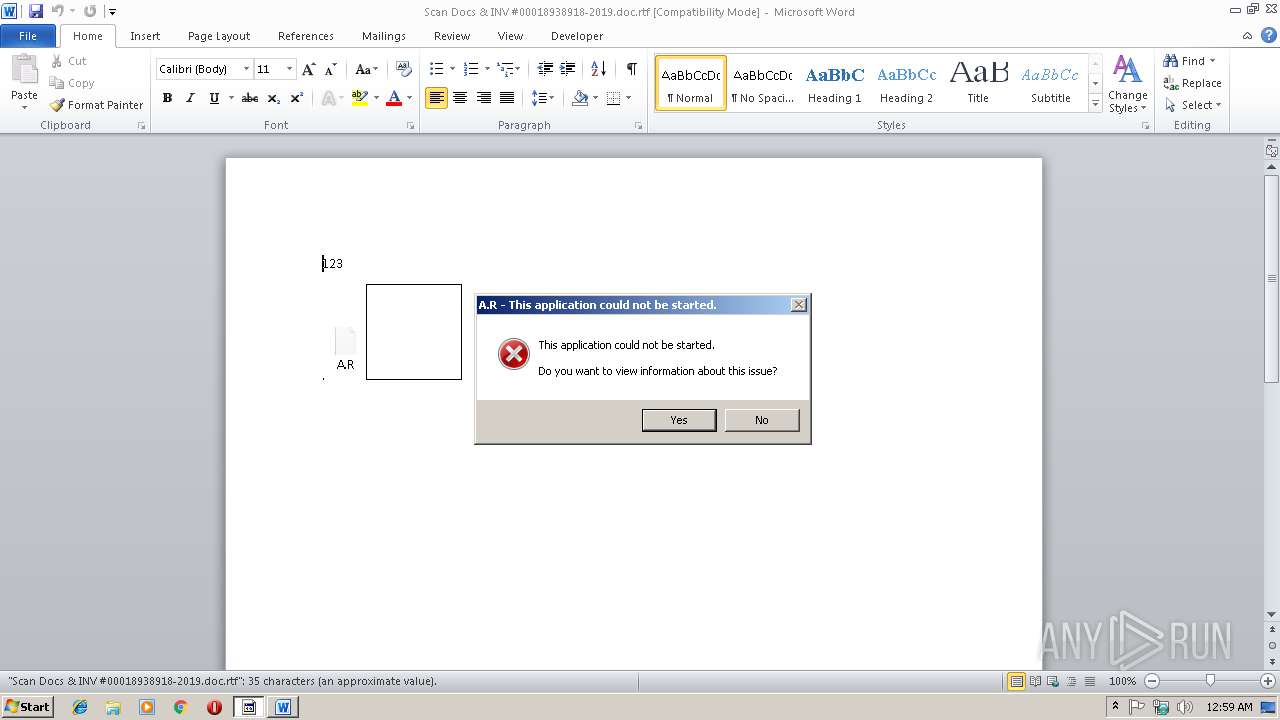
| File name: | Scan Docs & INV #00018938918-2019.doc |
| Full analysis: | https://app.any.run/tasks/c939d4ab-a557-4794-8fdf-cf0157792e14 |
| Verdict: | Malicious activity |
| Analysis date: | March 15, 2019, 00:59:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | F10EBC2B9DEB82802A21CE209CE45C07 |
| SHA1: | 8870B63E1A6C8311D6FBD78287D69AF99F15F3AE |
| SHA256: | DD47C39FA54FC00F3F71F79E8846A6FC38AC7A8FE2BC88E4410C436DA4FDF856 |
| SSDEEP: | 12288:sinOdX5MjrkBbC56nHridylQiNEDIszN2vmyqBBXrIv3nHOCQfgX:s3X5IrkooH2dy6iiVzwvmyQXkvXO4 |
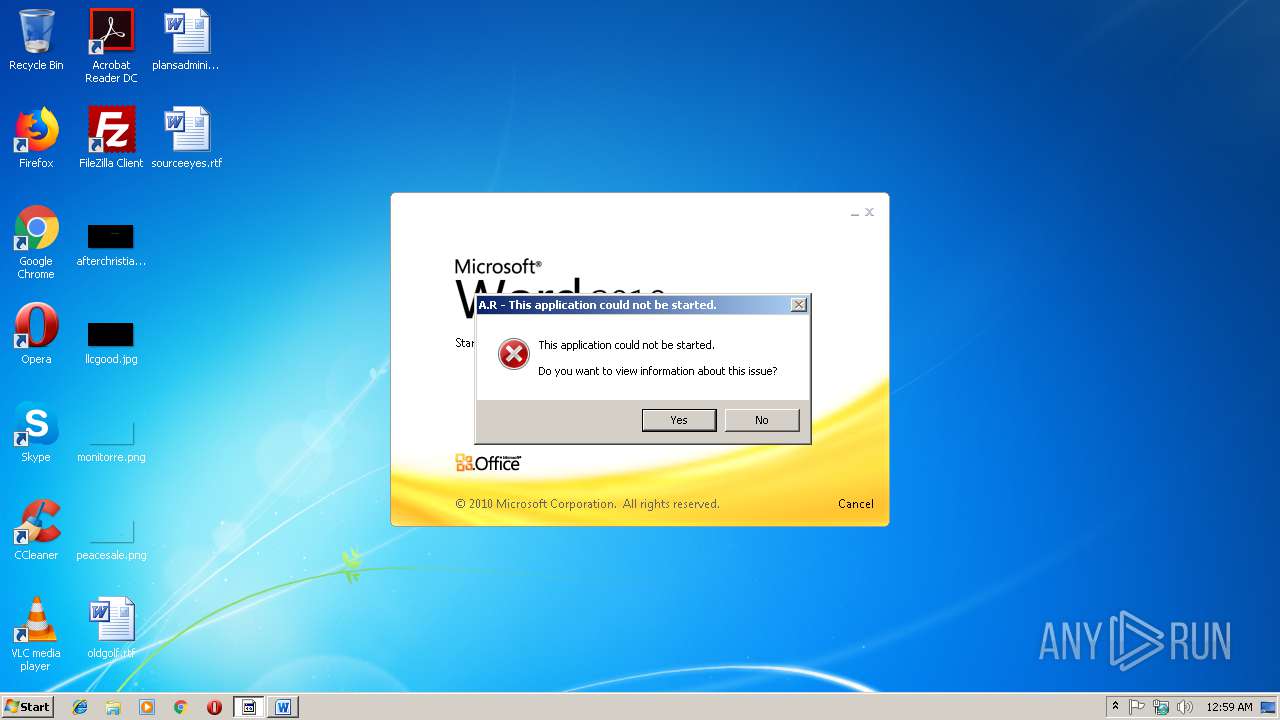
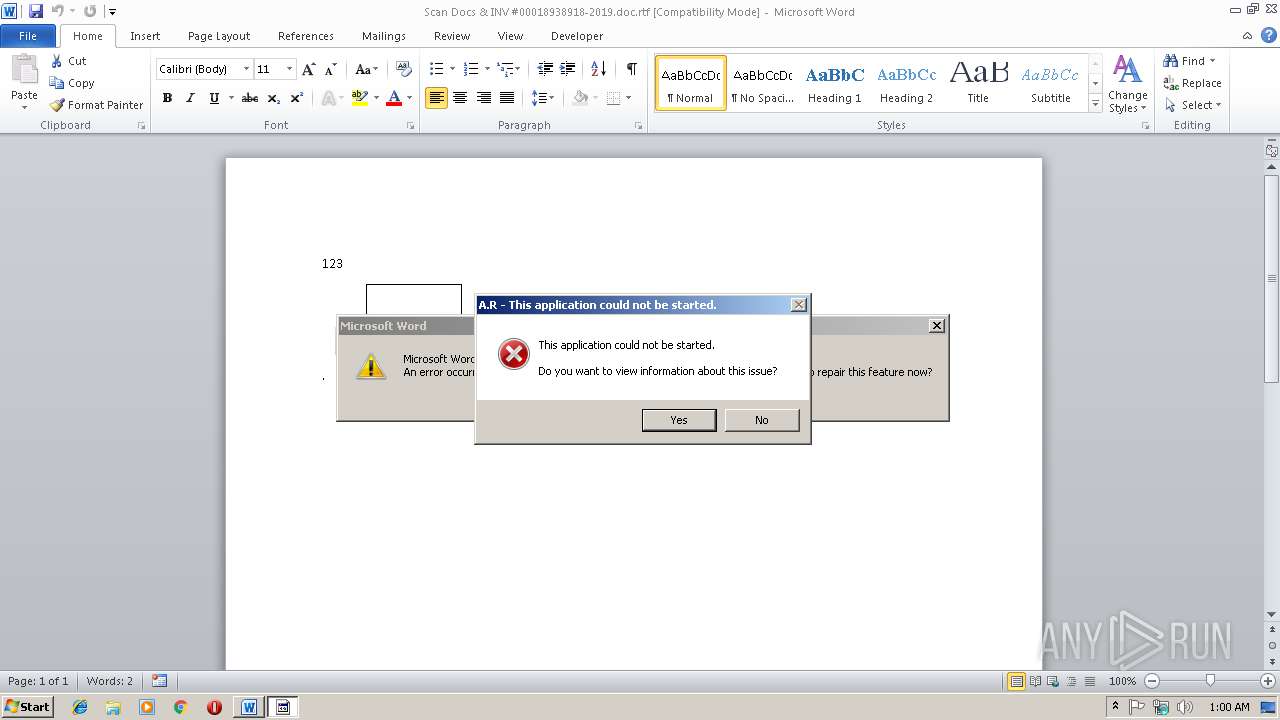
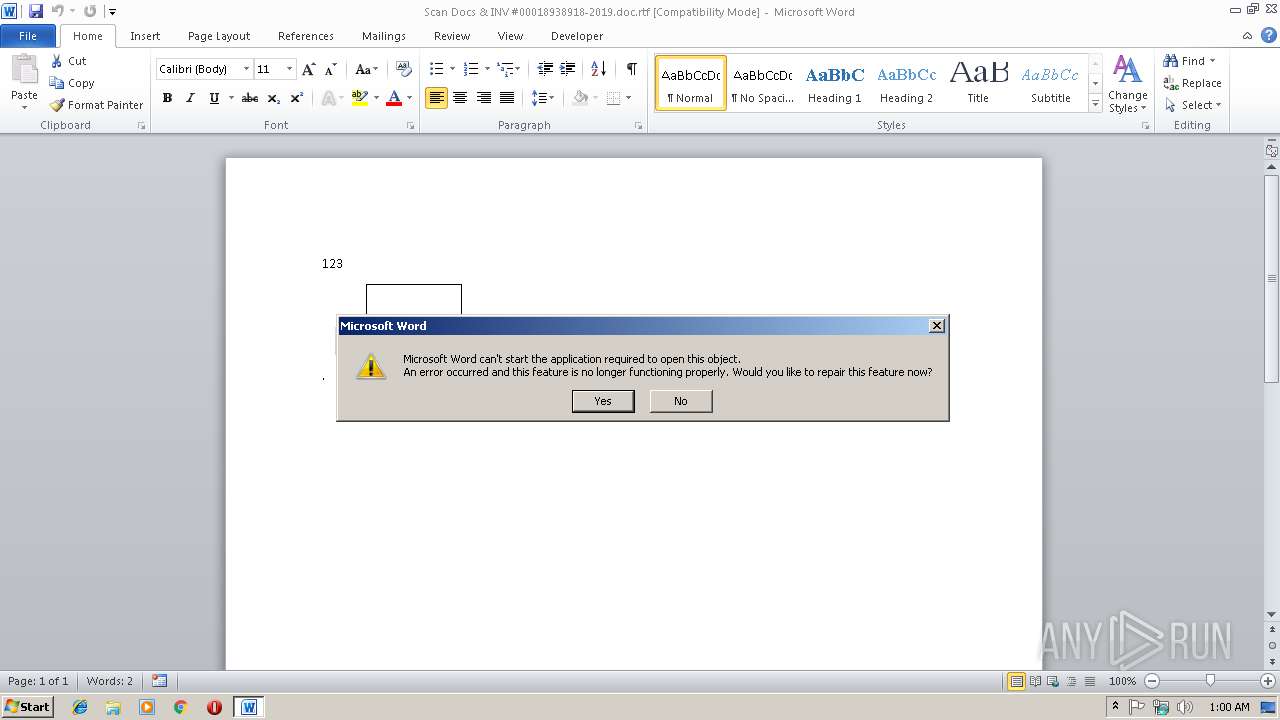
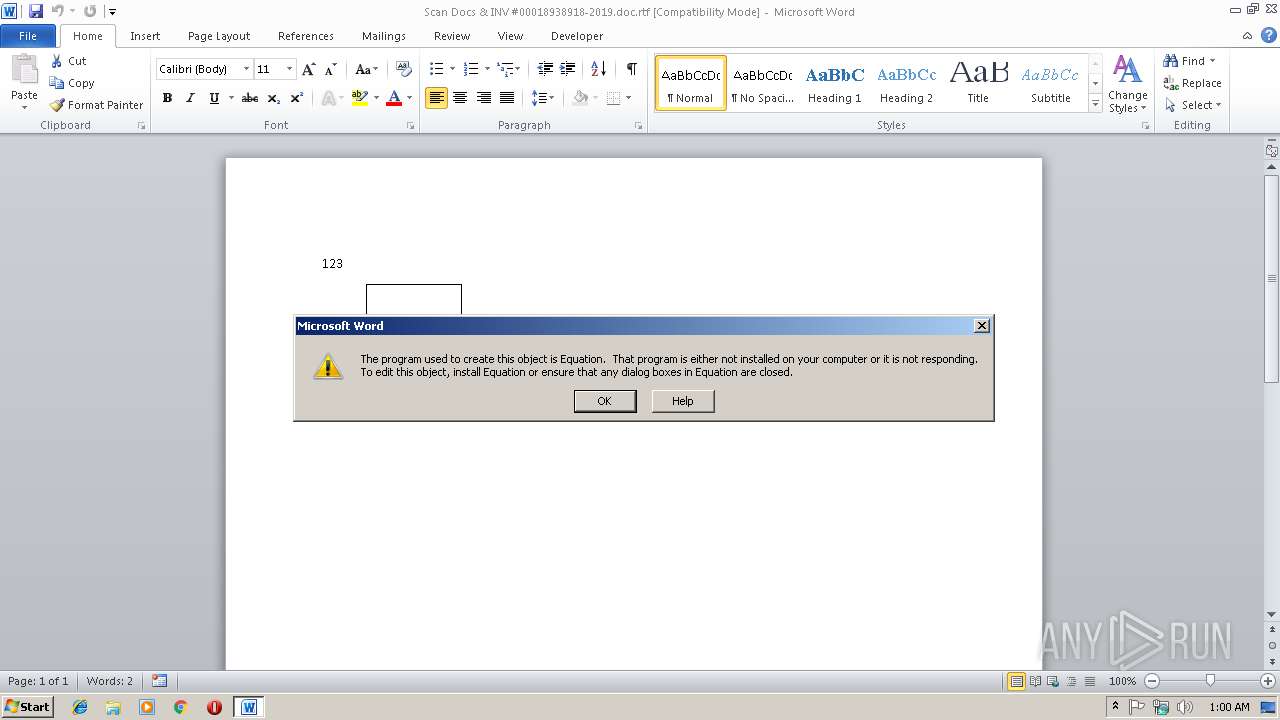
MALICIOUS
Equation Editor starts application (CVE-2017-11882)
- EQNEDT32.EXE (PID: 3780)
- EQNEDT32.EXE (PID: 3132)
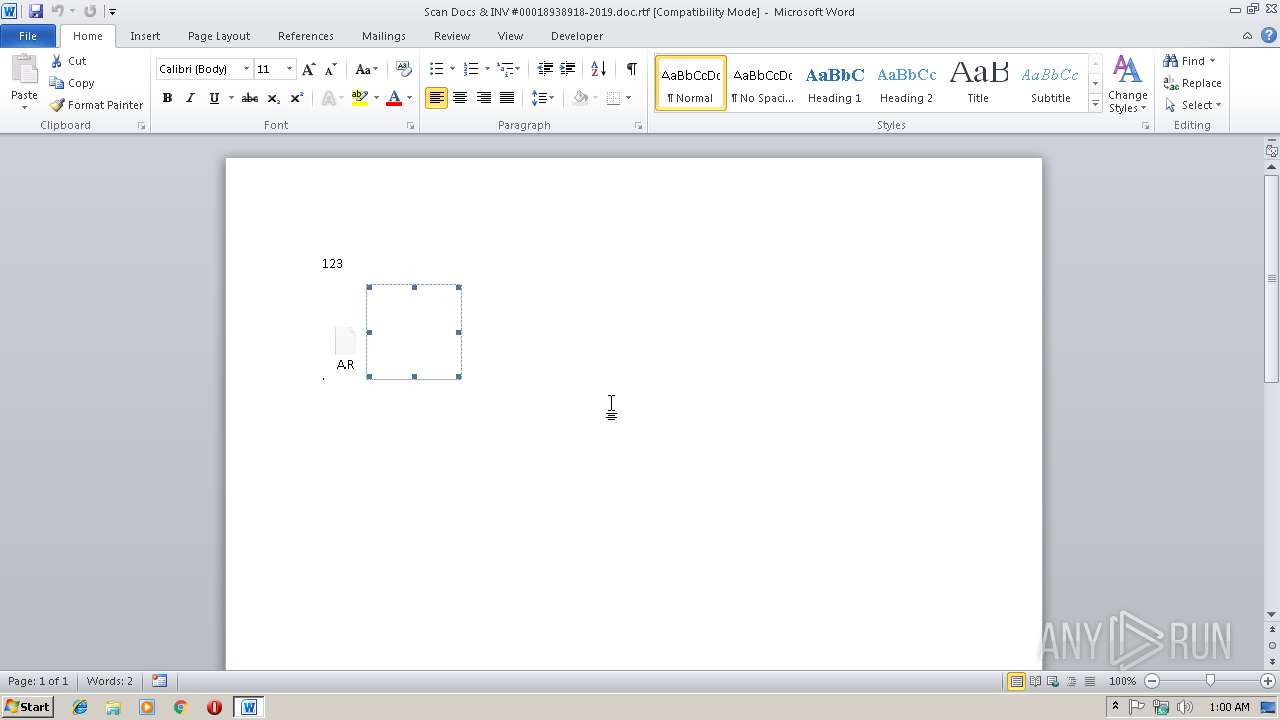
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 2896)
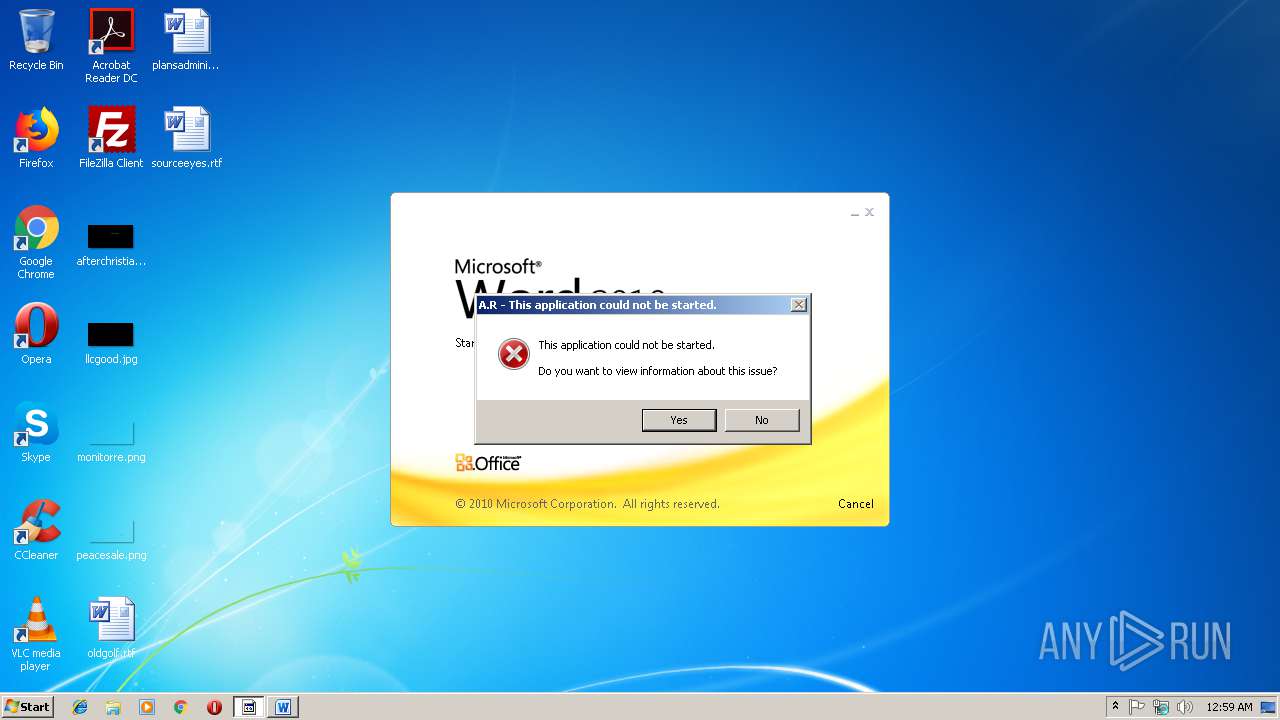
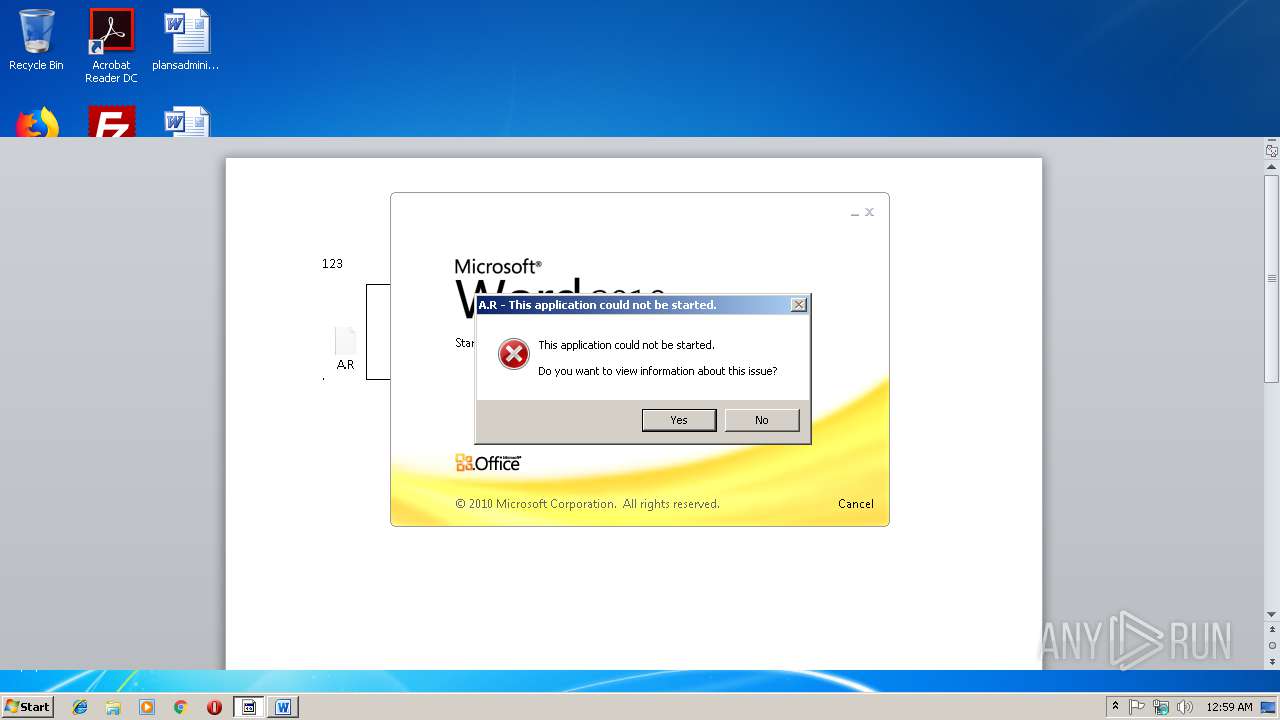
Application was dropped or rewritten from another process
- A.R (PID: 3232)
- A.R (PID: 2876)
- A.R (PID: 3816)
- A.R (PID: 3568)
- A.R (PID: 3616)
- A.R (PID: 3856)
SUSPICIOUS
Starts application with an unusual extension
- cmd.exe (PID: 2372)
- A.R (PID: 3232)
- A.R (PID: 2876)
- A.R (PID: 3616)
- A.R (PID: 3568)
- cmd.exe (PID: 3632)
Starts CMD.EXE for commands execution
- EQNEDT32.EXE (PID: 3780)
- EQNEDT32.EXE (PID: 3132)
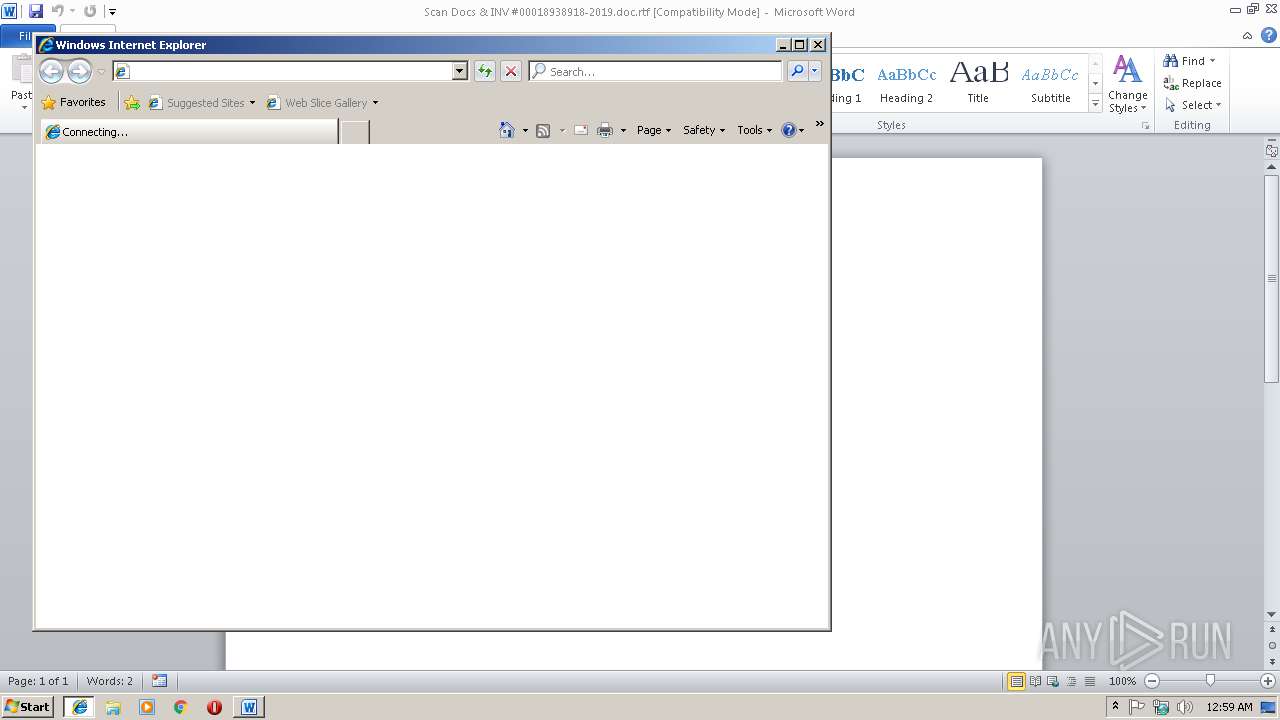
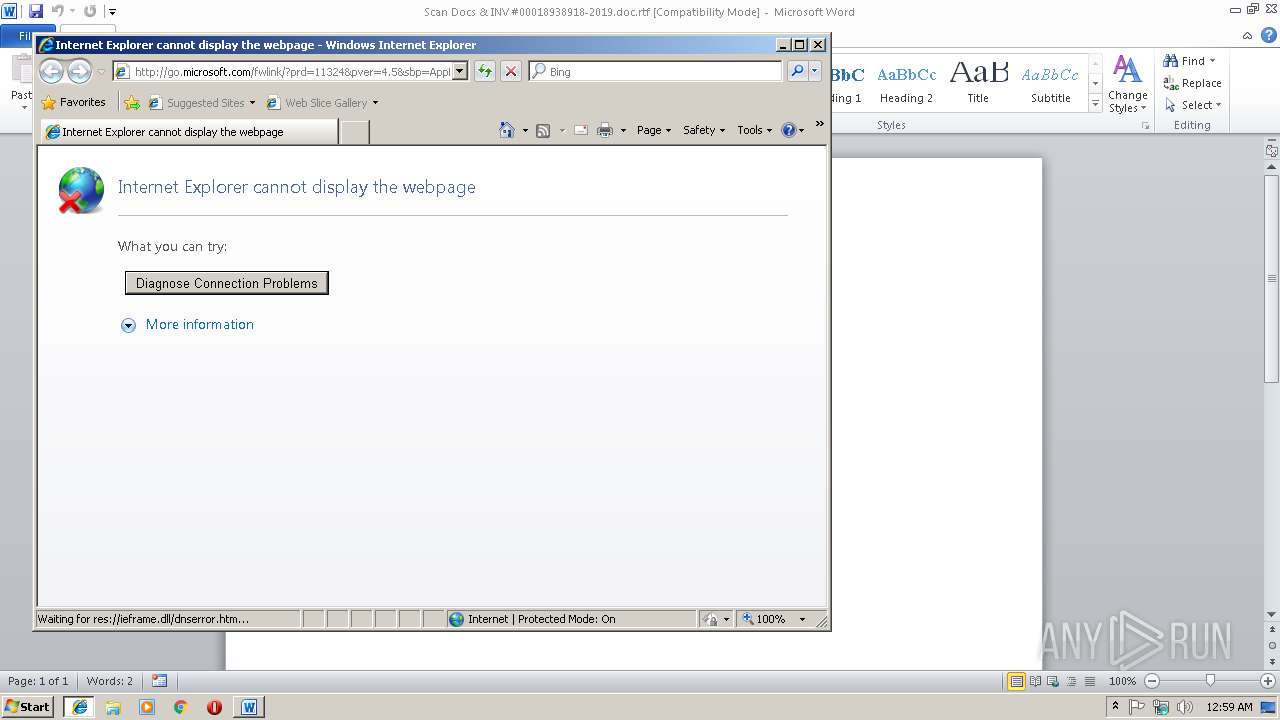
Starts Internet Explorer
- A.R (PID: 3816)
INFO
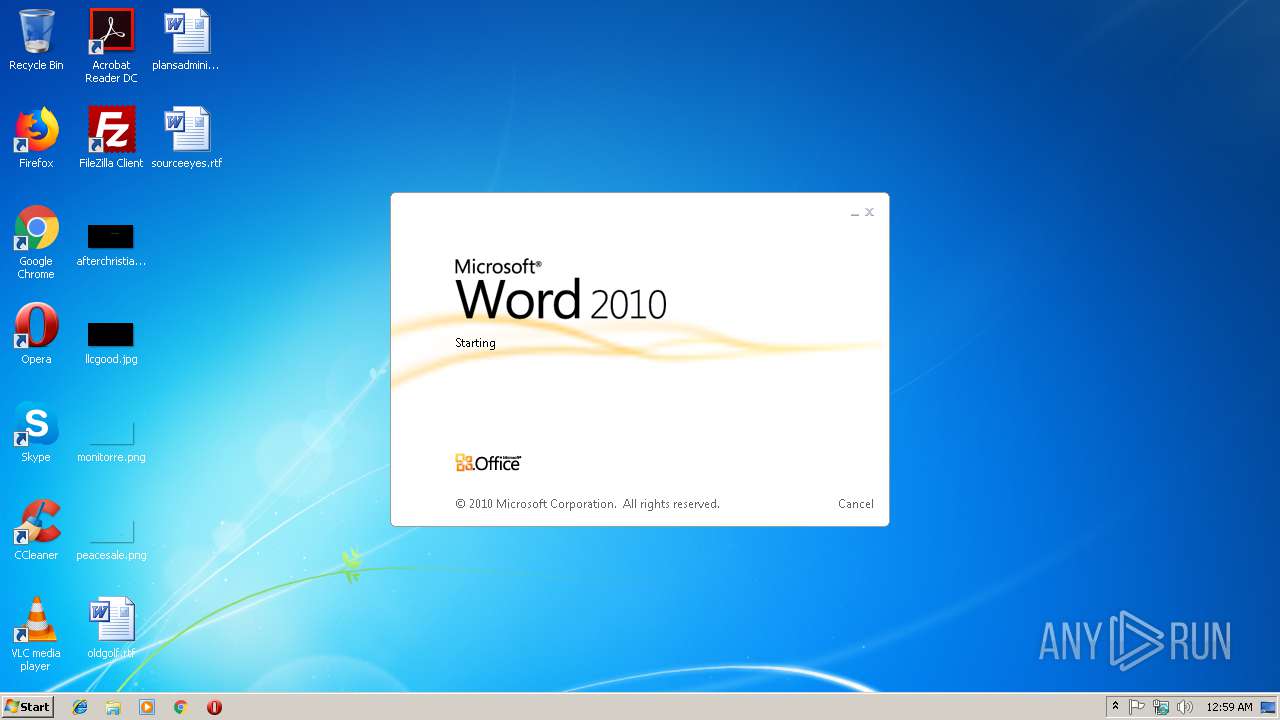
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2896)
Creates files in the user directory
- WINWORD.EXE (PID: 2896)
- iexplore.exe (PID: 3024)
Application was crashed
- EQNEDT32.EXE (PID: 3780)
- EQNEDT32.EXE (PID: 3132)
Application launched itself
- iexplore.exe (PID: 2516)
Changes internet zones settings
- iexplore.exe (PID: 2516)
Reads Internet Cache Settings
- iexplore.exe (PID: 3024)
Reads internet explorer settings
- iexplore.exe (PID: 3024)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
EXIF
RTF
| Author: | wuyan |
|---|---|
| LastModifiedBy: | wuyan |
| CreateDate: | 2019:01:03 16:14:00 |
| ModifyDate: | 2019:01:03 16:34:00 |
| RevisionNumber: | 3 |
| TotalEditTime: | 1 minute |
| Pages: | 1 |
| Words: | 4 |
| Characters: | 24 |
| CharactersWithSpaces: | 27 |
| InternalVersionNumber: | 57435 |
Total processes
47
Monitored processes
13
Malicious processes
3
Suspicious processes
7
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2372 | cmd /c %tMp%\A.R | C:\Windows\system32\cmd.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2516 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | A.R | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2876 | C:\Users\admin\AppData\Local\Temp\A.R | C:\Users\admin\AppData\Local\Temp\A.R | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2896 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Scan Docs & INV #00018938918-2019.doc.rtf" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3024 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2516 CREDAT:71937 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3132 | "C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE" -Embedding | C:\Program Files\Common Files\Microsoft Shared\EQUATION\EQNEDT32.EXE | svchost.exe | ||||||||||||
User: admin Company: Design Science, Inc. Integrity Level: MEDIUM Description: Microsoft Equation Editor Exit code: 0 Version: 00110900 Modules
| |||||||||||||||
| 3232 | C:\Users\admin\AppData\Local\Temp\A.R 3b | C:\Users\admin\AppData\Local\Temp\A.R | — | A.R | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3568 | C:\Users\admin\AppData\Local\Temp\A.R 3b | C:\Users\admin\AppData\Local\Temp\A.R | — | A.R | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3616 | C:\Users\admin\AppData\Local\Temp\A.R | C:\Users\admin\AppData\Local\Temp\A.R | — | cmd.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3632 | cmd /c %tMp%\A.R | C:\Windows\system32\cmd.exe | — | EQNEDT32.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 982
Read events
1 222
Write events
744
Delete events
16
Modification events
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | b6& |
Value: 62362600500B0000010000000000000000000000 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1315897365 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315897484 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315897485 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 500B0000F2C22658CADAD40100000000 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | x7& |
Value: 78372600500B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | x7& |
Value: 78372600500B000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (2896) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
3
Text files
12
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRE262.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF532321CDAC3DBCCF.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB941DE423FD088BD.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA7CD069FDD30CABA.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{A410BA5A-46BD-11E9-BEEC-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFA7B57A7EFE4CF694.TMP | — | |
MD5:— | SHA256:— | |||
| 2516 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{A410BA59-46BD-11E9-BEEC-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 2896 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{86B2F1B7-6E2C-4F22-847E-4772B6B577CF}.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
6
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3024 | iexplore.exe | GET | 302 | 104.109.80.115:80 | http://go.microsoft.com/fwlink/?prd=11324&pver=4.5&sbp=AppLaunch2&plcid=0x409&o1=SHIM_NOVERSION_FOUND&version=(null)&processName=A.R&platform=0000&osver=5&isServer=0&shimver=4.0.30319.0 | NL | — | — | whitelisted |
2516 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2516 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3024 | iexplore.exe | 104.109.80.115:80 | go.microsoft.com | Akamai International B.V. | NL | whitelisted |
3024 | iexplore.exe | 104.111.225.176:443 | docs.microsoft.com | Akamai International B.V. | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
docs.microsoft.com |
| whitelisted |