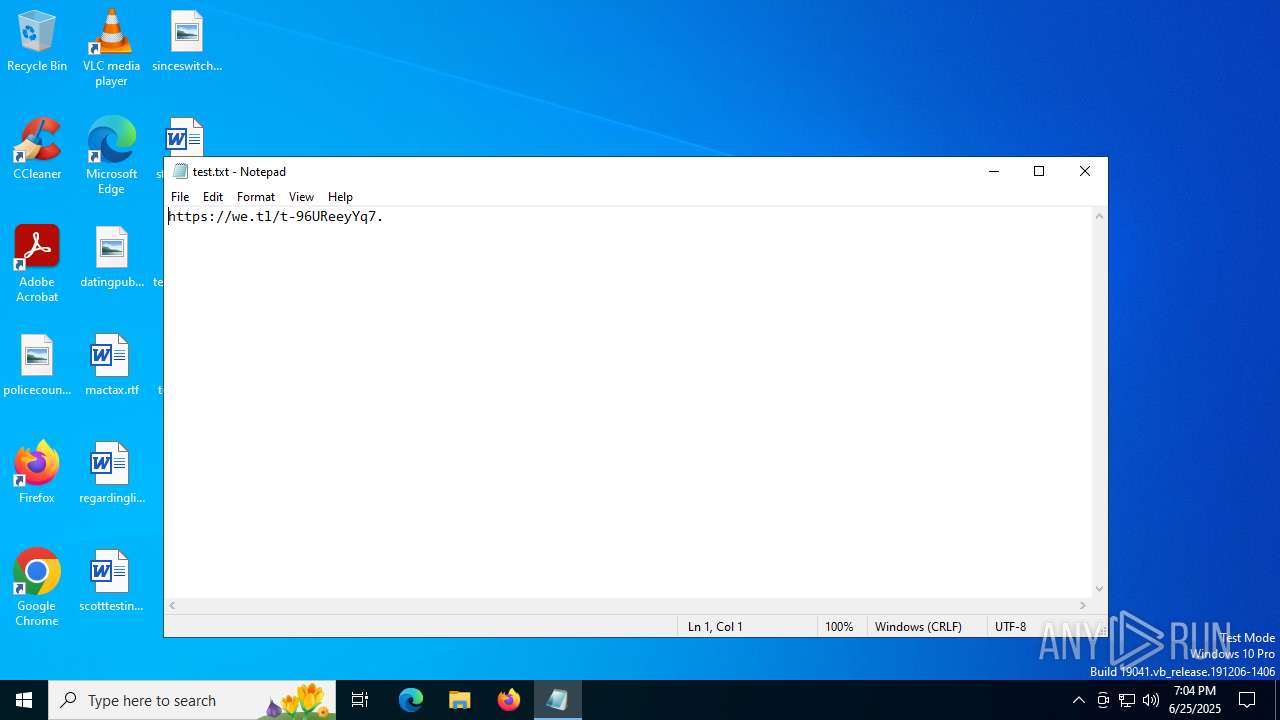
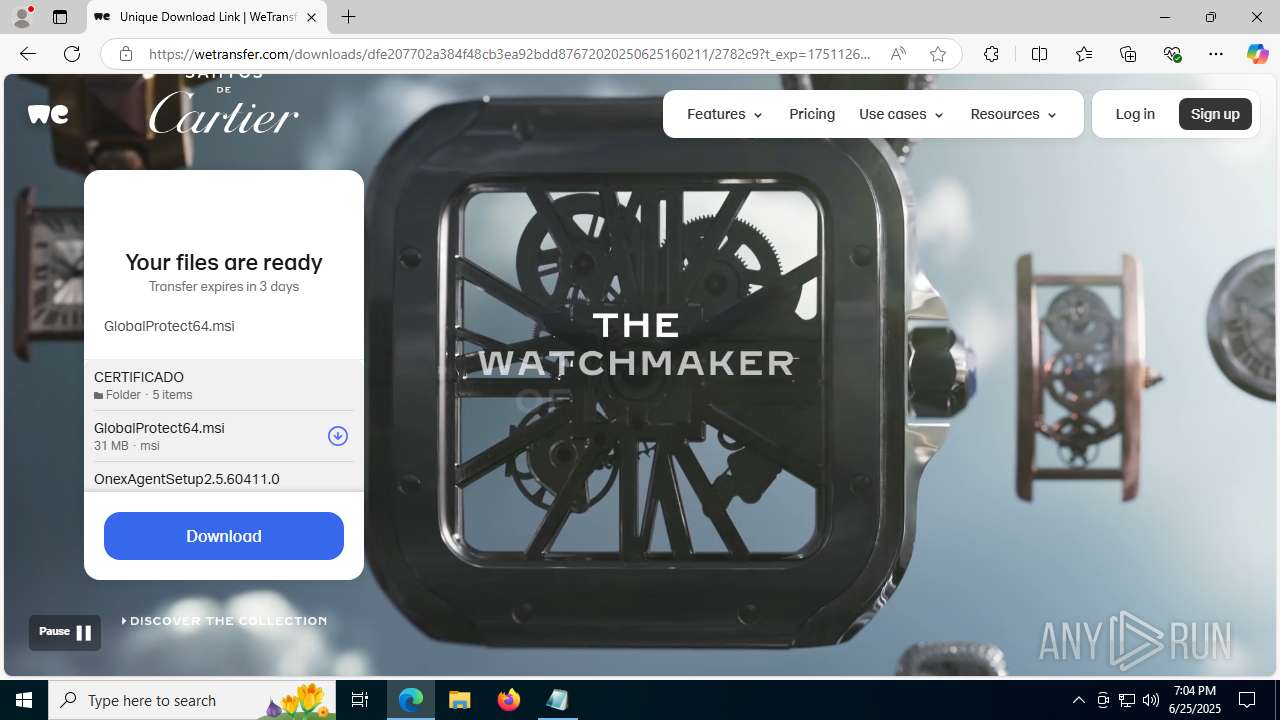
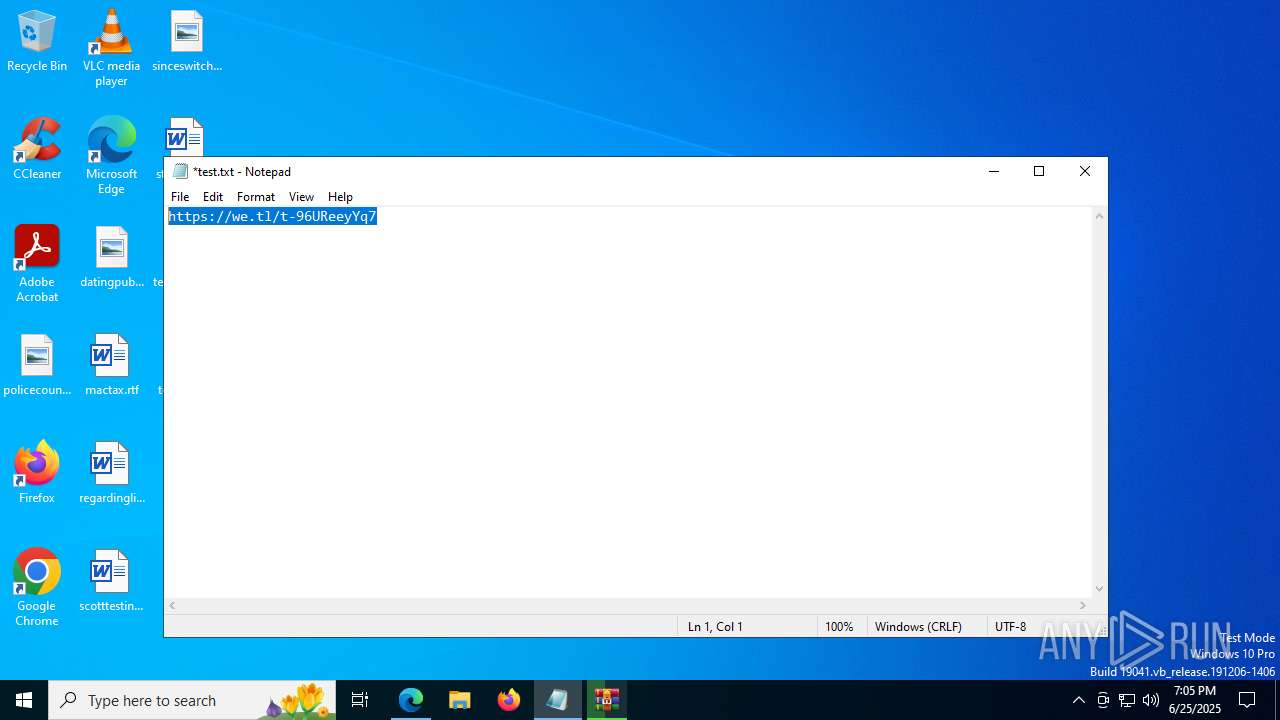
| File name: | test.txt |
| Full analysis: | https://app.any.run/tasks/5632ccbd-f412-4d26-84e6-93c0c503cbc4 |
| Verdict: | Malicious activity |
| Analysis date: | June 25, 2025, 19:04:04 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with no line terminators |
| MD5: | 8CEE4F964B12E72337E0D300CA94AF5F |
| SHA1: | 02ED20453E8329ECF806C8FE9ED20B9CFA097F03 |
| SHA256: | DD1EFFE797AC6480CB4A2DCA6BE17EA9B560F0A428D1D9530EB3E70C5D94399B |
| SSDEEP: | 3:N8RlJKmLLn:2dn |
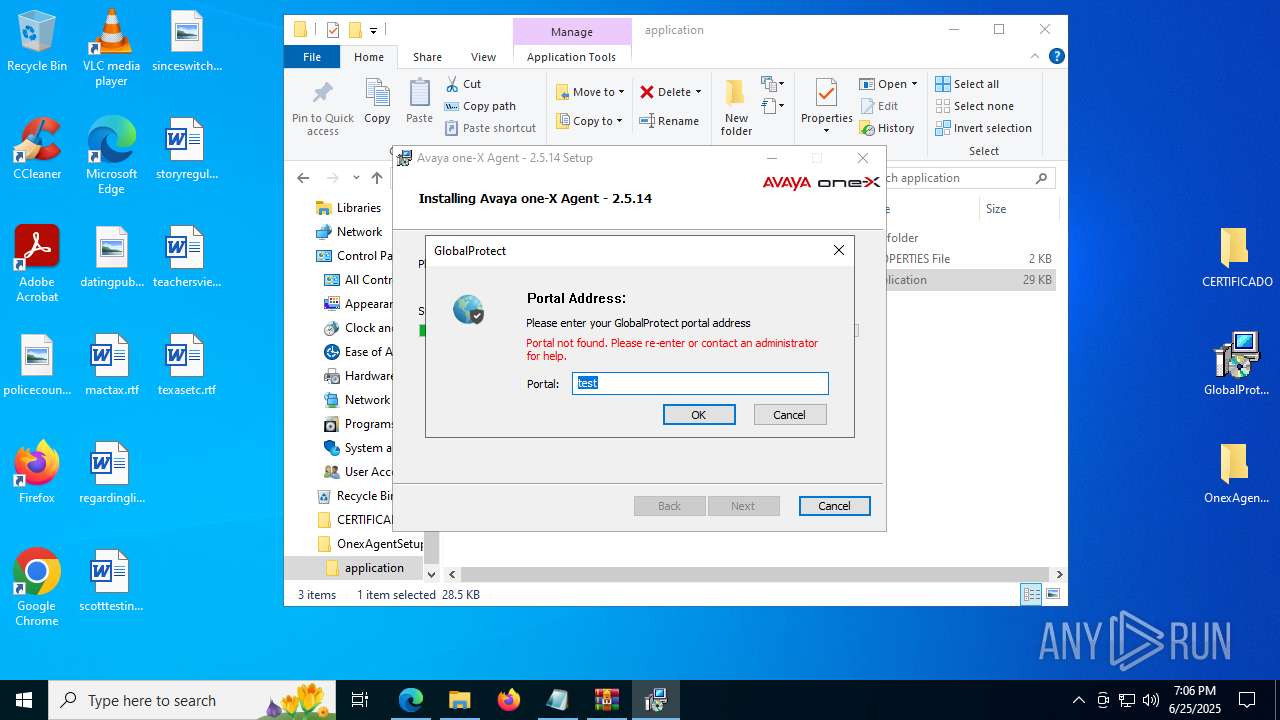
MALICIOUS
Changes the autorun value in the registry
- msiexec.exe (PID: 7108)
- vcredist_x86.exe (PID: 6128)
Executing a file with an untrusted certificate
- vcredist_x86.exe (PID: 6128)
- vcredist_x86.exe (PID: 7364)
- QosServM.exe (PID: 7136)
Creates a new registry key or changes the value of an existing one (SCRIPT)
- msiexec.exe (PID: 1480)
Registers / Runs the DLL via REGSVR32.EXE
- msiexec.exe (PID: 7108)
Accesses system services(Win32_Service) via WMI (SCRIPT)
- msiexec.exe (PID: 1480)
Reads the value of a key from the registry (SCRIPT)
- msiexec.exe (PID: 1480)
Starts Visual C# compiler
- OneXAgentUI.exe (PID: 4052)
SUSPICIOUS
Executes as Windows Service
- VSSVC.exe (PID: 7996)
- PanGPS.exe (PID: 4832)
- QosServM.exe (PID: 7136)
Reads the date of Windows installation
- OneXAgentSetup.exe (PID: 3936)
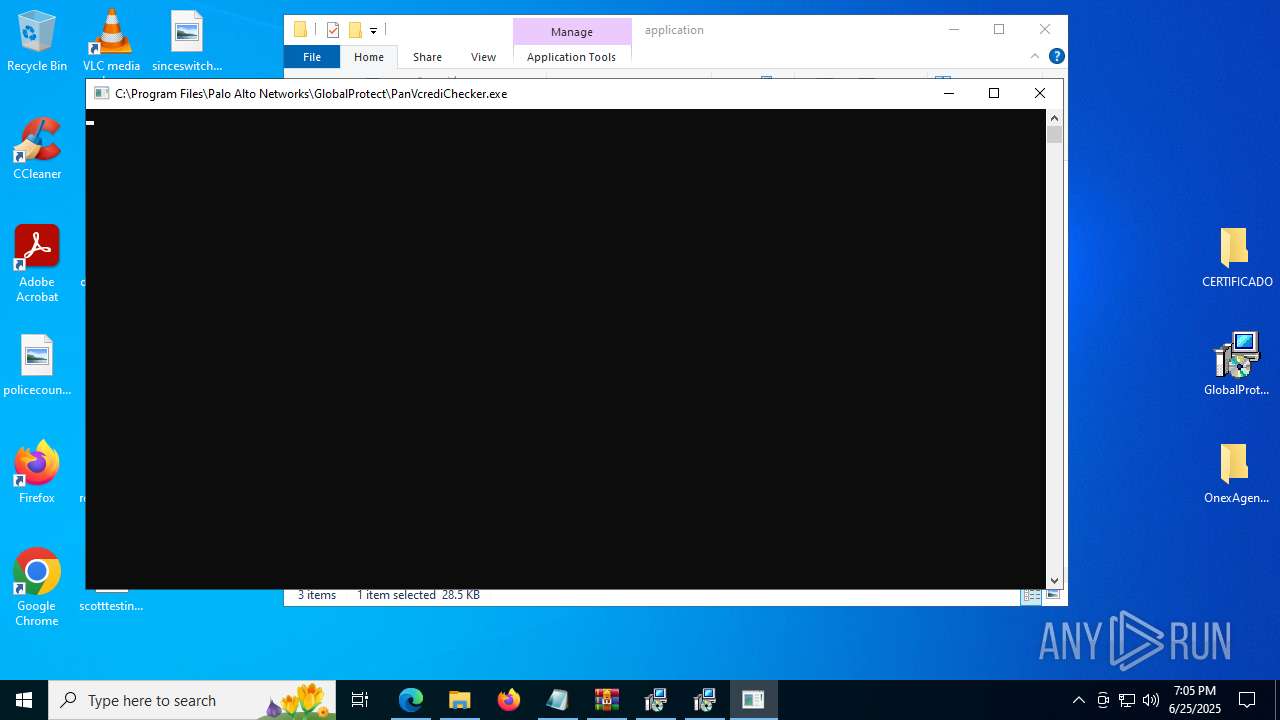
- PanVcrediChecker.exe (PID: 3968)
Reads security settings of Internet Explorer
- OneXAgentSetup.exe (PID: 3936)
- PanVcrediChecker.exe (PID: 3968)
- PanGPA.exe (PID: 3052)
- PanGPS.exe (PID: 4832)
- msiexec.exe (PID: 1636)
- OneXAgentUI.exe (PID: 4052)
Accesses OperatingSystem(Win32_OperatingSystem) via WMI (SCRIPT)
- msiexec.exe (PID: 1636)
Executes WMI query (SCRIPT)
- msiexec.exe (PID: 1636)
- msiexec.exe (PID: 1480)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 7108)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 7108)
- drvinst.exe (PID: 5612)
- PanGPS.exe (PID: 1480)
Process drops legitimate windows executable
- msiexec.exe (PID: 7108)
- vcredist_x86.exe (PID: 7364)
- vcredist_x86.exe (PID: 6128)
- TiWorker.exe (PID: 1328)
Accesses WMI object, sets custom ImpersonationLevel (SCRIPT)
- msiexec.exe (PID: 1636)
- msiexec.exe (PID: 1480)
Changes Internet Explorer settings (feature browser emulation)
- PanVcrediChecker.exe (PID: 3968)
Executing commands from a ".bat" file
- PanVcrediChecker.exe (PID: 3968)
Application launched itself
- vcredist_x86.exe (PID: 6128)
Starts CMD.EXE for commands execution
- PanVcrediChecker.exe (PID: 3968)
- QosServInst.exe (PID: 1840)
Executable content was dropped or overwritten
- vcredist_x86.exe (PID: 7364)
- vcredist_x86.exe (PID: 6128)
- PanGPS.exe (PID: 1480)
- TiWorker.exe (PID: 1328)
- cmd.exe (PID: 5908)
- drvinst.exe (PID: 5612)
- csc.exe (PID: 1484)
- csc.exe (PID: 6308)
- csc.exe (PID: 4652)
- csc.exe (PID: 8244)
- csc.exe (PID: 8336)
- csc.exe (PID: 8428)
- csc.exe (PID: 8624)
- csc.exe (PID: 8712)
- csc.exe (PID: 8532)
- csc.exe (PID: 8804)
- csc.exe (PID: 8896)
- csc.exe (PID: 9080)
- csc.exe (PID: 9168)
- csc.exe (PID: 8988)
- csc.exe (PID: 8408)
Creates a software uninstall entry
- vcredist_x86.exe (PID: 6128)
Creates/Modifies COM task schedule object
- PanGPS.exe (PID: 1480)
Creates files in the driver directory
- PanGPS.exe (PID: 1480)
- drvinst.exe (PID: 5612)
Creates or modifies Windows services
- PanGPS.exe (PID: 1480)
The process drops C-runtime libraries
- msiexec.exe (PID: 7108)
- TiWorker.exe (PID: 1328)
The process creates files with name similar to system file names
- msiexec.exe (PID: 7108)
Reads Microsoft Outlook installation path
- PanGPA.exe (PID: 3052)
Reads Internet Explorer settings
- PanGPA.exe (PID: 3052)
Uses .NET C# to load dll
- OneXAgentUI.exe (PID: 4052)
INFO
Reads security settings of Internet Explorer
- notepad.exe (PID: 2040)
- msiexec.exe (PID: 1832)
Application launched itself
- msedge.exe (PID: 6860)
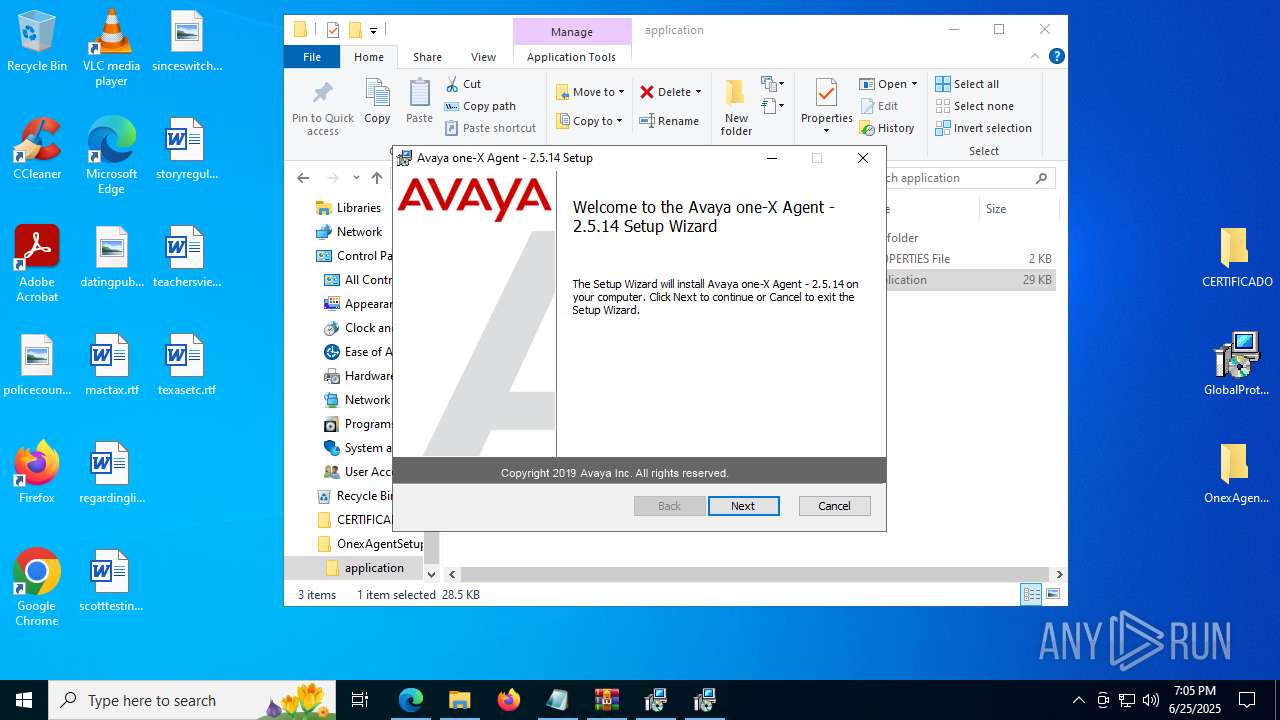
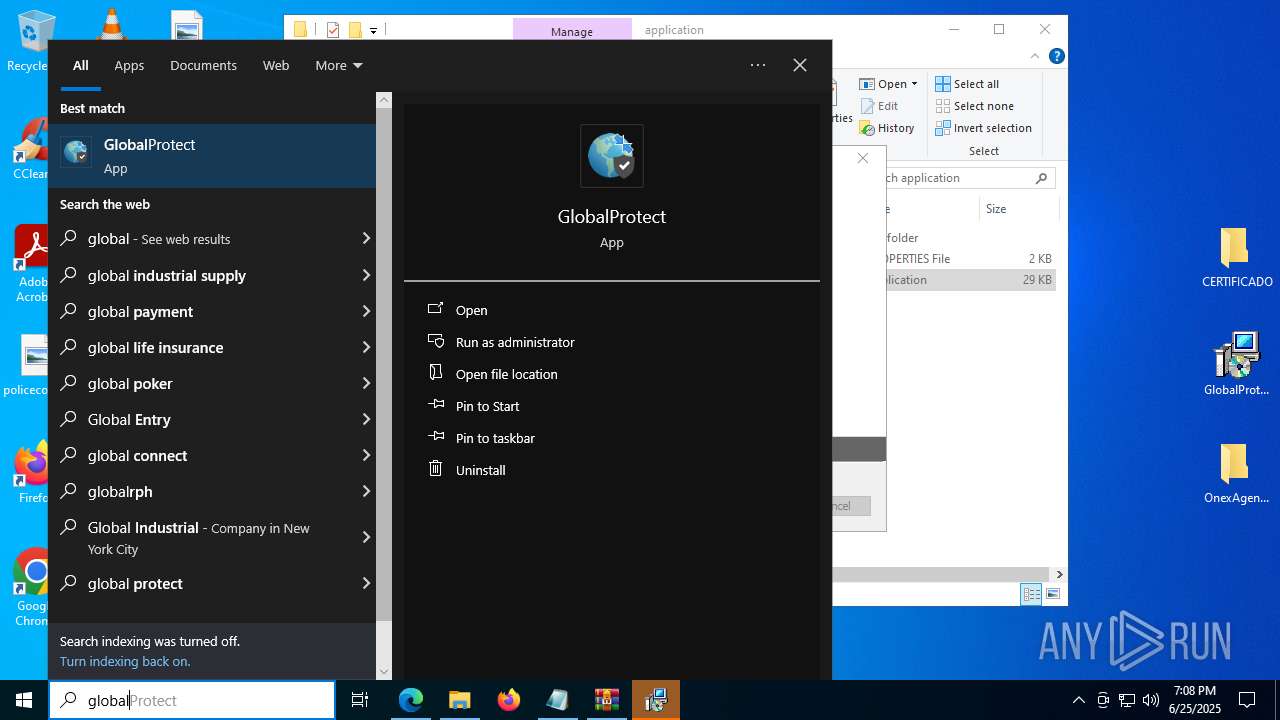
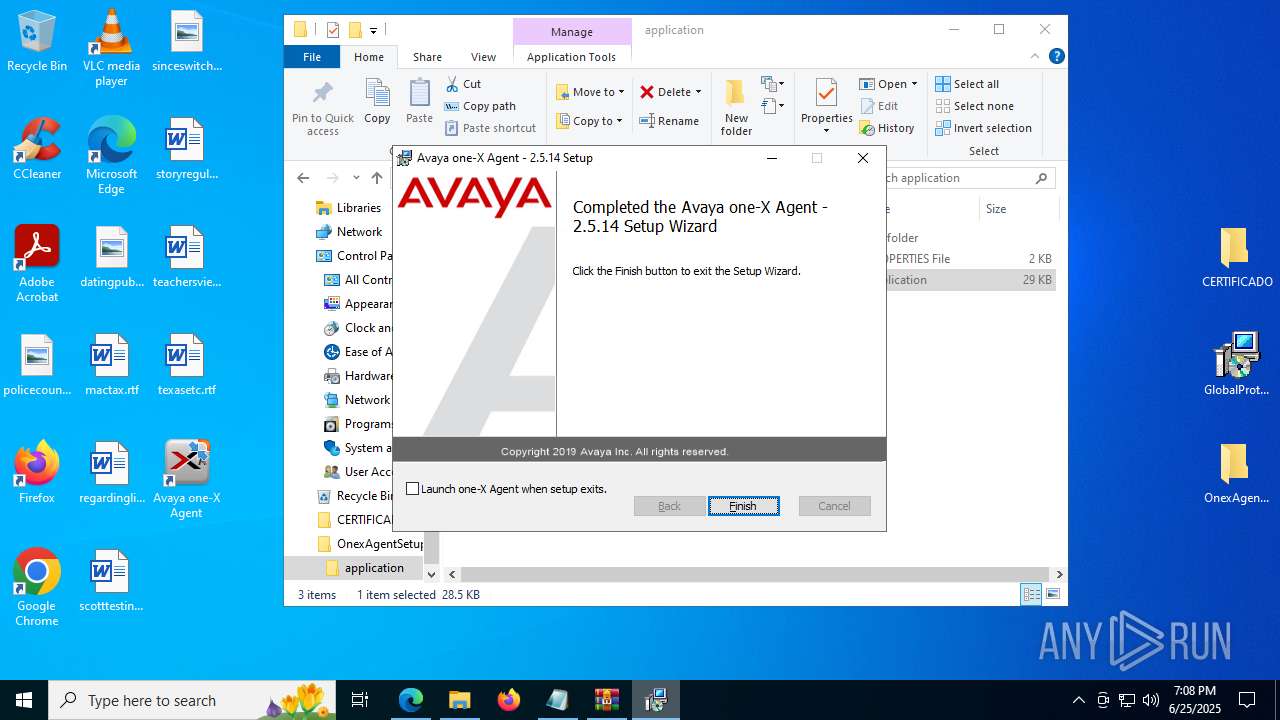
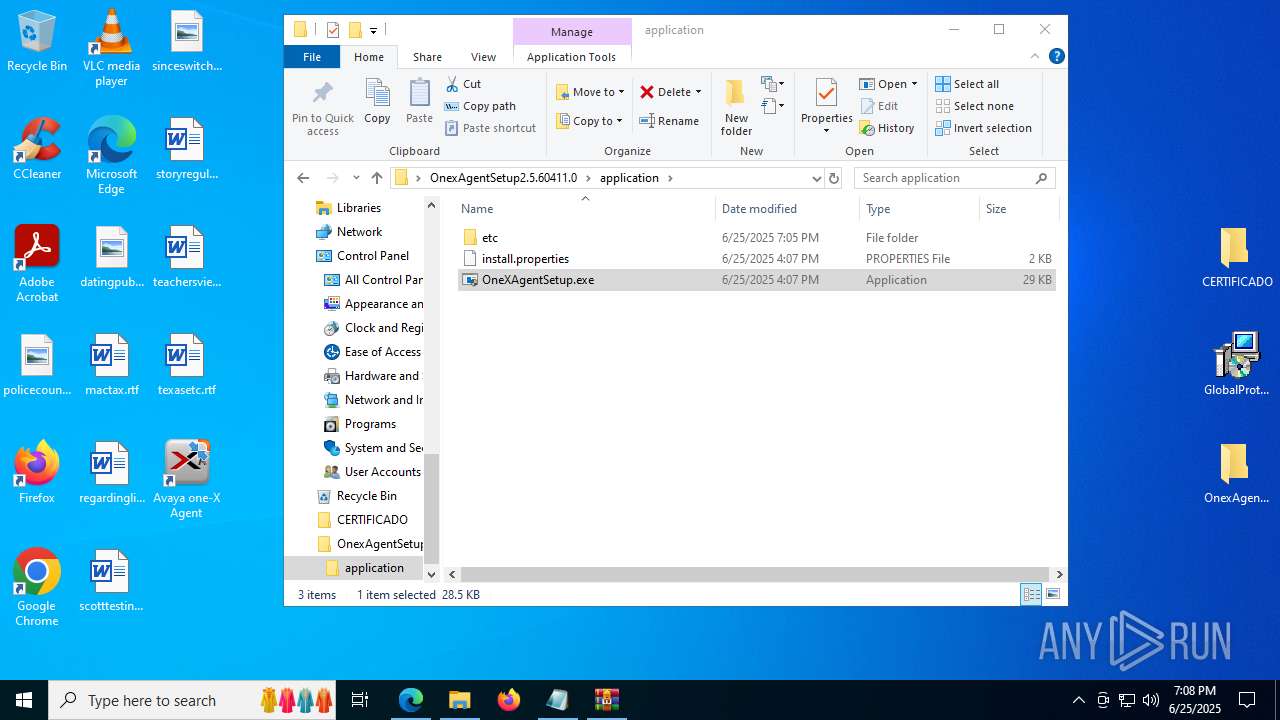
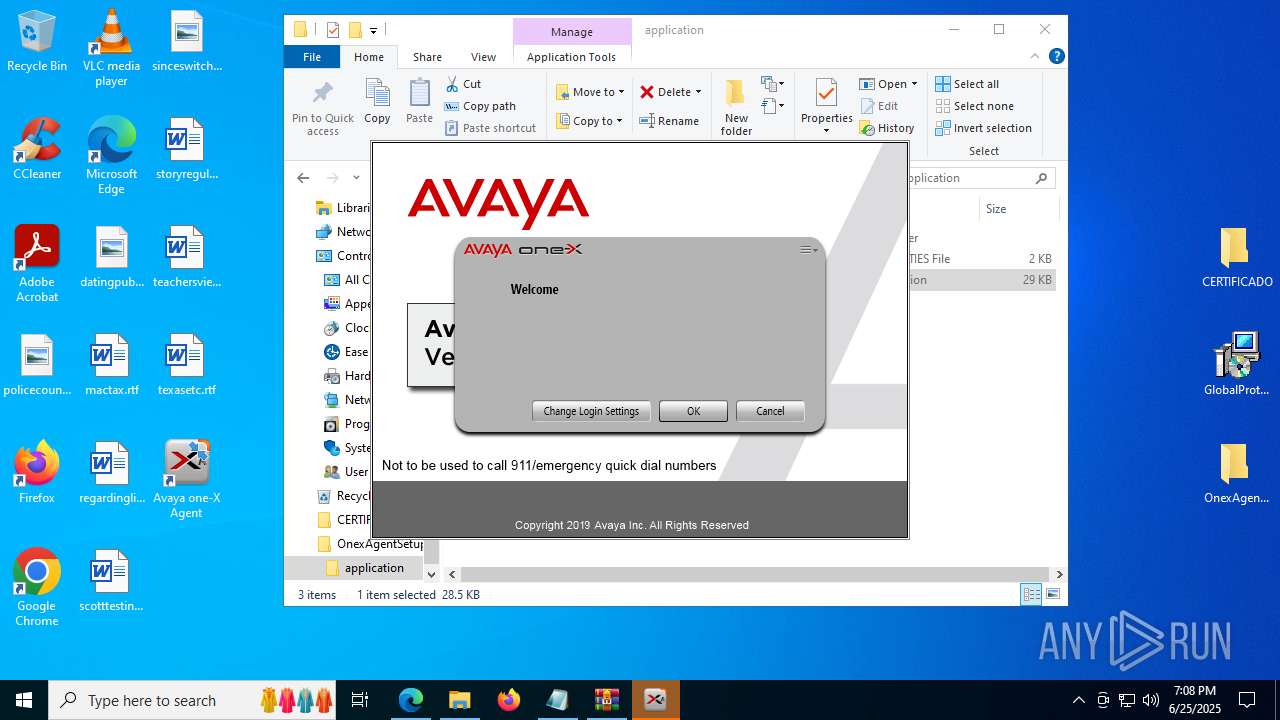
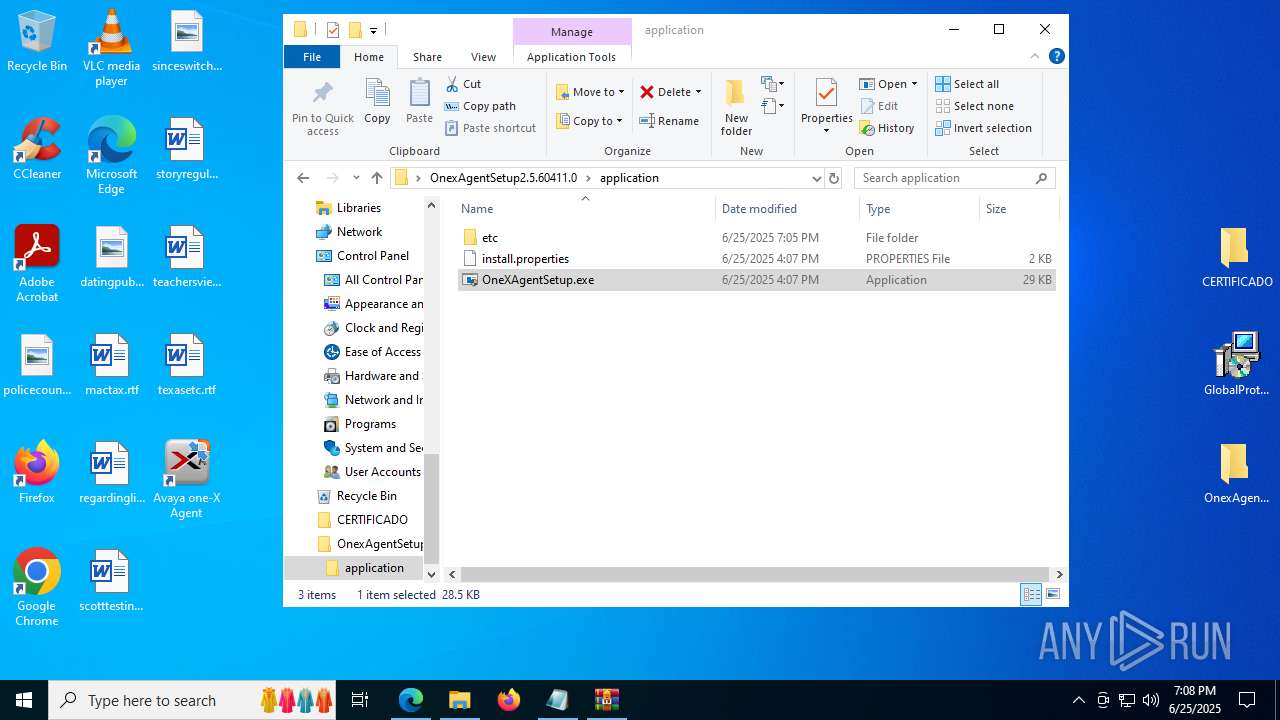
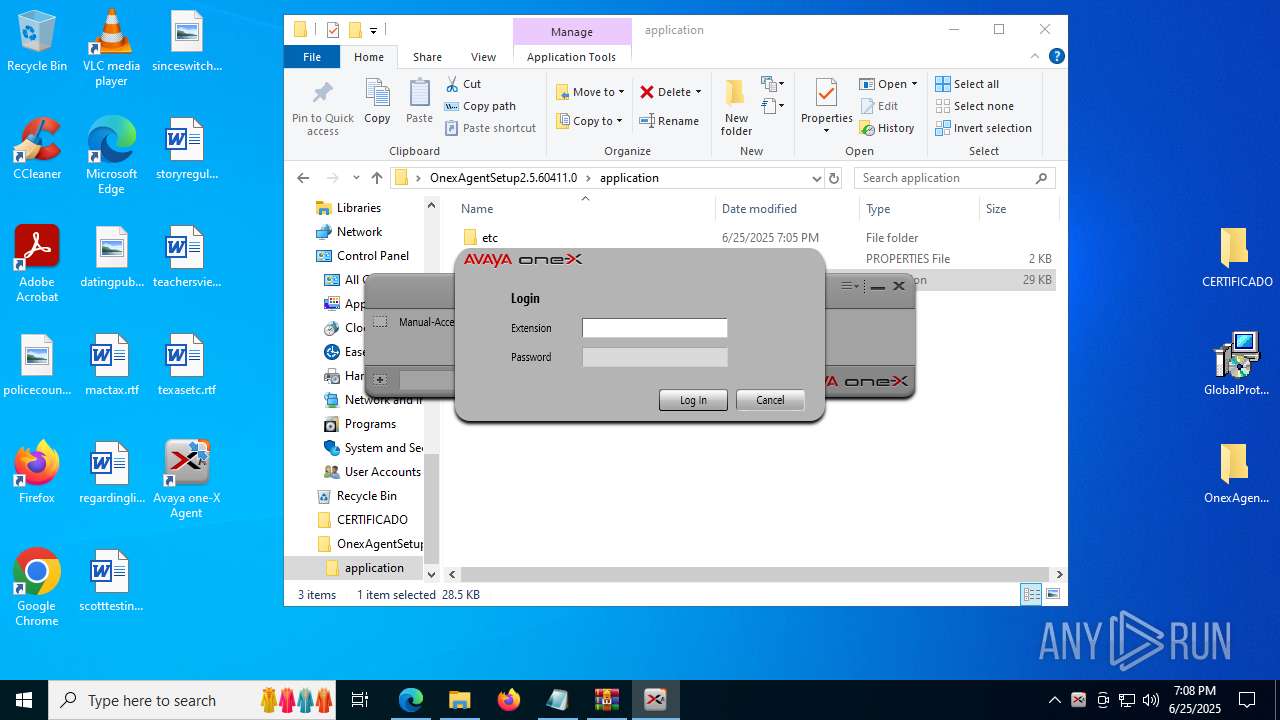
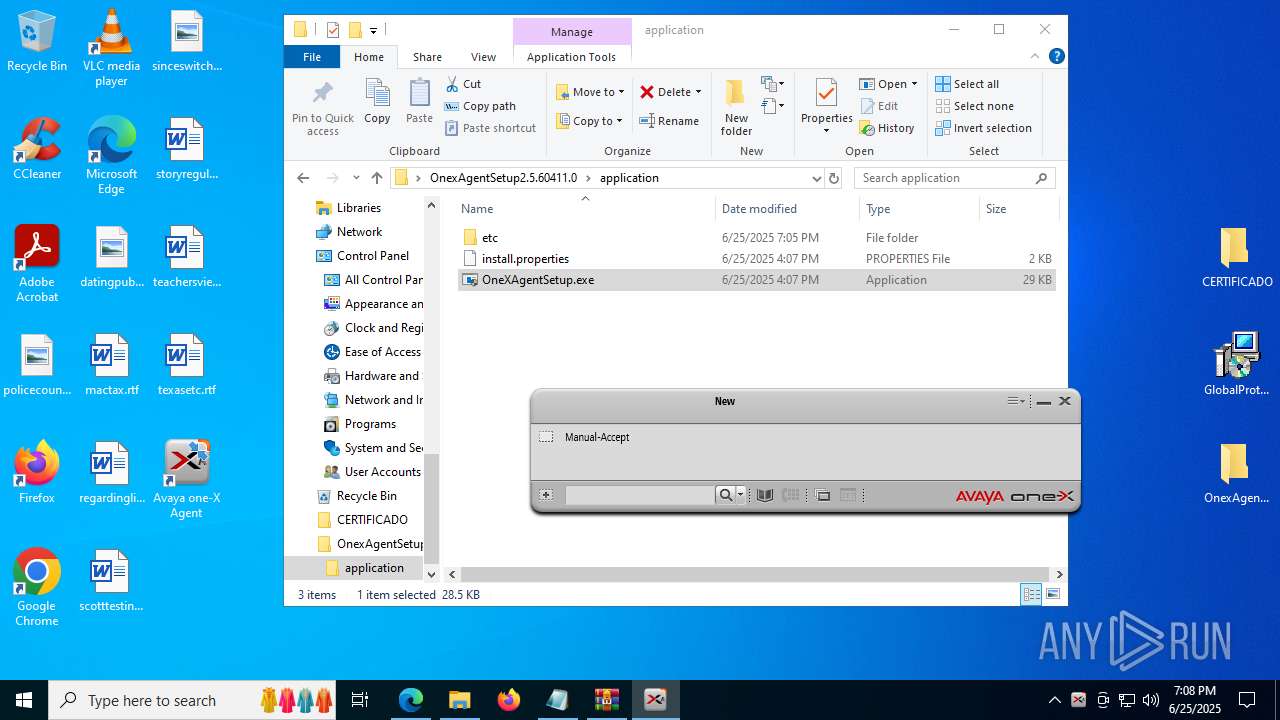
Manual execution by a user
- msedge.exe (PID: 6860)
- msiexec.exe (PID: 1832)
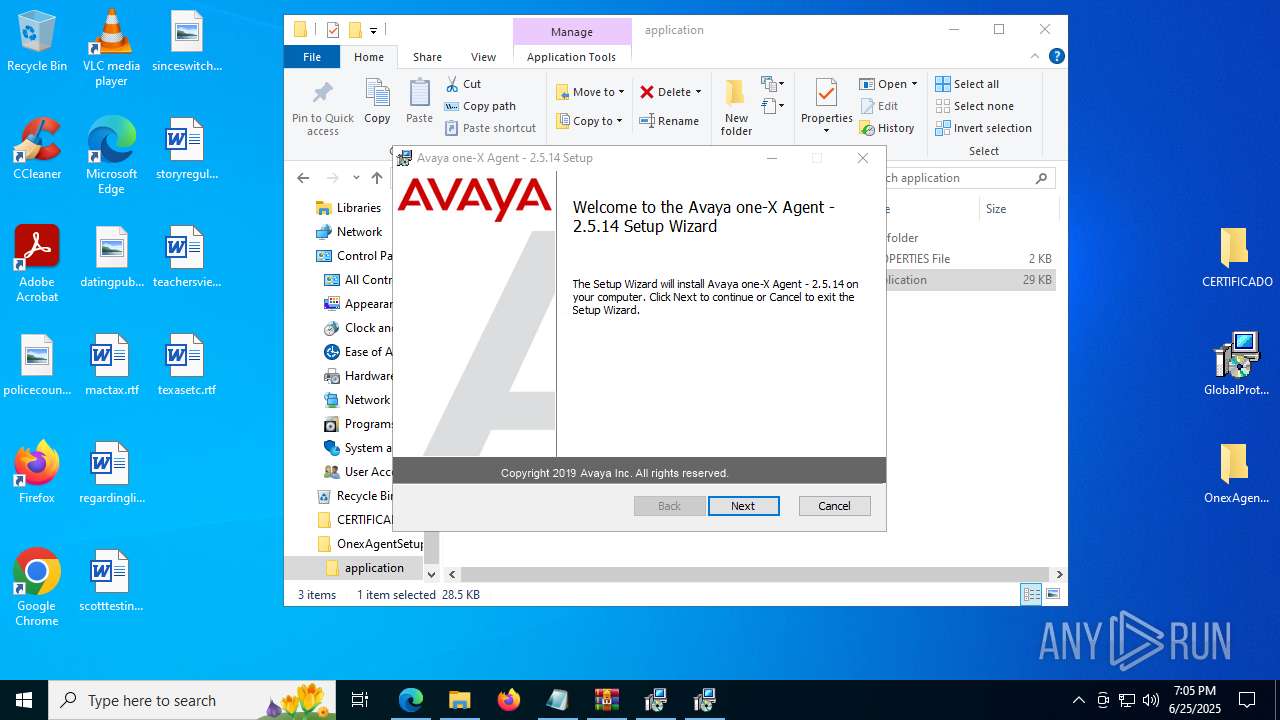
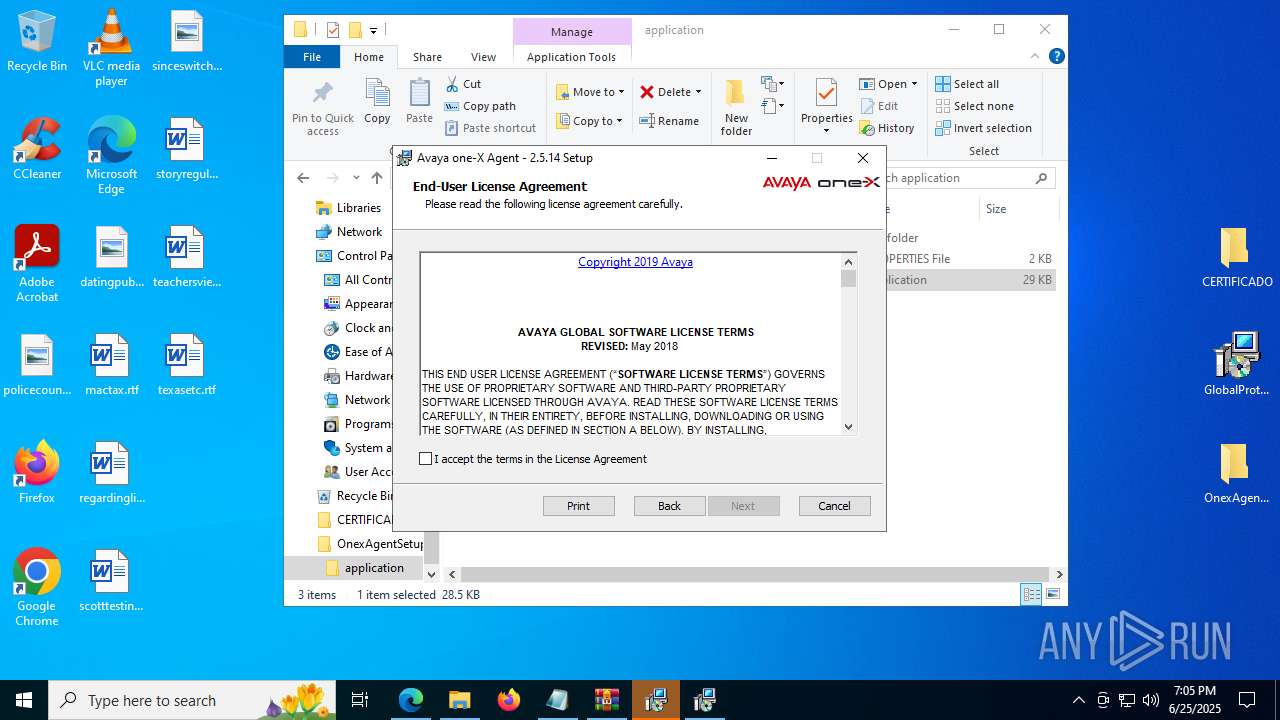
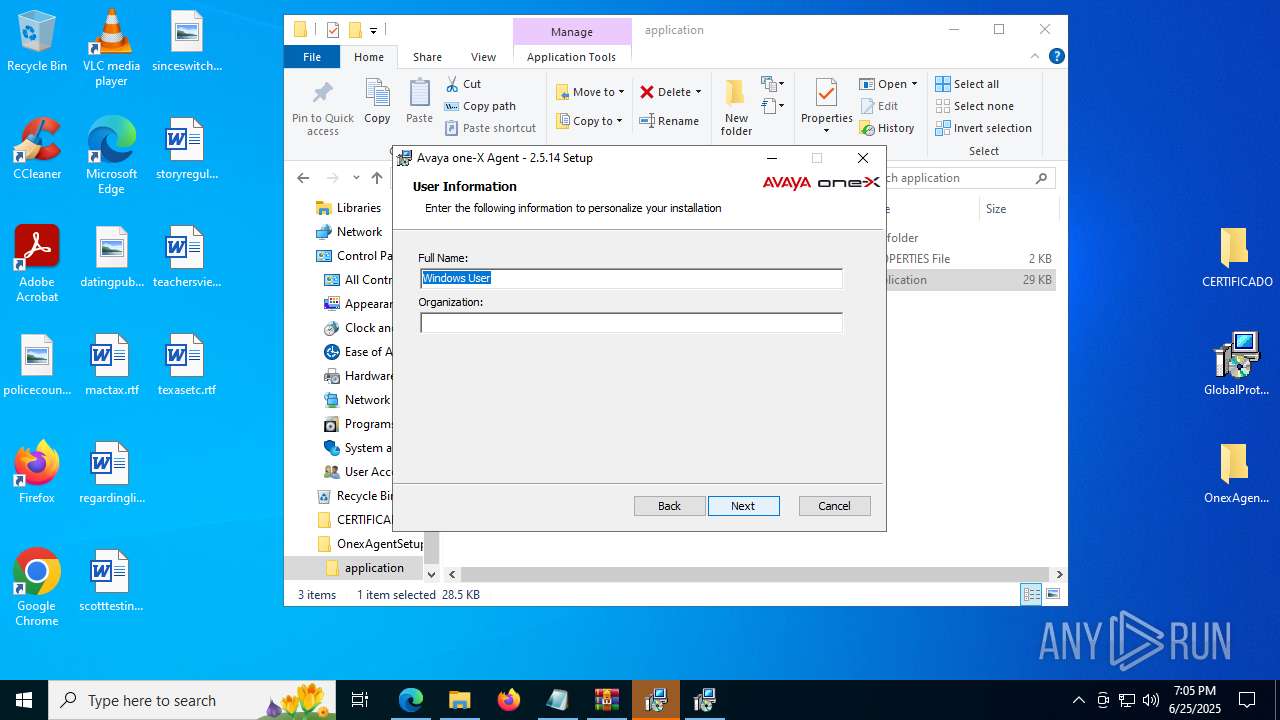
- OneXAgentSetup.exe (PID: 7364)
- OneXAgentSetup.exe (PID: 3936)
- PanGPA.exe (PID: 9028)
Executable content was dropped or overwritten
- msedge.exe (PID: 6384)
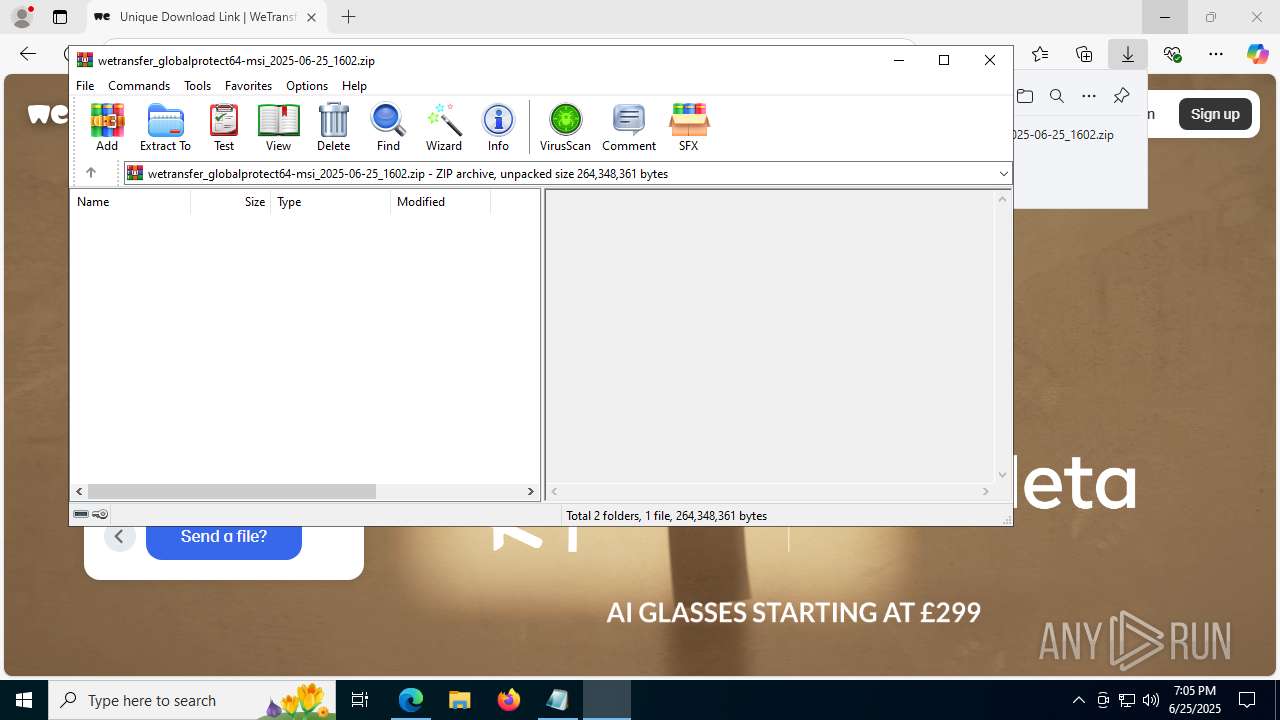
- WinRAR.exe (PID: 4700)
- msiexec.exe (PID: 7108)
- msiexec.exe (PID: 5500)
Reads the computer name
- identity_helper.exe (PID: 8092)
- OneXAgentSetup.exe (PID: 3936)
- msiexec.exe (PID: 1636)
- msiexec.exe (PID: 7108)
- PanVcrediChecker.exe (PID: 3968)
- vcredist_x86.exe (PID: 7364)
- vcredist_x86.exe (PID: 6128)
- PanGPS.exe (PID: 1480)
- drvinst.exe (PID: 5612)
- PanGPS.exe (PID: 4832)
- PanGPA.exe (PID: 3052)
- msiexec.exe (PID: 1480)
- QosServInst.exe (PID: 1840)
- QosServM.exe (PID: 7136)
- OneXAgentUI.exe (PID: 4052)
- SparkEmulator.exe (PID: 7180)
- PanGPA.exe (PID: 9028)
Checks proxy server information
- msiexec.exe (PID: 1832)
- slui.exe (PID: 6424)
- PanGPA.exe (PID: 3052)
Manages system restore points
- SrTasks.exe (PID: 7452)
- SrTasks.exe (PID: 7976)
Creates files or folders in the user directory
- msiexec.exe (PID: 1832)
- PanGPA.exe (PID: 3052)
- SparkEmulator.exe (PID: 7180)
- OneXAgentUI.exe (PID: 4052)
Reads the machine GUID from the registry
- msiexec.exe (PID: 7108)
- vcredist_x86.exe (PID: 6128)
- drvinst.exe (PID: 5612)
- PanGPS.exe (PID: 1480)
- PanGPA.exe (PID: 3052)
- PanGPS.exe (PID: 4832)
- SearchApp.exe (PID: 5328)
- OneXAgentUI.exe (PID: 4052)
- csc.exe (PID: 1484)
- csc.exe (PID: 6308)
- csc.exe (PID: 4652)
- csc.exe (PID: 8244)
- csc.exe (PID: 8336)
- csc.exe (PID: 8428)
- csc.exe (PID: 8532)
- csc.exe (PID: 8624)
- csc.exe (PID: 8712)
- csc.exe (PID: 8804)
- csc.exe (PID: 8896)
- csc.exe (PID: 8988)
- SparkEmulator.exe (PID: 7180)
- csc.exe (PID: 9168)
- csc.exe (PID: 8408)
- csc.exe (PID: 9080)
Create files in a temporary directory
- OneXAgentSetup.exe (PID: 3936)
- msiexec.exe (PID: 5500)
- PanVcrediChecker.exe (PID: 3968)
- vcredist_x86.exe (PID: 7364)
- vcredist_x86.exe (PID: 6128)
- SparkEmulator.exe (PID: 7180)
- cvtres.exe (PID: 7360)
- OneXAgentUI.exe (PID: 4052)
- cvtres.exe (PID: 2092)
- csc.exe (PID: 6308)
- cvtres.exe (PID: 8304)
- csc.exe (PID: 8336)
- csc.exe (PID: 4652)
- cvtres.exe (PID: 8200)
- cvtres.exe (PID: 8396)
- csc.exe (PID: 8244)
- csc.exe (PID: 8428)
- cvtres.exe (PID: 8500)
- csc.exe (PID: 8532)
- cvtres.exe (PID: 8592)
- cvtres.exe (PID: 8680)
- csc.exe (PID: 8624)
- csc.exe (PID: 8712)
- cvtres.exe (PID: 8772)
- csc.exe (PID: 8804)
- cvtres.exe (PID: 8864)
- csc.exe (PID: 8896)
- cvtres.exe (PID: 8956)
- csc.exe (PID: 8988)
- cvtres.exe (PID: 9048)
- cvtres.exe (PID: 9136)
- cvtres.exe (PID: 8220)
- csc.exe (PID: 9168)
- csc.exe (PID: 8408)
- csc.exe (PID: 9080)
- csc.exe (PID: 1484)
- cvtres.exe (PID: 8368)
Reads the software policy settings
- msiexec.exe (PID: 7108)
- msiexec.exe (PID: 1832)
- vcredist_x86.exe (PID: 6128)
- drvinst.exe (PID: 5612)
- slui.exe (PID: 6424)
- SearchApp.exe (PID: 5328)
Checks supported languages
- identity_helper.exe (PID: 8092)
- msiexec.exe (PID: 1636)
- msiexec.exe (PID: 7108)
- OneXAgentSetup.exe (PID: 3936)
- vcredist_x86.exe (PID: 6128)
- vcredist_x86.exe (PID: 7364)
- SearchApp.exe (PID: 5328)
- PanVcrediChecker.exe (PID: 3968)
- PanGPS.exe (PID: 1480)
- drvinst.exe (PID: 5612)
- PanGPS.exe (PID: 4832)
- msiexec.exe (PID: 1480)
- PanGPA.exe (PID: 3052)
- QosServInst.exe (PID: 1840)
- QosServM.exe (PID: 7136)
- SparkEmulator.exe (PID: 7180)
- csc.exe (PID: 1484)
- OneXAgentUI.exe (PID: 4052)
- cvtres.exe (PID: 7360)
- csc.exe (PID: 6308)
- cvtres.exe (PID: 2092)
- csc.exe (PID: 4652)
- cvtres.exe (PID: 8200)
- csc.exe (PID: 8244)
- cvtres.exe (PID: 8304)
- csc.exe (PID: 8336)
- cvtres.exe (PID: 8396)
- csc.exe (PID: 8428)
- cvtres.exe (PID: 8500)
- csc.exe (PID: 8532)
- csc.exe (PID: 8624)
- cvtres.exe (PID: 8680)
- csc.exe (PID: 8712)
- cvtres.exe (PID: 8772)
- csc.exe (PID: 8804)
- cvtres.exe (PID: 8592)
- cvtres.exe (PID: 8864)
- cvtres.exe (PID: 8956)
- csc.exe (PID: 8988)
- cvtres.exe (PID: 9048)
- csc.exe (PID: 8896)
- csc.exe (PID: 9168)
- cvtres.exe (PID: 9136)
- cvtres.exe (PID: 8220)
- csc.exe (PID: 8408)
- cvtres.exe (PID: 8368)
- csc.exe (PID: 9080)
- PanGPA.exe (PID: 9028)
Reads Environment values
- identity_helper.exe (PID: 8092)
- PanGPS.exe (PID: 4832)
- PanGPA.exe (PID: 3052)
- PanGPA.exe (PID: 9028)
Process checks computer location settings
- OneXAgentSetup.exe (PID: 3936)
- PanVcrediChecker.exe (PID: 3968)
- SearchApp.exe (PID: 5328)
- msiexec.exe (PID: 1636)
- OneXAgentUI.exe (PID: 4052)
Reads Microsoft Office registry keys
- msedge.exe (PID: 6860)
The sample compiled with english language support
- msiexec.exe (PID: 7108)
- vcredist_x86.exe (PID: 7364)
- vcredist_x86.exe (PID: 6128)
- drvinst.exe (PID: 5612)
- PanGPS.exe (PID: 1480)
- TiWorker.exe (PID: 1328)
- cmd.exe (PID: 5908)
Launching a file from a Registry key
- msiexec.exe (PID: 7108)
- vcredist_x86.exe (PID: 6128)
Creates a software uninstall entry
- msiexec.exe (PID: 7108)
Creates files in the program directory
- vcredist_x86.exe (PID: 6128)
- PanGPS.exe (PID: 1480)
The sample compiled with chinese language support
- msiexec.exe (PID: 7108)
- TiWorker.exe (PID: 1328)
The sample compiled with german language support
- msiexec.exe (PID: 7108)
- TiWorker.exe (PID: 1328)
The sample compiled with korean language support
- msiexec.exe (PID: 7108)
- TiWorker.exe (PID: 1328)
The sample compiled with french language support
- msiexec.exe (PID: 7108)
- TiWorker.exe (PID: 1328)
The sample compiled with russian language support
- msiexec.exe (PID: 7108)
The sample compiled with spanish language support
- msiexec.exe (PID: 7108)
- TiWorker.exe (PID: 1328)
The sample compiled with japanese language support
- msiexec.exe (PID: 7108)
- TiWorker.exe (PID: 1328)
Reads product name
- PanGPS.exe (PID: 4832)
- PanGPA.exe (PID: 3052)
- PanGPA.exe (PID: 9028)
The sample compiled with Italian language support
- msiexec.exe (PID: 7108)
- TiWorker.exe (PID: 1328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
290
Monitored processes
129
Malicious processes
13
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1232 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc4565f208,0x7ffc4565f214,0x7ffc4565f220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1328 | C:\WINDOWS\winsxs\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe -Embedding | C:\Windows\WinSxS\amd64_microsoft-windows-servicingstack_31bf3856ad364e35_10.0.19041.3989_none_7ddb45627cb30e03\TiWorker.exe | svchost.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Worker Version: 10.0.19041.3989 (WinBuild.160101.0800) Modules
| |||||||||||||||
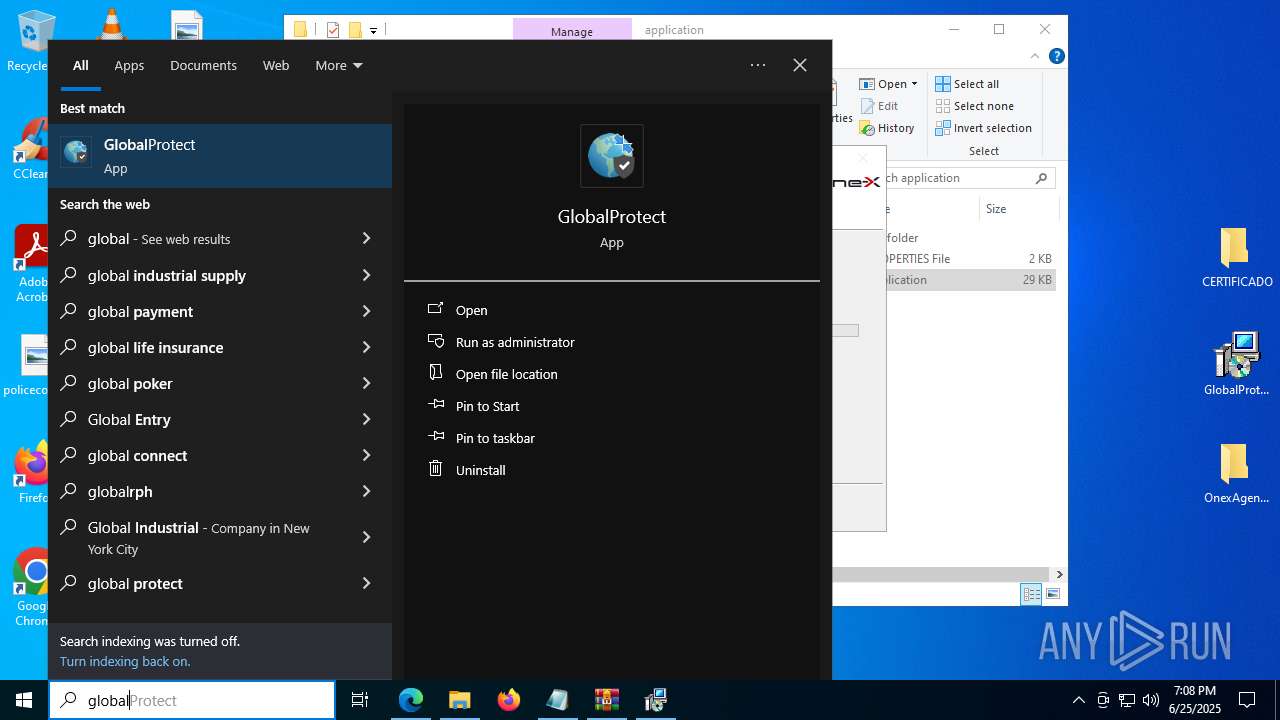
| 1480 | "C:\Program Files\Palo Alto Networks\GlobalProtect\PanGPS.exe" -commit | C:\Program Files\Palo Alto Networks\GlobalProtect\PanGPS.exe | cmd.exe | ||||||||||||
User: SYSTEM Company: Palo Alto Networks Integrity Level: SYSTEM Description: GlobalProtect service Exit code: 0 Version: 5.0.0-87 Modules
| |||||||||||||||
| 1480 | C:\Windows\syswow64\MsiExec.exe -Embedding A8DF30B6115F50763724423FCA617EB2 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1484 | "C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\nmp4twh1\nmp4twh1.cmdline" | C:\Windows\Microsoft.NET\Framework\v4.0.30319\csc.exe | OneXAgentUI.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Visual C# Command Line Compiler Exit code: 0 Version: 4.8.9037.0 built by: NET481REL1 Modules
| |||||||||||||||
| 1636 | C:\Windows\syswow64\MsiExec.exe -Embedding D672CFF923293EB48B4EF74ED9A21DD3 C | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
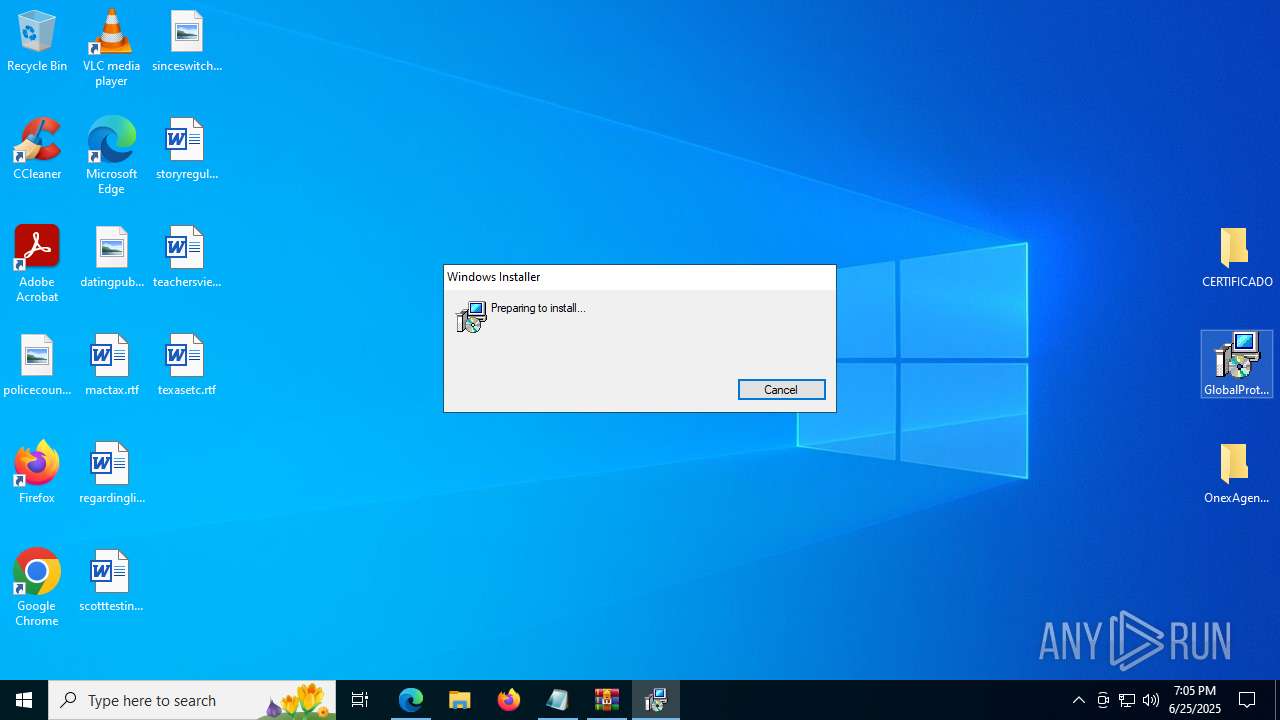
| 1832 | "C:\WINDOWS\System32\msiexec.exe" /i "C:\Users\admin\Desktop\GlobalProtect64.msi" | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
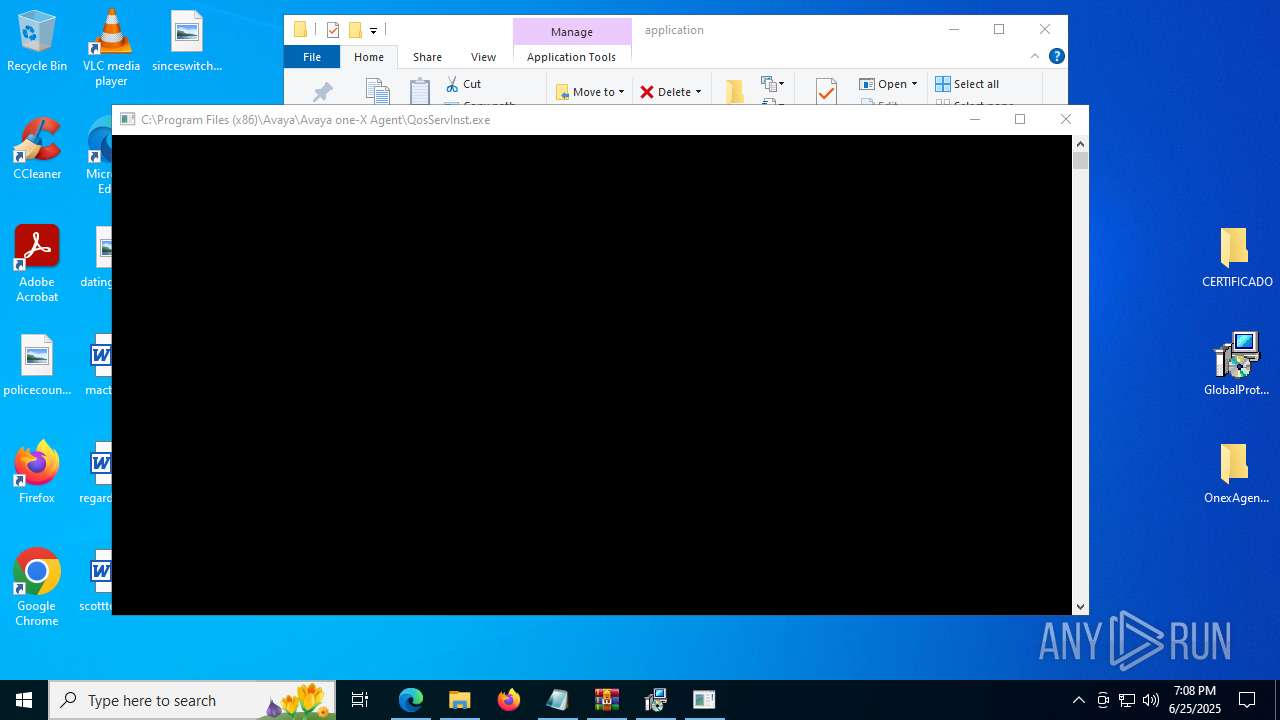
| 1840 | "C:\Program Files (x86)\Avaya\Avaya one-X Agent\QosServInst" -i C:\WINDOWS\SysWOW64\ | C:\Program Files (x86)\Avaya\Avaya one-X Agent\QosServInst.exe | — | msiexec.exe | |||||||||||
User: admin Company: Avaya Inc. Integrity Level: HIGH Description: QosServInst Exit code: 0 Version: 4, 1, 0, 1 Modules
| |||||||||||||||
| 1852 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=4276,i,5819471739112124505,5306678624751920114,262144 --variations-seed-version --mojo-platform-channel-handle=1544 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1852 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=35 --always-read-main-dll --field-trial-handle=8092,i,5819471739112124505,5306678624751920114,262144 --variations-seed-version --mojo-platform-channel-handle=5832 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
67 458
Read events
64 888
Write events
2 440
Delete events
130
Modification events
| (PID) Process: | (6860) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6860) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6860) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6860) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C5FE7E6500972F00 | |||
| (PID) Process: | (6860) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6860) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 4402846500972F00 | |||
| (PID) Process: | (6860) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197214 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {DFB916B4-0E8C-4EF8-8835-2B058CF48DAB} | |||
| (PID) Process: | (6860) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197214 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {910707A5-B8B4-4733-B47A-CCCA83FB000C} | |||
| (PID) Process: | (6860) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197214 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {833678CB-A729-40EA-B2E2-2F8DBEC6B6AC} | |||
| (PID) Process: | (6860) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\197214 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {6D368101-81E0-4307-BE04-A1218FB9ACE1} | |||
Executable files
215
Suspicious files
1 188
Text files
2 218
Unknown types
229
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6860 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1784a1.TMP | — | |
MD5:— | SHA256:— | |||
| 6860 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6860 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1784d0.TMP | — | |
MD5:— | SHA256:— | |||
| 6860 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6860 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF1784df.TMP | — | |
MD5:— | SHA256:— | |||
| 6860 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6860 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1784c0.TMP | — | |
MD5:— | SHA256:— | |||
| 6860 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6860 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF1784df.TMP | — | |
MD5:— | SHA256:— | |||
| 6860 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1784df.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
42
TCP/UDP connections
337
DNS requests
348
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.48.23.174:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6384 | msedge.exe | GET | 200 | 150.171.28.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:OfLQ18BiR8slXIGgCc2O4MDnIo6ML5nKCjkN29UPy94&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
1964 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
7312 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
1832 | msiexec.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBT3xL4LQLXDRDM9P665TW442vrsUQQUReuir%2FSSy4IxLVGLp6chnfNtyA8CEAQJGBtf1btmdVNDtW%2BVUAg%3D | unknown | — | — | whitelisted |
7388 | svchost.exe | HEAD | 200 | 23.50.131.218:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/bf8090eb-6e5c-4c51-9250-5bf9b46cf160?P1=1751145492&P2=404&P3=2&P4=CIZH79rEeP%2flc3e%2fCf7irNAO%2biMJI3m0myc6iaTdYi1MY3IzGzBZ4V7lXj63uRZSxzCYnS123mdvUPMYZ6byJw%3d%3d | unknown | — | — | whitelisted |
7312 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7388 | svchost.exe | HEAD | 200 | 23.50.131.218:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/9244b52a-55cc-41a2-b7c4-7f4983d8753c?P1=1751145495&P2=404&P3=2&P4=cRuaQeAYhxXgPzpY3LdfRvGHWT7q1YlgegvLe2J7rkcsIgWISDhDwGqxFLNRe%2bRwo2ba5GRcPs1KzsO%2fez0K9A%3d%3d | unknown | — | — | whitelisted |
1832 | msiexec.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSnR4FoxLLkI7vkvsUIFlZt%2BlGH3gQUWsS5eyoKo6XqcQPAYPkt9mV1DlgCEAtp%2F88yYIeGVBEyFfds0hk%3D | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 69.192.161.44:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5876 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.48.23.174:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
1964 | svchost.exe | 20.190.159.4:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1964 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ntp.msn.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
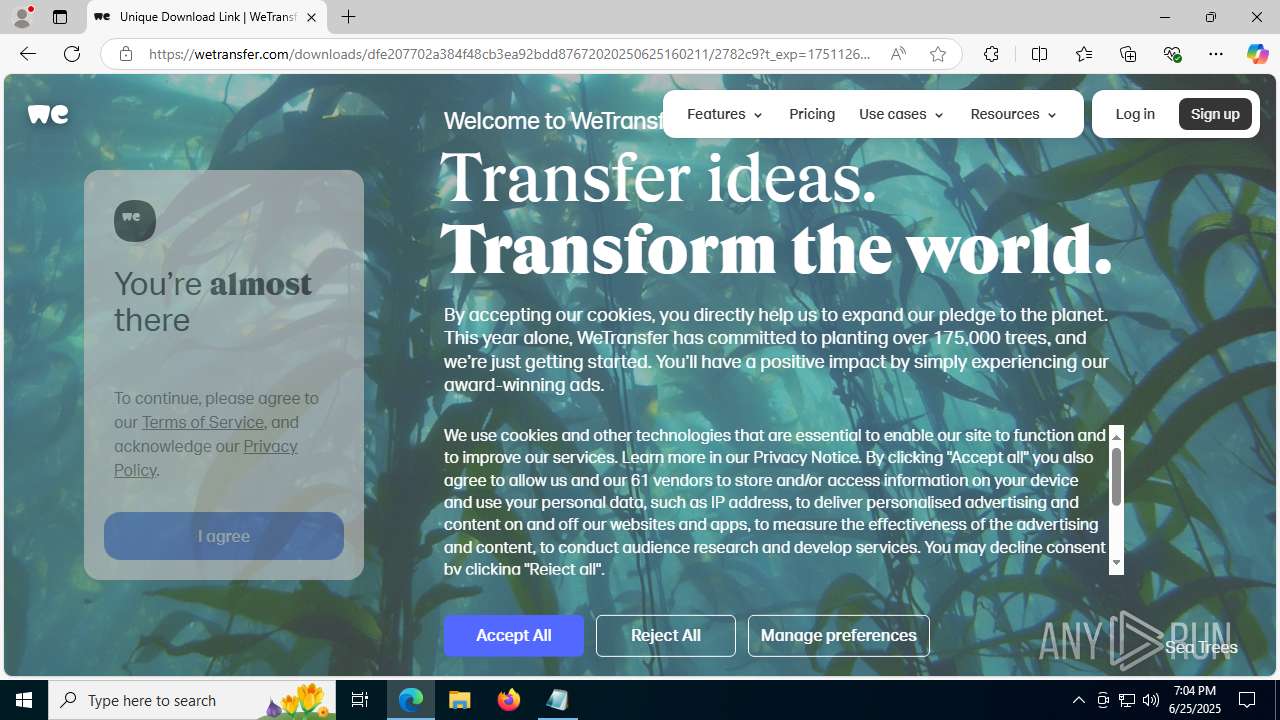
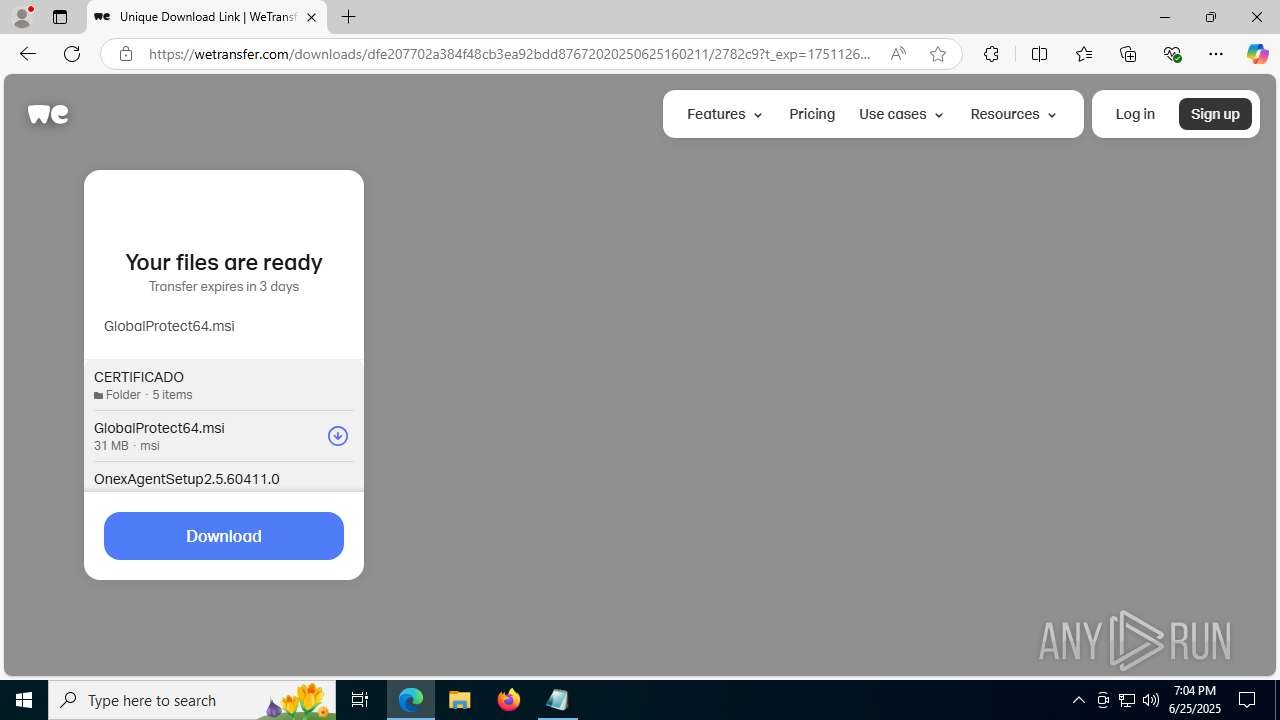
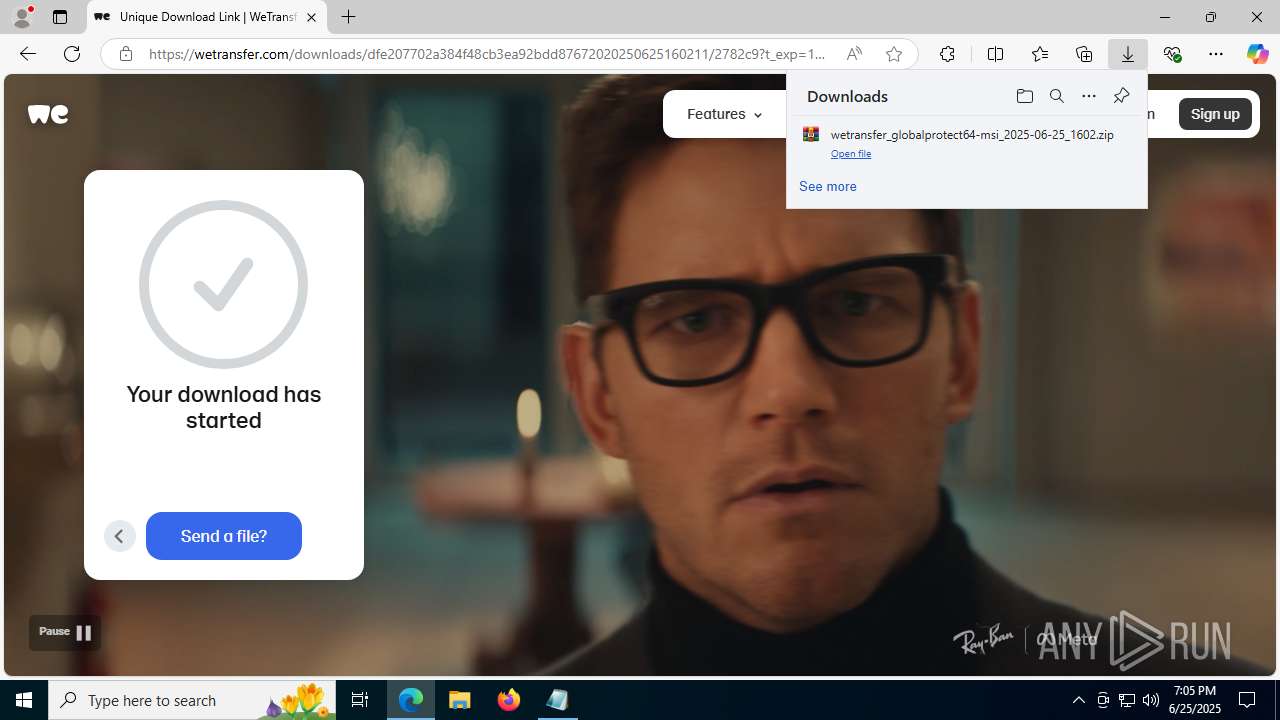
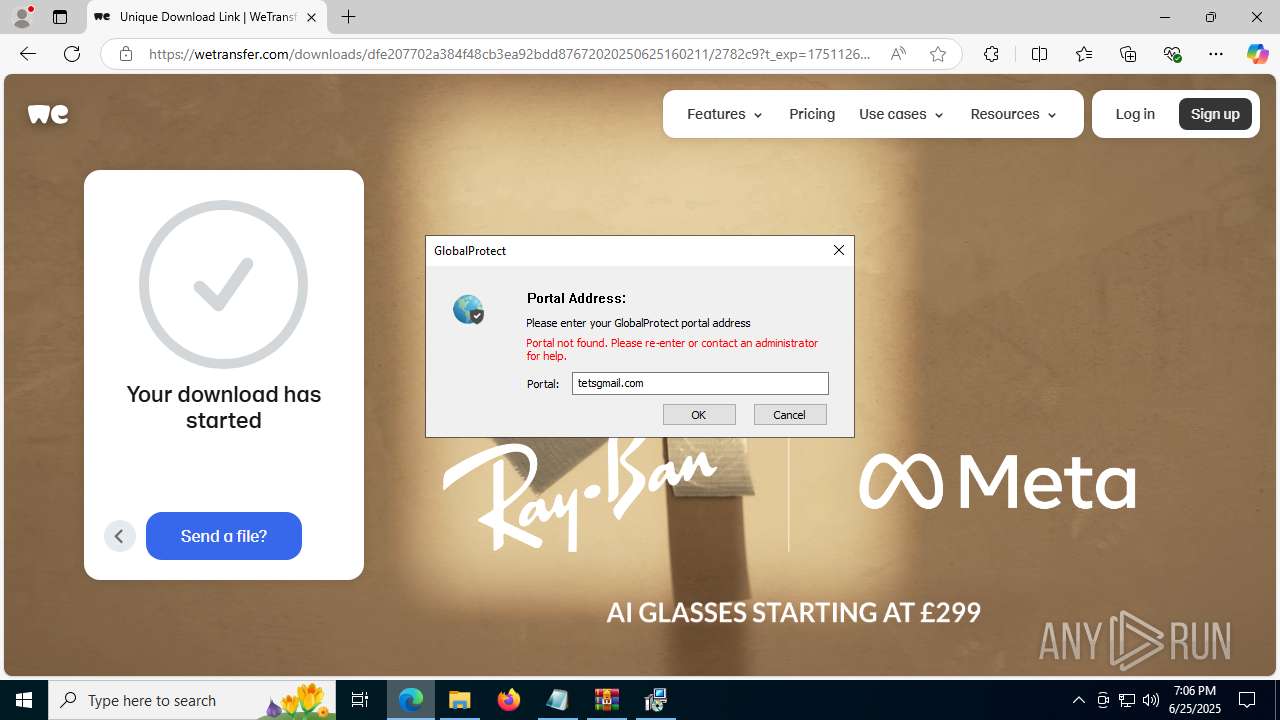
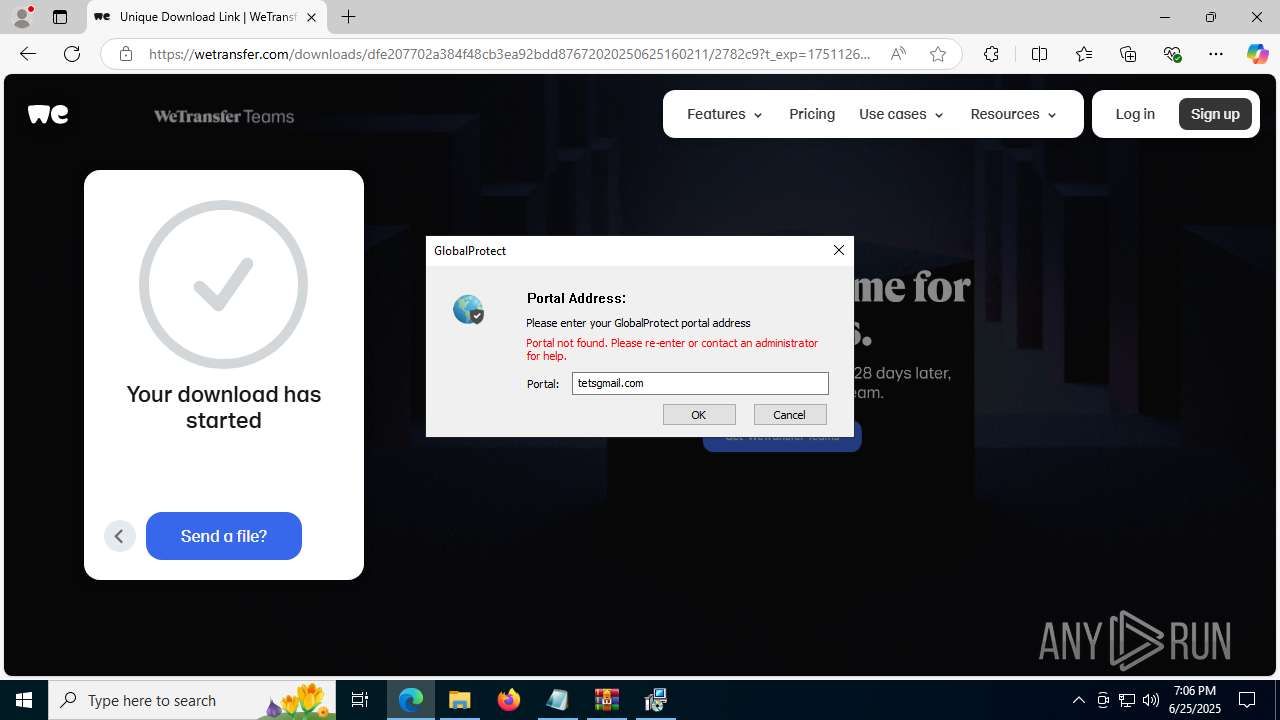
6384 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (wetransfer .com) |
6384 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (wetransfer .com) |
6384 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (wetransfer .com) |
6384 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (wetransfer .com) |
6384 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6384 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6384 | msedge.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
6384 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (wetransfer .com) |
6384 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (wetransfer .com) |
Process | Message |
|---|---|
OneXAgentUI.exe | Unable to read configuration section common/logging. Using no-op implemenation.
|
SparkEmulator.exe | CLocalDataAdaptor() : ContactsPath = C:\Users\admin\AppData\Roaming\Avaya\one-X Agent\2.5\contacts. |
SparkEmulator.exe | CLocalDataAdaptor() : LenovoSettingsPath = C:\Users\admin\AppData\Roaming\Avaya\one-X Agent\2.5\profilerequest. |
SparkEmulator.exe | CLocalDataAdaptor() : UserProfilePath = C:\Users\admin\AppData\Roaming\Avaya\one-X Agent\2.5\userprofile. |
SparkEmulator.exe | Open() : Failed for file skins/9630/9630.xml |
SparkEmulator.exe | CLocalDataAdaptor() : ConfigPath = C:\Users\admin\AppData\Roaming\Avaya\one-X Agent\2.5\config. |
SparkEmulator.exe | CLocalDataAdaptor() : DirServerSettingsPath = C:\Users\admin\AppData\Roaming\Avaya\one-X Agent\2.5\dirserver.xml |
SparkEmulator.exe | COneXPortalAdaptor::RemoveDirectory(C:\Users\admin\AppData\Roaming\Avaya\one-X Agent\2.5\Messages\) failed. rc=2
|
SparkEmulator.exe | CLocalDataAdaptor() : UserAddressPath = C:\Users\admin\AppData\Roaming\Avaya\one-X Agent\2.5\addresses. |
SparkEmulator.exe | Open() : Failed for file C:\Users\admin\AppData\Roaming\Avaya\one-X Agent\2.5\dirserver.xml |