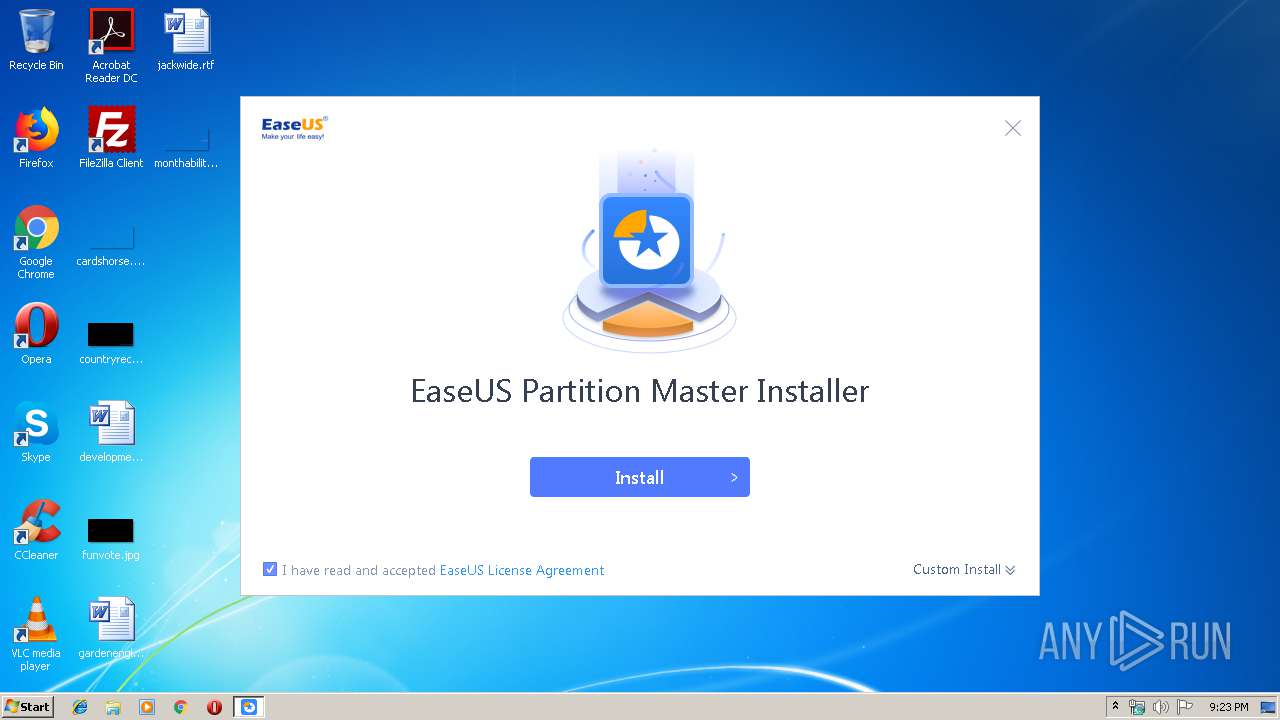
| download: | epm_free_installer.exe |
| Full analysis: | https://app.any.run/tasks/c63fb7da-c379-4af2-9552-20feb861b46f |
| Verdict: | Suspicious activity |
| Analysis date: | September 10, 2019, 20:23:19 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 4215CD77B22A4EAD66685035C9185677 |
| SHA1: | 79092E95678948BAC936C790D8EB8222FAC23763 |
| SHA256: | DD4B4D5662308B97406D933A6E1414E2AA05BB16155DEB3ADEDC54431EC7F2B6 |
| SSDEEP: | 24576:H6y5fqTd8JTcO1/sztni/aWO/CHhXYRFha/rCAU:Z5fqT2JTlsxHN/CHhog/O |
MALICIOUS
Application was dropped or rewritten from another process
- EDownloader.exe (PID: 3472)
SUSPICIOUS
Executable content was dropped or overwritten
- epm_free_installer.exe (PID: 576)
Reads internet explorer settings
- EDownloader.exe (PID: 3472)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:01:30 04:57:48+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 26624 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x338f |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jan-2018 03:57:48 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jan-2018 03:57:48 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006627 | 0x00006800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.45224 |
.rdata | 0x00008000 | 0x0000149A | 0x00001600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.00708 |
.data | 0x0000A000 | 0x0002AFF8 | 0x00000600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.03532 |
.ndata | 0x00035000 | 0x00010000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00045000 | 0x0005ADE0 | 0x0005AE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.21449 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28733 | 841 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 2.52031 | 67624 | UNKNOWN | English - United States | RT_ICON |
3 | 3.06845 | 16936 | UNKNOWN | English - United States | RT_ICON |
4 | 3.36894 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 3.74292 | 4264 | UNKNOWN | English - United States | RT_ICON |
6 | 4.42732 | 1128 | UNKNOWN | English - United States | RT_ICON |
103 | 2.76511 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.66174 | 256 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.88094 | 284 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.48825 | 96 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
37
Monitored processes
3
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 576 | "C:\Users\admin\AppData\Local\Temp\epm_free_installer.exe" | C:\Users\admin\AppData\Local\Temp\epm_free_installer.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3000 | "C:\Users\admin\AppData\Local\Temp\epm_free_installer.exe" | C:\Users\admin\AppData\Local\Temp\epm_free_installer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3472 | "C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\5free\EDownloader.exe" EXEDIR=C:\Users\admin\AppData\Local\Temp ||| EXENAME=epm_free_installer.exe ||| DOWNLOAD_VERSION=free ||| PRODUCT_VERSION=1.0.0 ||| INSTALL_TYPE=0 | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\5free\EDownloader.exe | epm_free_installer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
393
Read events
389
Write events
4
Delete events
0
Modification events
| (PID) Process: | (3472) EDownloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3472) EDownloader.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
1
Suspicious files
1
Text files
34
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3472 | EDownloader.exe | C:\Users\admin\AppData\Local\Temp\epm_free_easeus.exe.temp | — | |
MD5:— | SHA256:— | |||
| 576 | epm_free_installer.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\5free\skin.zip | compressed | |
MD5:— | SHA256:— | |||
| 576 | epm_free_installer.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\5free\ChineseTrad.ini | text | |
MD5:— | SHA256:— | |||
| 576 | epm_free_installer.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\5free\French.ini | text | |
MD5:— | SHA256:— | |||
| 576 | epm_free_installer.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\5free\Danish.ini | text | |
MD5:— | SHA256:— | |||
| 576 | epm_free_installer.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\5free\Dutch.ini | text | |
MD5:— | SHA256:— | |||
| 576 | epm_free_installer.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\5free\Spanish.ini | text | |
MD5:— | SHA256:— | |||
| 576 | epm_free_installer.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\5free\Polish.ini | text | |
MD5:— | SHA256:— | |||
| 576 | epm_free_installer.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\5free\Portuguese.ini | text | |
MD5:— | SHA256:— | |||
| 3472 | EDownloader.exe | C:\Users\admin\AppData\Local\Temp\downloader_easeus\1.0.0\5free\EasyLog.log | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
8
DNS requests
4
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3472 | EDownloader.exe | GET | — | 163.171.128.147:80 | http://download3.easeus.com/free/epm.exe | US | — | — | suspicious |
3472 | EDownloader.exe | GET | — | 163.171.128.147:80 | http://download3.easeus.com/free/epm.exe | US | — | — | suspicious |
3472 | EDownloader.exe | POST | 200 | 216.92.47.198:80 | http://track.easeus.com/product/index.php/?a=statistics&p_type=m_epm_download_record_table | US | — | — | suspicious |
3472 | EDownloader.exe | POST | 200 | 216.92.47.198:80 | http://track.easeus.com/product/index.php/?a=statistics&p_type=m_epm_download_record_table | US | — | — | suspicious |
3472 | EDownloader.exe | POST | 200 | 216.92.47.198:80 | http://track.easeus.com/product/index.php/?a=statistics&p_type=m_epm_download_record_table | US | — | — | suspicious |
3472 | EDownloader.exe | GET | — | 163.171.128.147:80 | http://download3.easeus.com/free/epm.exe | US | — | — | suspicious |
3472 | EDownloader.exe | GET | — | 163.171.128.147:80 | http://download3.easeus.com/free/epm.exe | US | — | — | suspicious |
3472 | EDownloader.exe | POST | 200 | 216.92.245.230:80 | http://yiwo.easeus.com/api/index.php/Home/index/productInstall | US | text | 221 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3472 | EDownloader.exe | 216.92.47.198:80 | track.easeus.com | pair Networks | US | suspicious |
3472 | EDownloader.exe | 216.92.245.230:80 | yiwo.easeus.com | pair Networks | US | unknown |
3472 | EDownloader.exe | 163.171.128.147:80 | download3.easeus.com | — | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
track.easeus.com |
| suspicious |
yiwo.easeus.com |
| unknown |
download3.easeus.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3472 | EDownloader.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
3472 | EDownloader.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
3472 | EDownloader.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
3472 | EDownloader.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
3472 | EDownloader.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |