| File name: | Windows_Loader_2.2.2_Downloadly.ir.exe |
| Full analysis: | https://app.any.run/tasks/7a6dd5cd-e1f6-48b0-a685-66a1a12c877e |
| Verdict: | Malicious activity |
| Analysis date: | February 15, 2025, 00:05:22 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive, 4 sections |
| MD5: | CEB87D371708691577A65CACCB6C6D53 |
| SHA1: | 135336BF47BD3E3AAC86D082CC1DBBBFD2C571CD |
| SHA256: | DCEA535498FEF0805A44ABF93F64C0F74DB194FAFA5A2923BEB01D186DA7AF7D |
| SSDEEP: | 49152:AxukU/vlsJBajCeE07I0HDU+T/sWRf0T4JnLoDO:AxcrD7ILcl0EtX |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads security settings of Internet Explorer
- Windows_Loader_2.2.2_Downloadly.ir.exe (PID: 6364)
There is functionality for taking screenshot (YARA)
- Windows_Loader_2.2.2_Downloadly.ir.exe (PID: 6364)
Reads Internet Explorer settings
- Windows_Loader_2.2.2_Downloadly.ir.exe (PID: 6364)
Reads Microsoft Outlook installation path
- Windows_Loader_2.2.2_Downloadly.ir.exe (PID: 6364)
INFO
Reads the computer name
- Windows_Loader_2.2.2_Downloadly.ir.exe (PID: 6364)
Checks supported languages
- Windows_Loader_2.2.2_Downloadly.ir.exe (PID: 6364)
Checks proxy server information
- Windows_Loader_2.2.2_Downloadly.ir.exe (PID: 6364)
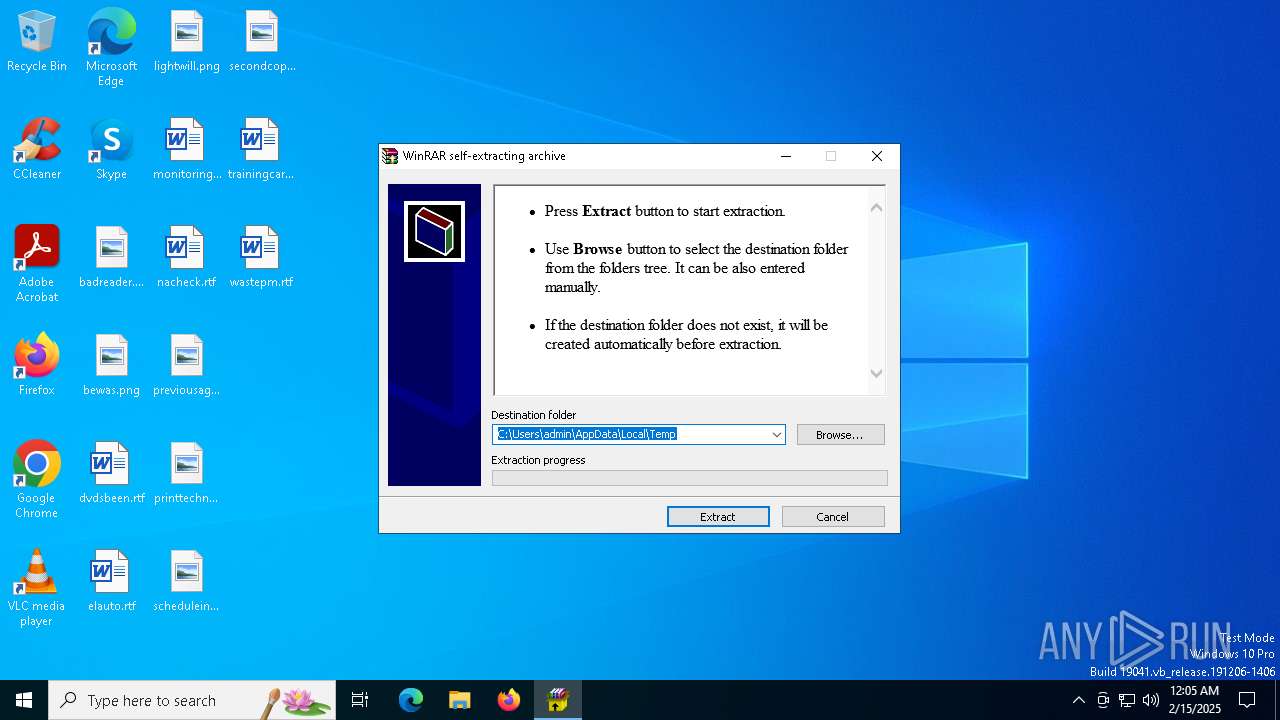
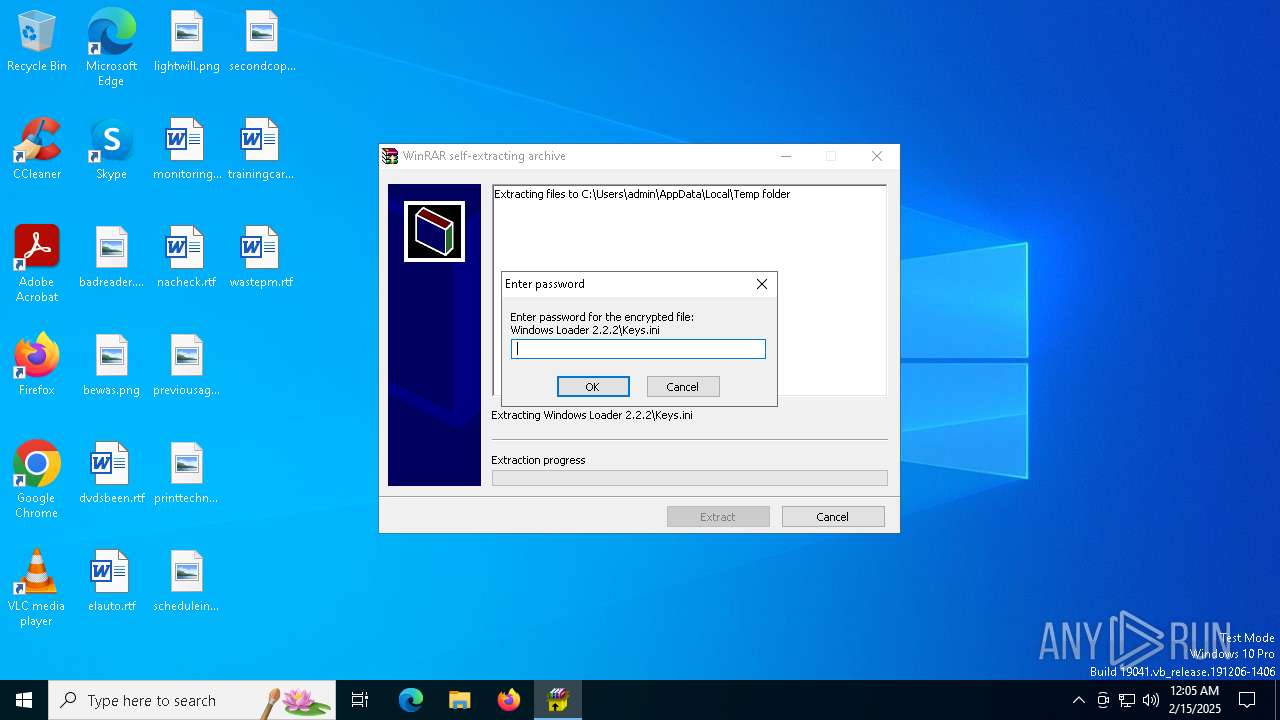
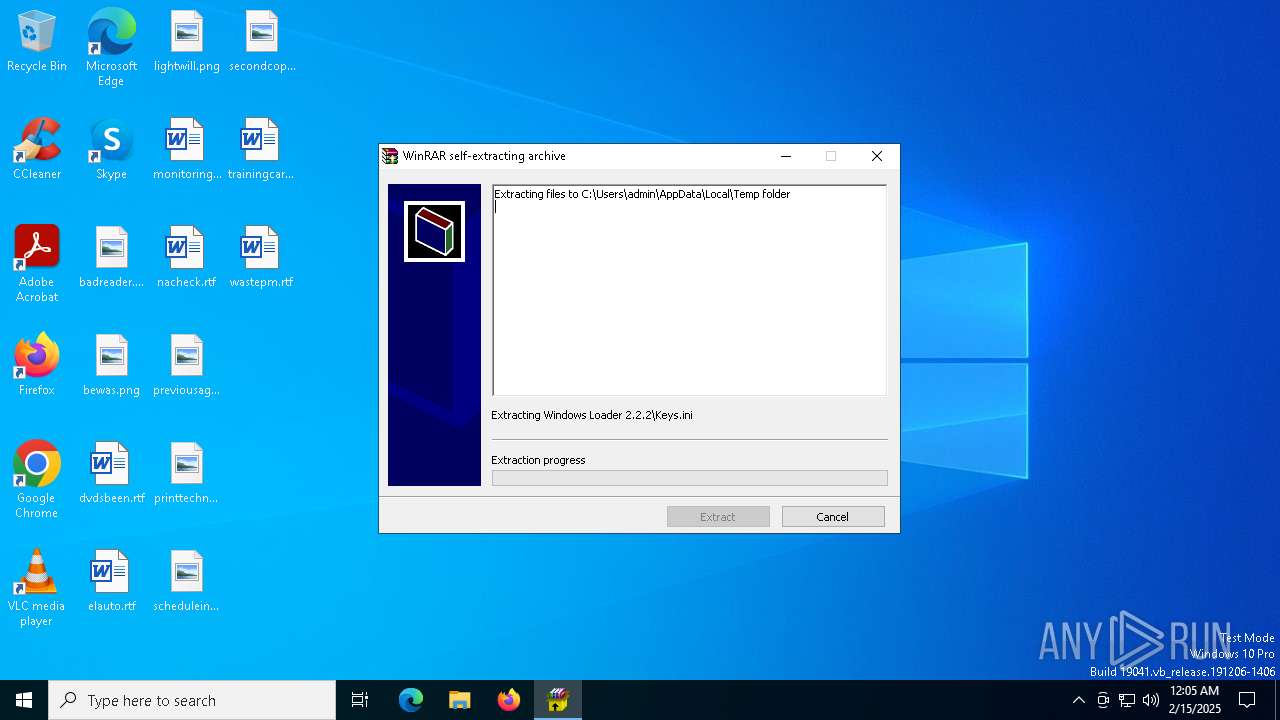
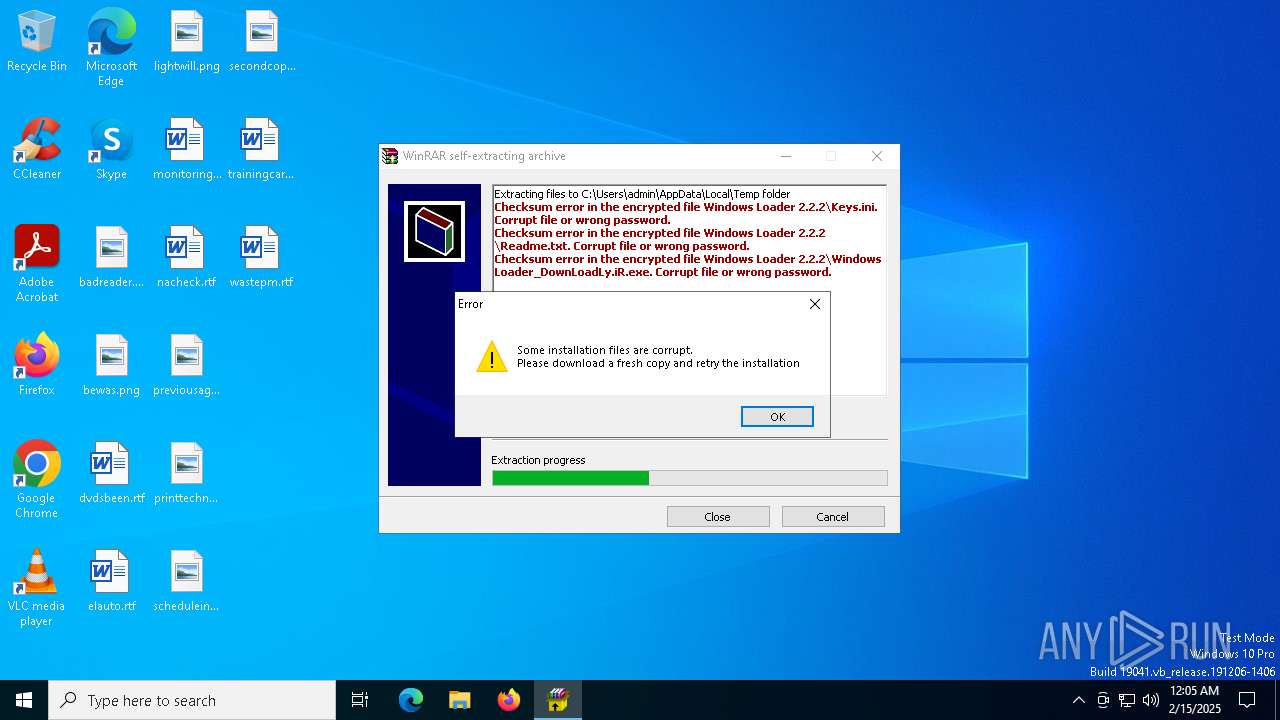
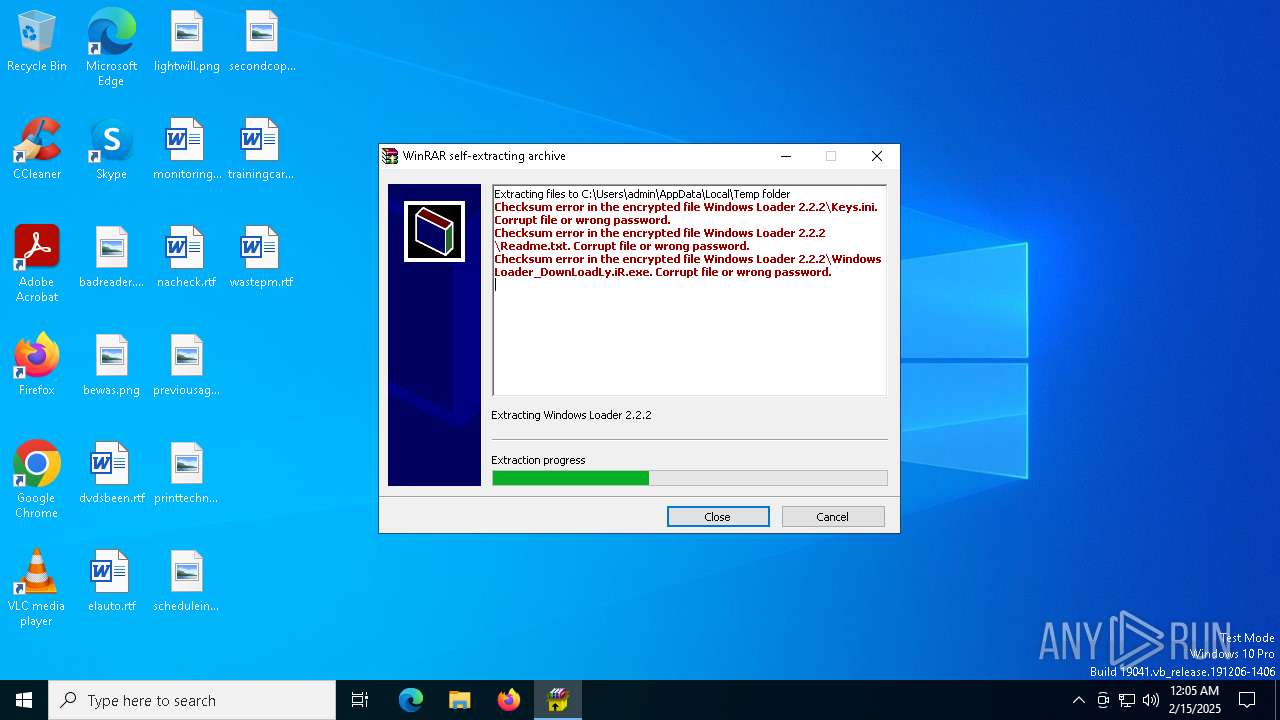
Create files in a temporary directory
- Windows_Loader_2.2.2_Downloadly.ir.exe (PID: 6364)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:12:01 08:08:23+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 153088 |
| InitializedDataSize: | 175104 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d728 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Total processes
130
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6364 | "C:\Users\admin\AppData\Local\Temp\Windows_Loader_2.2.2_Downloadly.ir.exe" | C:\Users\admin\AppData\Local\Temp\Windows_Loader_2.2.2_Downloadly.ir.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3 Modules
| |||||||||||||||
Total events
618
Read events
613
Write events
3
Delete events
2
Modification events
| (PID) Process: | (6364) Windows_Loader_2.2.2_Downloadly.ir.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (6364) Windows_Loader_2.2.2_Downloadly.ir.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (6364) Windows_Loader_2.2.2_Downloadly.ir.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (6364) Windows_Loader_2.2.2_Downloadly.ir.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFavoritesInitialSelection |
Value: | |||
| (PID) Process: | (6364) Windows_Loader_2.2.2_Downloadly.ir.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\LowRegistry |
| Operation: | delete value | Name: | AddToFeedsInitialSelection |
Value: | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6364 | Windows_Loader_2.2.2_Downloadly.ir.exe | C:\Users\admin\AppData\Local\Temp\Windows Loader 2.2.2\Keys.ini | binary | |
MD5:1723E753E7B2A7F86349CB5C50CE7488 | SHA256:5B40BFC1DB11D914898865C0C4488C7509FA415A24CA02CD739C6F2191F3AE94 | |||
| 6364 | Windows_Loader_2.2.2_Downloadly.ir.exe | C:\Users\admin\AppData\Local\Temp\Windows Loader 2.2.2\Windows Loader_DownLoadLy.iR.exe | binary | |
MD5:0C2AE787589695BBA2C35AE0B37D143E | SHA256:908AB97E05C4DDCA00FDB59C3A9E7FA61C1A78A6382B26448B6137C916116C3F | |||
| 6364 | Windows_Loader_2.2.2_Downloadly.ir.exe | C:\Users\admin\AppData\Local\Temp\Windows Loader 2.2.2\Readme.txt | binary | |
MD5:42C85DD004DECD6D93318A3DF4E62B89 | SHA256:850492E2C31E9072F386C1CB453E326BAF15DCEFC8A6DFA234AFE0775B57AC8F | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
29
DNS requests
14
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 1.01 Kb | whitelisted |
1176 | svchost.exe | GET | 200 | 2.23.77.188:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
— | — | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | CL | binary | 973 b | whitelisted |
5192 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 408 b | whitelisted |
5192 | SIHClient.exe | GET | 200 | 2.19.217.218:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 419 b | whitelisted |
6952 | backgroundTaskHost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 23.219.150.101:80 | www.microsoft.com | AKAMAI-AS | CL | whitelisted |
3464 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4724 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
1176 | svchost.exe | 20.190.159.129:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1176 | svchost.exe | 2.23.77.188:80 | — | AKAMAI-AS | DE | unknown |
1076 | svchost.exe | 2.19.106.8:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
arc.msn.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
fd.api.iris.microsoft.com |
| whitelisted |