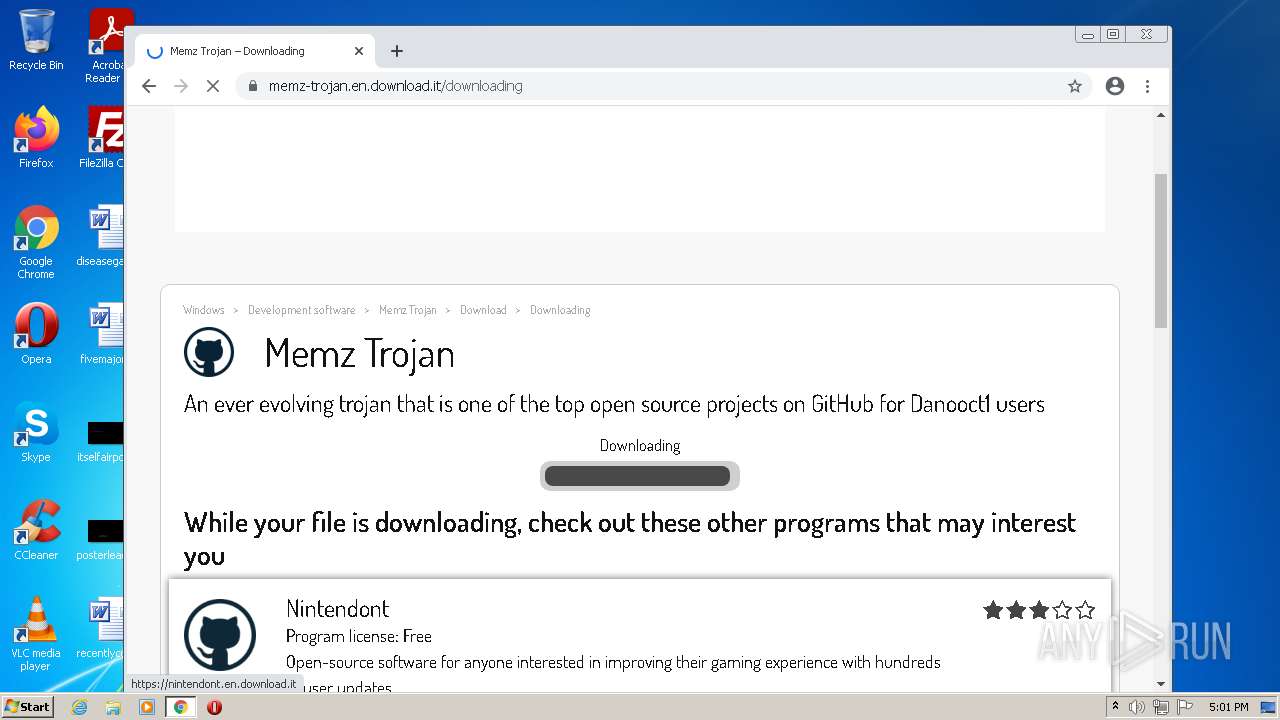
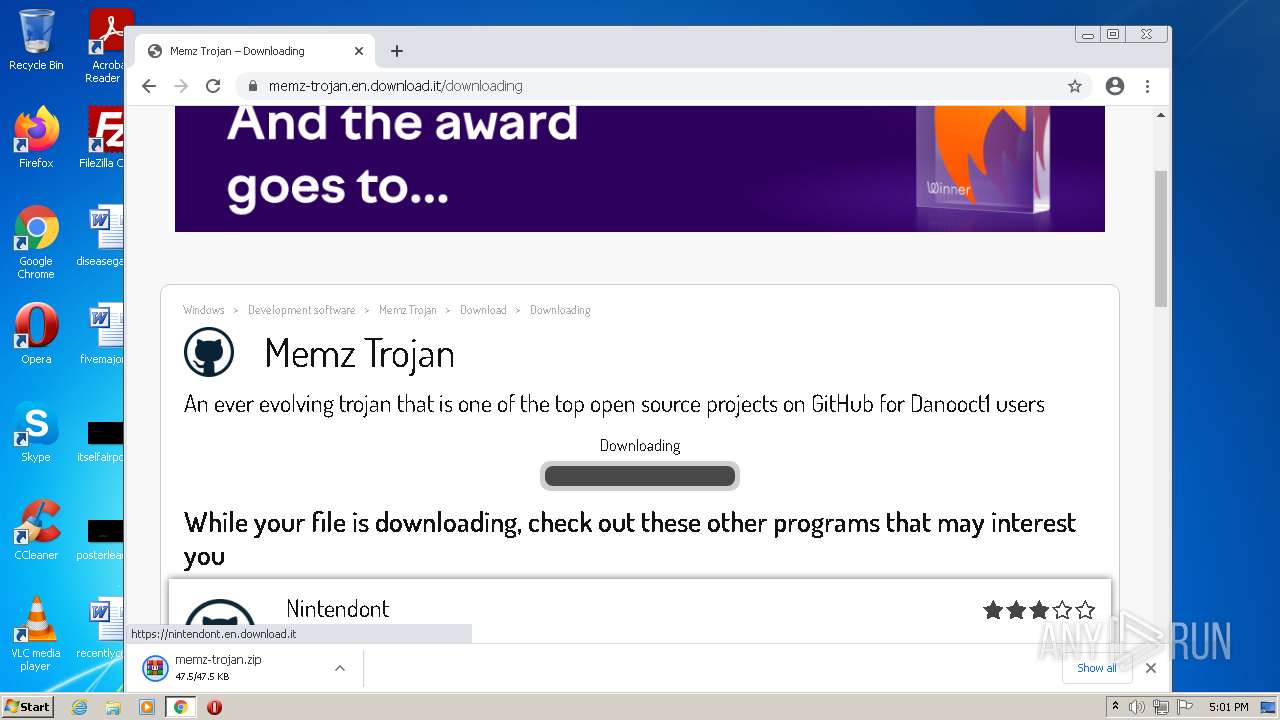
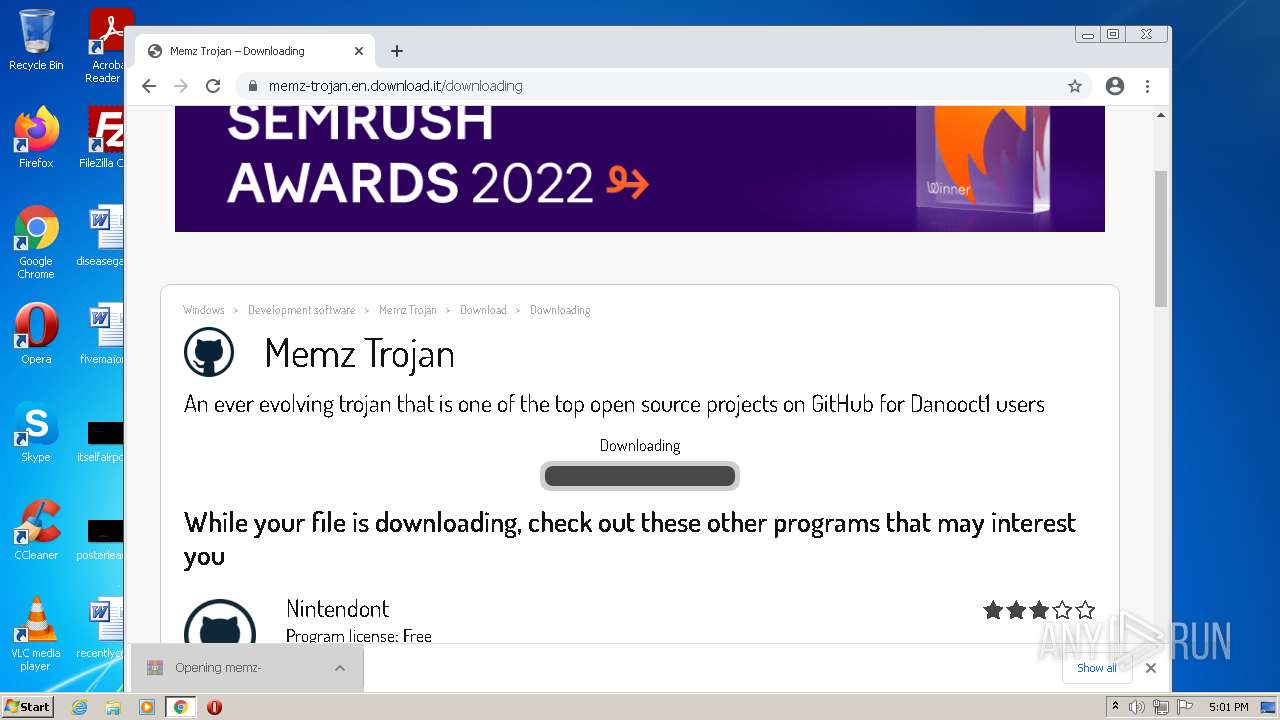
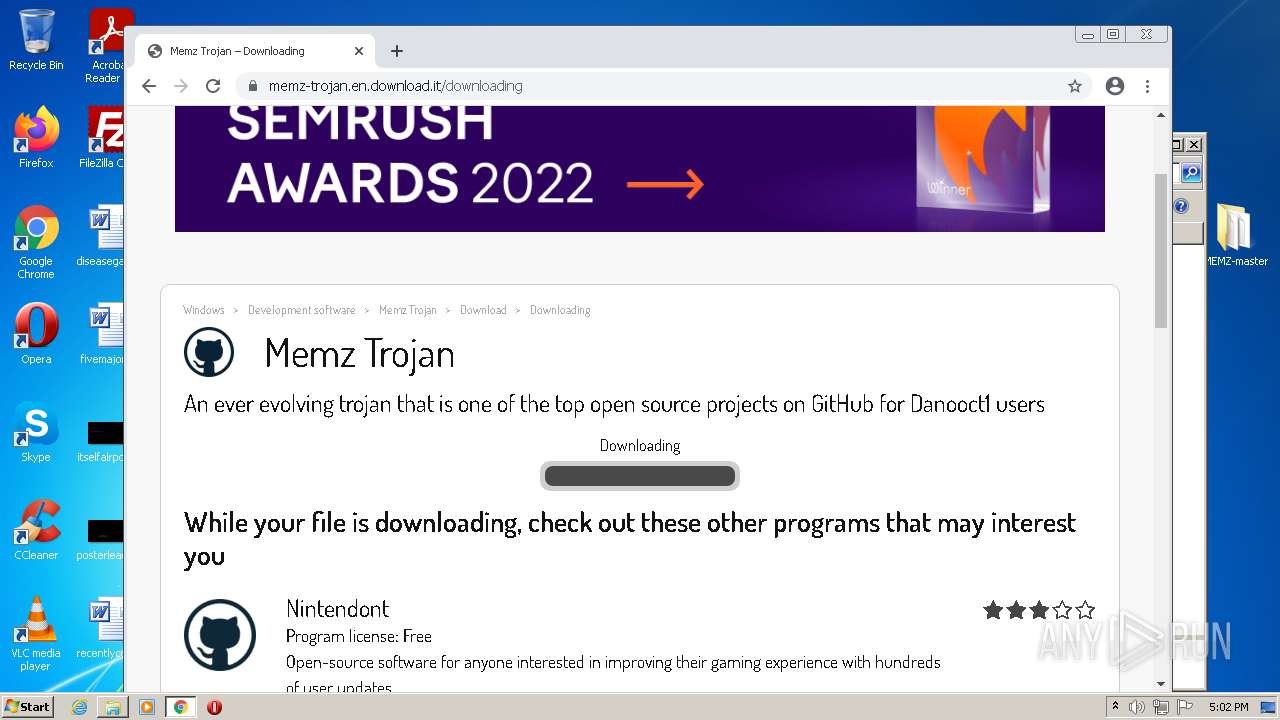
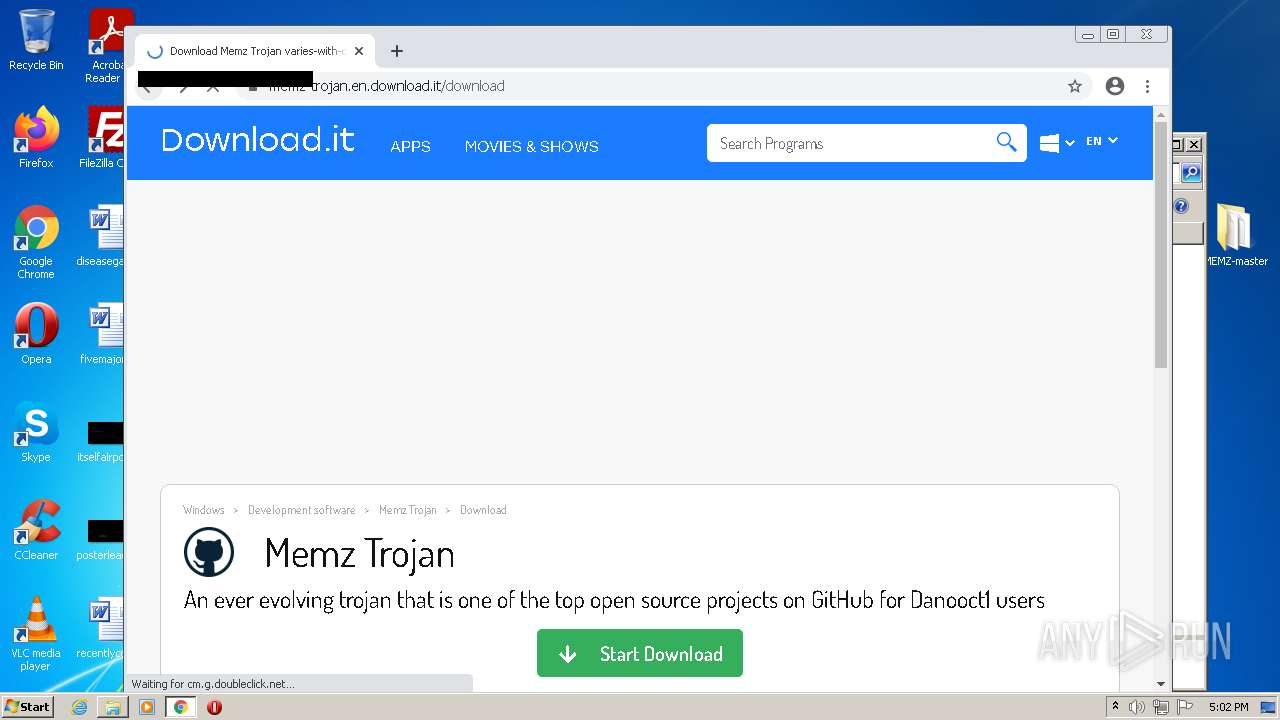
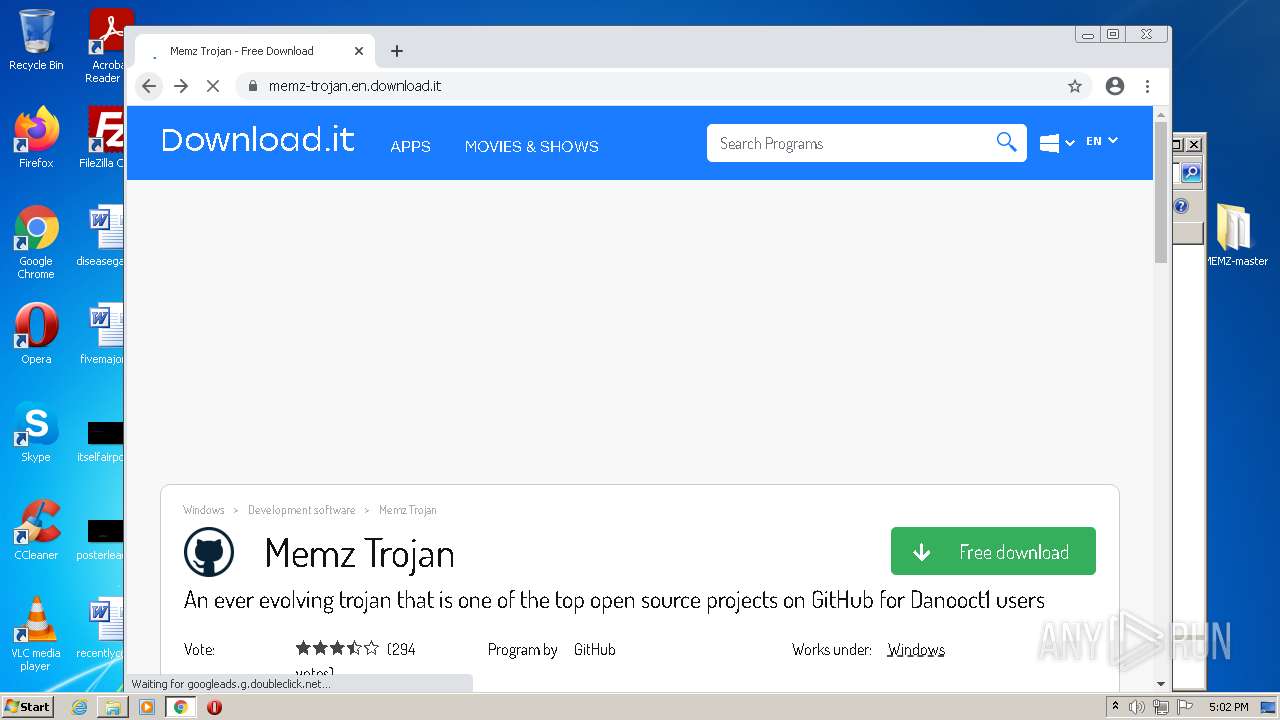
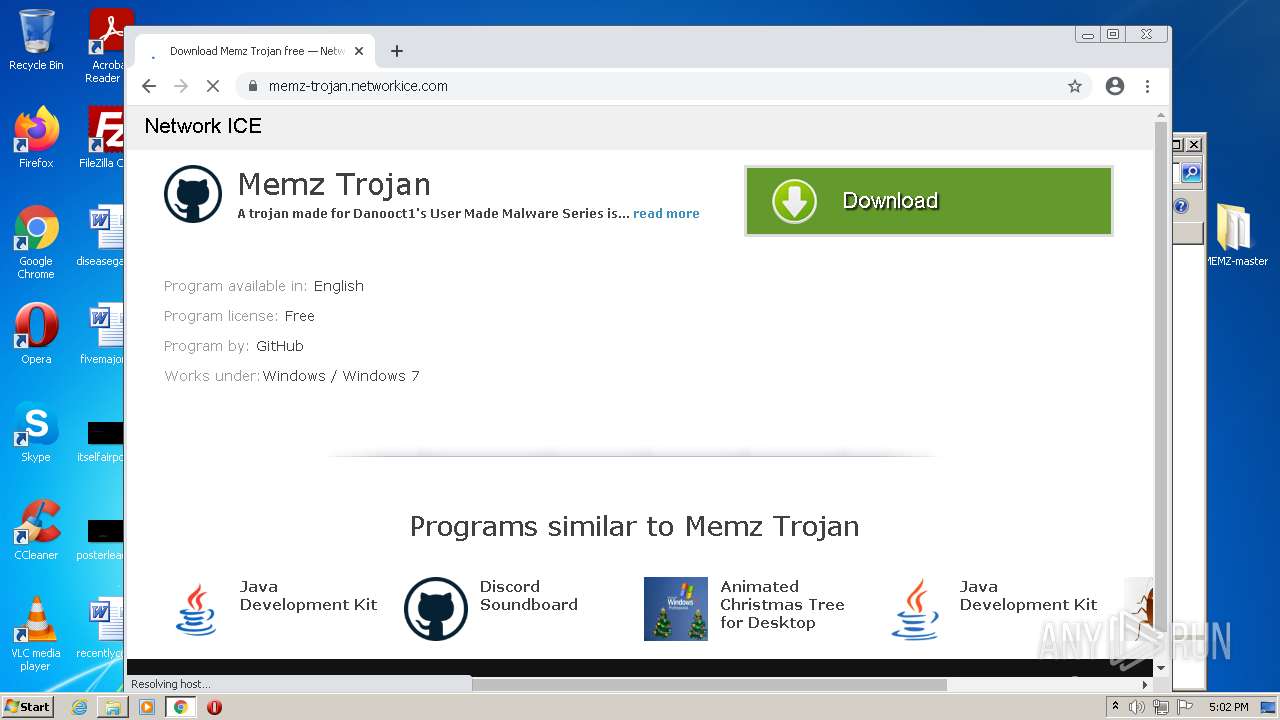
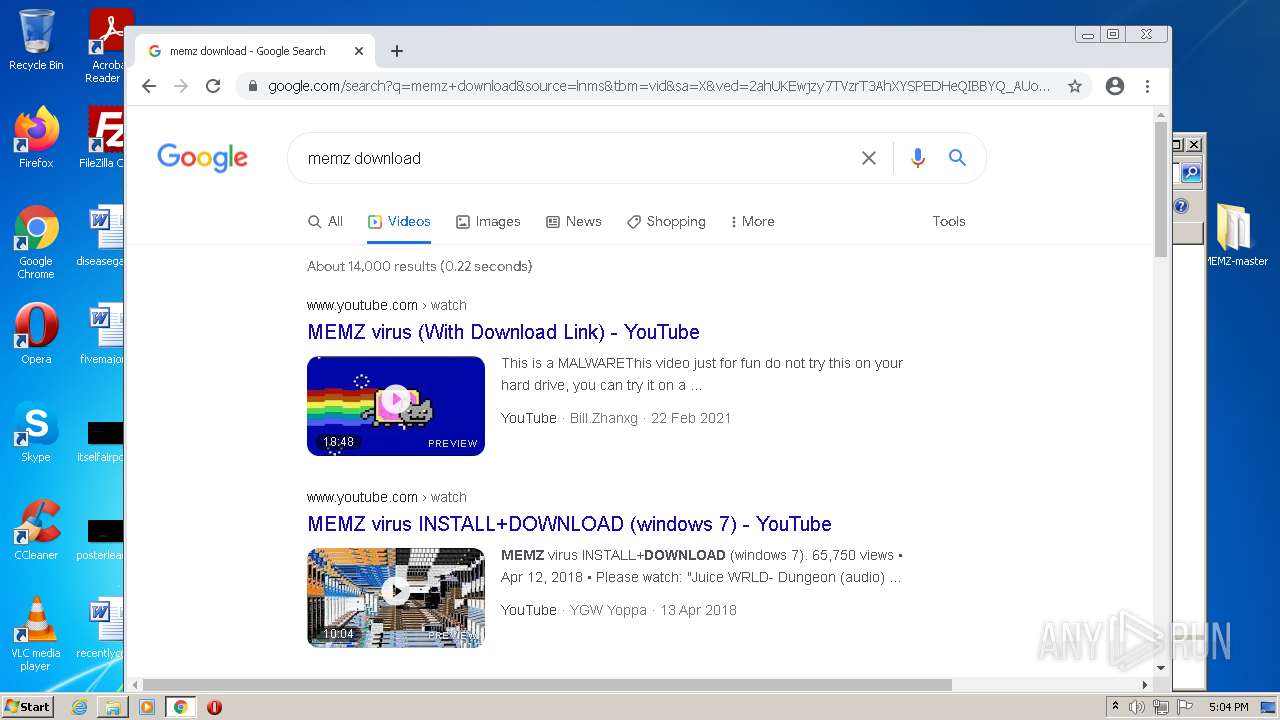
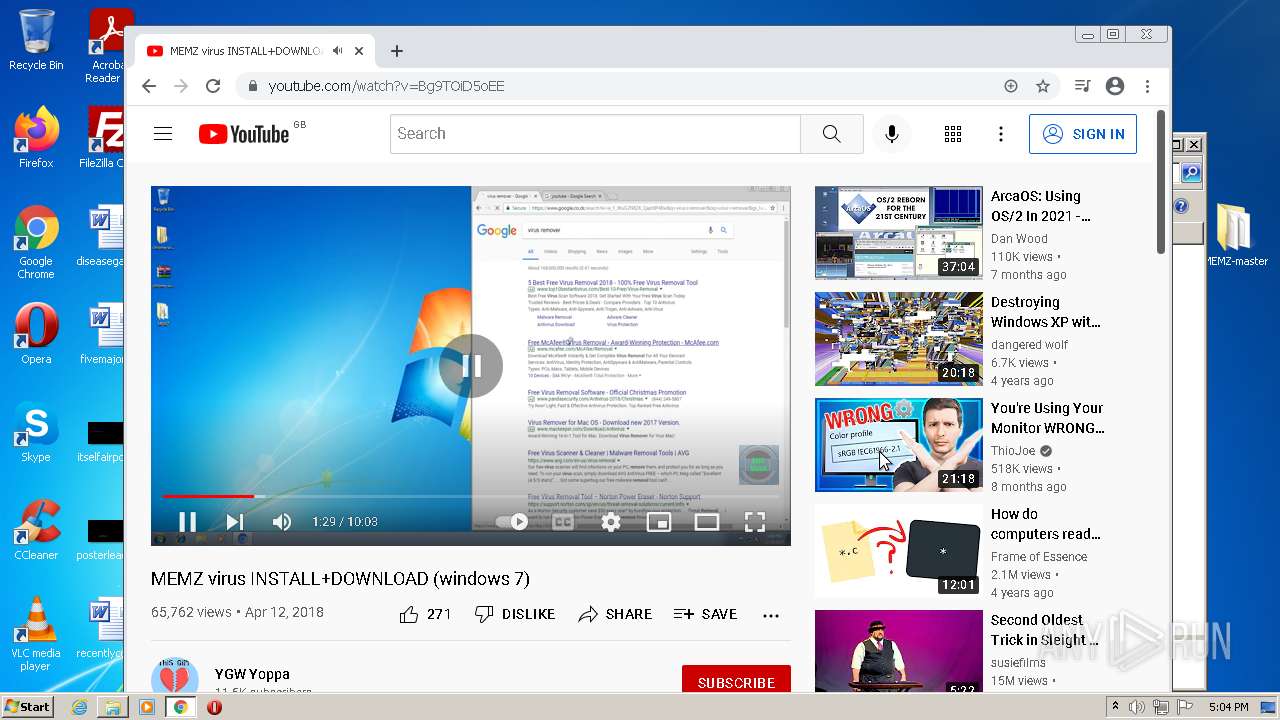
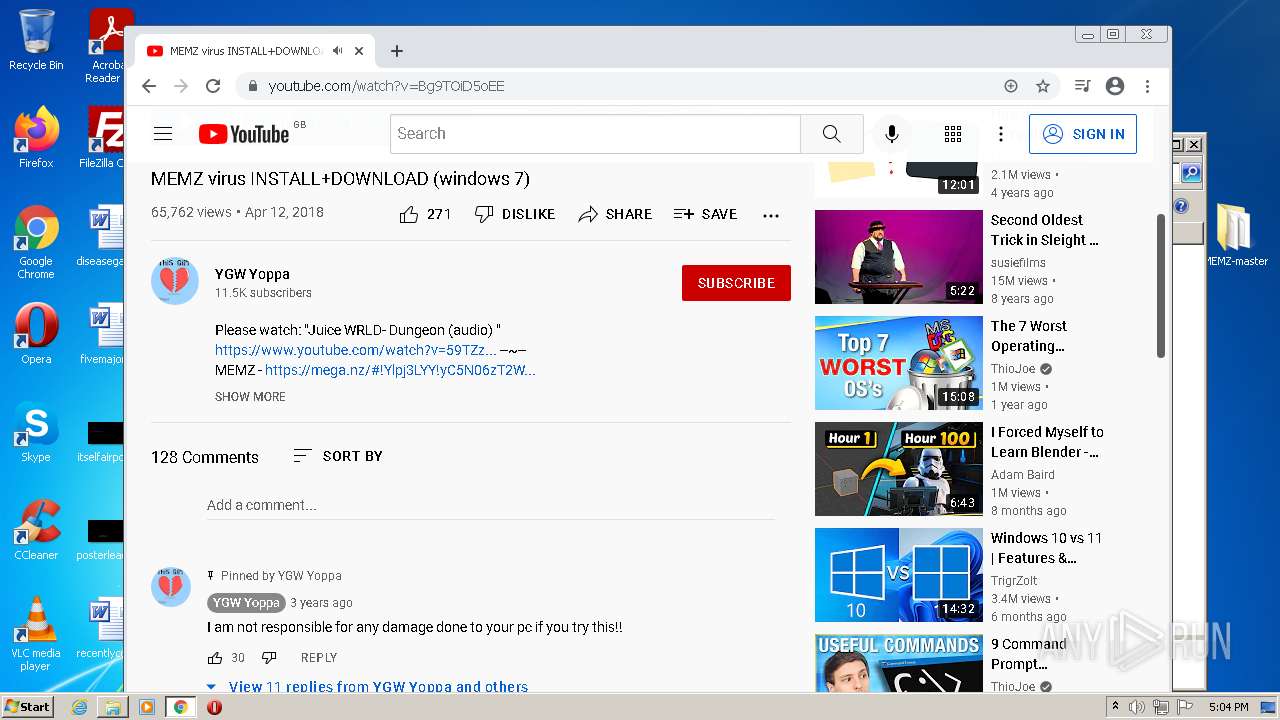
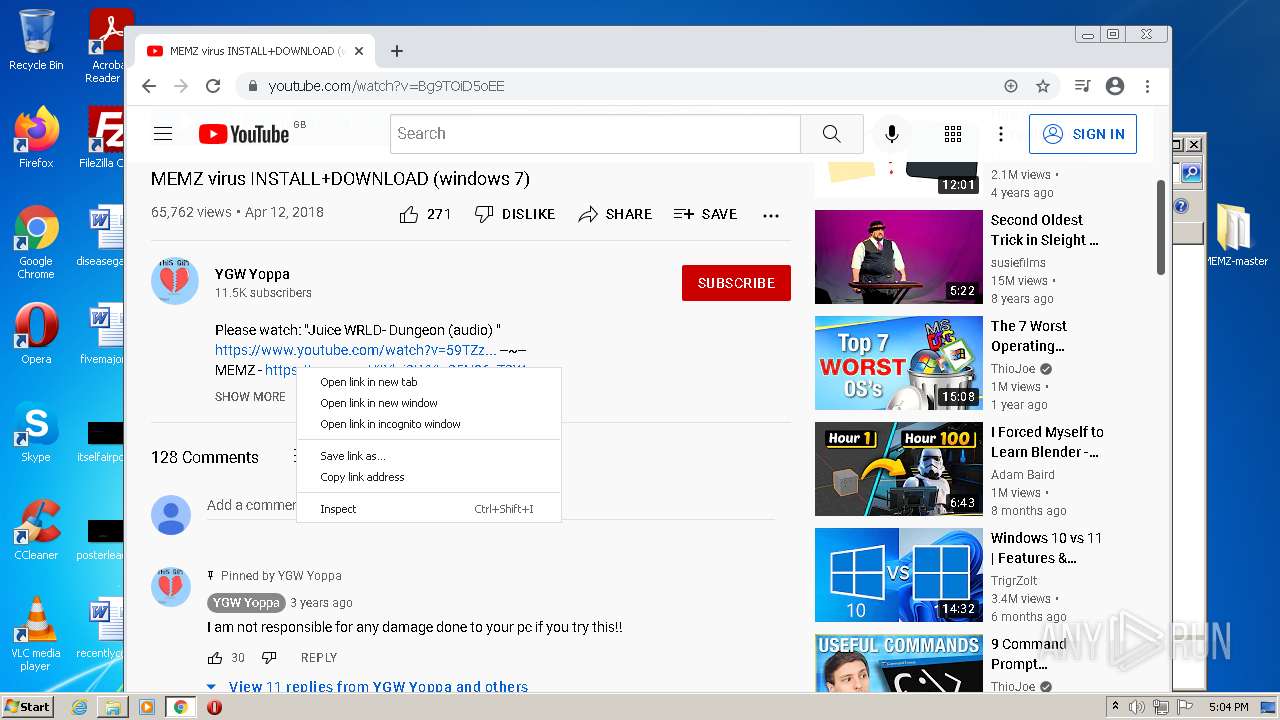
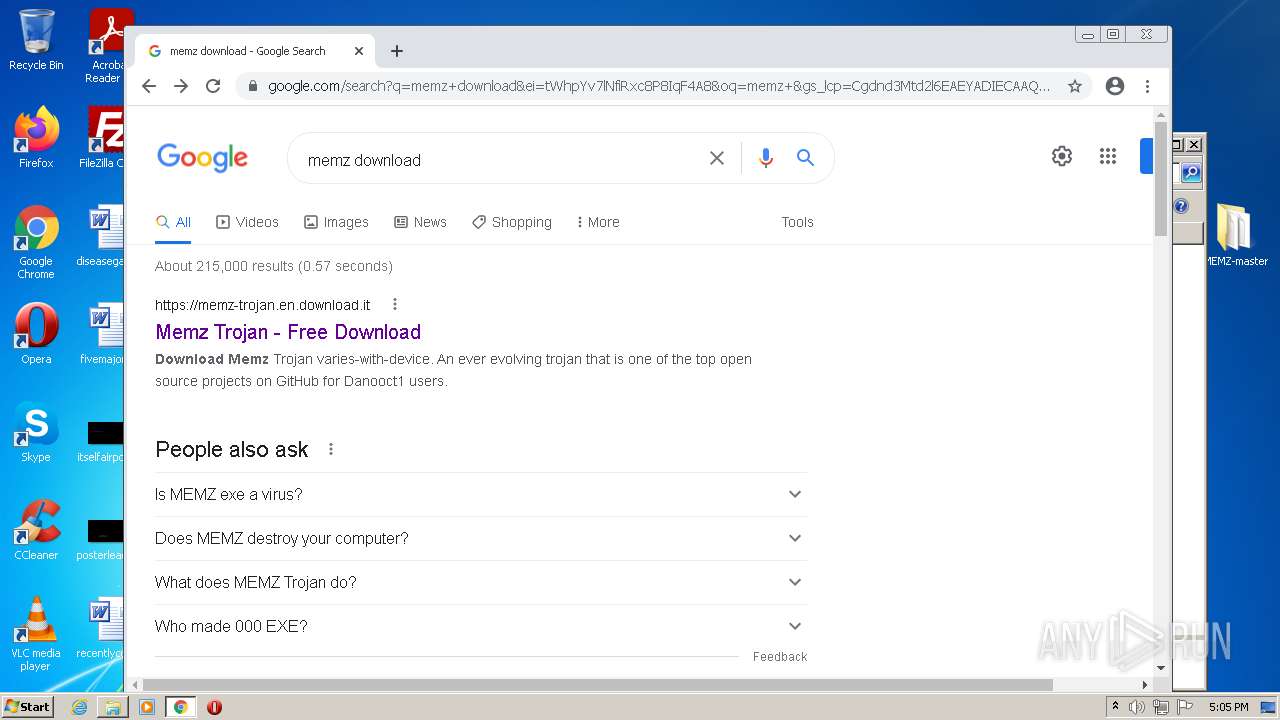
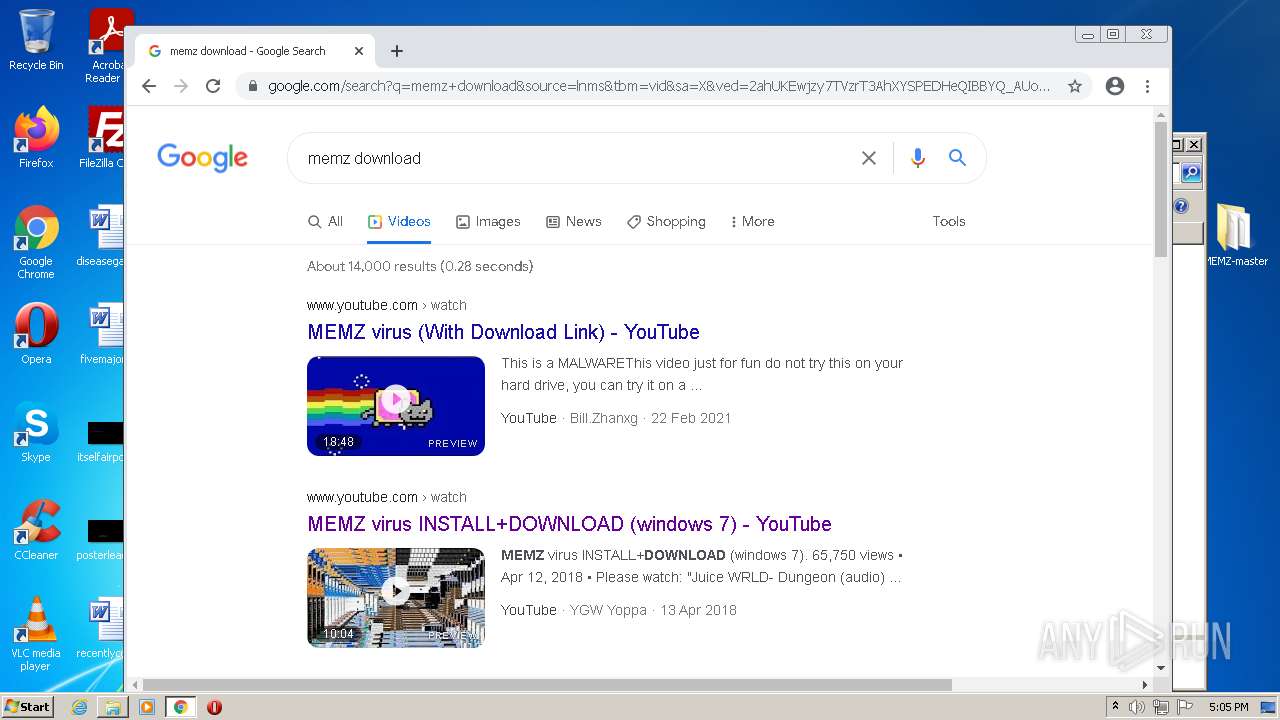
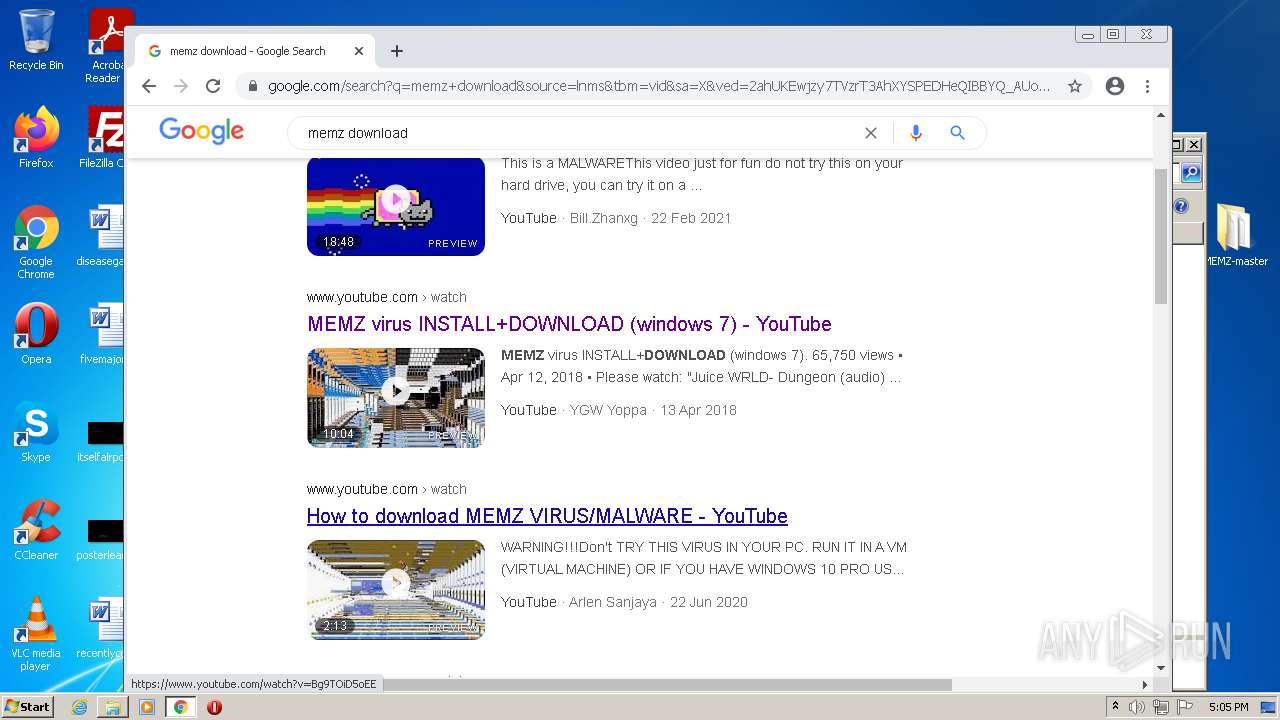
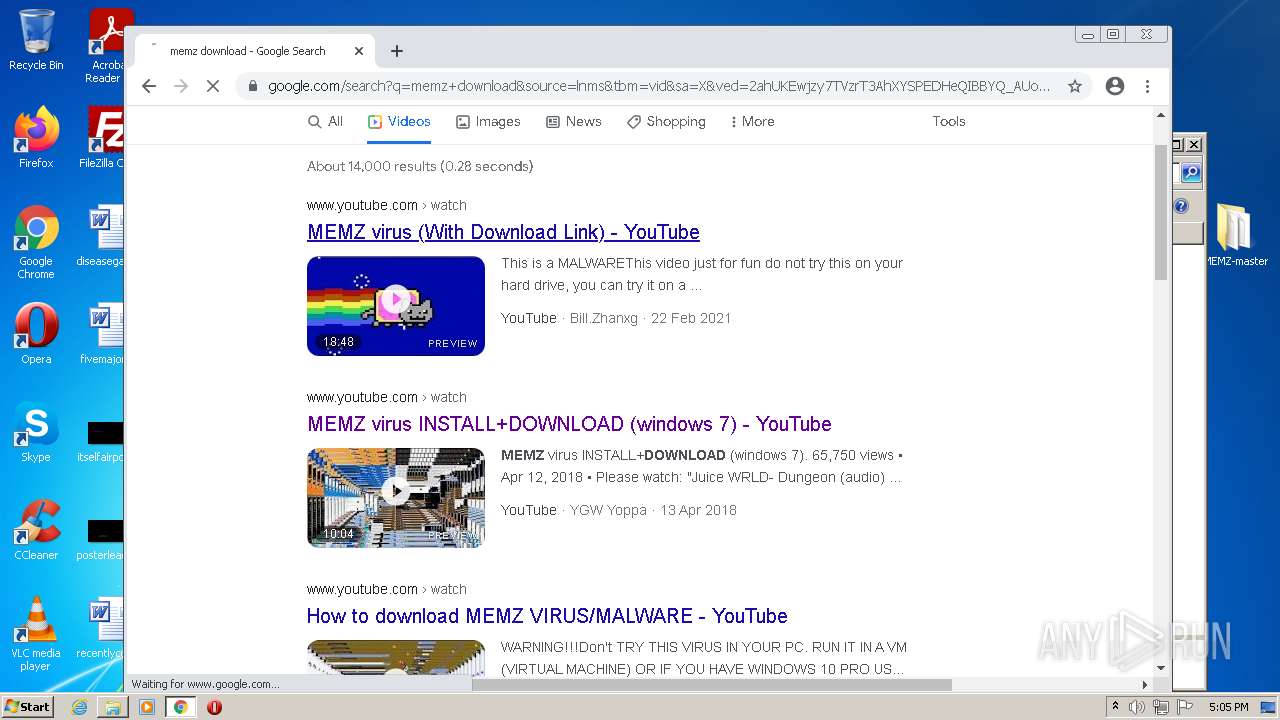
| Description: | Descargar la última versión de Memz Trojan. Gratis. |
| Title: | Descargar Memz Trojan varies-with-device gratuitamente |
Total processes
123
Monitored processes
76
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6eb3d988,0x6eb3d998,0x6eb3d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
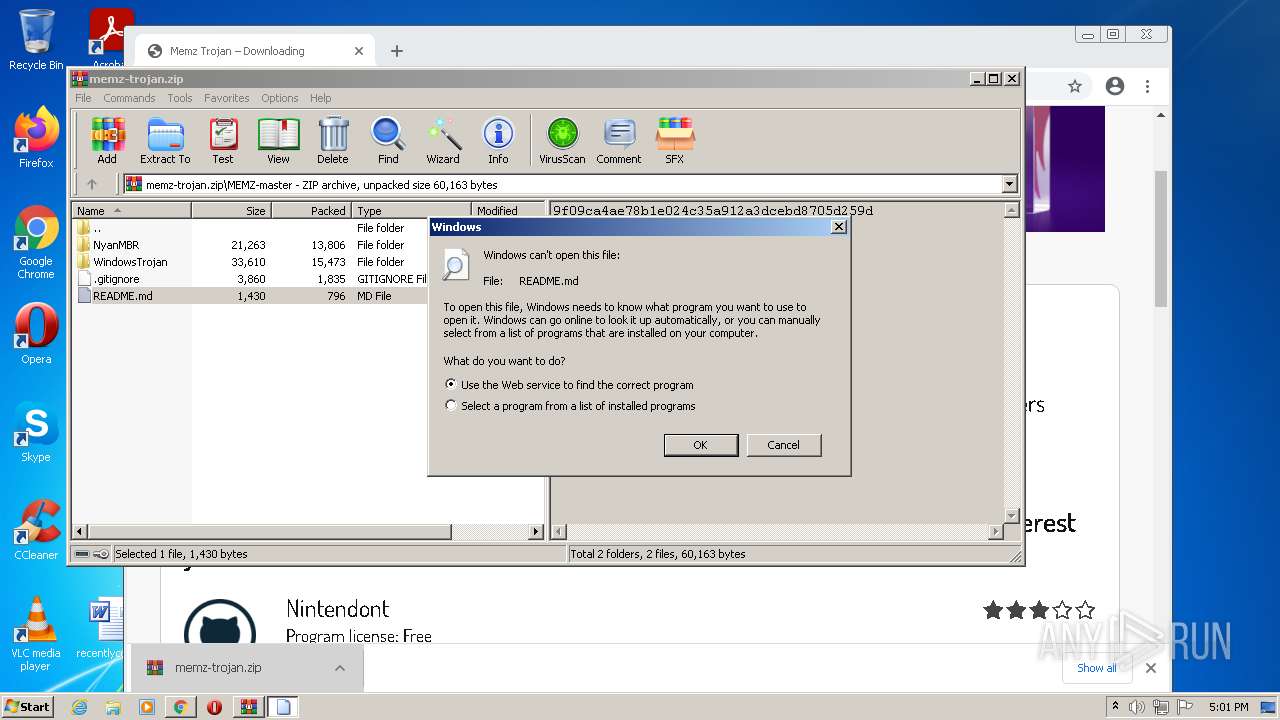
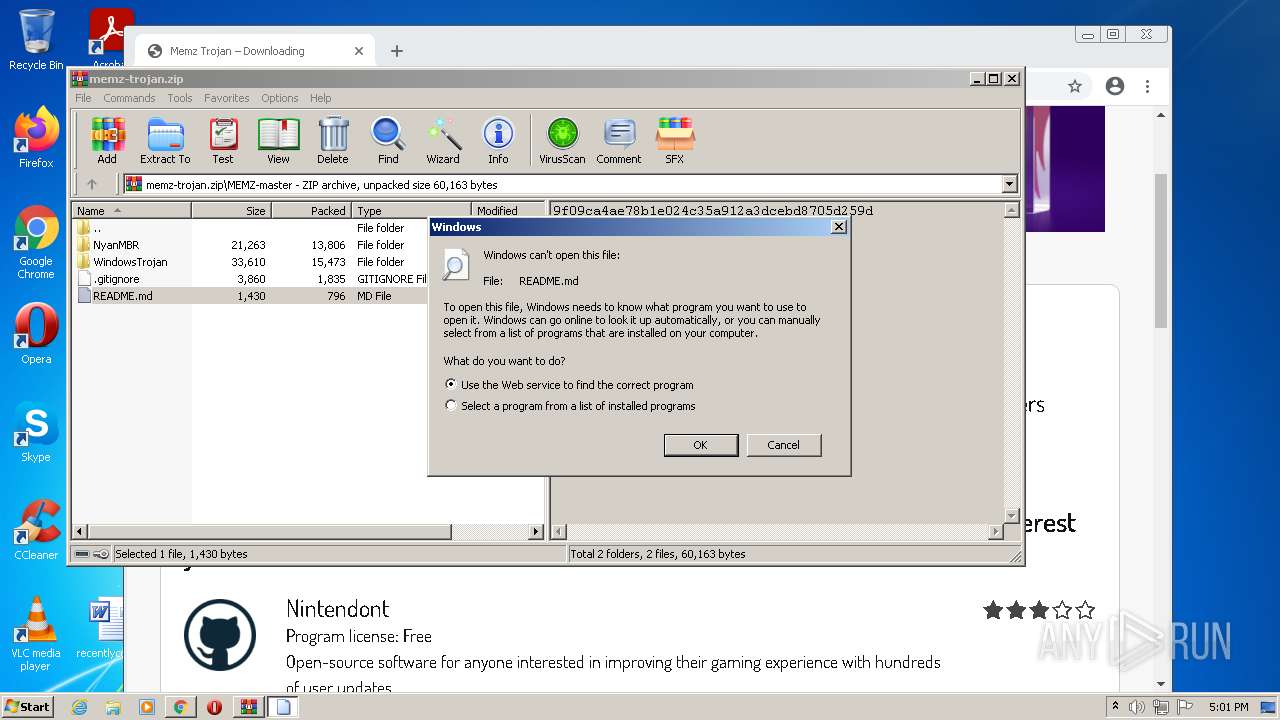
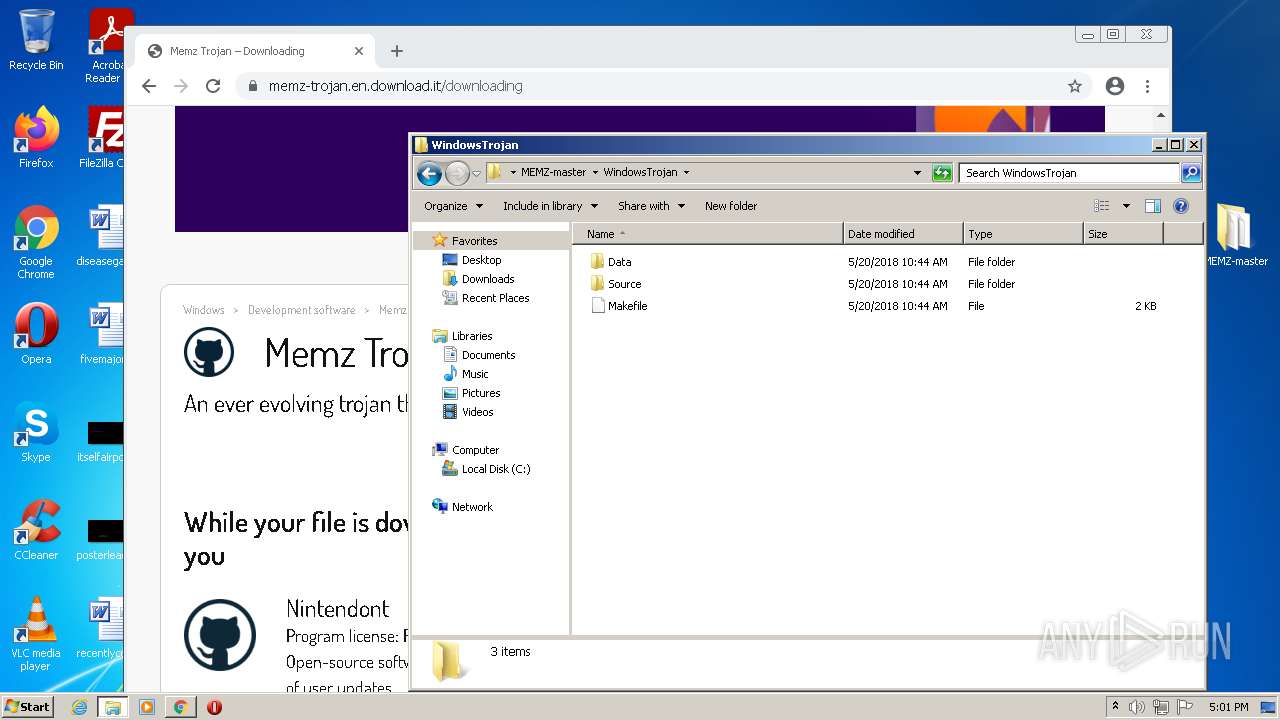
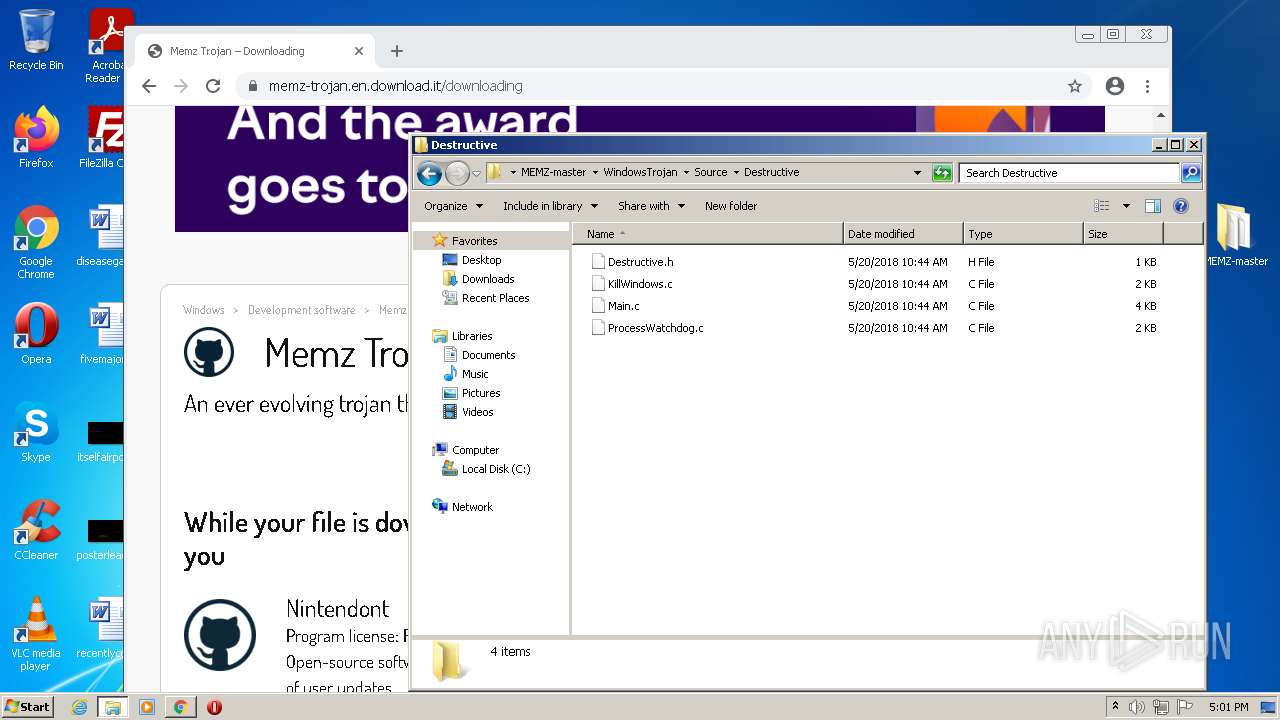
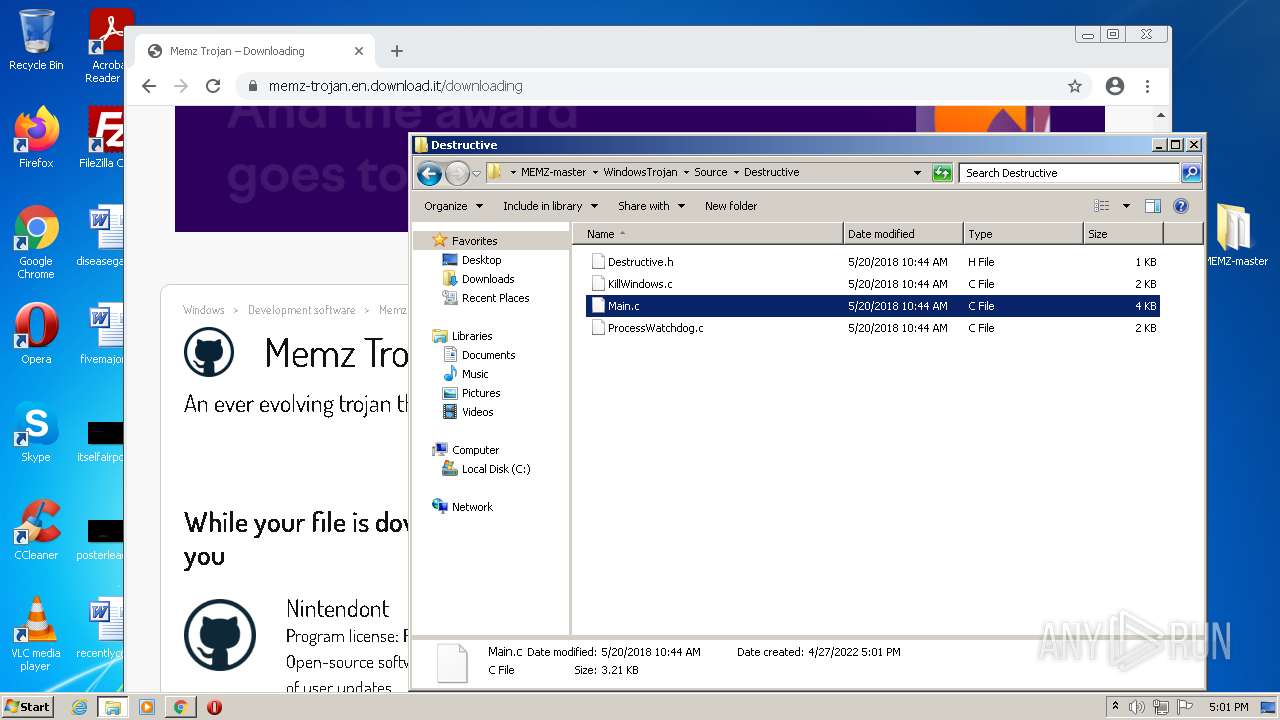
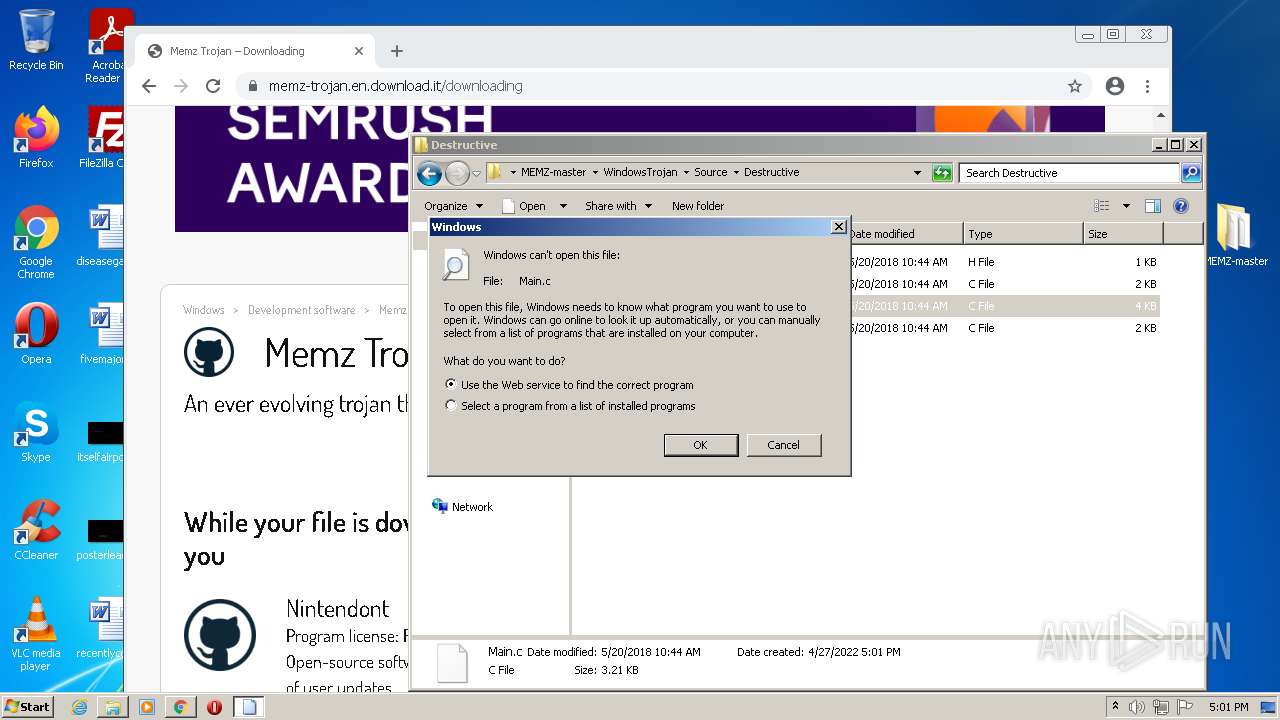
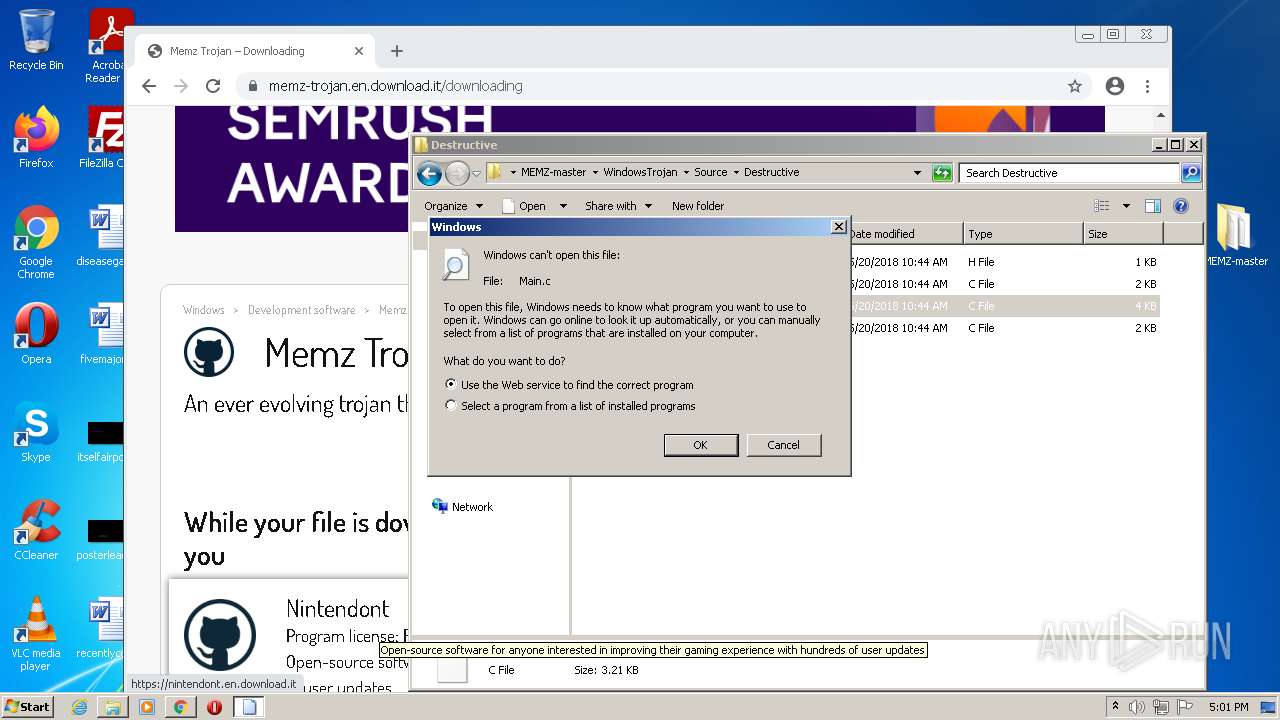
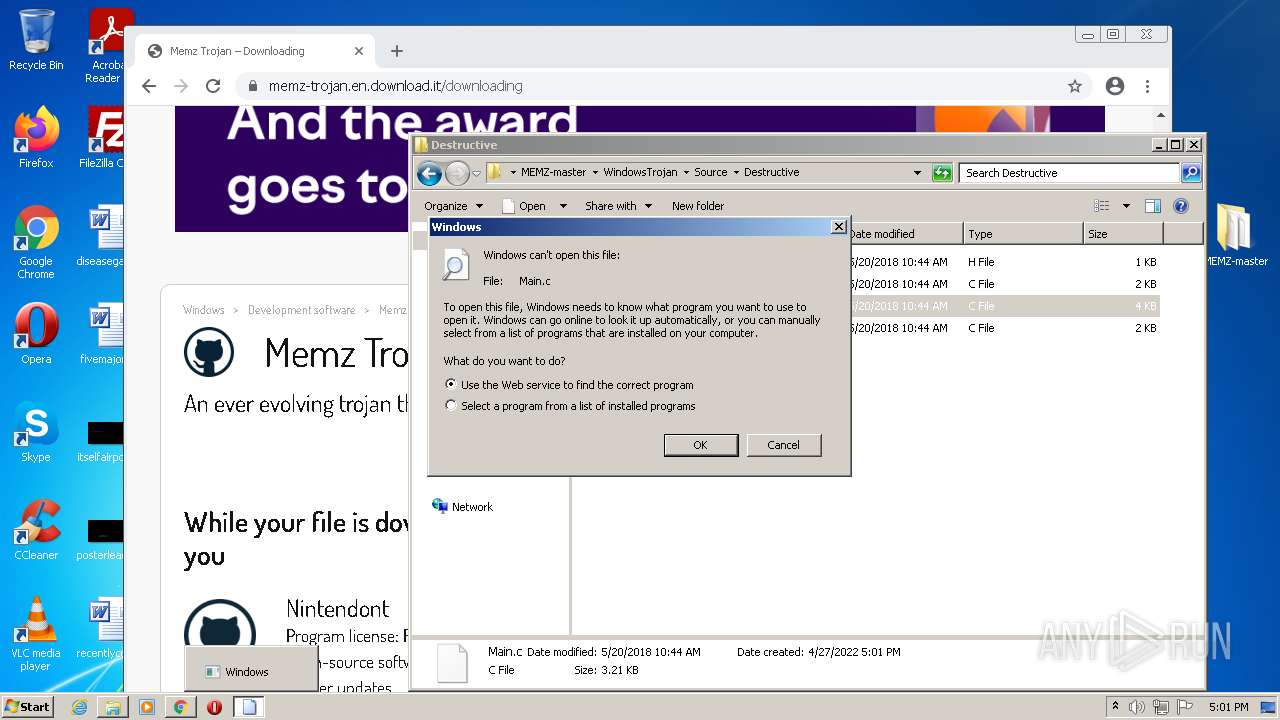
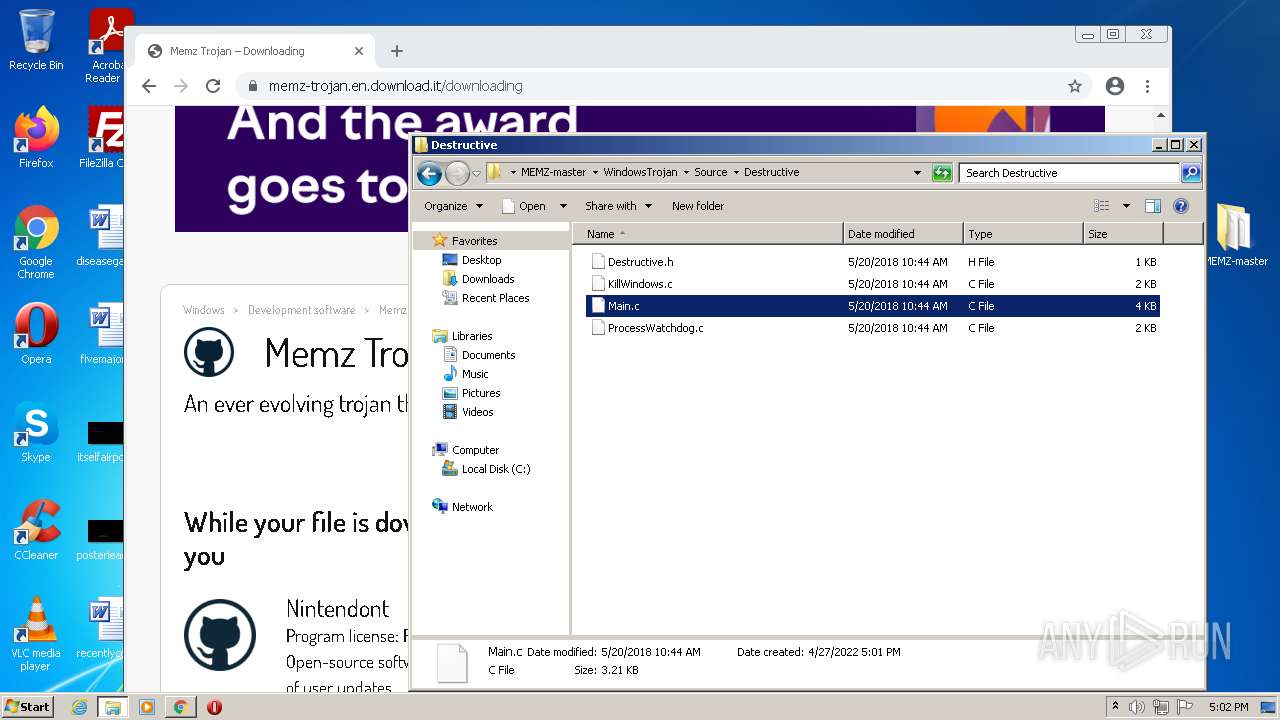
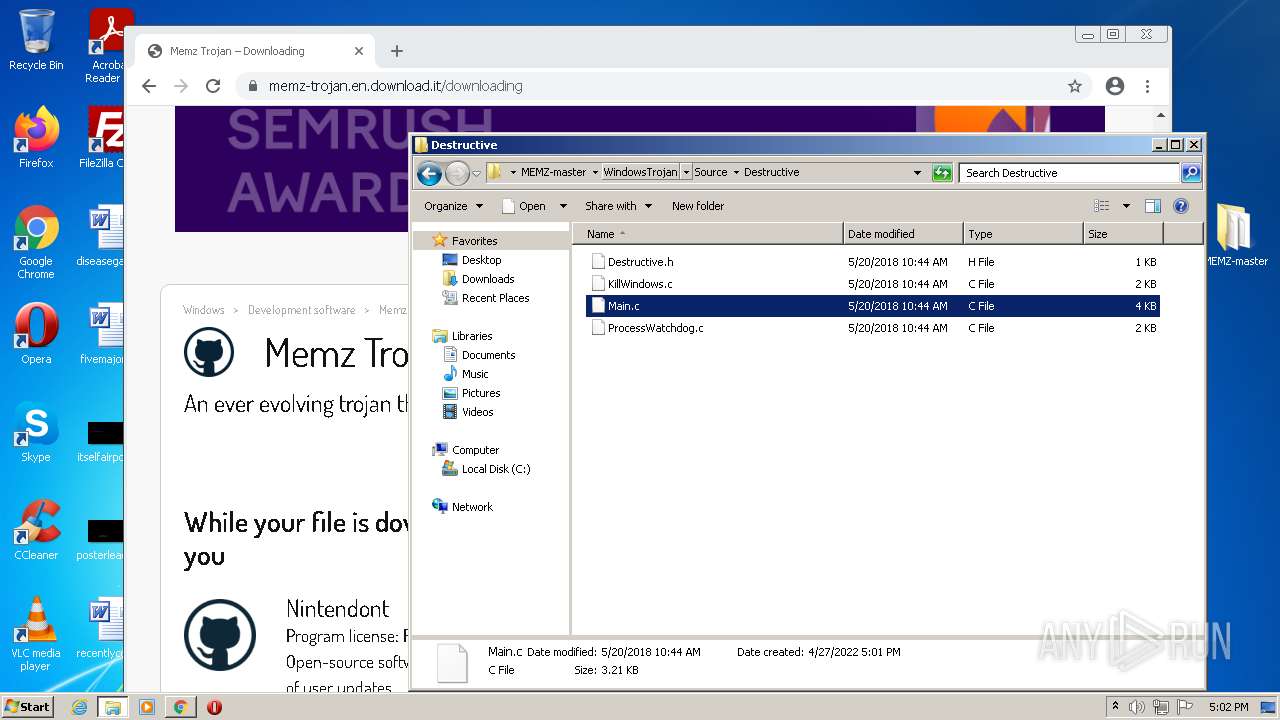
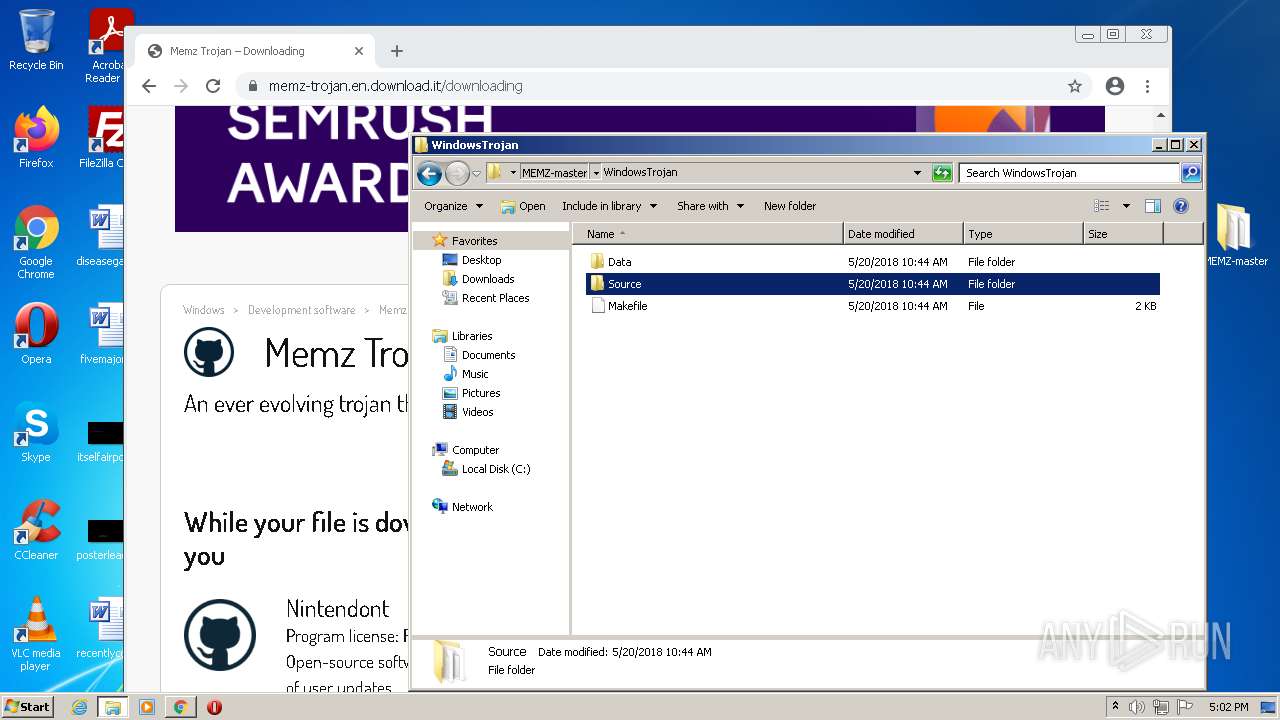
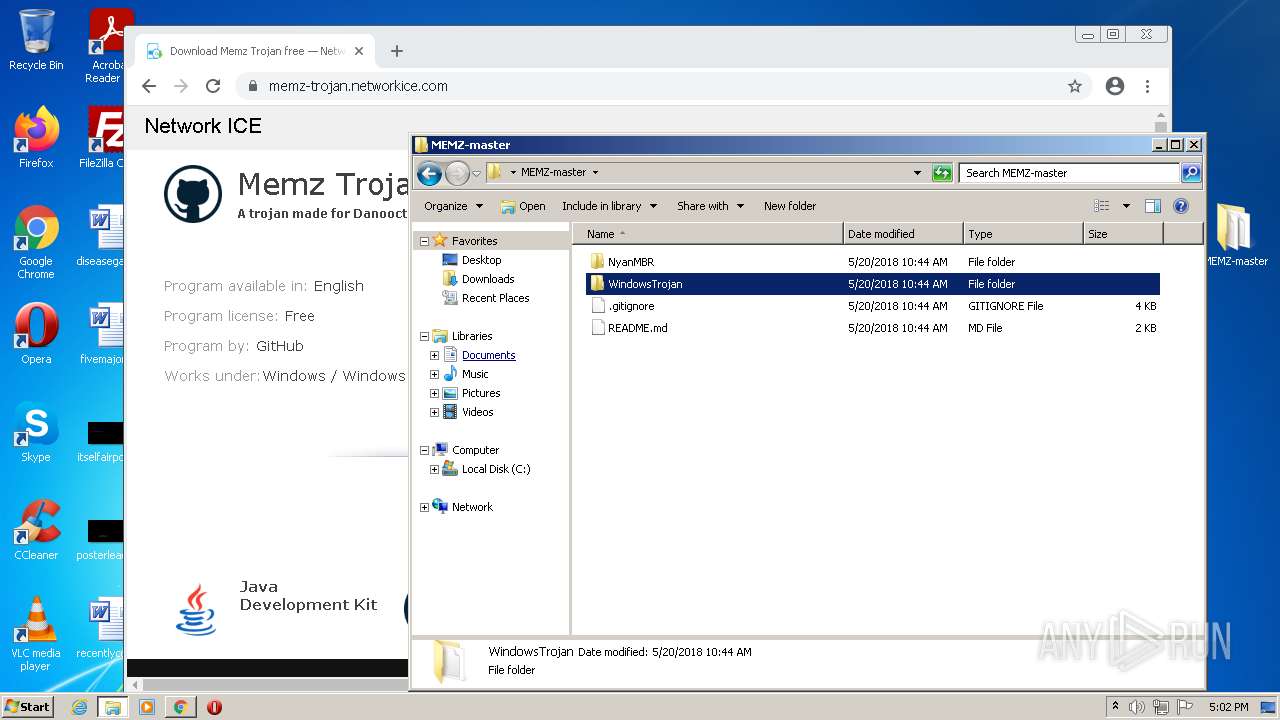
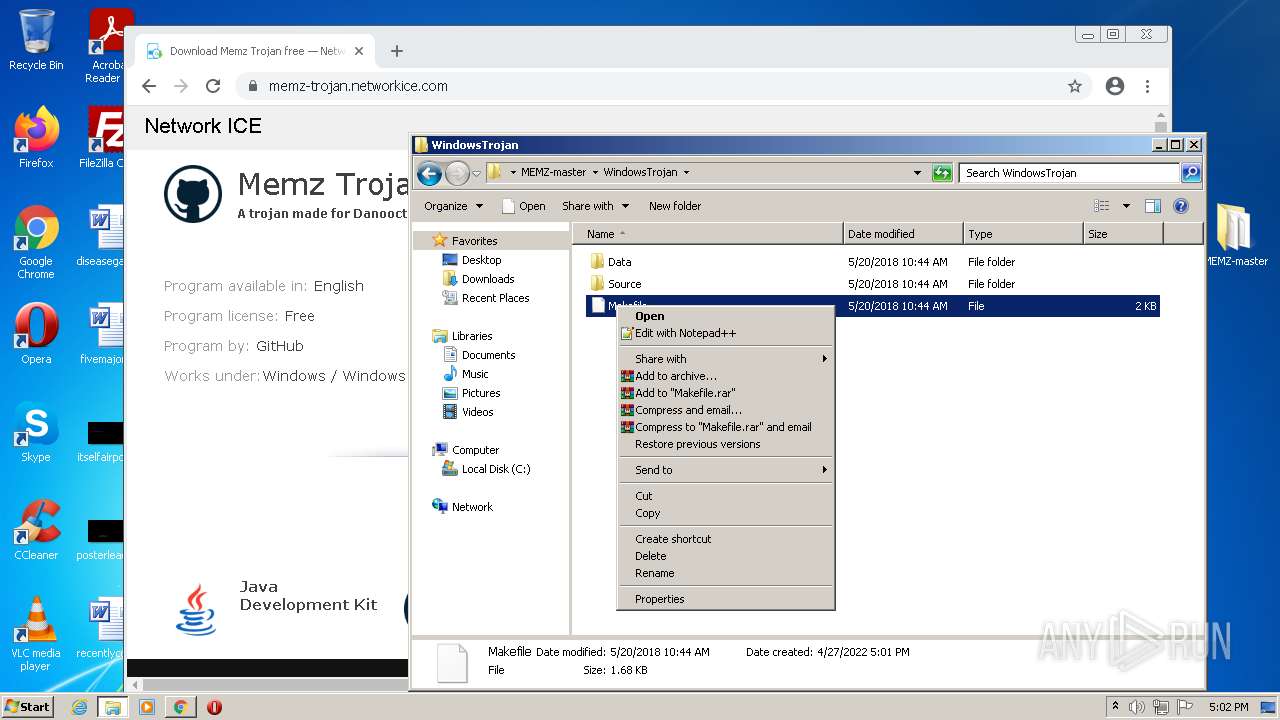
| 268 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\MEMZ-master\WindowsTrojan\Source\Destructive\Main.c | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 472 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,6421163476892644696,14182421520691936603,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=38 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1716 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 560 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1032,6421163476892644696,14182421520691936603,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1788 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,6421163476892644696,14182421520691936603,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1816 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 668 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,6421163476892644696,14182421520691936603,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2688 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 856 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --field-trial-handle=1032,6421163476892644696,14182421520691936603,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=3992 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 956 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL "C:\Users\admin\AppData\Local\Temp\download" | C:\Windows\system32\rundll32.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1100 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,6421163476892644696,14182421520691936603,131072 --enable-features=PasswordImport --lang=en-US --extension-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2212 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1032,6421163476892644696,14182421520691936603,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=3416 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
Total events
30 795
Read events
30 463
Write events
322
Delete events
10
Modification events
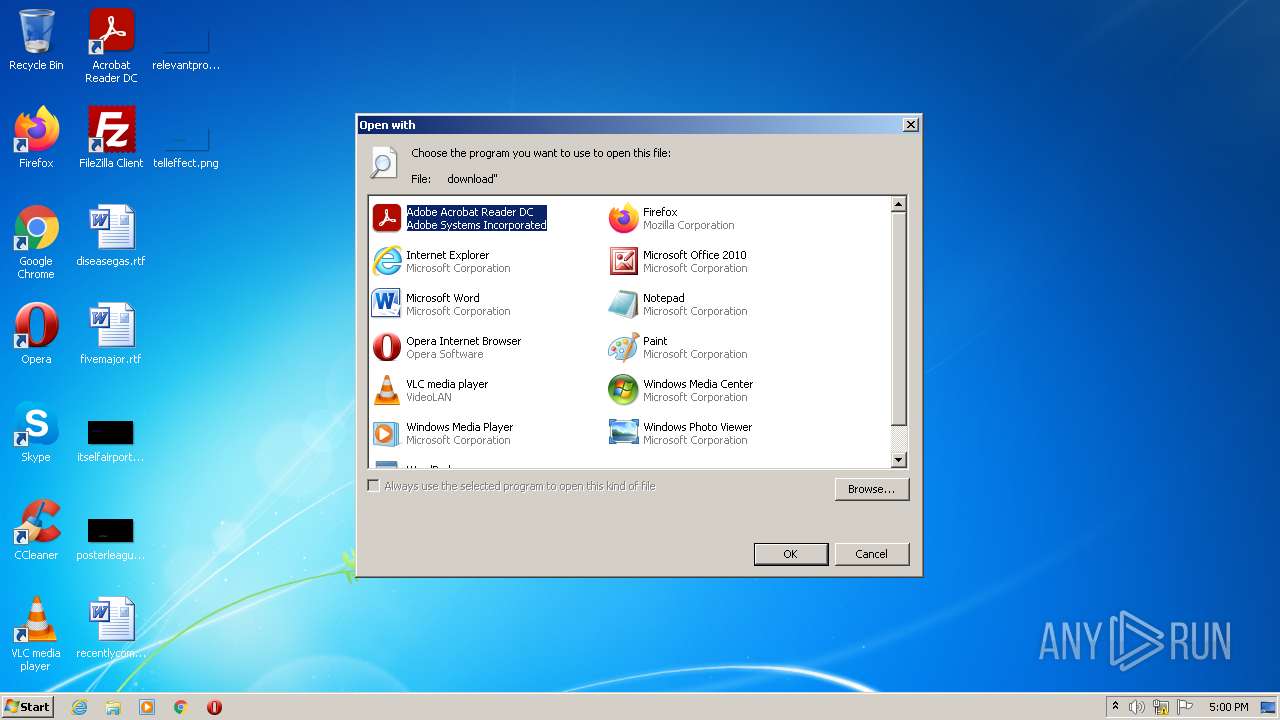
| (PID) Process: | (956) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\eHome\ehshell.exe |
Value: Windows Media Center | |||
| (PID) Process: | (956) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: Firefox | |||
| (PID) Process: | (956) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\mspaint.exe |
Value: Paint | |||
| (PID) Process: | (956) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Windows\system32\NOTEPAD.EXE |
Value: Notepad | |||
| (PID) Process: | (956) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\PROGRA~1\MICROS~1\Office14\OIS.EXE |
Value: Microsoft Office 2010 | |||
| (PID) Process: | (956) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Opera\Opera.exe |
Value: Opera Internet Browser | |||
| (PID) Process: | (956) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Windows Photo Viewer\PhotoViewer.dll |
Value: Windows Photo Viewer | |||
| (PID) Process: | (956) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\VideoLAN\VLC\vlc.exe |
Value: VLC media player | |||
| (PID) Process: | (956) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE |
Value: Microsoft Word | |||
| (PID) Process: | (956) rundll32.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
0
Suspicious files
473
Text files
348
Unknown types
26
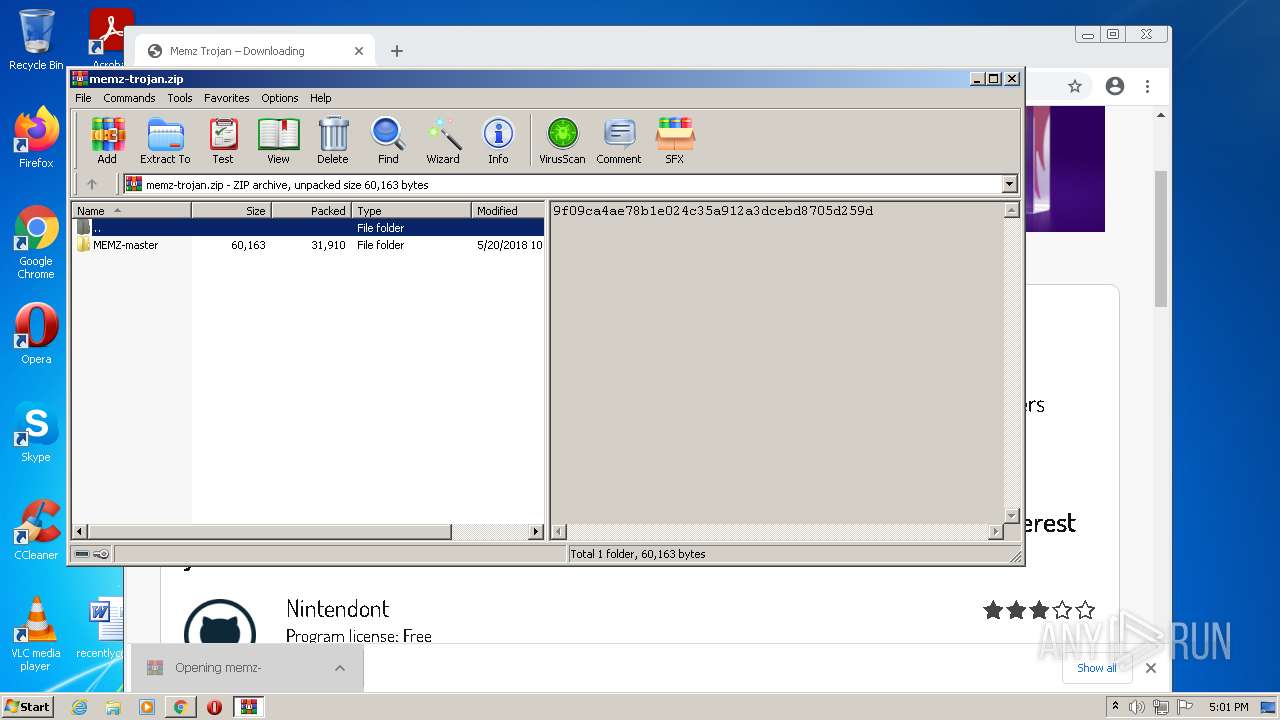
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-626968A2-790.pma | — | |
MD5:— | SHA256:— | |||
| 1936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\7fb13333-f329-4775-bd70-d8149d78cf55.tmp | text | |
MD5:— | SHA256:— | |||
| 1936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 1936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:7721CDA9F5B73CE8A135471EB53B4E0E | SHA256:DD730C576766A46FFC84E682123248ECE1FF1887EC0ACAB22A5CE93A450F4500 | |||
| 1936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\f711edbe-c5d9-4e2c-9169-ef42ca20c68e.tmp | binary | |
MD5:5058F1AF8388633F609CADB75A75DC9D | SHA256:— | |||
| 1936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFfb676.TMP | text | |
MD5:64AD8ED3E666540337BA541C549F72F7 | SHA256:BECBDB08B5B37D203A85F2E974407334053BB1D2270F0B3C9A4DB963896F2206 | |||
| 1936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old~RFfb676.TMP | text | |
MD5:936EB7280DA791E6DD28EF3A9B46D39C | SHA256:CBAF2AFD831B32F6D1C12337EE5D2F090D6AE1F4DCB40B08BEF49BF52AD9721F | |||
| 1936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RFfb695.TMP | text | |
MD5:81F483F77EE490F35306A4F94DB2286B | SHA256:82434CE3C9D13F509EBEEBE3A7A1A1DE9AB4557629D9FC855761E0CFA45E8BCE | |||
| 1936 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
133
DNS requests
76
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2440 | iexplore.exe | GET | 301 | 92.123.224.107:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=md | unknown | — | — | whitelisted |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | — | — | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 20.9 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 9.70 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 43.4 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 9.70 Kb | whitelisted |
— | — | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvODJiQUFYYVJaZ0k5di1hUFlXS1prX2xDZw/1.0.0.13_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | US | binary | 404 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 5.64 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | binary | 178 Kb | whitelisted |
— | — | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adktovjj3t3n7jwiiegl5h6y3v5q_1.3.36.121/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.121_win_bxugoraqoudfswxg22hsatfdbi.crx3 | US | skr | 358 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3396 | chrome.exe | 142.250.184.227:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3396 | chrome.exe | 142.250.185.141:443 | accounts.google.com | Google Inc. | US | whitelisted |
3396 | chrome.exe | 142.250.185.78:443 | clients2.google.com | Google Inc. | US | whitelisted |
3396 | chrome.exe | 142.250.181.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3396 | chrome.exe | 142.250.185.67:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3396 | chrome.exe | 142.250.186.110:443 | apis.google.com | Google Inc. | US | whitelisted |
— | — | 142.250.181.234:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3396 | chrome.exe | 142.250.186.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3396 | chrome.exe | 172.217.16.142:443 | encrypted-tbn0.gstatic.com | Google Inc. | US | whitelisted |
3396 | chrome.exe | 142.250.74.195:443 | update.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
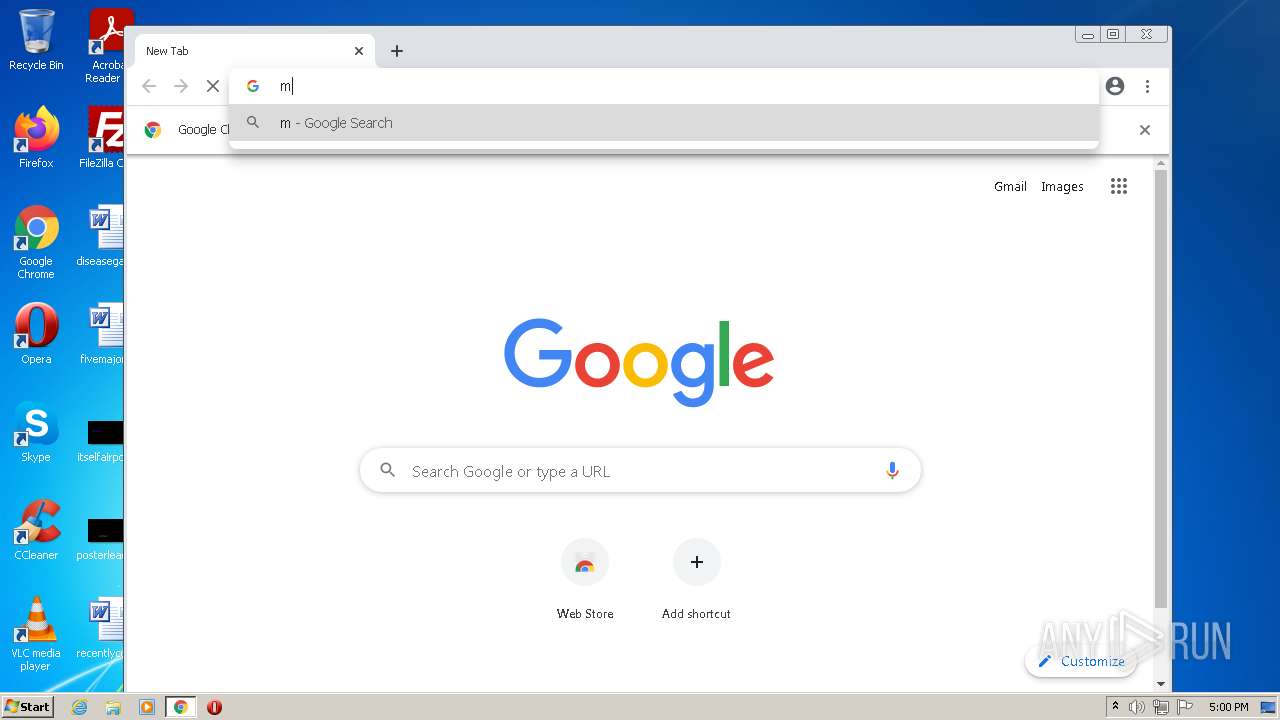
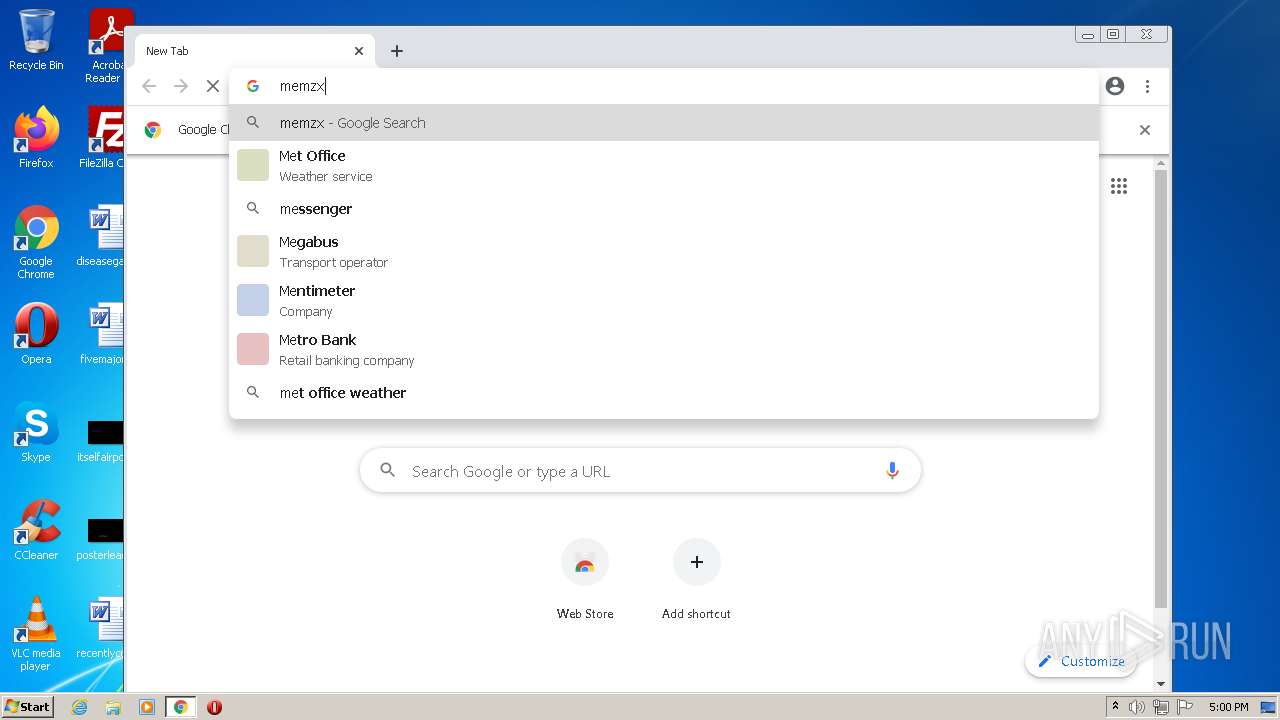
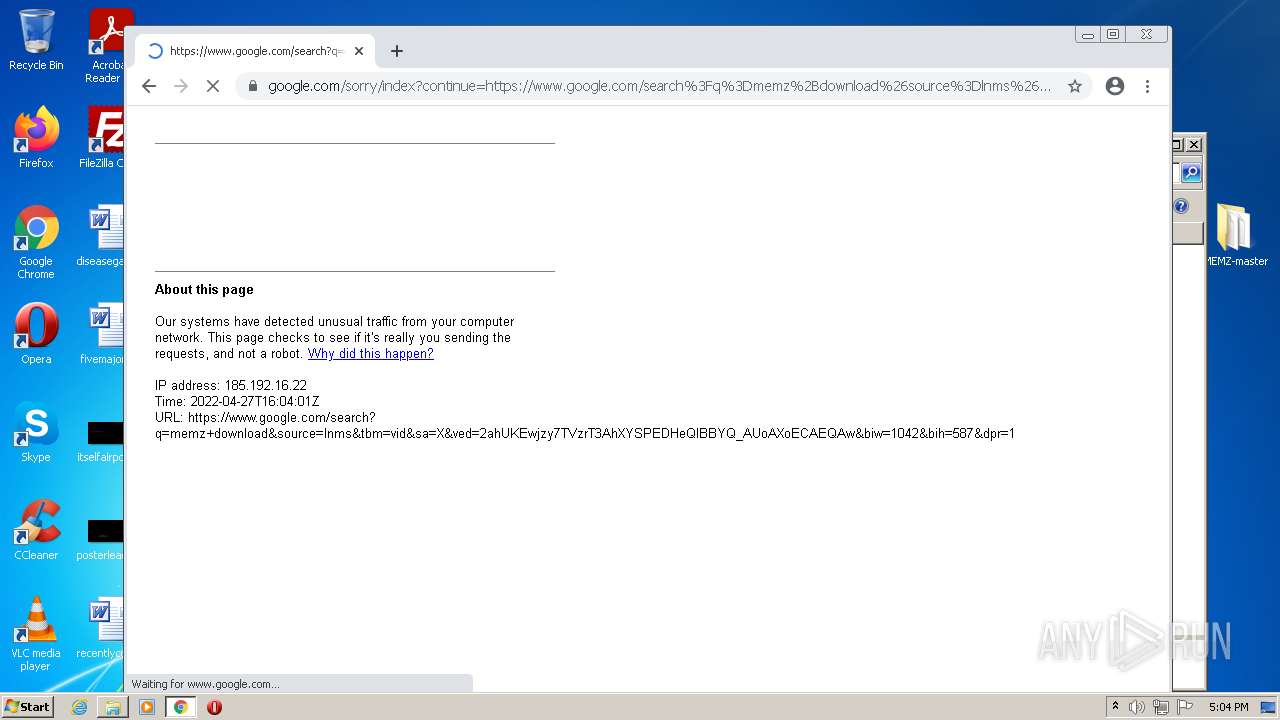
www.google.com |
| malicious |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |