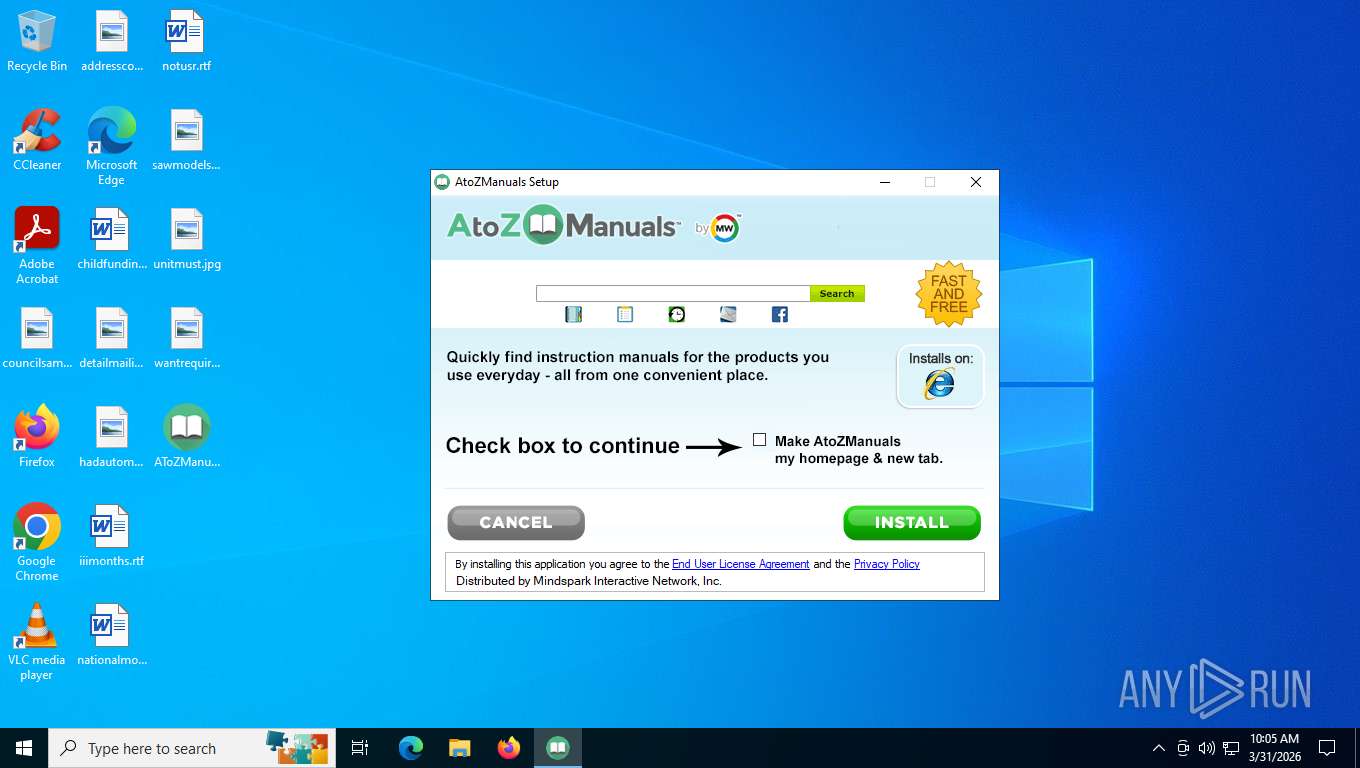
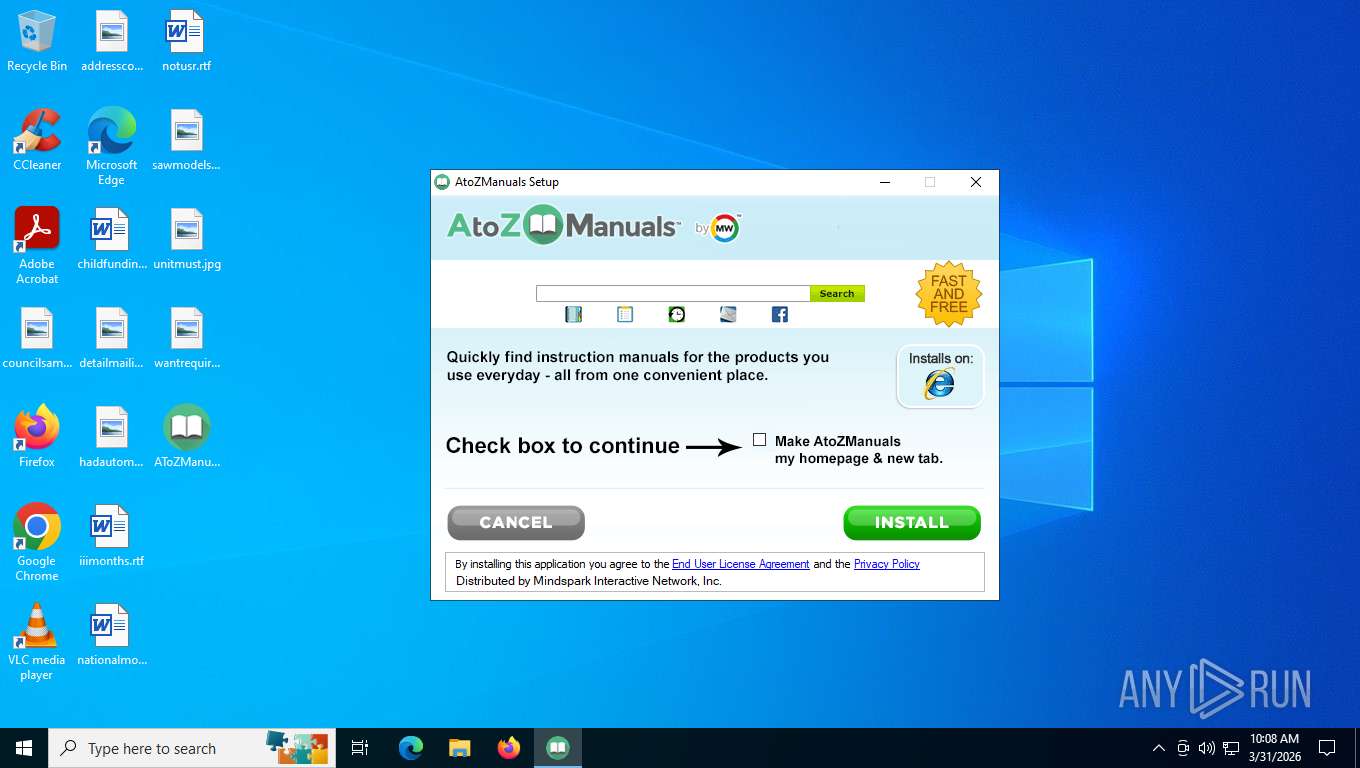
| File name: | AToZManuals.exe |
| Full analysis: | https://app.any.run/tasks/1f2cf998-3f54-4a64-a056-2bc704eb5f79 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2026, 14:05:25 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive, 5 sections |
| MD5: | 0CCD926D0EC64BCAA18EA08FBFE8AE1B |
| SHA1: | 42888D29C30E6107A6D3EA439D6B62399B26F128 |
| SHA256: | DCEBE82DFCCF0DD71FF442B1B581F5F3F040DB1AFBC19D1476CAFDA81F0C5DD4 |
| SSDEEP: | 12288:0hF8O+a8g4CZKck4LbsVDIVIitfMQeB5z4RYa5E:0cOx8g4CxkUbsVDMIitfLeB58H5E |
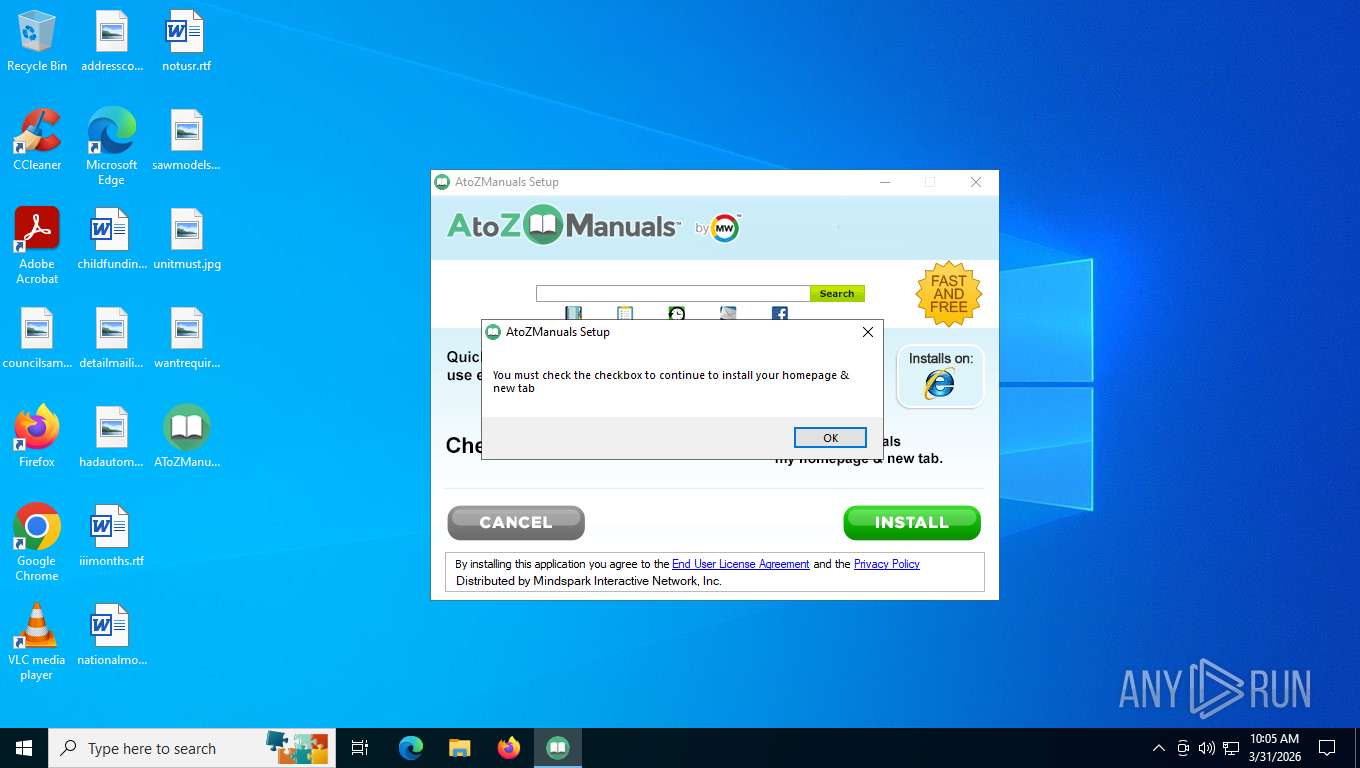
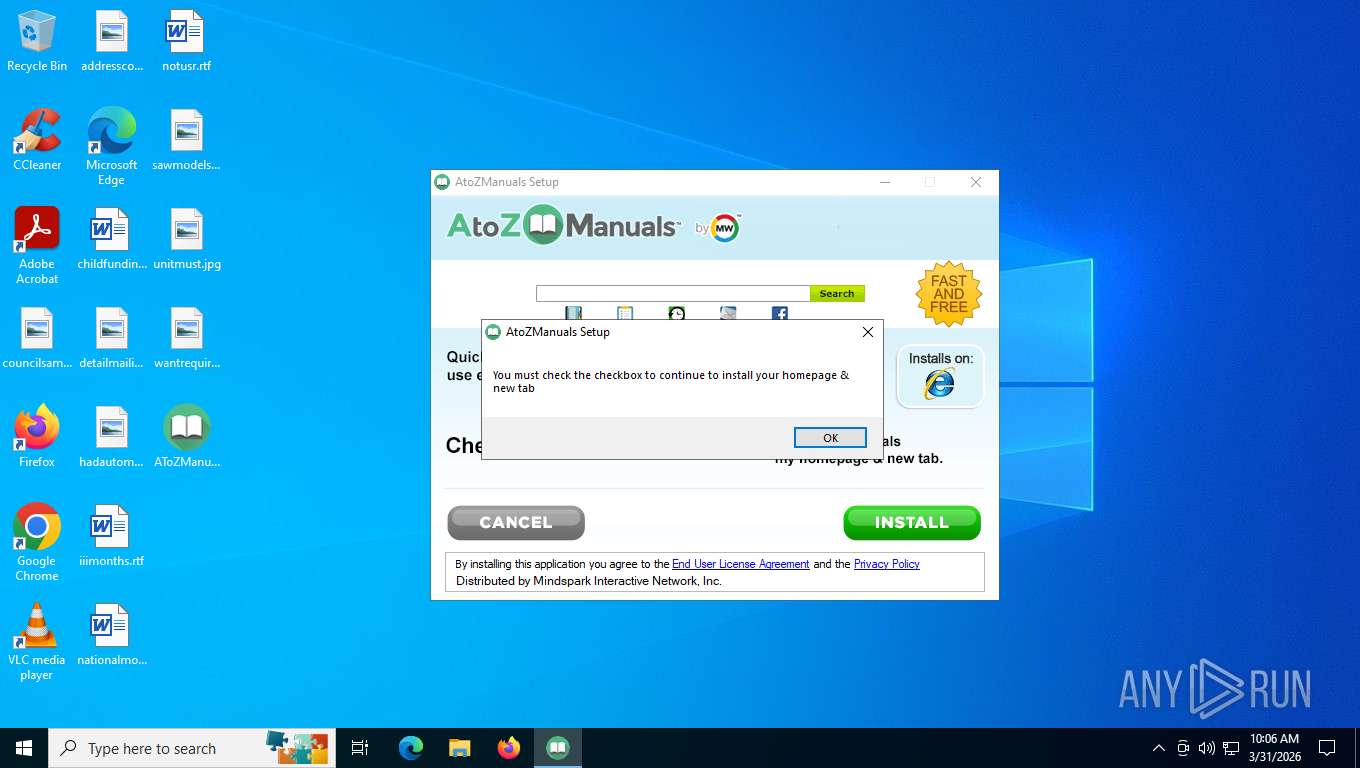
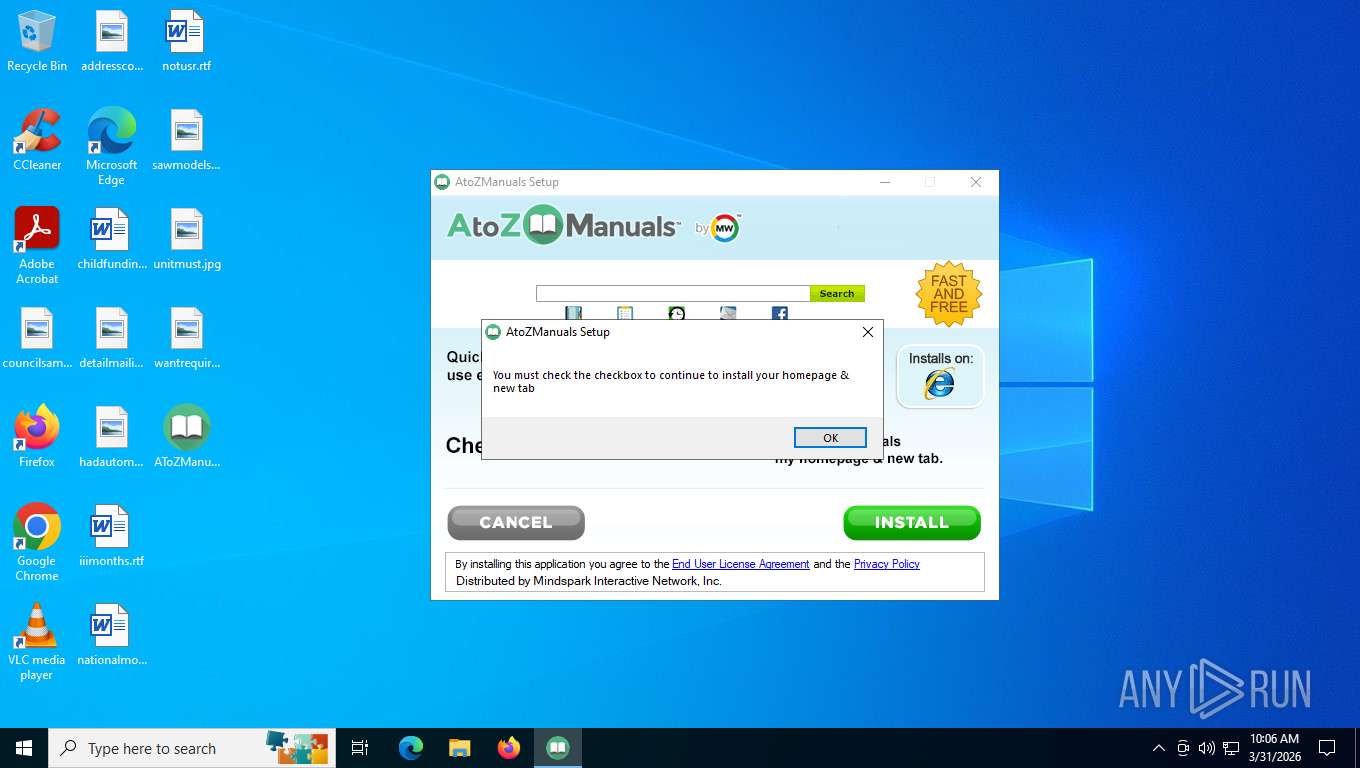
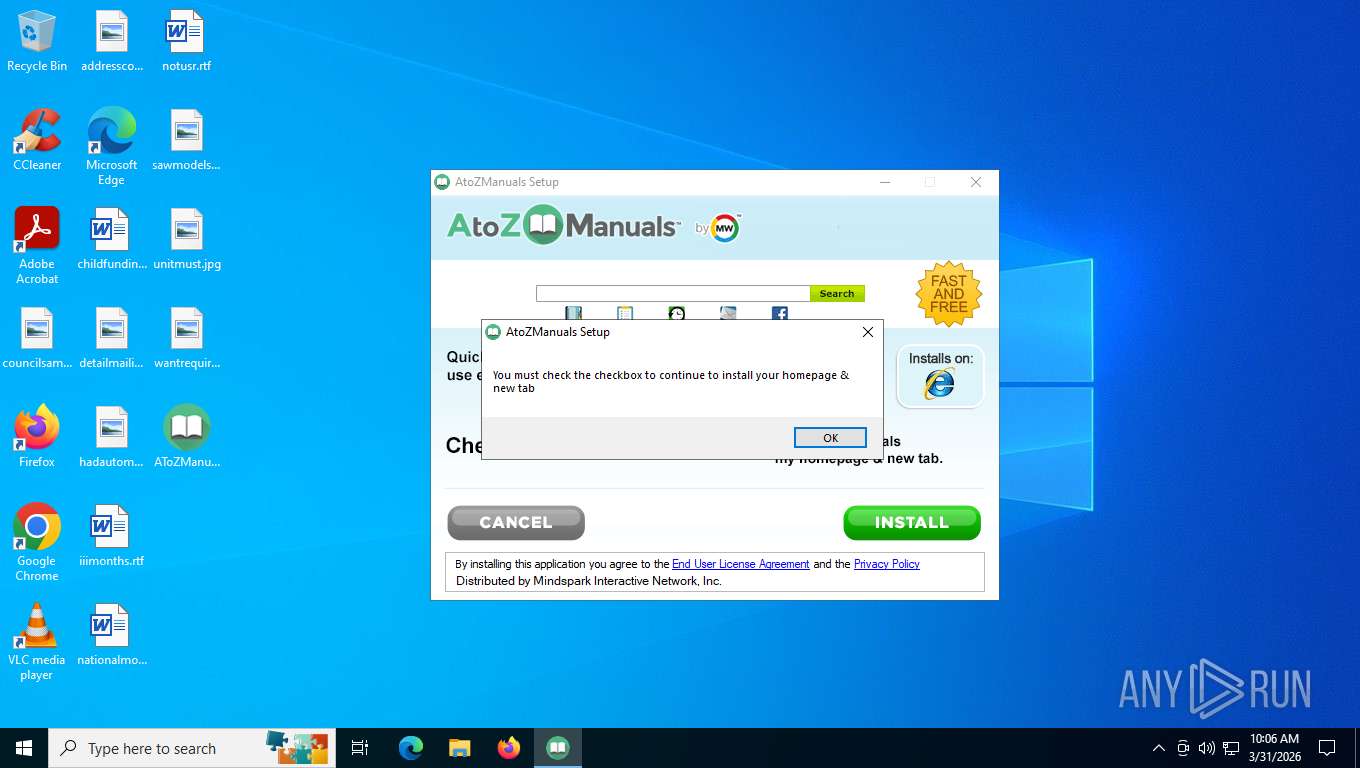
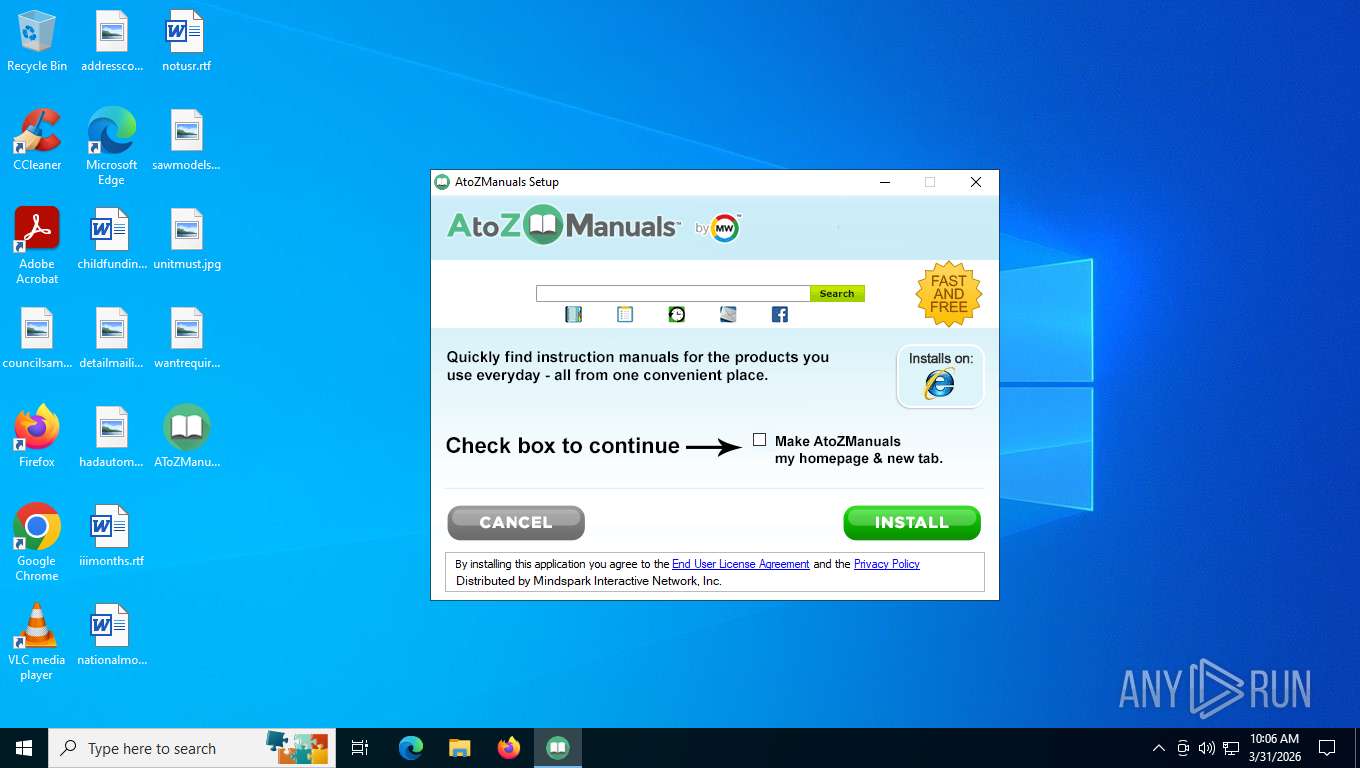
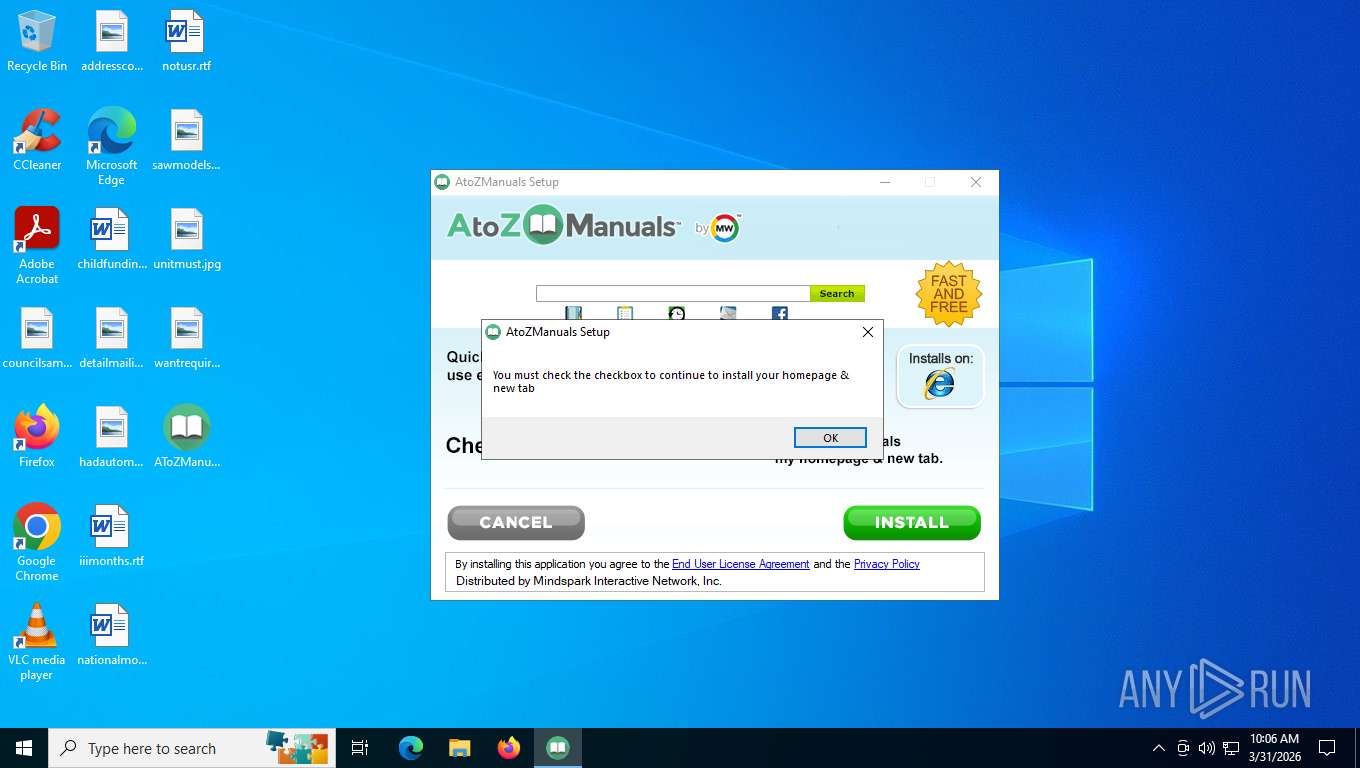
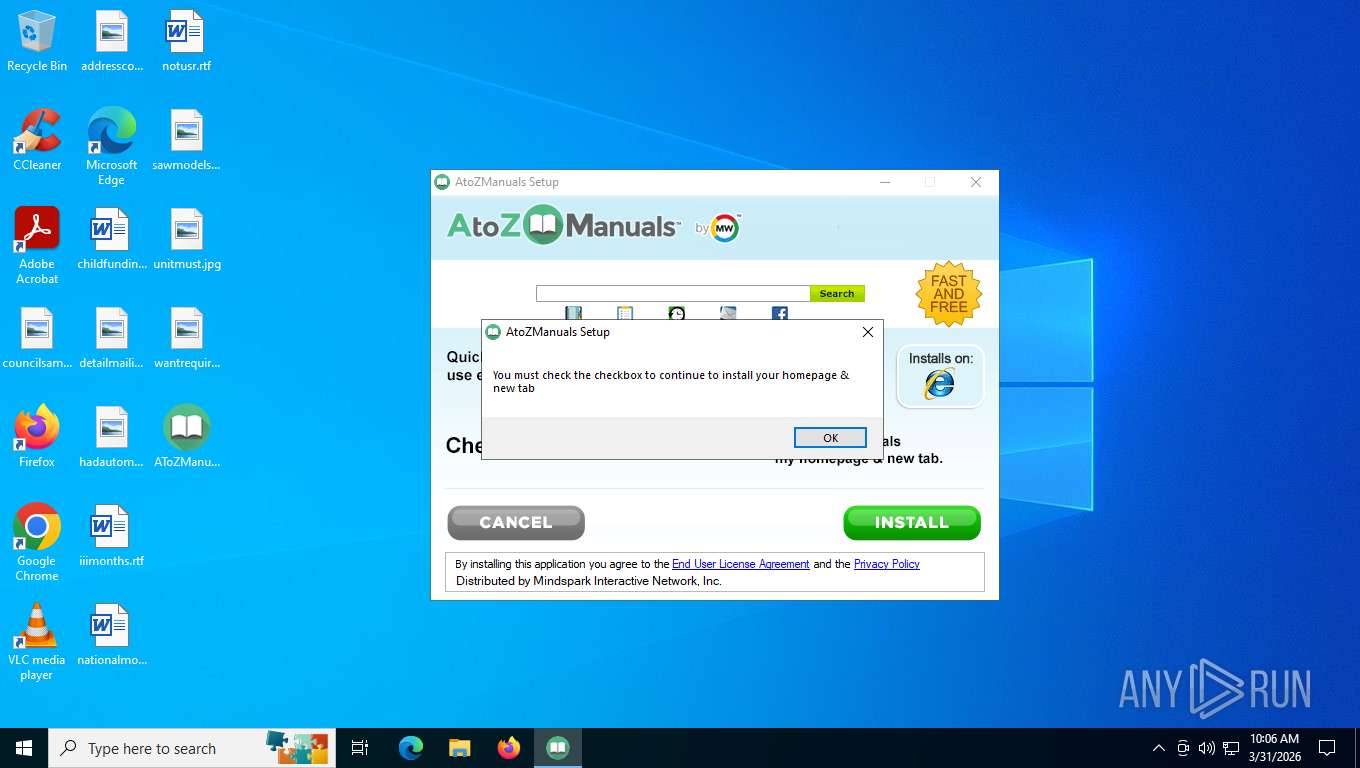
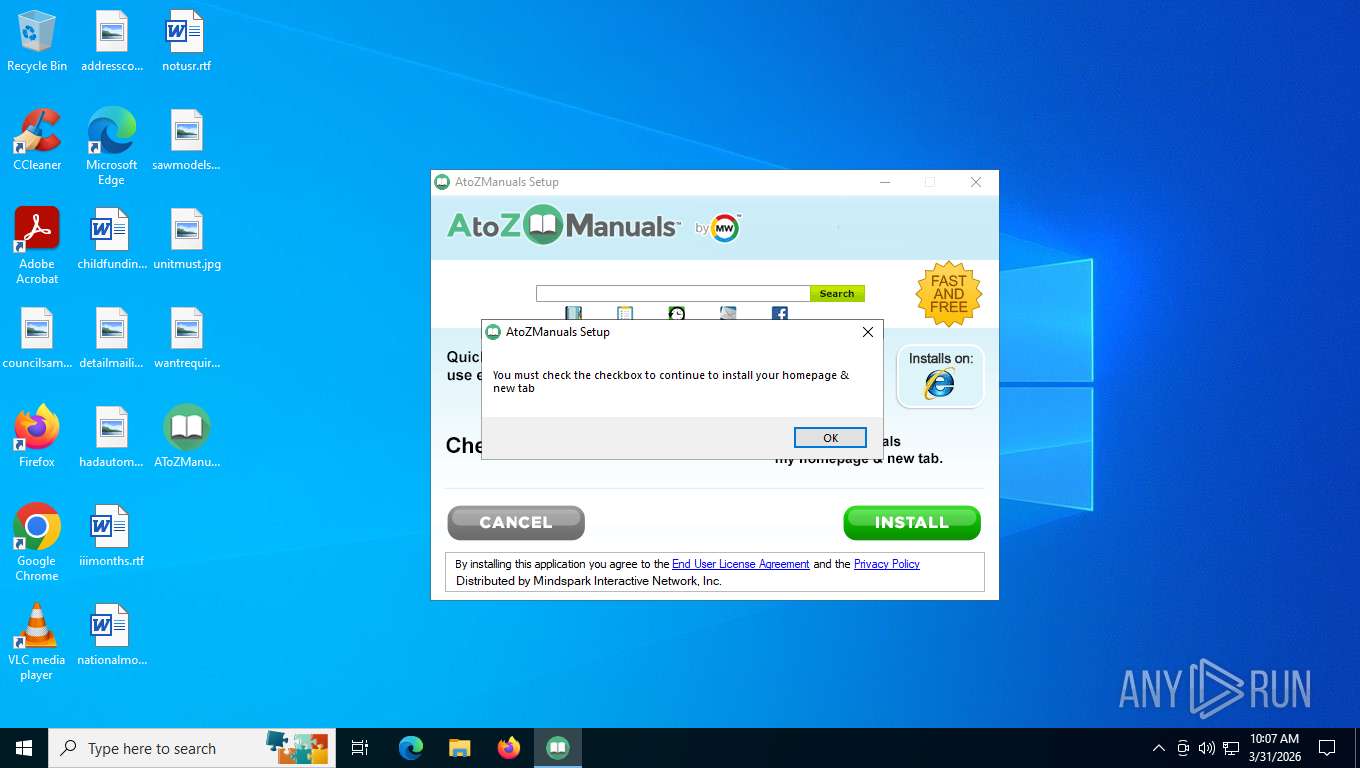
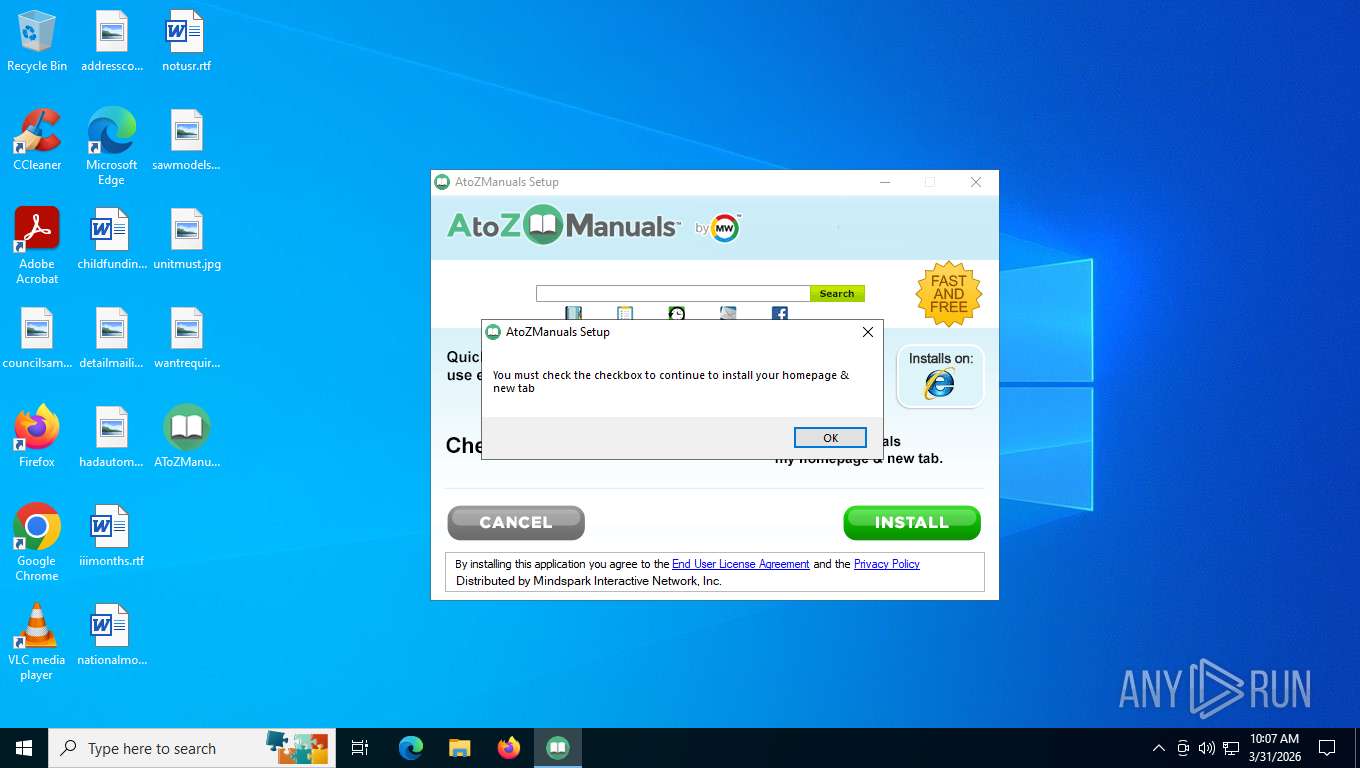
MALICIOUS
Executing a file with an untrusted certificate
- AToZManuals.exe (PID: 2828)
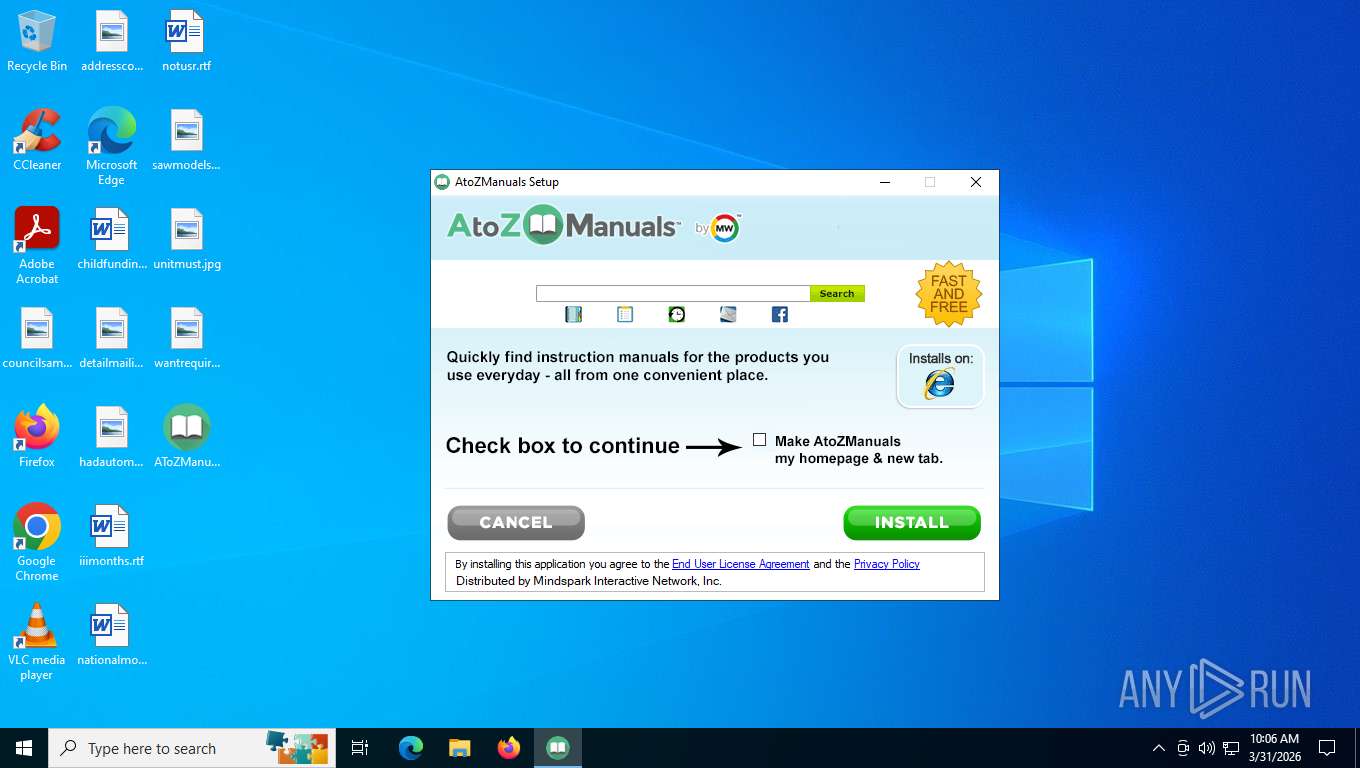
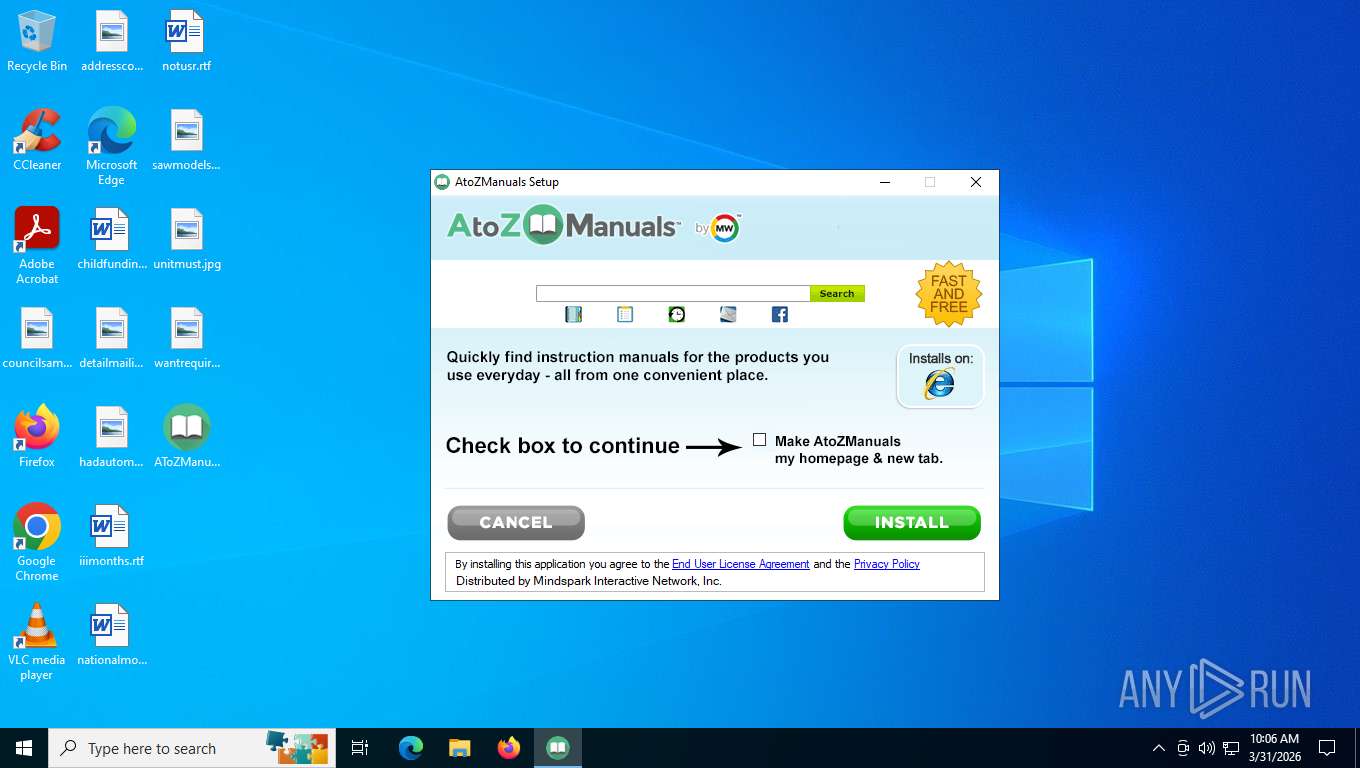
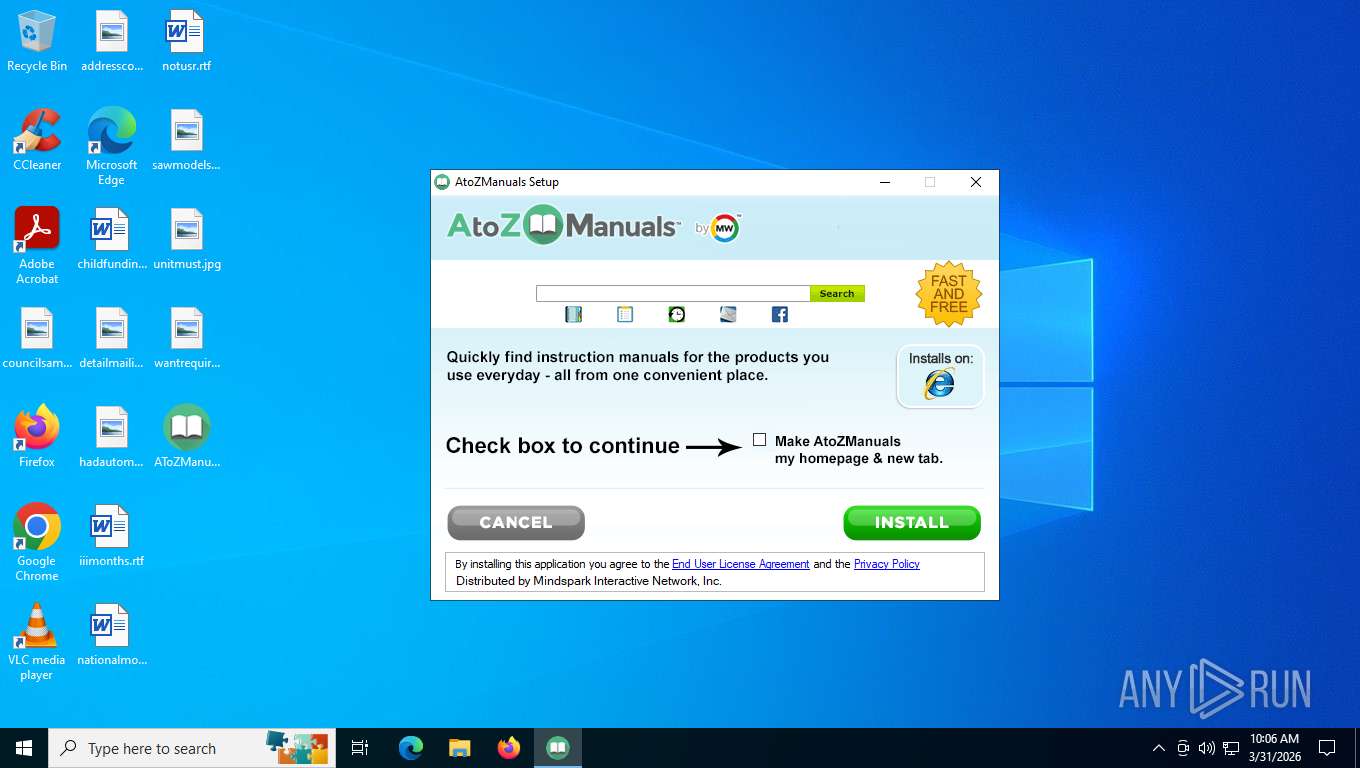
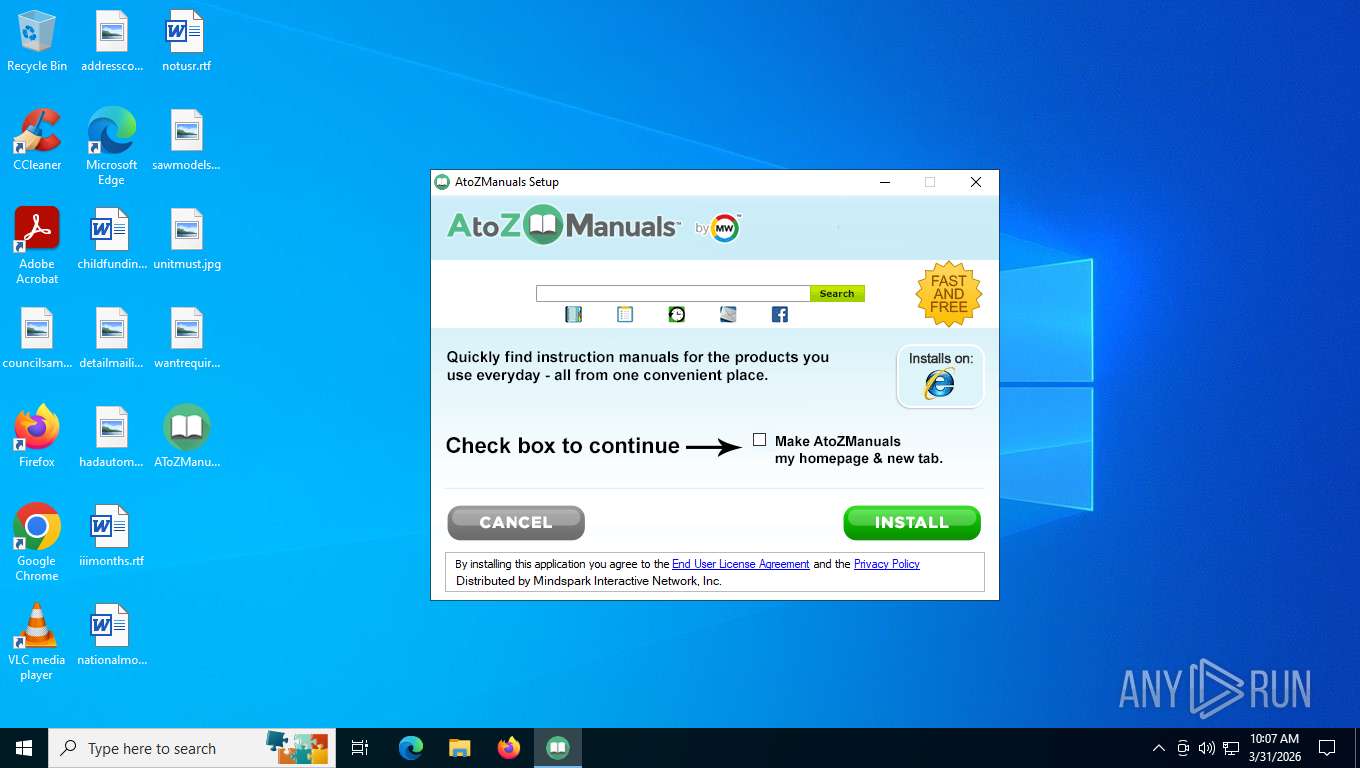
SUSPICIOUS
The process creates files with name similar to system file names
- AToZManuals.exe (PID: 2828)
Malware-specific behavior (creating "System.dll" in Temp)
- AToZManuals.exe (PID: 2828)
Executable content was dropped or overwritten
- AToZManuals.exe (PID: 2828)
INFO
The sample compiled with english language support
- AToZManuals.exe (PID: 2828)
Checks supported languages
- AToZManuals.exe (PID: 2828)
Reads the computer name
- AToZManuals.exe (PID: 2828)
Create files in a temporary directory
- AToZManuals.exe (PID: 2828)
Reads security settings of Internet Explorer
- AToZManuals.exe (PID: 2828)
Reads the machine GUID from the registry
- AToZManuals.exe (PID: 2828)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:12:25 05:01:44+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 25088 |
| InitializedDataSize: | 186368 |
| UninitializedDataSize: | 2048 |
| EntryPoint: | 0x3229 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 2.7.1.3000 |
| ProductVersionNumber: | 2.7.1.3000 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | ASCII |
| Comments: | http://www.mindspark.com |
| CompanyName: | Mindspark Interactive Network, Inc. |
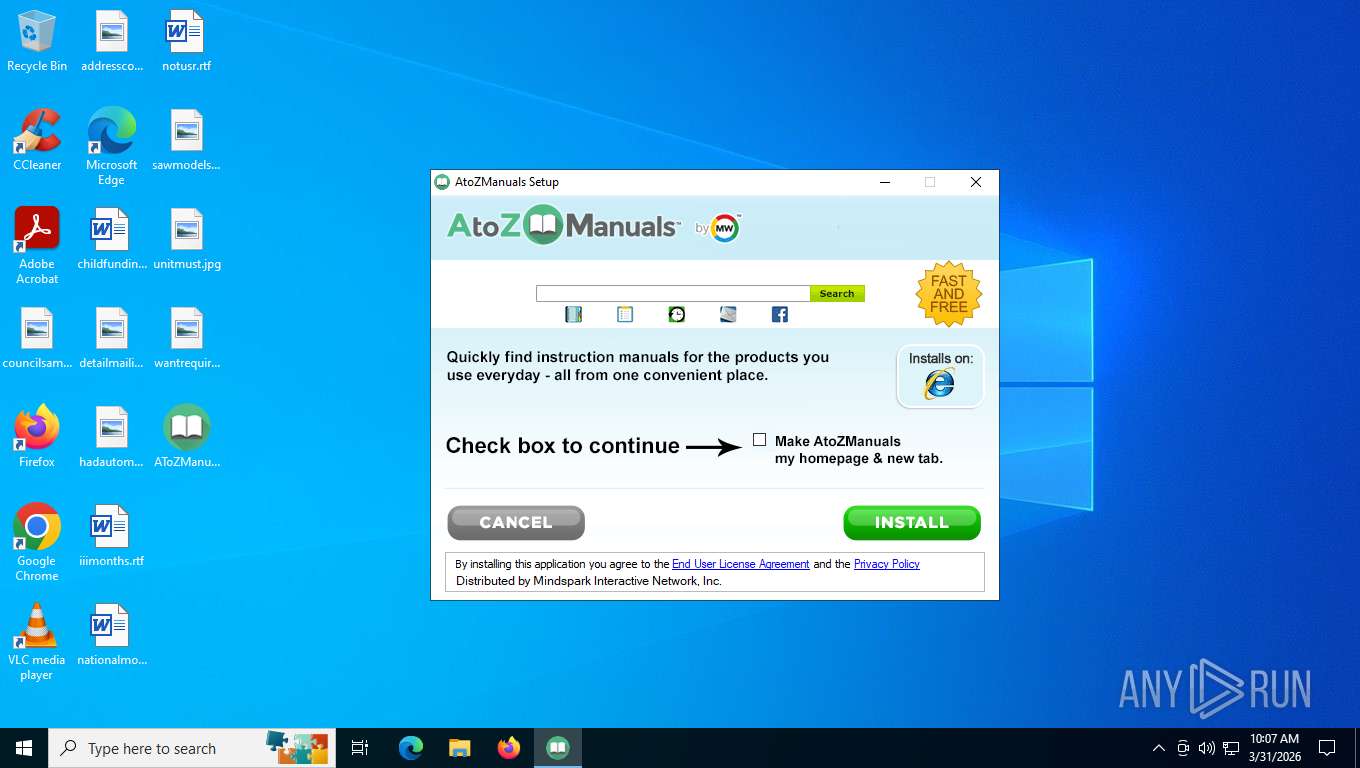
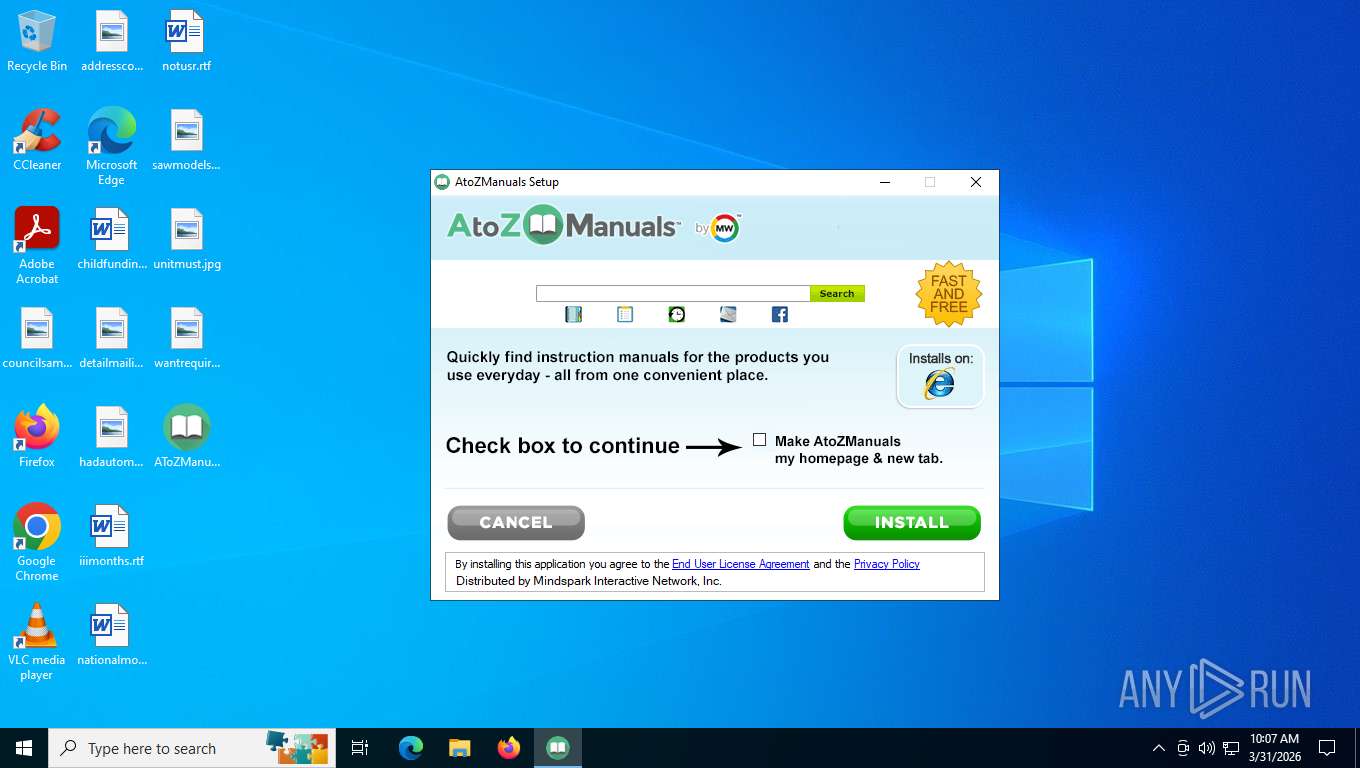
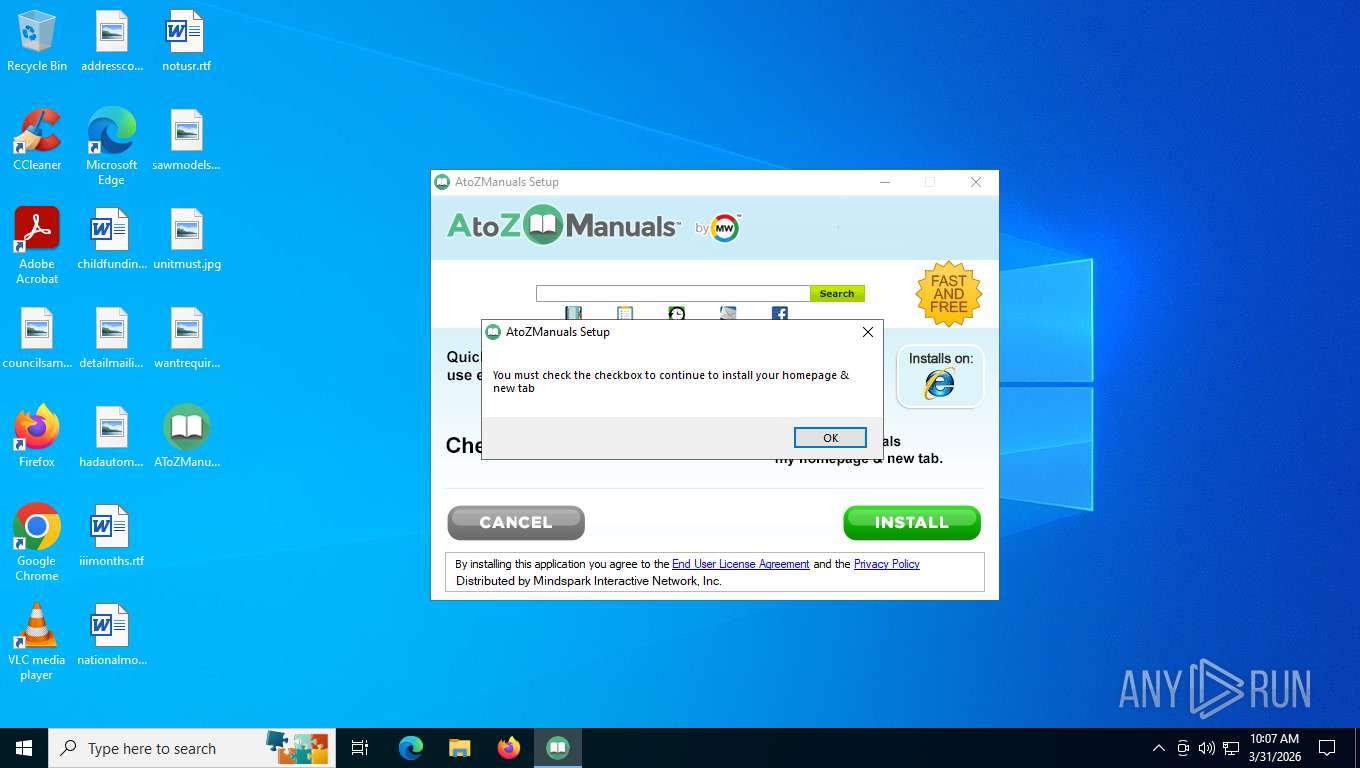
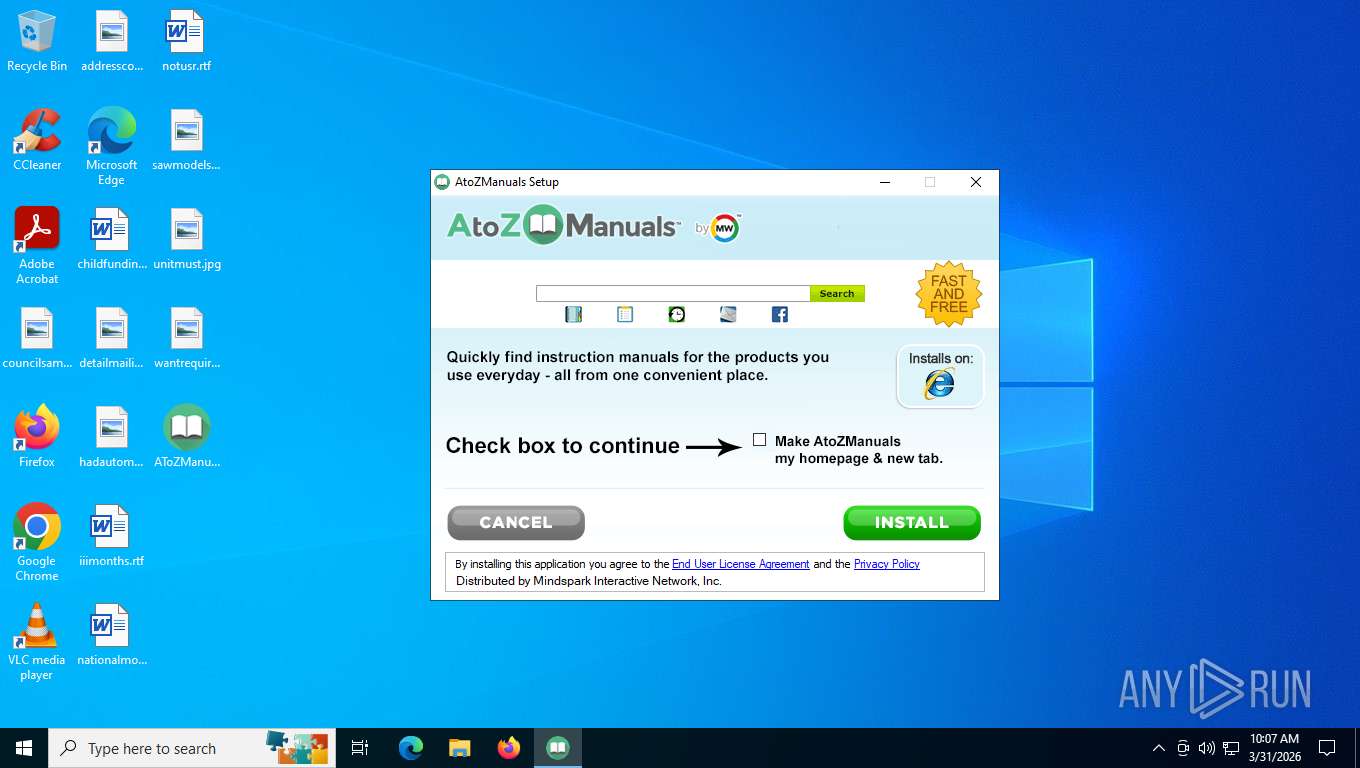
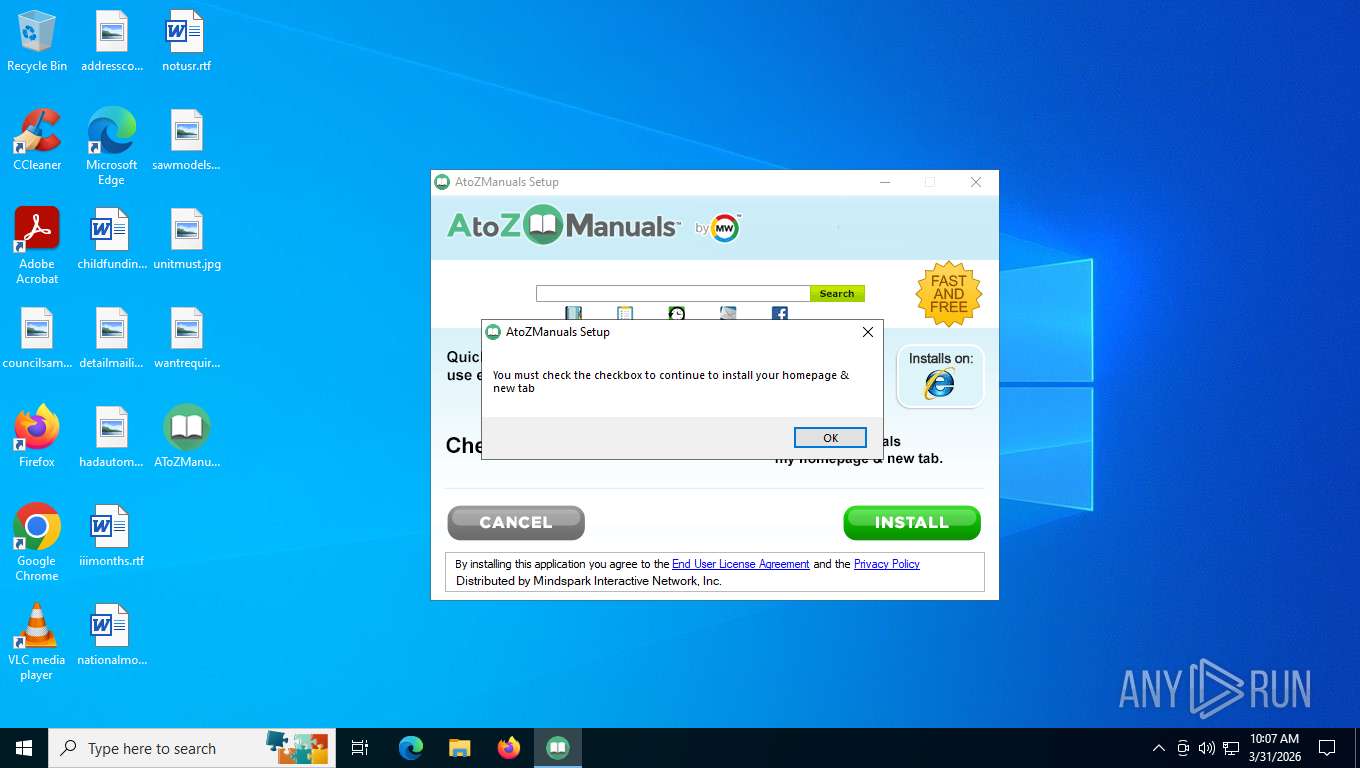
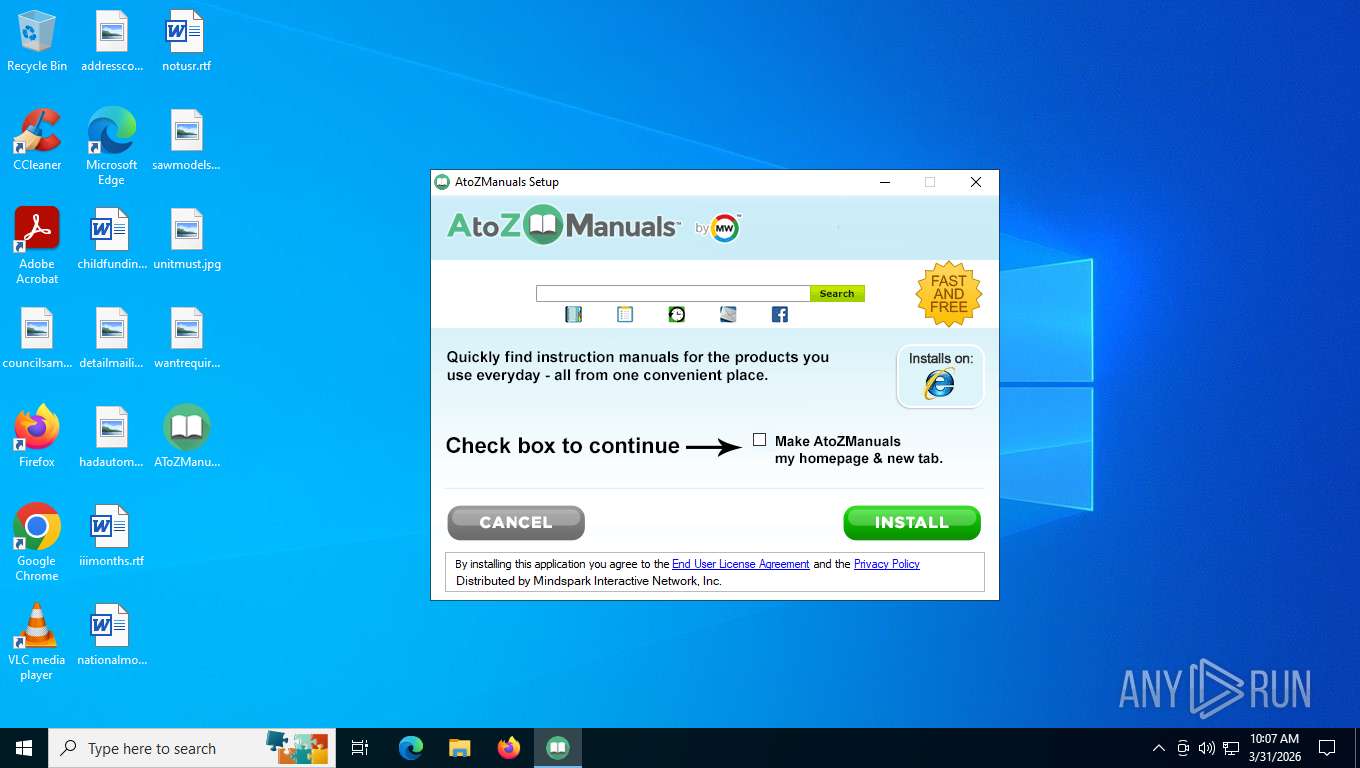
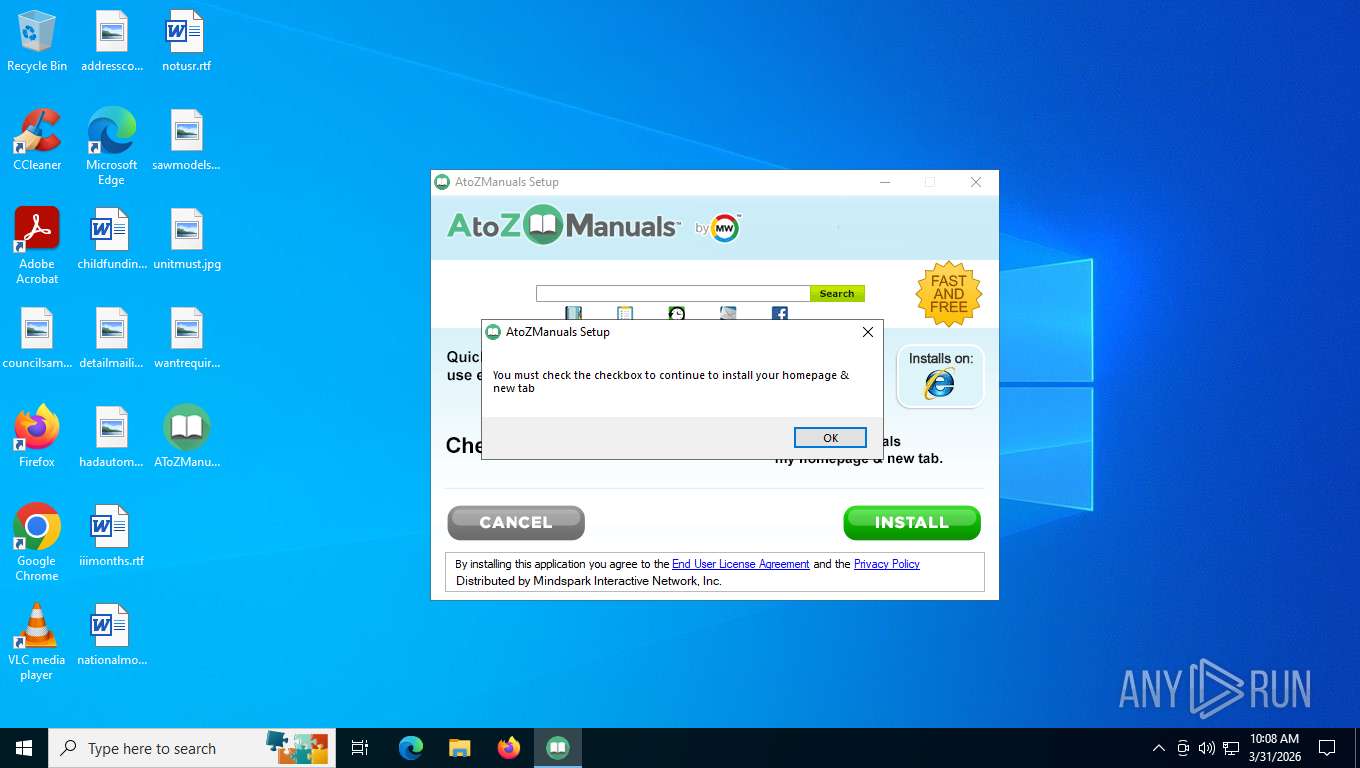
| FileDescription: | AtoZManuals Setup |
| FileVersion: | 2.7.1.3000 |
| InternalName: | AtoZManuals |
| LegalCopyright: | © 2016 Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| LegalTrademarks: | ® & ™ Mindspark Interactive Network, Inc. An IAC Company. All rights reserved. |
| ProductName: | AtoZManuals |
| ProductVersion: | 2.7.1.3000 |
Total processes
134
Monitored processes
2
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2528 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2828 | "C:\Users\admin\Desktop\AToZManuals.exe" | C:\Users\admin\Desktop\AToZManuals.exe | explorer.exe | ||||||||||||
User: admin Company: Mindspark Interactive Network, Inc. Integrity Level: MEDIUM Description: AtoZManuals Setup Version: 2.7.1.3000 Modules
| |||||||||||||||
Total events
6 839
Read events
6 838
Write events
1
Delete events
0
Modification events
| (PID) Process: | (2528) slui.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\3d\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\sppcomapi.dll,-3200 |
Value: Software Licensing | |||
Executable files
2
Suspicious files
0
Text files
3
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2828 | AToZManuals.exe | C:\Users\admin\AppData\Local\Temp\nscDA9.tmp\AtoZManauls_msi_bg-copy_1501852810543_1528830768010.bmp | image | |
MD5:C216326B5FA3F989FB182D238555315D | SHA256:C75B31EEBA2DD14F61CE8D80E52115E16092A2F121CE667326181FE1B5833B7D | |||
| 2828 | AToZManuals.exe | C:\Users\admin\AppData\Local\Temp\nscDA9.tmp\Install_ENG_1436200260055.bmp | image | |
MD5:7078777F775A58435028C19515955085 | SHA256:DF2BD2E2781DAA4D3270FF3BAC2CFAE49FCB42E2A331D10F4F0CBDA2E3B1DDDC | |||
| 2828 | AToZManuals.exe | C:\Users\admin\AppData\Local\Temp\nscDA9.tmp\english_cancel_mip_1482425559536.bmp | image | |
MD5:12845D5CC068D0A6942889845974AA16 | SHA256:342CFBBA0DC6B853801FC14B6FE529A242A19A8031956BC9569643F07BB004EC | |||
| 2828 | AToZManuals.exe | C:\Users\admin\AppData\Local\Temp\nscDA9.tmp\nsDialogs.dll | executable | |
MD5:B9A5A272154FC0DD652EF9C59C5D63A0 | SHA256:D84D810B8F8819F4A34D5E033B72951EADDA1BBB5ED0B8C76874B6C25001CAA9 | |||
| 2828 | AToZManuals.exe | C:\Users\admin\AppData\Local\Temp\nscDA9.tmp\System.dll | executable | |
MD5:7399323923E3946FE9140132AC388132 | SHA256:5A1C20A3E2E2EB182976977669F2C5D9F3104477E98F74D69D2434E79B92FDC3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
47
TCP/UDP connections
42
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2648 | SIHClient.exe | GET | 304 | 135.233.95.144:443 | https://slscr.update.microsoft.com/SLS/%7B522D76A4-93E1-47F8-B8CE-07C937AD1A1E%7D/x64/10.0.19045.4046/0?CH=686&L=en-US&P=&PT=0x30&WUA=10.0.19041.3996&MK=DELL&MD=DELL | US | — | — | whitelisted |
5484 | svchost.exe | GET | 200 | 23.216.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.37:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
5484 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
5276 | MoUsoCoreWorker.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | US | binary | 814 b | whitelisted |
2648 | SIHClient.exe | GET | 200 | 135.233.95.135:443 | https://fe3cr.delivery.mp.microsoft.com/clientwebservice/ping | US | — | — | whitelisted |
2828 | AToZManuals.exe | GET | — | 34.120.232.229:80 | http://anx.mindspark.com/anx.gif?anxa=CAPDownloadProcess&anxe=Error&errorCode=-16&errorType=nsisError&errorDetails=&platform=vicinio&anxv=2.7.1.3000&anxd=2018-06-12&coid=&refPartner=^CG7^mni000^TTAB02&refSub=&anxl=en-US&anxr=-2037364968&refCobrand=CG7&refCampaign=mni000&refTrack=TTAB02&refCountry= | US | — | — | unknown |
2648 | SIHClient.exe | GET | 200 | 135.233.95.144:443 | https://slscr.update.microsoft.com/sls/ping | US | — | — | whitelisted |
— | — | POST | 500 | 128.24.231.64:443 | https://activation-v2.sls.microsoft.com/SLActivateProduct/SLActivateProduct.asmx?configextension=Retail | US | xml | 512 b | whitelisted |
2828 | AToZManuals.exe | GET | — | 34.120.232.229:80 | http://anx.mindspark.com/anx.gif?anxa=CAPDownloadProcess&anxe=Error&errorCode=-8&errorType=nsisError&errorDetails=AToZManuals%2Eexe&platform=vicinio&anxv=2.7.1.3000&anxd=2018-06-12&coid=302b8d7ff8874355b406a3784ba00e90&refPartner=^CG7^mni000^TTAB02&refSub=&anxl=en-US&anxr=-2020175123&refCobrand=CG7&refCampaign=mni000&refTrack=TTAB02&refCountry= | US | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 48.192.1.64:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 2.16.204.149:443 | www.bing.com | AKAMAI-ASN1 | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
5484 | svchost.exe | 23.216.77.37:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5276 | MoUsoCoreWorker.exe | 23.216.77.37:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5484 | svchost.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
5276 | MoUsoCoreWorker.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
activation-v2.sls.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
anx.mindspark.com |
| whitelisted |
dp.tb.ask.com |
| whitelisted |
self.events.data.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |