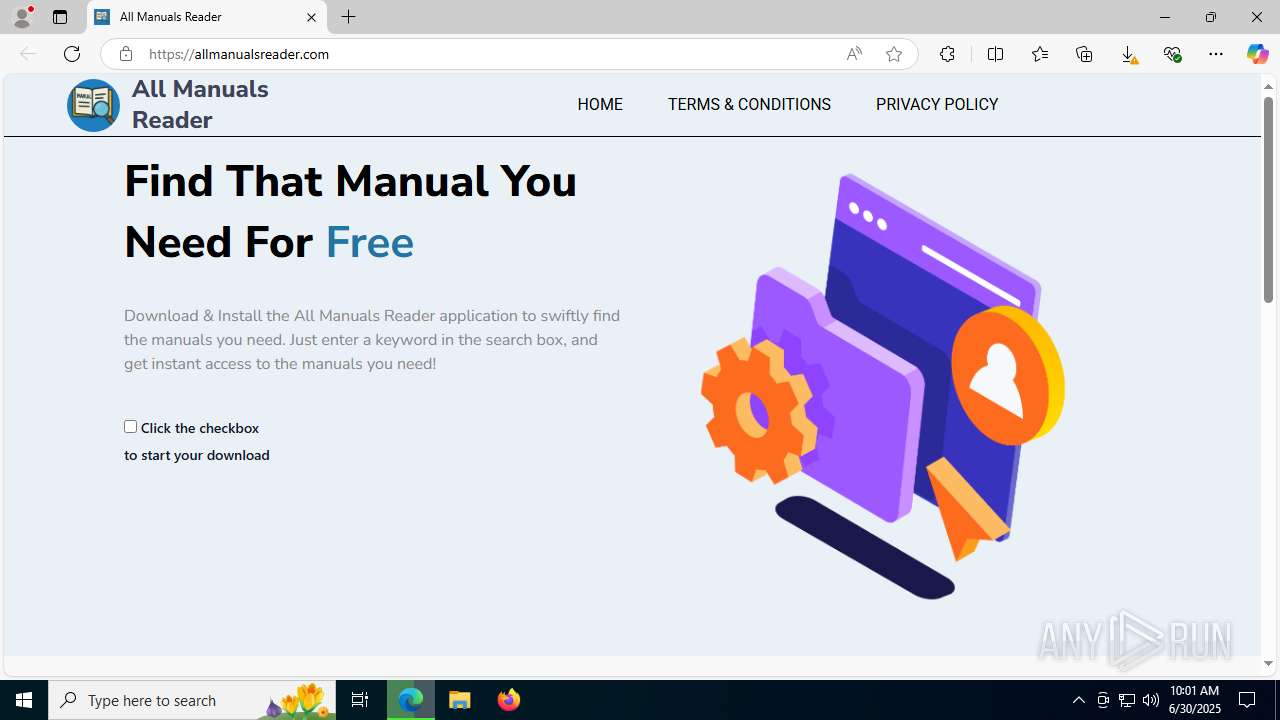
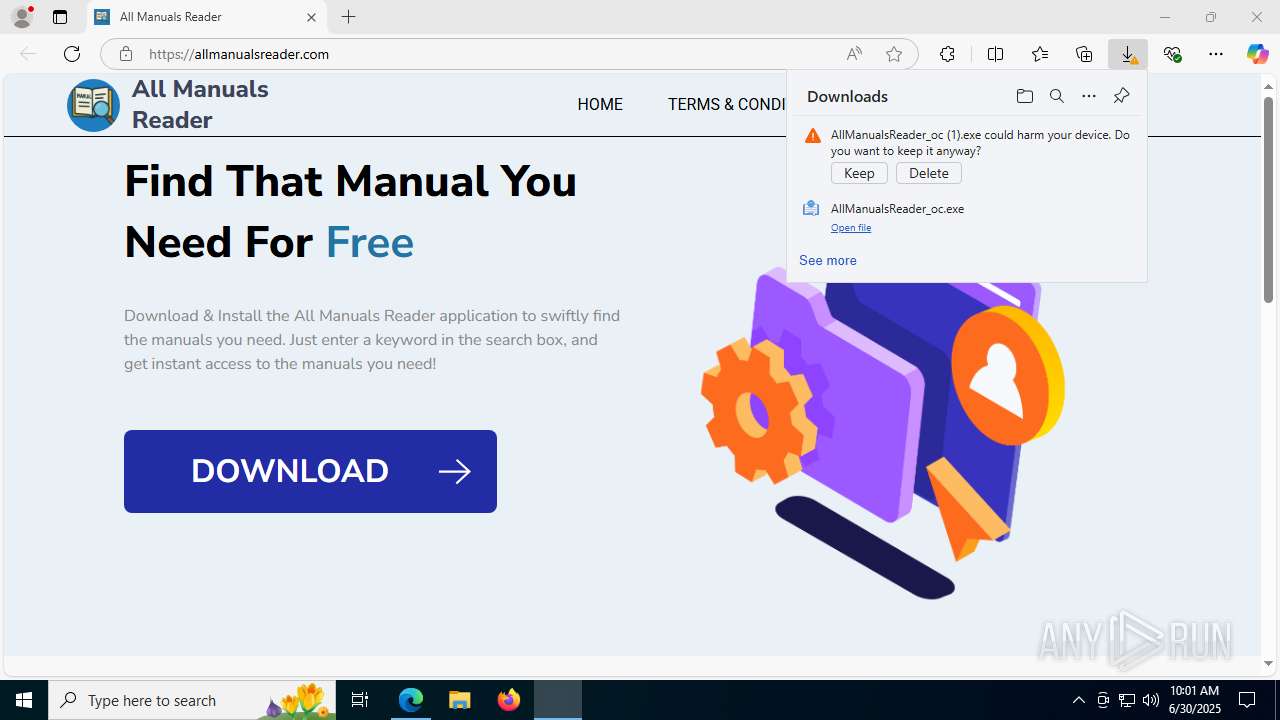
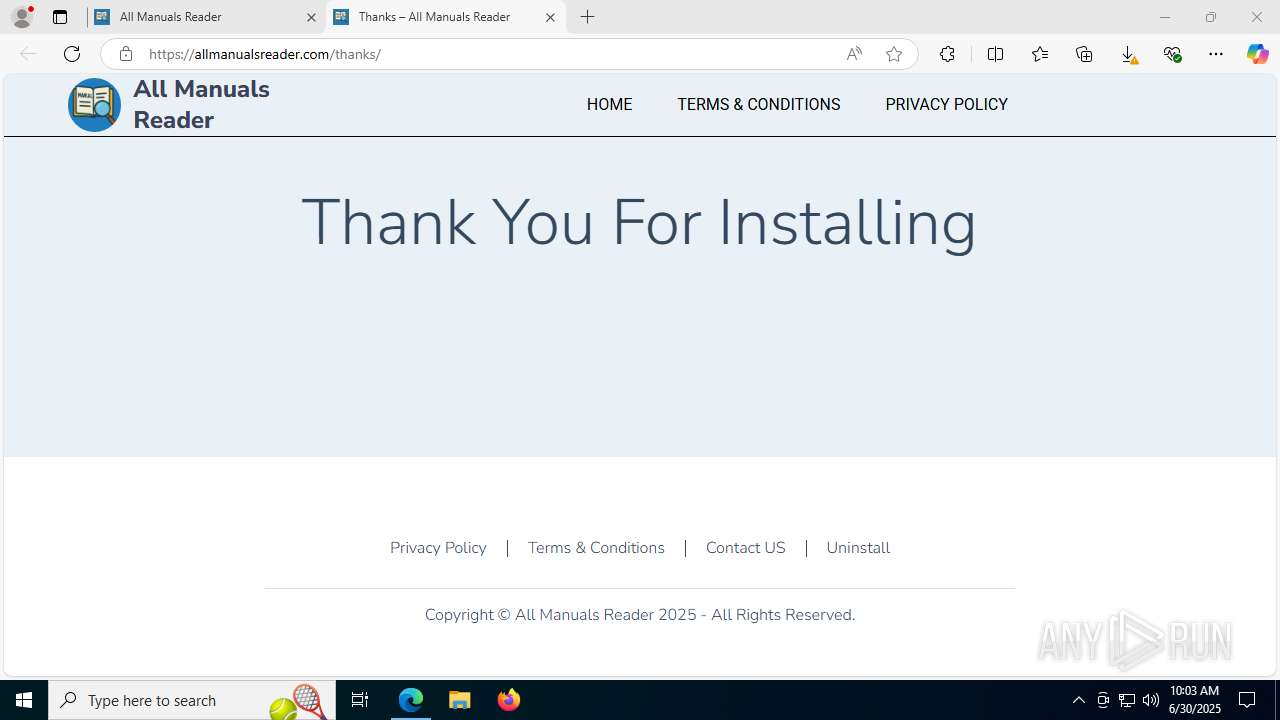
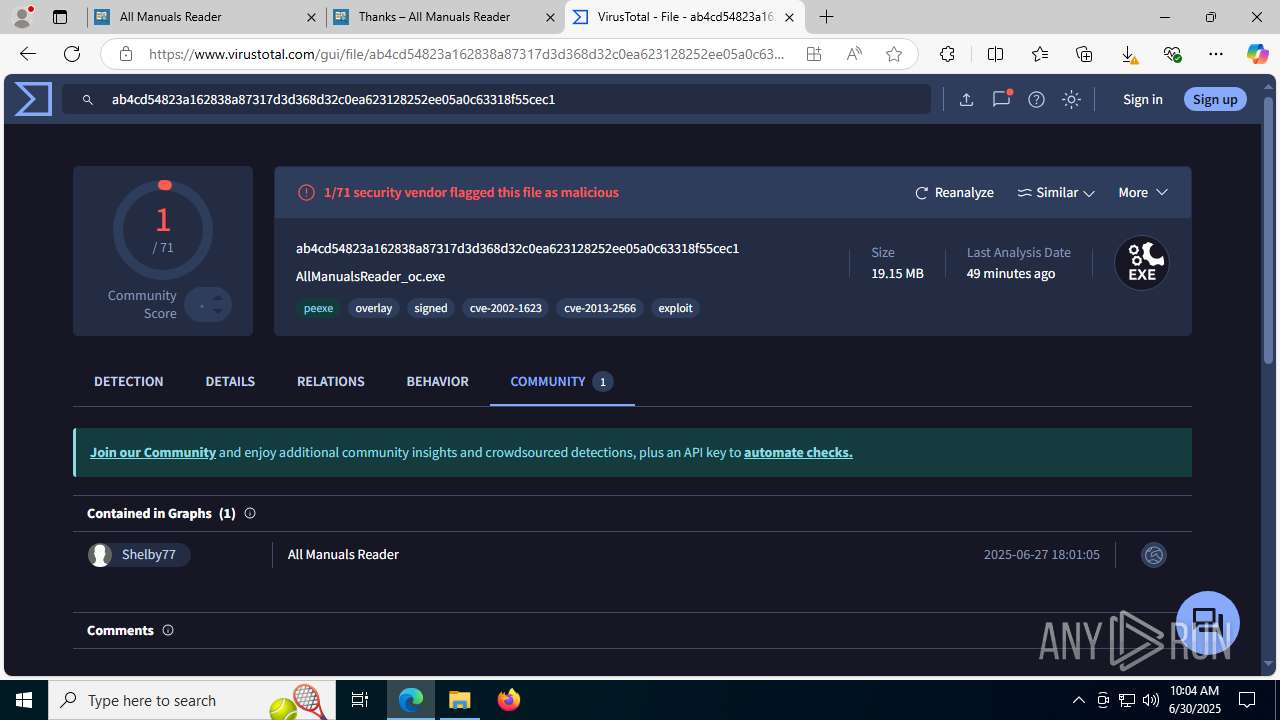
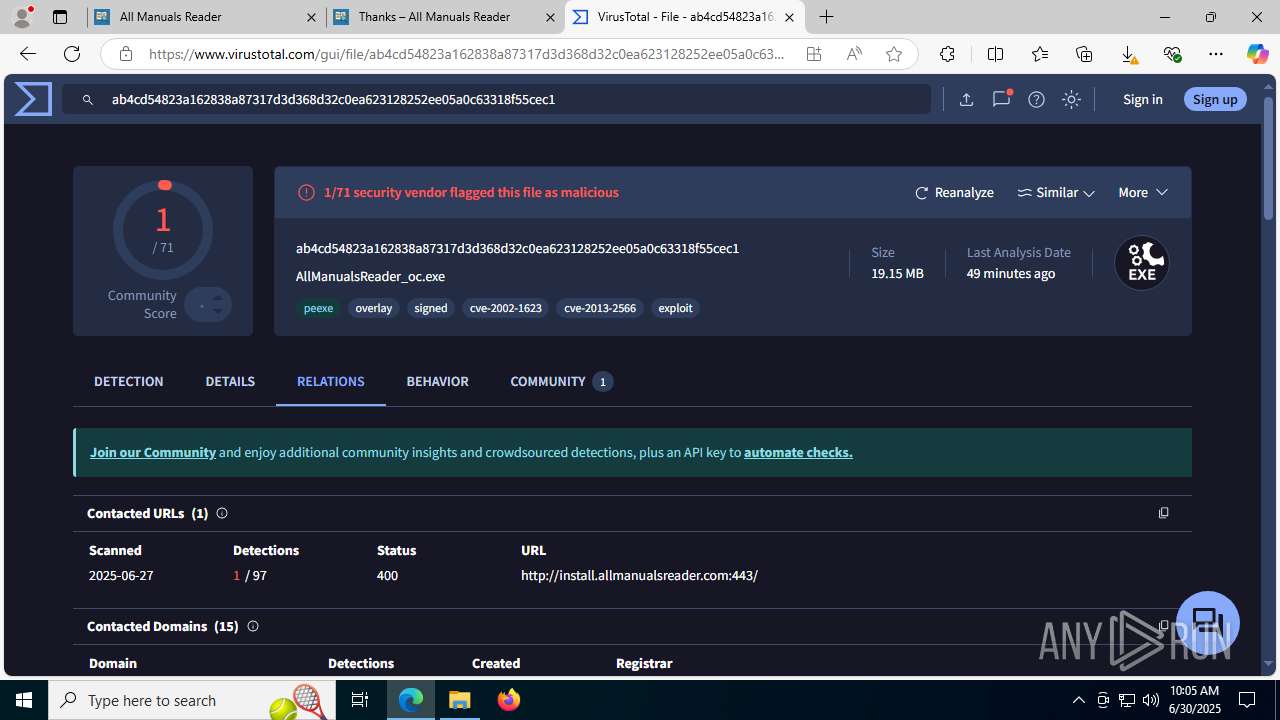
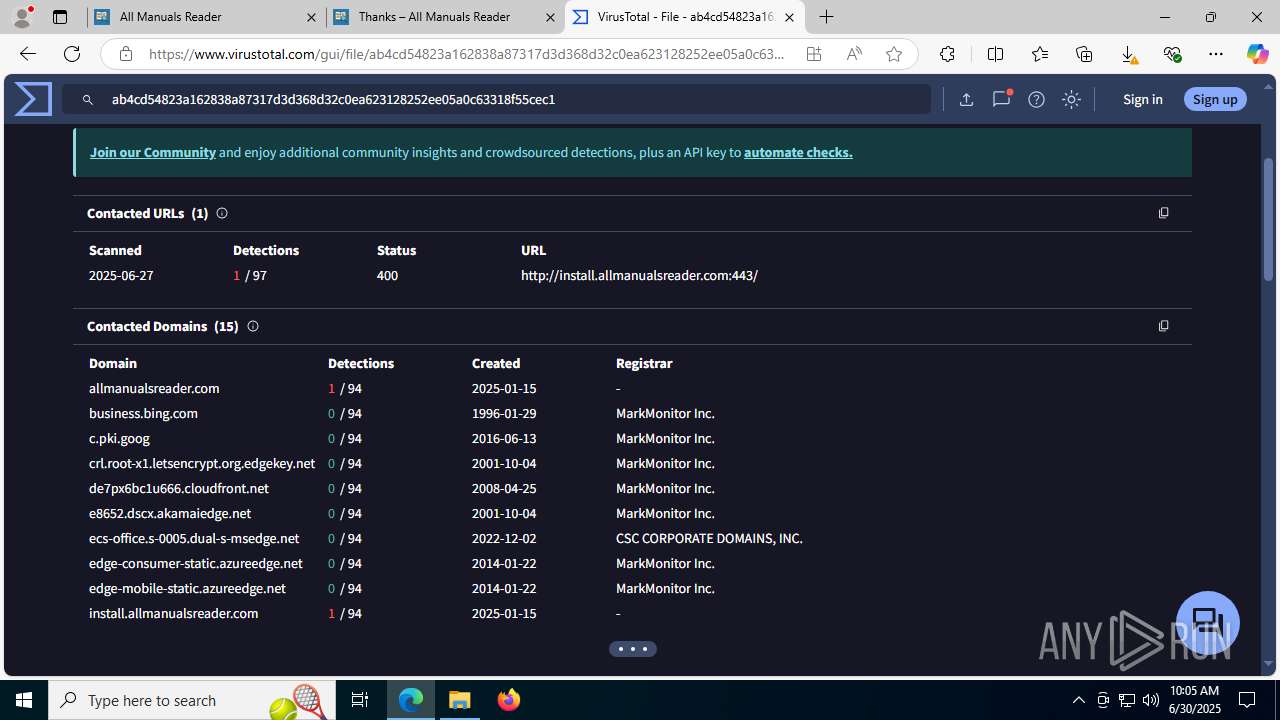
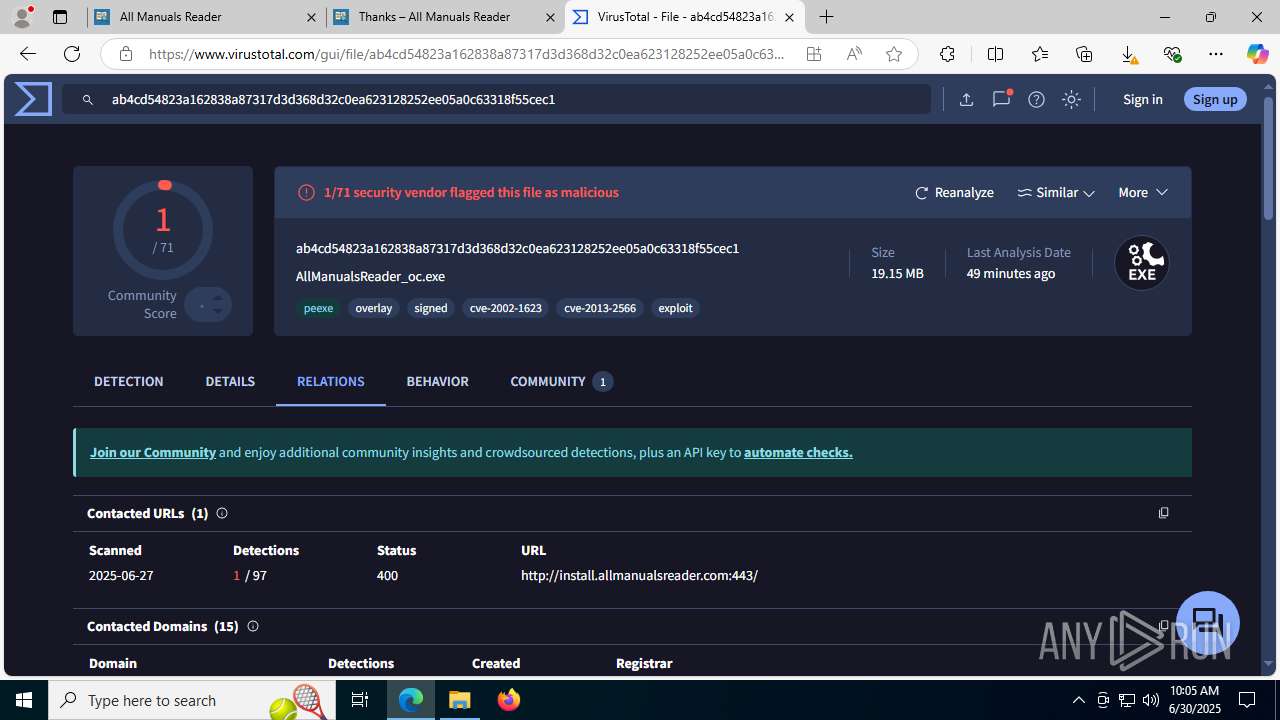
| URL: | allmanualsreader.com |
| Full analysis: | https://app.any.run/tasks/17014ab2-2d43-4e4c-bb28-86f9fe6da65d |
| Verdict: | Malicious activity |
| Analysis date: | June 30, 2025, 10:01:19 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
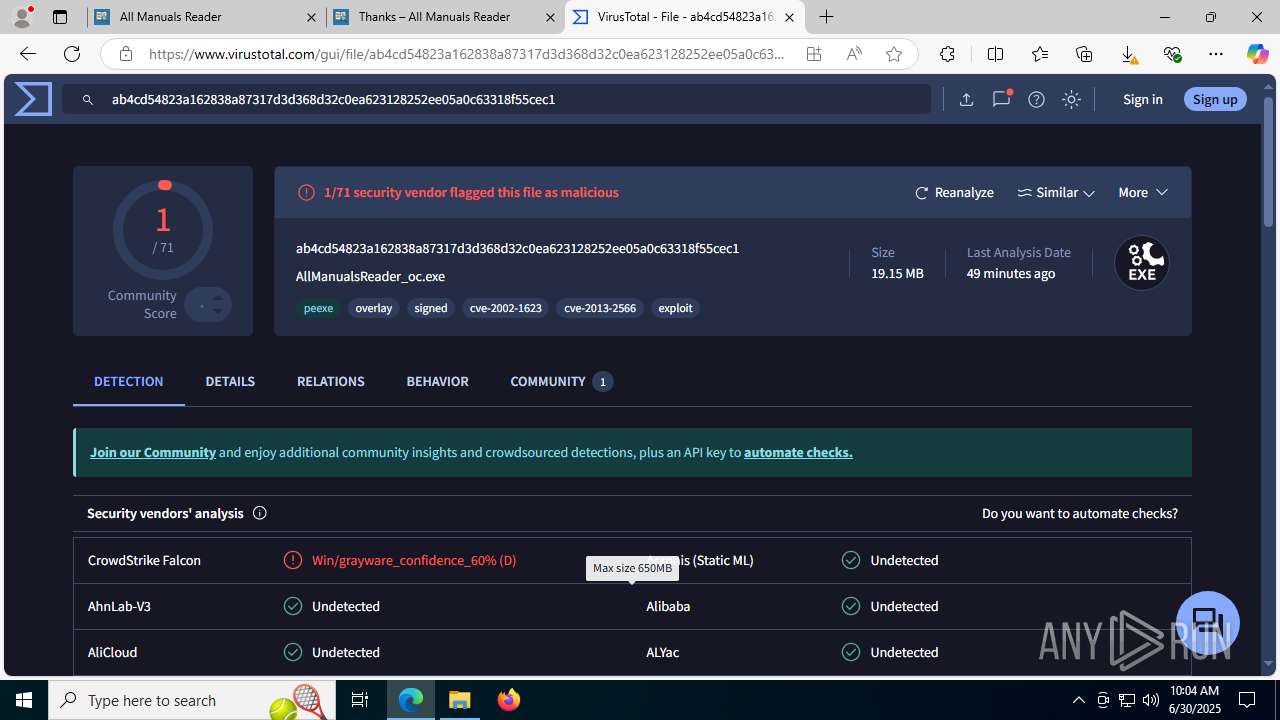
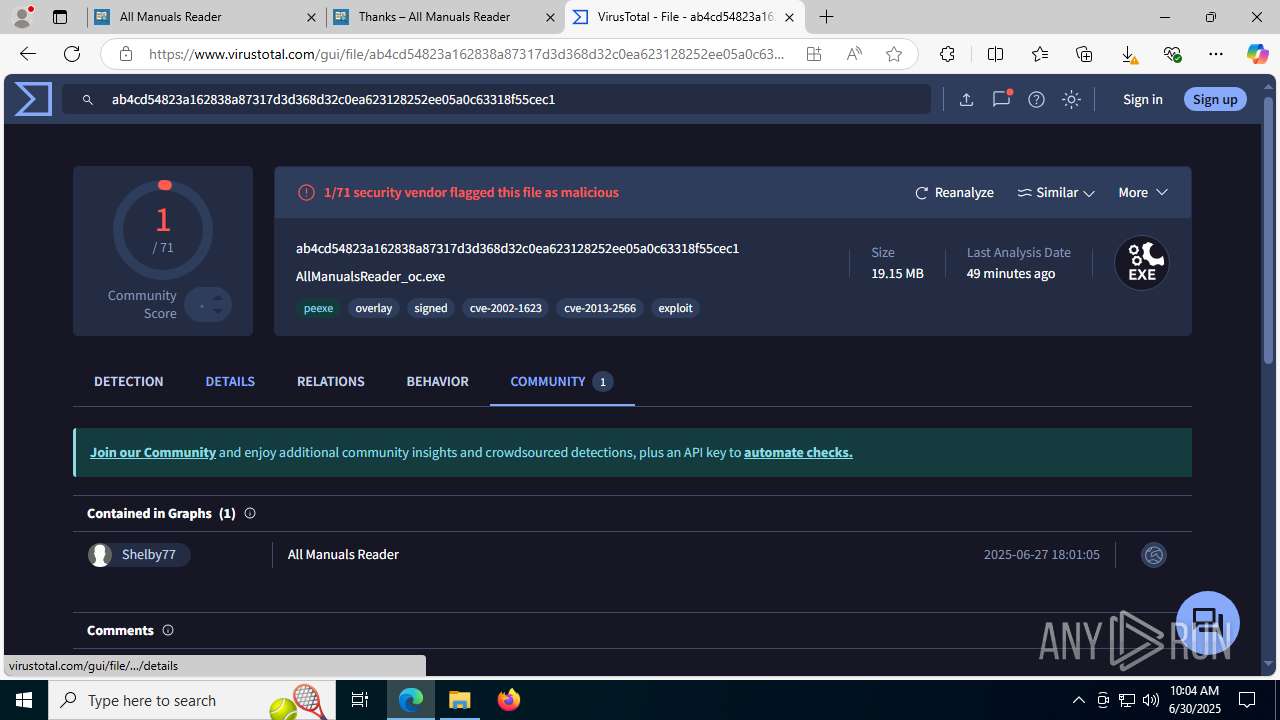
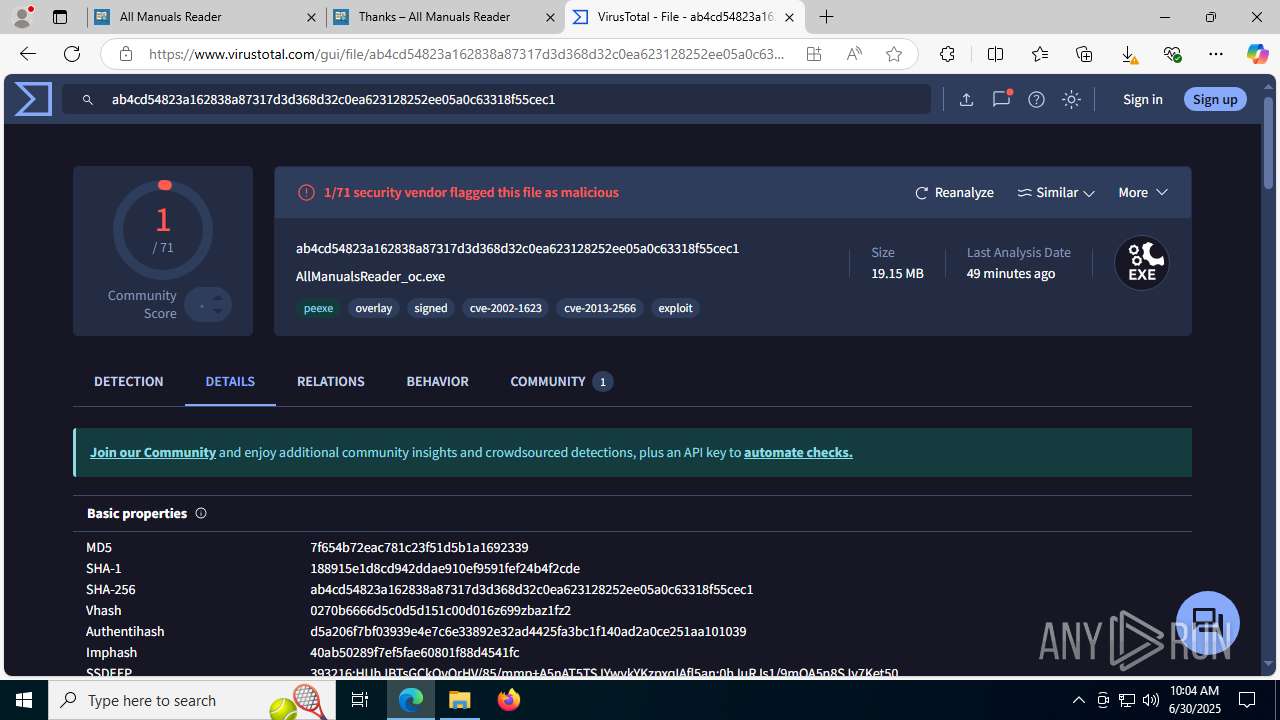
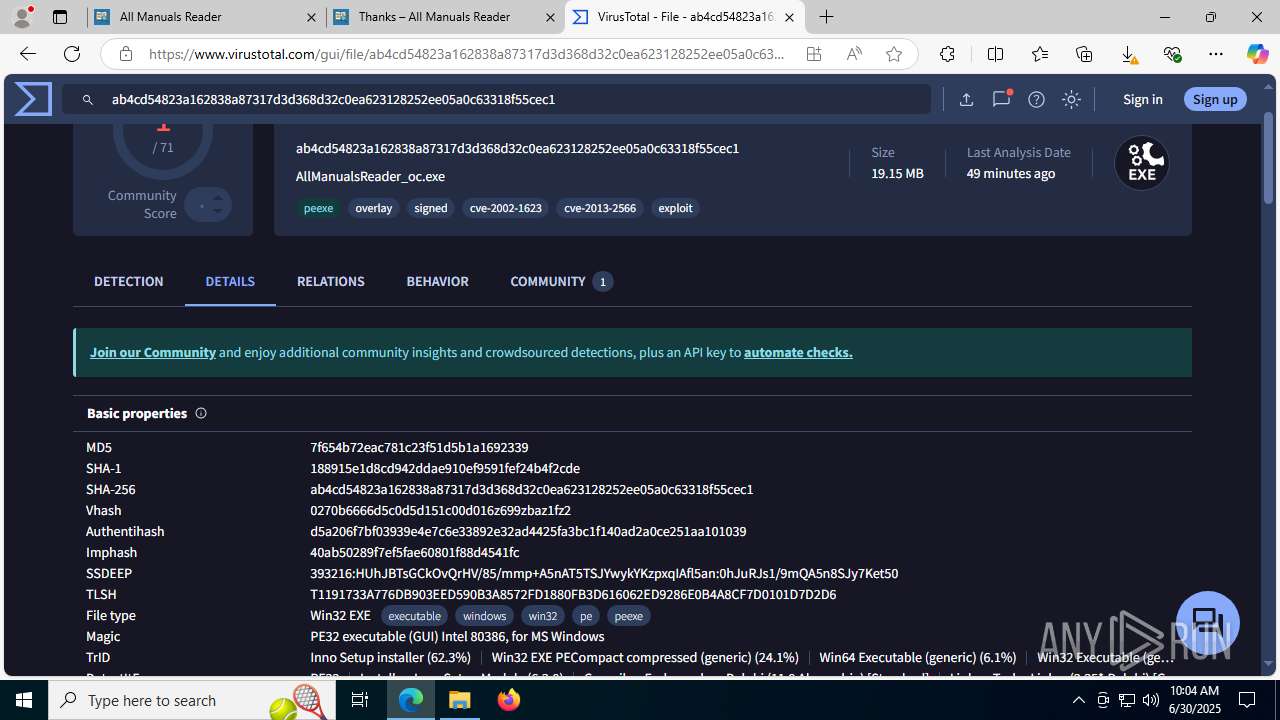
| MD5: | 2B6EC04FC6DD8301153748C64F8B6B76 |
| SHA1: | 4FC890C7C3E8968915E605159E4D63EE72144CCC |
| SHA256: | DD2FAEB64777CFF25DEEC06F0CA47D2732E479B18AF0E44229DC3E935FDB4B85 |
| SSDEEP: | 3:gJ5LWwLGKI:gLGT |
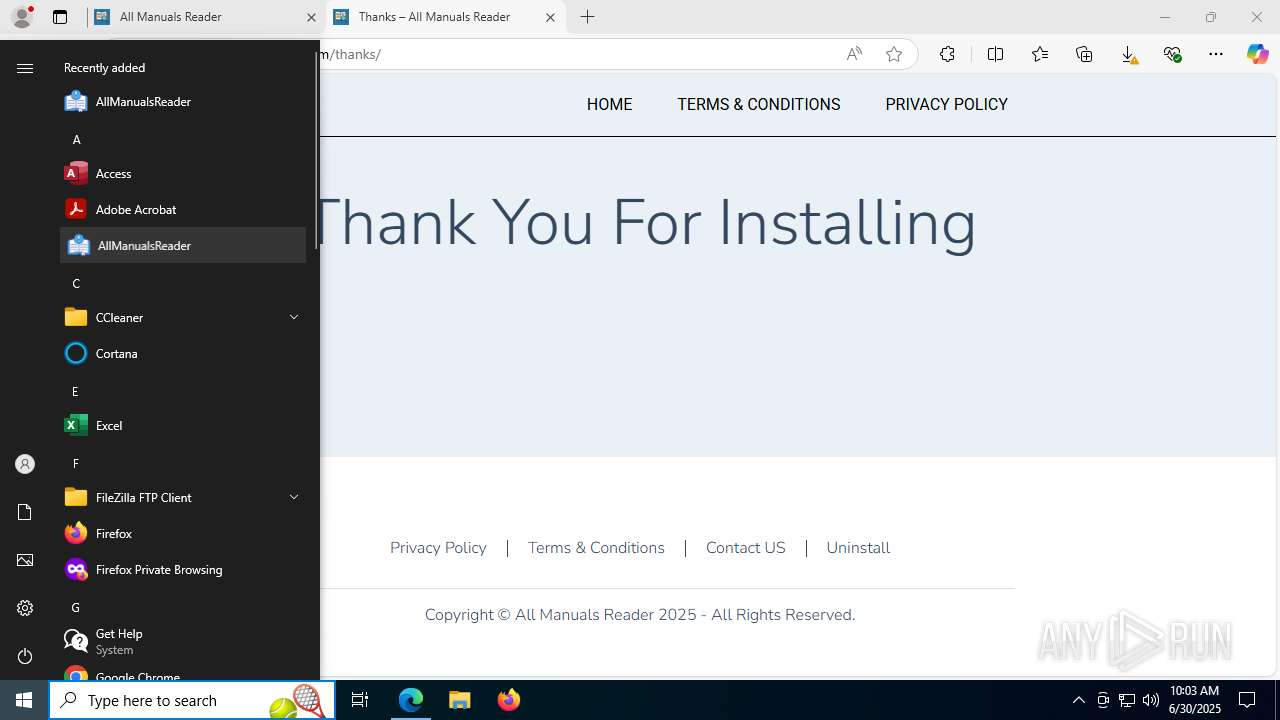
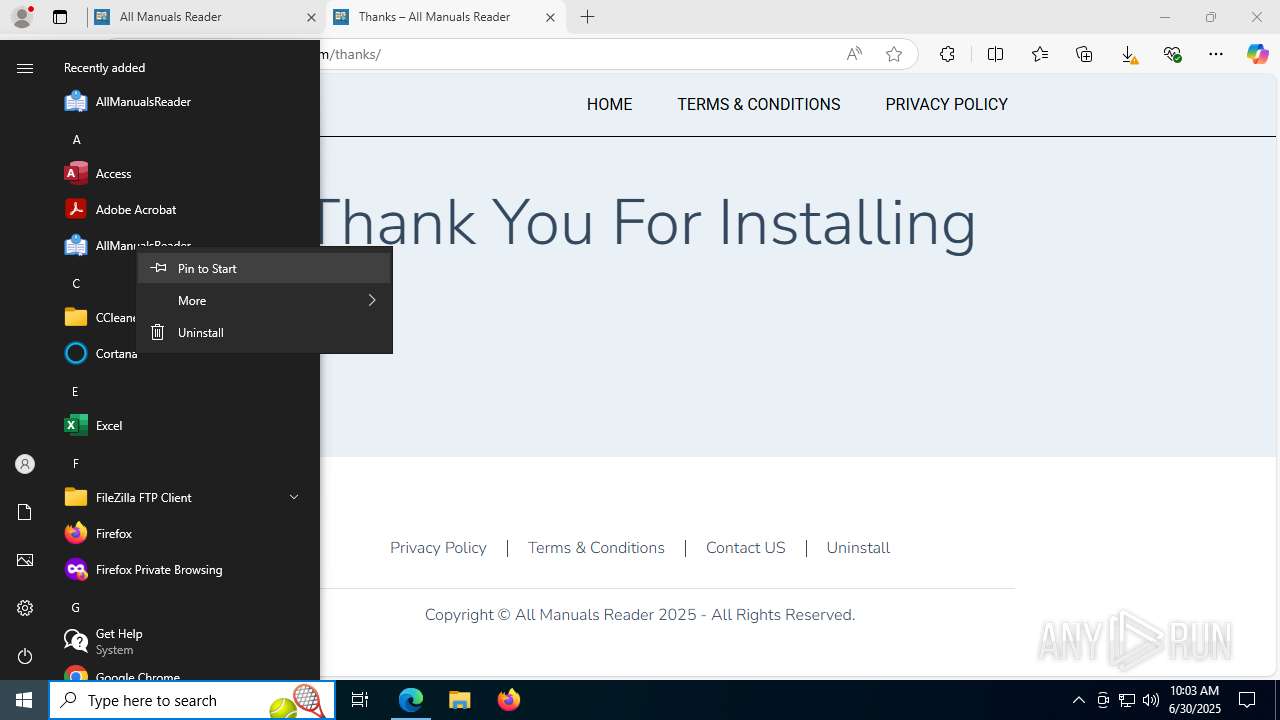
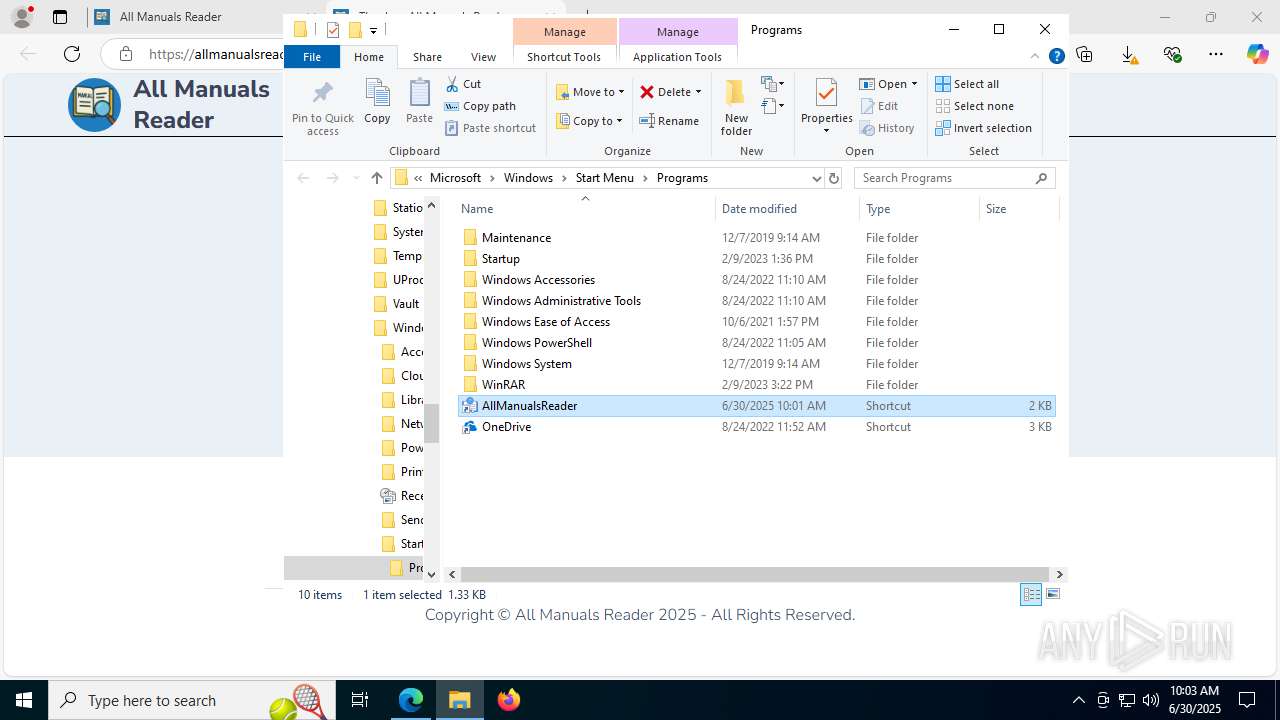
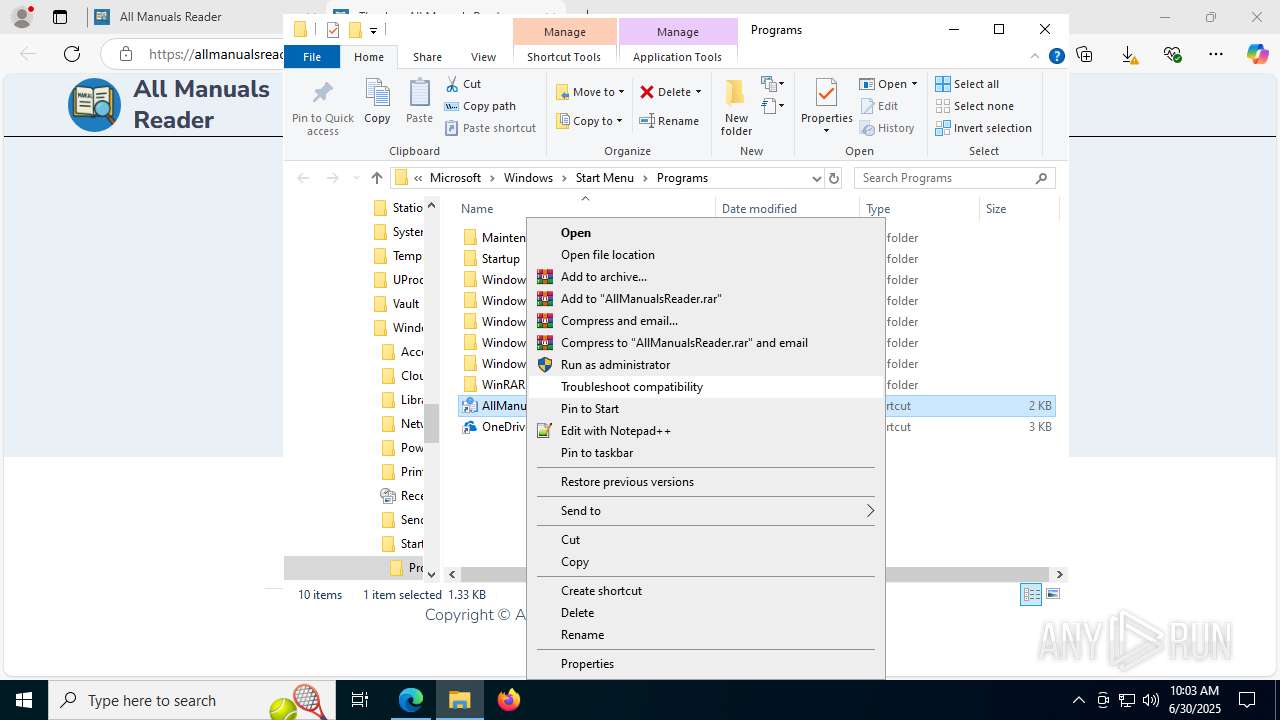
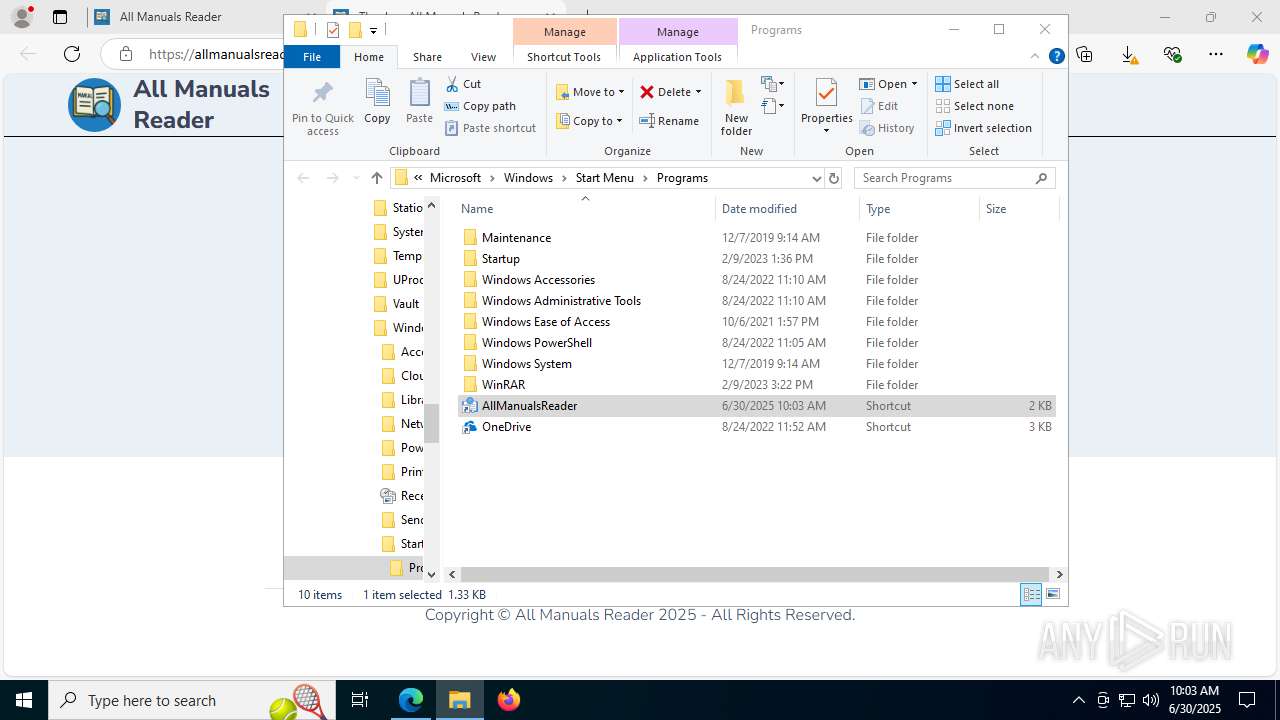
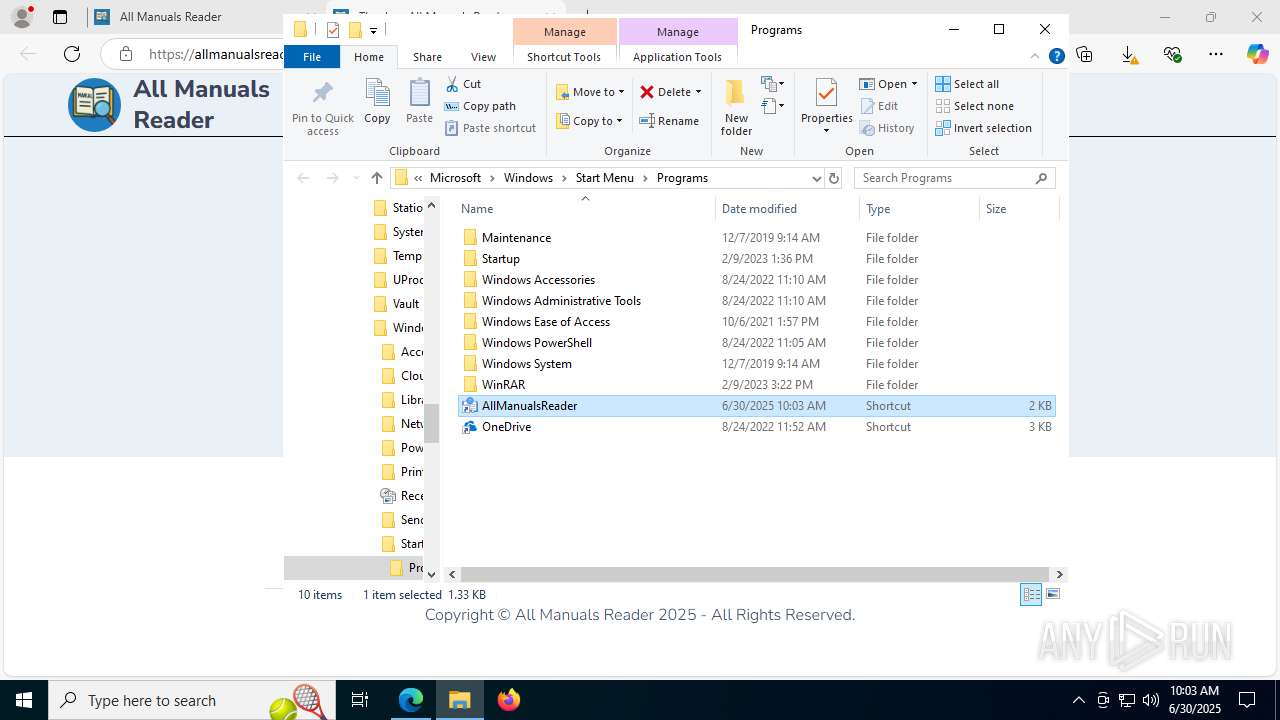
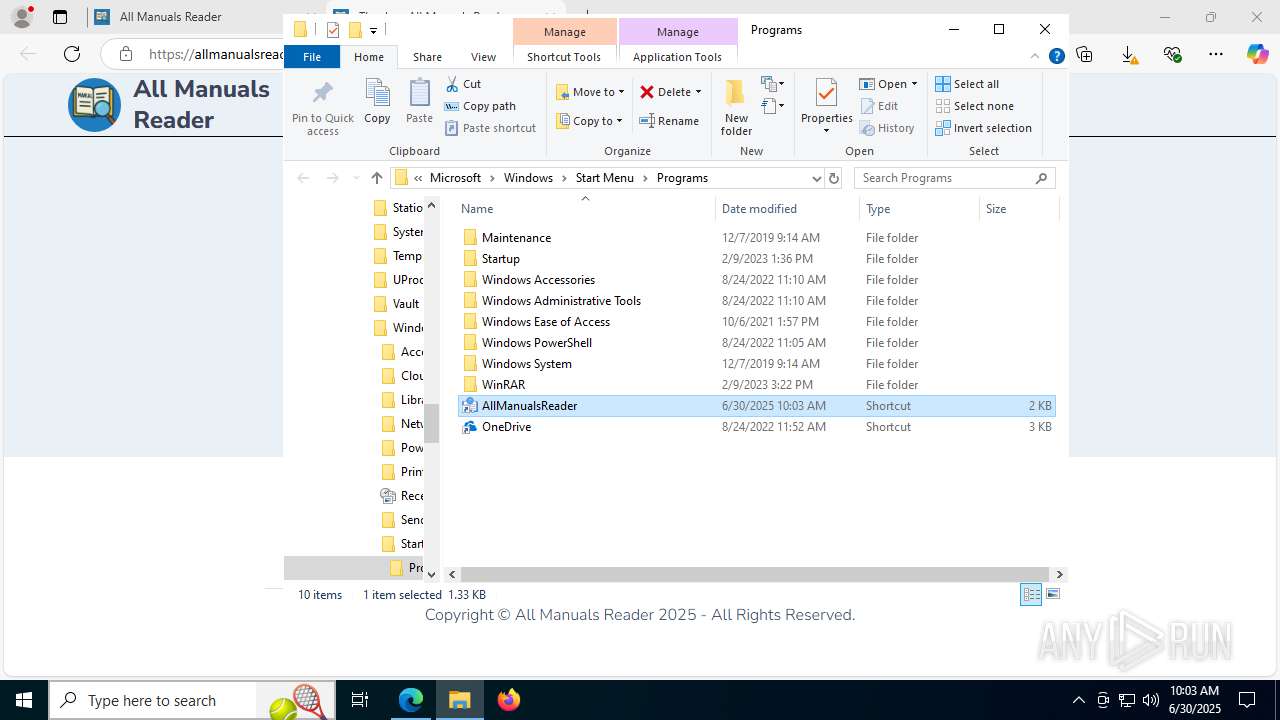
MALICIOUS
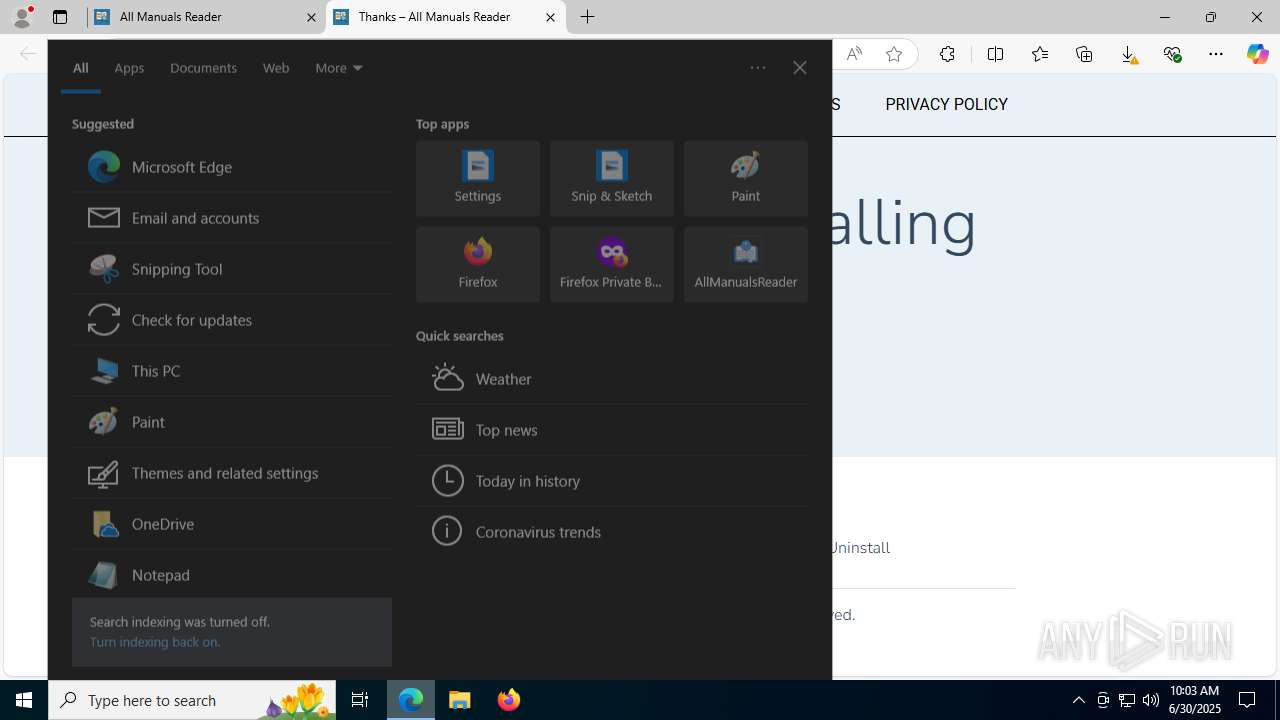
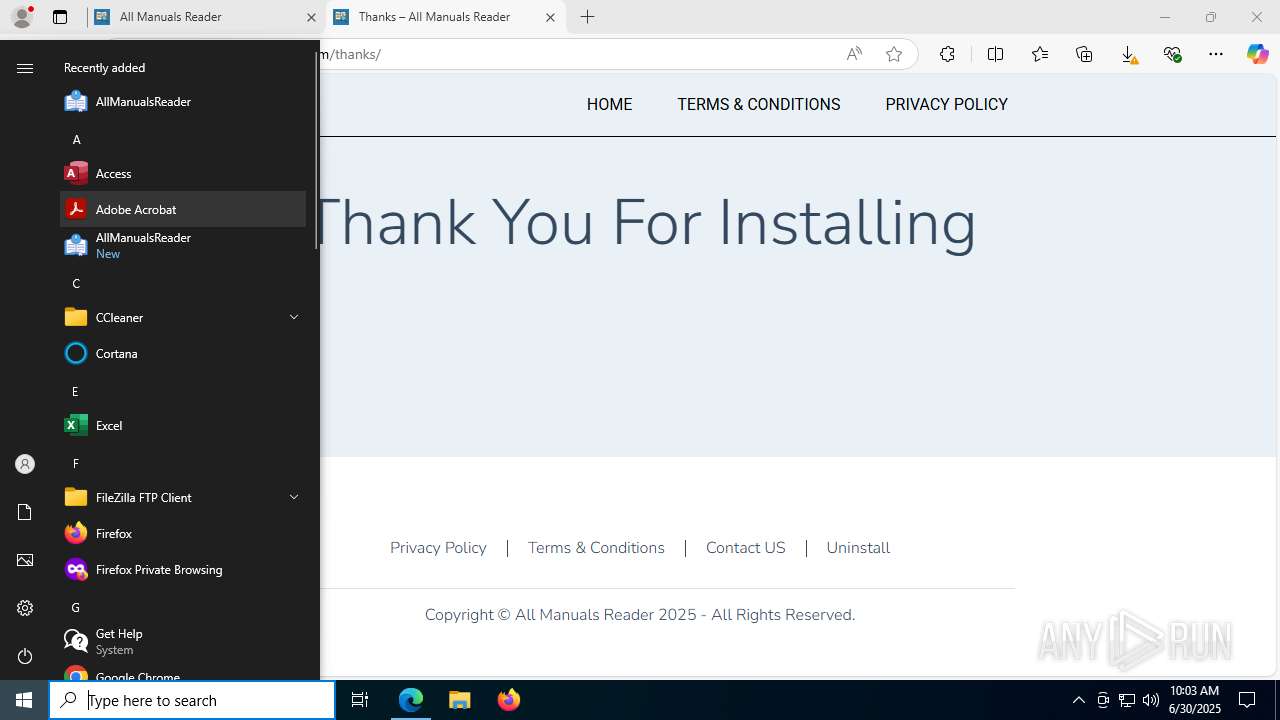
Uses Task Scheduler to run other applications
- cmd.exe (PID: 4832)
SUSPICIOUS
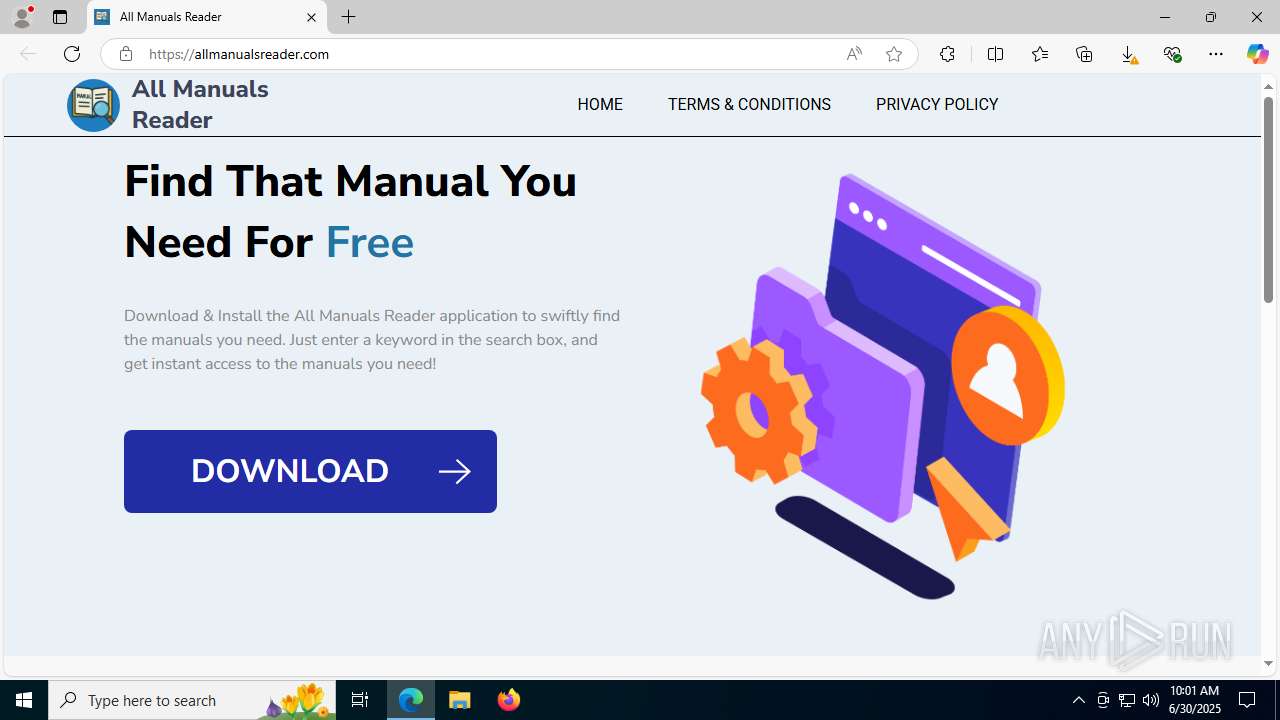
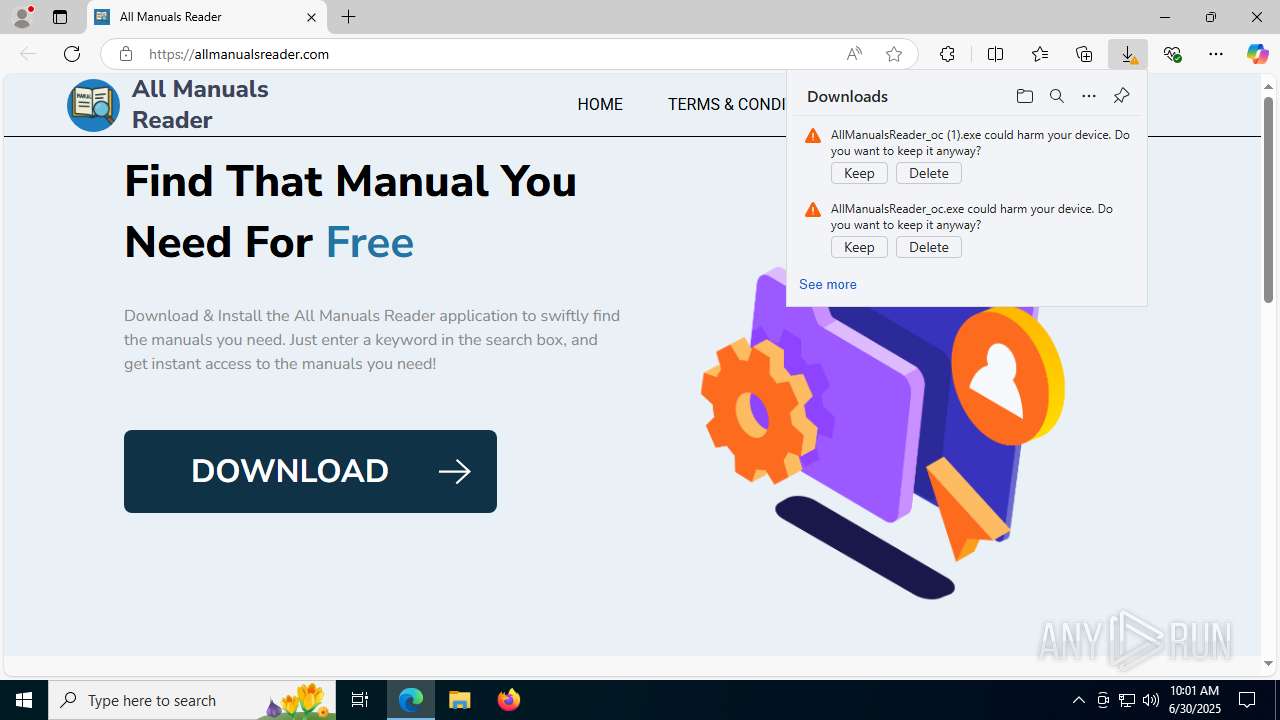
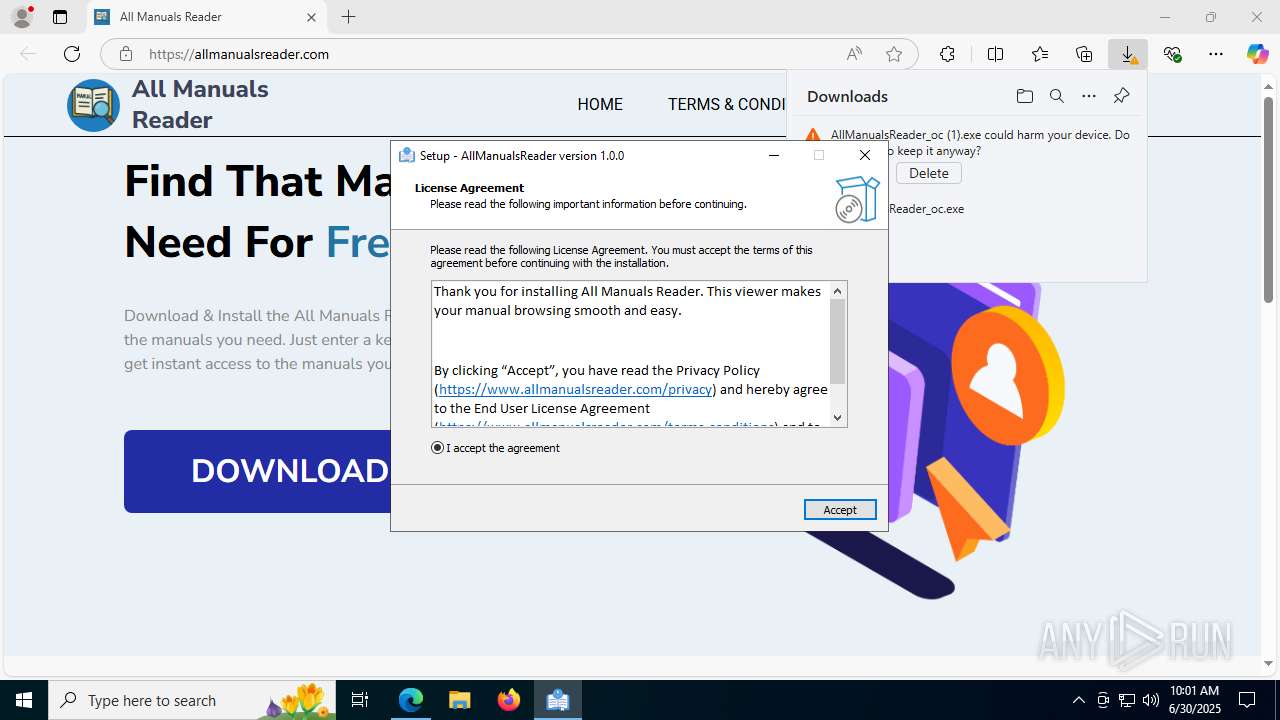
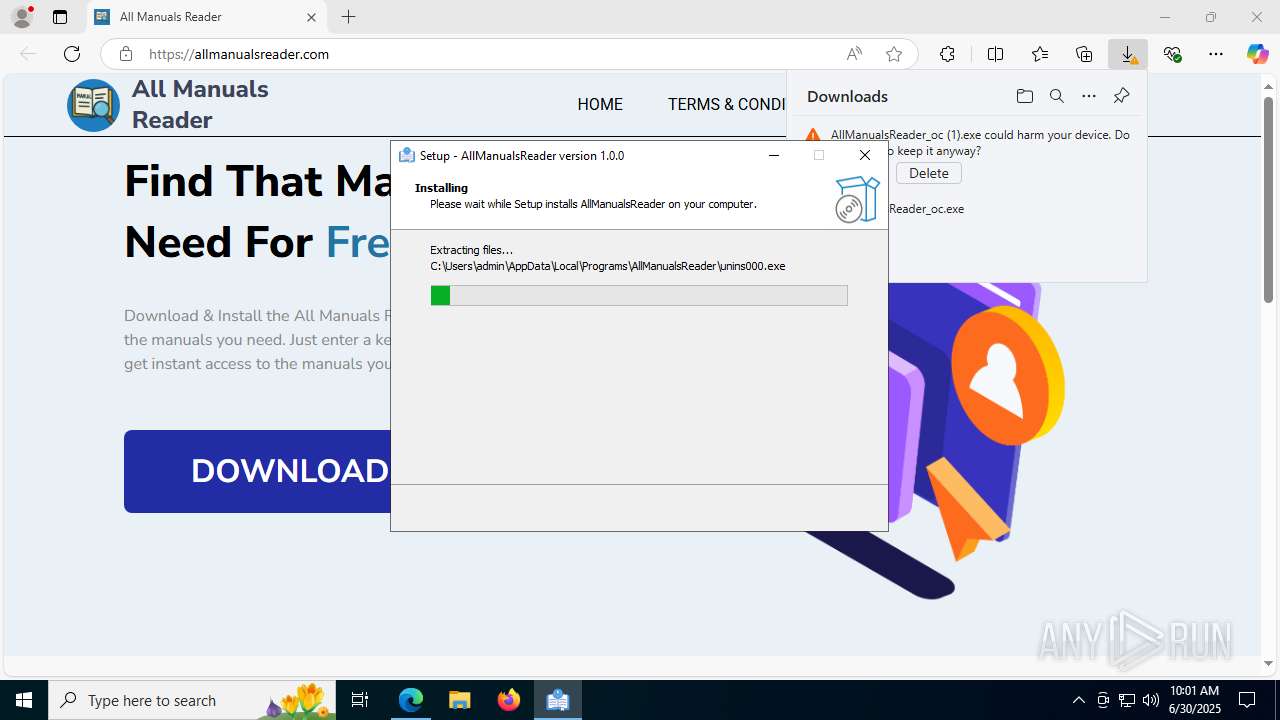
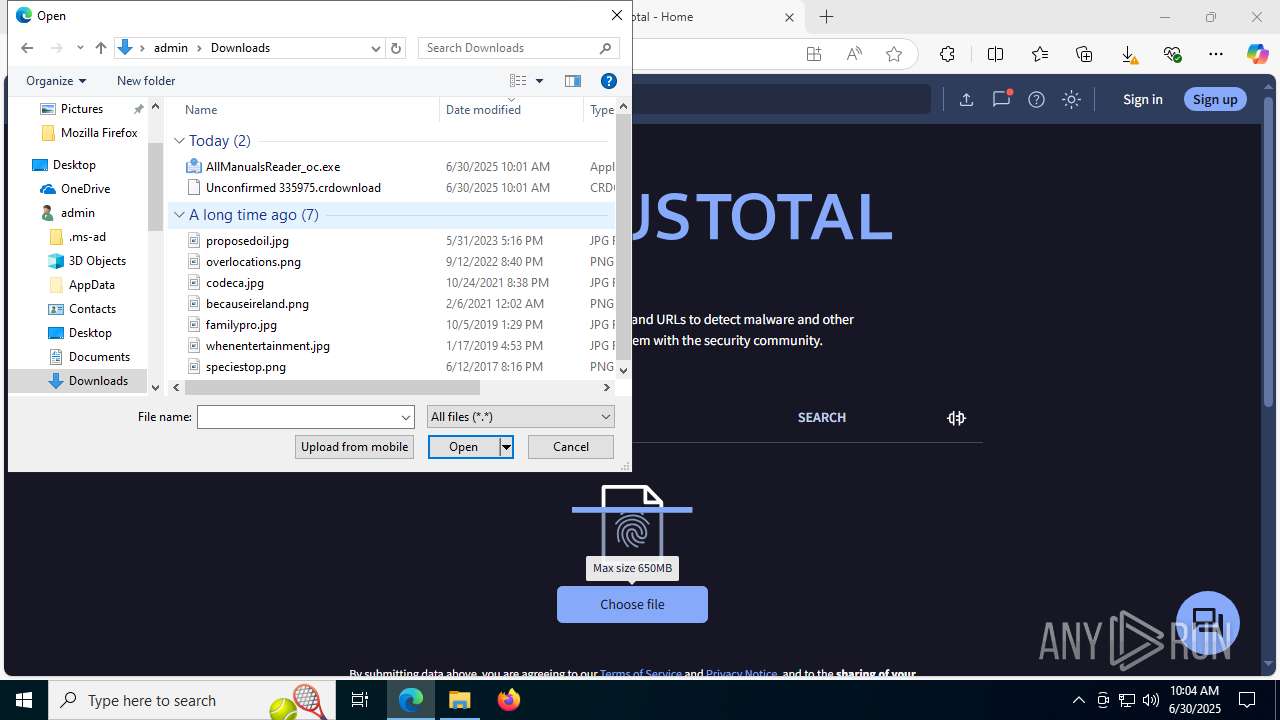
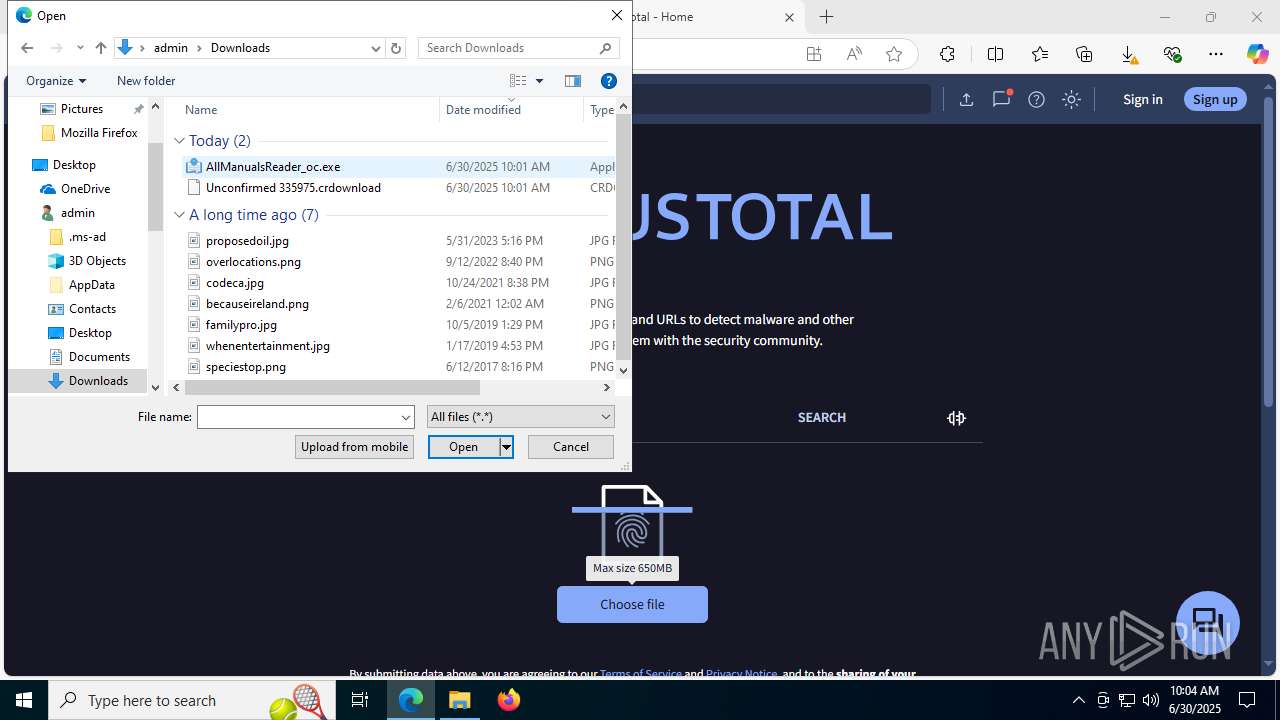
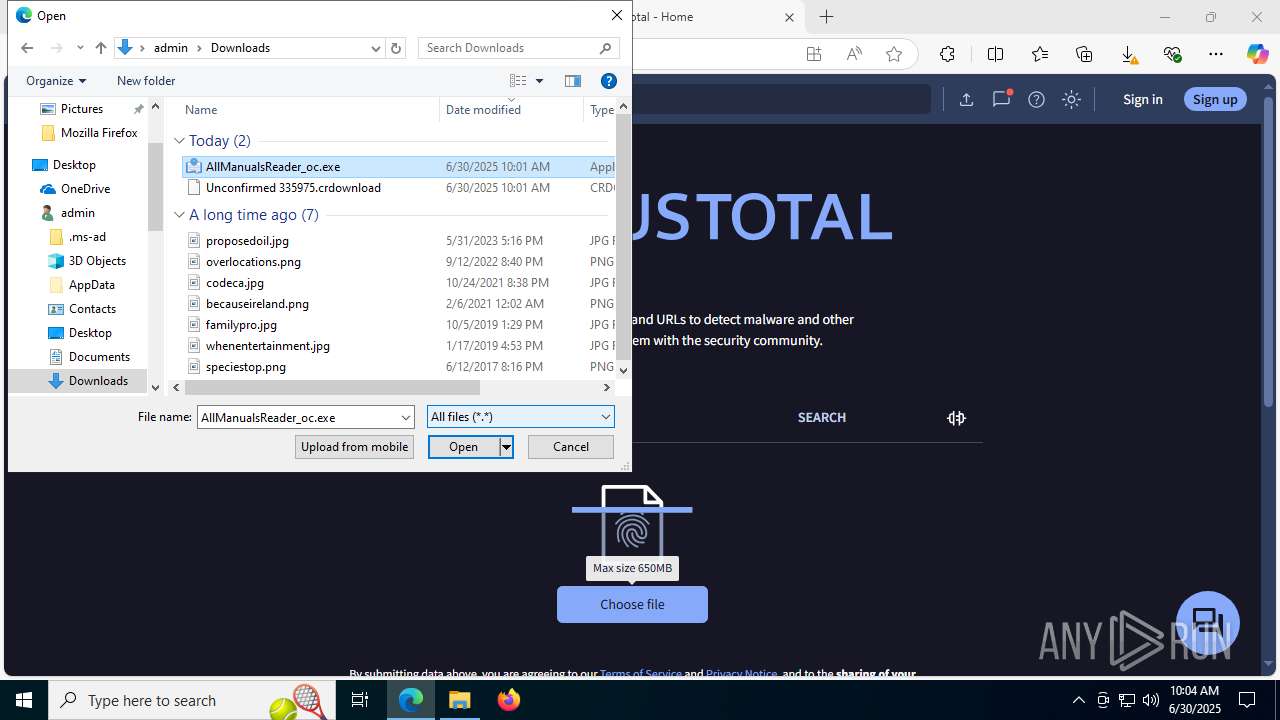
Executable content was dropped or overwritten
- AllManualsReader_oc.exe (PID: 7560)
- AllManualsReader_oc.tmp (PID: 6636)
Reads the Windows owner or organization settings
- AllManualsReader_oc.tmp (PID: 6636)
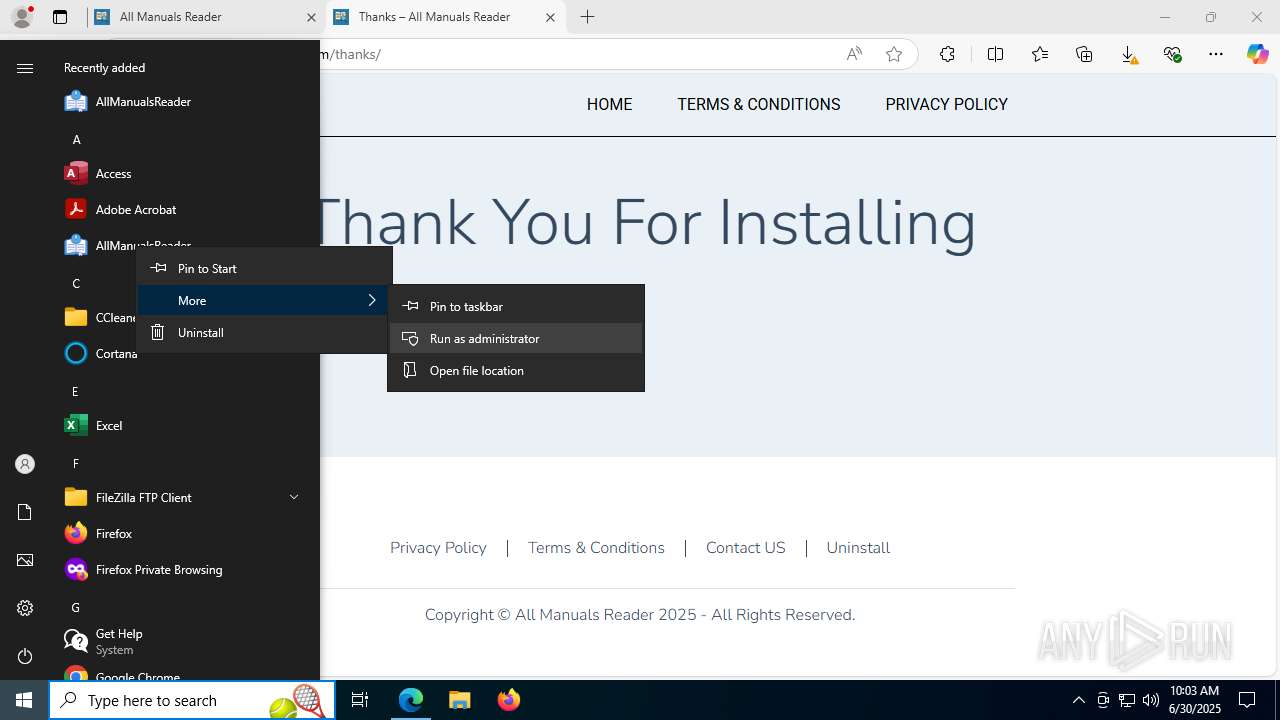
Executes script using NodeJS
- node.exe (PID: 7820)
Starts CMD.EXE for commands execution
- AllManualsReader_oc.tmp (PID: 6636)
- node.exe (PID: 7820)
The process executes via Task Scheduler
- cmd.exe (PID: 1828)
Reads security settings of Internet Explorer
- AllManualsReader_oc.tmp (PID: 6636)
Process drops legitimate windows executable
- AllManualsReader_oc.tmp (PID: 6636)
Executes application which crashes
- AllManualsReader.exe (PID: 5140)
- AllManualsReader.exe (PID: 6424)
- AllManualsReader.exe (PID: 7004)
- AllManualsReader.exe (PID: 2324)
- AllManualsReader.exe (PID: 7892)
- AllManualsReader.exe (PID: 2800)
INFO
Checks supported languages
- identity_helper.exe (PID: 7956)
- AllManualsReader_oc.exe (PID: 7560)
- AllManualsReader_oc.tmp (PID: 6636)
- AllManualsReader.exe (PID: 5140)
- node.exe (PID: 7820)
- SearchApp.exe (PID: 5328)
- AllManualsReader.exe (PID: 6424)
- AllManualsReader.exe (PID: 7004)
- AllManualsReader.exe (PID: 2324)
- AllManualsReader.exe (PID: 2800)
- AllManualsReader.exe (PID: 7892)
Reads Environment values
- identity_helper.exe (PID: 7956)
- node.exe (PID: 7820)
Application launched itself
- msedge.exe (PID: 4500)
Reads the computer name
- identity_helper.exe (PID: 7956)
- AllManualsReader_oc.tmp (PID: 6636)
- AllManualsReader.exe (PID: 5140)
- node.exe (PID: 7820)
- AllManualsReader.exe (PID: 6424)
- AllManualsReader.exe (PID: 7004)
- AllManualsReader.exe (PID: 2324)
- AllManualsReader.exe (PID: 7892)
- AllManualsReader.exe (PID: 2800)
Executable content was dropped or overwritten
- msedge.exe (PID: 4500)
- msedge.exe (PID: 3572)
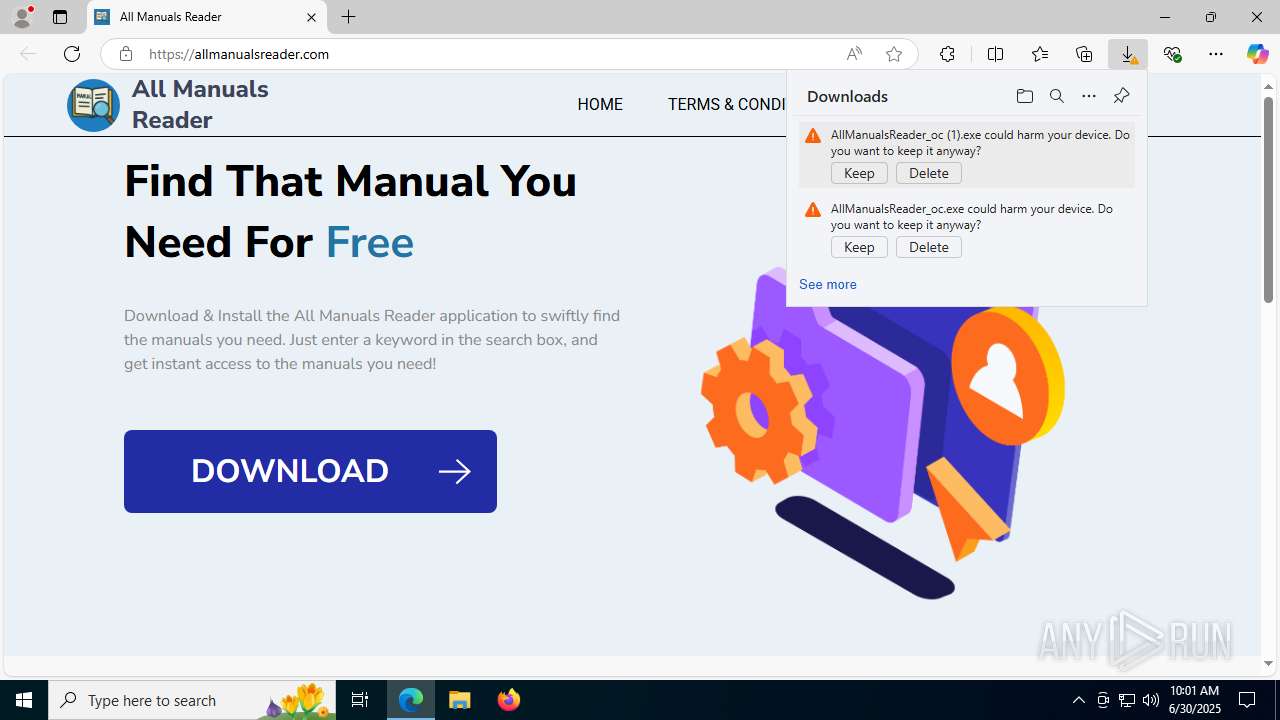
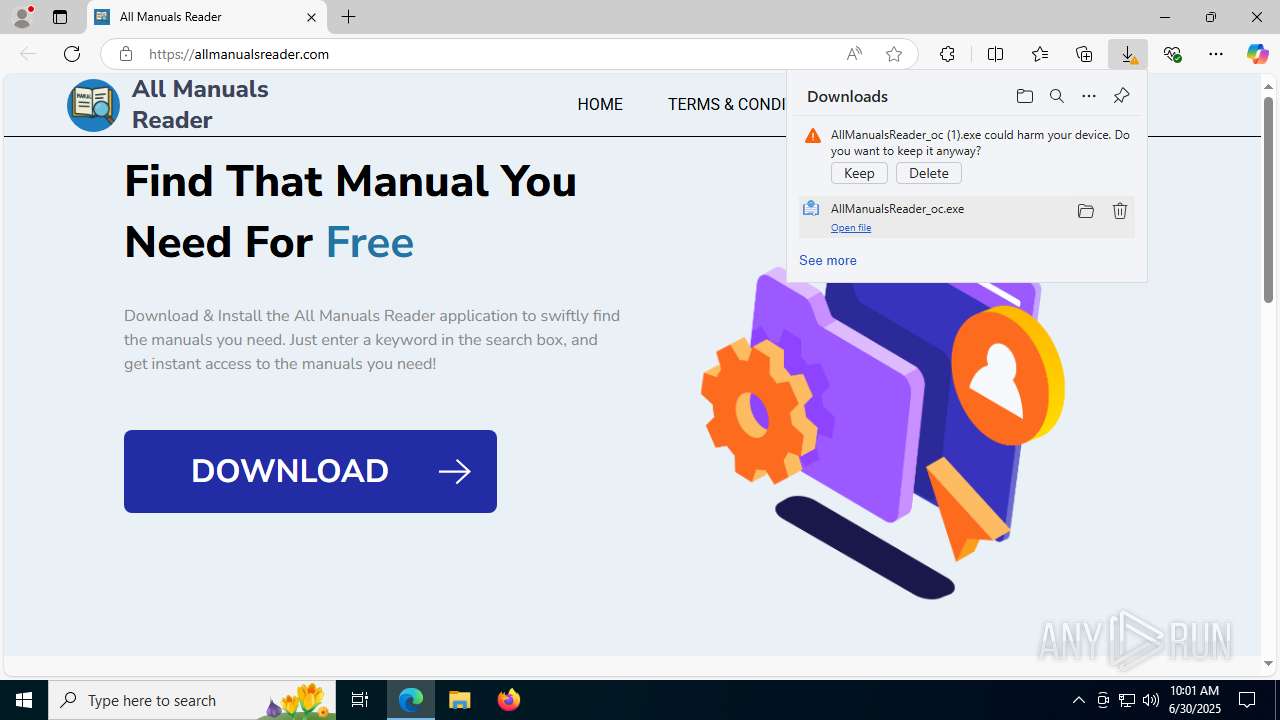
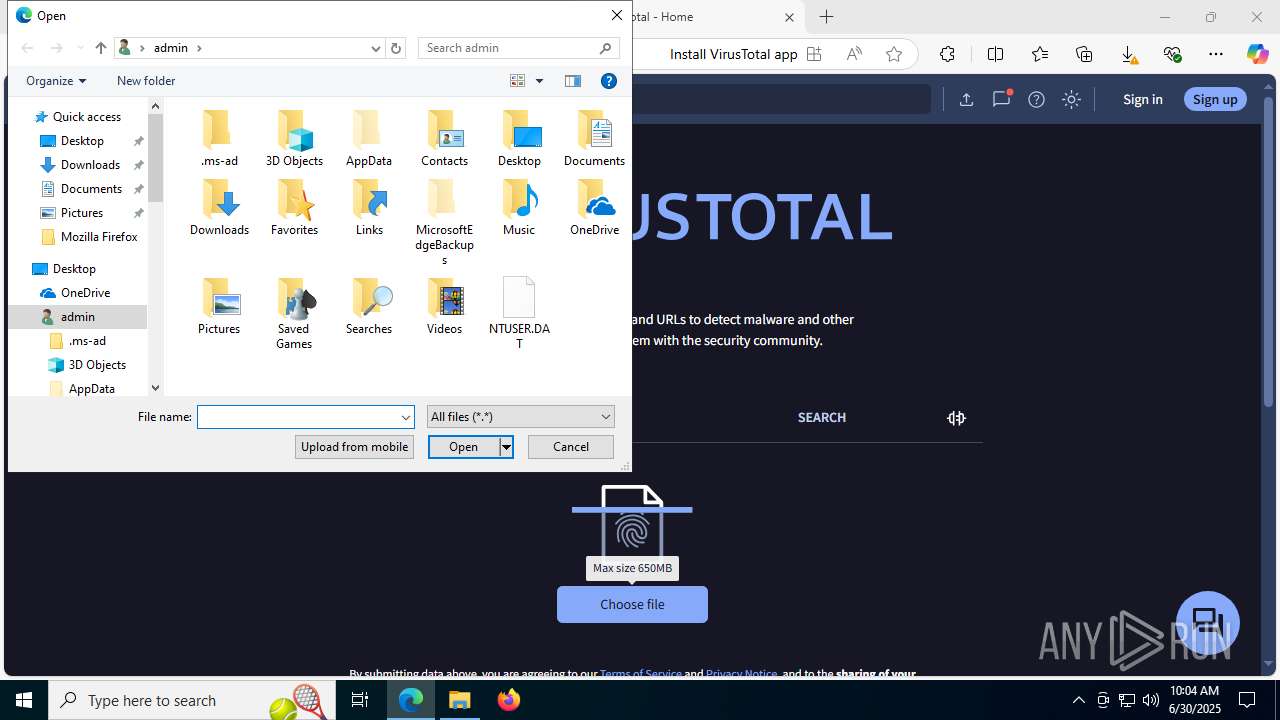
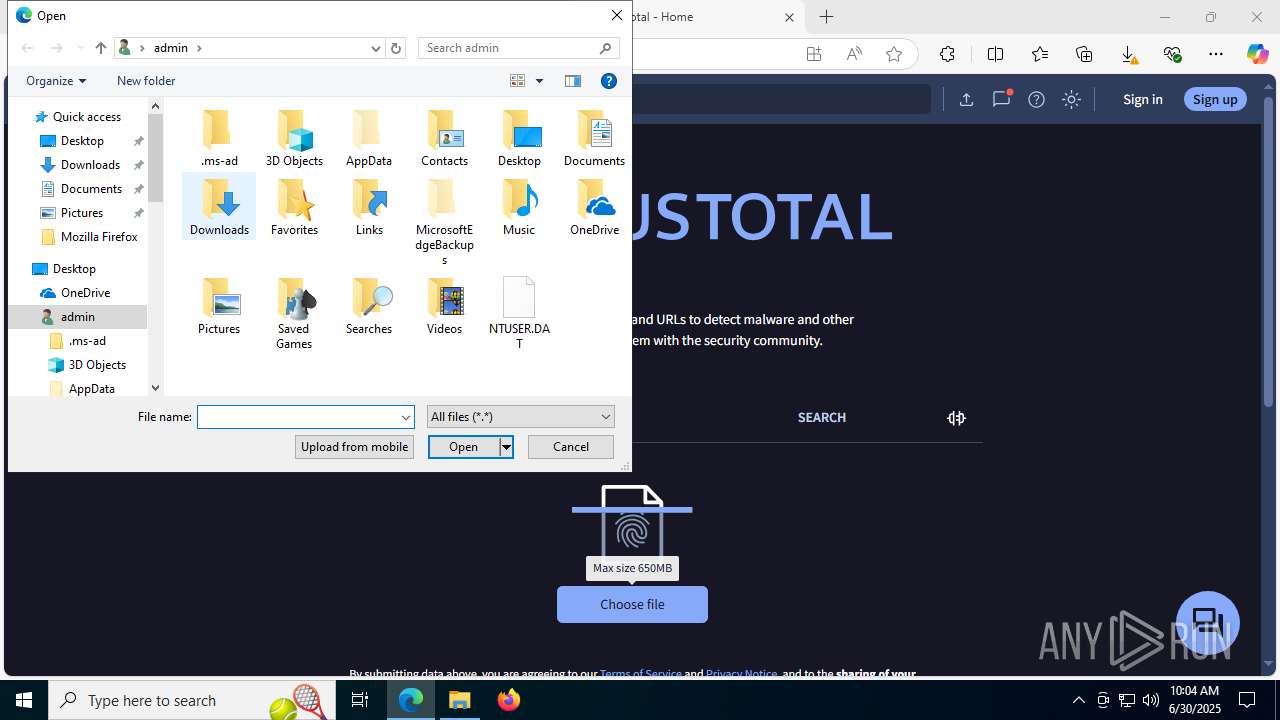
Launching a file from the Downloads directory
- msedge.exe (PID: 4500)
Create files in a temporary directory
- AllManualsReader_oc.exe (PID: 7560)
- AllManualsReader_oc.tmp (PID: 6636)
Reads the machine GUID from the registry
- AllManualsReader.exe (PID: 5140)
- AllManualsReader_oc.tmp (PID: 6636)
- SearchApp.exe (PID: 5328)
- AllManualsReader.exe (PID: 7004)
- AllManualsReader.exe (PID: 6424)
- AllManualsReader.exe (PID: 7892)
- AllManualsReader.exe (PID: 2324)
- AllManualsReader.exe (PID: 2800)
Reads the software policy settings
- AllManualsReader_oc.tmp (PID: 6636)
- WerFault.exe (PID: 3980)
- WerFault.exe (PID: 6380)
- SearchApp.exe (PID: 5328)
- WerFault.exe (PID: 888)
- WerFault.exe (PID: 2180)
- slui.exe (PID: 2704)
- WerFault.exe (PID: 7116)
- WerFault.exe (PID: 1160)
Creates files or folders in the user directory
- AllManualsReader_oc.tmp (PID: 6636)
- WerFault.exe (PID: 3980)
- node.exe (PID: 7820)
- WerFault.exe (PID: 888)
- WerFault.exe (PID: 6380)
- WerFault.exe (PID: 2180)
- WerFault.exe (PID: 7116)
- WerFault.exe (PID: 1160)
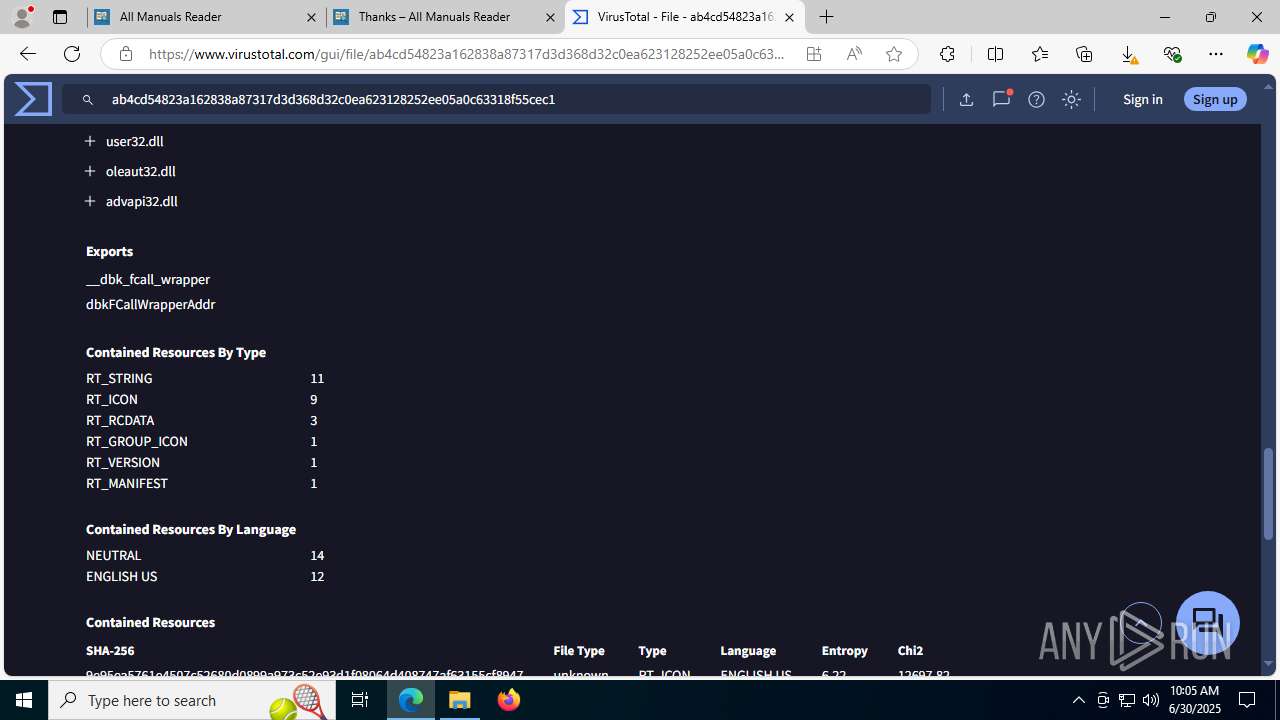
The sample compiled with english language support
- AllManualsReader_oc.tmp (PID: 6636)
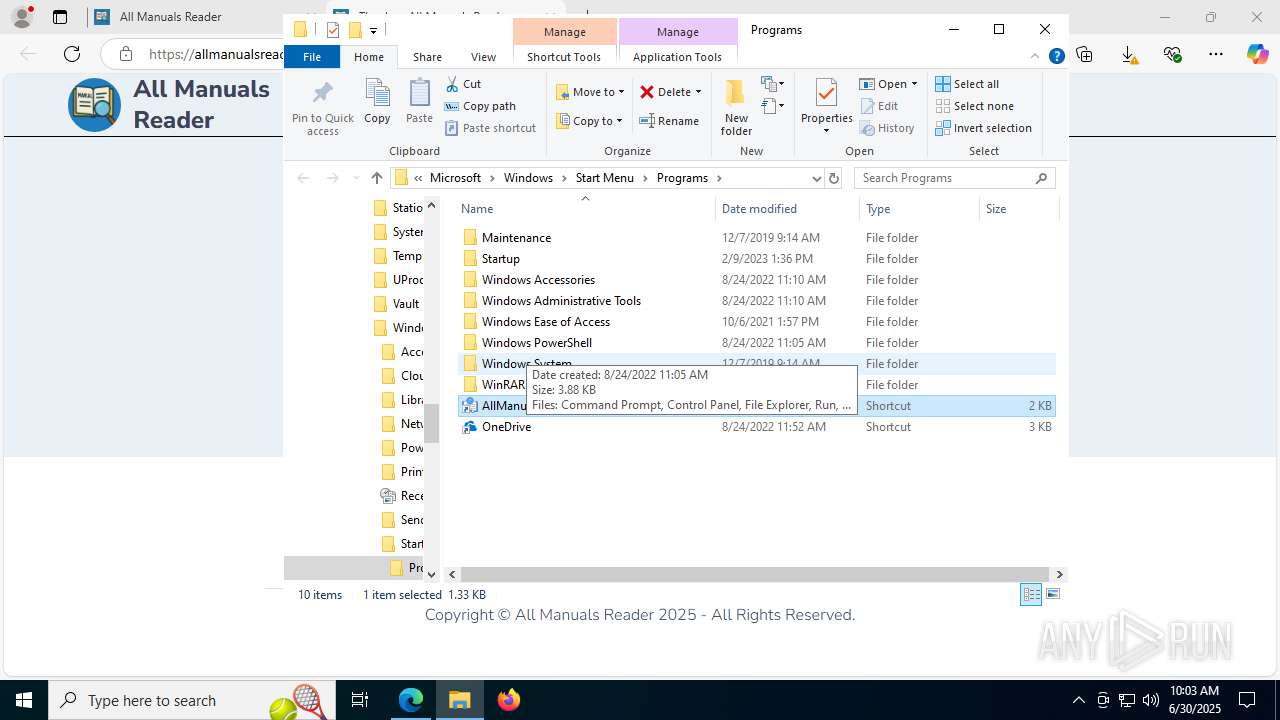
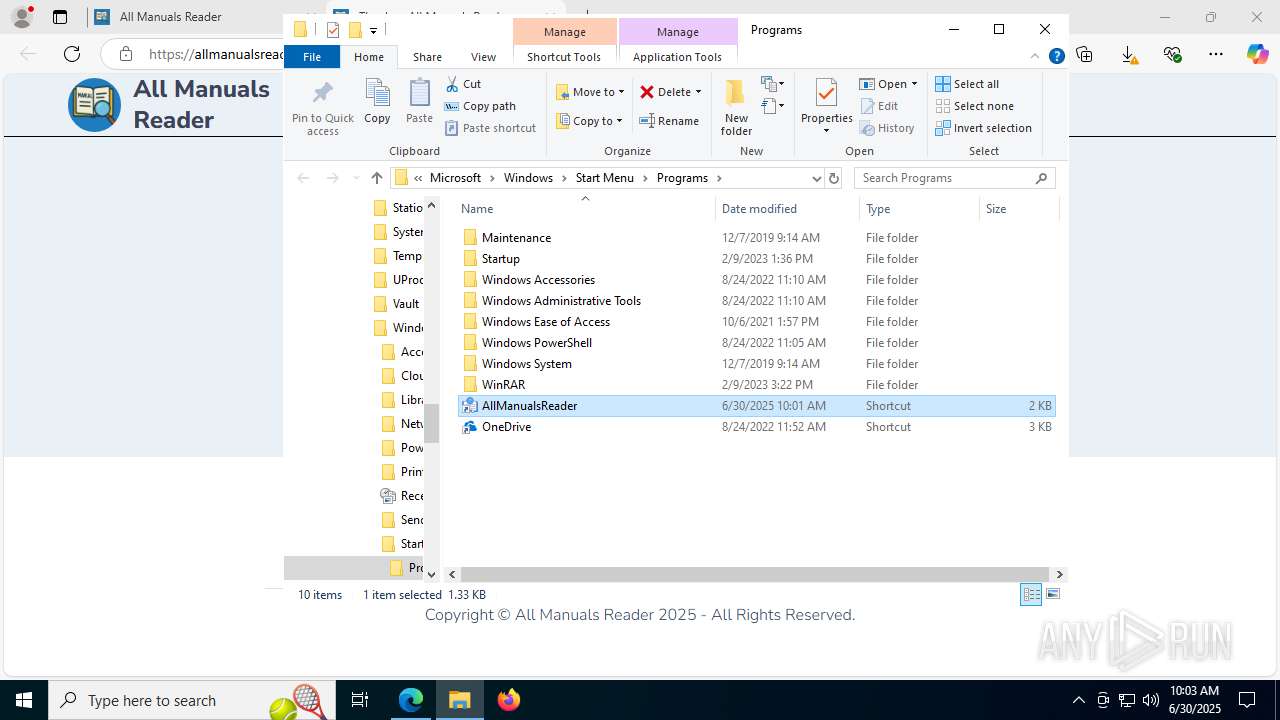
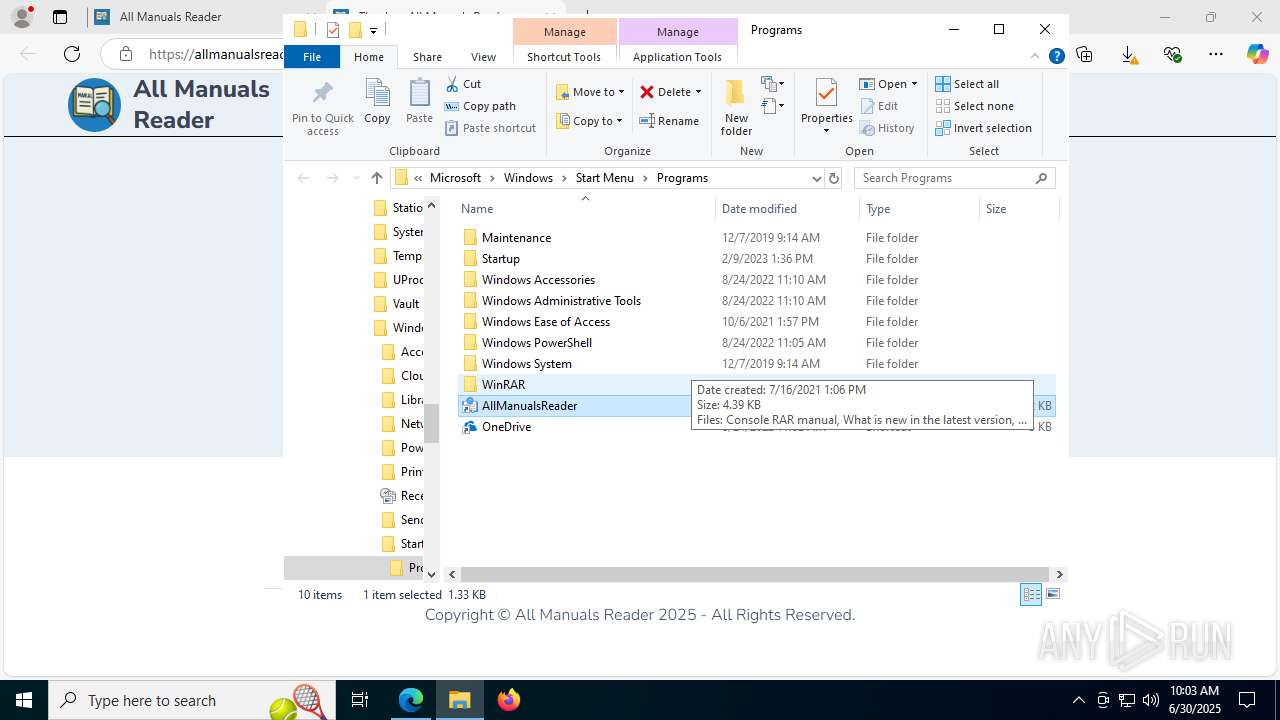
Creates a software uninstall entry
- AllManualsReader_oc.tmp (PID: 6636)
Process checks computer location settings
- SearchApp.exe (PID: 5328)
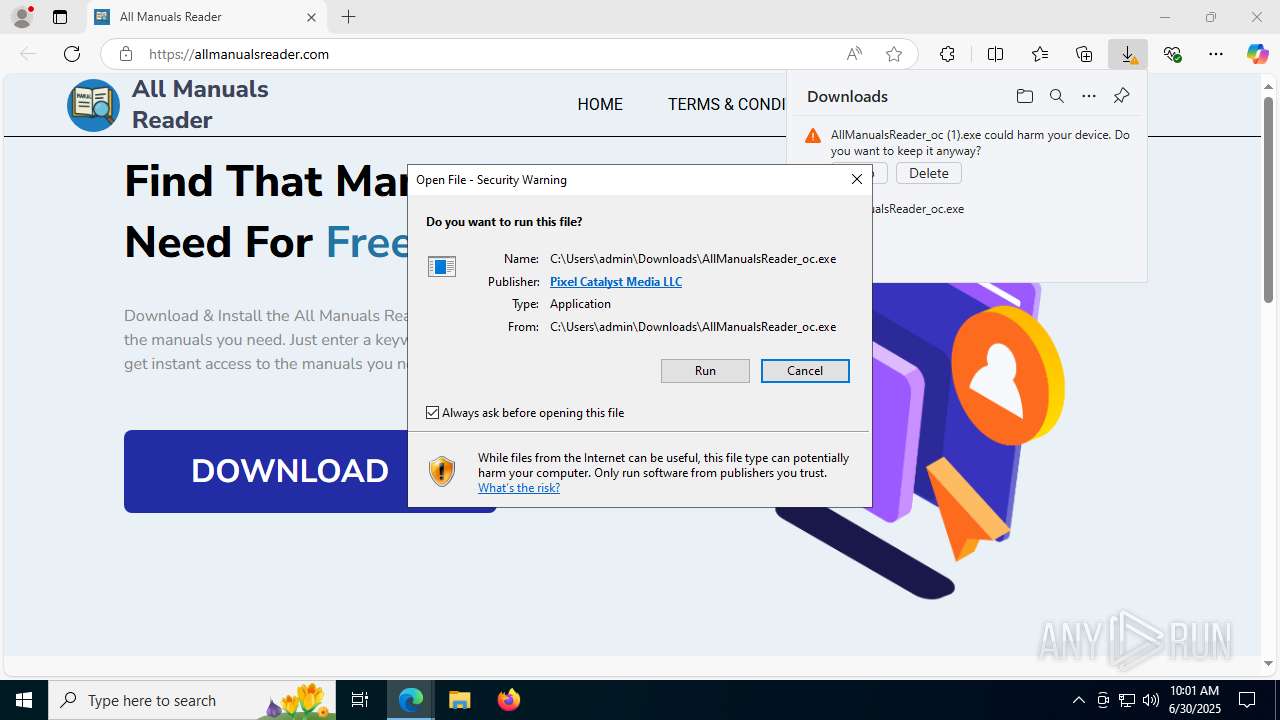
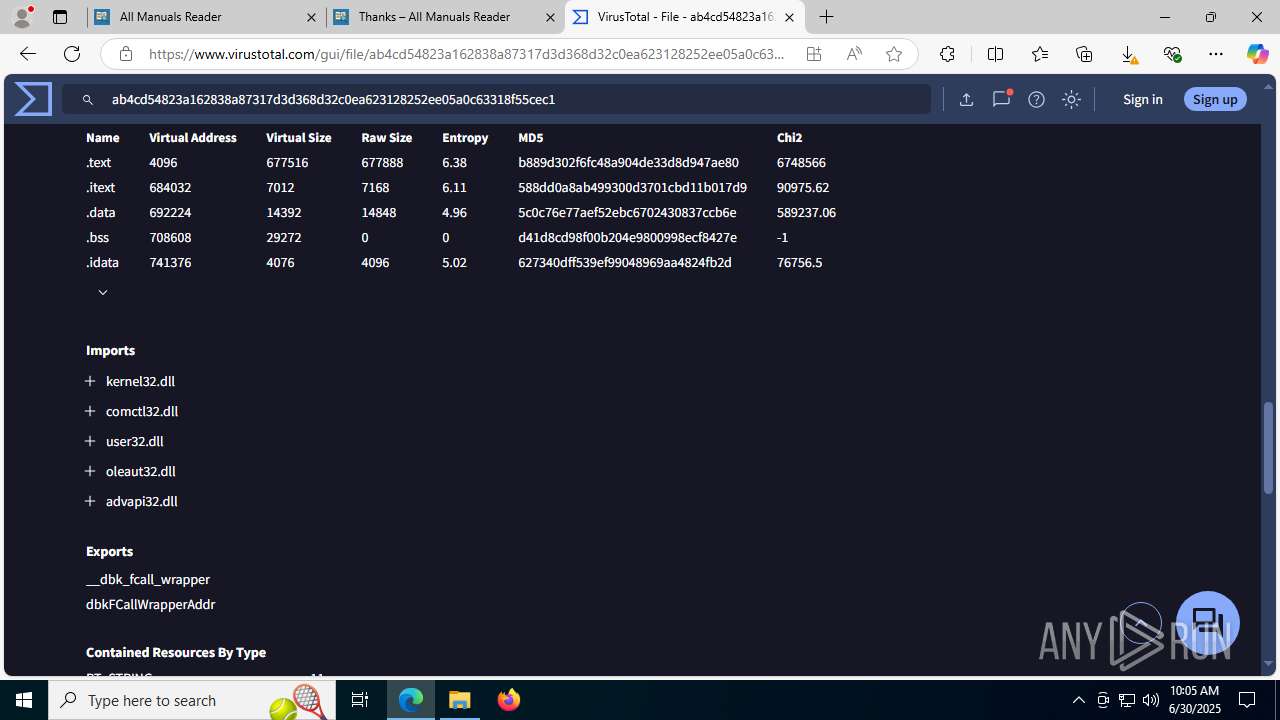
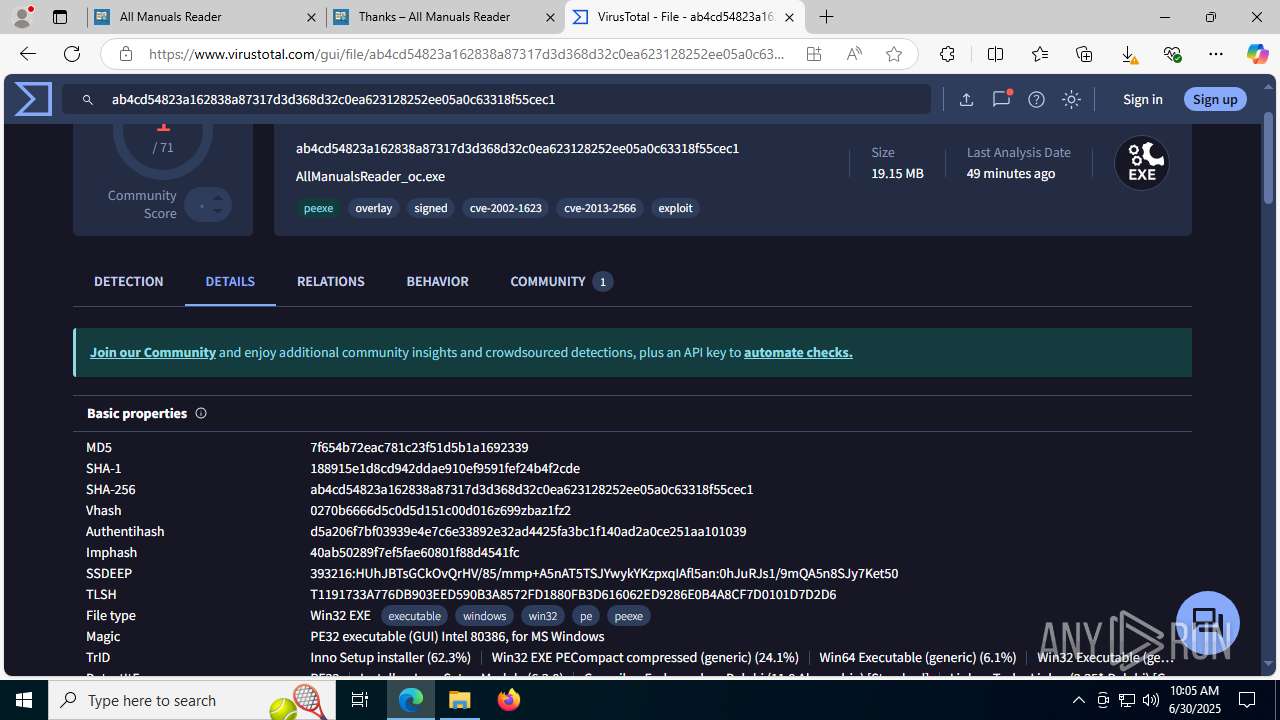
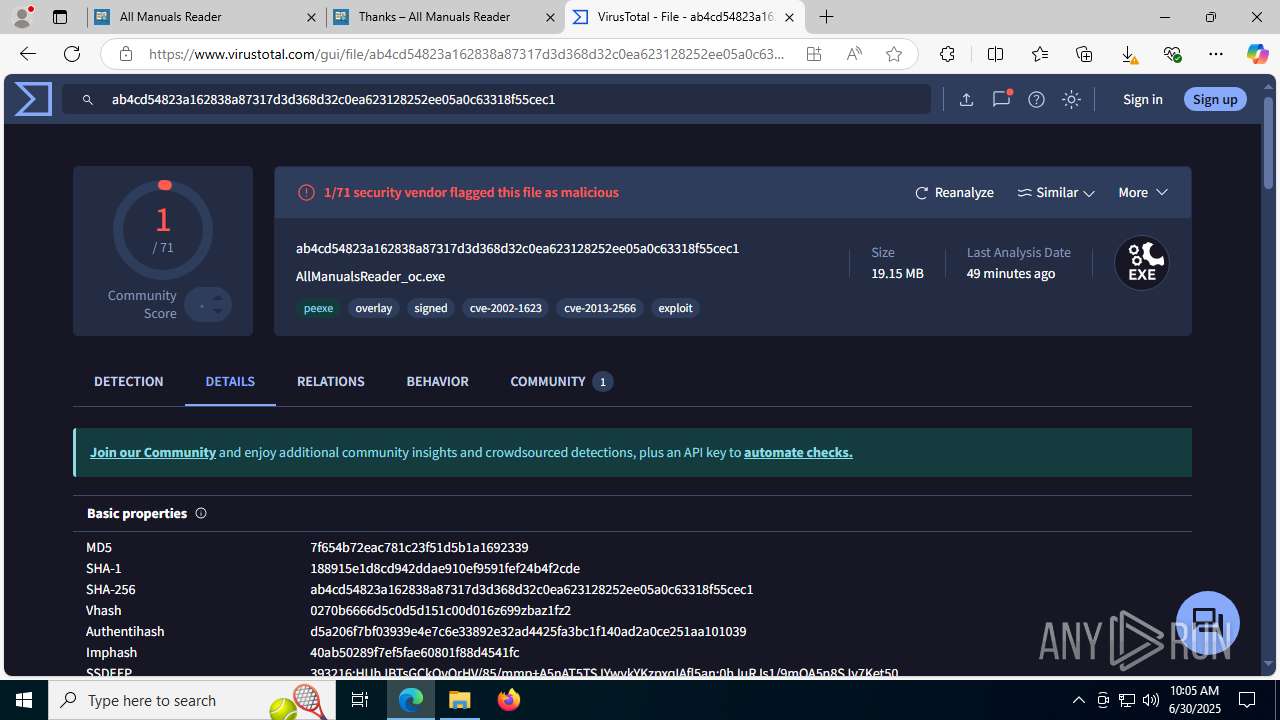
Detects InnoSetup installer (YARA)
- AllManualsReader_oc.exe (PID: 7560)
Compiled with Borland Delphi (YARA)
- AllManualsReader_oc.exe (PID: 7560)
Checks proxy server information
- WerFault.exe (PID: 3980)
- WerFault.exe (PID: 888)
- WerFault.exe (PID: 6380)
- WerFault.exe (PID: 2180)
- slui.exe (PID: 2704)
- WerFault.exe (PID: 7116)
- WerFault.exe (PID: 1160)
Reads product name
- node.exe (PID: 7820)
Manual execution by a user
- AllManualsReader.exe (PID: 6424)
- AllManualsReader.exe (PID: 7004)
- AllManualsReader.exe (PID: 2324)
- AllManualsReader.exe (PID: 2800)
- AllManualsReader.exe (PID: 7892)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
229
Monitored processes
76
Malicious processes
1
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
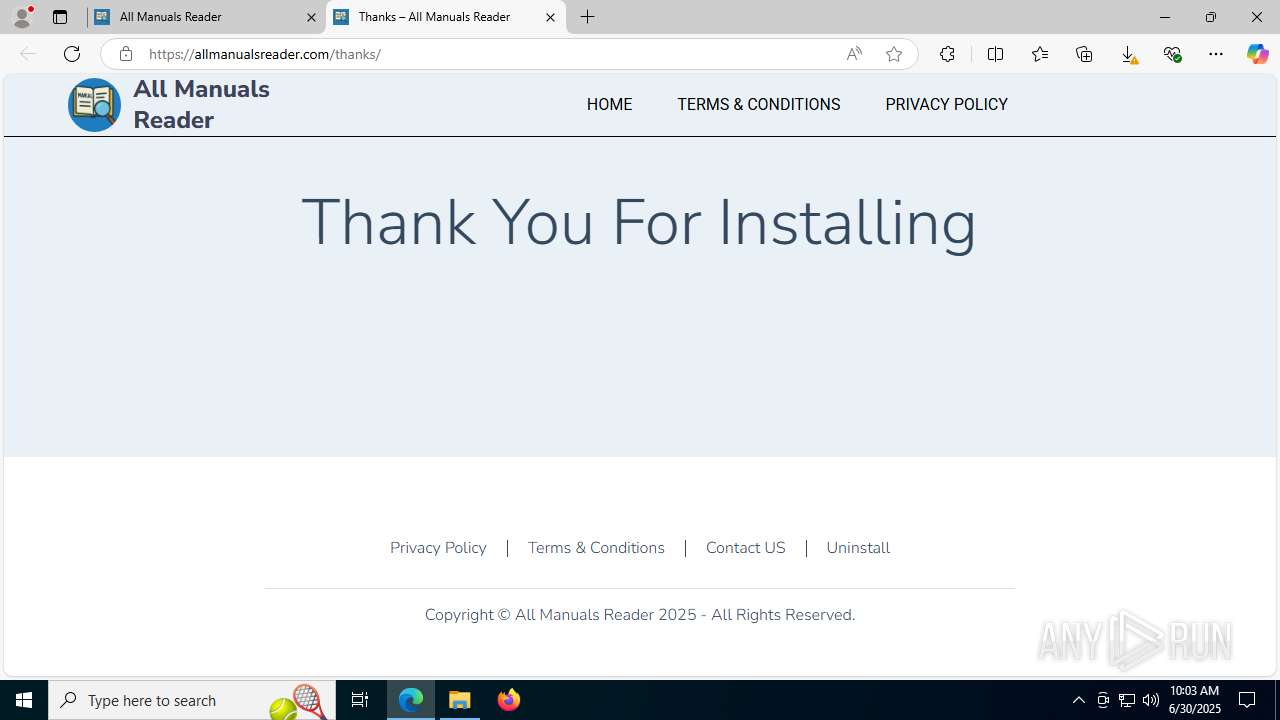
| 504 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --single-argument https://www.allmanualsreader.com/thanks | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | AllManualsReader_oc.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 888 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7004 -s 1176 | C:\Windows\SysWOW64\WerFault.exe | AllManualsReader.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1160 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 2800 -s 1252 | C:\Windows\SysWOW64\WerFault.exe | AllManualsReader.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1564 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=1556,i,6189170740712140174,7538072134683855689,262144 --variations-seed-version --mojo-platform-channel-handle=8588 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3648,i,6189170740712140174,7538072134683855689,262144 --variations-seed-version --mojo-platform-channel-handle=3696 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1812 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=21 --always-read-main-dll --field-trial-handle=7172,i,6189170740712140174,7538072134683855689,262144 --variations-seed-version --mojo-platform-channel-handle=5776 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1828 | "C:\Windows\System32\cmd.exe" /C start "" /min "C:\Users\admin\AppData\Local\Programs\AllManualsReader\node\node.exe" "C:\Users\admin\AppData\Local\Programs\AllManualsReader\License.js" | C:\Windows\System32\cmd.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2132 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --instant-process --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=36 --always-read-main-dll --field-trial-handle=8196,i,6189170740712140174,7538072134683855689,262144 --variations-seed-version --mojo-platform-channel-handle=6092 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2168 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=7200,i,6189170740712140174,7538072134683855689,262144 --variations-seed-version --mojo-platform-channel-handle=9064 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2180 | C:\WINDOWS\SysWOW64\WerFault.exe -u -p 7892 -s 1260 | C:\Windows\SysWOW64\WerFault.exe | AllManualsReader.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
48 750
Read events
48 409
Write events
319
Delete events
22
Modification events
| (PID) Process: | (6240) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkLowPart |
Value: 0 | |||
| (PID) Process: | (6240) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | L1WatermarkHighPart |
Value: 0 | |||
| (PID) Process: | (6240) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 0 | |||
| (PID) Process: | (6240) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 0 | |||
| (PID) Process: | (6240) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 25908188 | |||
| (PID) Process: | (6240) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\UrlBlock |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 31189414 | |||
| (PID) Process: | (6240) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6240) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6240) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6240) iexplore.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
Executable files
24
Suspicious files
749
Text files
330
Unknown types
85
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF175af1.TMP | — | |
MD5:— | SHA256:— | |||
| 4500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF175af1.TMP | — | |
MD5:— | SHA256:— | |||
| 4500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF175af1.TMP | — | |
MD5:— | SHA256:— | |||
| 4500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF175af1.TMP | — | |
MD5:— | SHA256:— | |||
| 4500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF175b01.TMP | — | |
MD5:— | SHA256:— | |||
| 4500 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
32
TCP/UDP connections
171
DNS requests
196
Threats
14
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3572 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:ge1hVO7gj-MuE7ylp3pMzm6xjFprTDmlXxDLdskiJnQ&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7020 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
4500 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEDPXCKiRQFMZ4qW70zm5rW4%3D | unknown | — | — | whitelisted |
4500 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
4500 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRd0JozUYXMqqW4y4zJTrLcMCRSkAQUgTKSQSsozUbIxKLGKjkS7EipPxQCEH0GxIzLDgmUXOZVfHyOtag%3D | unknown | — | — | whitelisted |
7532 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7532 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
3980 | WerFault.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6404 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3572 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3572 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3572 | msedge.exe | 172.217.18.8:443 | www.googletagmanager.com | GOOGLE | US | whitelisted |
3572 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3572 | msedge.exe | 2.23.227.211:443 | copilot.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
allmanualsreader.com |
| unknown |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.google.com |
| whitelisted |
cdn-defaultasset.s3.us-east-1.amazonaws.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3572 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3572 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3572 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3572 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3572 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3572 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
— | — | Potential Corporate Privacy Violation | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Potentially Bad Traffic | ET INFO Executable served from Amazon S3 |
5328 | SearchApp.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Front Door domain observed in TLS SNI ( .azurefd .net) |
Process | Message |
|---|---|
AllManualsReader.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
AllManualsReader.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
AllManualsReader.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
AllManualsReader.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
AllManualsReader.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
AllManualsReader.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|