| File name: | Yandex.exe |
| Full analysis: | https://app.any.run/tasks/7ef7ceb6-6833-4004-8442-031eb2d18e0f |
| Verdict: | Malicious activity |
| Analysis date: | April 14, 2019, 20:16:44 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 3D611D16FEA99AA0FA56085485C9CB5D |
| SHA1: | 1AD7488ECAADA764E84AB1CA3D53AF75A435967E |
| SHA256: | DD3EA602199F490A179170816A29B21727671887C114A46669CDE01EB49089E0 |
| SSDEEP: | 24576:eW1+qGEUnBUBmEuHr+QDodTJvTAaFaiH6:H8BJ+iod1vTCd |
MALICIOUS
Changes settings of System certificates
- setup.exe (PID: 1532)
Application was dropped or rewritten from another process
- setup.exe (PID: 1532)
- setup.exe (PID: 2264)
- setup.exe (PID: 3352)
- service_update.exe (PID: 2896)
- service_update.exe (PID: 3044)
- service_update.exe (PID: 3540)
- service_update.exe (PID: 3604)
- service_update.exe (PID: 2744)
- service_update.exe (PID: 2972)
- service_update.exe (PID: 3556)
- clidmgr.exe (PID: 3264)
- service_update.exe (PID: 884)
- clidmgr.exe (PID: 3256)
- clidmgr.exe (PID: 3924)
- clidmgr.exe (PID: 3208)
- browser.exe (PID: 2164)
- browser.exe (PID: 3224)
- browser.exe (PID: 2940)
- browser.exe (PID: 3996)
- browser.exe (PID: 2096)
- browser.exe (PID: 3236)
- browser.exe (PID: 3404)
- browser.exe (PID: 3660)
- browser.exe (PID: 3040)
- browser.exe (PID: 3384)
- browser.exe (PID: 2608)
- browser.exe (PID: 3188)
- browser.exe (PID: 1752)
- browser.exe (PID: 1520)
- browser.exe (PID: 3076)
- browser.exe (PID: 3900)
- browser.exe (PID: 2804)
- browser.exe (PID: 456)
- browser.exe (PID: 2408)
- browser.exe (PID: 3964)
- browser.exe (PID: 2228)
- browser.exe (PID: 2176)
- browser.exe (PID: 2968)
- browser.exe (PID: 2700)
Loads the Task Scheduler COM API
- service_update.exe (PID: 2896)
- browser.exe (PID: 3224)
Loads the Task Scheduler DLL interface
- service_update.exe (PID: 884)
- service_update.exe (PID: 3556)
- browser.exe (PID: 3224)
Loads dropped or rewritten executable
- browser.exe (PID: 3224)
- browser.exe (PID: 2164)
- browser.exe (PID: 2940)
- browser.exe (PID: 2096)
- browser.exe (PID: 3996)
- browser.exe (PID: 3236)
- browser.exe (PID: 2700)
- browser.exe (PID: 3384)
- browser.exe (PID: 3660)
- browser.exe (PID: 3040)
- browser.exe (PID: 2608)
- browser.exe (PID: 3188)
- browser.exe (PID: 1520)
- browser.exe (PID: 1752)
- browser.exe (PID: 3900)
- browser.exe (PID: 3076)
- browser.exe (PID: 2804)
- browser.exe (PID: 456)
- browser.exe (PID: 2408)
- browser.exe (PID: 3964)
- browser.exe (PID: 2228)
- browser.exe (PID: 2176)
- browser.exe (PID: 2968)
- browser.exe (PID: 3404)
Actions looks like stealing of personal data
- browser.exe (PID: 3224)
SUSPICIOUS
Starts itself from another location
- Yandex.exe (PID: 3072)
Application launched itself
- Yandex.exe (PID: 3904)
- setup.exe (PID: 2264)
- service_update.exe (PID: 3044)
- service_update.exe (PID: 884)
- browser.exe (PID: 3224)
Executable content was dropped or overwritten
- ybFE0F.tmp (PID: 4084)
- Yandex.exe (PID: 3072)
- setup.exe (PID: 1532)
- service_update.exe (PID: 3604)
- service_update.exe (PID: 2744)
Creates files in the user directory
- Yandex.exe (PID: 3904)
- setup.exe (PID: 1532)
- clidmgr.exe (PID: 3256)
Starts application with an unusual extension
- Yandex.exe (PID: 2976)
Adds / modifies Windows certificates
- setup.exe (PID: 1532)
Modifies the open verb of a shell class
- setup.exe (PID: 1532)
- browser.exe (PID: 3224)
Creates files in the program directory
- service_update.exe (PID: 2744)
Creates a software uninstall entry
- setup.exe (PID: 1532)
Creates files in the Windows directory
- service_update.exe (PID: 884)
- service_update.exe (PID: 3044)
- service_update.exe (PID: 3556)
- service_update.exe (PID: 2972)
Removes files from Windows directory
- service_update.exe (PID: 3044)
- service_update.exe (PID: 2972)
Reads the cookies of Google Chrome
- browser.exe (PID: 2176)
INFO
Dropped object may contain Bitcoin addresses
- setup.exe (PID: 1532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:04:08 07:00:00+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 14 |
| CodeSize: | 384512 |
| InitializedDataSize: | 475648 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x3eca0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 19.3.2.177 |
| ProductVersionNumber: | 19.3.2.177 |
| FileFlagsMask: | 0x0017 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | YANDEX LLC |
| FileDescription: | Yandex |
| FileVersion: | 19.3.2.177 |
| InternalName: | lite_installer |
| LegalCopyright: | Copyright (c) 2012-2018 YANDEX LLC. All Rights Reserved. |
| ProductName: | Yandex |
| ProductVersion: | 19.3.2.177 |
| ProductChromiumVersion: | 72.0.3626.121 |
| ProductYandexVersion: | 19.3.2.177 |
| CompanyShortName: | YANDEX LLC |
| ProductShortName: | Yandex Installer |
| LastChange: | f291cd76ba21f855939afee43aa27aaa2ca3fde1 |
| OfficialBuild: | 1 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 08-Apr-2019 05:00:00 |
| Detected languages: |
|
| Debug artifacts: |
|
| CompanyName: | YANDEX LLC |
| FileDescription: | Yandex |
| FileVersion: | 19.3.2.177 |
| InternalName: | lite_installer |
| LegalCopyright: | Copyright (c) 2012-2018 YANDEX LLC. All Rights Reserved. |
| ProductName: | Yandex |
| ProductVersion: | 19.3.2.177 |
| ProductChromiumVersion: | 72.0.3626.121 |
| ProductYandexVersion: | 19.3.2.177 |
| CompanyShortName: | YANDEX LLC |
| ProductShortName: | Yandex Installer |
| LastChange: | f291cd76ba21f855939afee43aa27aaa2ca3fde1 |
| Official Build: | 1 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0078 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0x0000 |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x0000 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000078 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 9 |
| Time date stamp: | 08-Apr-2019 05:00:00 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0005DD70 | 0x0005DE00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.6467 |
.rdata | 0x0005F000 | 0x00017E0C | 0x00018000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.12611 |
.data | 0x00077000 | 0x0000239C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.89452 |
.00cfg | 0x0007A000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.0611629 |
.tls | 0x0007B000 | 0x00000009 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.0203931 |
SHARED | 0x0007C000 | 0x00000004 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED, IMAGE_SCN_MEM_WRITE | 0 |
Shared | 0x0007D000 | 0x00001052 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_SHARED, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0007F000 | 0x000554AC | 0x00055600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.30894 |
.reloc | 0x000D5000 | 0x00003FC8 | 0x00004000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.69778 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.1744 | 2002 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 4.44702 | 9832 | Latin 1 / Western European | UNKNOWN | RT_ICON |
3 | 4.58339 | 4392 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 4.56164 | 2488 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 4.80269 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
26 | 3.34409 | 1120 | Latin 1 / Western European | Spanish - Spain (International sort) | RT_STRING |
27 | 3.2921 | 1658 | Latin 1 / Western European | Spanish - Spain (International sort) | RT_STRING |
28 | 3.21322 | 672 | Latin 1 / Western European | Spanish - Spain (International sort) | RT_STRING |
128 | 2.68263 | 76 | Latin 1 / Western European | UNKNOWN | RT_GROUP_ICON |
129 | 2.07664 | 406 | Latin 1 / Western European | UNKNOWN | RT_DIALOG |
Imports
GDI32.dll (delay-loaded) |
KERNEL32.dll |
WINHTTP.dll |
Total processes
84
Monitored processes
43
Malicious processes
17
Suspicious processes
11
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 456 | "C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe" --type=utility --field-trial-handle=948,2511525863342270084,2708011542406287673,131072 --lang=en-US --no-sandbox --user-id=D6CD7390-5E59-40D6-BDB0-339BF466423A --brand-id=int --service-request-channel-token=13573164707440109856 --process-name="Windows Utilities" --mojo-platform-channel-handle=3080 /prefetch:8 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe | — | browser.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: MEDIUM Description: Yandex Exit code: 0 Version: 19.3.2.177 Modules
| |||||||||||||||
| 884 | "C:\Program Files\Yandex\YandexBrowser\19.3.2.177\service_update.exe" --update-scheduler | C:\Program Files\Yandex\YandexBrowser\19.3.2.177\service_update.exe | — | service_update.exe | |||||||||||
User: SYSTEM Company: YANDEX LLC Integrity Level: SYSTEM Description: Yandex Exit code: 0 Version: 19.3.2.177 Modules
| |||||||||||||||
| 1520 | "C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe" --broupdater --bits_job_guid={E7D089A7-D822-4CEC-B454-00B09FE06662} | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe | — | svchost.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: MEDIUM Description: Yandex Exit code: 0 Version: 19.3.2.177 Modules
| |||||||||||||||
| 1532 | "C:\Users\admin\AppData\Local\Temp\YB_04051.tmp\setup.exe" --install-archive="C:\Users\admin\AppData\Local\Temp\YB_04051.tmp\BROWSER.PACKED.7Z" --searchband-file="C:\Users\admin\AppData\Local\Temp\YB_04051.tmp\SEARCHBAND.EXE" --brand-name=int --brand-package="C:\Users\admin\AppData\Local\Temp\BrandFile" --clids-file="C:\Users\admin\AppData\Local\Temp\clids.xml" --clids-searchband-file="C:\Users\admin\AppData\Local\Temp\clids_searchband.xml" --installerdata="C:\Users\admin\AppData\Local\Temp\master_preferences" --make-browser-default-after-import --ok-button-pressed-time=1248114257 --progress-window=196912 --send-statistics --source=lite --spawned_in_protected_dir --verbose-logging --yandex-website-icon-file="C:\Users\admin\AppData\Local\Temp\website.ico" --verbose-logging --run-as-admin --target-path="C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application" --child-setup-process --restart-as-admin-time=1312348632 | C:\Users\admin\AppData\Local\Temp\YB_04051.tmp\setup.exe | setup.exe | ||||||||||||
User: admin Company: YANDEX LLC Integrity Level: HIGH Description: Yandex Exit code: 1 Version: 19.3.2.177 Modules
| |||||||||||||||
| 1752 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Yandex\YandexBrowser\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Yandex\YandexBrowser\User Data\Crashpad" --url=https://crash-reports.browser.yandex.net/submit --annotation=install_date=1555273131 --annotation=machine_id=5f735395d68db0638bd0a2a58101e17a --annotation=main_process_pid=1520 --annotation=metrics_client_id=f28f382576e0492284a56699125daebd --annotation=plat=Win32 --annotation=prod=Yandex --annotation=session_logout=False --annotation=ver=19.3.2.177 --initial-client-data=0xa4,0xac,0xb0,0xa0,0xb4,0x6da32270,0x6da32280,0x6da3228c,0xa8 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe | — | browser.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: MEDIUM Description: Yandex Exit code: 0 Version: 19.3.2.177 Modules
| |||||||||||||||
| 2096 | "C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe" --type=utility --field-trial-handle=948,2511525863342270084,2708011542406287673,131072 --lang=en-US --no-sandbox --user-id=D6CD7390-5E59-40D6-BDB0-339BF466423A --brand-id=int --service-request-channel-token=5980525464881309866 --process-name="Profile Importer" --mojo-platform-channel-handle=2200 /prefetch:8 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe | — | browser.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: MEDIUM Description: Yandex Exit code: 0 Version: 19.3.2.177 Modules
| |||||||||||||||
| 2164 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Yandex\YandexBrowser\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Yandex\YandexBrowser\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Yandex\YandexBrowser\User Data" --url=https://crash-reports.browser.yandex.net/submit --annotation=install_date=1555273131 --annotation=machine_id=5f735395d68db0638bd0a2a58101e17a --annotation=main_process_pid=3224 --annotation=metrics_client_id=f28f382576e0492284a56699125daebd --annotation=plat=Win32 --annotation=prod=Yandex --annotation=session_logout=False --annotation=ver=19.3.2.177 --initial-client-data=0xa0,0xa8,0xac,0x9c,0xb0,0x6da32270,0x6da32280,0x6da3228c,0xa4 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe | — | browser.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: MEDIUM Description: Yandex Exit code: 0 Version: 19.3.2.177 Modules
| |||||||||||||||
| 2176 | "C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe" --type=utility --field-trial-handle=948,2511525863342270084,2708011542406287673,131072 --lang=en-US --no-sandbox --user-id=D6CD7390-5E59-40D6-BDB0-339BF466423A --brand-id=int --service-request-channel-token=10205292387864129533 --process-name="Profile Importer" --mojo-platform-channel-handle=628 /prefetch:8 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe | — | browser.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: MEDIUM Description: Yandex Exit code: 0 Version: 19.3.2.177 Modules
| |||||||||||||||
| 2228 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Yandex\YandexBrowser\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Yandex\YandexBrowser\User Data\Crashpad" --url=https://crash-reports.browser.yandex.net/submit --annotation=install_date=1555273131 --annotation=machine_id=5f735395d68db0638bd0a2a58101e17a --annotation=main_process_pid=3964 --annotation=metrics_client_id=f28f382576e0492284a56699125daebd --annotation=plat=Win32 --annotation=prod=Yandex --annotation=session_logout=False --annotation=ver=19.3.2.177 --initial-client-data=0xa4,0xac,0xb0,0xa0,0xb4,0x6da32270,0x6da32280,0x6da3228c,0xa8 | C:\Users\admin\AppData\Local\Yandex\YandexBrowser\Application\browser.exe | — | browser.exe | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: MEDIUM Description: Yandex Exit code: 0 Version: 19.3.2.177 Modules
| |||||||||||||||
| 2264 | "C:\Users\admin\AppData\Local\Temp\YB_04051.tmp\setup.exe" --install-archive="C:\Users\admin\AppData\Local\Temp\YB_04051.tmp\BROWSER.PACKED.7Z" --searchband-file="C:\Users\admin\AppData\Local\Temp\YB_04051.tmp\SEARCHBAND.EXE" --brand-name=int --brand-package="C:\Users\admin\AppData\Local\Temp\BrandFile" --clids-file="C:\Users\admin\AppData\Local\Temp\clids.xml" --clids-searchband-file="C:\Users\admin\AppData\Local\Temp\clids_searchband.xml" --installerdata="C:\Users\admin\AppData\Local\Temp\master_preferences" --make-browser-default-after-import --ok-button-pressed-time=1248114257 --progress-window=196912 --send-statistics --source=lite --spawned_in_protected_dir --verbose-logging --yandex-website-icon-file="C:\Users\admin\AppData\Local\Temp\website.ico" | C:\Users\admin\AppData\Local\Temp\YB_04051.tmp\setup.exe | — | ybFE0F.tmp | |||||||||||
User: admin Company: YANDEX LLC Integrity Level: HIGH Description: Yandex Exit code: 1 Version: 19.3.2.177 Modules
| |||||||||||||||
Total events
3 004
Read events
2 321
Write events
669
Delete events
14
Modification events
| (PID) Process: | (3904) Yandex.exe | Key: | HKEY_CURRENT_USER\Software\Yandex\YandexBrowser |
| Operation: | write | Name: | lang |
Value: en | |||
| (PID) Process: | (3904) Yandex.exe | Key: | HKEY_CURRENT_USER\Software\Yandex\YandexBrowser |
| Operation: | write | Name: | InstallerData |
Value: C:\Users\admin\AppData\Local\Temp\master_preferences | |||
| (PID) Process: | (3904) Yandex.exe | Key: | HKEY_CURRENT_USER\Software\Yandex\YandexBrowser |
| Operation: | write | Name: | ClidsFile |
Value: C:\Users\admin\AppData\Local\Temp\clids.xml | |||
| (PID) Process: | (3904) Yandex.exe | Key: | HKEY_CURRENT_USER\Software\Yandex\YandexBrowser |
| Operation: | write | Name: | ClidsSearchbandFile |
Value: C:\Users\admin\AppData\Local\Temp\clids_searchband.xml | |||
| (PID) Process: | (3904) Yandex.exe | Key: | HKEY_CURRENT_USER\Software\Yandex\YandexBrowser |
| Operation: | write | Name: | YandexWebsiteIconFile |
Value: C:\Users\admin\AppData\Local\Temp\website.ico | |||
| (PID) Process: | (3904) Yandex.exe | Key: | HKEY_CURRENT_USER\Software\Yandex\YandexBrowser |
| Operation: | write | Name: | brand |
Value: int | |||
| (PID) Process: | (3904) Yandex.exe | Key: | HKEY_CURRENT_USER\Software\Yandex\YandexBrowser |
| Operation: | write | Name: | BrandFile |
Value: C:\Users\admin\AppData\Local\Temp\BrandFile | |||
| (PID) Process: | (3904) Yandex.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Yandex_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3904) Yandex.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Yandex_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3904) Yandex.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\Yandex_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
Executable files
35
Suspicious files
183
Text files
468
Unknown types
55
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3072 | Yandex.exe | C:\Users\admin\AppData\Local\Temp\3072_29363\Yandex.exe | executable | |
MD5:— | SHA256:— | |||
| 3904 | Yandex.exe | C:\Users\admin\AppData\Local\Temp\lite_installer.log | text | |
MD5:— | SHA256:— | |||
| 3904 | Yandex.exe | C:\Users\admin\AppData\Local\Temp\BrandFile | compressed | |
MD5:— | SHA256:— | |||
| 3904 | Yandex.exe | C:\Users\admin\AppData\Local\Temp\master_preferences | text | |
MD5:— | SHA256:— | |||
| 3904 | Yandex.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\browser-setup[1].arc | — | |
MD5:— | SHA256:— | |||
| 3904 | Yandex.exe | C:\Users\admin\AppData\Local\Temp\ybFE0F.tmp | — | |
MD5:— | SHA256:— | |||
| 3904 | Yandex.exe | C:\Users\admin\AppData\Local\Temp\Cab2ED.tmp | — | |
MD5:— | SHA256:— | |||
| 3904 | Yandex.exe | C:\Users\admin\AppData\Local\Temp\Tar2EE.tmp | — | |
MD5:— | SHA256:— | |||
| 3904 | Yandex.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\02[1].jpg | image | |
MD5:— | SHA256:— | |||
| 4084 | ybFE0F.tmp | C:\Users\admin\AppData\Local\Temp\YB_04051.tmp\BROWSER.PACKED.7Z | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
128
DNS requests
87
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3044 | service_update.exe | GET | 200 | 104.18.20.226:80 | http://crl.globalsign.net/root.crl | US | der | 782 b | whitelisted |
3904 | Yandex.exe | GET | 200 | 104.18.20.226:80 | http://crl.globalsign.net/root.crl | US | der | 782 b | whitelisted |
2972 | service_update.exe | GET | 200 | 151.139.236.246:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR5iK7tYk9tqQEoeQhZNkKcAol9bgQUjEPEy22YwaechGnr30oNYJY6w%2FsCEQCTkoVAAWVxX5R%2FKI%2FvyZso | US | der | 1.62 Kb | whitelisted |
3044 | service_update.exe | GET | 200 | 104.18.21.226:80 | http://crl.globalsign.com/gs/gstimestampingg2.crl | US | der | 905 b | whitelisted |
3904 | Yandex.exe | GET | 200 | 104.18.21.226:80 | http://crl.globalsign.com/gs/gstimestampingg2.crl | US | der | 905 b | whitelisted |
3904 | Yandex.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkfDD%2F78IrsoD5b%2Bp1JR | US | der | 1.49 Kb | whitelisted |
3904 | Yandex.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/gscodesigng3/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTHTu2Y6Nr%2FMkfa3PrlxnwonnIpxQQUs9Pm1XFWfTlYs3jSK7j3oR%2F9S5sCDGUxOJI7m%2BYpSWV%2FXQ%3D%3D | US | der | 1.50 Kb | whitelisted |
3044 | service_update.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/ME8wTTBLMEkwRzAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDkfDD%2F78IrsoD5b%2Bp1JR | US | der | 1.49 Kb | whitelisted |
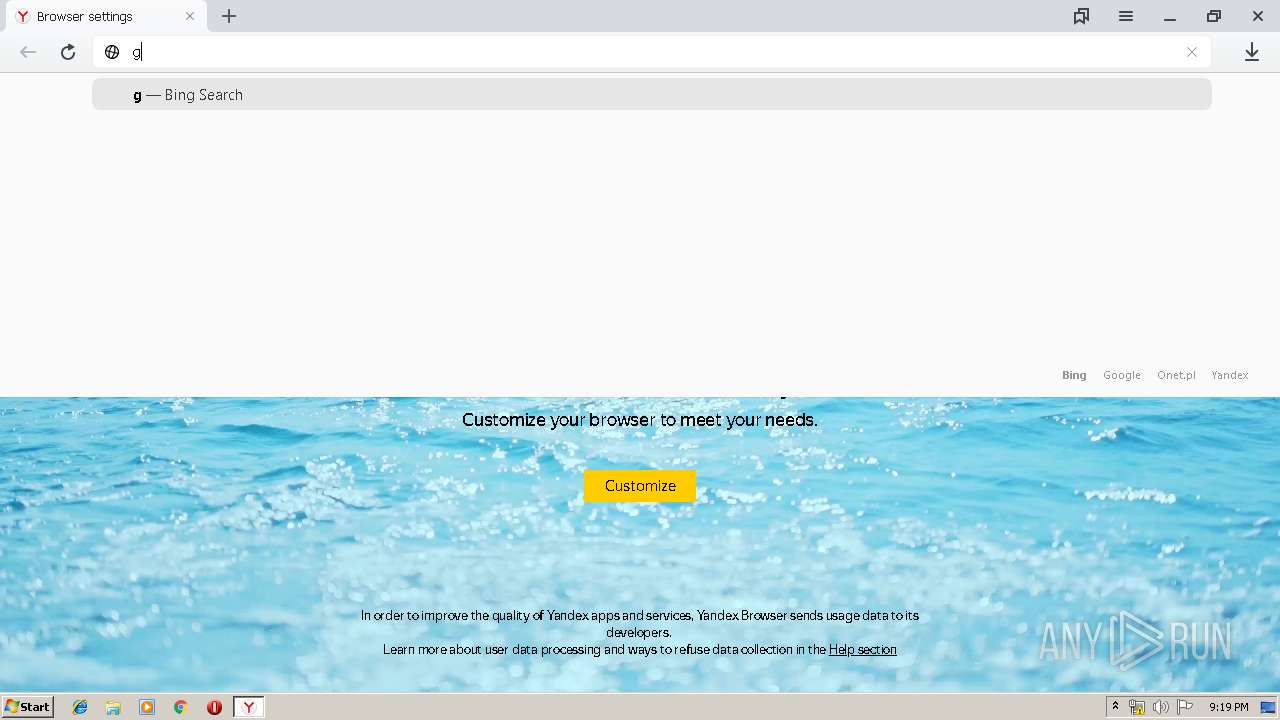
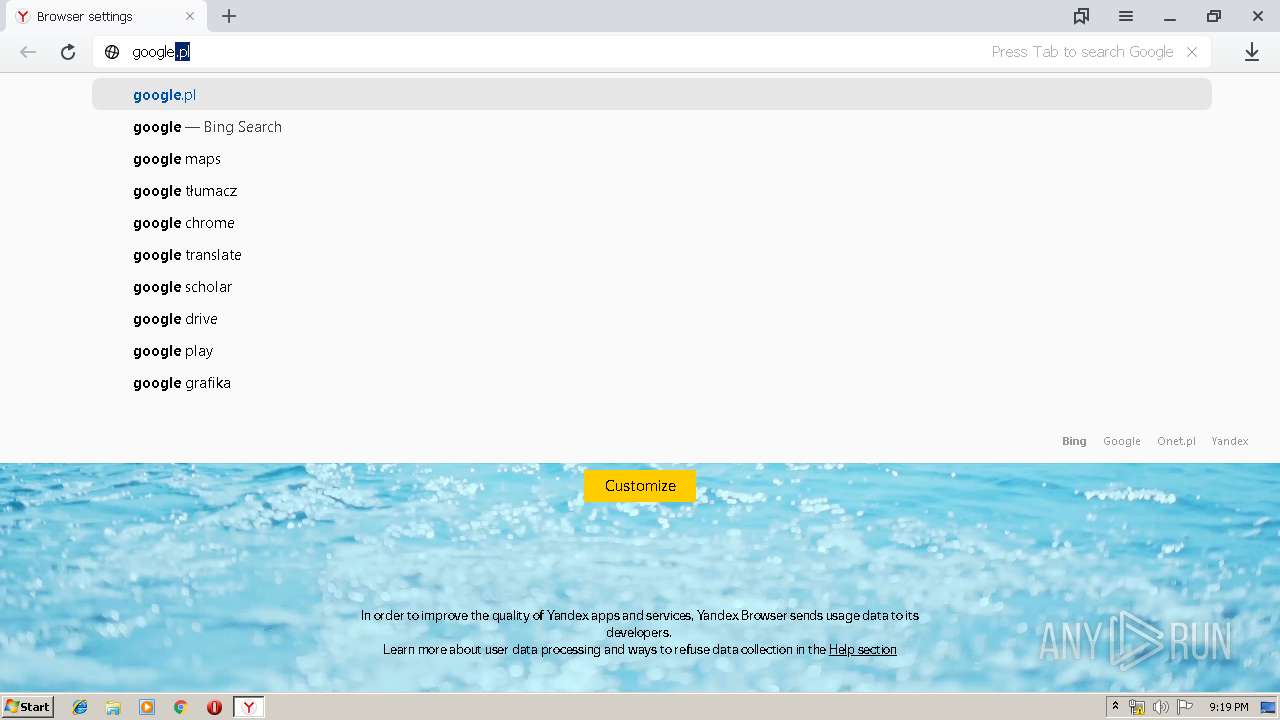
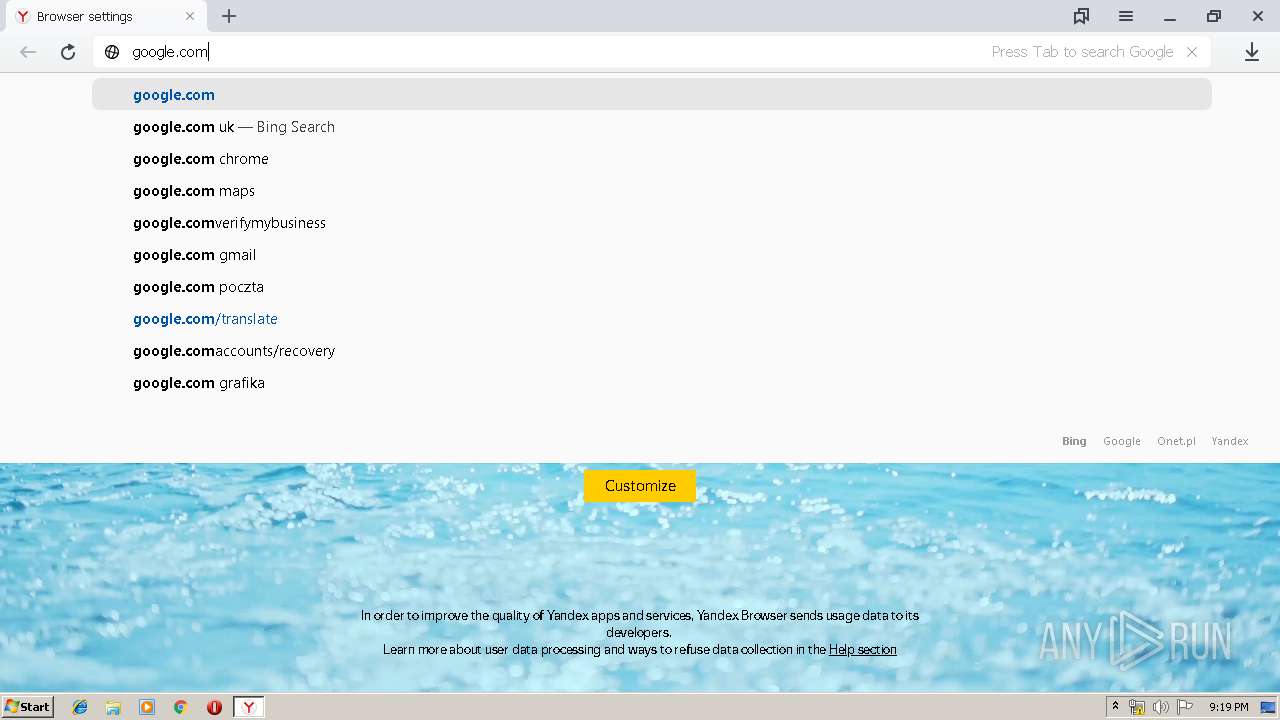
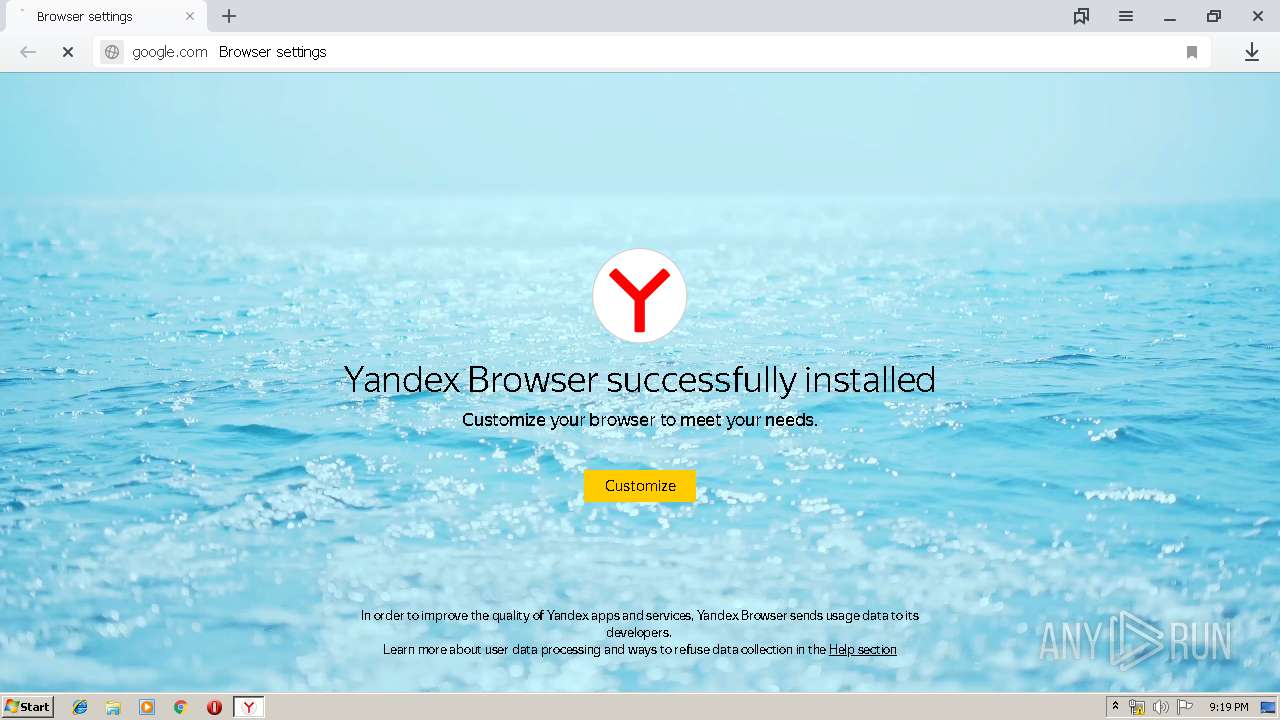
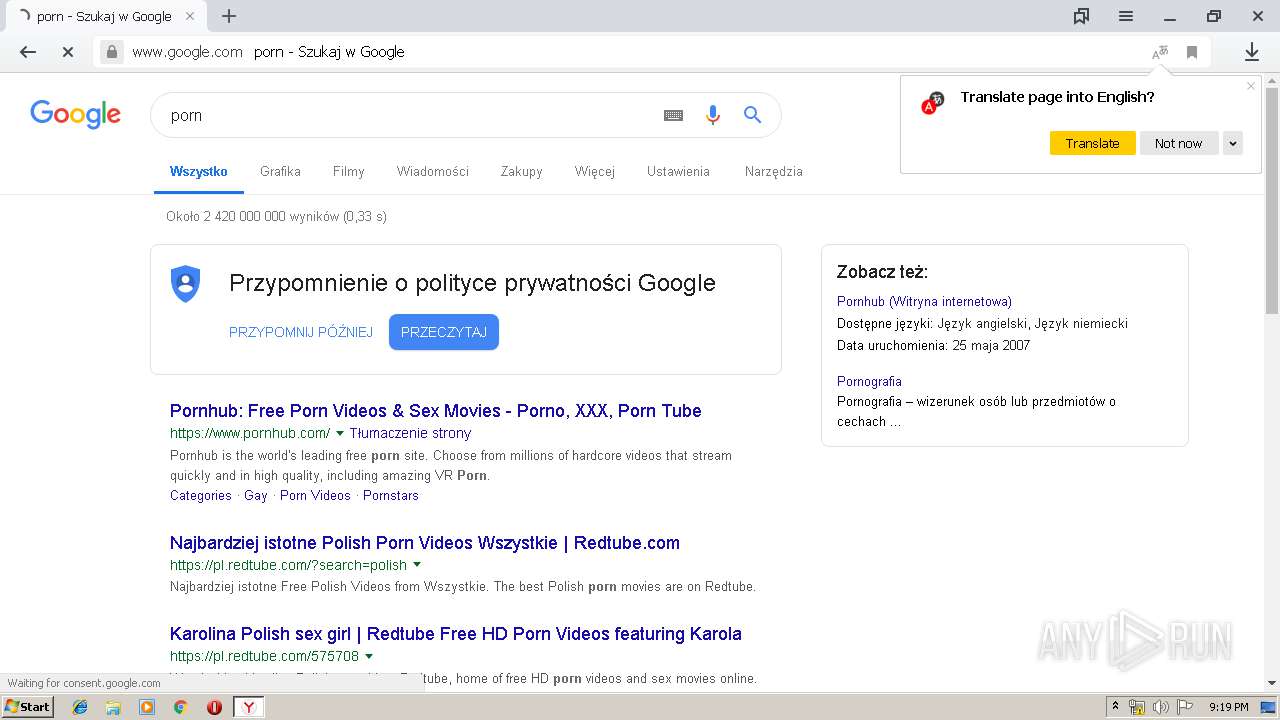
3224 | browser.exe | GET | 301 | 216.58.206.14:80 | http://google.com/ | US | html | 219 b | malicious |
3044 | service_update.exe | GET | 200 | 104.18.21.226:80 | http://ocsp2.globalsign.com/gscodesigng3/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBTHTu2Y6Nr%2FMkfa3PrlxnwonnIpxQQUs9Pm1XFWfTlYs3jSK7j3oR%2F9S5sCDGUxOJI7m%2BYpSWV%2FXQ%3D%3D | US | der | 1.50 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3904 | Yandex.exe | 93.158.134.82:443 | api.browser.yandex.ru | YANDEX LLC | RU | whitelisted |
3904 | Yandex.exe | 213.180.193.14:443 | clck.yandex.ru | YANDEX LLC | RU | whitelisted |
3904 | Yandex.exe | 87.250.250.221:443 | cache-default99v.cdn.yandex.net | YANDEX LLC | RU | whitelisted |
3904 | Yandex.exe | 37.140.166.230:443 | cache-default06h.cdn.yandex.net | YANDEX LLC | RU | whitelisted |
3904 | Yandex.exe | 37.140.166.226:443 | cache-default02h.cdn.yandex.net | YANDEX LLC | RU | whitelisted |
3904 | Yandex.exe | 37.140.166.229:443 | cache-default05h.cdn.yandex.net | YANDEX LLC | RU | whitelisted |
3904 | Yandex.exe | 37.140.166.227:443 | cache-default03h.cdn.yandex.net | YANDEX LLC | RU | whitelisted |
3904 | Yandex.exe | 5.45.205.221:443 | cache-default99i.cdn.yandex.net | YANDEX LLC | RU | whitelisted |
3904 | Yandex.exe | 37.140.166.228:443 | cache-default04h.cdn.yandex.net | YANDEX LLC | RU | whitelisted |
3904 | Yandex.exe | 5.45.205.245:443 | download.cdn.yandex.net | YANDEX LLC | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download.cdn.yandex.net |
| whitelisted |
api.browser.yandex.ru |
| whitelisted |
cache-default99v.cdn.yandex.net |
| whitelisted |
clck.yandex.ru |
| whitelisted |
cache-default06h.cdn.yandex.net |
| whitelisted |
cache-default02h.cdn.yandex.net |
| whitelisted |
cache-default03h.cdn.yandex.net |
| whitelisted |
cache-default05h.cdn.yandex.net |
| whitelisted |
cache-default04h.cdn.yandex.net |
| whitelisted |
cache-default99i.cdn.yandex.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3904 | Yandex.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
Process | Message |
|---|---|
clidmgr.exe | GetSidFromEnumSess(): i = 0 : szUserName = Administrator, szDomain = USER-PC, dwSessionId = 0
|
clidmgr.exe | GetSidFromEnumSess(): i = 0 : szUserName = Administrator, szDomain = USER-PC, dwSessionId = 0
|
clidmgr.exe | GetSidFromEnumSess(): LsaEnumerateLogonSessions() lpszSid = S-1-5-21-1302019708-1500728564-335382590-1000
|
clidmgr.exe | GetSidFromEnumSess(): LsaEnumerateLogonSessions() lpszSid = S-1-5-21-1302019708-1500728564-335382590-1000
|
clidmgr.exe | GetLoggedCreds_WTSSessionInfo(): szUserName = admin, szDomain = USER-PC, dwSessionId = 1
|
clidmgr.exe | GetSidFromEnumSess(): i = 0 : szUserName = Administrator, szDomain = USER-PC, dwSessionId = 0
|
clidmgr.exe | GetSidFromEnumSess(): ProfileImagePath(1) = C:\Users\admin
|
clidmgr.exe | GetSidFromEnumSess(): LsaEnumerateLogonSessions() lpszSid = S-1-5-21-1302019708-1500728564-335382590-1000
|
clidmgr.exe | GetLoggedCreds_WTSSessionInfo(): szUserName = admin, szDomain = USER-PC, dwSessionId = 1
|
clidmgr.exe | GetSidFromEnumSess(): i = 0 : szUserName = Administrator, szDomain = USER-PC, dwSessionId = 0
|