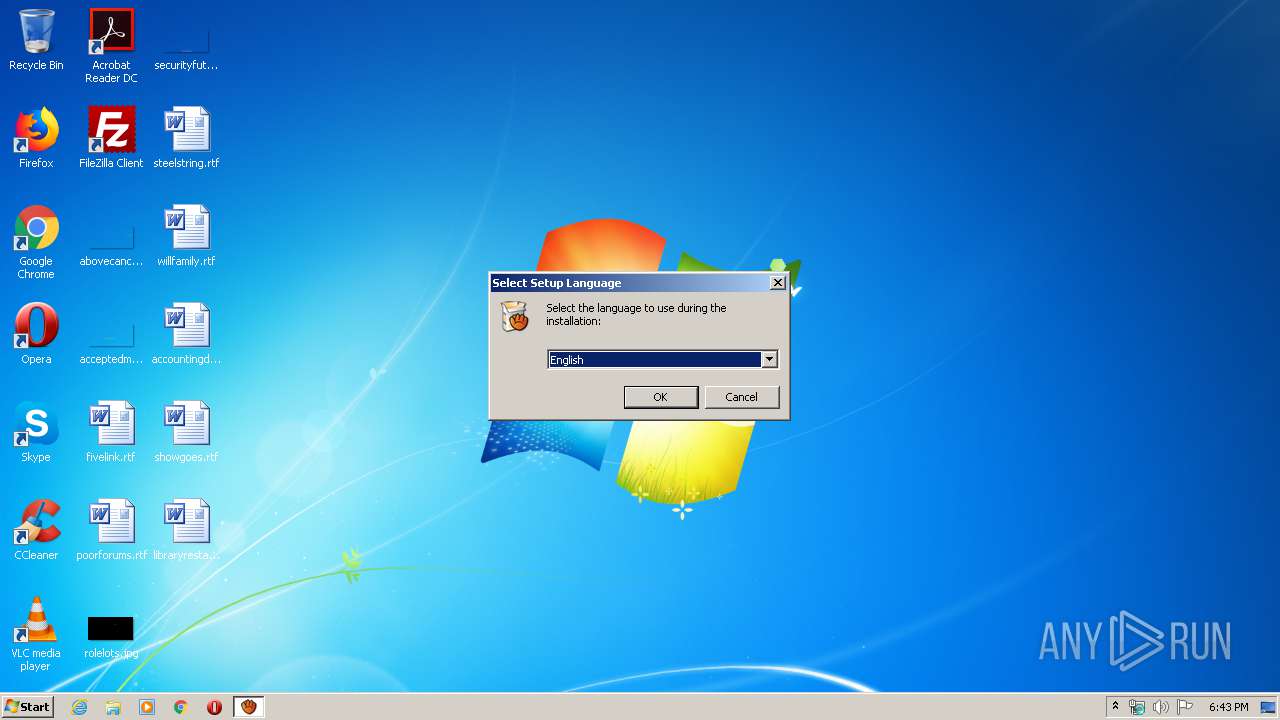
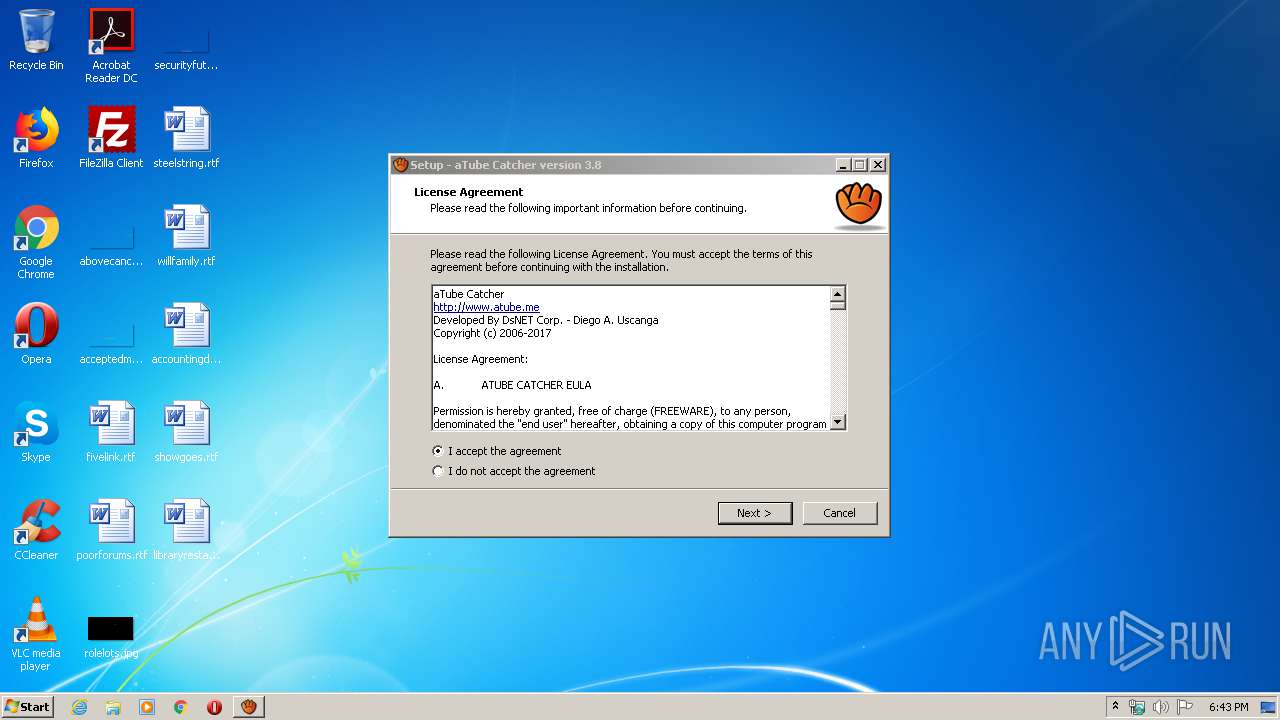
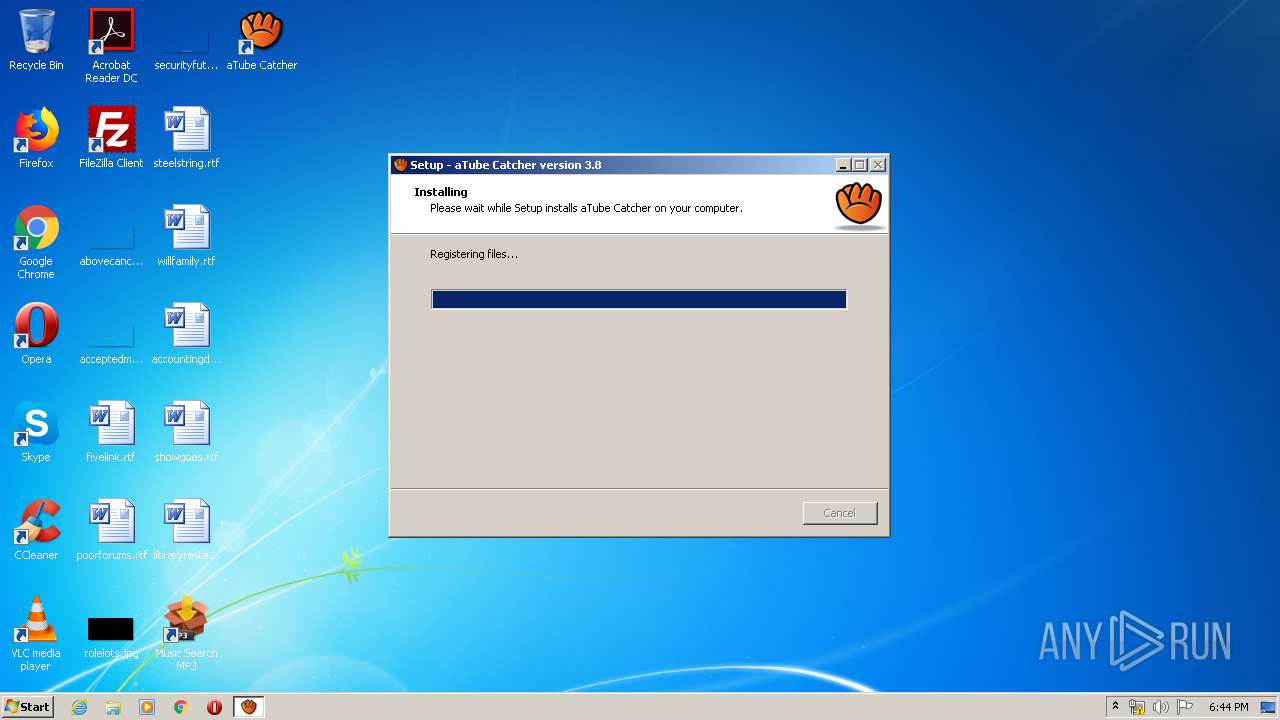
| download: | aTube_Catcher.exe |
| Full analysis: | https://app.any.run/tasks/3611b49c-ecd8-4434-92c1-14823ed76bf2 |
| Verdict: | Malicious activity |
| Analysis date: | February 03, 2020, 18:42:23 |
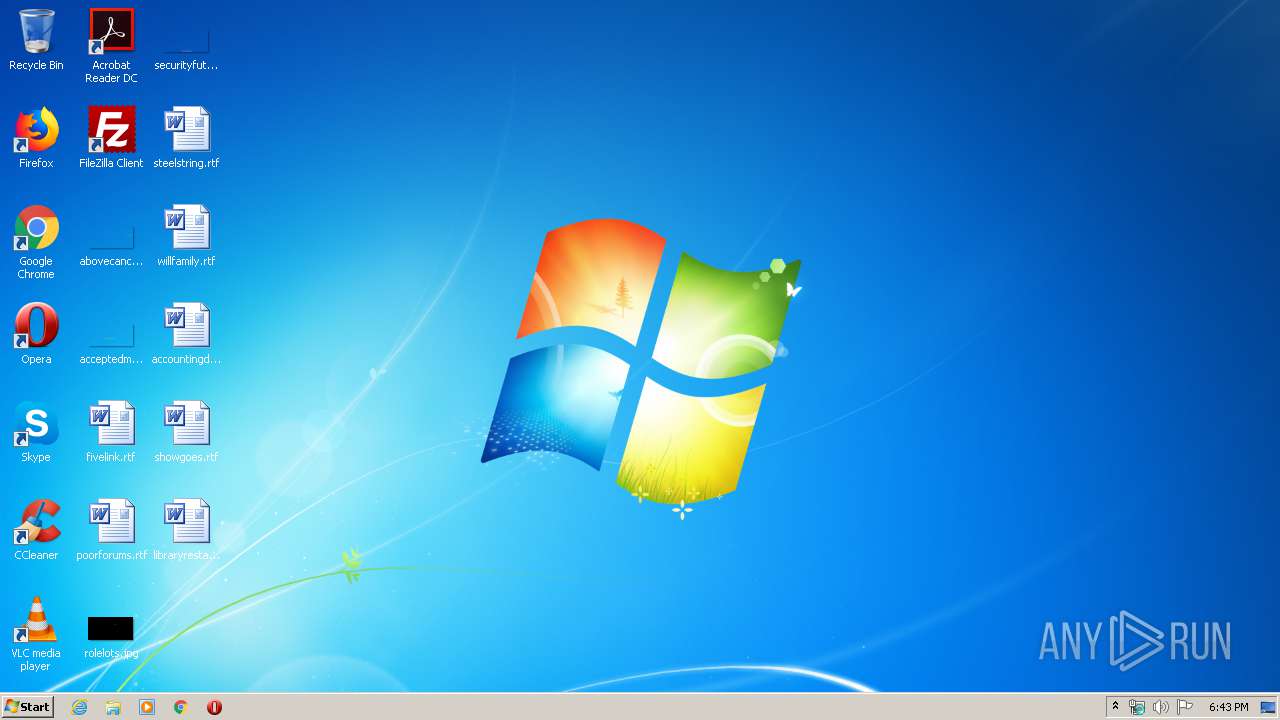
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | A25AF0D0AB1DA2D241407865C2612655 |
| SHA1: | DBA909373E536C5241C59D292E5A544A0F88F395 |
| SHA256: | DD0CA1D77C200BA62A14F863965722E1D49F02AC76EDEA35710E8677FE7E01C5 |
| SSDEEP: | 393216:sq3+yJUW24bGzK5Er0aY4sLyGddXxwnEtUX4w4GeuOwCk5+AnMYmCKARCiRpRz:xbHpqKYWWGdd6i21xO1hYuADrRz |
MALICIOUS
Loads dropped or rewritten executable
- regsvr32.exe (PID: 3252)
- regsvr32.exe (PID: 1744)
- regsvr32.exe (PID: 2412)
Registers / Runs the DLL via REGSVR32.EXE
- aTube_Catcher.tmp (PID: 3480)
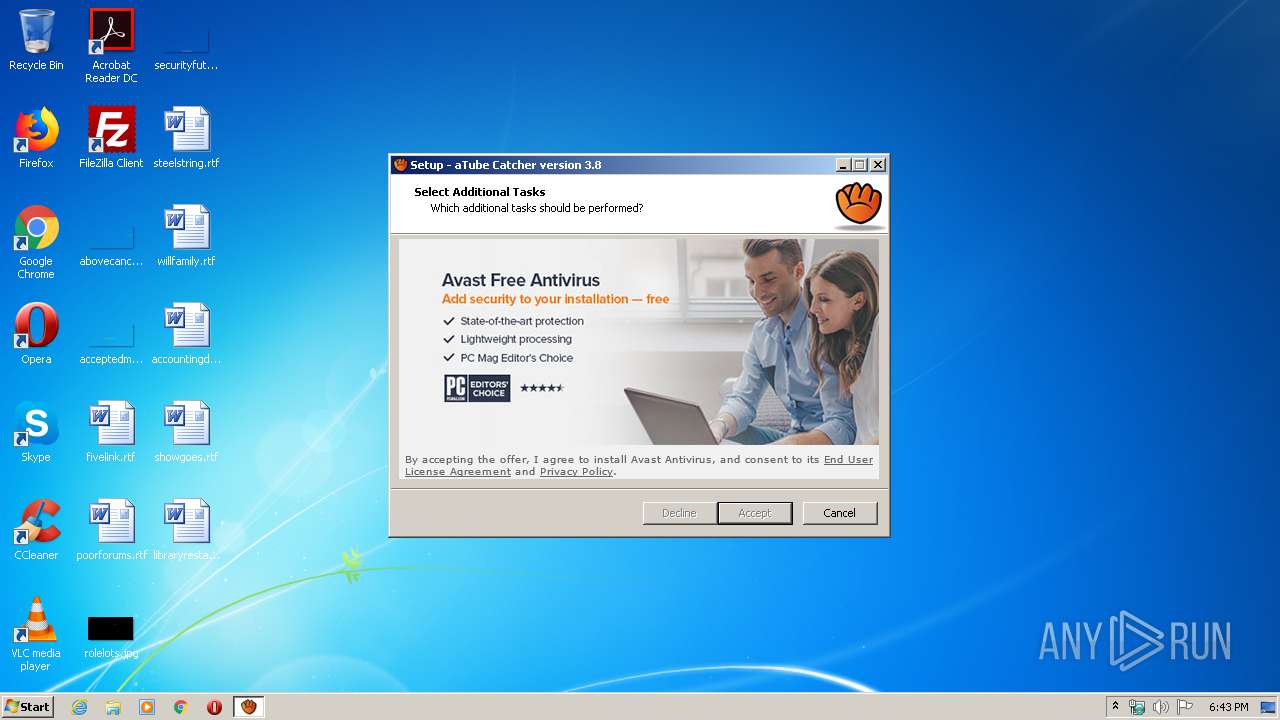
SUSPICIOUS
Executable content was dropped or overwritten
- aTube_Catcher.exe (PID: 2628)
- aTube_Catcher.exe (PID: 1724)
- aTube_Catcher.tmp (PID: 3480)
Reads Windows owner or organization settings
- aTube_Catcher.tmp (PID: 3480)
Reads the Windows organization settings
- aTube_Catcher.tmp (PID: 3480)
Reads internet explorer settings
- aTube_Catcher.tmp (PID: 3480)
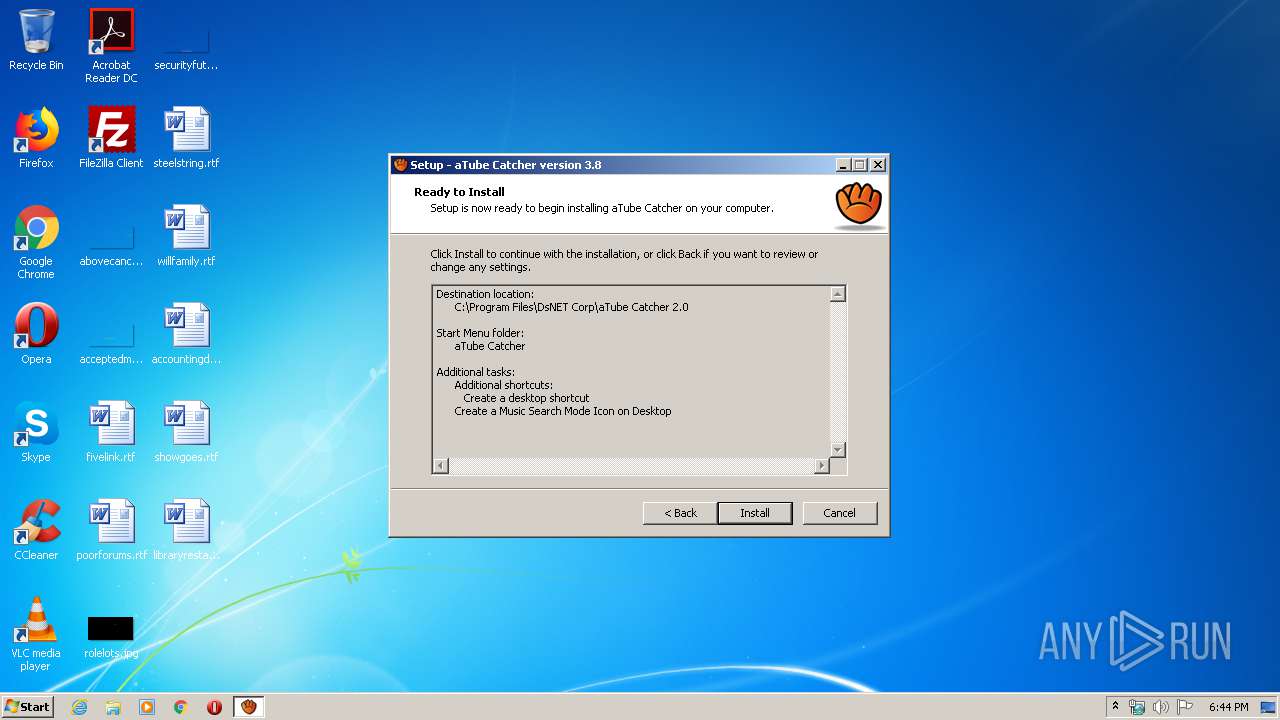
Creates files in the Windows directory
- aTube_Catcher.tmp (PID: 3480)
- regsvr32.exe (PID: 1744)
Reads Internet Cache Settings
- aTube_Catcher.tmp (PID: 3480)
Reads Environment values
- aTube_Catcher.tmp (PID: 3480)
Uses TASKKILL.EXE to kill process
- aTube_Catcher.tmp (PID: 3480)
Creates COM task schedule object
- regsvr32.exe (PID: 3252)
- regsvr32.exe (PID: 1744)
INFO
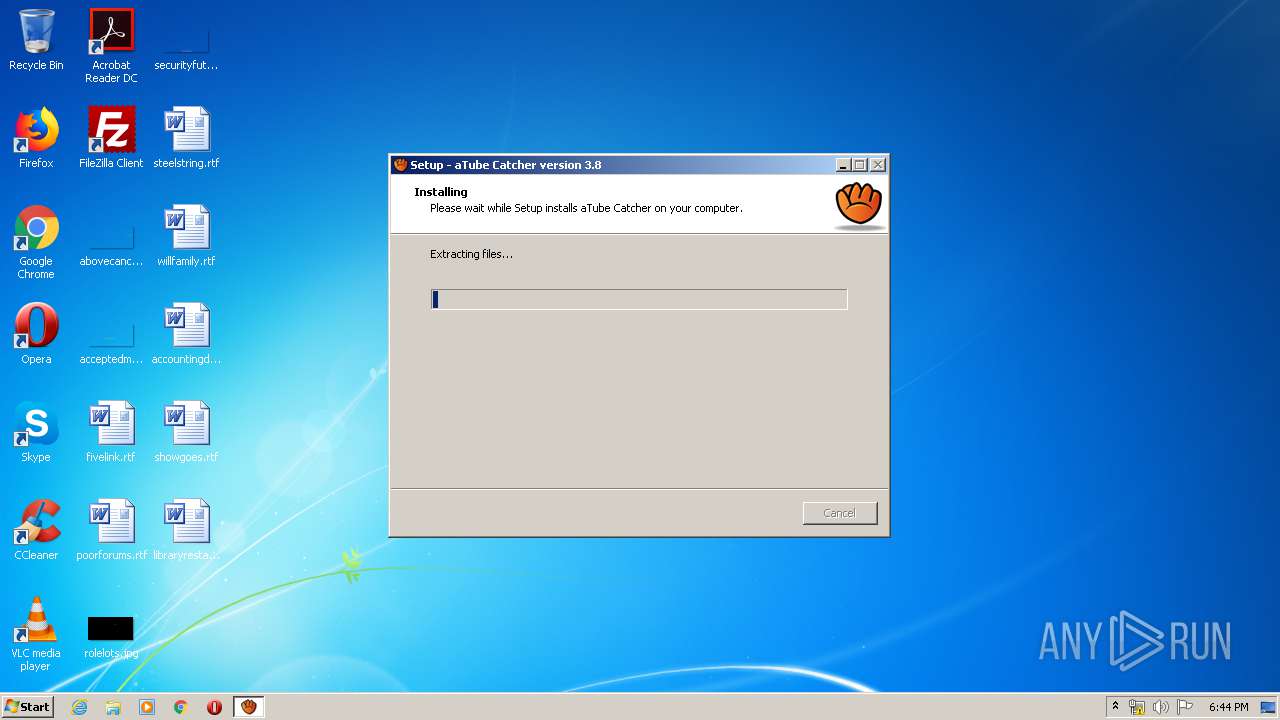
Application was dropped or rewritten from another process
- aTube_Catcher.tmp (PID: 3960)
- aTube_Catcher.tmp (PID: 3480)
Loads dropped or rewritten executable
- aTube_Catcher.tmp (PID: 3480)
Dropped object may contain Bitcoin addresses
- aTube_Catcher.tmp (PID: 3480)
Creates files in the program directory
- aTube_Catcher.tmp (PID: 3480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (42.6) |
|---|---|---|
| .exe | | | Win16/32 Executable Delphi generic (19.5) |
| .exe | | | Generic Win/DOS Executable (18.9) |
| .exe | | | DOS Executable Generic (18.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:06:14 15:27:46+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 66560 |
| InitializedDataSize: | 74240 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1181c |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
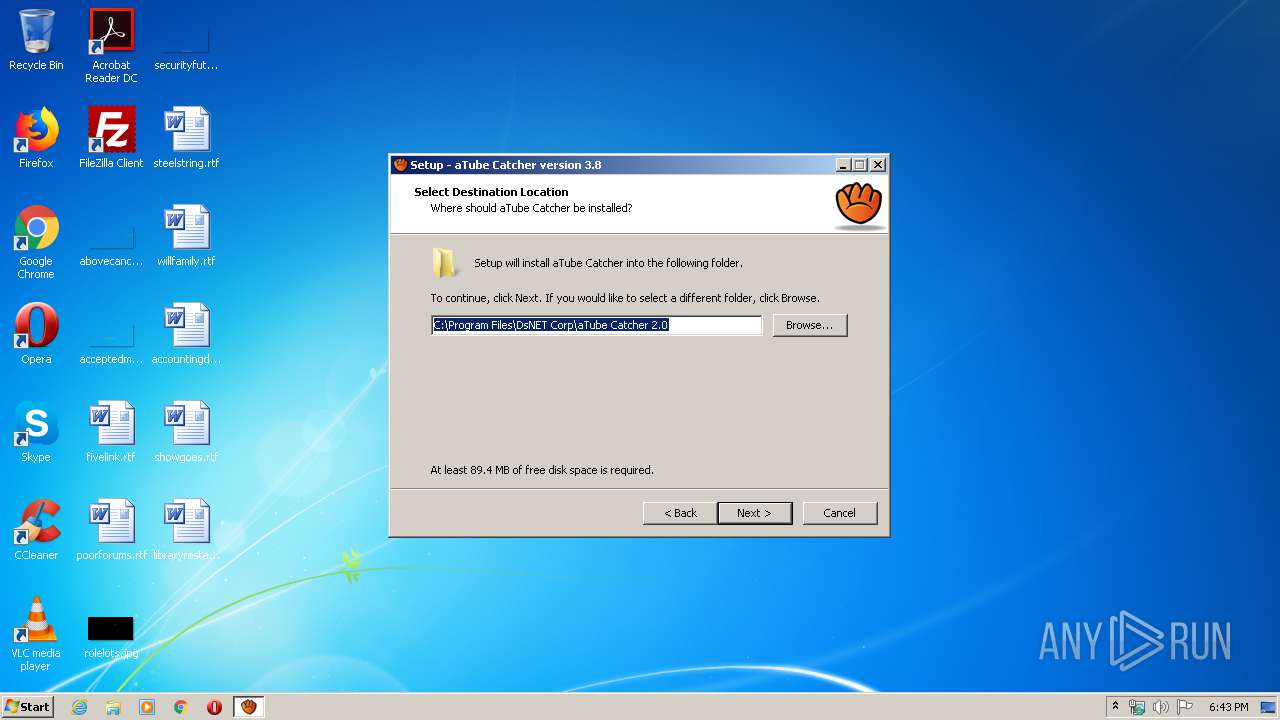
| CompanyName: | DsNET Corp |
| FileDescription: | aTube Catcher Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | aTube Catcher |
| ProductVersion: | 3.8 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Jun-2018 13:27:46 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | DsNET Corp |
| FileDescription: | aTube Catcher Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | aTube Catcher |
| ProductVersion: | 3.8 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 14-Jun-2018 13:27:46 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F25C | 0x0000F400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.37588 |
.itext | 0x00011000 | 0x00000FA4 | 0x00001000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.77877 |
.data | 0x00012000 | 0x00000C8C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.30283 |
.bss | 0x00013000 | 0x000056BC | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000E04 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.59781 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x00010178 | 0x00010200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.99009 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 3.64547 | 744 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 2.89946 | 296 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 5.26706 | 3752 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 5.42291 | 2216 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 5.88079 | 1384 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 5.45637 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 6.26108 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 5.47173 | 1128 | Latin 1 / Western European | English - United States | RT_ICON |
4091 | 2.56031 | 104 | Latin 1 / Western European | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
55
Monitored processes
10
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1724 | "C:\Users\admin\AppData\Local\Temp\aTube_Catcher.exe" | C:\Users\admin\AppData\Local\Temp\aTube_Catcher.exe | explorer.exe | ||||||||||||
User: admin Company: DsNET Corp Integrity Level: MEDIUM Description: aTube Catcher Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 1744 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\DsNET Corp\aTube Catcher 2.0\aTubeRec.dll" | C:\Windows\system32\regsvr32.exe | aTube_Catcher.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2412 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\DsNET Corp\aTube Catcher 2.0\mscomctl.OCX" | C:\Windows\system32\regsvr32.exe | — | aTube_Catcher.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2624 | "taskkill.exe" /f /im "yct.exe" | C:\Windows\system32\taskkill.exe | — | aTube_Catcher.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2628 | "C:\Users\admin\AppData\Local\Temp\aTube_Catcher.exe" /SPAWNWND=$601CA /NOTIFYWND=$90140 | C:\Users\admin\AppData\Local\Temp\aTube_Catcher.exe | aTube_Catcher.tmp | ||||||||||||
User: admin Company: DsNET Corp Integrity Level: HIGH Description: aTube Catcher Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3020 | "taskkill.exe" /f /im "eworker.exe" | C:\Windows\system32\taskkill.exe | — | aTube_Catcher.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3252 | "C:\Windows\system32\regsvr32.exe" /s "C:\Program Files\DsNET Corp\aTube Catcher 2.0\aTubeRawSocket.dll" | C:\Windows\system32\regsvr32.exe | — | aTube_Catcher.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
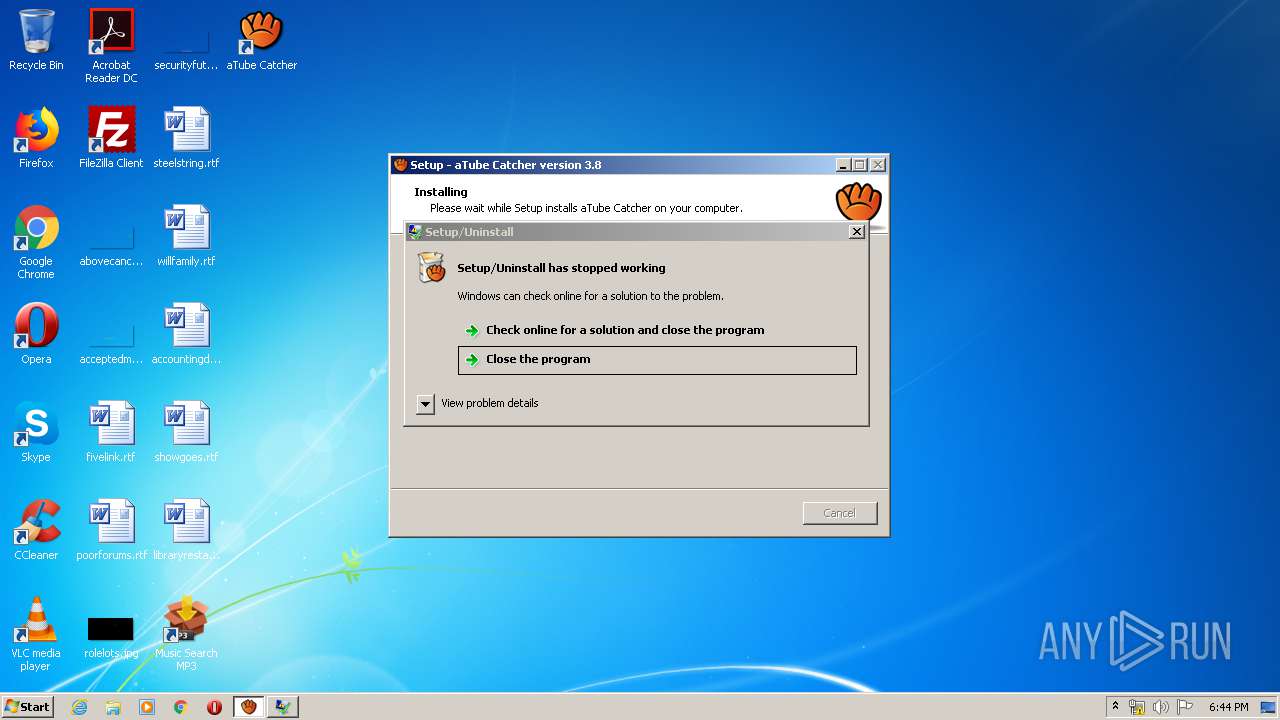
| 3480 | "C:\Users\admin\AppData\Local\Temp\is-CML2C.tmp\aTube_Catcher.tmp" /SL5="$90150,26394399,141824,C:\Users\admin\AppData\Local\Temp\aTube_Catcher.exe" /SPAWNWND=$601CA /NOTIFYWND=$90140 | C:\Users\admin\AppData\Local\Temp\is-CML2C.tmp\aTube_Catcher.tmp | aTube_Catcher.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
| 3912 | "taskkill.exe" /f /im "ffmpeg.dll" | C:\Windows\system32\taskkill.exe | — | aTube_Catcher.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3960 | "C:\Users\admin\AppData\Local\Temp\is-O1KDC.tmp\aTube_Catcher.tmp" /SL5="$90140,26394399,141824,C:\Users\admin\AppData\Local\Temp\aTube_Catcher.exe" | C:\Users\admin\AppData\Local\Temp\is-O1KDC.tmp\aTube_Catcher.tmp | — | aTube_Catcher.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
1 395
Read events
752
Write events
569
Delete events
74
Modification events
| (PID) Process: | (3480) aTube_Catcher.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 980D000016EC61D2C1DAD501 | |||
| (PID) Process: | (3480) aTube_Catcher.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 1459BD8237E1777C592B0195880E39A043B21C37D9573899EA9B323667BA9E00 | |||
| (PID) Process: | (3480) aTube_Catcher.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3480) aTube_Catcher.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3480) aTube_Catcher.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3480) aTube_Catcher.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3480) aTube_Catcher.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3480) aTube_Catcher.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A1000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3480) aTube_Catcher.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3480) aTube_Catcher.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
46
Suspicious files
5
Text files
162
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3480 | aTube_Catcher.tmp | C:\Users\admin\AppData\Local\Temp\00A6E75B.log | — | |
MD5:— | SHA256:— | |||
| 3480 | aTube_Catcher.tmp | C:\Users\admin\AppData\Local\Temp\is-6C93M.tmp\lgadfak.dll | executable | |
MD5:— | SHA256:— | |||
| 2628 | aTube_Catcher.exe | C:\Users\admin\AppData\Local\Temp\is-CML2C.tmp\aTube_Catcher.tmp | executable | |
MD5:DB1676059E94B886C062A4FE2ED6E194 | SHA256:955A7B3D2A8416084550FF6F8918C148B071613FF9391FD6BE6F9E7B5F2ACF1A | |||
| 1724 | aTube_Catcher.exe | C:\Users\admin\AppData\Local\Temp\is-O1KDC.tmp\aTube_Catcher.tmp | executable | |
MD5:DB1676059E94B886C062A4FE2ED6E194 | SHA256:955A7B3D2A8416084550FF6F8918C148B071613FF9391FD6BE6F9E7B5F2ACF1A | |||
| 3480 | aTube_Catcher.tmp | C:\Users\admin\AppData\Local\Temp\nsd1093820321722\locale\AZ.locale | text | |
MD5:90A482EF6F51D900B5F3FBBFDEEEDD8B | SHA256:254679039A064418809EB8C9187C0D6588A0F2E44C671B77F79C82806C900750 | |||
| 3480 | aTube_Catcher.tmp | C:\Users\admin\AppData\Local\Temp\nsd1093820321722\css\sdk-ui\checkbox.css | text | |
MD5:64773C6B0E3413C81AEBC46CCE8C9318 | SHA256:B09504C1BF0486D3EC46500592B178A3A6C39284672AF8815C3687CC3D29560D | |||
| 3480 | aTube_Catcher.tmp | C:\Users\admin\AppData\Local\Temp\nsd1093820321722\css\sdk-ui\images\progress-bg2.png | image | |
MD5:B582D9A67BFE77D523BA825FD0B9DAE3 | SHA256:AB4EEB3EA1EEF4E84CB61ECCB0BA0998B32108D70B3902DF3619F4D9393F74C3 | |||
| 3480 | aTube_Catcher.tmp | C:\Users\admin\AppData\Local\Temp\nsd1093820321722\css\sdk-ui\images\button-bg.png | image | |
MD5:98B1DE48DFA64DC2AA1E52FACFBEE3B0 | SHA256:2693930C474FE640E2FE8D6EF98ABE2ECD303D2392C3D8B2E006E8942BA8F534 | |||
| 3480 | aTube_Catcher.tmp | C:\Users\admin\AppData\Local\Temp\nsd1093820321722\css\sdk-ui\progress-bar.css | text | |
MD5:5335F1C12201B5F7CF5F8B4F5692E3D1 | SHA256:974CD89E64BDAA85BF36ED2A50AF266D245D781A8139F5B45D7C55A0B0841DDA | |||
| 3480 | aTube_Catcher.tmp | C:\Users\admin\AppData\Local\Temp\nsd1093820321722\locale\BG.locale | text | |
MD5:C77A1F22BC00991DB483DAAD060C21B9 | SHA256:F3CFC4B300D6AC056CD21934C9A4CEFBFDE6531905323F08BF1985F9F3867DA9 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
11
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3480 | aTube_Catcher.tmp | HEAD | 200 | 185.59.222.146:80 | http://cdneu.repositoryconecptsoftware.com/ofr/Webinebinec/Webinebinec_Links_13Oct15 | NL | — | — | malicious |
3480 | aTube_Catcher.tmp | GET | 200 | 185.59.222.146:80 | http://cdneu.repositoryconecptsoftware.com/ofr/Webinebinec/Webinebinec_Links_13Oct15 | NL | binary | 7.67 Kb | malicious |
3480 | aTube_Catcher.tmp | POST | 200 | 52.51.217.55:80 | http://rp.repositoryconecptsoftware.com/ | IE | — | — | malicious |
3480 | aTube_Catcher.tmp | POST | 200 | 52.51.217.55:80 | http://rp.repositoryconecptsoftware.com/ | IE | — | — | malicious |
3480 | aTube_Catcher.tmp | GET | 200 | 52.215.31.191:80 | http://rp.repositoryconecptsoftware.com/ | IE | — | — | malicious |
3480 | aTube_Catcher.tmp | GET | 200 | 199.115.112.67:80 | http://cdnus.repositoryconecptsoftware.com/img/Webinebinec/teal_logo.png | US | image | 978 b | malicious |
3480 | aTube_Catcher.tmp | GET | 200 | 199.115.112.67:80 | http://cdnus.repositoryconecptsoftware.com/img/Sibarasawi/bg_comp.png | US | image | 25.2 Kb | malicious |
3480 | aTube_Catcher.tmp | GET | 200 | 199.115.112.67:80 | http://cdnus.repositoryconecptsoftware.com/img/Webinebinec/teal_logo_white.png | US | image | 1.50 Kb | malicious |
3480 | aTube_Catcher.tmp | GET | 200 | 199.115.112.67:80 | http://cdnus.repositoryconecptsoftware.com/img/Sibarasawi/logo_comp.png | US | image | 12.4 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3480 | aTube_Catcher.tmp | 52.215.31.191:80 | rp.repositoryconecptsoftware.com | Amazon.com, Inc. | IE | malicious |
3480 | aTube_Catcher.tmp | 52.51.217.55:80 | rp.repositoryconecptsoftware.com | Amazon.com, Inc. | IE | malicious |
3480 | aTube_Catcher.tmp | 52.51.129.59:80 | os.repositoryconecptsoftware.com | Amazon.com, Inc. | IE | malicious |
— | — | 185.59.222.146:80 | cdneu.repositoryconecptsoftware.com | Datacamp Limited | NL | malicious |
— | — | 199.115.112.67:80 | cdnus.repositoryconecptsoftware.com | Leaseweb USA, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
rp.repositoryconecptsoftware.com |
| malicious |
os.repositoryconecptsoftware.com |
| malicious |
cdnus.repositoryconecptsoftware.com |
| malicious |
cdneu.repositoryconecptsoftware.com |
| malicious |
Threats
Process | Message |
|---|---|
regsvr32.exe | 18:44:19:969.716 [01692] : [InitDebug]: Level=0
|