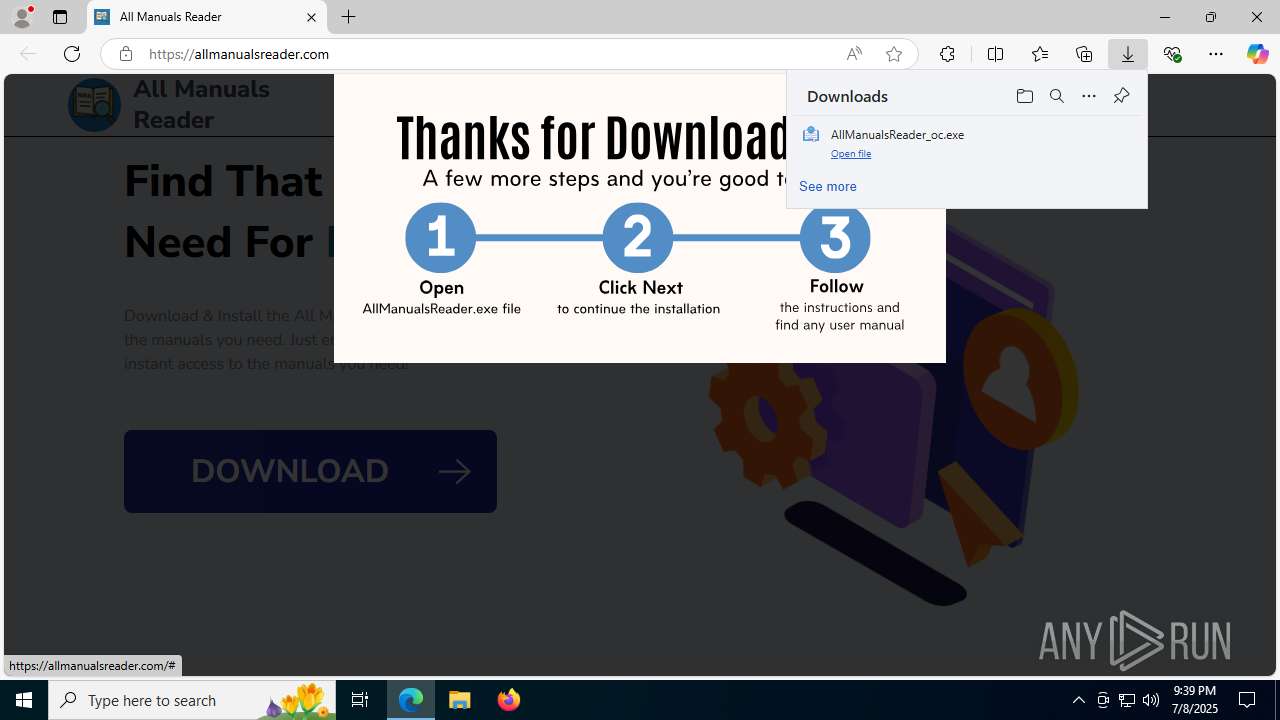
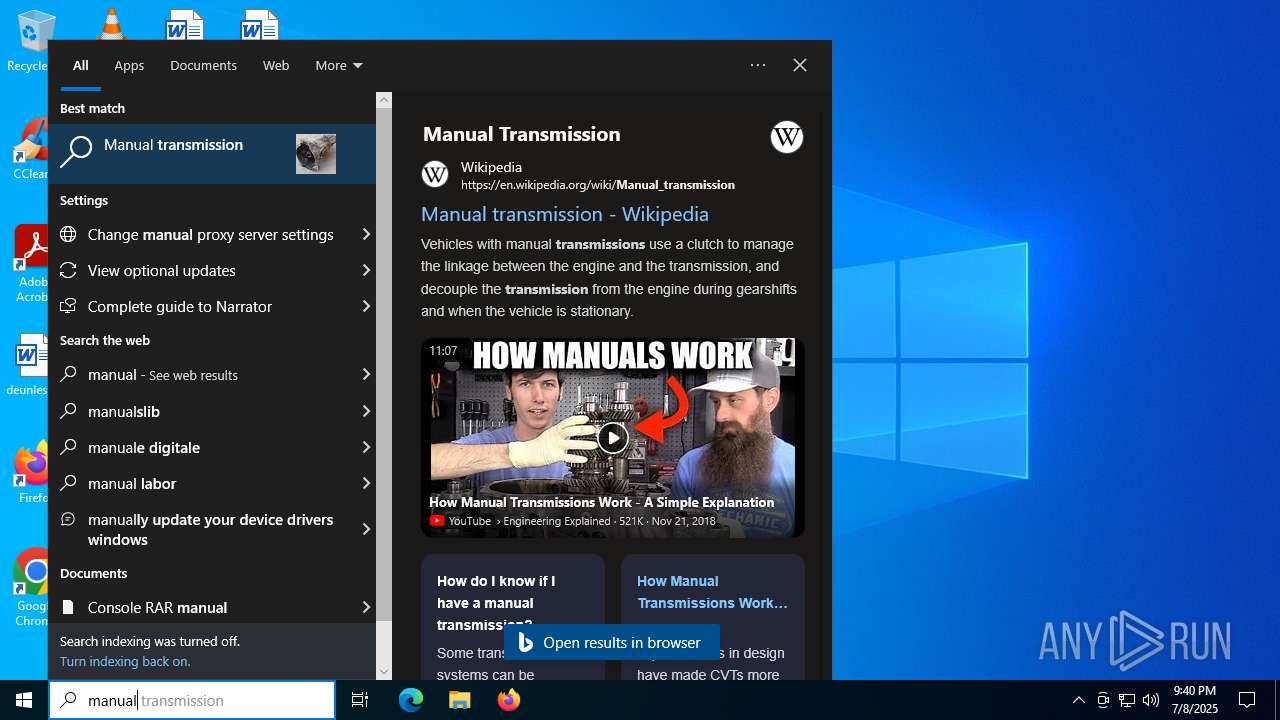
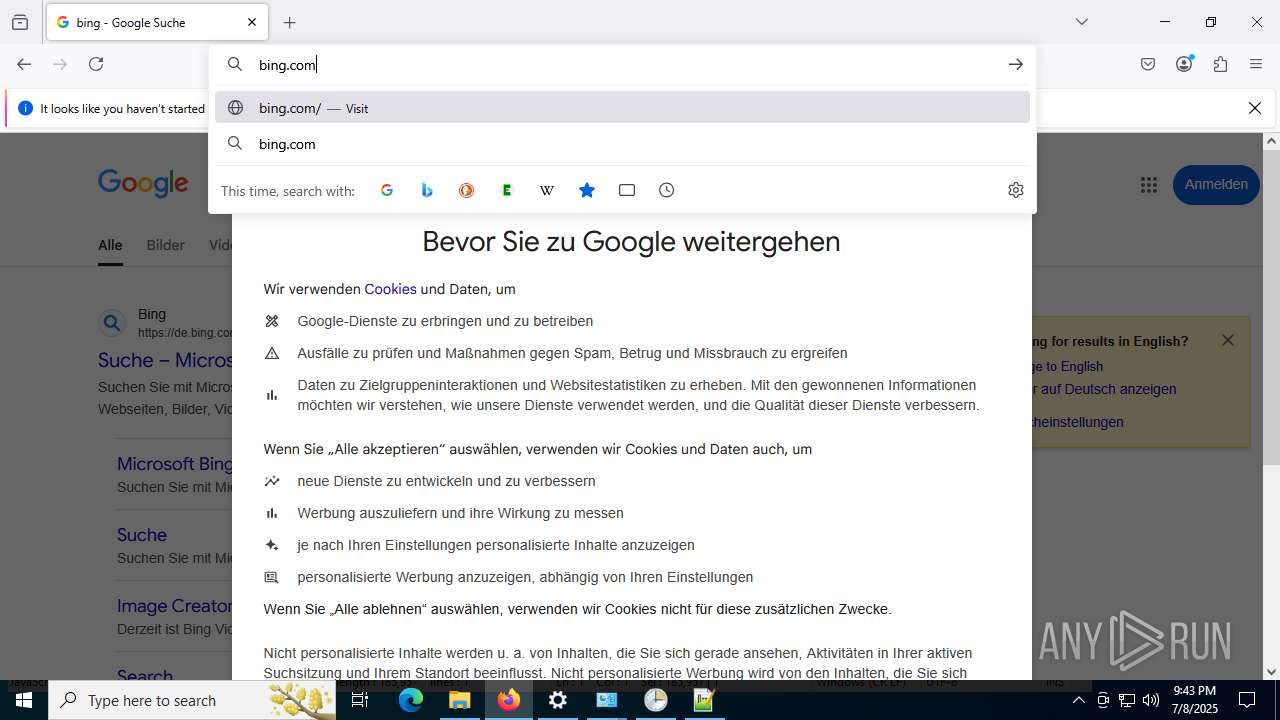
| URL: | allmanualsreader.com |
| Full analysis: | https://app.any.run/tasks/0d8f057f-dd60-46ab-8e54-5286fb9ce26b |
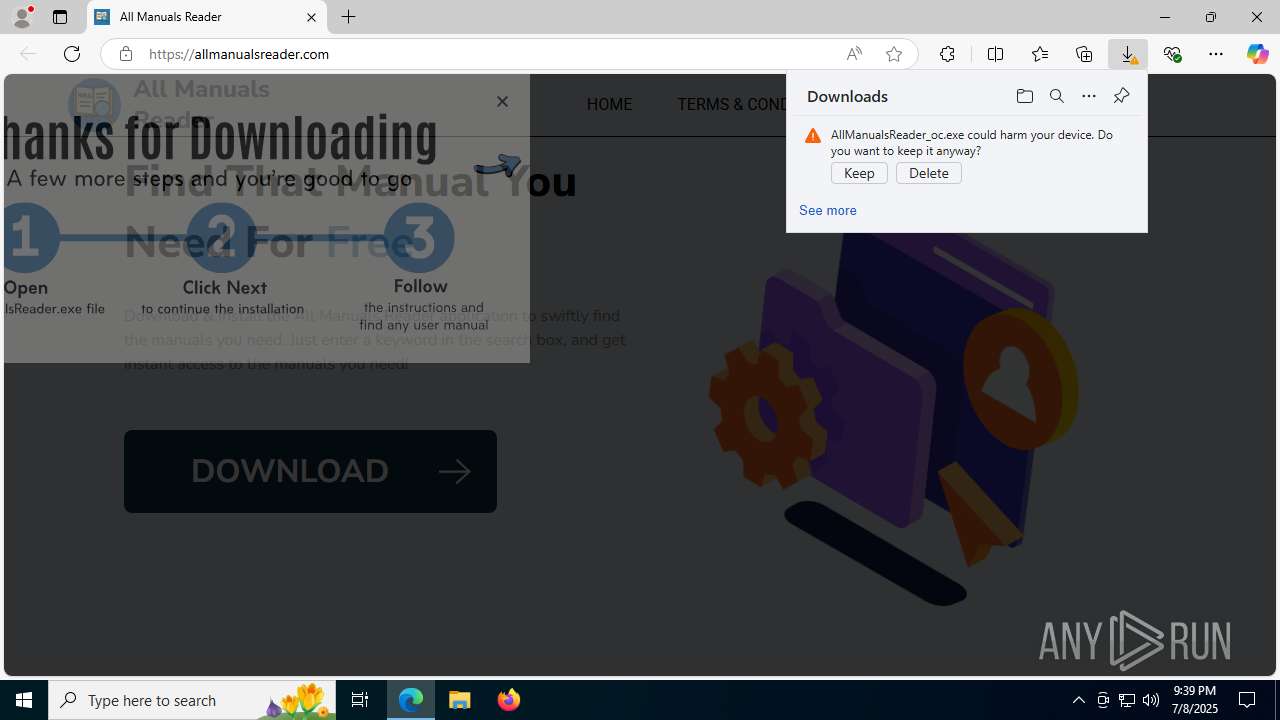
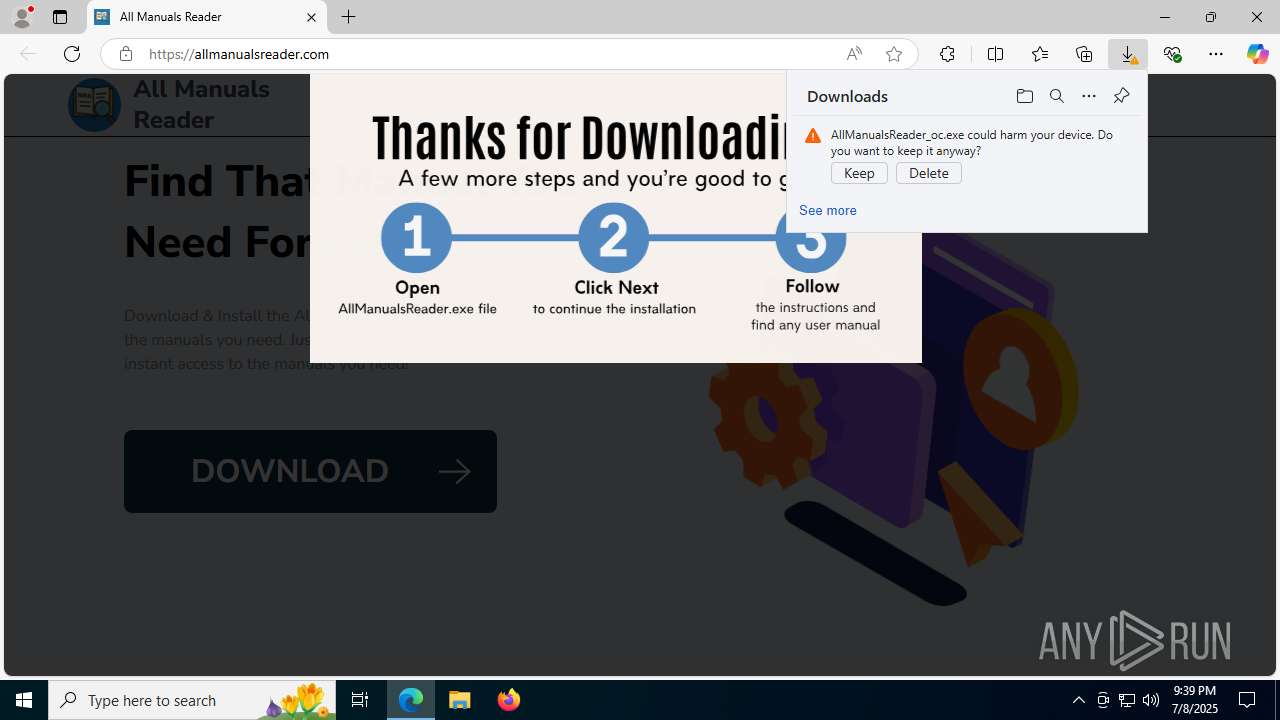
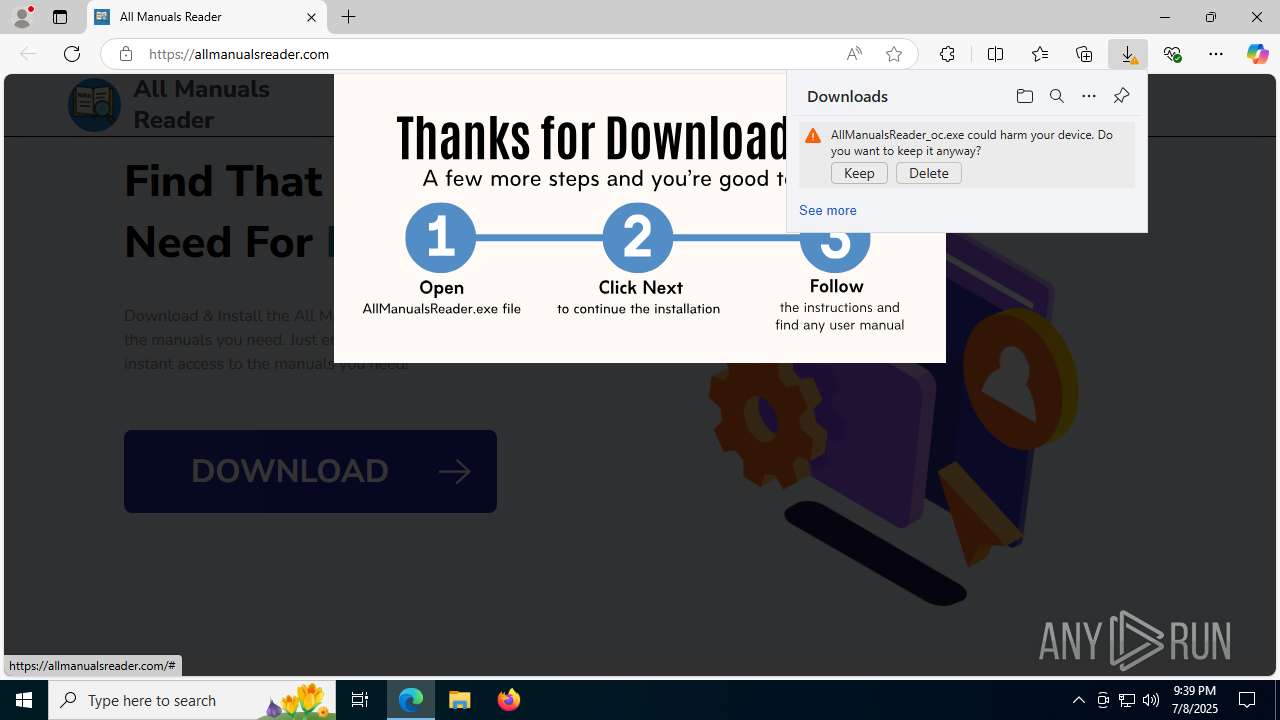
| Verdict: | Malicious activity |
| Analysis date: | July 08, 2025, 21:39:23 |
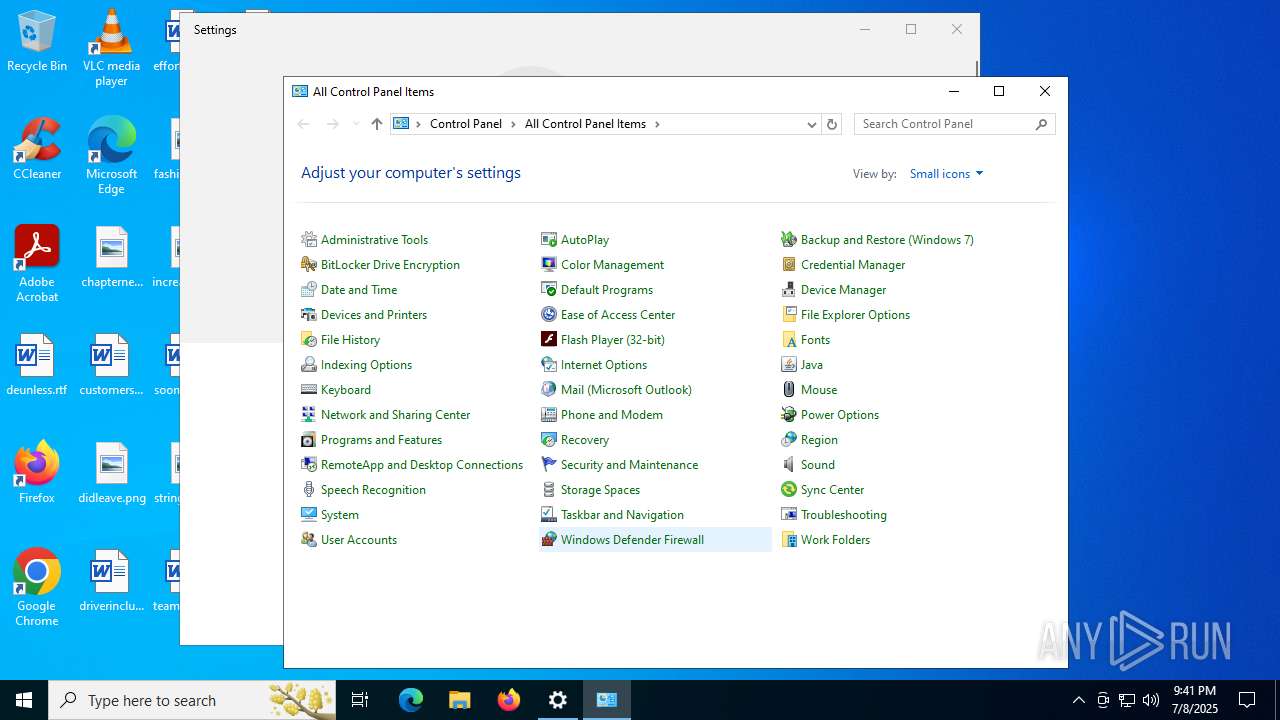
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| MD5: | 2B6EC04FC6DD8301153748C64F8B6B76 |
| SHA1: | 4FC890C7C3E8968915E605159E4D63EE72144CCC |
| SHA256: | DD2FAEB64777CFF25DEEC06F0CA47D2732E479B18AF0E44229DC3E935FDB4B85 |
| SSDEEP: | 3:gJ5LWwLGKI:gLGT |
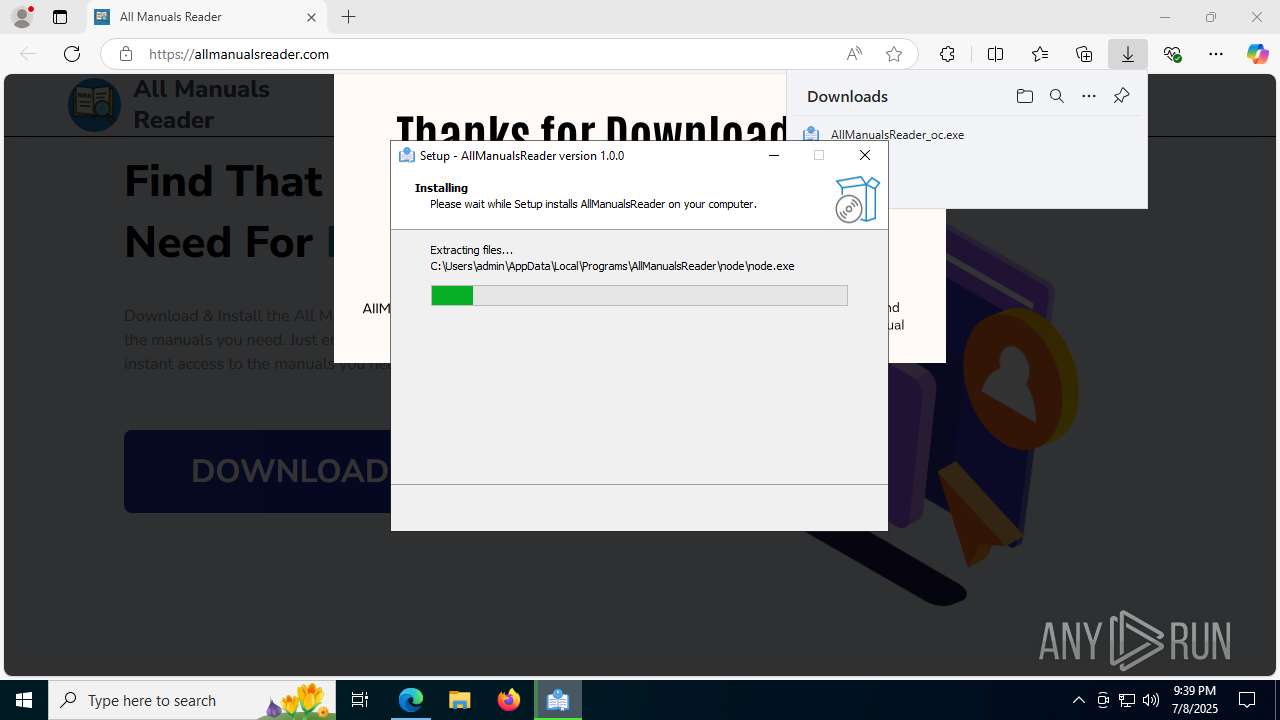
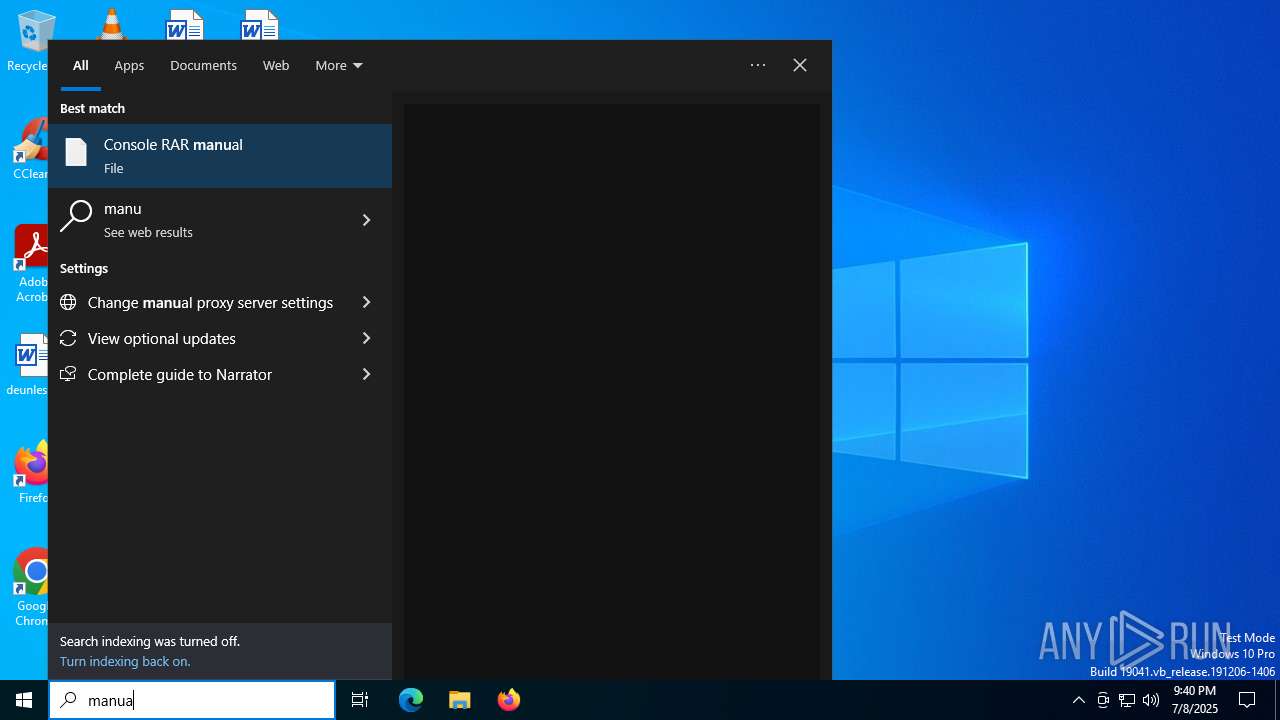
MALICIOUS
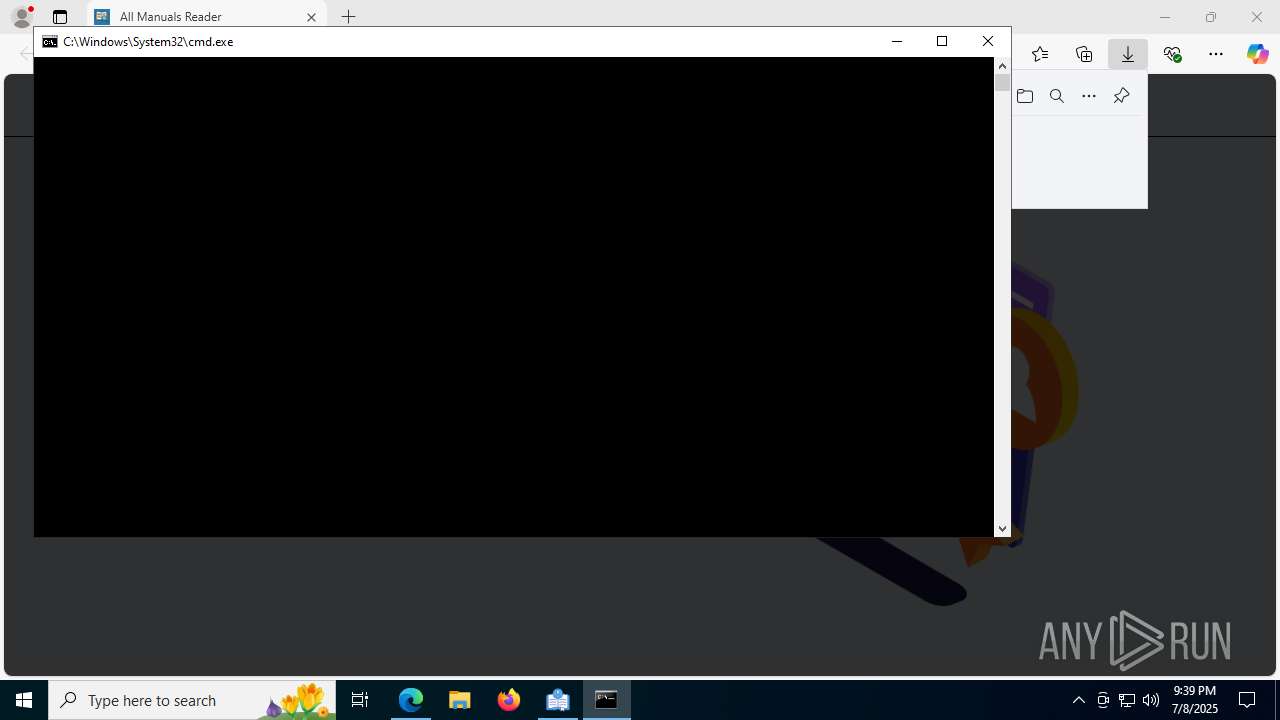
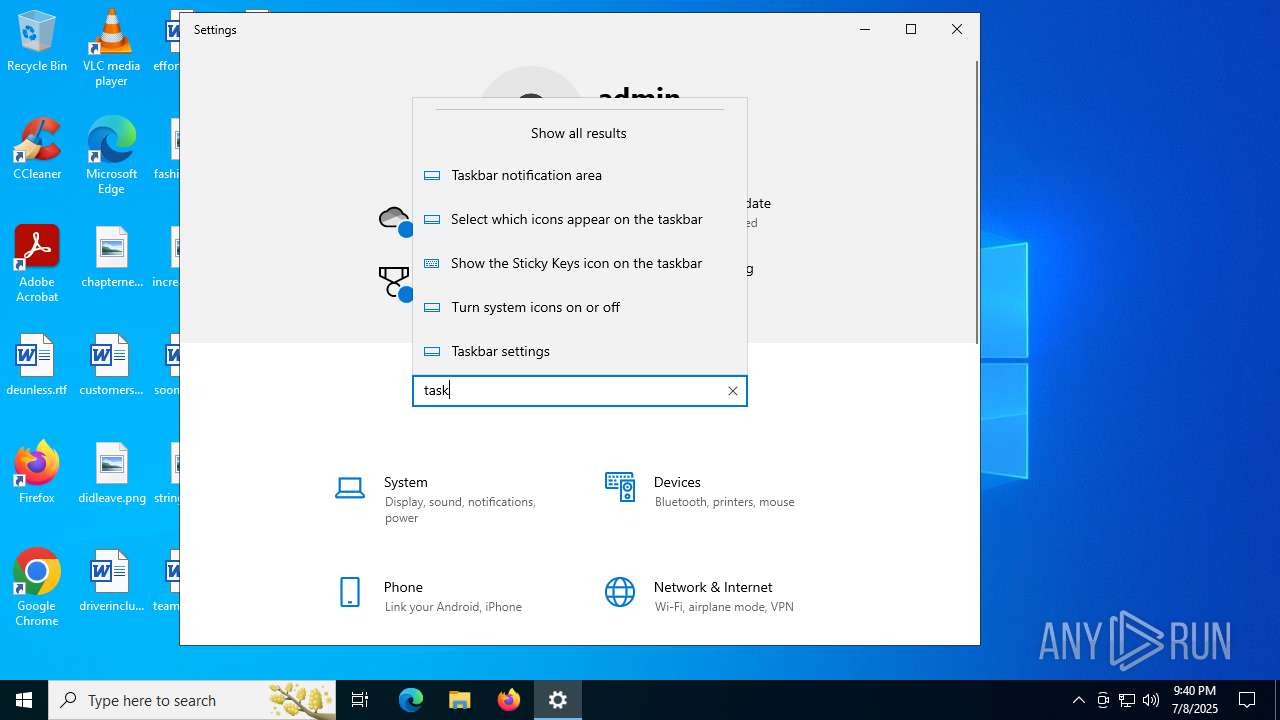
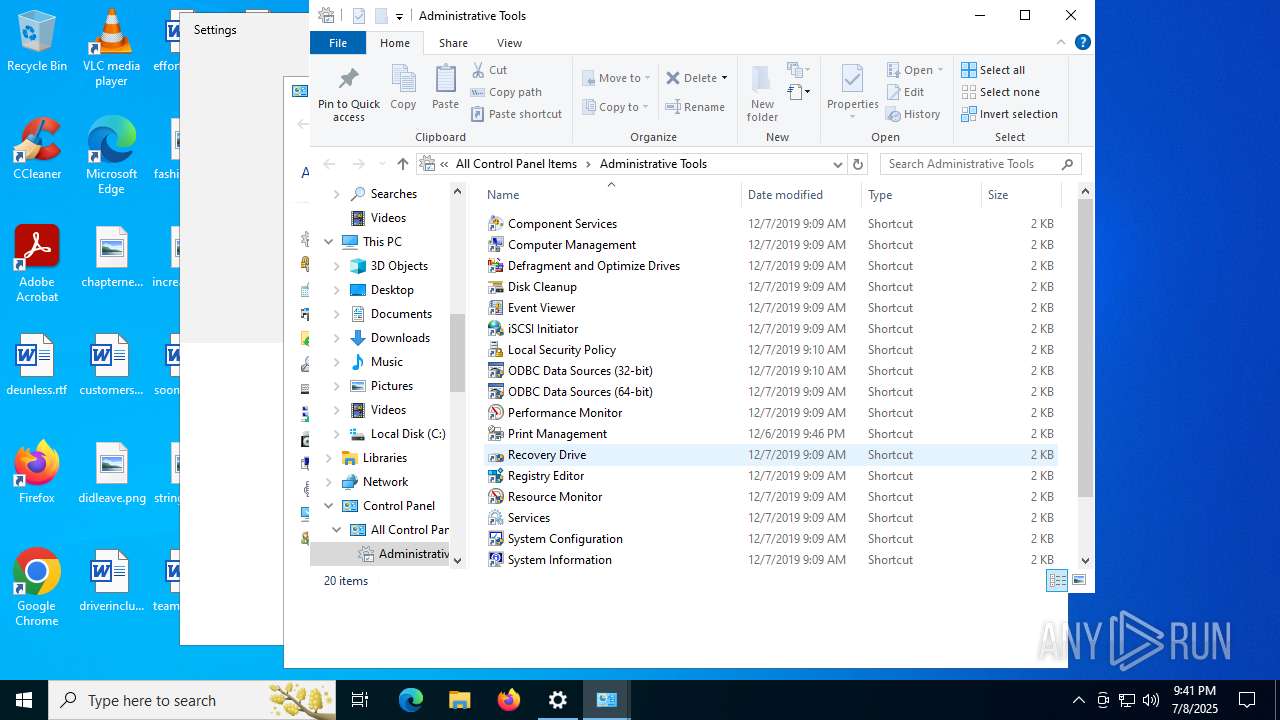
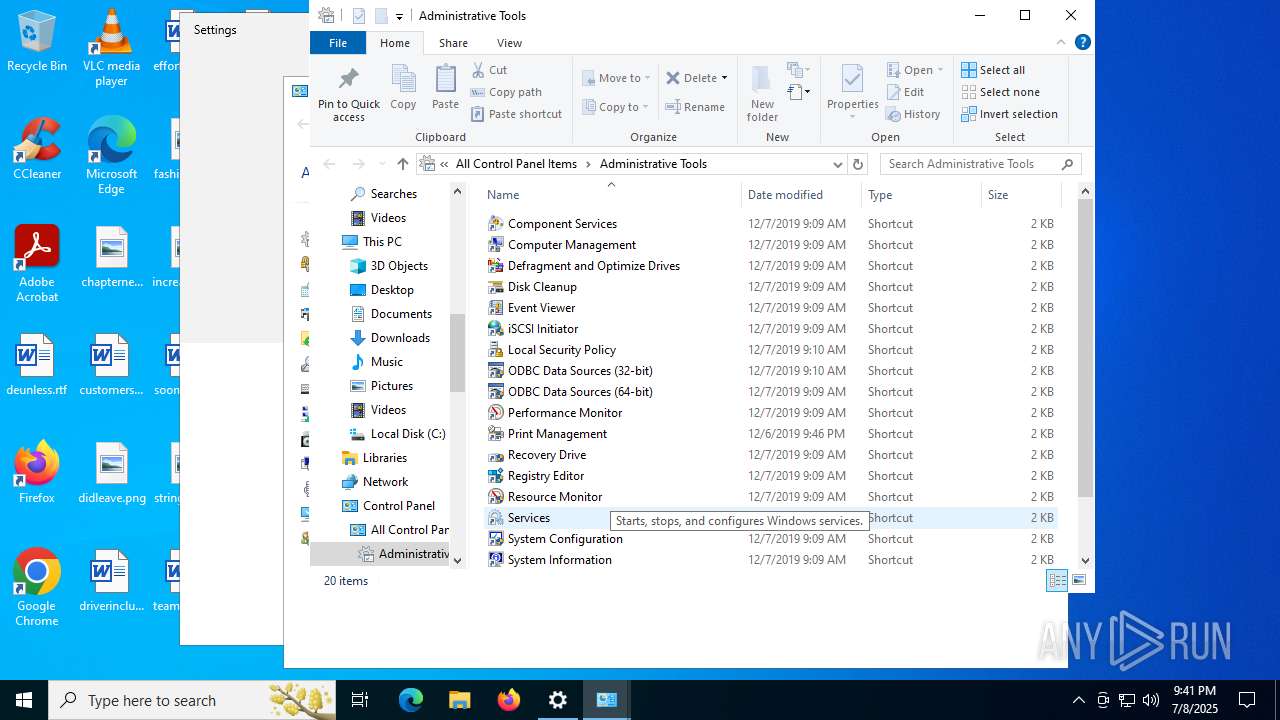
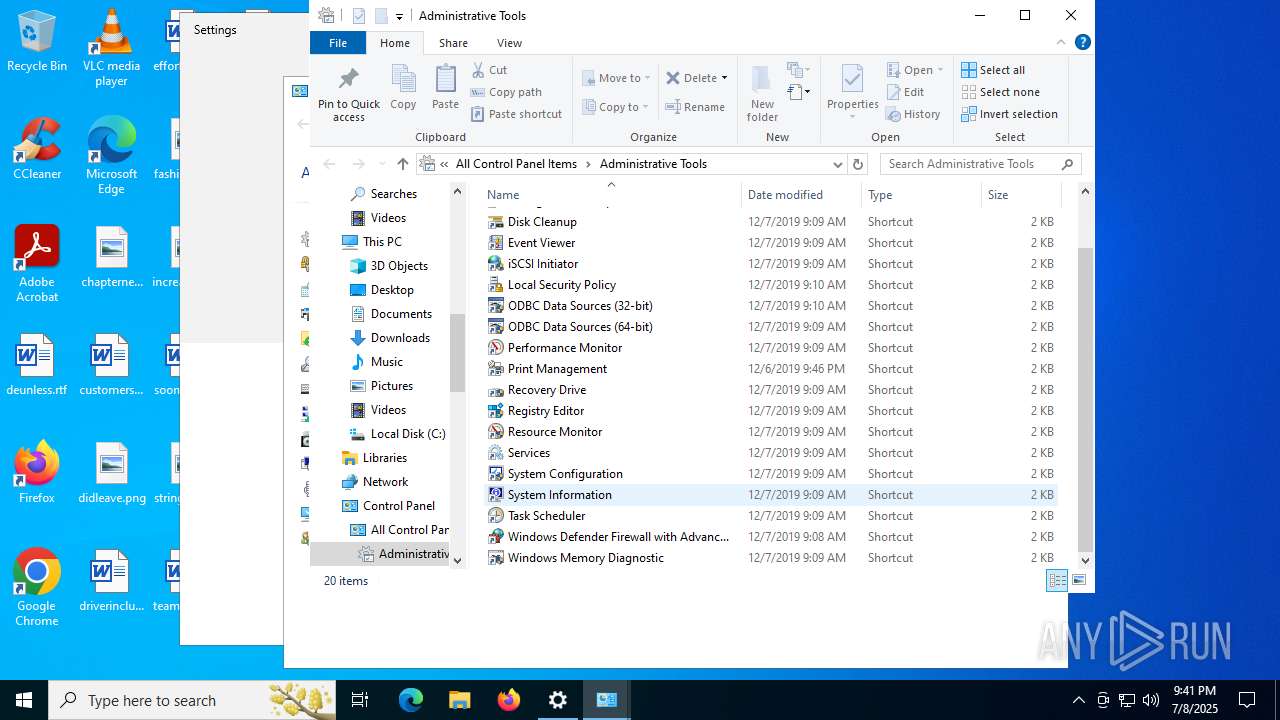
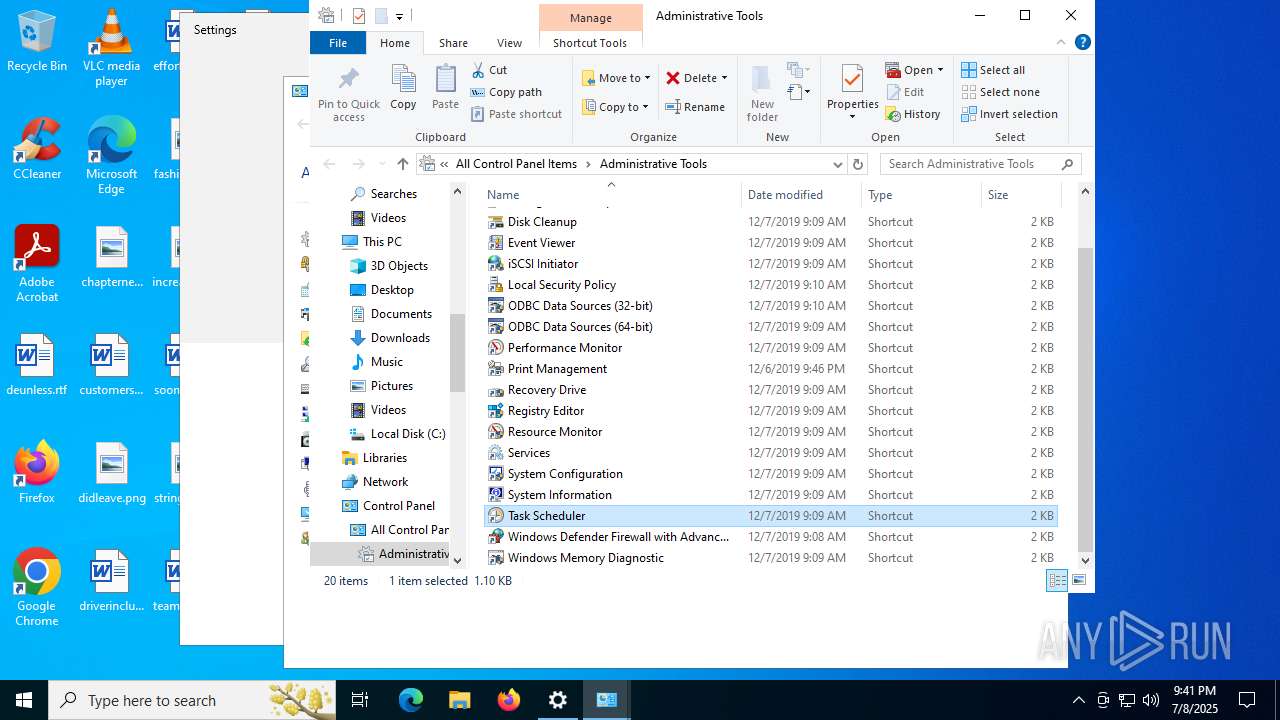
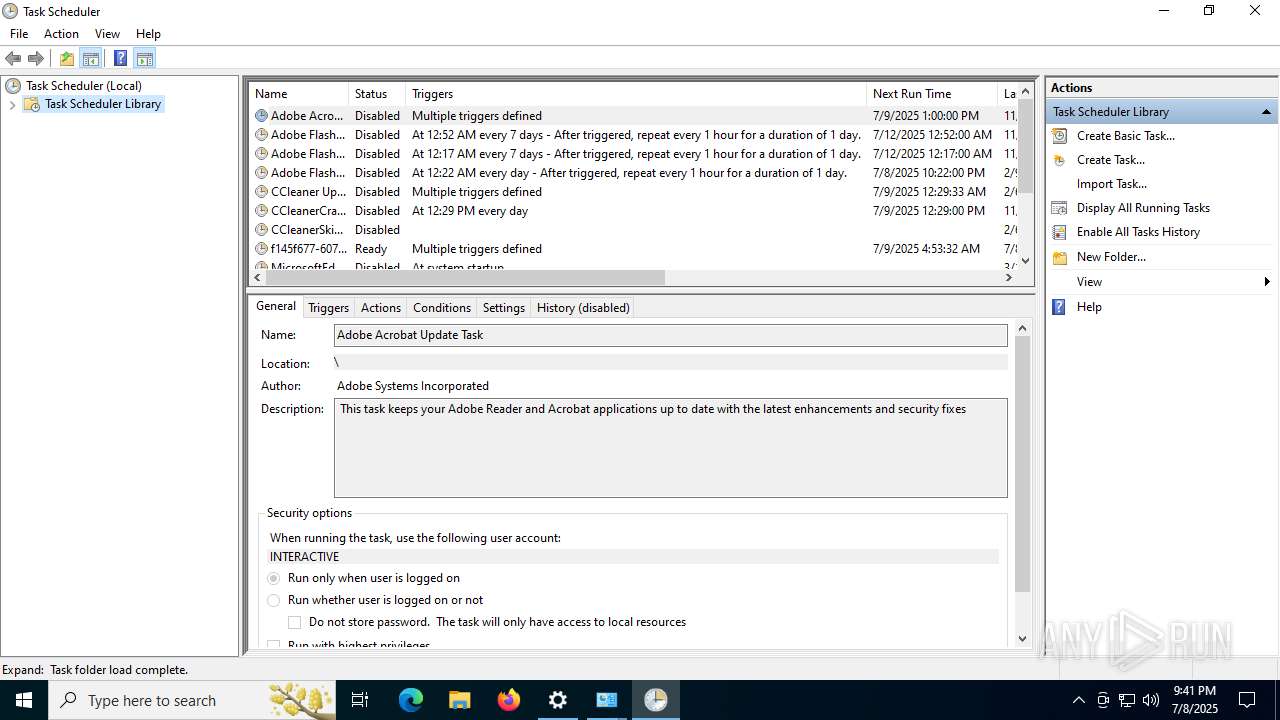
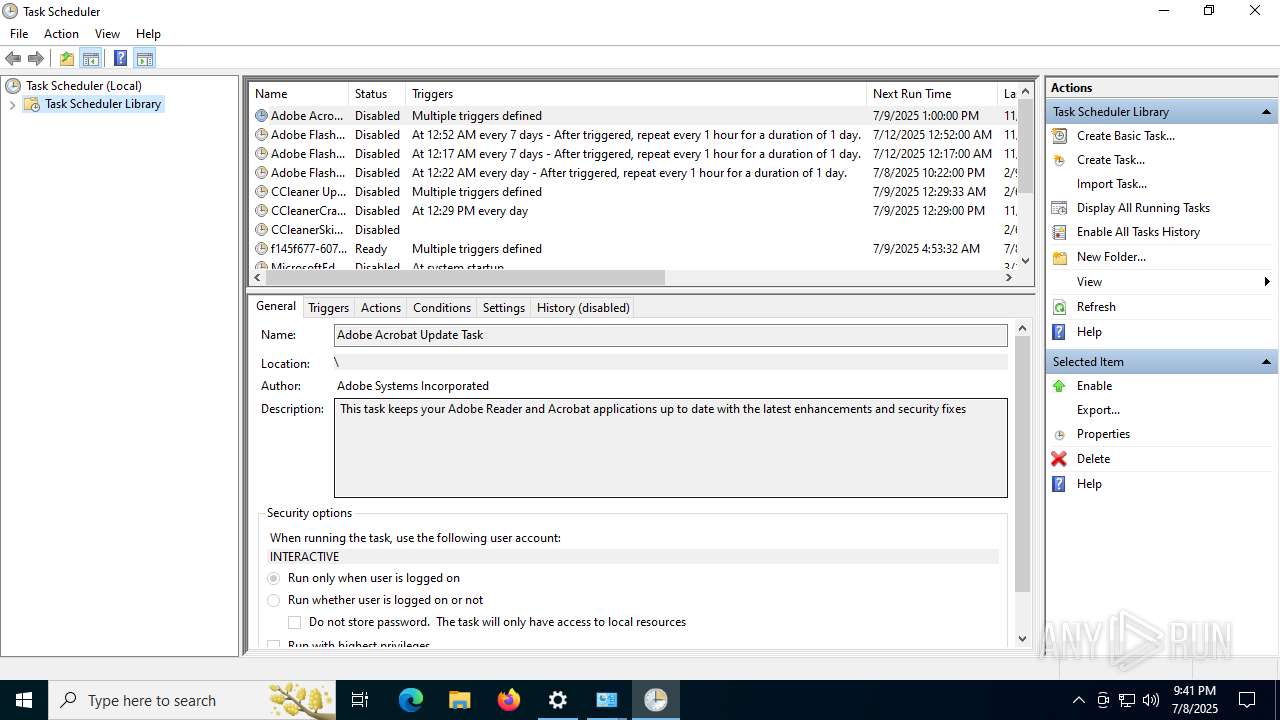
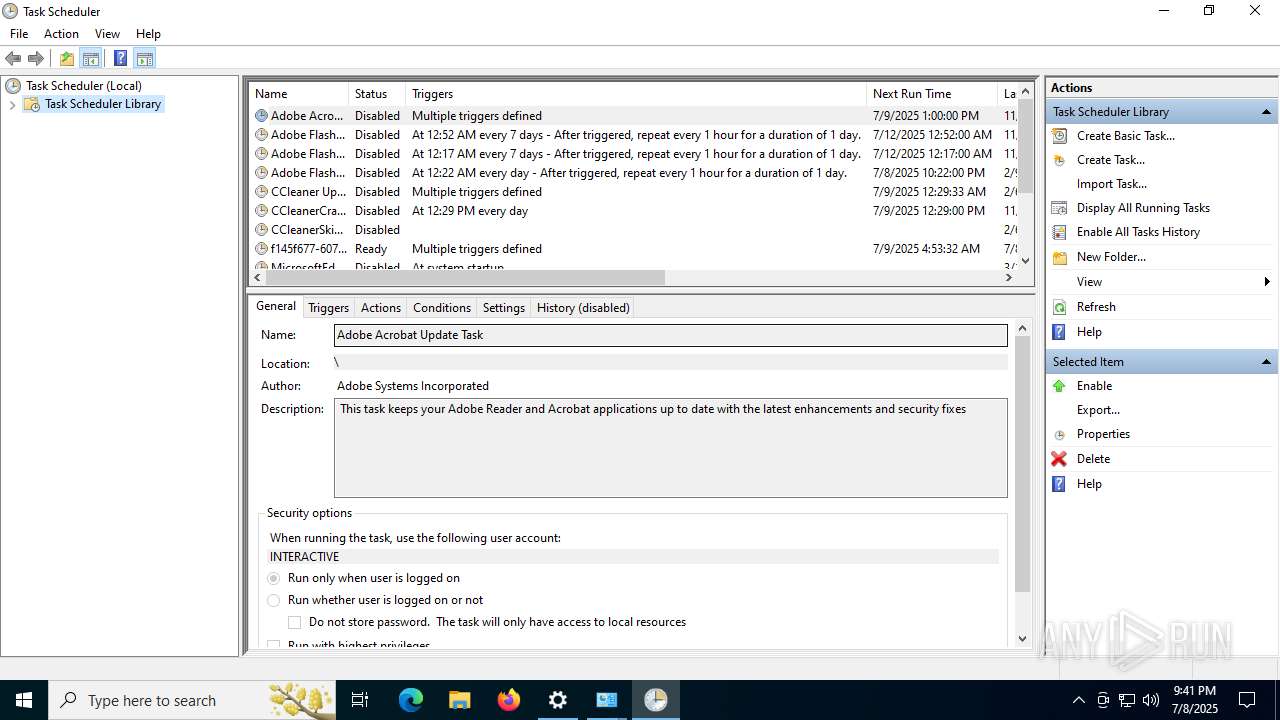
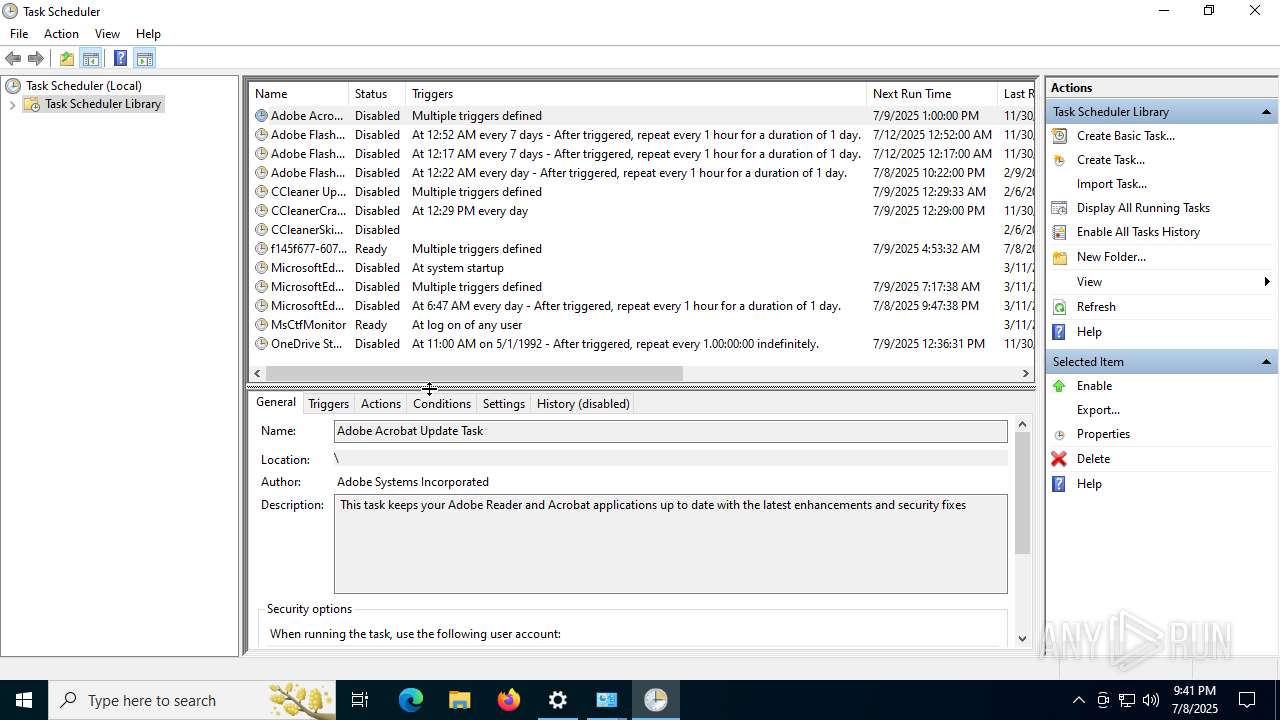
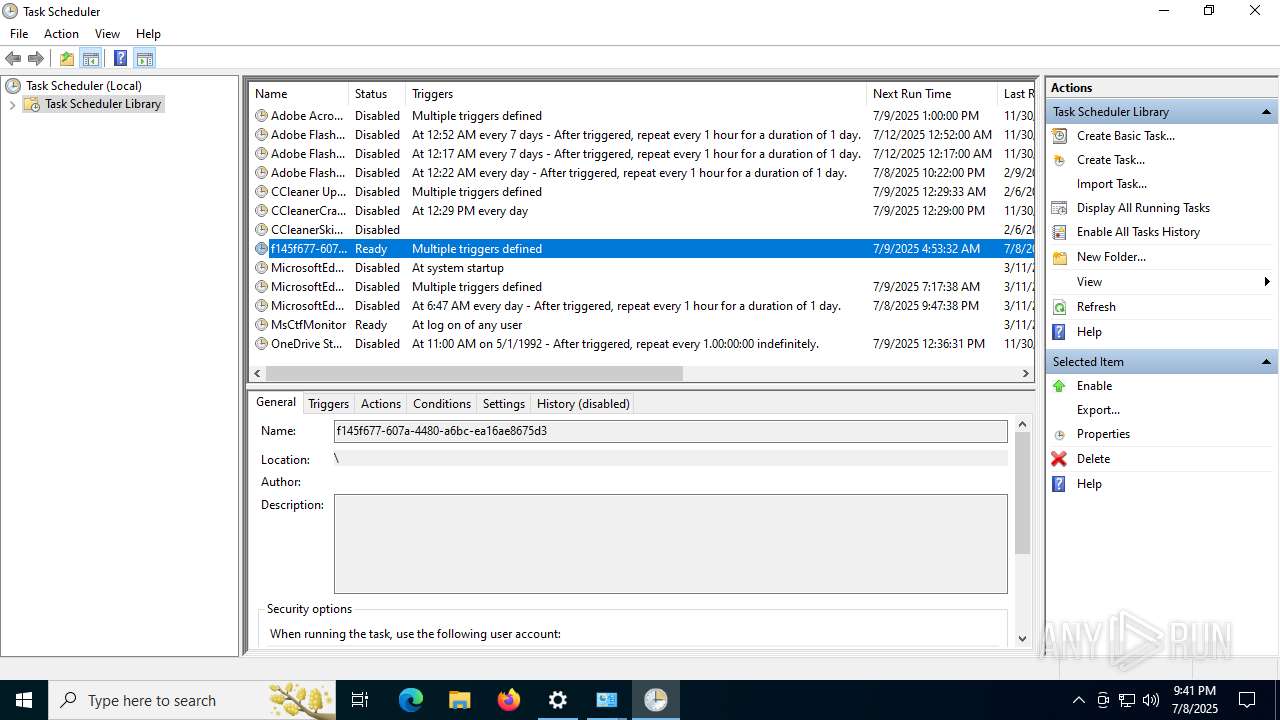
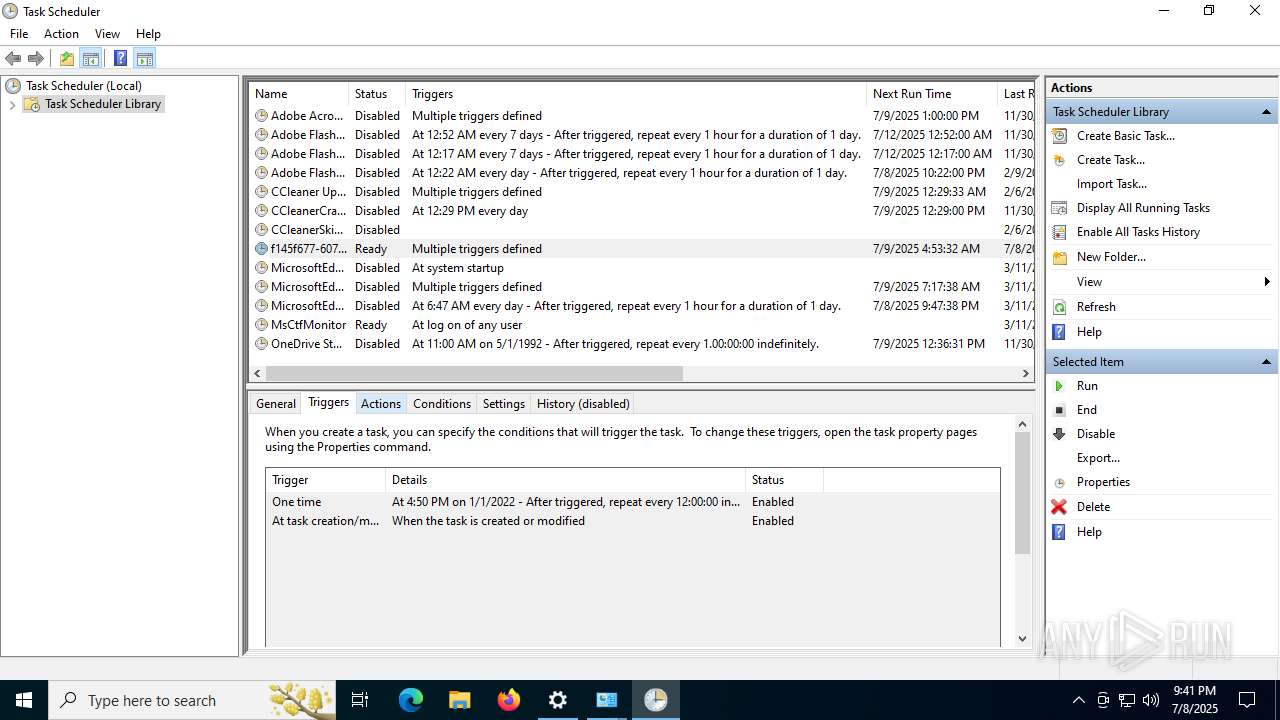
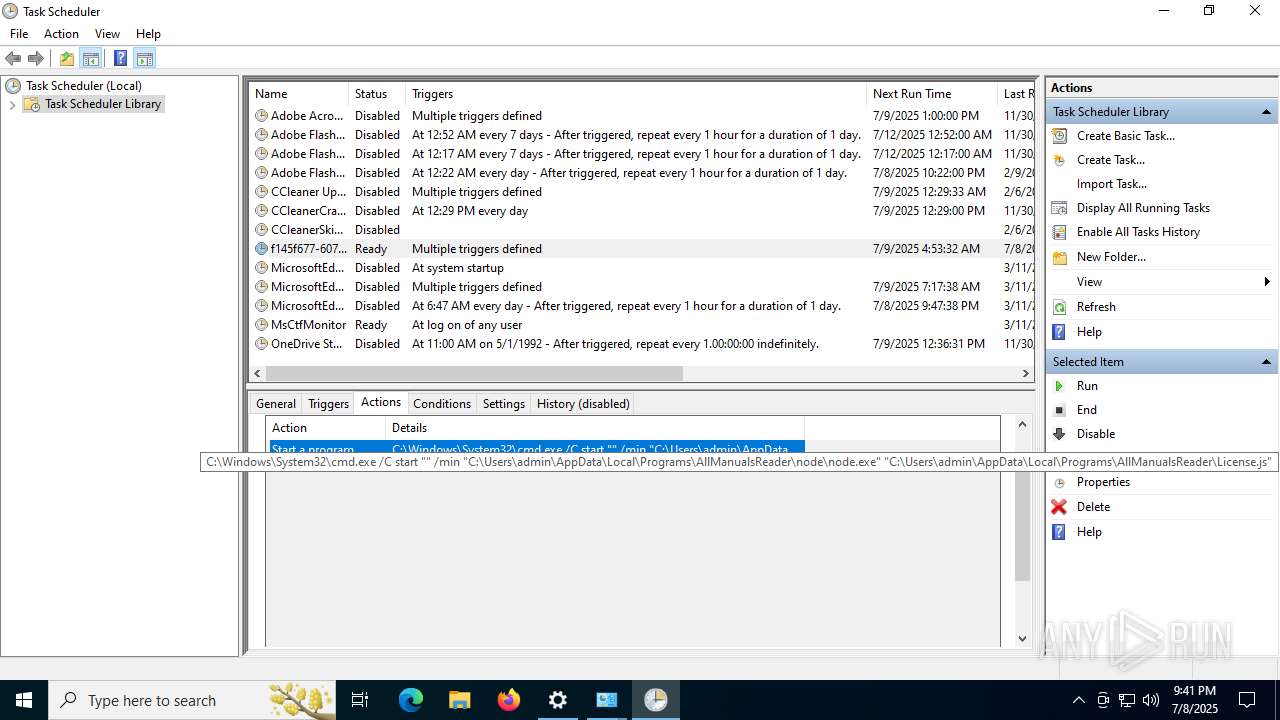
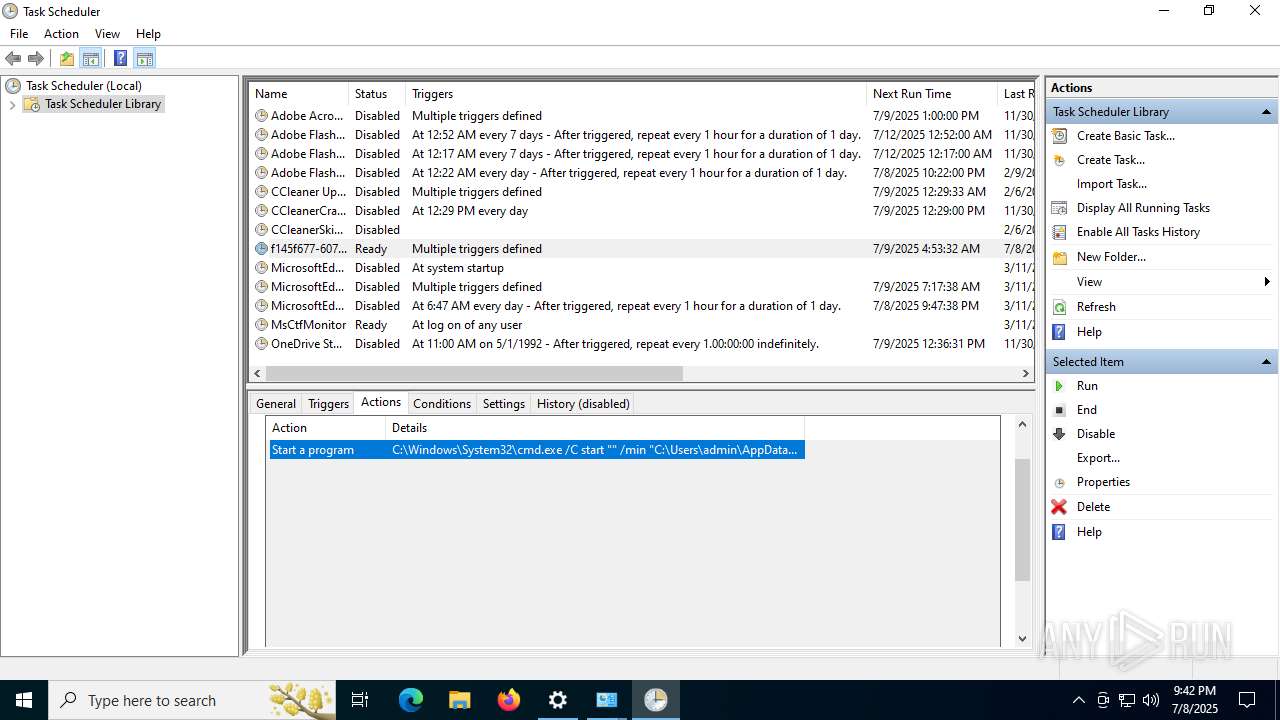
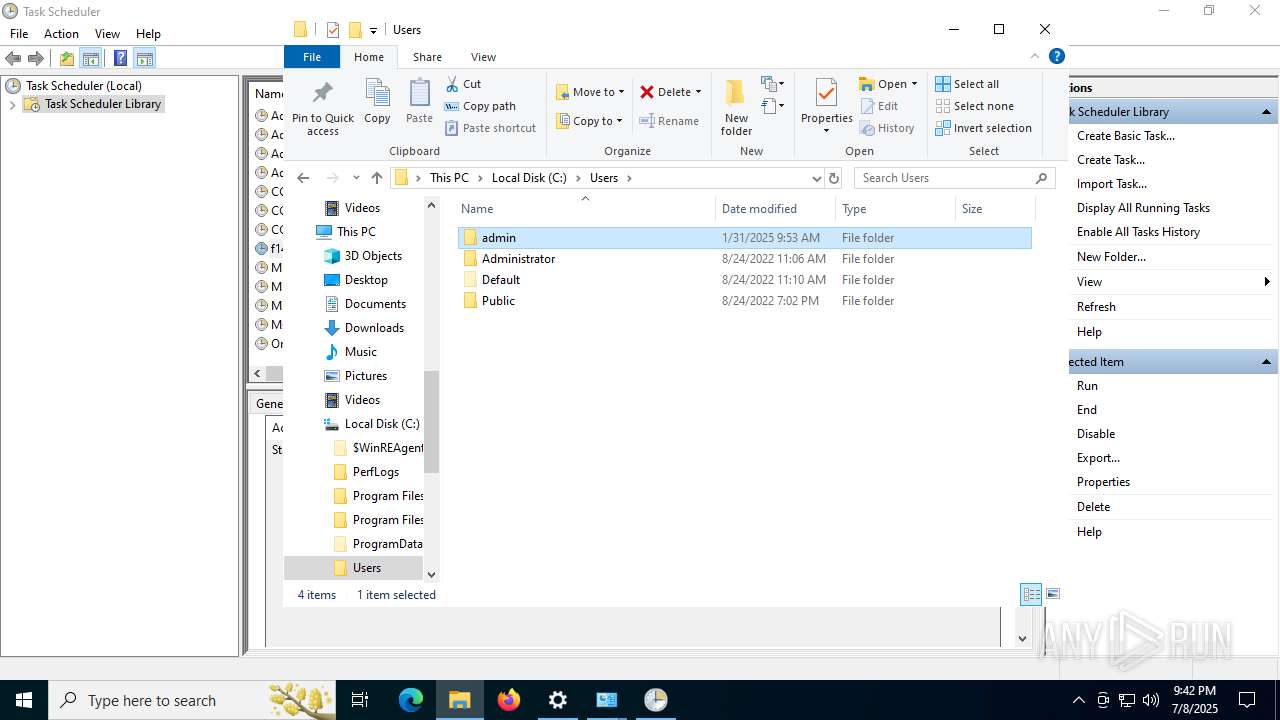
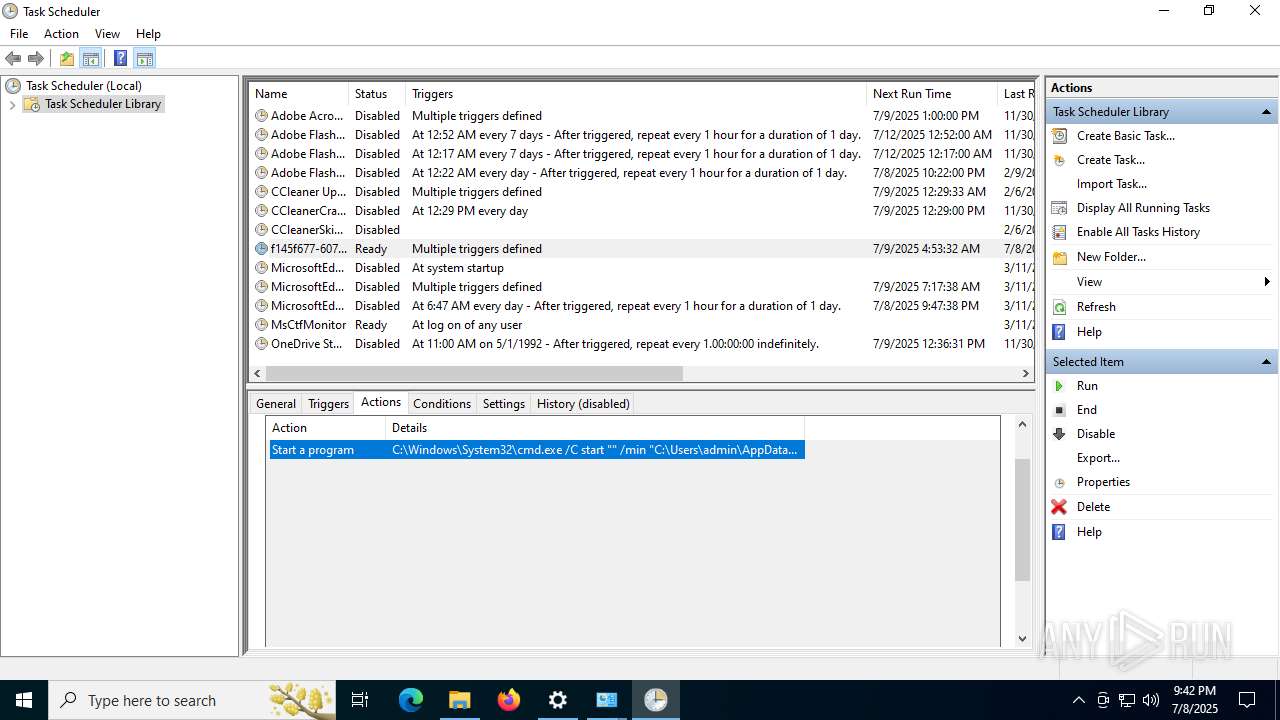
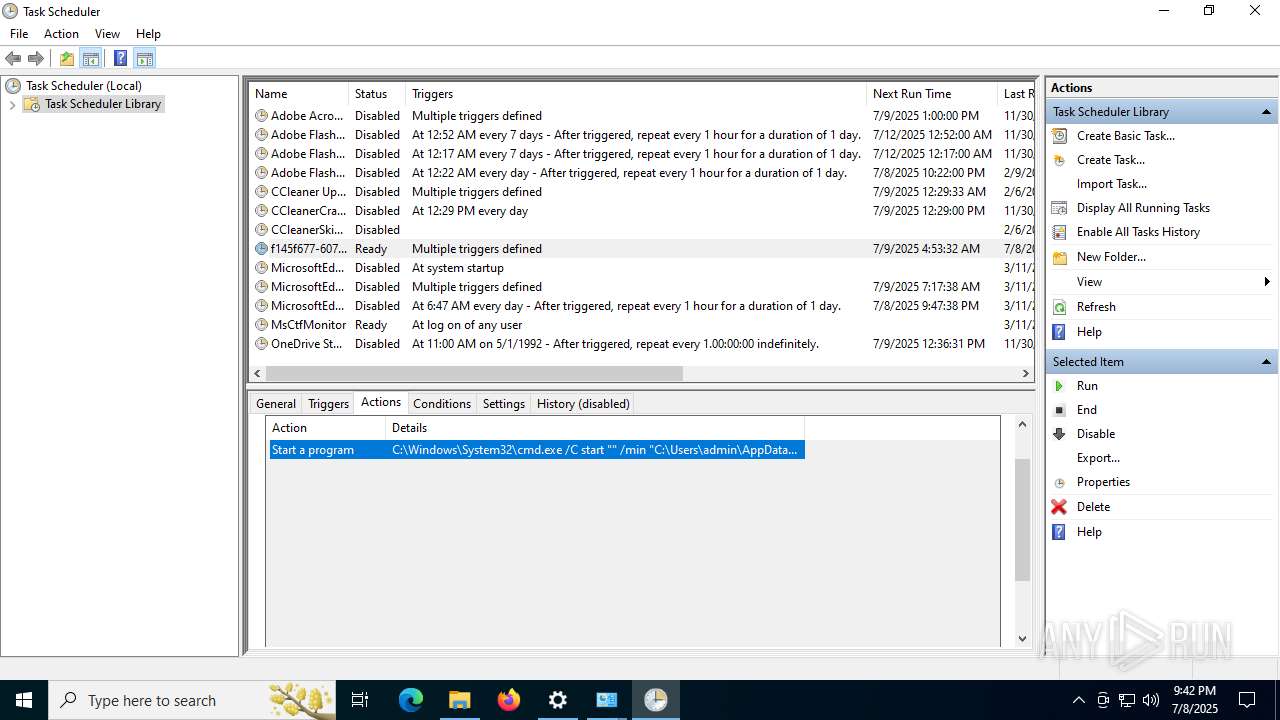
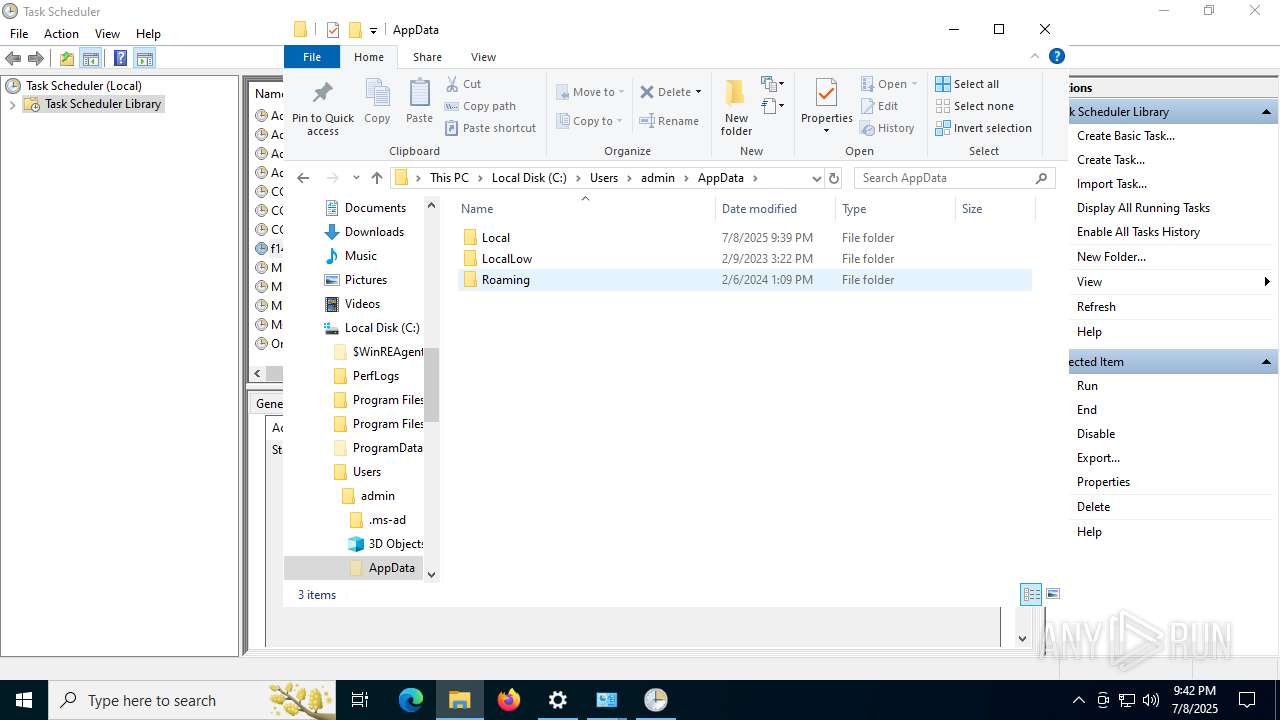
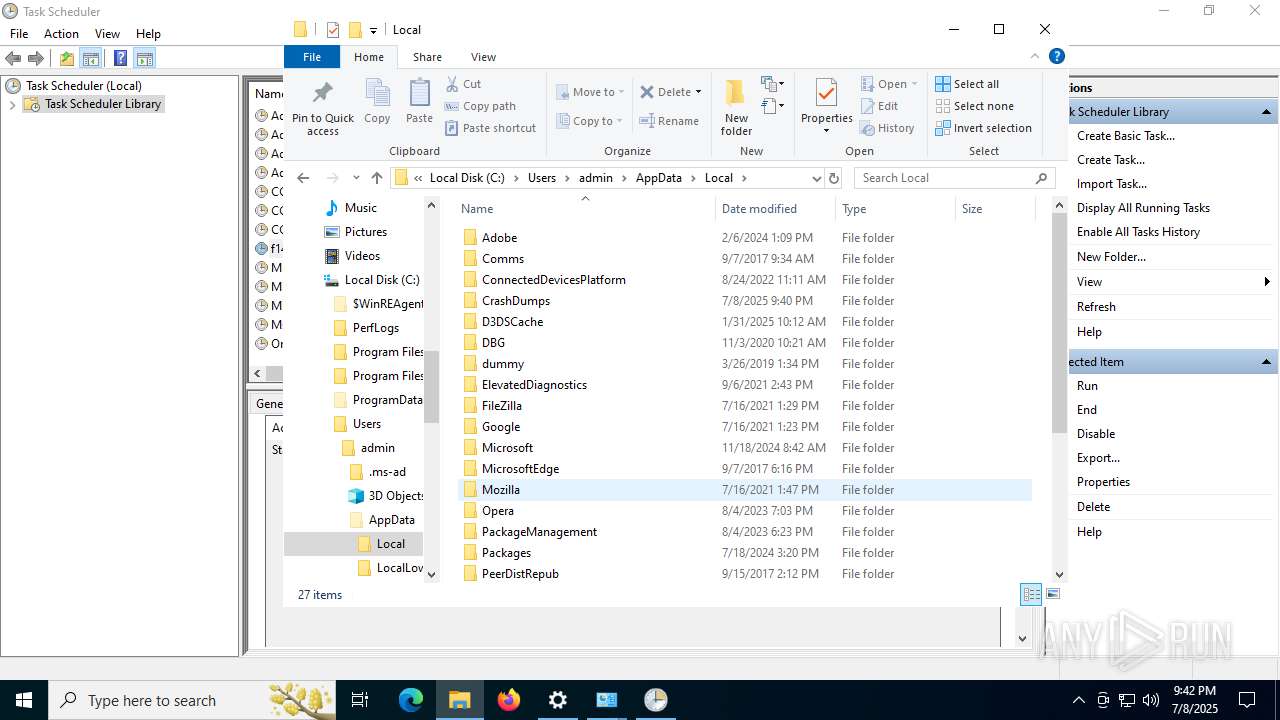
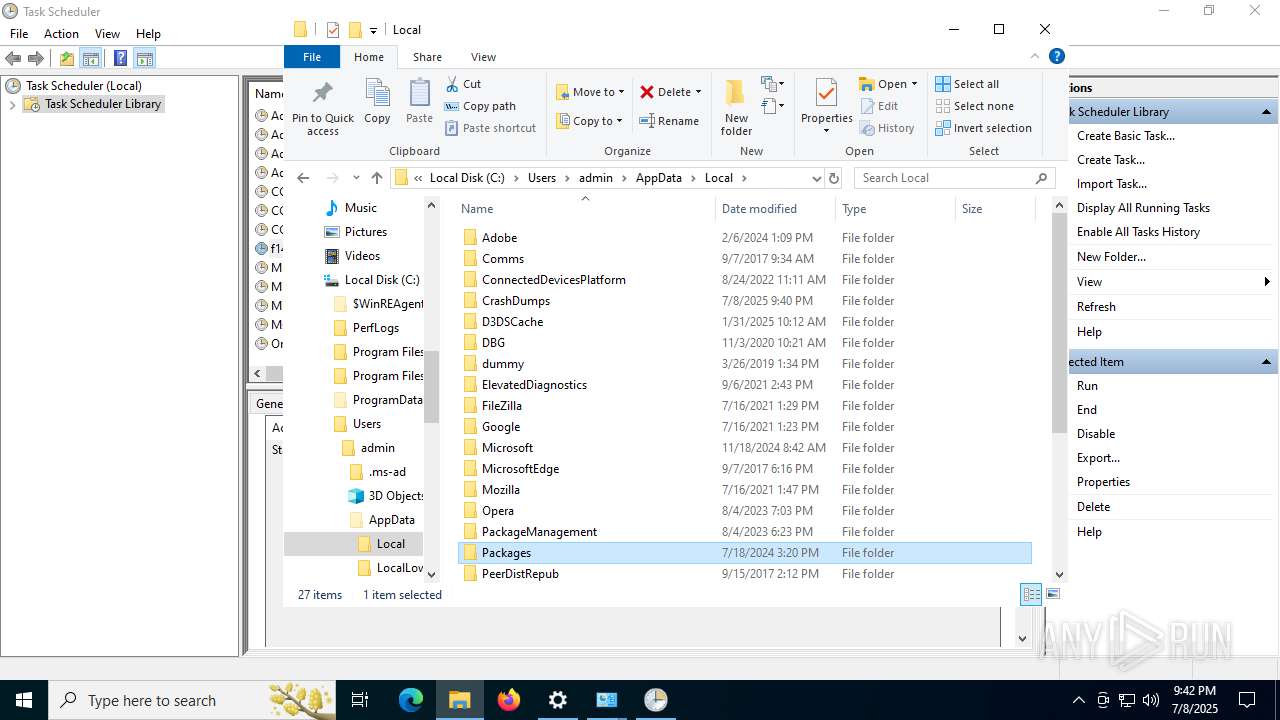
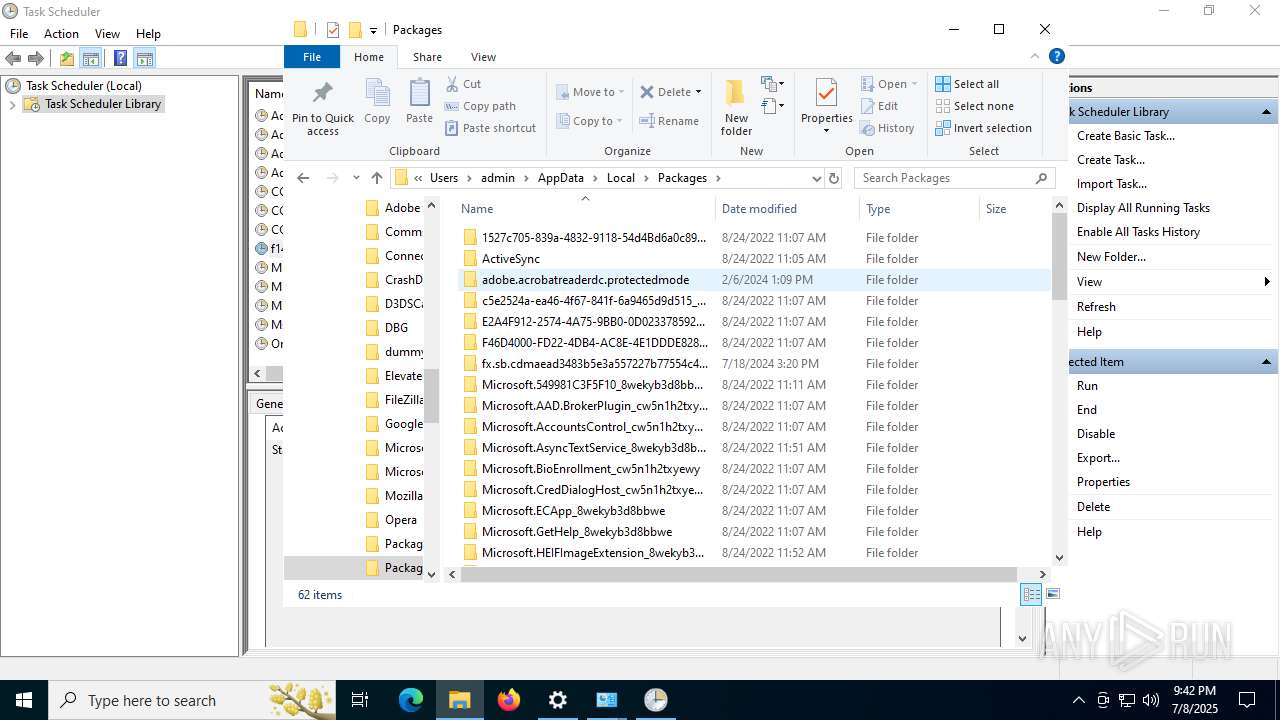
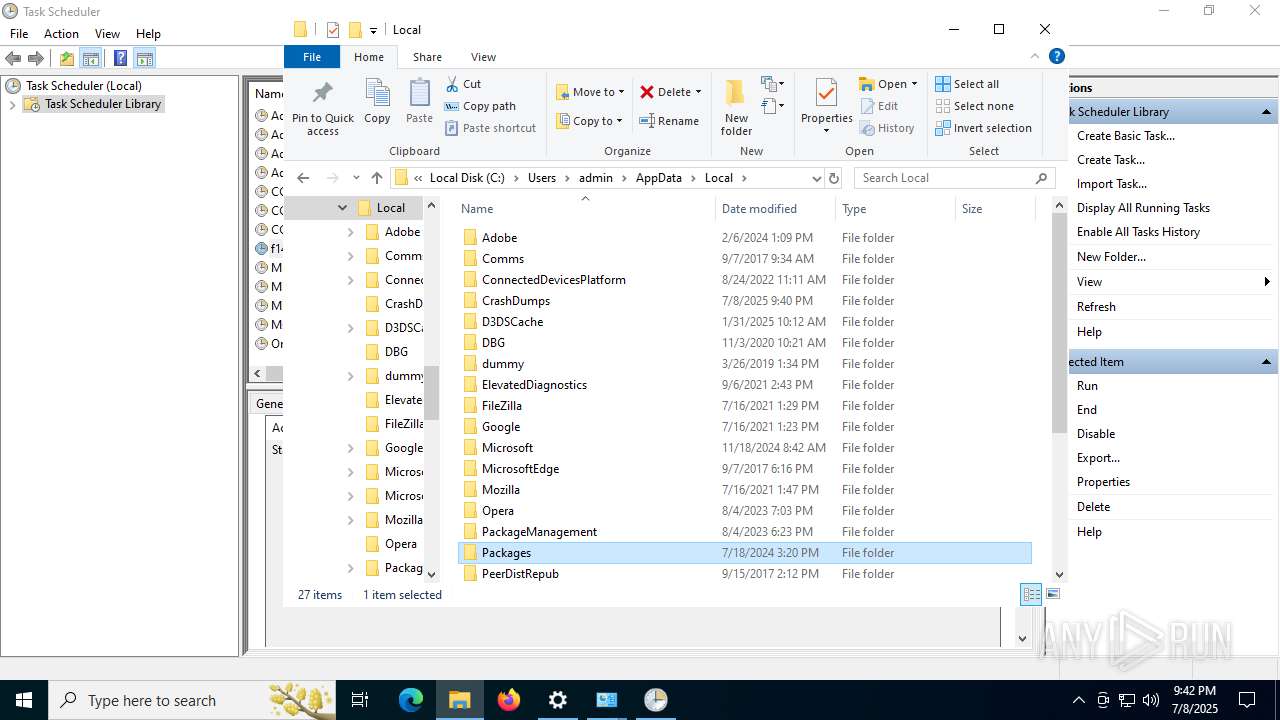
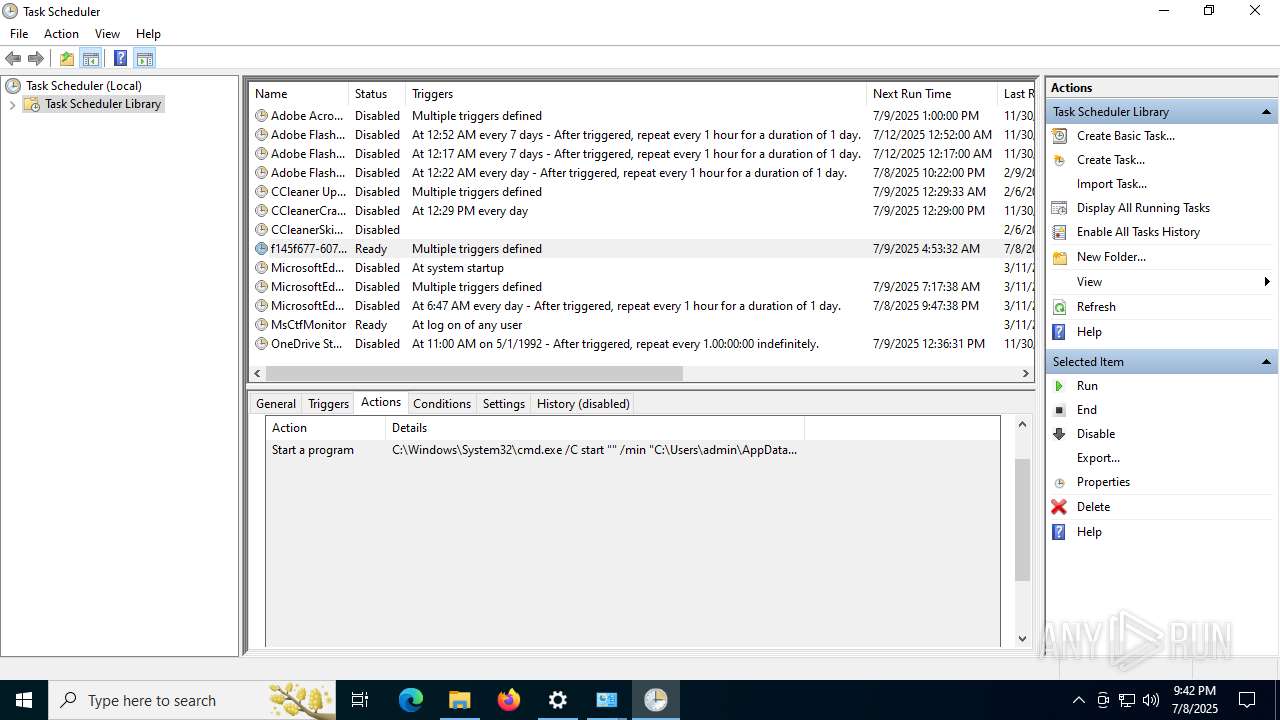
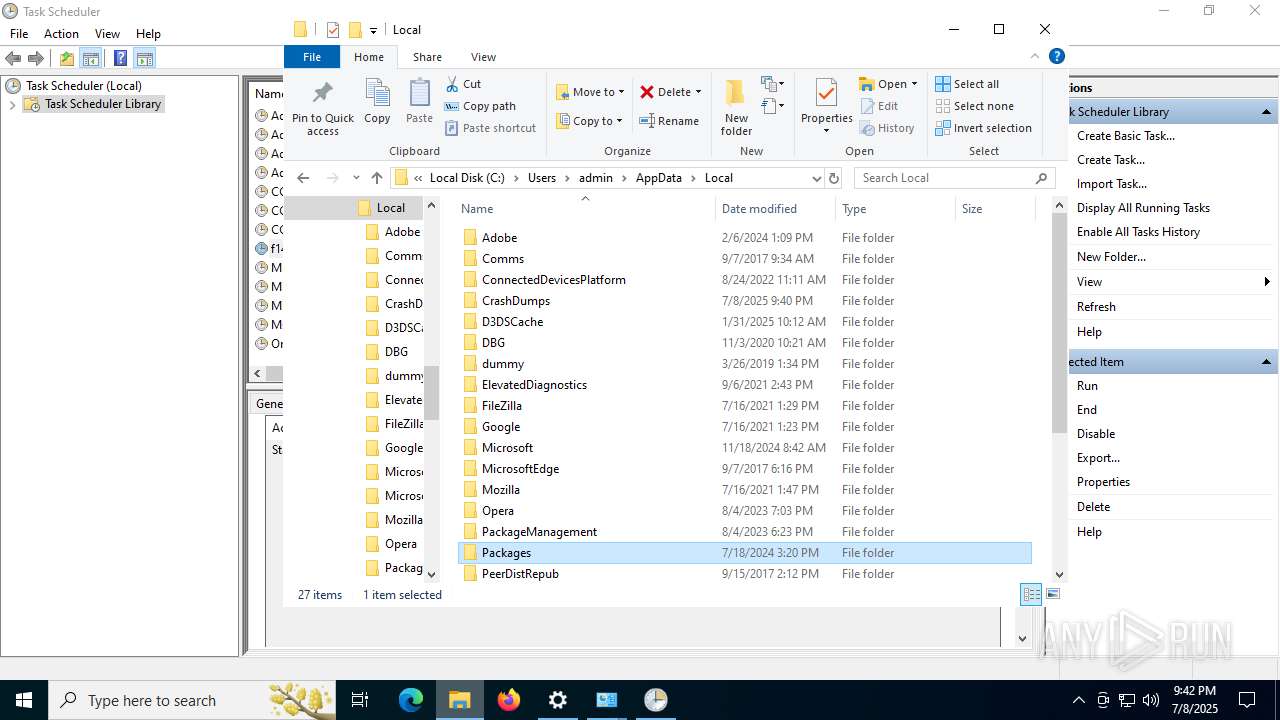
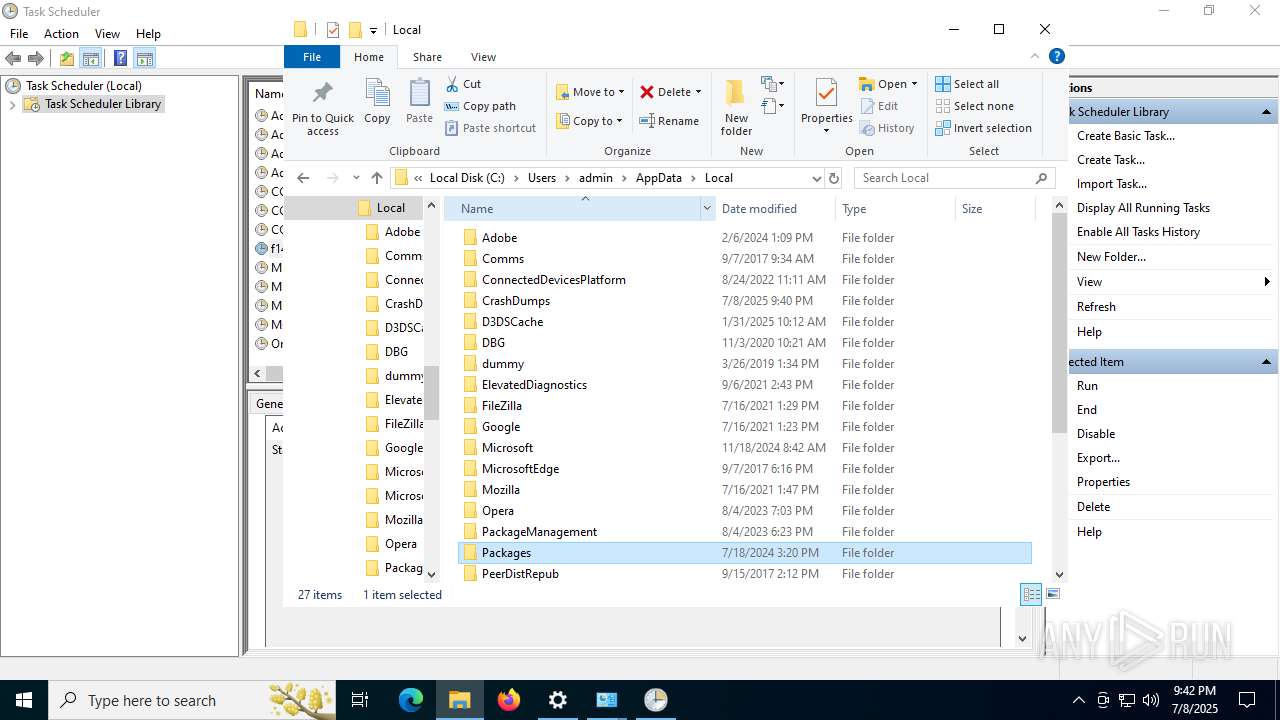
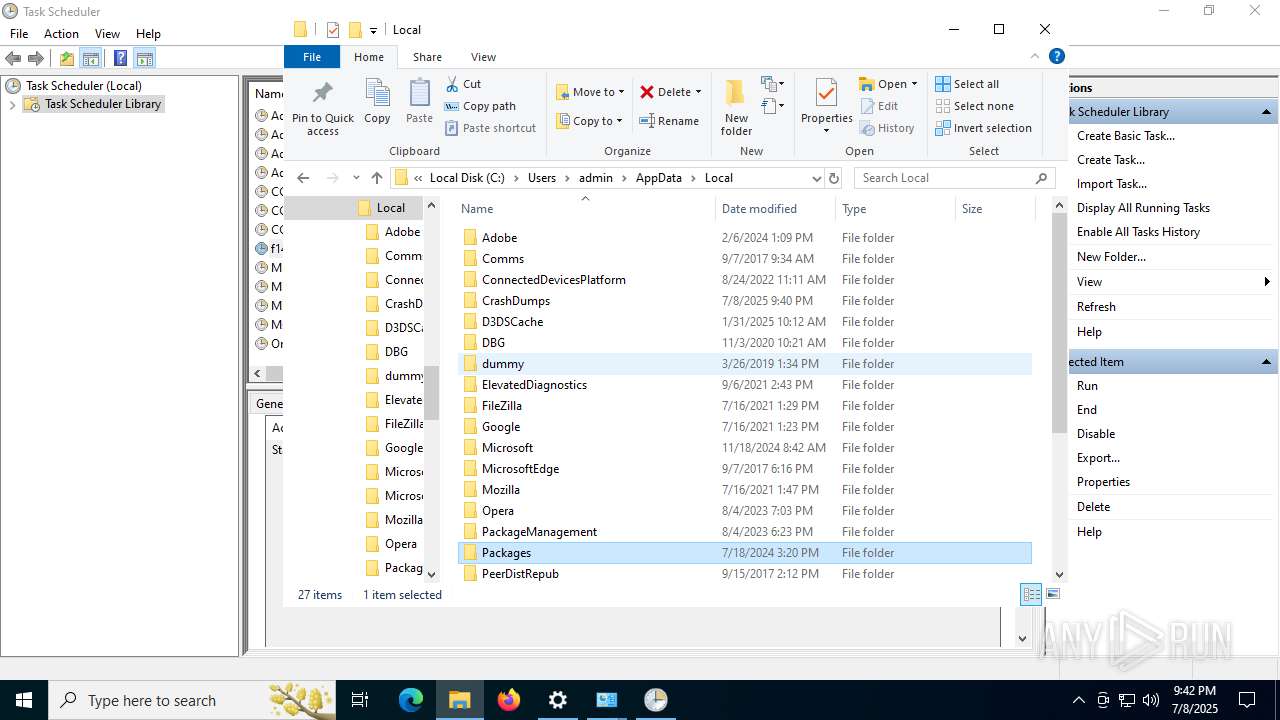
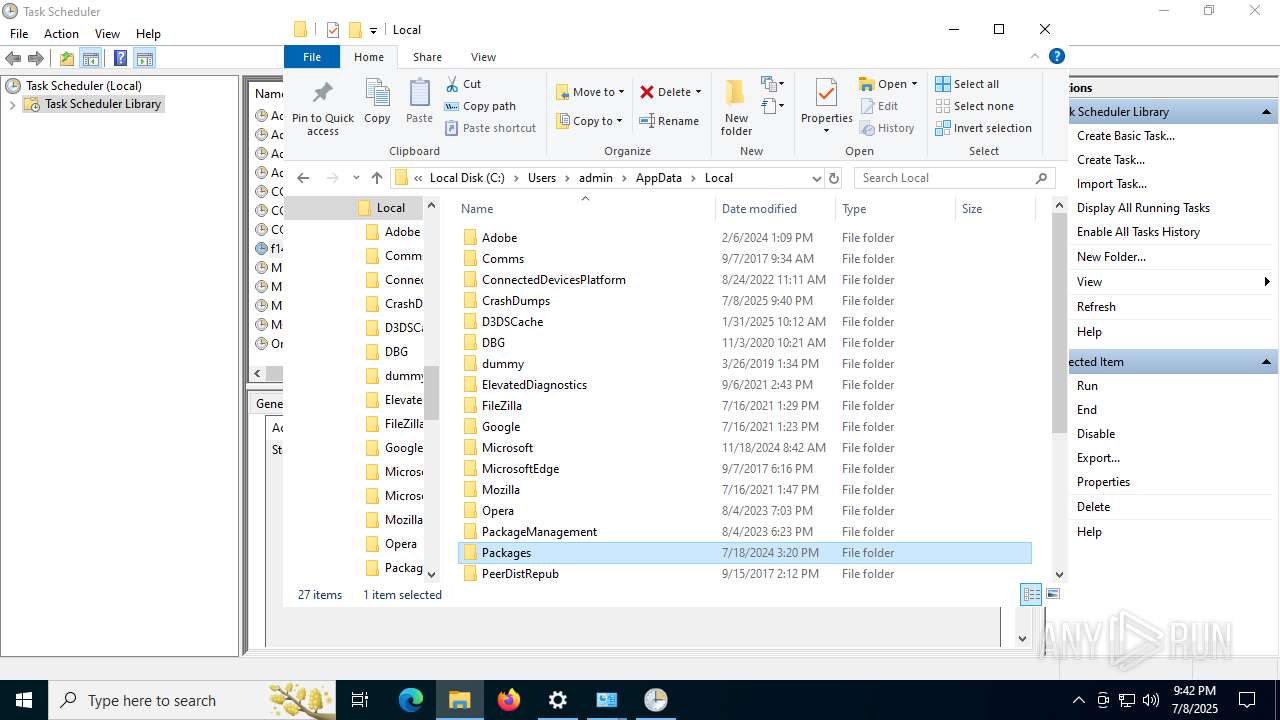
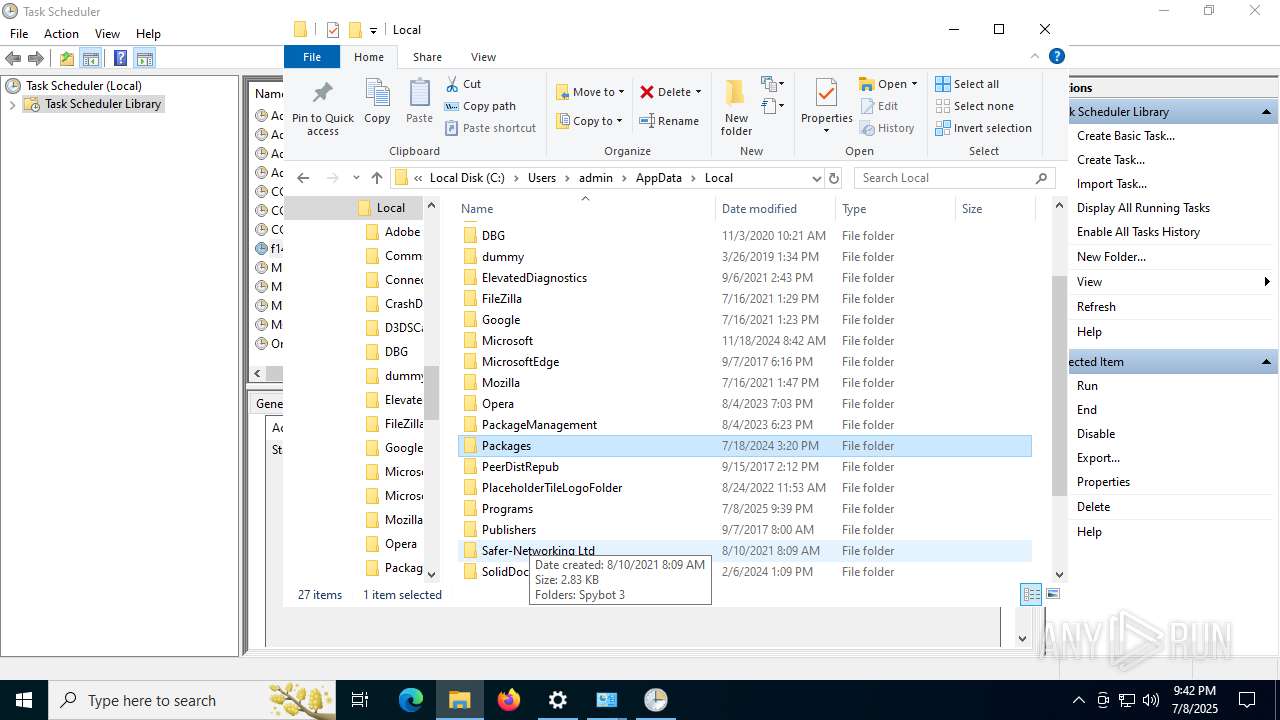
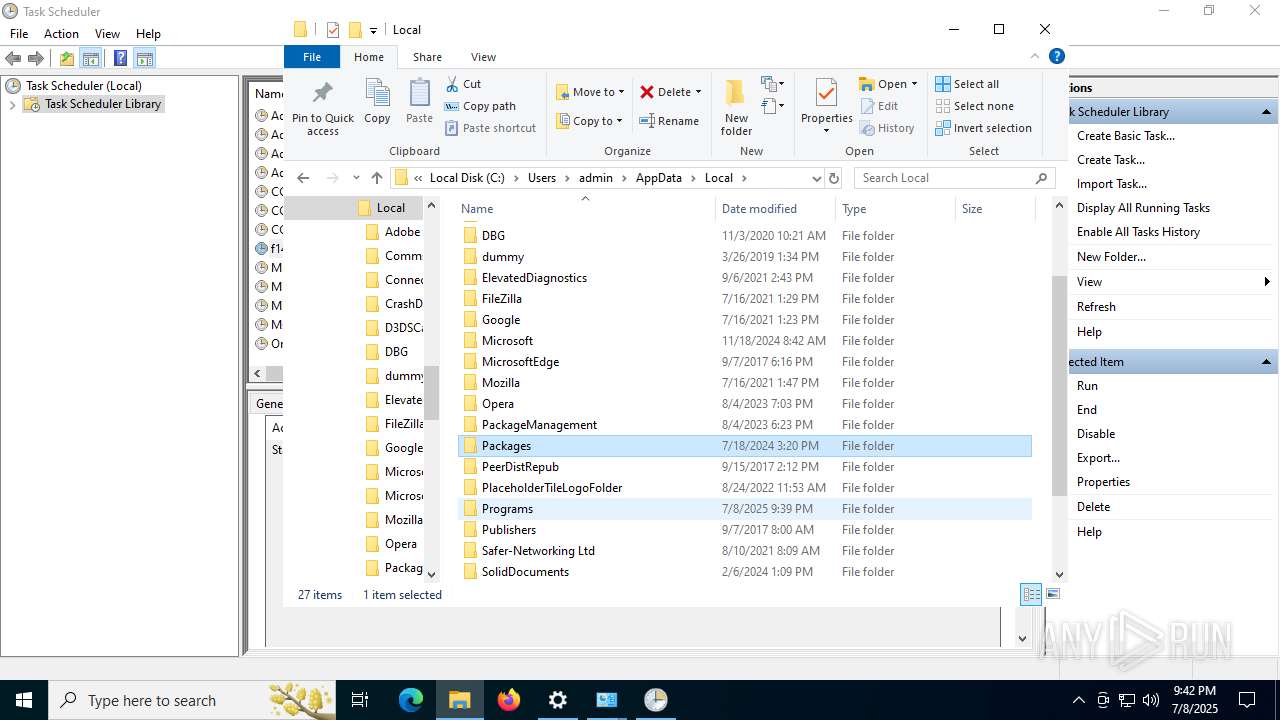
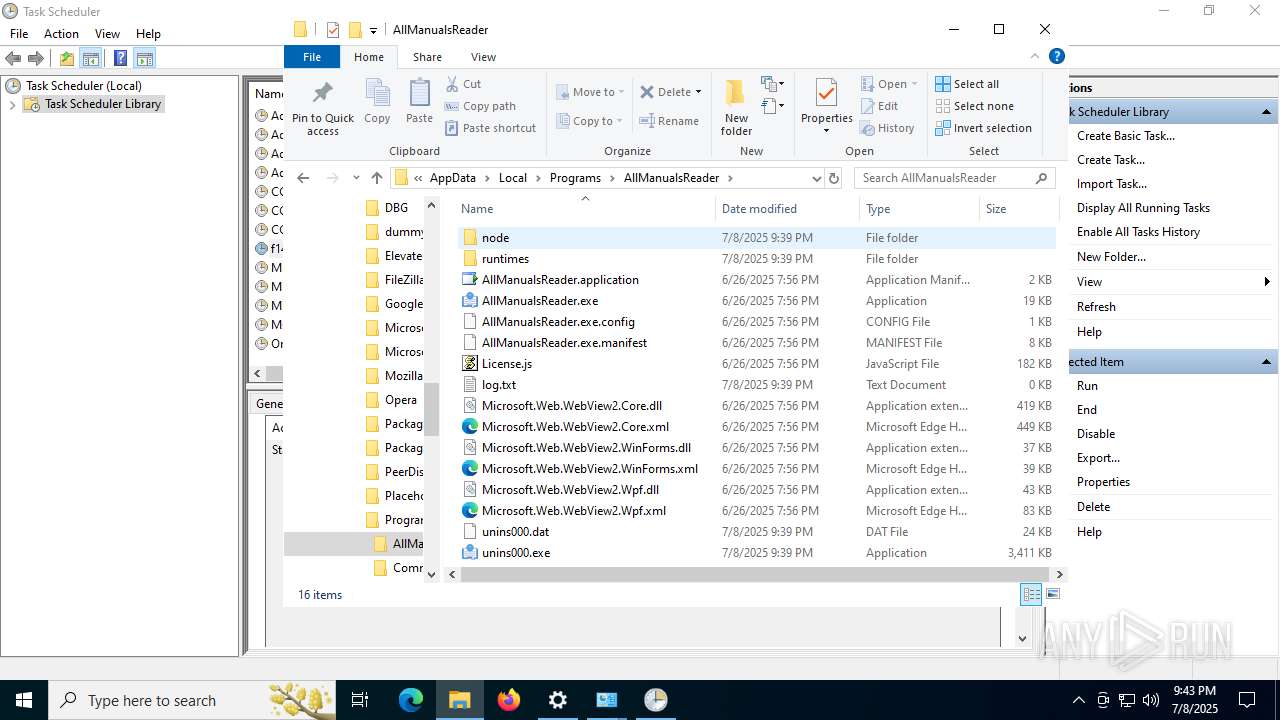
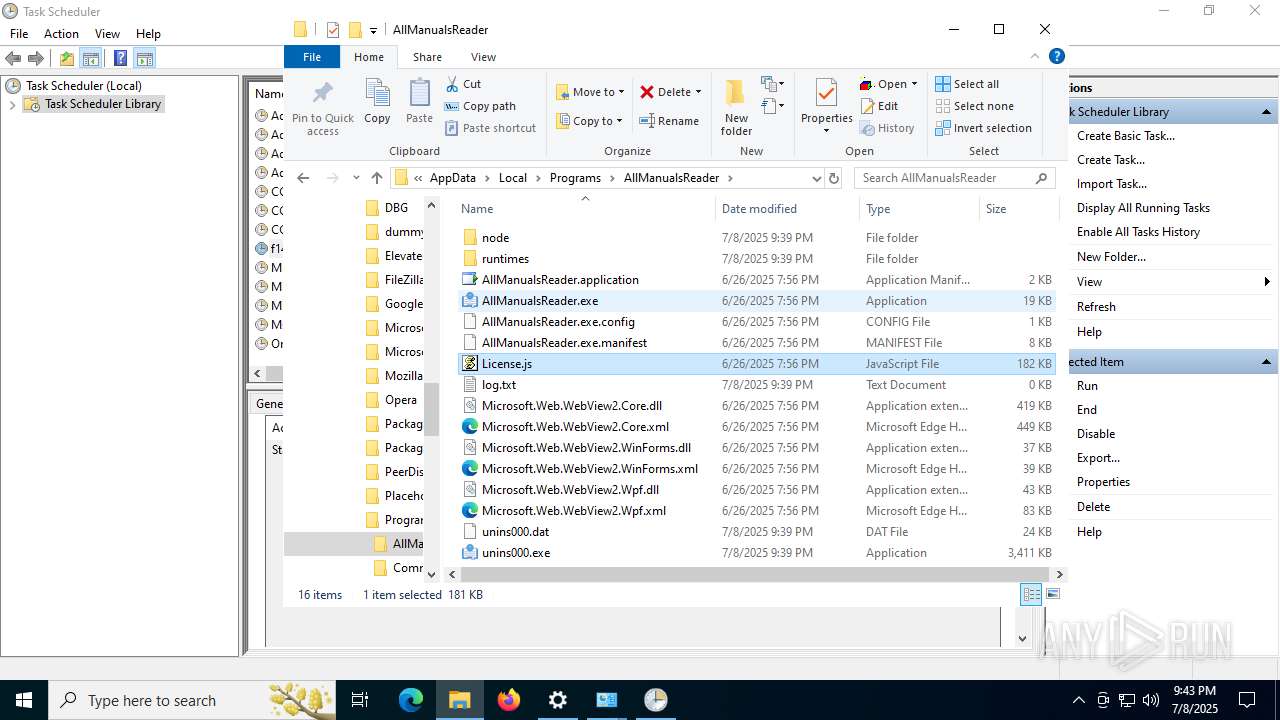
Uses Task Scheduler to run other applications
- cmd.exe (PID: 5244)
SUSPICIOUS
Reads the Windows owner or organization settings
- AllManualsReader_oc.tmp (PID: 8036)
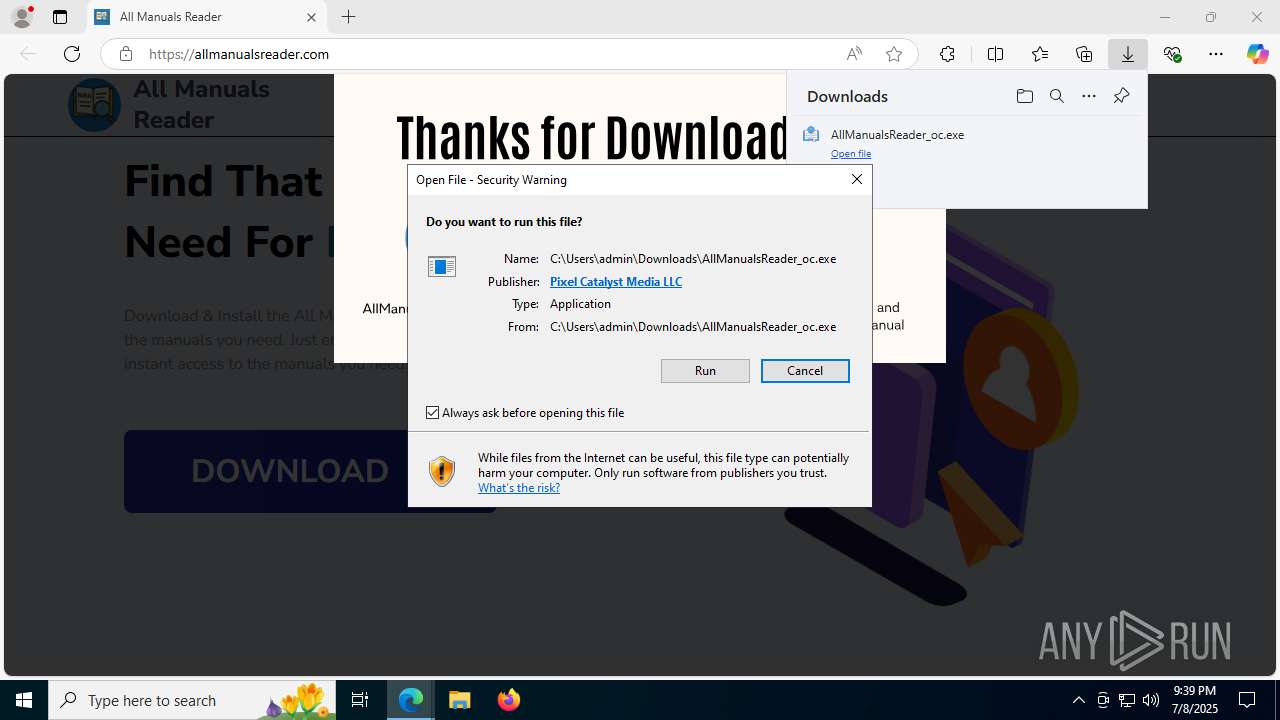
Executable content was dropped or overwritten
- AllManualsReader_oc.exe (PID: 6128)
- AllManualsReader_oc.tmp (PID: 8036)
Process drops legitimate windows executable
- AllManualsReader_oc.tmp (PID: 8036)
The process executes via Task Scheduler
- cmd.exe (PID: 4112)
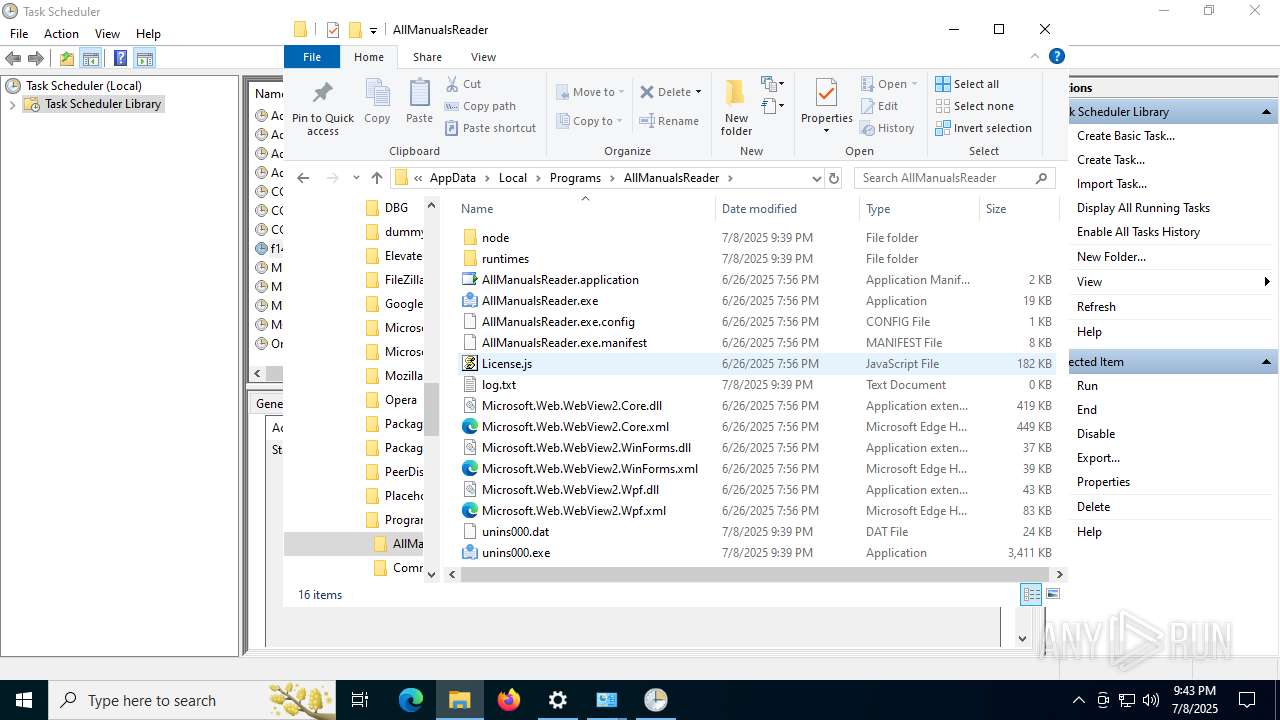
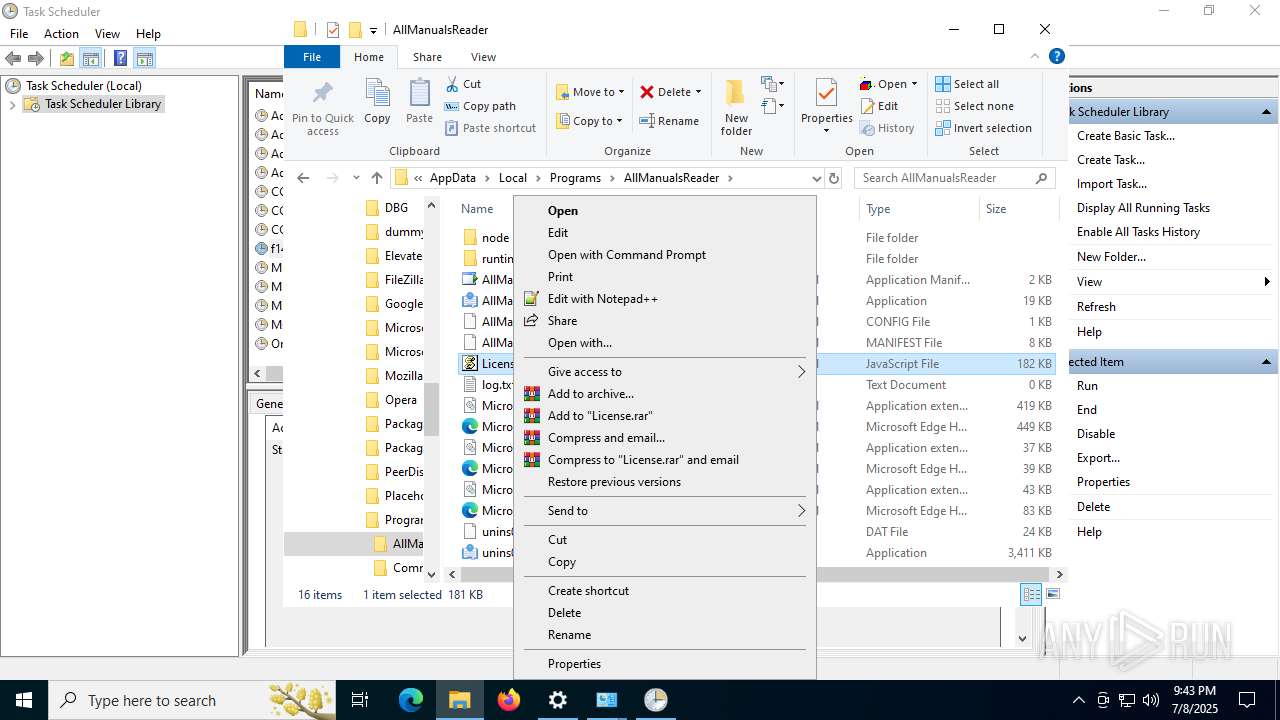
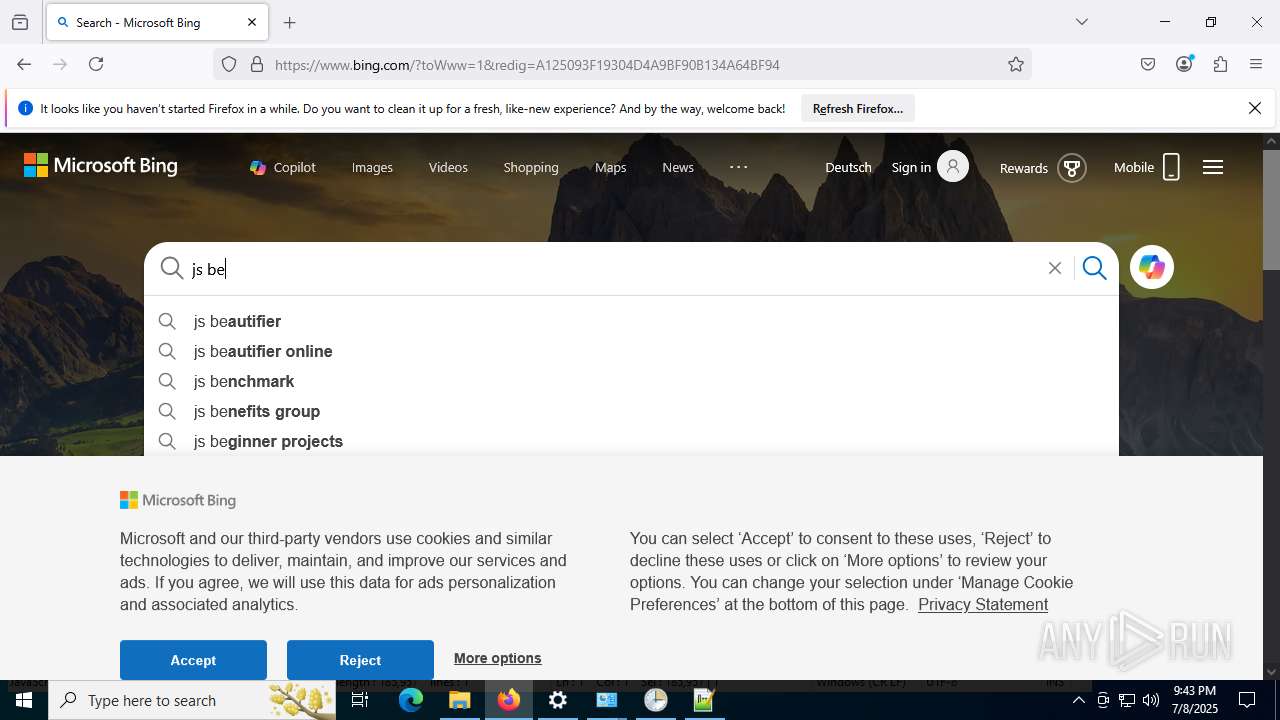
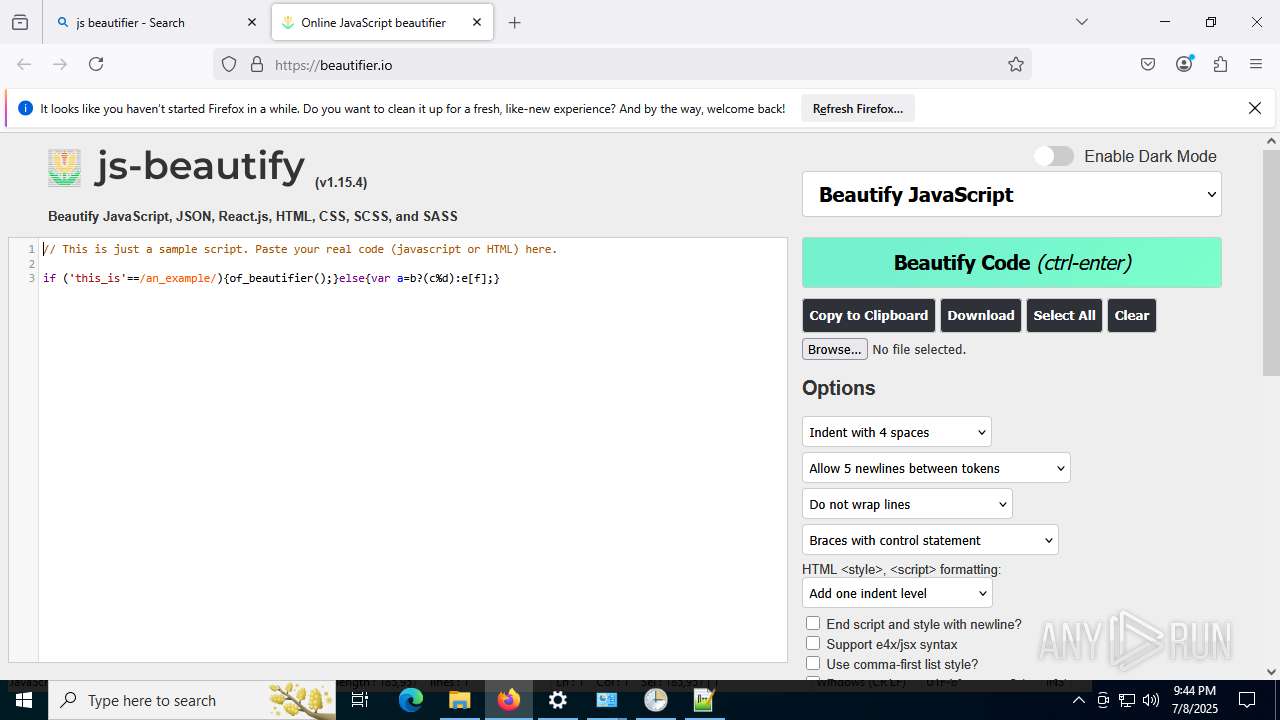
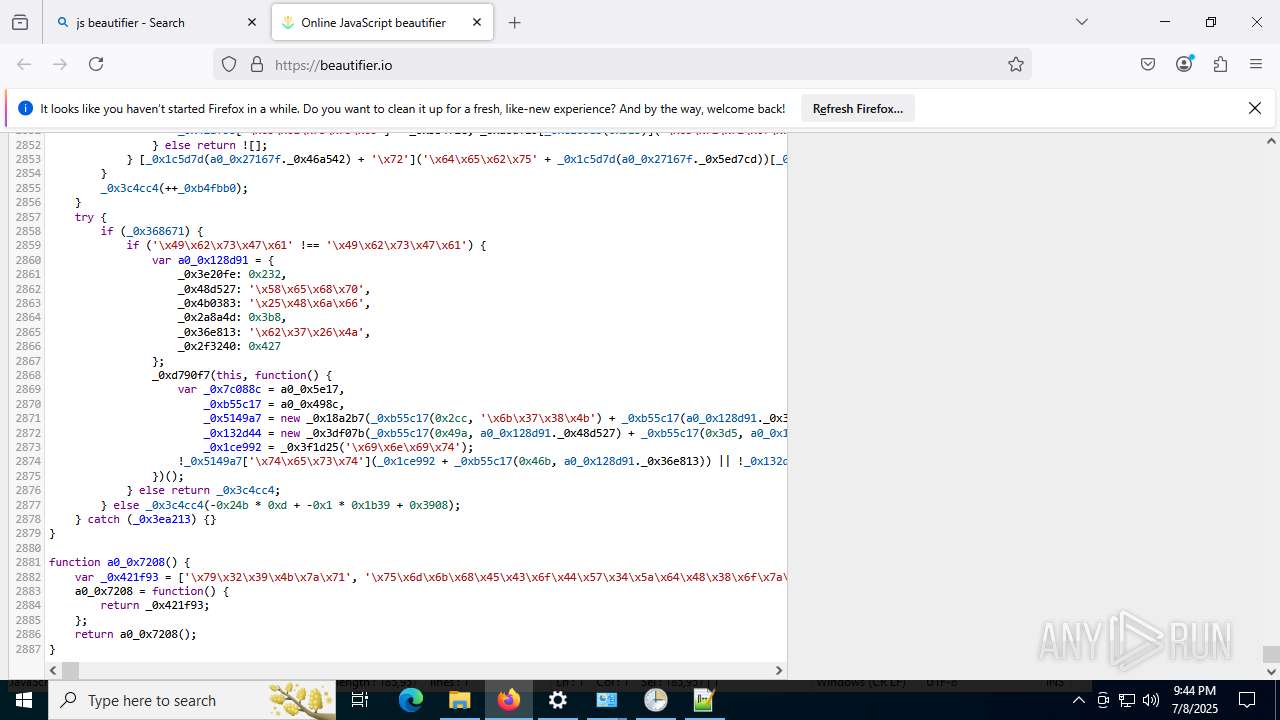
Executes script using NodeJS
- node.exe (PID: 304)
Reads security settings of Internet Explorer
- AllManualsReader_oc.tmp (PID: 8036)
Starts CMD.EXE for commands execution
- node.exe (PID: 304)
- AllManualsReader_oc.tmp (PID: 8036)
Executes application which crashes
- AllManualsReader.exe (PID: 8020)
- AllManualsReader.exe (PID: 7136)
- AllManualsReader.exe (PID: 2708)
INFO
Executable content was dropped or overwritten
- msedge.exe (PID: 188)
- msedge.exe (PID: 3688)
Application launched itself
- msedge.exe (PID: 188)
- msedge.exe (PID: 3888)
- firefox.exe (PID: 7188)
- firefox.exe (PID: 7928)
Reads Environment values
- identity_helper.exe (PID: 7964)
- node.exe (PID: 304)
- identity_helper.exe (PID: 7520)
Reads the computer name
- identity_helper.exe (PID: 7964)
- AllManualsReader_oc.tmp (PID: 8036)
- AllManualsReader.exe (PID: 8020)
- node.exe (PID: 304)
- identity_helper.exe (PID: 7520)
- AllManualsReader.exe (PID: 7136)
- AllManualsReader.exe (PID: 2708)
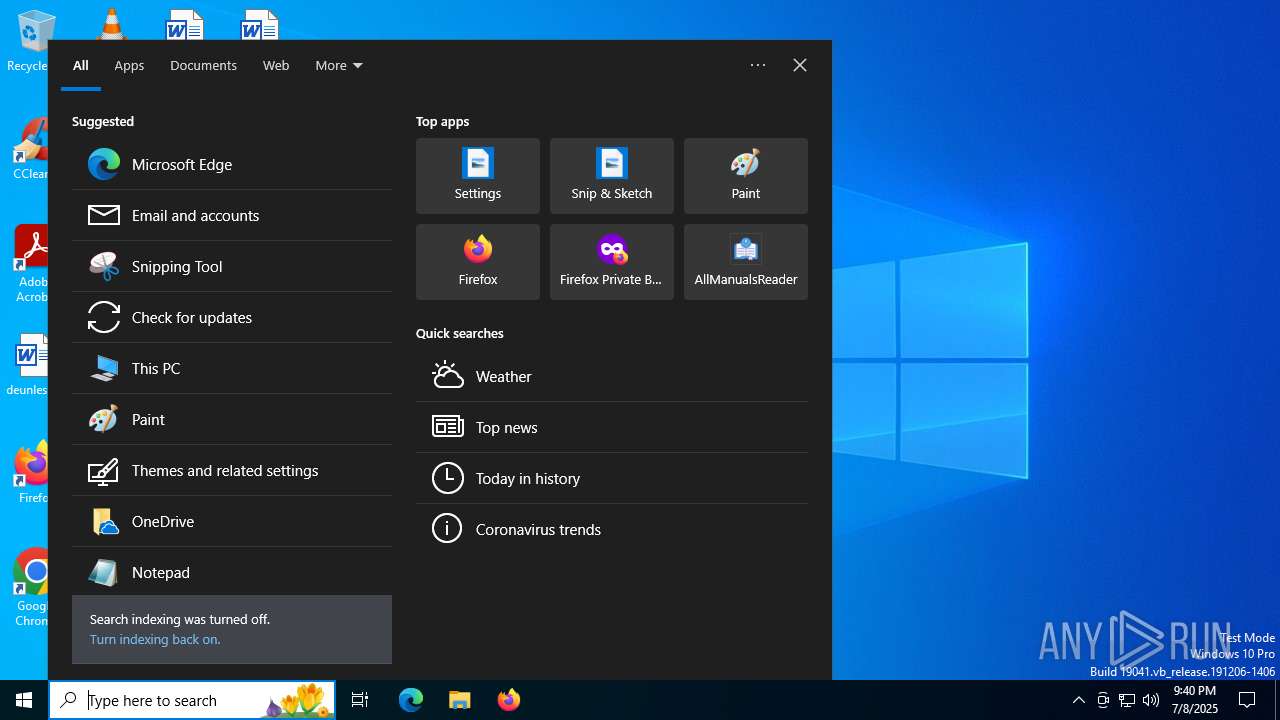
Checks supported languages
- AllManualsReader_oc.exe (PID: 6128)
- identity_helper.exe (PID: 7964)
- AllManualsReader_oc.tmp (PID: 8036)
- node.exe (PID: 304)
- AllManualsReader.exe (PID: 8020)
- SearchApp.exe (PID: 5328)
- identity_helper.exe (PID: 7520)
- AllManualsReader.exe (PID: 7136)
- AllManualsReader.exe (PID: 2708)
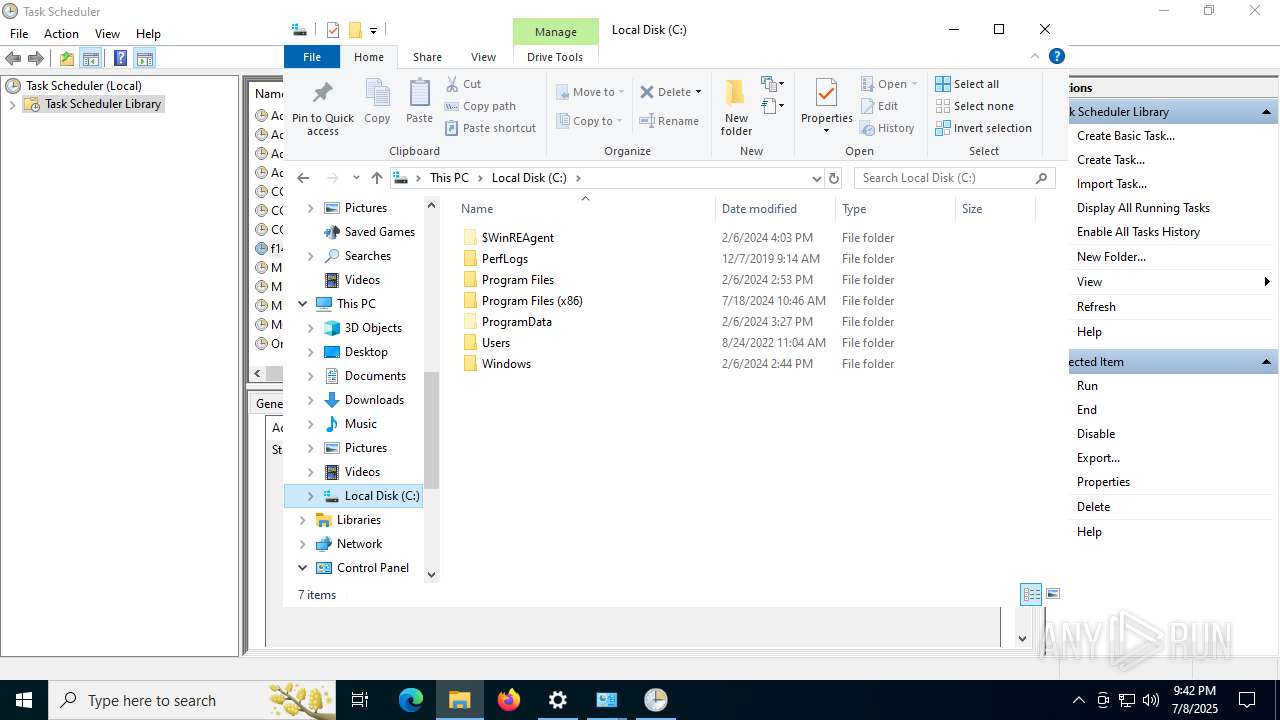
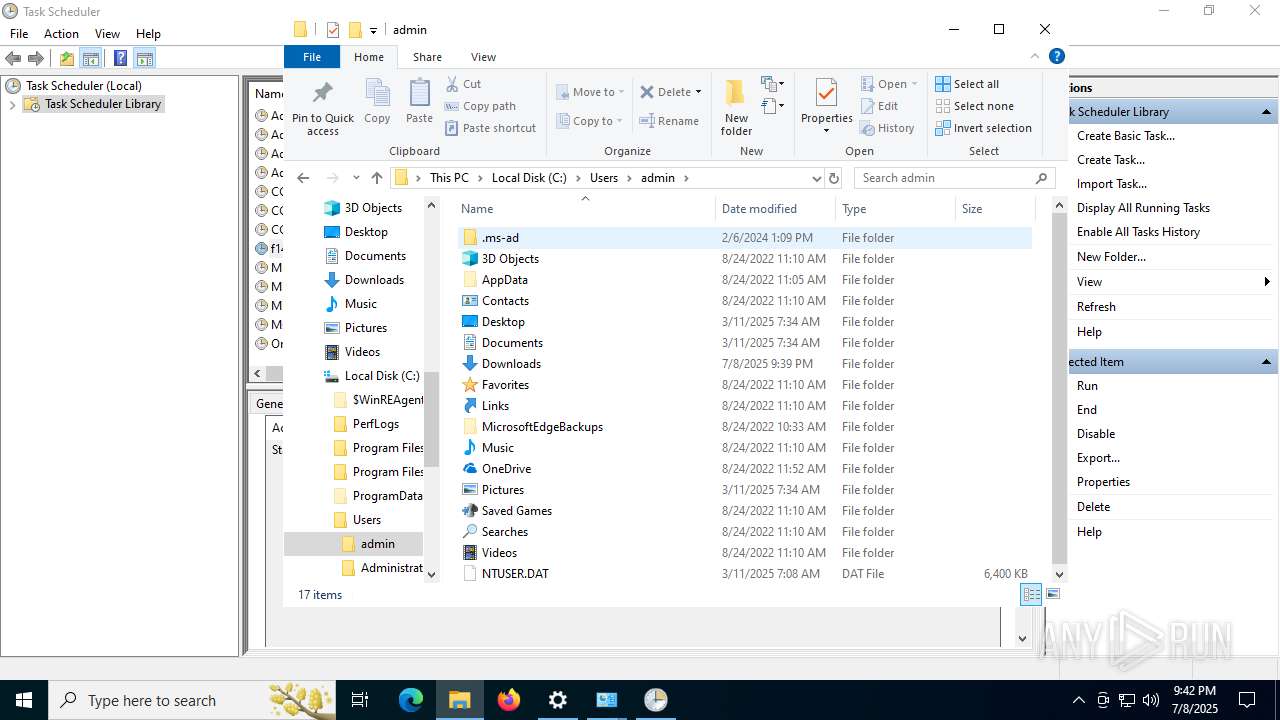
Create files in a temporary directory
- AllManualsReader_oc.exe (PID: 6128)
- AllManualsReader_oc.tmp (PID: 8036)
Reads the machine GUID from the registry
- AllManualsReader_oc.tmp (PID: 8036)
- AllManualsReader.exe (PID: 8020)
- SearchApp.exe (PID: 5328)
- AllManualsReader.exe (PID: 7136)
- AllManualsReader.exe (PID: 2708)
Reads the software policy settings
- AllManualsReader_oc.tmp (PID: 8036)
- WerFault.exe (PID: 2972)
- SearchApp.exe (PID: 5328)
- WerFault.exe (PID: 7424)
- WerFault.exe (PID: 7656)
- slui.exe (PID: 4880)
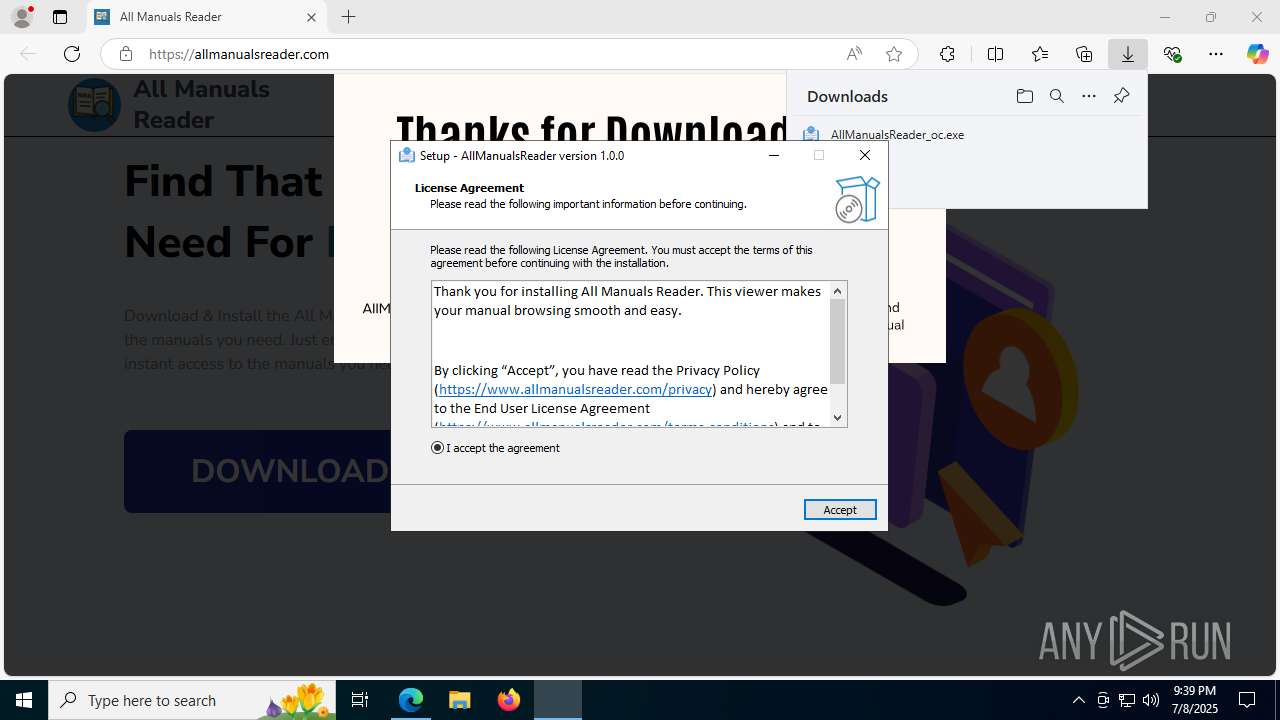
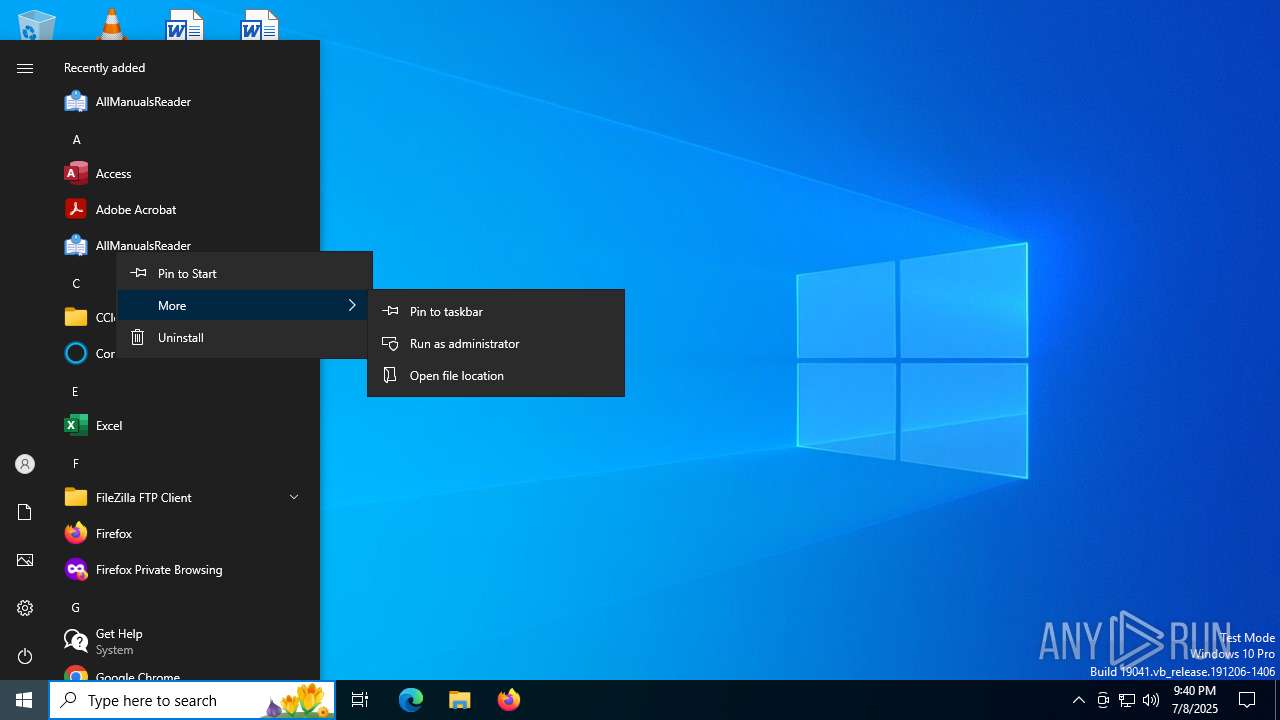
Creates a software uninstall entry
- AllManualsReader_oc.tmp (PID: 8036)
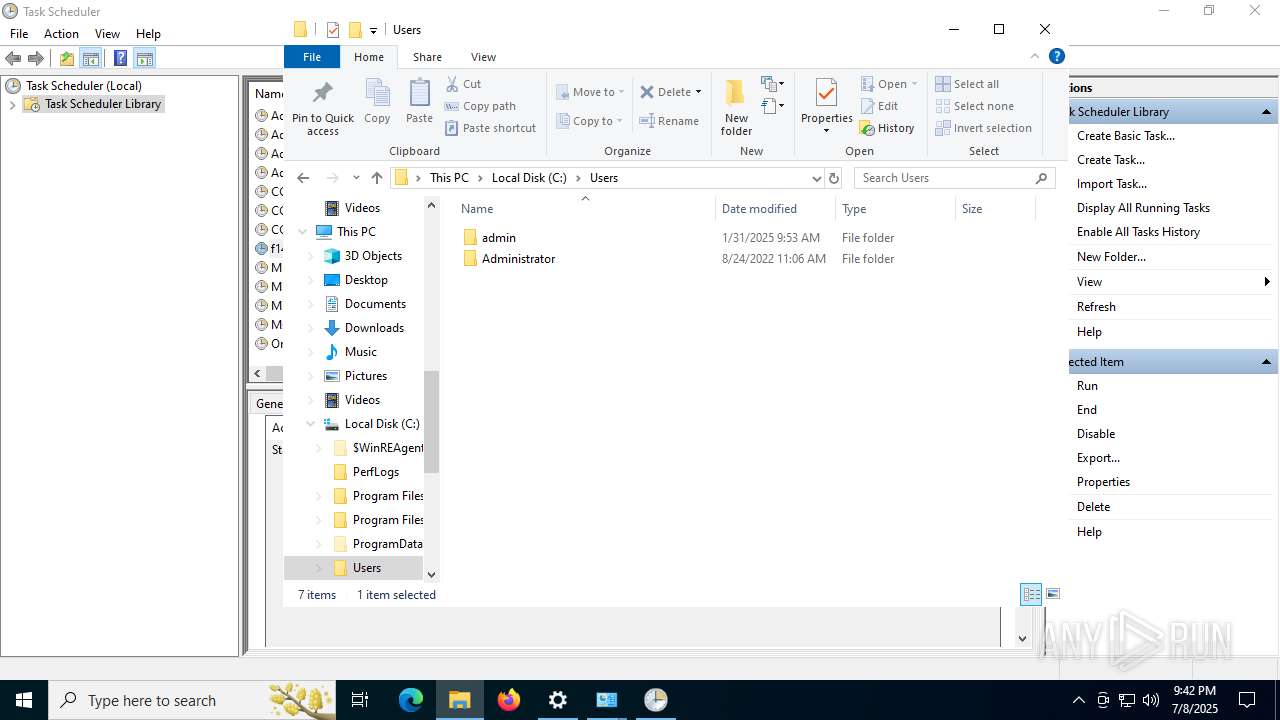
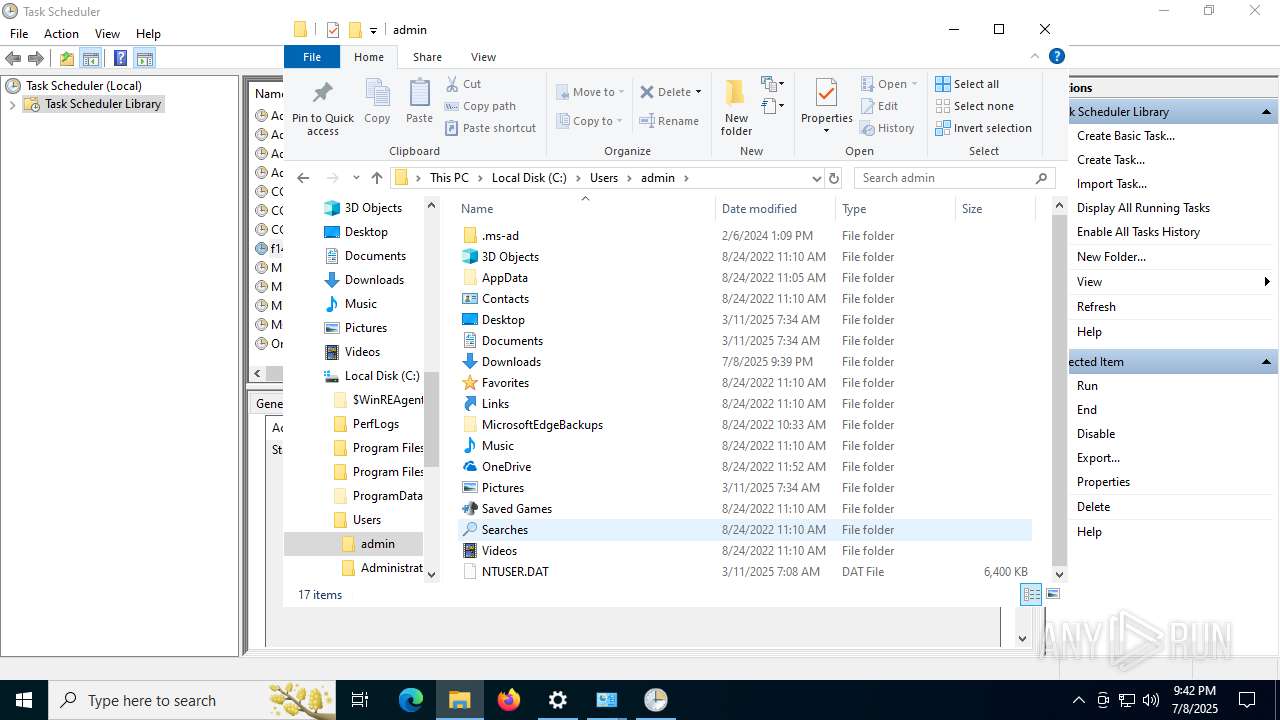
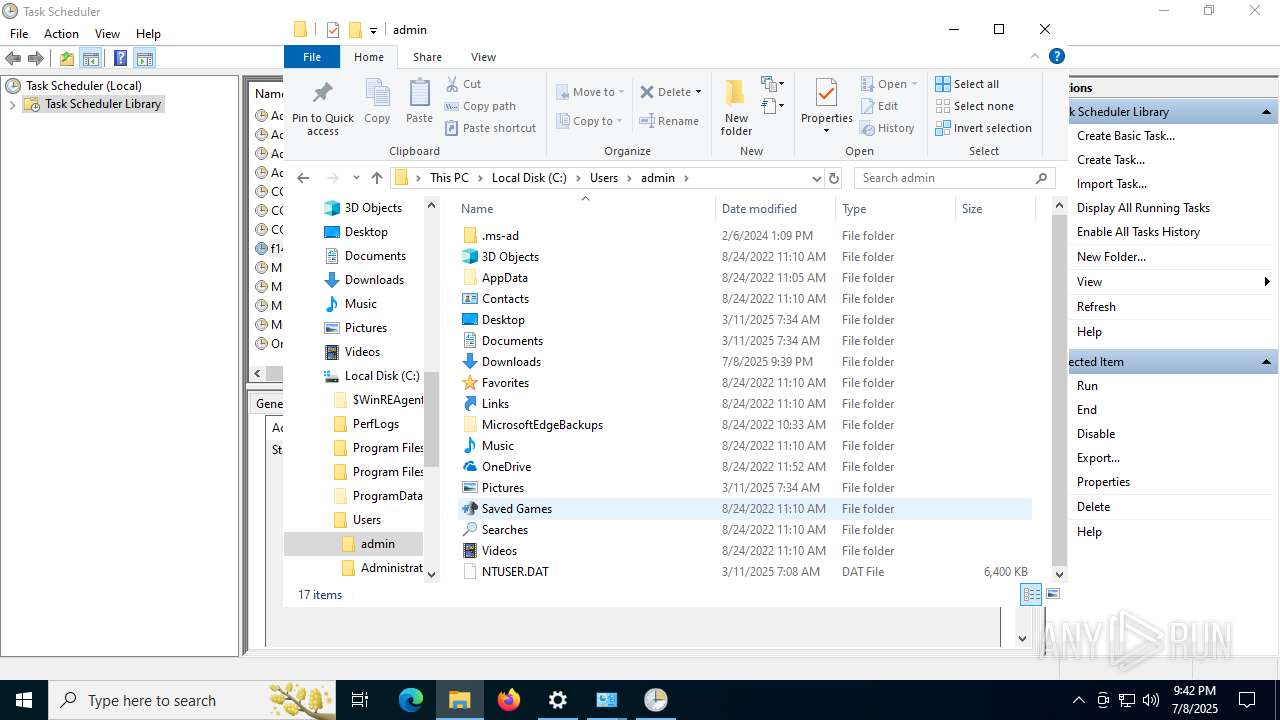
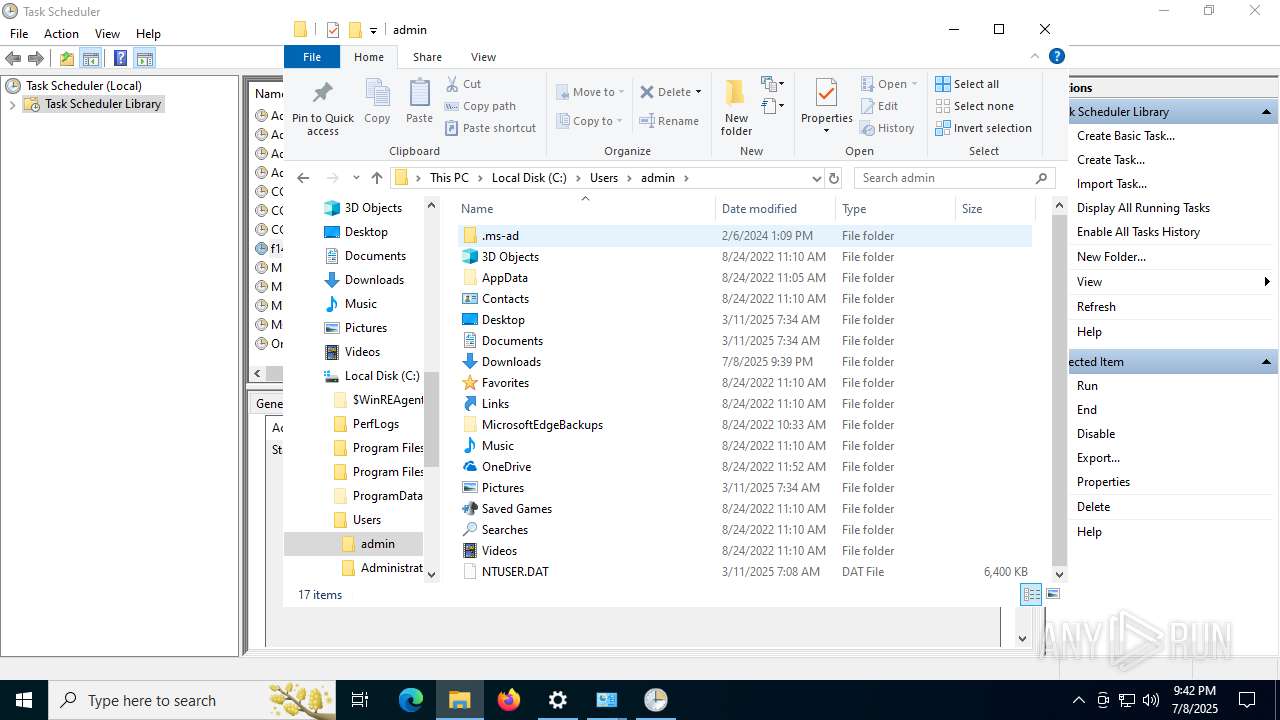
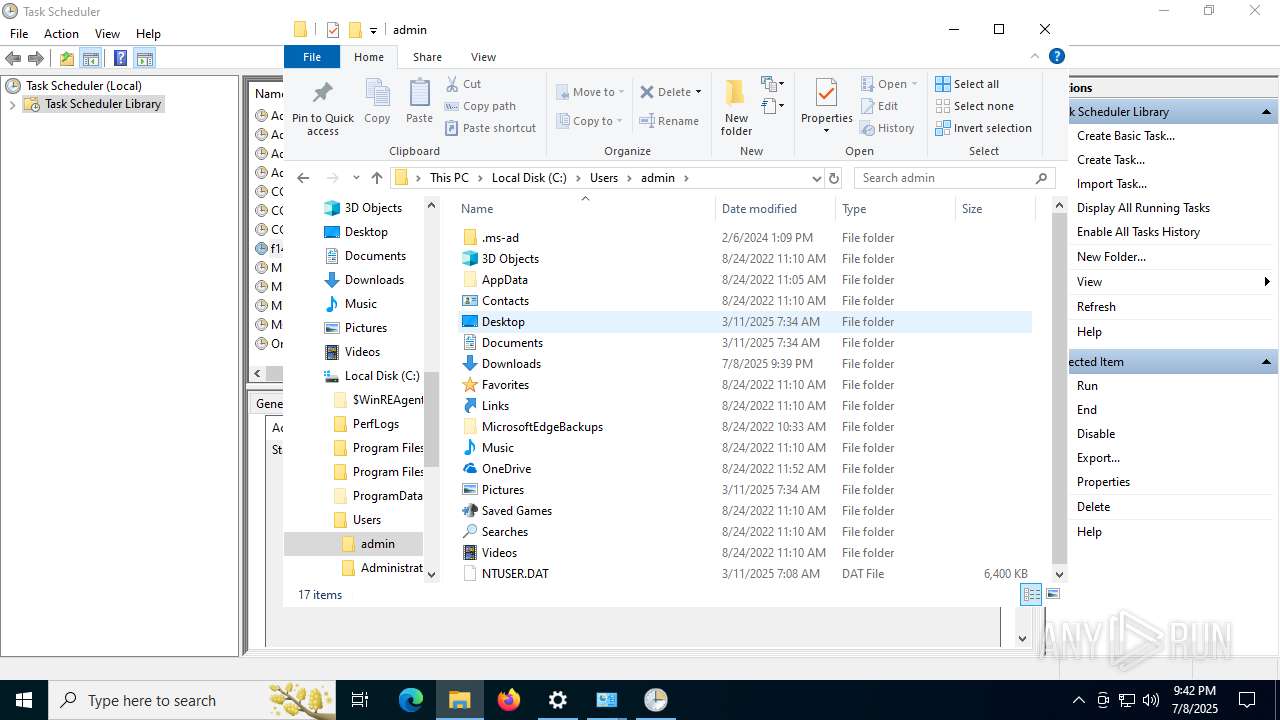
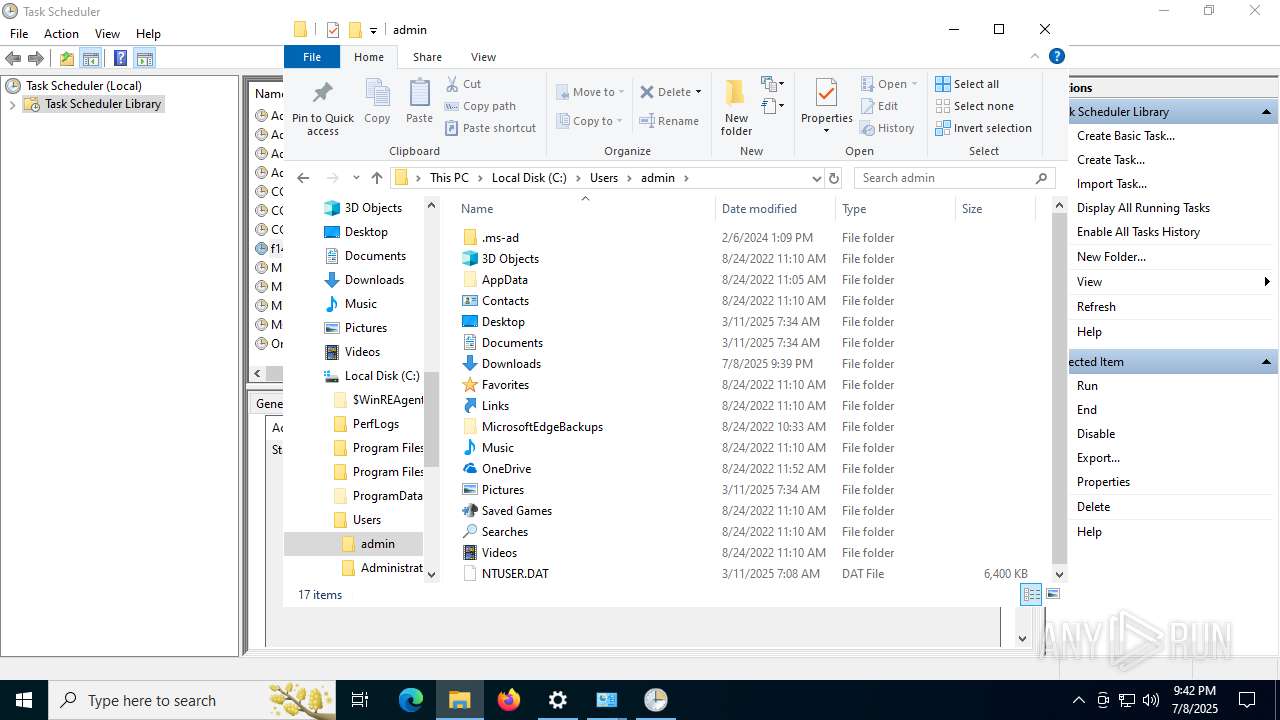
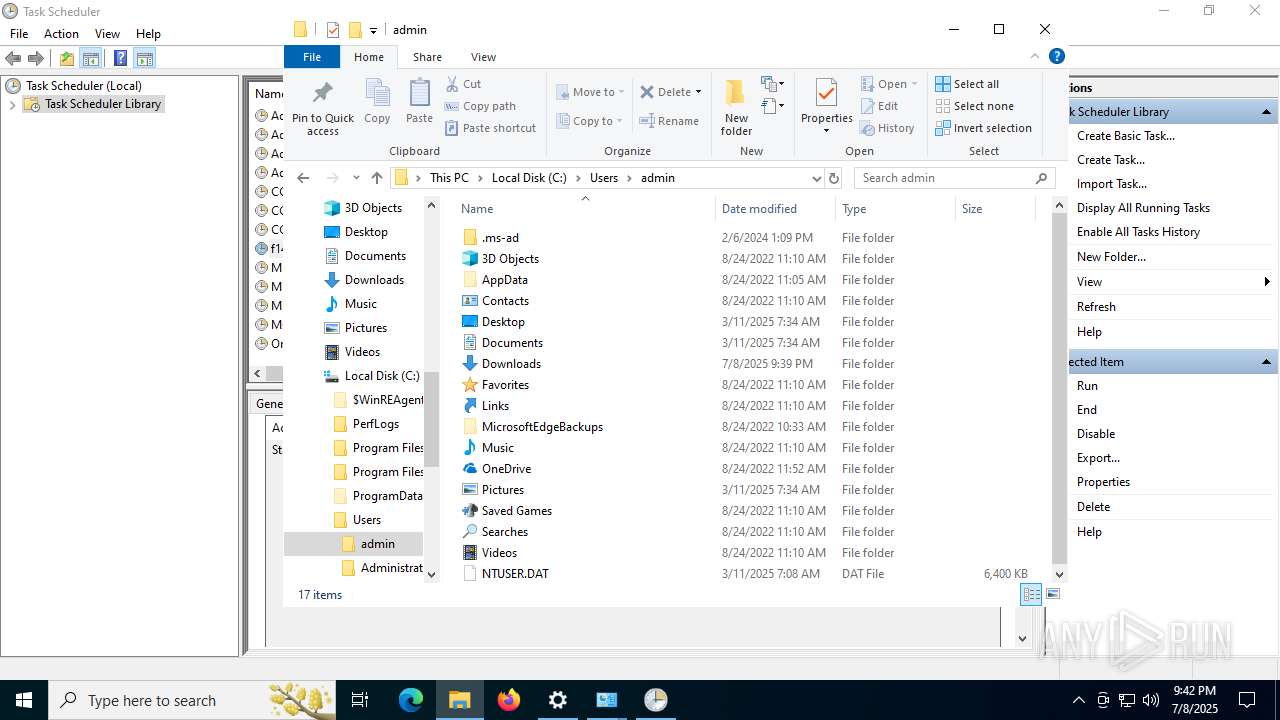
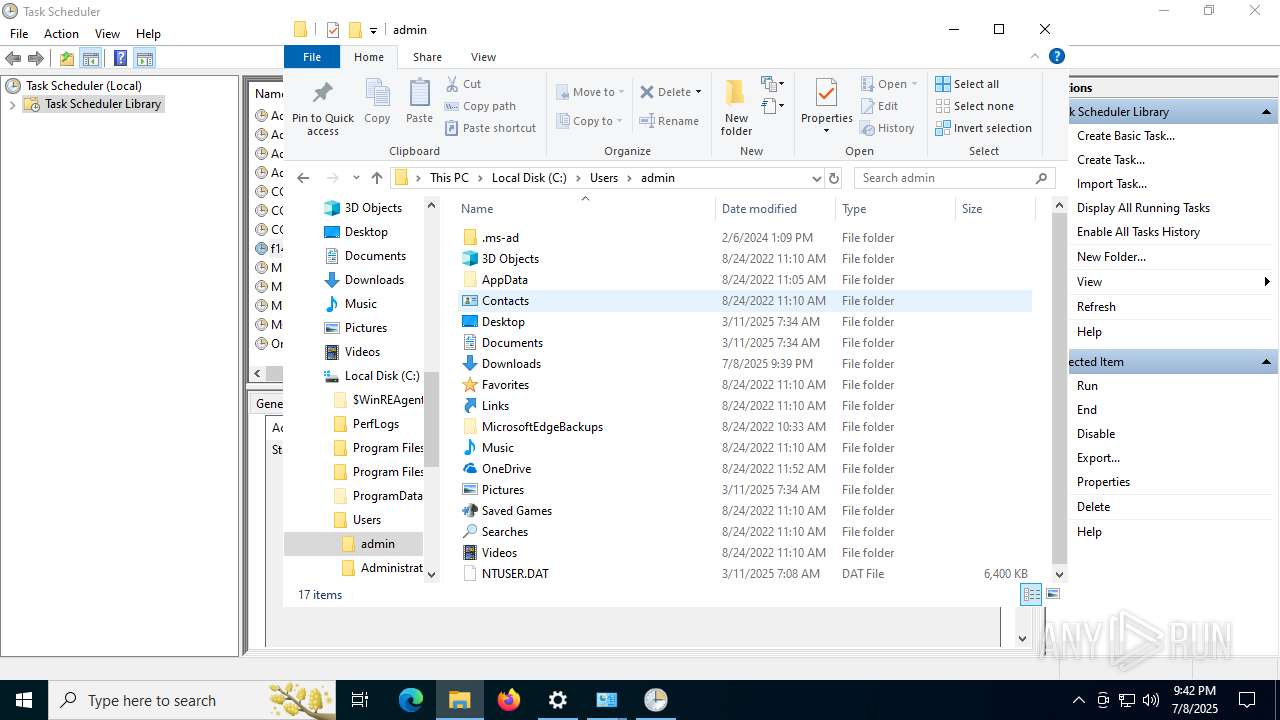
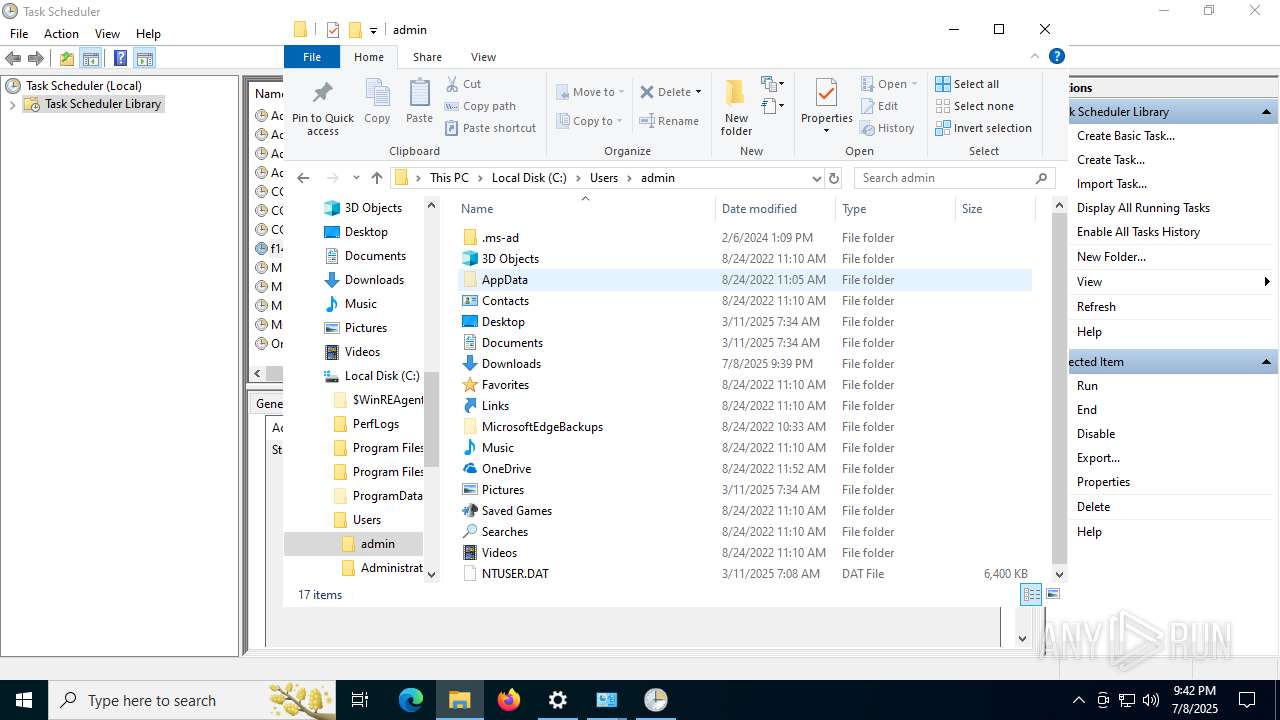
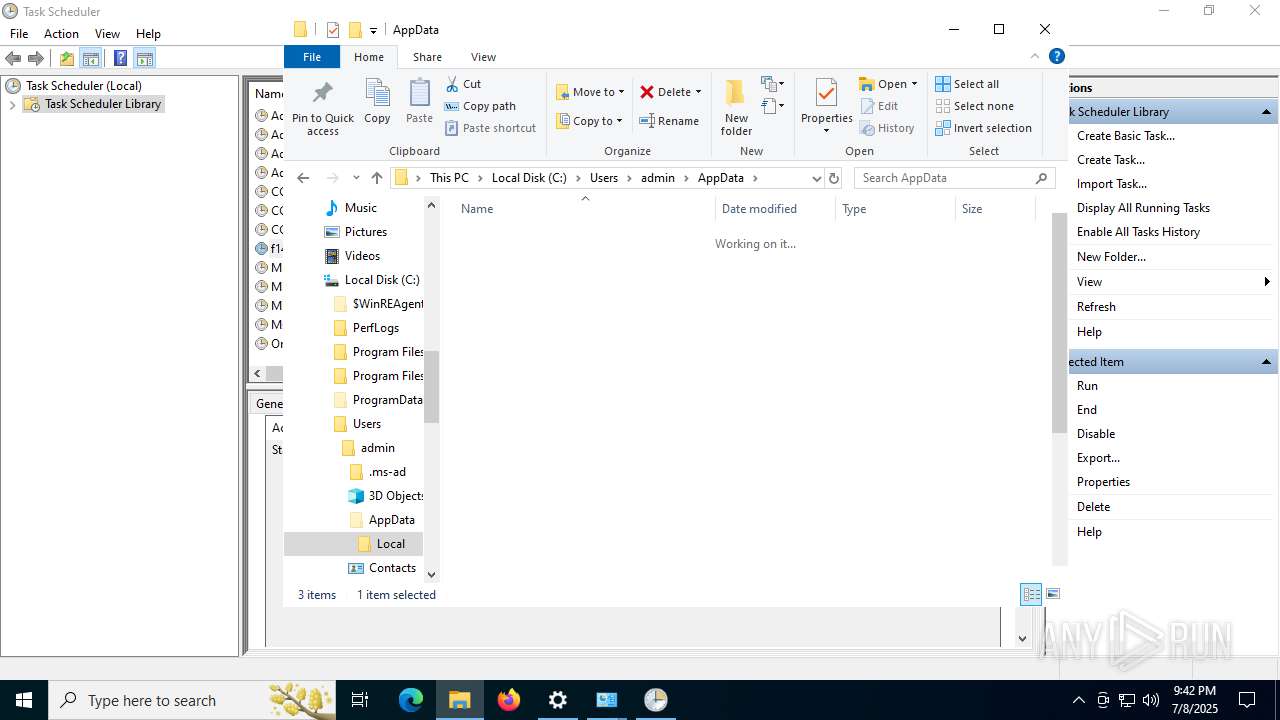
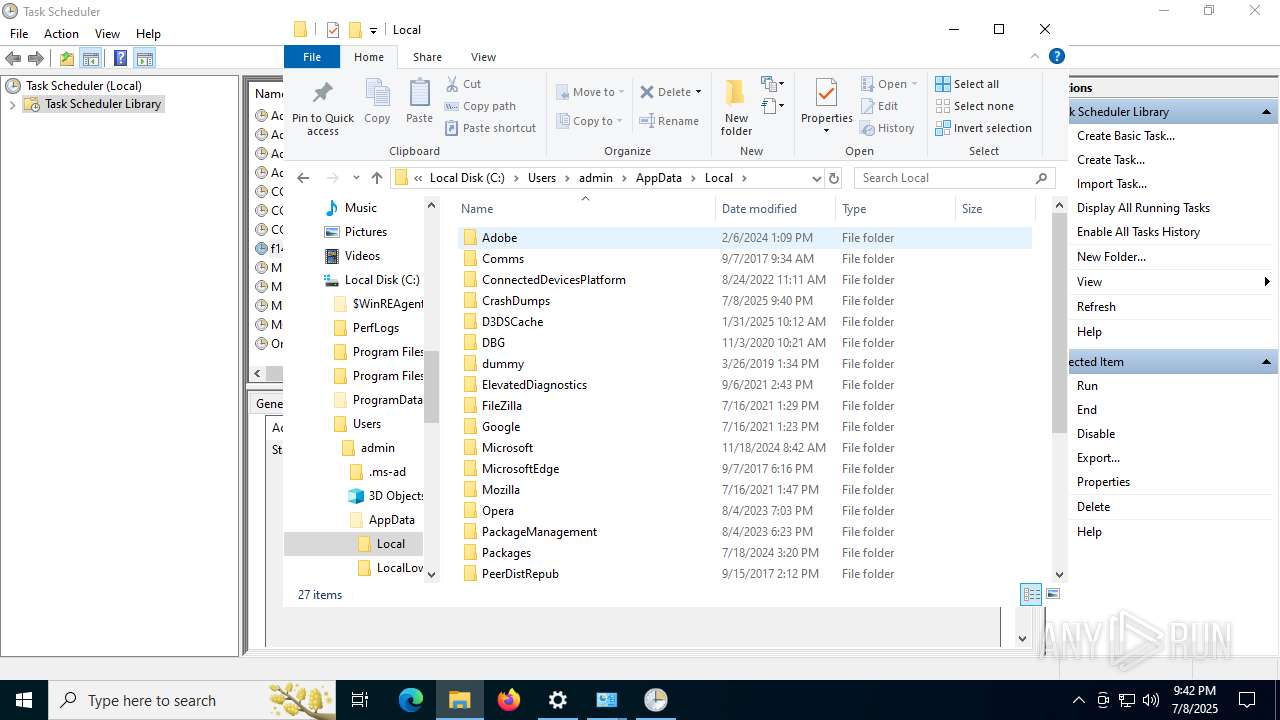
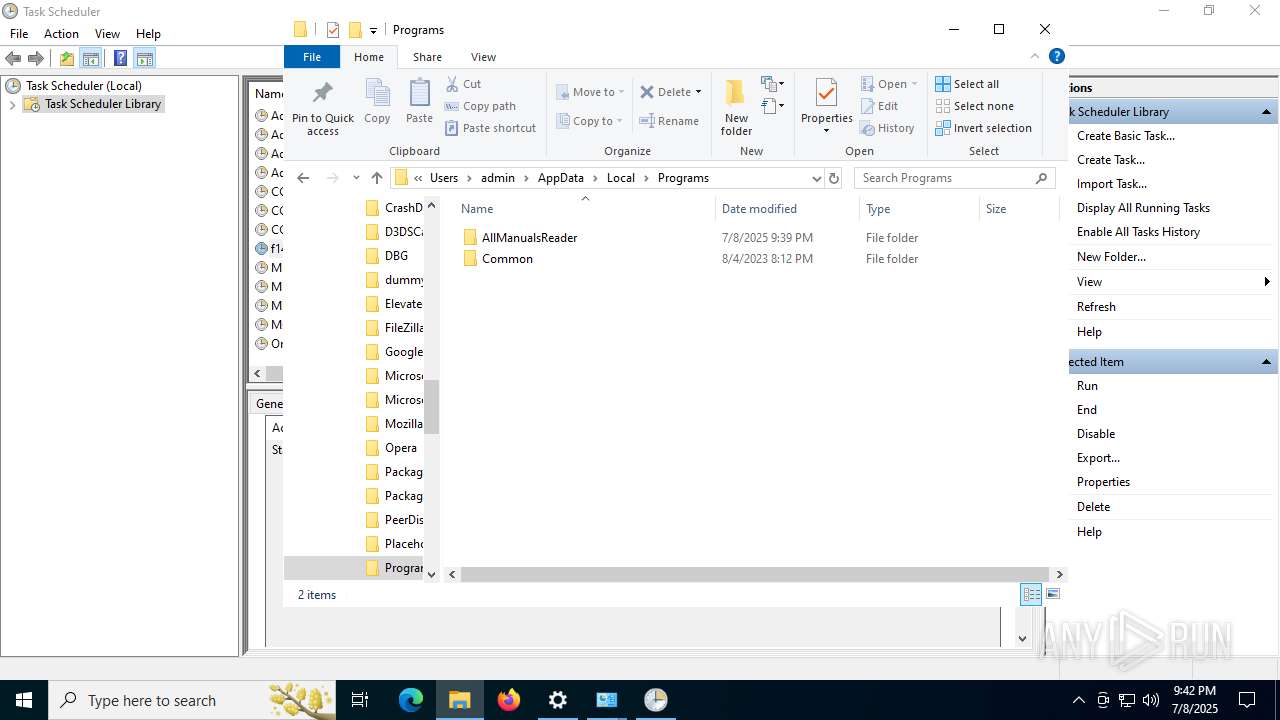
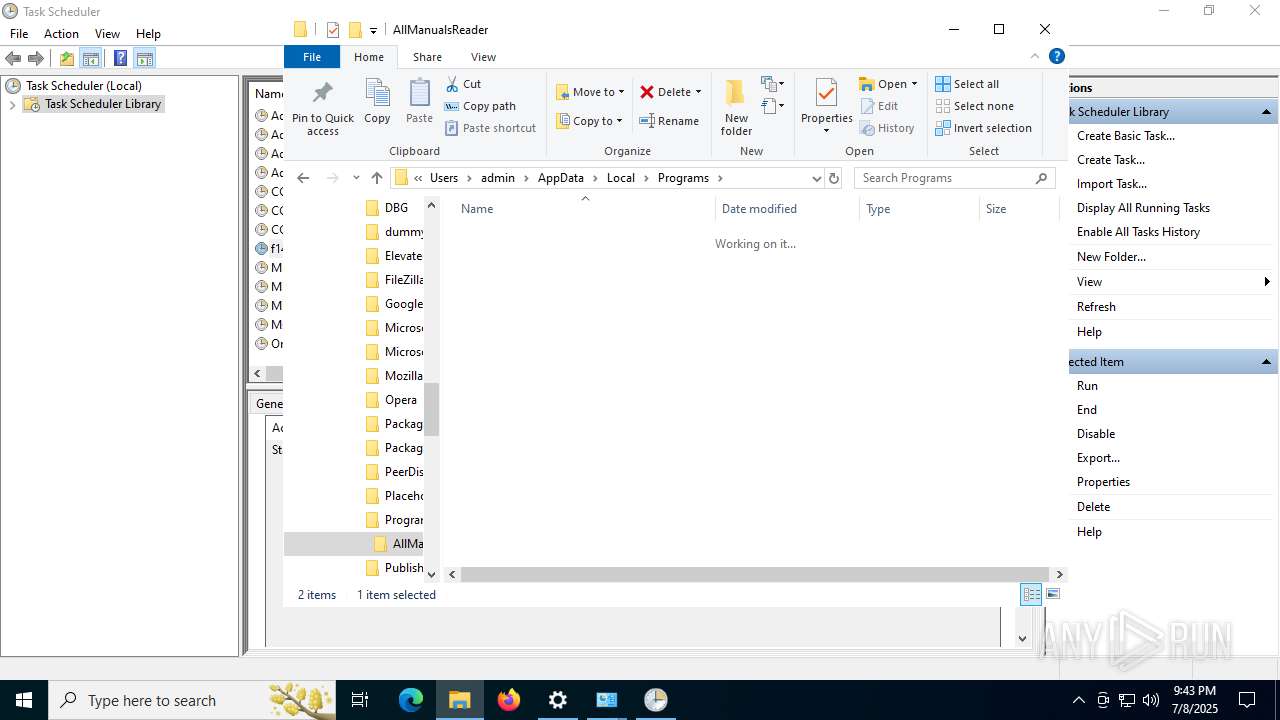
Creates files or folders in the user directory
- AllManualsReader_oc.tmp (PID: 8036)
- node.exe (PID: 304)
- WerFault.exe (PID: 2972)
- WerFault.exe (PID: 7424)
- WerFault.exe (PID: 7656)
The sample compiled with english language support
- AllManualsReader_oc.tmp (PID: 8036)
Detects InnoSetup installer (YARA)
- AllManualsReader_oc.exe (PID: 6128)
- AllManualsReader_oc.tmp (PID: 8036)
Compiled with Borland Delphi (YARA)
- AllManualsReader_oc.exe (PID: 6128)
- AllManualsReader_oc.tmp (PID: 8036)
Reads product name
- node.exe (PID: 304)
Process checks computer location settings
- SearchApp.exe (PID: 5328)
Checks proxy server information
- WerFault.exe (PID: 2972)
- WerFault.exe (PID: 7424)
- WerFault.exe (PID: 7656)
- slui.exe (PID: 4880)
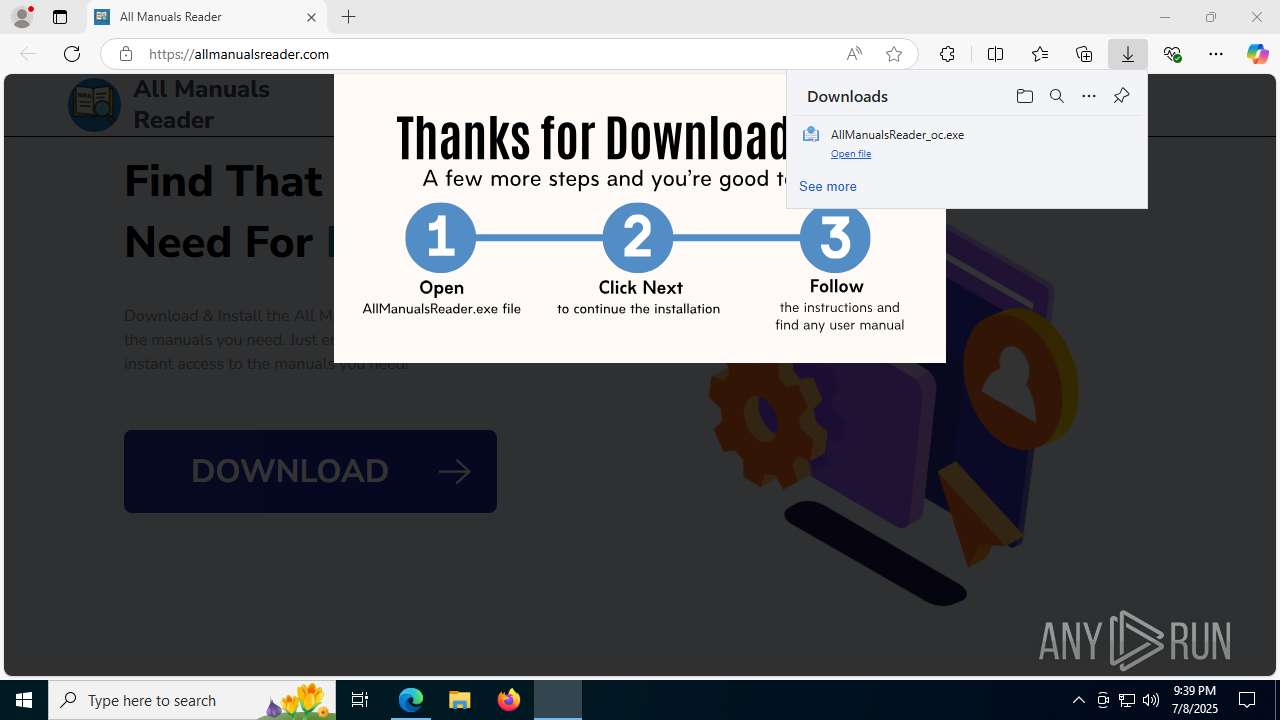
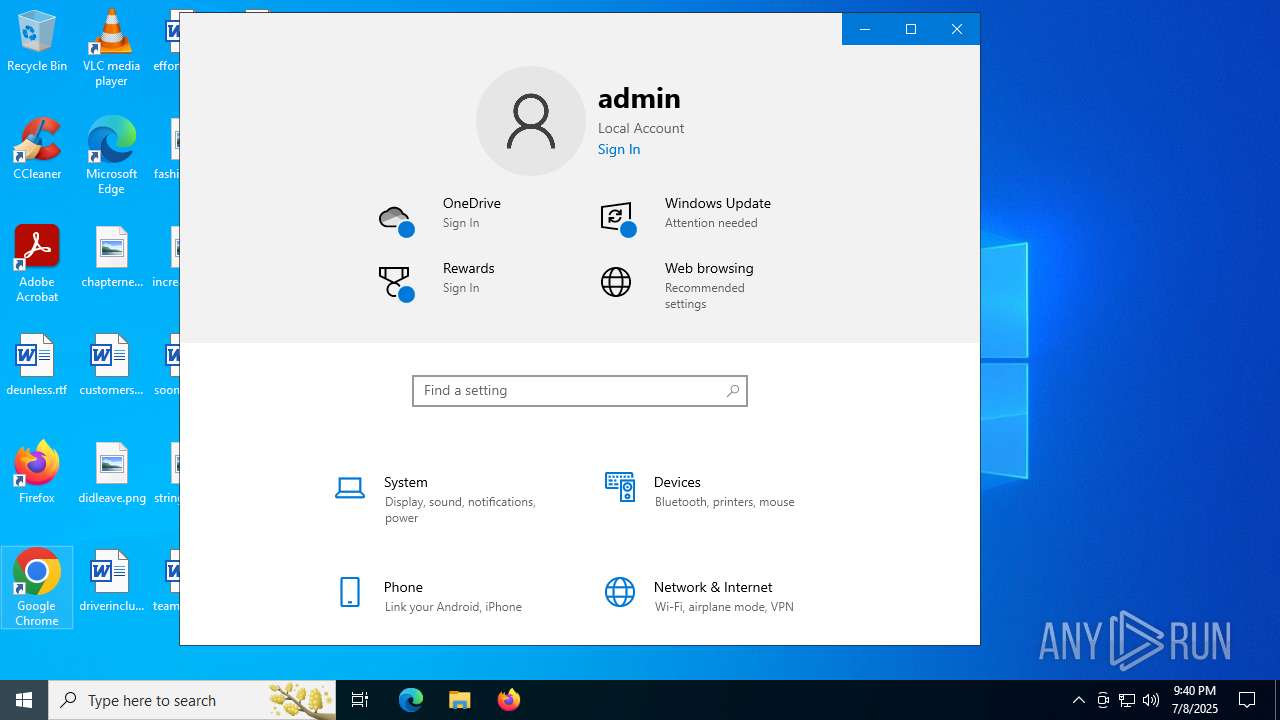
Manual execution by a user
- AllManualsReader.exe (PID: 7136)
- AllManualsReader.exe (PID: 2708)
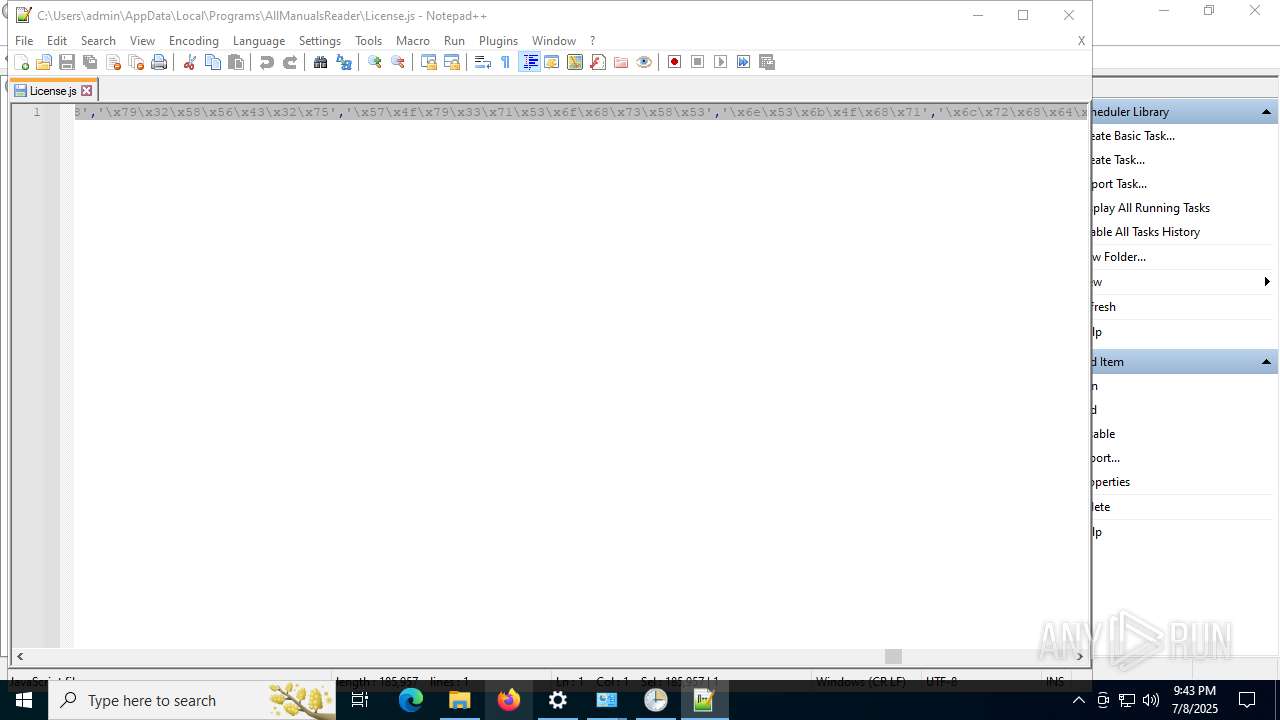
- notepad++.exe (PID: 8020)
- firefox.exe (PID: 7188)
Node.js compiler has been detected
- AllManualsReader_oc.tmp (PID: 8036)
Reads security settings of Internet Explorer
- explorer.exe (PID: 6388)
- mmc.exe (PID: 3820)
Reads Microsoft Office registry keys
- firefox.exe (PID: 7928)
- explorer.exe (PID: 6388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
252
Monitored processes
96
Malicious processes
1
Suspicious processes
3
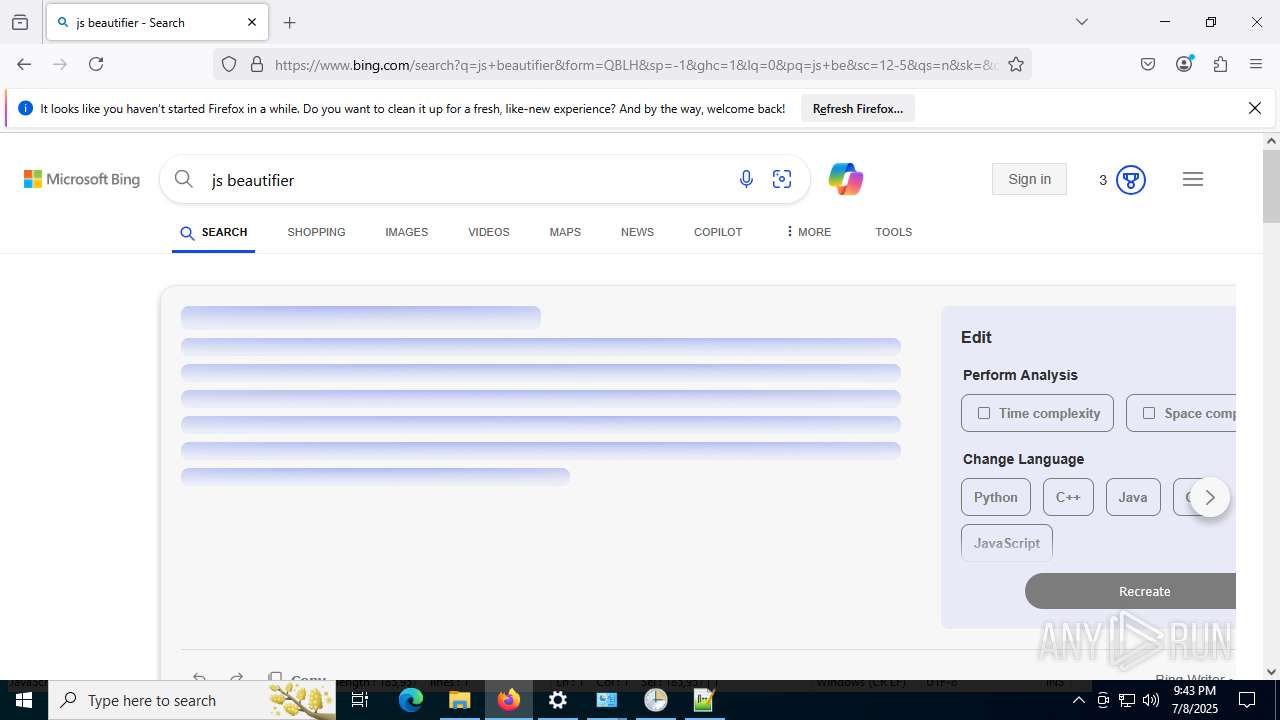
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" "allmanualsreader.com" | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 304 | "C:\Users\admin\AppData\Local\Programs\AllManualsReader\node\node.exe" "C:\Users\admin\AppData\Local\Programs\AllManualsReader\License.js" | C:\Users\admin\AppData\Local\Programs\AllManualsReader\node\node.exe | cmd.exe | ||||||||||||
User: admin Company: Node.js Integrity Level: MEDIUM Description: Node.js JavaScript Runtime Exit code: 0 Version: 20.17.0 Modules
| |||||||||||||||
| 544 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 5752 -prefsLen 39430 -prefMapHandle 6056 -prefMapSize 272997 -jsInitHandle 5664 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 2676 -initialChannelId {ec89ec90-633c-468c-b433-fe2ba01ca9b6} -parentPid 7928 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7928" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 17 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 1028 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc438af208,0x7ffc438af214,0x7ffc438af220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1212 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 4844 -prefsLen 39231 -prefMapHandle 4848 -prefMapSize 272997 -jsInitHandle 4796 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 1140 -initialChannelId {f4307b2c-c8e7-4e47-ac73-4e87a306f5f8} -parentPid 7928 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7928" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 11 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 136.0 Modules
| |||||||||||||||
| 1284 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5072,i,9322952555809751742,14732765885309420443,262144 --variations-seed-version --mojo-platform-channel-handle=3444 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1580 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -parentBuildID 20250227124745 -prefsHandle 3328 -prefsLen 36996 -prefMapHandle 3332 -prefMapSize 272997 -ipcHandle 3340 -initialChannelId {19fb84c2-bc4a-4963-baa3-b512f74e4d8d} -parentPid 7928 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7928" -appDir "C:\Program Files\Mozilla Firefox\browser" - 4 rdd | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 1800 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc -isForBrowser -prefsHandle 5072 -prefsLen 39068 -prefMapHandle 5076 -prefMapSize 272997 -jsInitHandle 5080 -jsInitLen 247456 -parentBuildID 20250227124745 -ipcHandle 5020 -initialChannelId {a0845a97-3de2-4b53-8894-73c50c16a1d0} -parentPid 7928 -crashReporter "\\.\pipe\gecko-crash-server-pipe.7928" -win32kLockedDown -appDir "C:\Program Files\Mozilla Firefox\browser" - 7 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Version: 136.0 Modules
| |||||||||||||||
| 2040 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4912,i,9322952555809751742,14732765885309420443,262144 --variations-seed-version --mojo-platform-channel-handle=5176 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2124 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
65 993
Read events
65 758
Write events
223
Delete events
12
Modification events
| (PID) Process: | (188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (188) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: E4882B1408982F00 | |||
| (PID) Process: | (188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459490 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {694F8962-77AF-4535-AE76-BC33F9D17828} | |||
| (PID) Process: | (188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459490 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {8E7561BA-DDA0-46EC-B28E-1D4394E8EF0C} | |||
| (PID) Process: | (188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459490 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {986F08D1-922A-4FC8-AEDD-65C788D7AD8D} | |||
| (PID) Process: | (188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459490 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6372F2AF-6AE6-4CB8-BDF5-A126452F98B7} | |||
| (PID) Process: | (188) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459490 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A8BD9BD3-3A08-49A1-9C45-B070EE7060B6} | |||
Executable files
22
Suspicious files
592
Text files
345
Unknown types
207
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1759d8.TMP | — | |
MD5:— | SHA256:— | |||
| 188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1759e7.TMP | — | |
MD5:— | SHA256:— | |||
| 188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1759e7.TMP | — | |
MD5:— | SHA256:— | |||
| 188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1759f7.TMP | — | |
MD5:— | SHA256:— | |||
| 188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1759f7.TMP | — | |
MD5:— | SHA256:— | |||
| 188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 188 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF175a07.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
67
TCP/UDP connections
252
DNS requests
318
Threats
12
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3688 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:O5ESs3DXPGvaDtrtkXivCQYntmF2U0bJ8bgYdylB794&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.25:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2552 | svchost.exe | GET | 200 | 23.63.118.230:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
188 | msedge.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSdE3gf41WAic8Uh9lF92%2BIJqh5qwQUMuuSmv81lkgvKEBCcCA2kVwXheYCEDPXCKiRQFMZ4qW70zm5rW4%3D | unknown | — | — | whitelisted |
188 | msedge.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEEj8k7RgVZSNNqfJionWlBY%3D | unknown | — | — | whitelisted |
2348 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
188 | msedge.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.sectigo.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRd0JozUYXMqqW4y4zJTrLcMCRSkAQUgTKSQSsozUbIxKLGKjkS7EipPxQCEH0GxIzLDgmUXOZVfHyOtag%3D | unknown | — | — | whitelisted |
2348 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
2972 | WerFault.exe | GET | 200 | 23.216.77.27:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2276 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3688 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3688 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3688 | msedge.exe | 150.171.27.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3688 | msedge.exe | 104.22.37.177:443 | allmanualsreader.com | CLOUDFLARENET | — | unknown |
3688 | msedge.exe | 2.16.204.153:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
allmanualsreader.com |
| unknown |
copilot.microsoft.com |
| whitelisted |
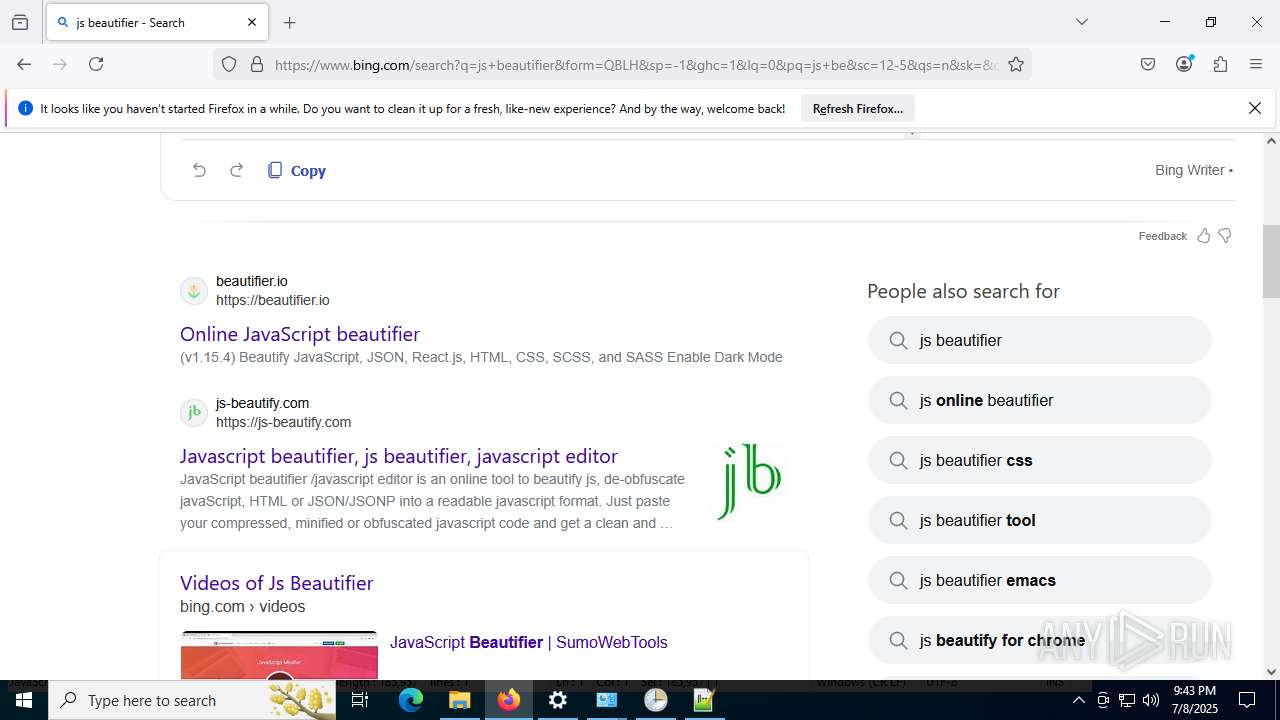
www.bing.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
www.google.com |
| whitelisted |
cdn-defaultasset.s3.us-east-1.amazonaws.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
3688 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Tag Manager analytics (googletagmanager .com) |
Process | Message |
|---|---|
AllManualsReader.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
AllManualsReader.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
AllManualsReader.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
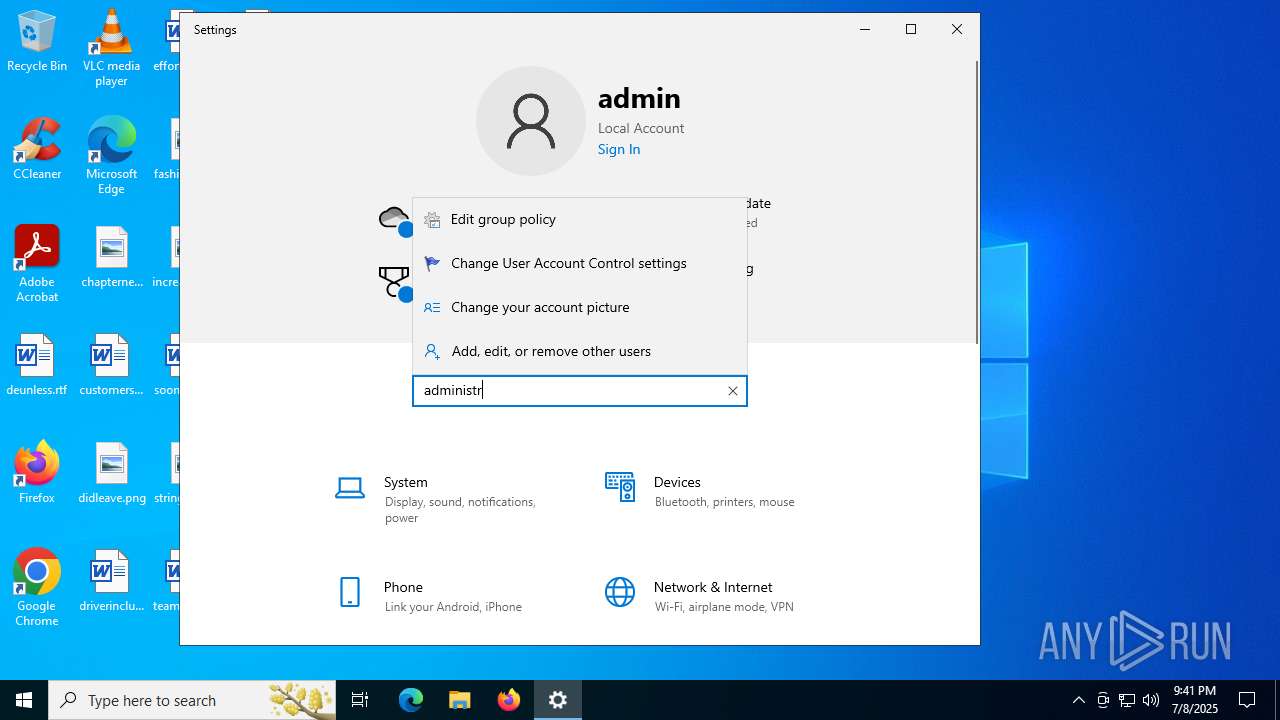
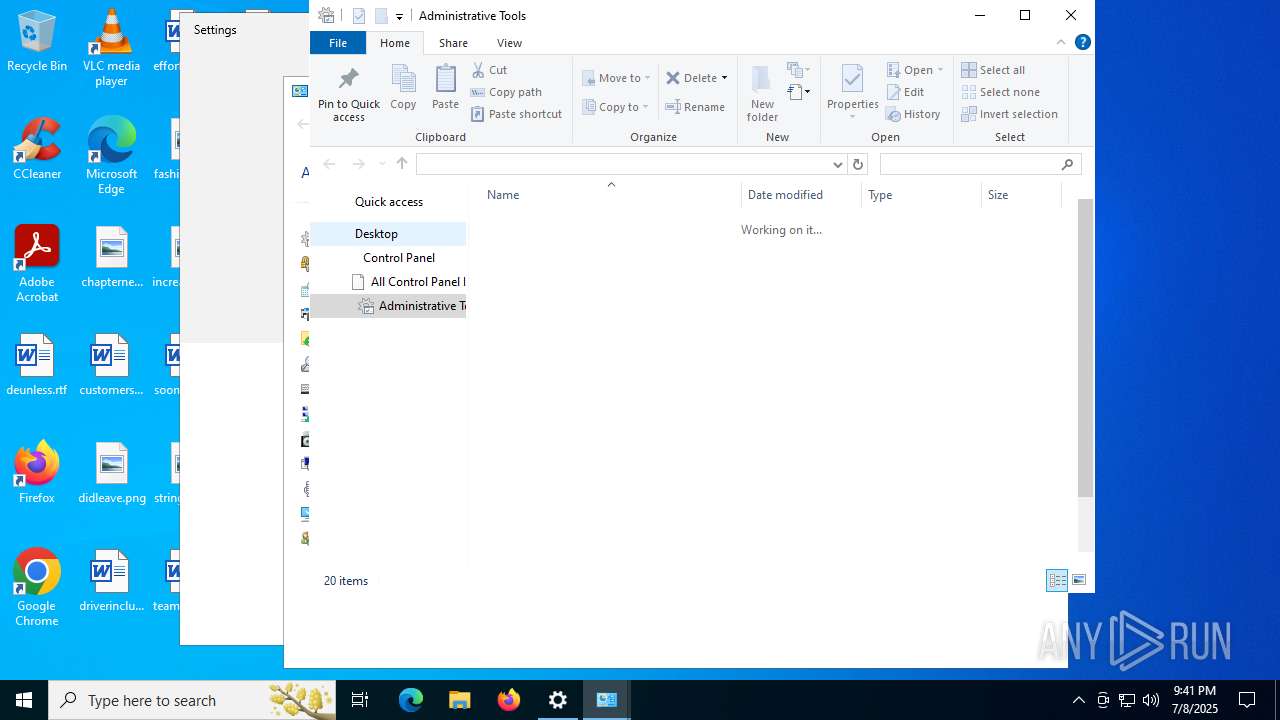
mmc.exe | Constructor: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | OnInitialize: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | AddIcons: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
mmc.exe | ProcessCommandLineArguments: Microsoft.TaskScheduler.SnapIn.TaskSchedulerSnapIn
|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | ED255D9151912E40DF048A56288E969A8D0DAFA3
|