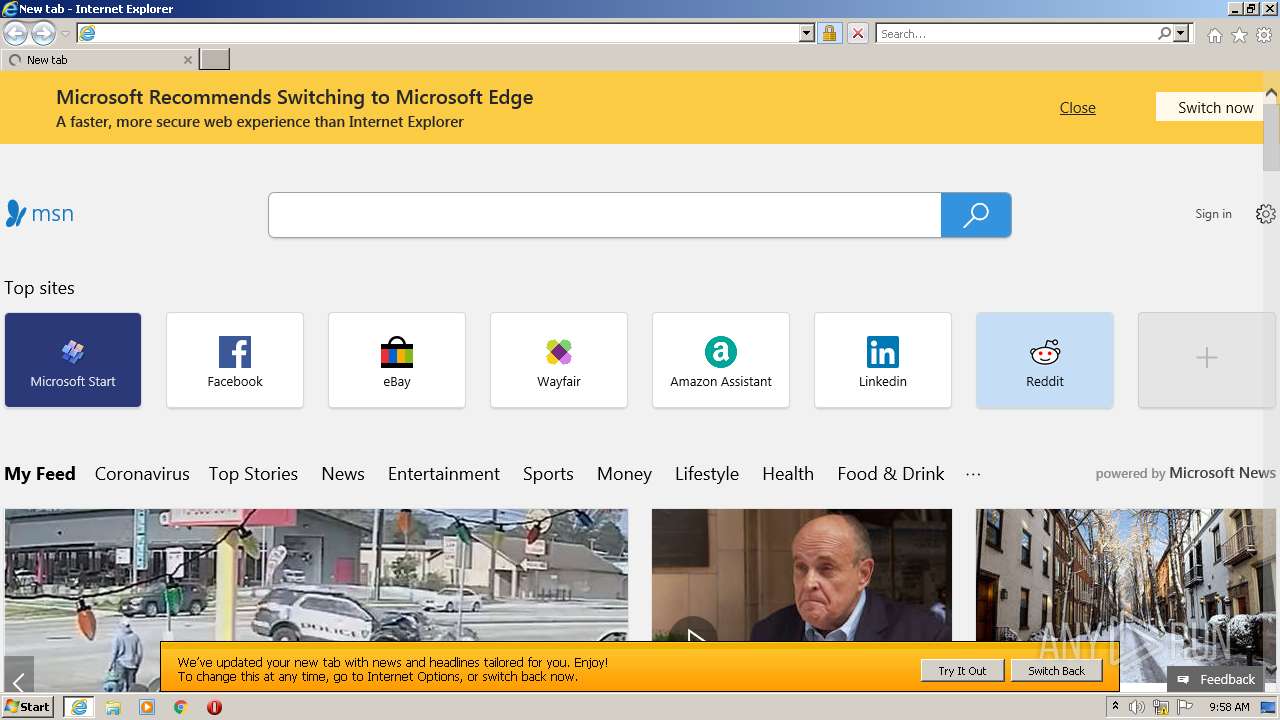
| URL: | https://www.msn.com/spartan/ientp?locale=en-US&market=US&enableregulatorypsm=0&enablecpsm=0&NTLogo=1&IsFRE=0 |
| Full analysis: | https://app.any.run/tasks/7f778cb1-f2f1-49b8-8e19-545311065ebf |
| Verdict: | Malicious activity |
| Analysis date: | January 26, 2022, 09:58:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 290234E7C41149325CBFEE6808C10FEC |
| SHA1: | 22D71B36220704381781704A6180438158B5DF60 |
| SHA256: | DCEA34F5769EECCF1544B9BFBA48649B14F63EB3136BB8DD5488BA7759B1A4C2 |
| SSDEEP: | 3:N8DSLfZmVuiALudFYAgDLrwwQKsM8luy7ExkCoNV:2OLhmVuiu8jgDzx8E+Yk5V |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2148)
- iexplore.exe (PID: 3728)
INFO
Changes internet zones settings
- iexplore.exe (PID: 3728)
Reads the computer name
- iexplore.exe (PID: 3728)
- iexplore.exe (PID: 2148)
Checks supported languages
- iexplore.exe (PID: 2148)
- iexplore.exe (PID: 3728)
Reads internet explorer settings
- iexplore.exe (PID: 2148)
Checks Windows Trust Settings
- iexplore.exe (PID: 3728)
- iexplore.exe (PID: 2148)
Reads settings of System Certificates
- iexplore.exe (PID: 2148)
- iexplore.exe (PID: 3728)
Application launched itself
- iexplore.exe (PID: 3728)
Creates files in the user directory
- iexplore.exe (PID: 3728)
- iexplore.exe (PID: 2148)
Changes settings of System certificates
- iexplore.exe (PID: 3728)
Adds / modifies Windows certificates
- iexplore.exe (PID: 3728)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
37
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2148 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3728 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3728 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://www.msn.com/spartan/ientp?locale=en-US&market=US&enableregulatorypsm=0&enablecpsm=0&NTLogo=1&IsFRE=0" | C:\Program Files\Internet Explorer\iexplore.exe | Explorer.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
19 422
Read events
19 266
Write events
154
Delete events
2
Modification events
| (PID) Process: | (3728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (3728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: | |||
| (PID) Process: | (3728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30937755 | |||
| (PID) Process: | (3728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (3728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30937755 | |||
| (PID) Process: | (3728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3728) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
0
Suspicious files
39
Text files
232
Unknown types
37
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3728 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 2148 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\BWXCB92Q.txt | text | |
MD5:— | SHA256:— | |||
| 2148 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\PA1NPRP9.txt | text | |
MD5:— | SHA256:— | |||
| 2148 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\5IWPIAR9\kernel-f98e286b[1].css | text | |
MD5:— | SHA256:— | |||
| 2148 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\0722KHM1.txt | text | |
MD5:— | SHA256:— | |||
| 3728 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2148 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\ientp[1].htm | html | |
MD5:— | SHA256:— | |||
| 2148 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_D975BBA8033175C8D112023D8A7A8AD6 | binary | |
MD5:— | SHA256:— | |||
| 2148 | iexplore.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\Low\T7H22YA4.txt | text | |
MD5:— | SHA256:— | |||
| 3728 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
36
TCP/UDP connections
203
DNS requests
80
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3728 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2148 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAxq6XzO1ZmDhpCgCp6lMhQ%3D | US | der | 471 b | whitelisted |
2148 | iexplore.exe | GET | 200 | 18.66.242.45:80 | http://ocsp.rootg2.amazontrust.com/MFQwUjBQME4wTDAJBgUrDgMCGgUABBSIfaREXmfqfJR3TkMYnD7O5MhzEgQUnF8A36oB1zArOIiiuG1KnPIRkYMCEwZ%2FlEoqJ83z%2BsKuKwH5CO65xMY%3D | US | der | 1.51 Kb | whitelisted |
3728 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2148 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
2148 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAo1CNVcKSsBffitZcAP9%2BQ%3D | US | der | 471 b | whitelisted |
2148 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQQX6Z6gAidtSefNc6DC0OInqPHDQQUD4BhHIIxYdUvKOeNRji0LOHG2eICEAz6fp3Hax5gxRDcvnNvdB8%3D | US | der | 471 b | whitelisted |
2148 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
2148 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTPJvUY%2Bsl%2Bj4yzQuAcL2oQno5fCgQUUWj%2FkK8CB3U8zNllZGKiErhZcjsCEA%2F6bQK5DKEZnVbQQLO8AOY%3D | US | der | 471 b | whitelisted |
2148 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfqhLjKLEJQZPin0KCzkdAQpVYowQUsT7DaQP4v0cB1JgmGggC72NkK8MCEATh56TcXPLzbcArQrhdFZ8%3D | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2148 | iexplore.exe | 204.79.197.203:443 | www.msn.com | Microsoft Corporation | US | malicious |
3728 | iexplore.exe | 131.253.33.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
3728 | iexplore.exe | 23.32.238.208:80 | ctldl.windowsupdate.com | XO Communications | US | unknown |
3728 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2148 | iexplore.exe | 77.238.180.12:443 | jill.fc.yahoo.com | Yahoo! UK Services Limited | GB | shared |
2148 | iexplore.exe | 2.16.186.42:443 | static-spartan-neu-s-msn-com.akamaized.net | Akamai International B.V. | — | whitelisted |
2148 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2148 | iexplore.exe | 2.16.186.18:443 | img-s-msn-com.akamaized.net | Akamai International B.V. | — | whitelisted |
2148 | iexplore.exe | 104.111.215.107:443 | img.s-msn.com | Akamai International B.V. | NL | whitelisted |
— | — | 13.32.99.23:443 | sb.scorecardresearch.com | Amazon.com, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.msn.com |
| whitelisted |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
static-spartan-neu-s-msn-com.akamaized.net |
| whitelisted |
jill.fc.yahoo.com |
| whitelisted |
img-s-msn-com.akamaized.net |
| whitelisted |
img.s-msn.com |
| whitelisted |
c.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2148 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2148 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2148 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2148 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2148 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2148 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2148 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2148 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2148 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |
2148 | iexplore.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |