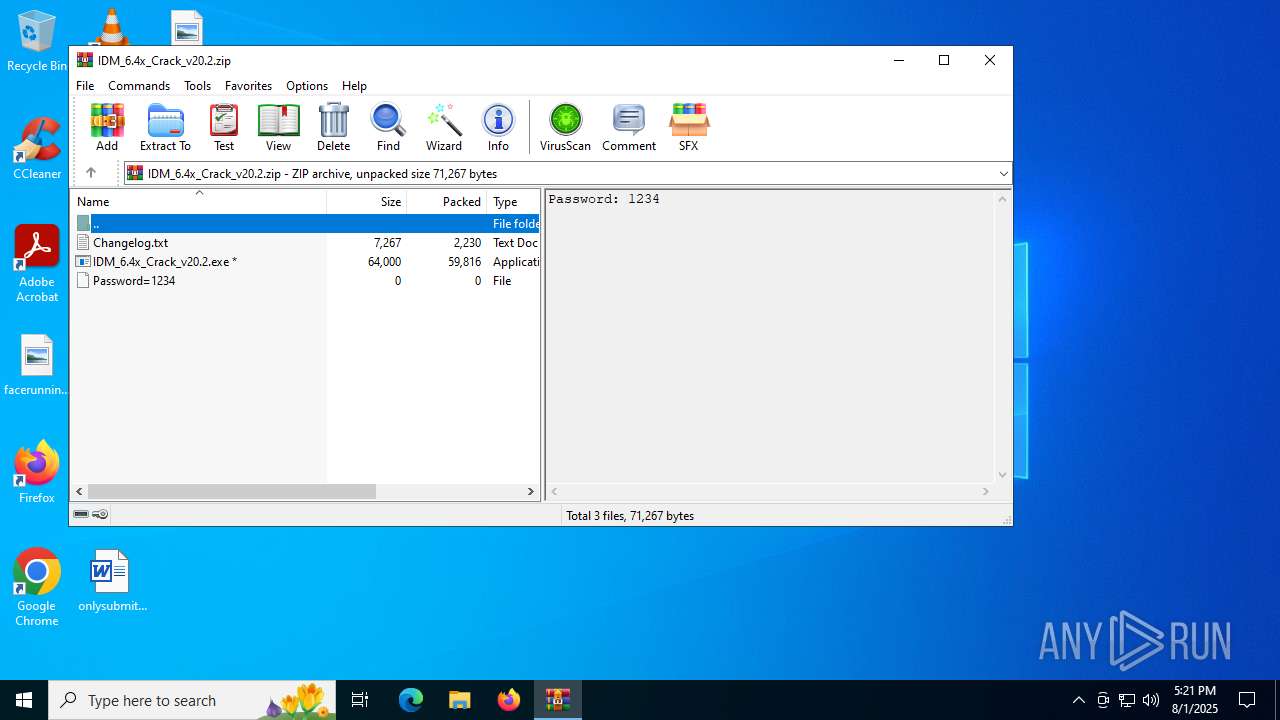
| File name: | IDM_6.4x_Crack_v20.2.zip |
| Full analysis: | https://app.any.run/tasks/6631eaf7-b44f-4107-853f-916914ddf7bf |
| Verdict: | Malicious activity |
| Analysis date: | August 01, 2025, 17:21:26 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
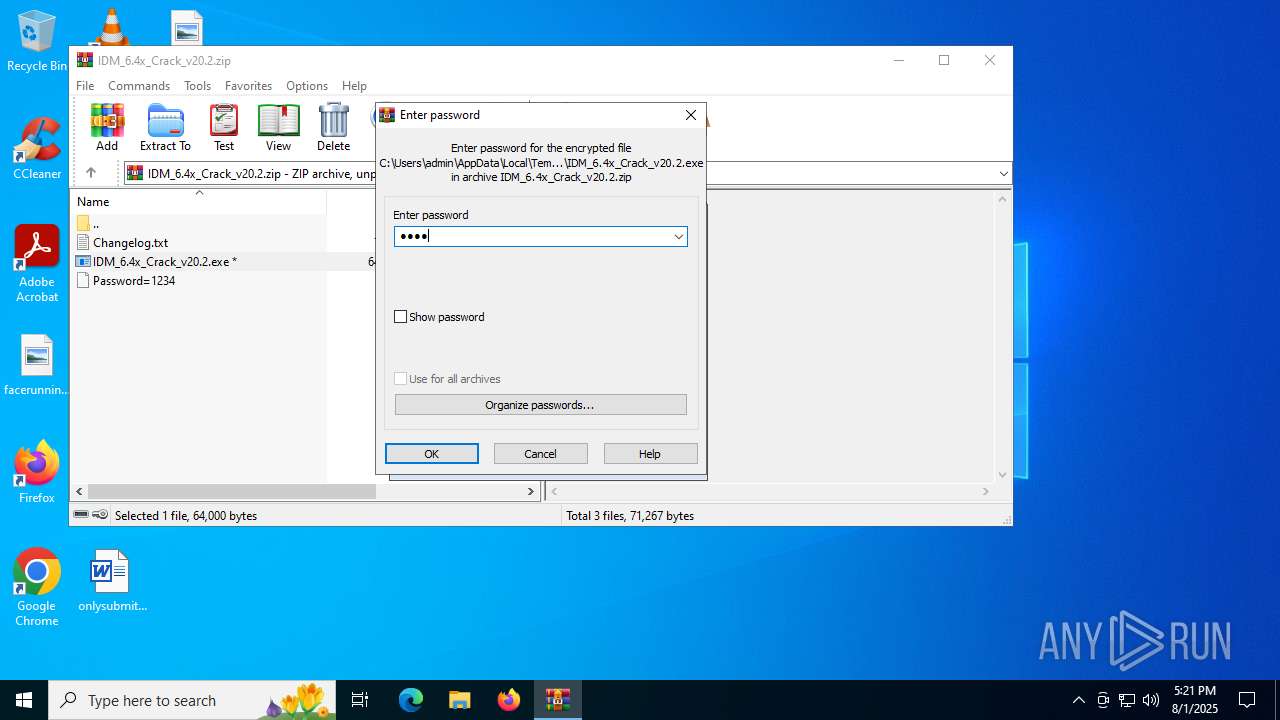
| File info: | Zip archive data, at least v2.0 to extract, compression method=AES Encrypted |
| MD5: | DF11314121570C3420D0E161366CBC12 |
| SHA1: | 47E2546D9EB4591ECA512ADB145D1BD0B2BD2AB0 |
| SHA256: | DD3C5782032EF7244DF8F00107B1A9035720EA843F8482429F1C312DA004A276 |
| SSDEEP: | 1536:LbB+v3vnJBFeOKv4PE2/4On8zYp/K9obakAKzgW:L0nJDyv4PERYRK9obaRTW |
MALICIOUS
Opens an HTTP connection (SCRIPT)
- wscript.exe (PID: 1352)
Creates internet connection object (SCRIPT)
- wscript.exe (PID: 1352)
Sends HTTP request (SCRIPT)
- wscript.exe (PID: 1352)
Deletes a file (SCRIPT)
- wscript.exe (PID: 1352)
SUSPICIOUS
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 1352)
Generic archive extractor
- WinRAR.exe (PID: 1668)
The process executes VB scripts
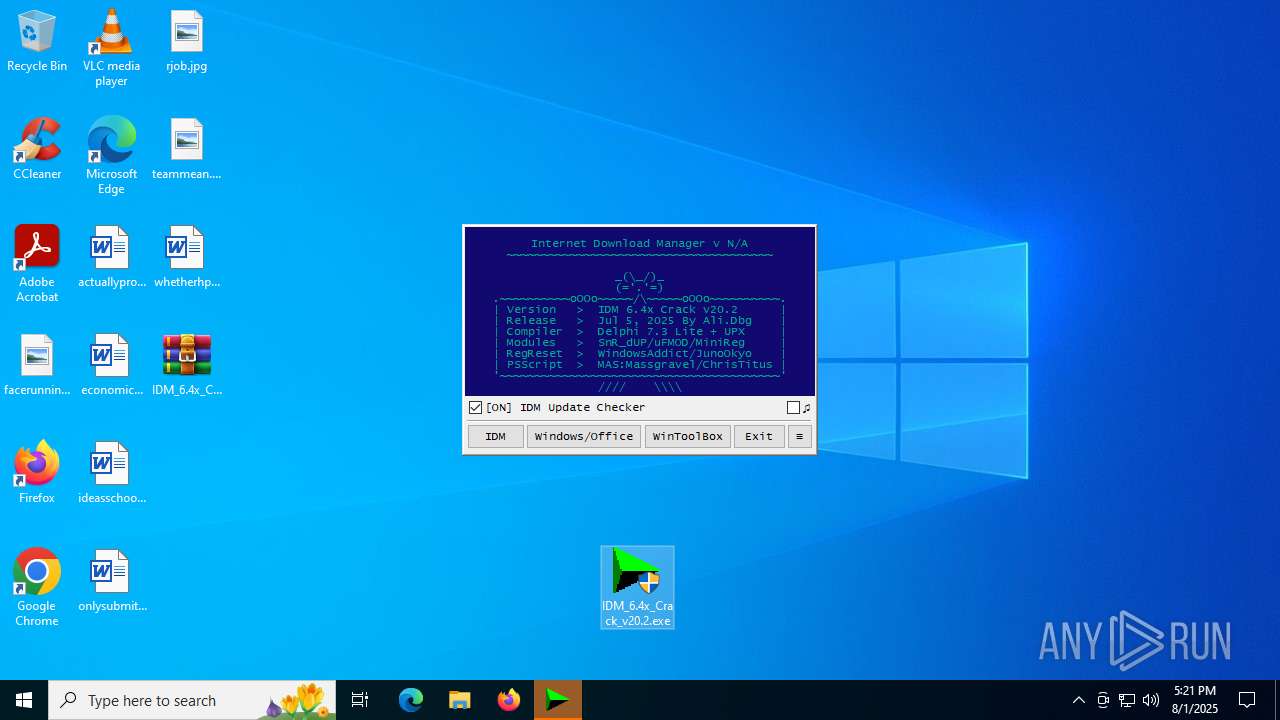
- IDM_6.4x_Crack_v20.2.exe (PID: 3844)
Adds, changes, or deletes HTTP request header (SCRIPT)
- wscript.exe (PID: 1352)
Executing commands from a ".bat" file
- IDM_6.4x_Crack_v20.2.exe (PID: 3844)
- cmd.exe (PID: 4400)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 4400)
- cmd.exe (PID: 7016)
- IDM_6.4x_Crack_v20.2.exe (PID: 3844)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4400)
- cmd.exe (PID: 4552)
- cmd.exe (PID: 6216)
Application launched itself
- cmd.exe (PID: 7016)
- cmd.exe (PID: 4400)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 4400)
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 4400)
Hides command output
- cmd.exe (PID: 6216)
- cmd.exe (PID: 1936)
Gets full path of the running script (SCRIPT)
- wscript.exe (PID: 1352)
Sets XML DOM element text (SCRIPT)
- wscript.exe (PID: 1352)
Uses REG/REGEDIT.EXE to modify registry
- IDM_6.4x_Crack_v20.2.exe (PID: 3844)
- cmd.exe (PID: 4400)
- cmd.exe (PID: 1936)
Starts application with an unusual extension
- cmd.exe (PID: 4400)
INFO
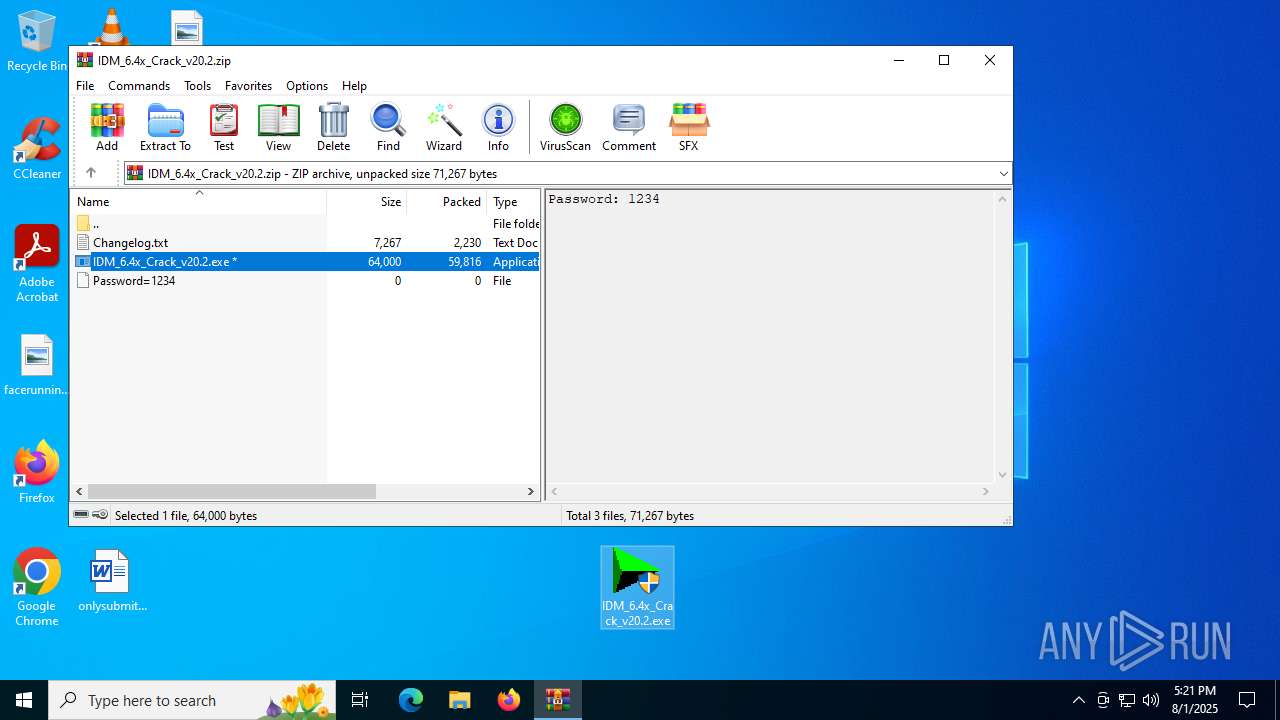
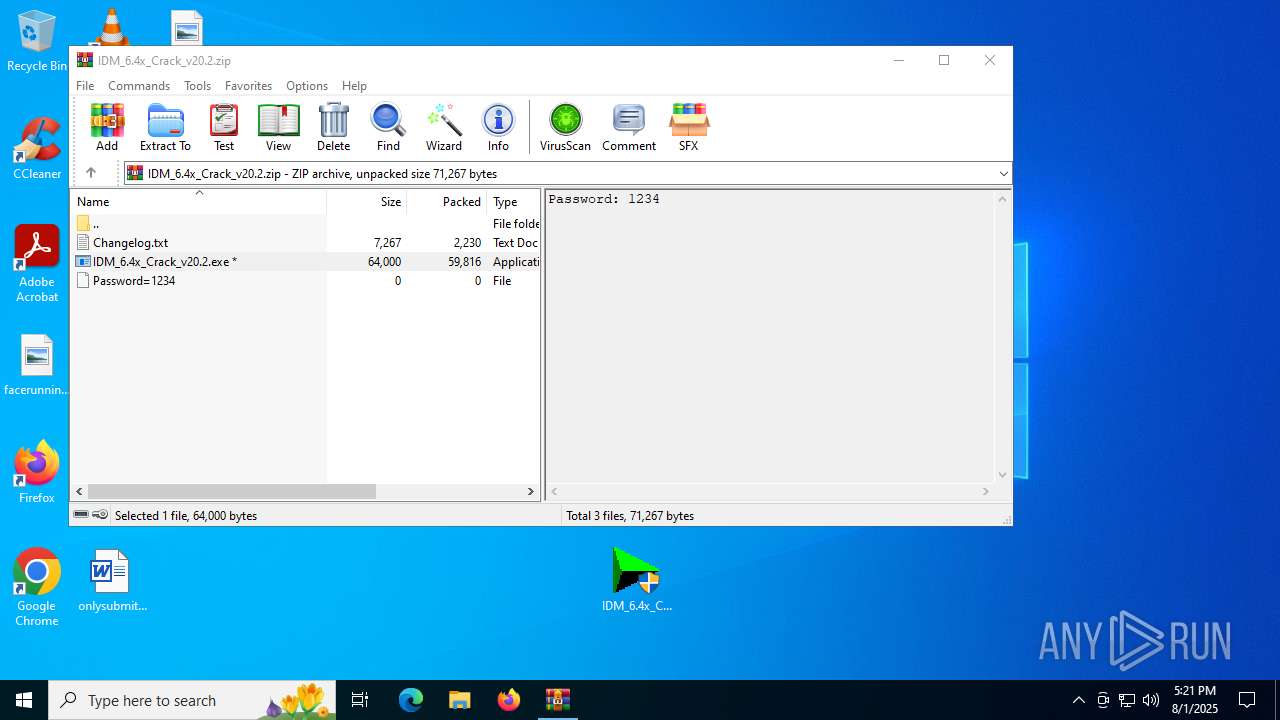
Manual execution by a user
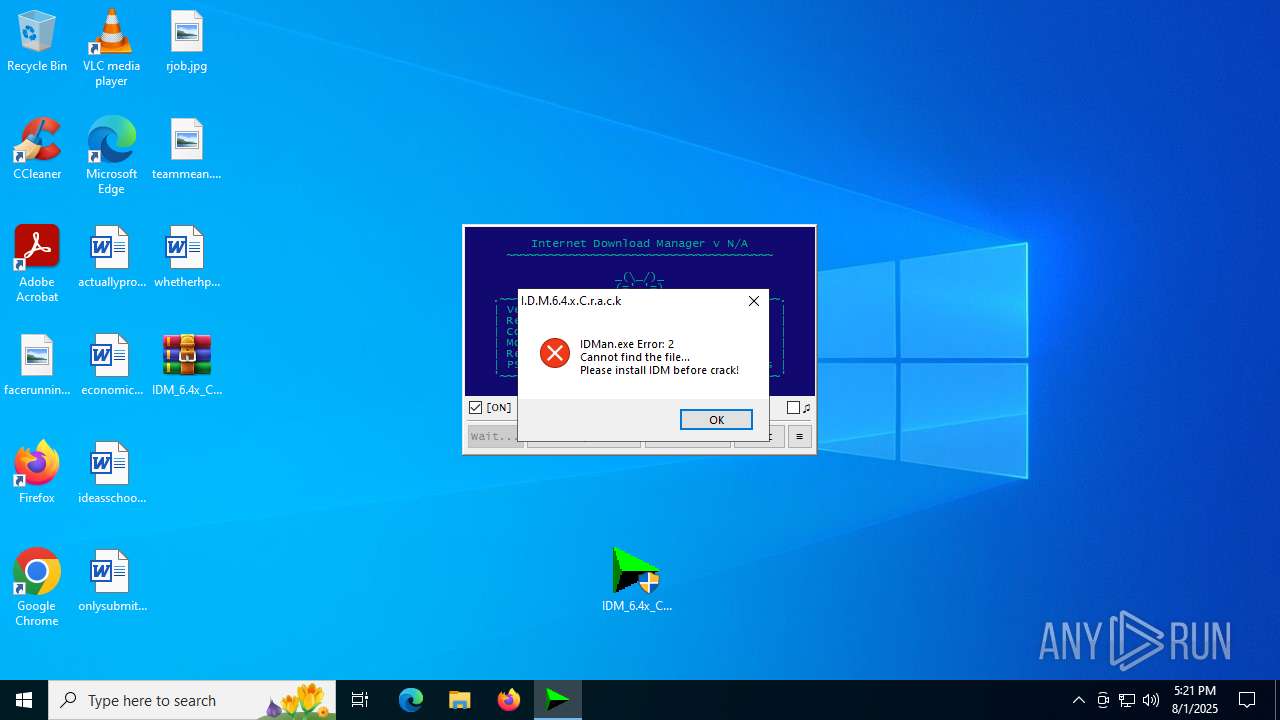
- IDM_6.4x_Crack_v20.2.exe (PID: 3844)
- IDM_6.4x_Crack_v20.2.exe (PID: 4156)
Checks supported languages
- IDM_6.4x_Crack_v20.2.exe (PID: 3844)
- chcp.com (PID: 2492)
Creates files or folders in the user directory
- IDM_6.4x_Crack_v20.2.exe (PID: 3844)
Reads the computer name
- IDM_6.4x_Crack_v20.2.exe (PID: 3844)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1668)
Checks proxy server information
- wscript.exe (PID: 1352)
Create files in a temporary directory
- IDM_6.4x_Crack_v20.2.exe (PID: 3844)
- reg.exe (PID: 1100)
Checks operating system version
- cmd.exe (PID: 4400)
Checks whether the specified file exists (POWERSHELL)
- powershell.exe (PID: 4156)
- powershell.exe (PID: 6584)
Changes the display of characters in the console
- cmd.exe (PID: 4400)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2025:07:05 16:10:10 |
| ZipCRC: | 0xc46c2076 |
| ZipCompressedSize: | 59816 |
| ZipUncompressedSize: | 64000 |
| ZipFileName: | IDM_6.4x_Crack_v20.2.exe |
Total processes
192
Monitored processes
57
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 868 | reg delete HKU\S-1-5-21-1693682860-607145093-2874071422-1001\IAS_TEST /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 892 | reg query "HKCU\Software\DownloadManager" "/v" "Email" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 984 | reg add HKU\S-1-5-21-1693682860-607145093-2874071422-1001\Software\Classes\Wow6432Node\CLSID\IAS_TEST | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1036 | reg query "HKCU\Software\DownloadManager" "/v" "LastCheckQU" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1068 | reg delete HKCU\IAS_TEST /f | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1100 | reg export HKCU\Software\Classes\Wow6432Node\CLSID "C:\WINDOWS\Temp\_Backup_HKCU_CLSID_20250801-172156294.reg" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1160 | reg.exe import C:\Users\admin\AppData\Local\Temp\IDMRegClean.reg | C:\Windows\SysWOW64\reg.exe | — | IDM_6.4x_Crack_v20.2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1352 | wscript.exe "C:\Users\admin\AppData\Local\Temp\\CRK_UPDT.vbs" "https://idm.0dy.ir/" "Version" "Download_URL" "20.2" "Crack" "C:\Program Files\Google\Chrome\Application\chrome.exe" silent | C:\Windows\SysWOW64\wscript.exe | IDM_6.4x_Crack_v20.2.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1352 | reg query "HKCU\Software\DownloadManager" "/v" "tvfrdt" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1468 | reg query HKU\S-1-5-21-1693682860-607145093-2874071422-1001\Software\Classes\Wow6432Node\CLSID\IAS_TEST | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
25 468
Read events
25 406
Write events
47
Delete events
15
Modification events
| (PID) Process: | (1668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (1668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (1668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (1668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\IDM_6.4x_Crack_v20.2.zip | |||
| (PID) Process: | (1668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1668) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3844) IDM_6.4x_Crack_v20.2.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows Script Host\Settings |
| Operation: | write | Name: | Enabled |
Value: 1 | |||
Executable files
1
Suspicious files
3
Text files
18
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1668 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb1668.20288\IDM_6.4x_Crack_v20.2.exe | executable | |
MD5:689F245046CA30CE27203DE3EDEC8327 | SHA256:D80B7BD24276190D25B7FEE3A09530C5A9736306DA83842D37A4D52D92BBA897 | |||
| 1352 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | binary | |
MD5:C5131AFF4F37E87F202253D5620CE8EB | SHA256:FB023CFE525658DC622EE090FF24590BA198CDE695B2BB97C6C1E58FF0A40980 | |||
| 1352 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\8B2B9A00839EED1DFDCCC3BFC2F5DF12 | der | |
MD5:CA8A9BDCA7AD59F5C8B7E1AA63160039 | SHA256:81B7FA53B692B4D26E2E8943F2DDA2F9563CFCB0E11F48679EB2BE4F8C375B90 | |||
| 3844 | IDM_6.4x_Crack_v20.2.exe | C:\Users\admin\AppData\Local\Temp\IDM_UPDT.vbs | text | |
MD5:B91C1157D6F1E605CC965D092551B307 | SHA256:92FE72CCEB630C7EFF3B2D3BED9C6969F53E5B9DFF1F481888754E59B3C76AB7 | |||
| 1352 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B46811C17859FFB409CF0E904A4AA8F8 | der | |
MD5:1FBB37F79B317A9A248E7C4CE4F5BAC5 | SHA256:9BF639C595FE335B6F694EE35990BEFD2123F5E07FD1973FF619E3FC88F5F49F | |||
| 3844 | IDM_6.4x_Crack_v20.2.exe | C:\Users\admin\AppData\Roaming\WinRAR\rarreg.key | text | |
MD5:CC72935D4E4BD54DB0ED6BF4701FDC9E | SHA256:2ABE74BB821BA46762AFDB23EAC95454EC7155D5379E3CD56385D900C34CB1BF | |||
| 1352 | wscript.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\B46811C17859FFB409CF0E904A4AA8F8 | binary | |
MD5:CDC33DC007DD4A99797813A406CB6AC9 | SHA256:3BF526FC5C3E1E35D75667BF778E8691A4D28054E8B1246F024DC21FE155EE73 | |||
| 3844 | IDM_6.4x_Crack_v20.2.exe | C:\Users\admin\AppData\Local\Temp\CRK_UPDT.vbs | text | |
MD5:B91C1157D6F1E605CC965D092551B307 | SHA256:92FE72CCEB630C7EFF3B2D3BED9C6969F53E5B9DFF1F481888754E59B3C76AB7 | |||
| 4156 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:64DD0EB6DDF7DB44C22F48E33653ECDB | SHA256:35EA448FA64E55D066076B8AD7365DEE52412F8CD3B90BB69659BA958E08FA1F | |||
| 4156 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_b5opsiky.jsv.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
22
DNS requests
17
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1352 | wscript.exe | GET | 200 | 142.250.186.67:80 | http://c.pki.goog/r/r4.crl | unknown | — | — | whitelisted |
1352 | wscript.exe | GET | 200 | 142.250.186.67:80 | http://c.pki.goog/r/gsr1.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 88.221.110.122:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
3092 | svchost.exe | GET | 200 | 23.196.96.159:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
3488 | SIHClient.exe | GET | 200 | 2.23.10.85:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
3488 | SIHClient.exe | GET | 200 | 2.23.10.85:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.10.85:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2432 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1352 | wscript.exe | 188.114.96.3:443 | idm.0dy.ir | CLOUDFLARENET | NL | unknown |
1352 | wscript.exe | 142.250.186.67:80 | c.pki.goog | GOOGLE | US | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 88.221.110.122:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 2.23.10.85:80 | www.microsoft.com | AKAMAI-AS | CZ | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
idm.0dy.ir |
| unknown |
c.pki.goog |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |