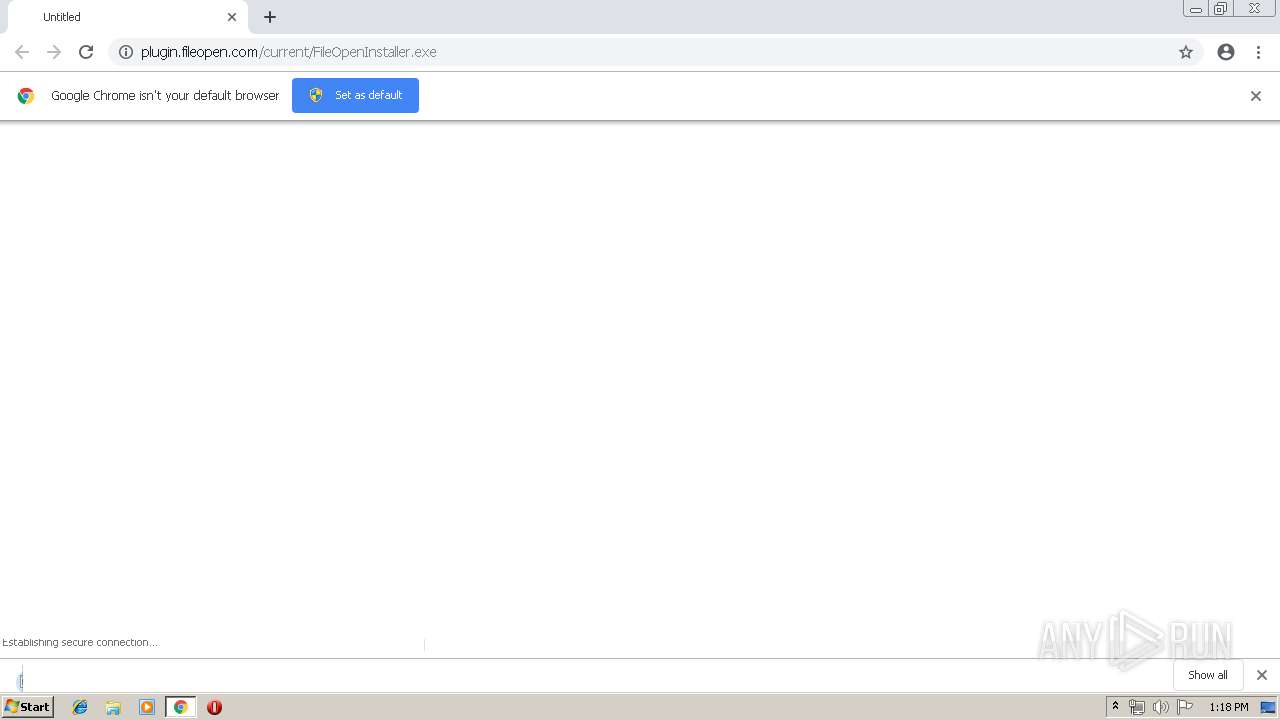
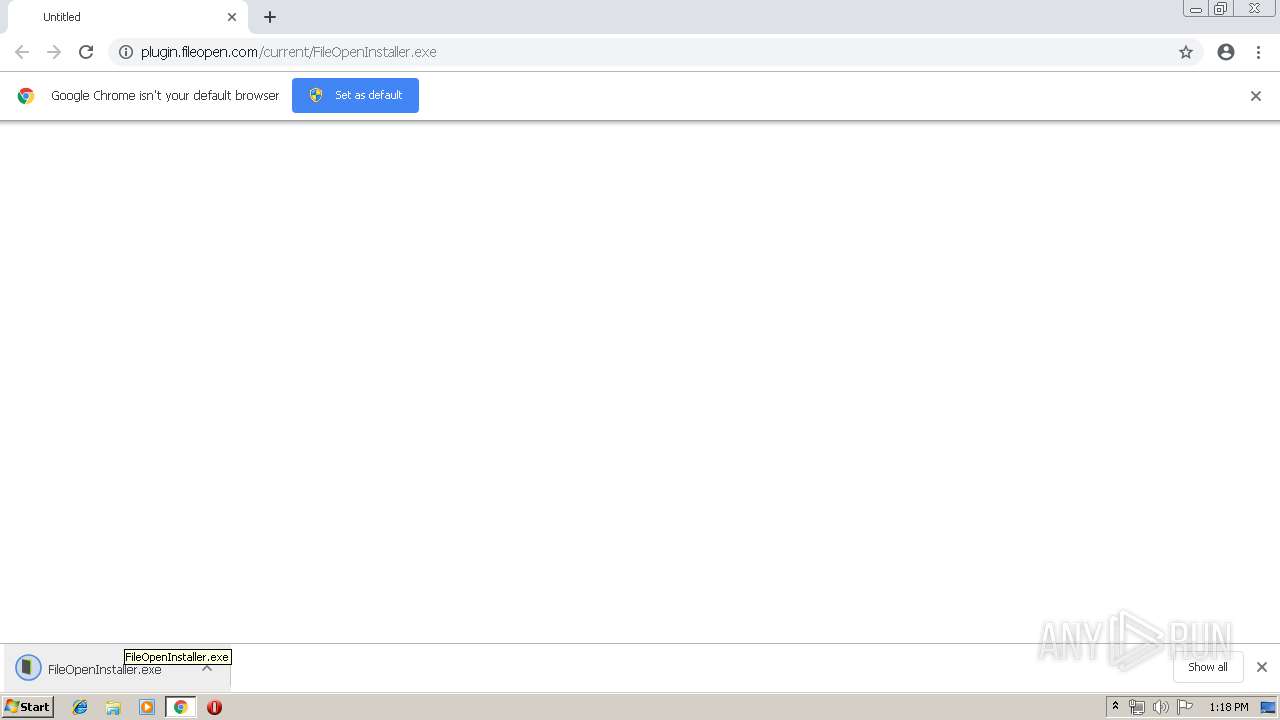
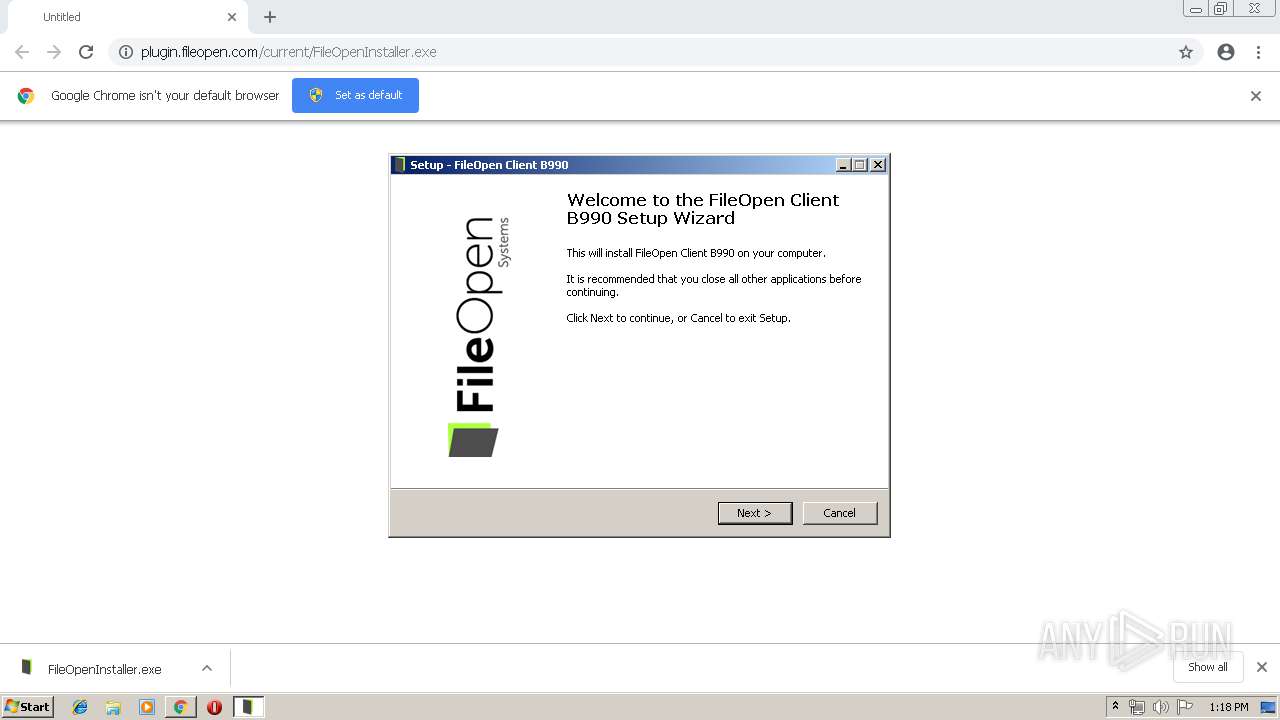
| URL: | http://plugin.fileopen.com/current/FileOpenInstaller.exe |
| Full analysis: | https://app.any.run/tasks/c6aff7ed-13a6-41e5-9a6b-786b03b22c23 |
| Verdict: | Suspicious activity |
| Analysis date: | April 03, 2019, 12:18:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 262080EE9ABA376441D9A2A55F19838E |
| SHA1: | 9049F7E800AE72CA9B054A88500BC4271F817BE1 |
| SHA256: | DD498AC7B18DC336785A74AB97253C79868C65A15FF6CA85DC433836015A8B7D |
| SSDEEP: | 3:N1KOJXKLQJN7dQiJyYZOXLNn:COJXQU7dOAOXLN |
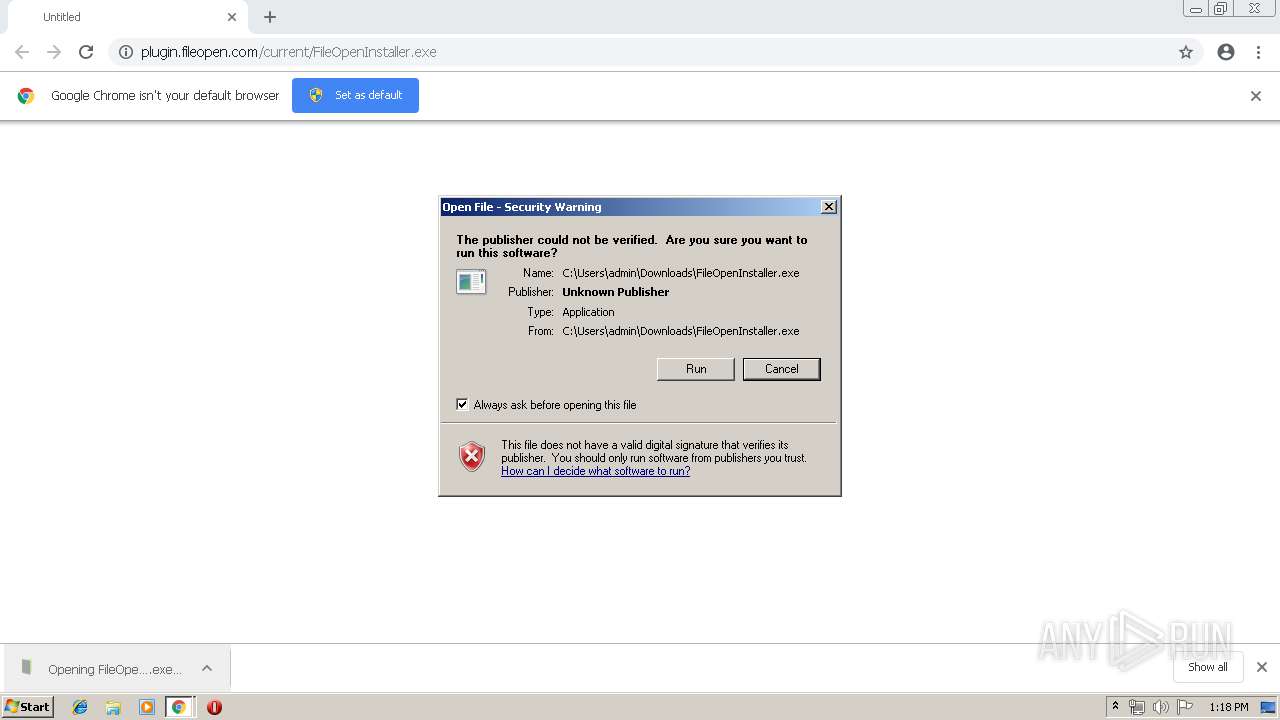
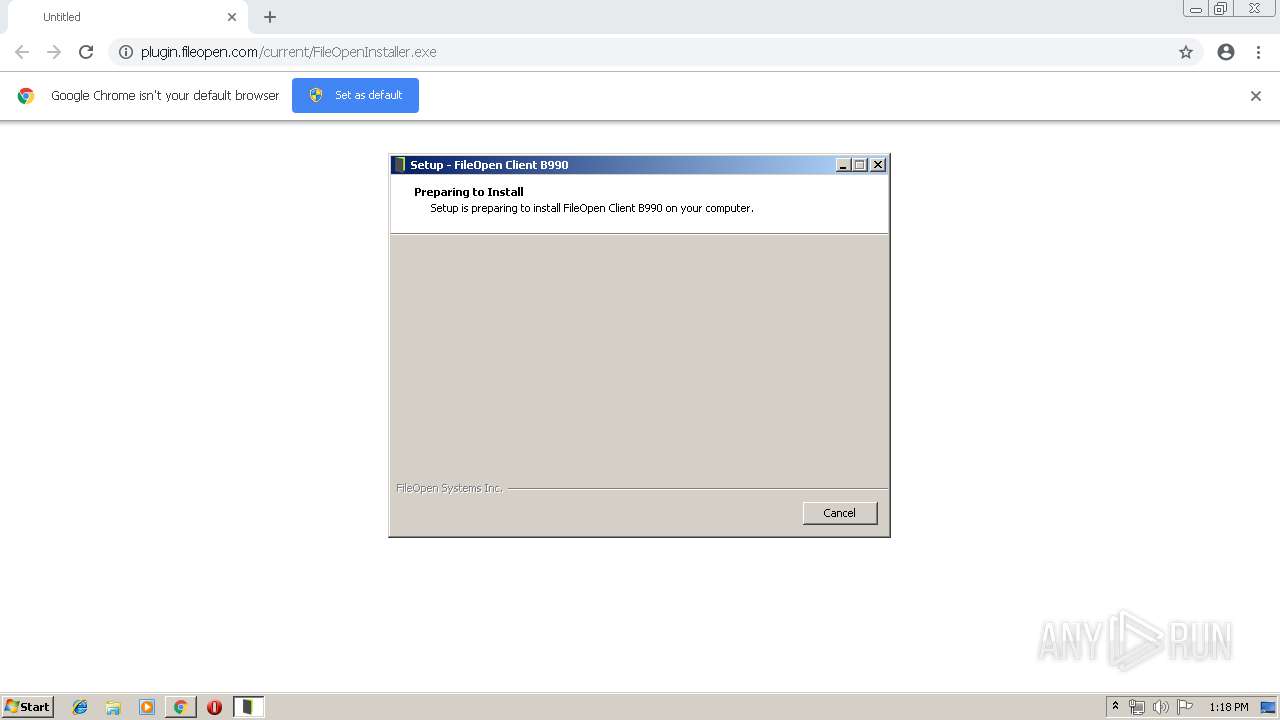
MALICIOUS
Application was dropped or rewritten from another process
- FileOpenInstaller.exe (PID: 3584)
- FileOpenInstaller.exe (PID: 2460)
- FileOpenManager32.exe (PID: 2992)
- FileOpenBroker32.exe (PID: 3828)
Changes the autorun value in the registry
- FileOpenInstaller.tmp (PID: 3332)
Loads dropped or rewritten executable
- AcroRd32.exe (PID: 2864)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2388)
- chrome.exe (PID: 2660)
- FileOpenInstaller.exe (PID: 3584)
- FileOpenInstaller.exe (PID: 2460)
- FileOpenInstaller.tmp (PID: 3332)
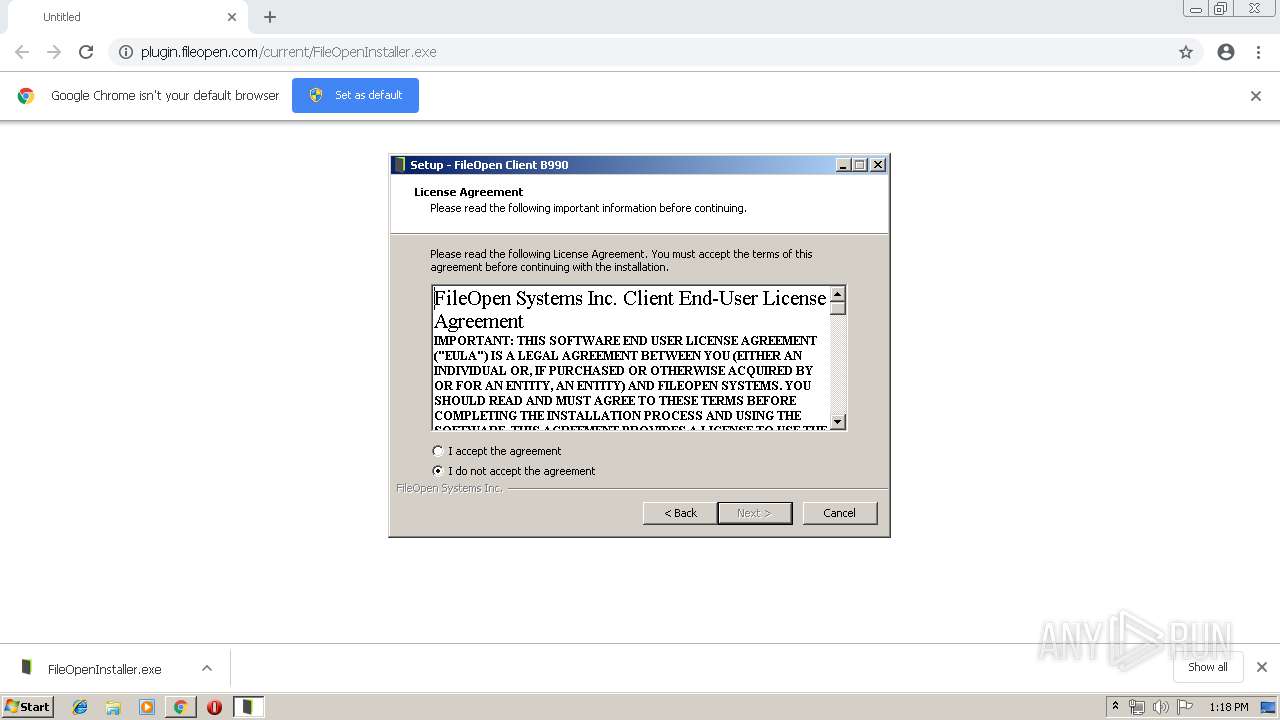
Reads Windows owner or organization settings
- FileOpenInstaller.tmp (PID: 3332)
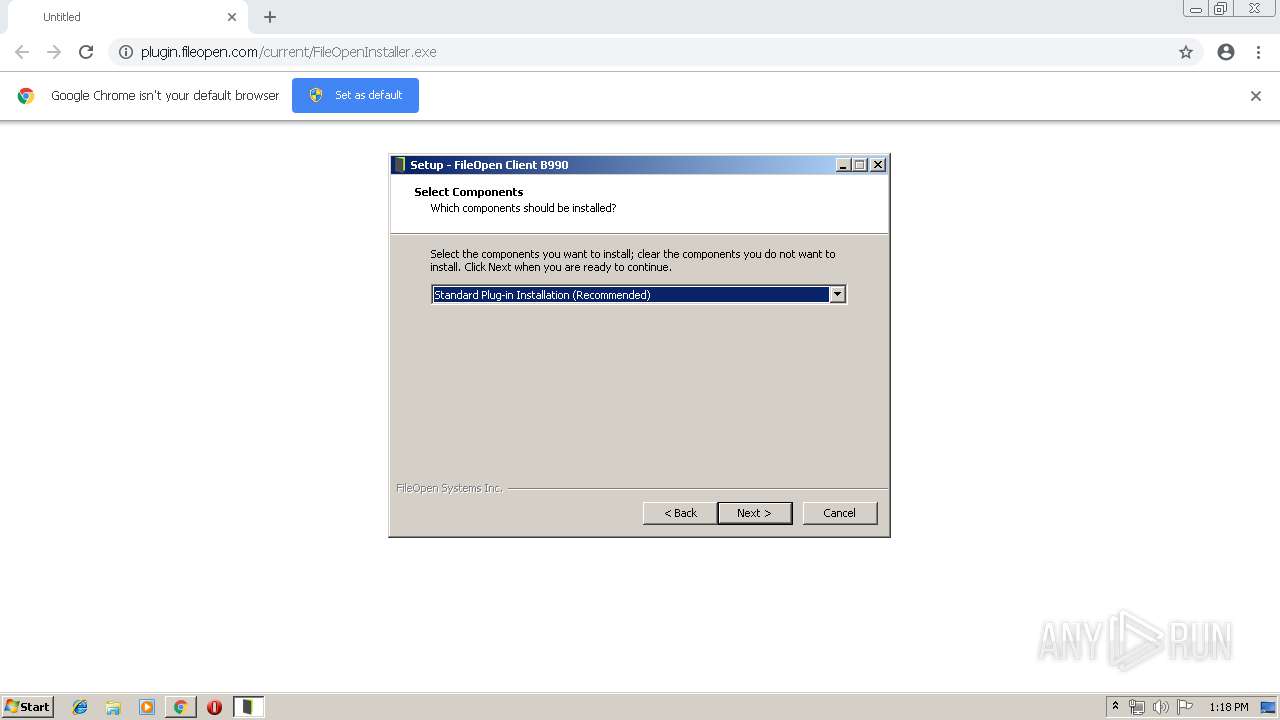
Starts SC.EXE for service management
- FileOpenInstaller.tmp (PID: 3332)
Reads the Windows organization settings
- FileOpenInstaller.tmp (PID: 3332)
Creates or modifies windows services
- FileOpenManager32.exe (PID: 2992)
Creates files in the user directory
- FileOpenBroker32.exe (PID: 3828)
INFO
Application launched itself
- chrome.exe (PID: 2660)
- RdrCEF.exe (PID: 2620)
Application was dropped or rewritten from another process
- FileOpenInstaller.tmp (PID: 3000)
- FileOpenInstaller.tmp (PID: 3332)
Reads settings of System Certificates
- chrome.exe (PID: 2660)
Loads dropped or rewritten executable
- FileOpenInstaller.tmp (PID: 3332)
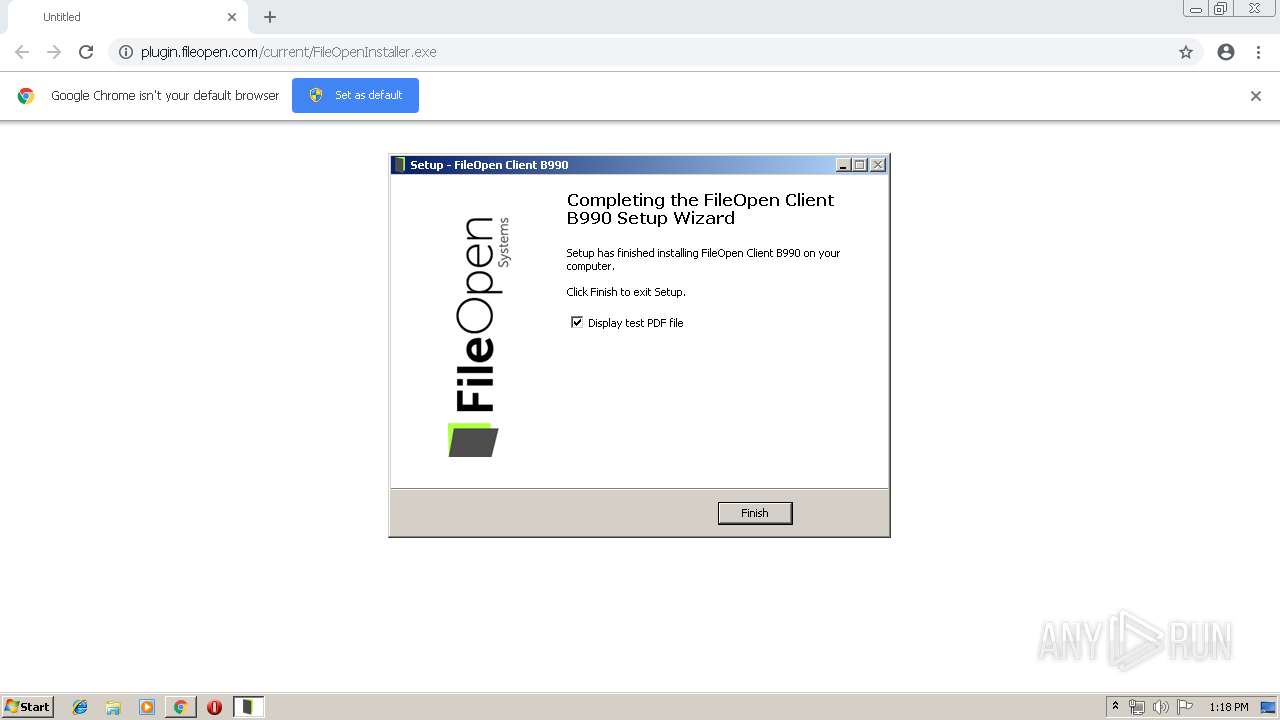
Creates a software uninstall entry
- FileOpenInstaller.tmp (PID: 3332)
Creates files in the program directory
- FileOpenInstaller.tmp (PID: 3332)
Creates files in the user directory
- AcroRd32.exe (PID: 352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
60
Monitored processes
24
Malicious processes
3
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" installcomplete.pdf | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | FileOpenInstaller.tmp | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 15.23.20070.215641 Modules
| |||||||||||||||
| 880 | "C:\Windows\system32\sc.exe" description FileOpenManager "FileOpen Client Manager" | C:\Windows\system32\sc.exe | — | FileOpenInstaller.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1240 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --disable-3d-apis --disable-databases --disable-direct-npapi-requests --disable-file-system --disable-notifications --disable-shared-workers --disable-direct-write --lang=en-US --lang=en-US --log-severity=disable --product-version="ReaderServices/15.23.20053 Chrome/45.0.2454.85" --device-scale-factor=1 --enable-delegated-renderer --num-raster-threads=2 --gpu-rasterization-msaa-sample-count=8 --content-image-texture-target=3553 --video-image-texture-target=3553 --disable-accelerated-video-decode --disable-webrtc-hw-encoding --disable-gpu-compositing --channel="2620.0.681874819\1152978794" --allow-no-sandbox-job /prefetch:673131151 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2232 | "C:\Windows\system32\sc.exe" create FileOpenManager binpath= "\"C:\Program Files\FileOpen\Services\FileOpenManager32.exe\"" start= auto | C:\Windows\system32\sc.exe | — | FileOpenInstaller.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2364 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=73.0.3683.75 --initial-client-data=0x7c,0x80,0x84,0x78,0x88,0x6fa90f18,0x6fa90f28,0x6fa90f34 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2388 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=968,4264294120935130364,3160071493445238977,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=1749391958620690936 --mojo-platform-channel-handle=1472 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2460 | "C:\Users\admin\Downloads\FileOpenInstaller.exe" /SPAWNWND=$2015C /NOTIFYWND=$3012C | C:\Users\admin\Downloads\FileOpenInstaller.exe | FileOpenInstaller.tmp | ||||||||||||
User: admin Company: FileOpen Systems Inc. Integrity Level: HIGH Description: {cm:FileOpenClient} B990 Exit code: 0 Version: 1.0.86.990 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16448250 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | AcroRd32.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe RdrCEF Exit code: 3221225547 Version: 15.23.20053.211670 Modules
| |||||||||||||||
| 2660 | "C:\Program Files\Google\Chrome\Application\chrome.exe" http://plugin.fileopen.com/current/FileOpenInstaller.exe | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 2700 | "C:\Windows\system32\sc.exe" start FileOpenManager | C:\Windows\system32\sc.exe | — | FileOpenInstaller.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: A tool to aid in developing services for WindowsNT Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 589
Read events
1 364
Write events
213
Delete events
12
Modification events
| (PID) Process: | (3308) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2660-13198767520666250 |
Value: 259 | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3488-13197474229333984 |
Value: 0 | |||
| (PID) Process: | (2660) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 2660-13198767520666250 |
Value: 259 | |||
Executable files
14
Suspicious files
23
Text files
59
Unknown types
17
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\c4ef6cbc-acb5-49c9-b07a-b9c4cc99d92b.tmp | — | |
MD5:— | SHA256:— | |||
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000018.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 2660 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
14
DNS requests
9
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
352 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/280_15_23_20070.zip | unknown | — | — | whitelisted |
352 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/279_15_23_20070.zip | unknown | — | — | whitelisted |
2660 | chrome.exe | GET | 200 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
352 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/message.zip | unknown | — | — | whitelisted |
— | — | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
352 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/277_15_23_20070.zip | unknown | — | — | whitelisted |
2660 | chrome.exe | GET | 304 | 93.184.221.240:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
352 | AcroRd32.exe | GET | 304 | 2.16.186.33:80 | http://acroipm2.adobe.com/15/rdr/ENU/win/nooem/none/consumer/281_15_23_20070.zip | unknown | — | — | whitelisted |
2388 | chrome.exe | GET | 301 | 64.106.211.88:80 | http://plugin.fileopen.com/current/FileOpenInstaller.exe | US | html | 180 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2388 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2388 | chrome.exe | 64.106.211.88:80 | plugin.fileopen.com | DataPipe, Inc. | US | unknown |
2388 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
2388 | chrome.exe | 64.106.211.88:443 | plugin.fileopen.com | DataPipe, Inc. | US | unknown |
2388 | chrome.exe | 172.217.18.174:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2388 | chrome.exe | 172.217.18.99:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
2660 | chrome.exe | 93.184.221.240:80 | www.download.windowsupdate.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
3828 | FileOpenBroker32.exe | 64.106.211.88:443 | plugin.fileopen.com | DataPipe, Inc. | US | unknown |
352 | AcroRd32.exe | 2.18.233.74:443 | armmf.adobe.com | Akamai International B.V. | — | whitelisted |
352 | AcroRd32.exe | 2.16.186.33:80 | acroipm2.adobe.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
plugin.fileopen.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
sb-ssl.google.com |
| whitelisted |
www.download.windowsupdate.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
acroipm2.adobe.com |
| whitelisted |
armmf.adobe.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2388 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
Process | Message |
|---|---|
FileOpenInstaller.tmp | AcroFind.cpp(113) : atlTraceGeneral - Checking HKEY for SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\AcroRd32.exe
|
FileOpenInstaller.tmp | AcroFind.cpp(113) : atlTraceGeneral - Found file: C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe
|
FileOpenInstaller.tmp | AcroFind.cpp(113) : atlTraceGeneral - app path search: plug_ins dir = C:\Program Files\Adobe\Acrobat Reader DC\Reader\plug_ins
|
FileOpenInstaller.tmp | AcroFind.cpp(113) : atlTraceGeneral - Found version: 15
|
FileOpenInstaller.tmp | AcroFind.cpp(113) : atlTraceGeneral - Checking HKEY for SOFTWARE\Adobe\Acrobat Reader\DC\InstallPath
|
FileOpenInstaller.tmp | AcroFind.cpp(113) : atlTraceGeneral - install path search: plug_ins dir = C:\Program Files\Adobe\Acrobat Reader DC\Reader\plug_ins
|
FileOpenInstaller.tmp | AcroFind.cpp(113) : atlTraceGeneral - Checking HKEY for SOFTWARE\Adobe\Acrobat Reader\2019\InstallPath
|
FileOpenInstaller.tmp | AcroFind.cpp(113) : atlTraceGeneral - AcroFind::installpath_search(): The handle is invalid.
|
FileOpenInstaller.tmp | AcroFind.cpp(113) : atlTraceGeneral - Checking HKEY for SOFTWARE\Adobe\Acrobat Reader\2018\InstallPath
|
FileOpenInstaller.tmp | AcroFind.cpp(113) : atlTraceGeneral - AcroFind::installpath_search(): The handle is invalid.
|