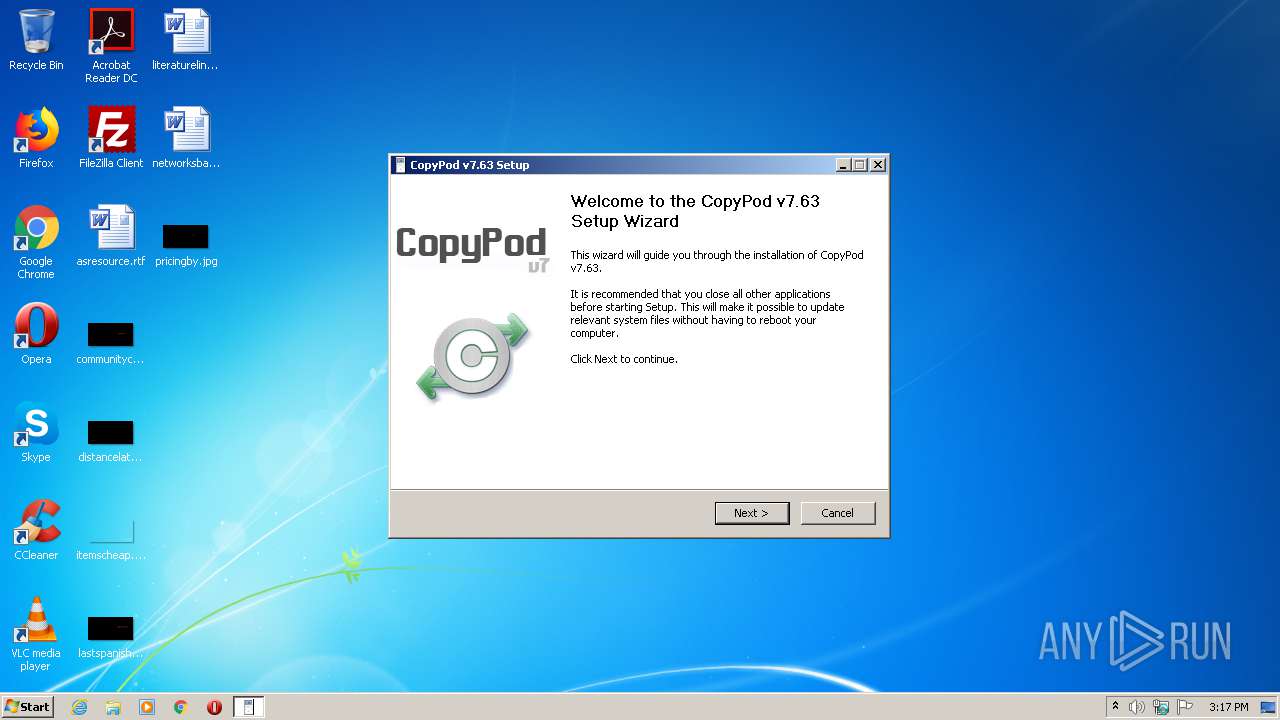
| File name: | CopyPod_v7.63.exe |
| Full analysis: | https://app.any.run/tasks/3d9af22e-e876-47b2-bd9c-32b4ae728934 |
| Verdict: | Malicious activity |
| Analysis date: | August 19, 2020, 14:17:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
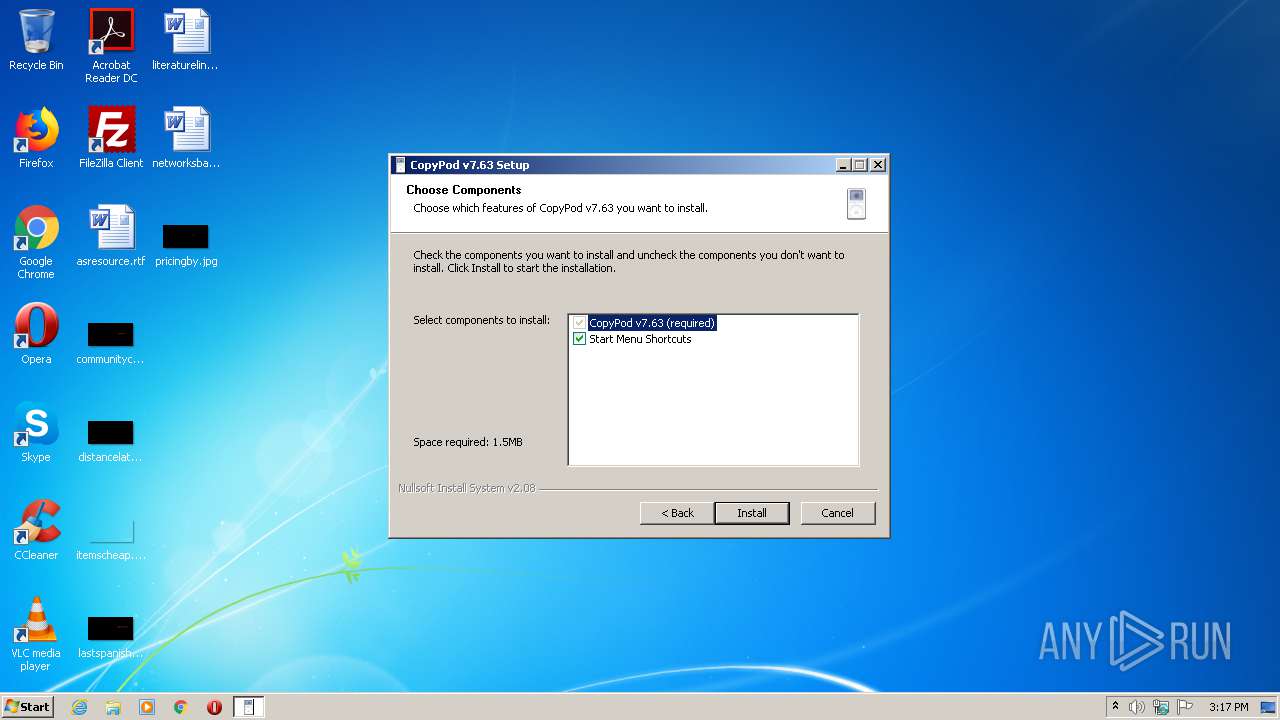
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 105F1DBCE7505D6E3018A959647464EF |
| SHA1: | 818D7AD1223D8A227F12BBA5C948896A8AA20191 |
| SHA256: | DCD8457CF69B9D7E81417452A261603CE7A9E0D666C277D2A31FF20DC304FC7C |
| SSDEEP: | 24576:HVWq/l0GbcXd8YdWX+hesBXQ5Vw6gTNrRqE8ITJuBCoPO9aVE2hXprbIz1zCCDJ:HVL/atXd8lEesBg3S8eJgdPO9a62nnez |
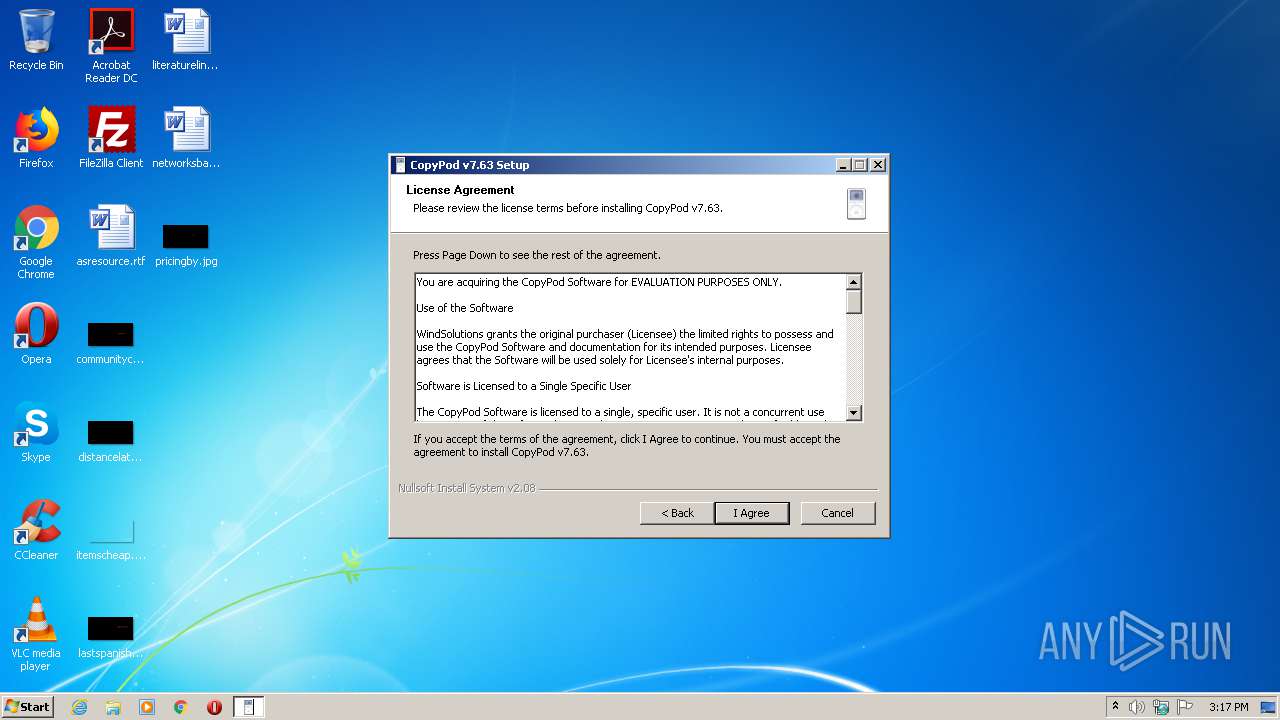
MALICIOUS
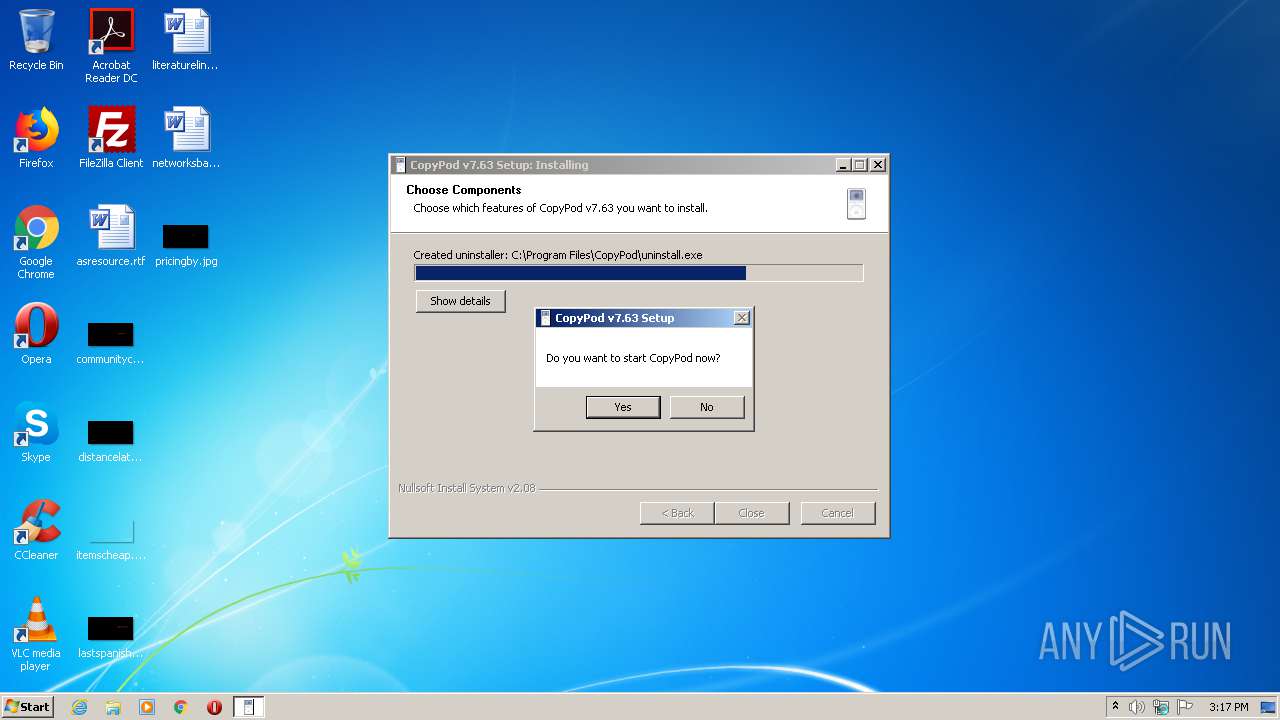
Loads dropped or rewritten executable
- CopyPod_v7.63.exe (PID: 3700)
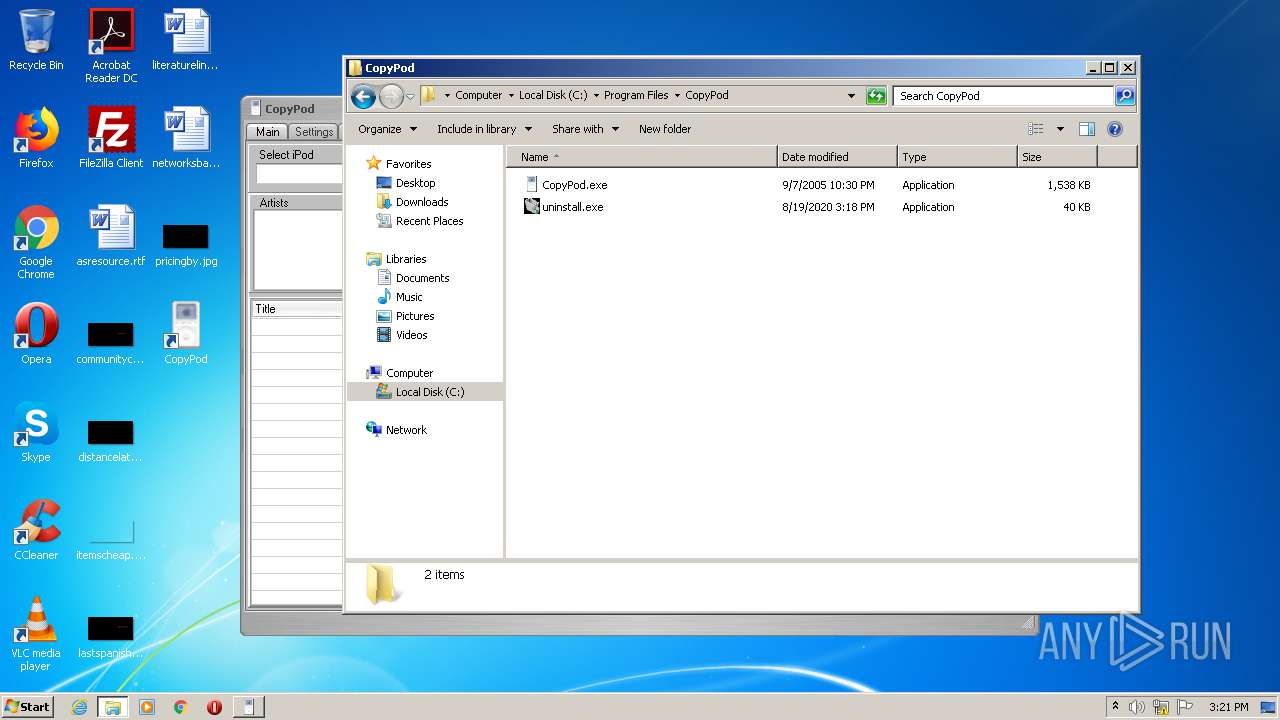
Application was dropped or rewritten from another process
- CopyPod.exe (PID: 3540)
SUSPICIOUS
Executable content was dropped or overwritten
- CopyPod_v7.63.exe (PID: 3700)
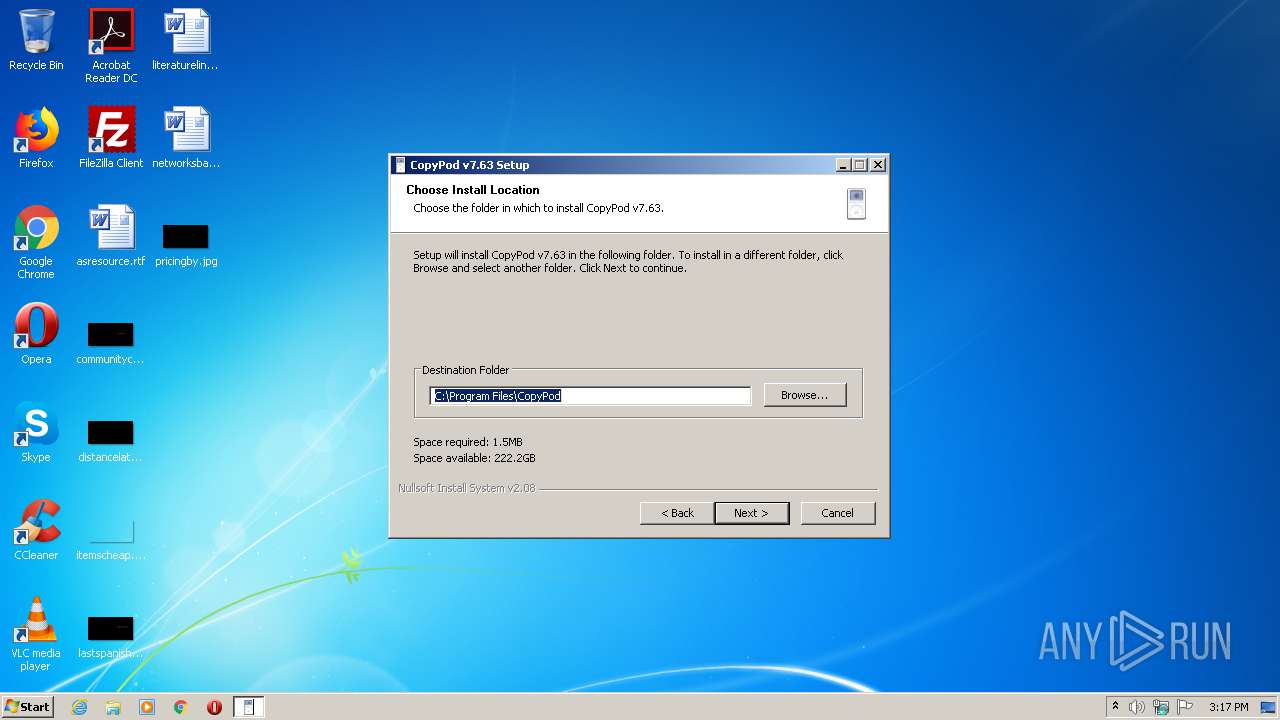
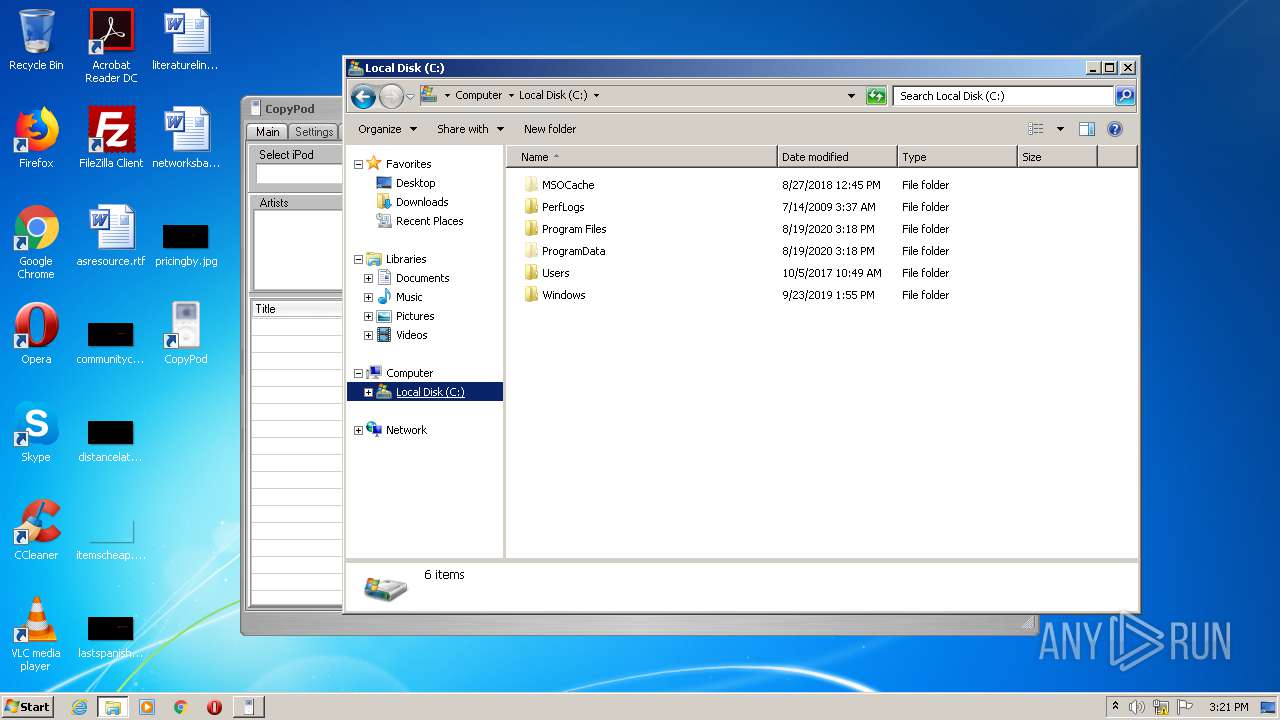
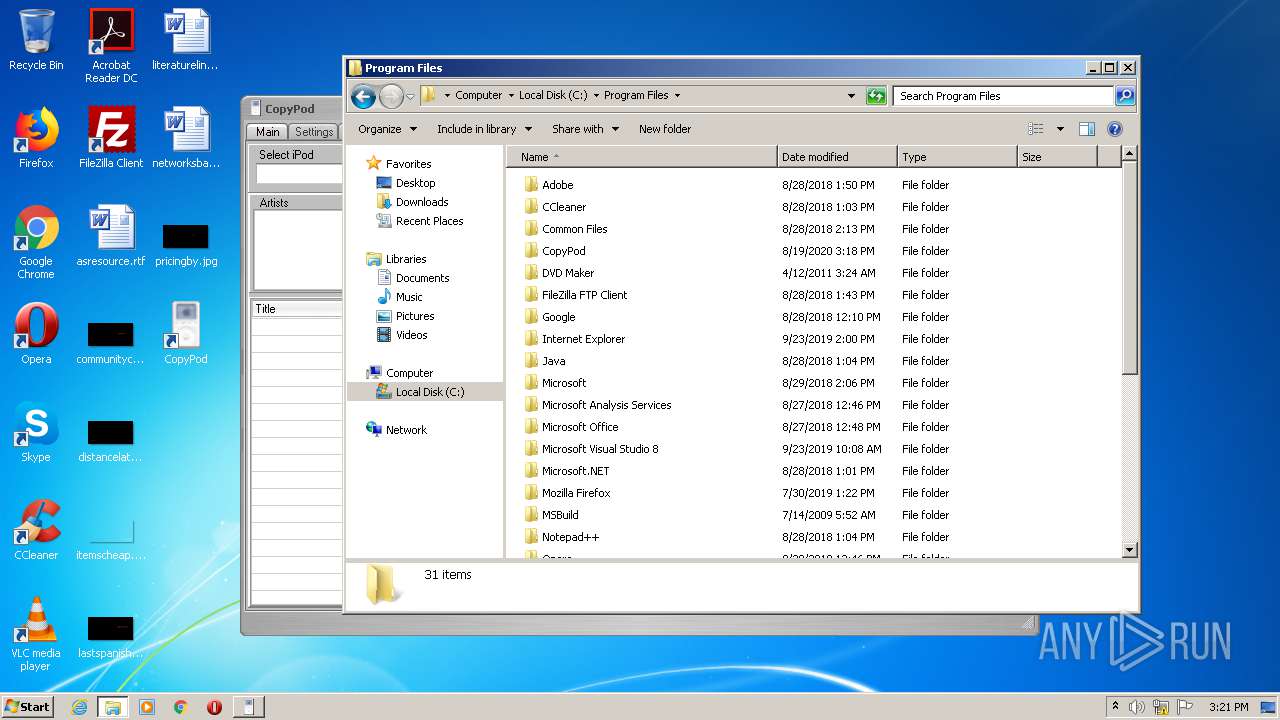
Creates files in the program directory
- CopyPod_v7.63.exe (PID: 3700)
- CopyPod.exe (PID: 3540)
Creates a software uninstall entry
- CopyPod_v7.63.exe (PID: 3700)
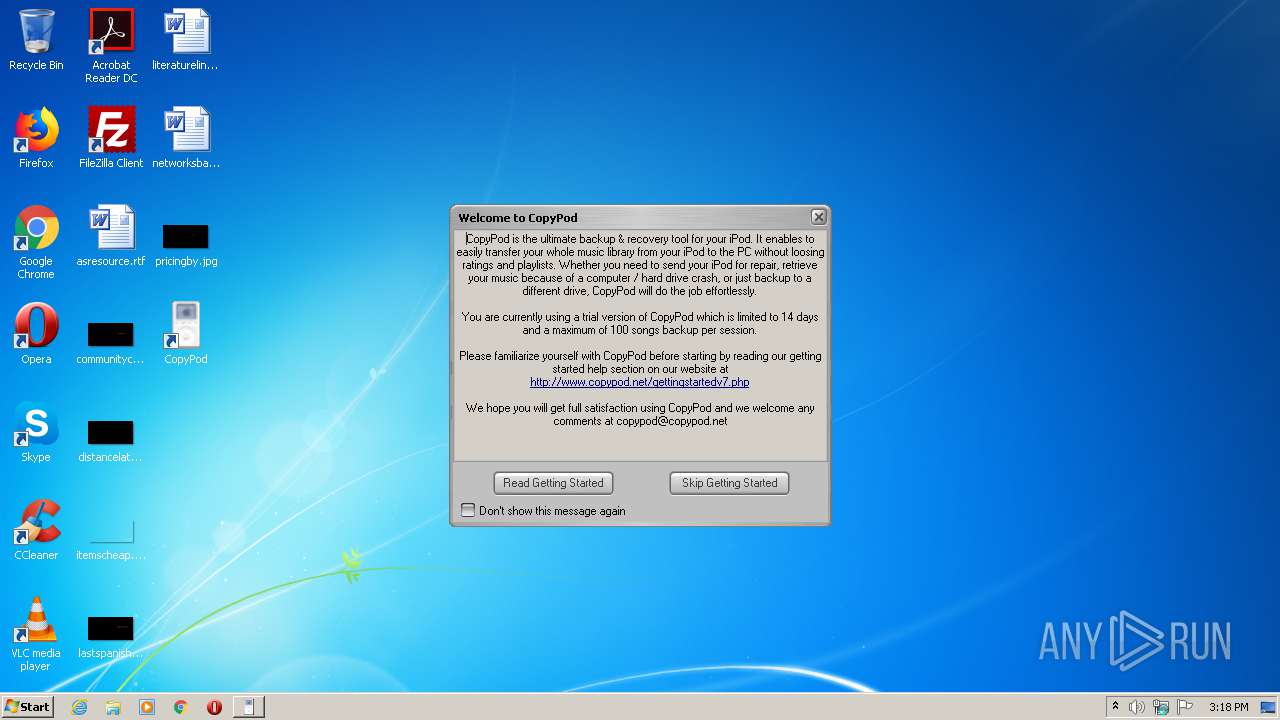
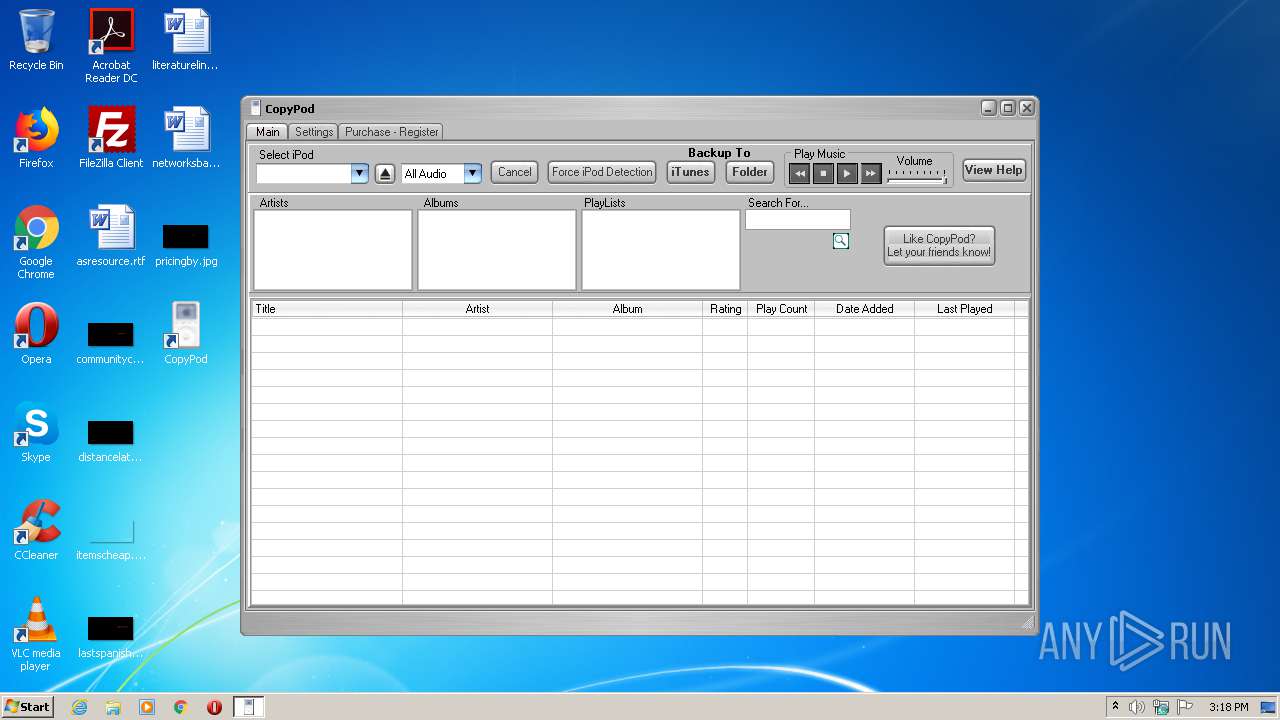
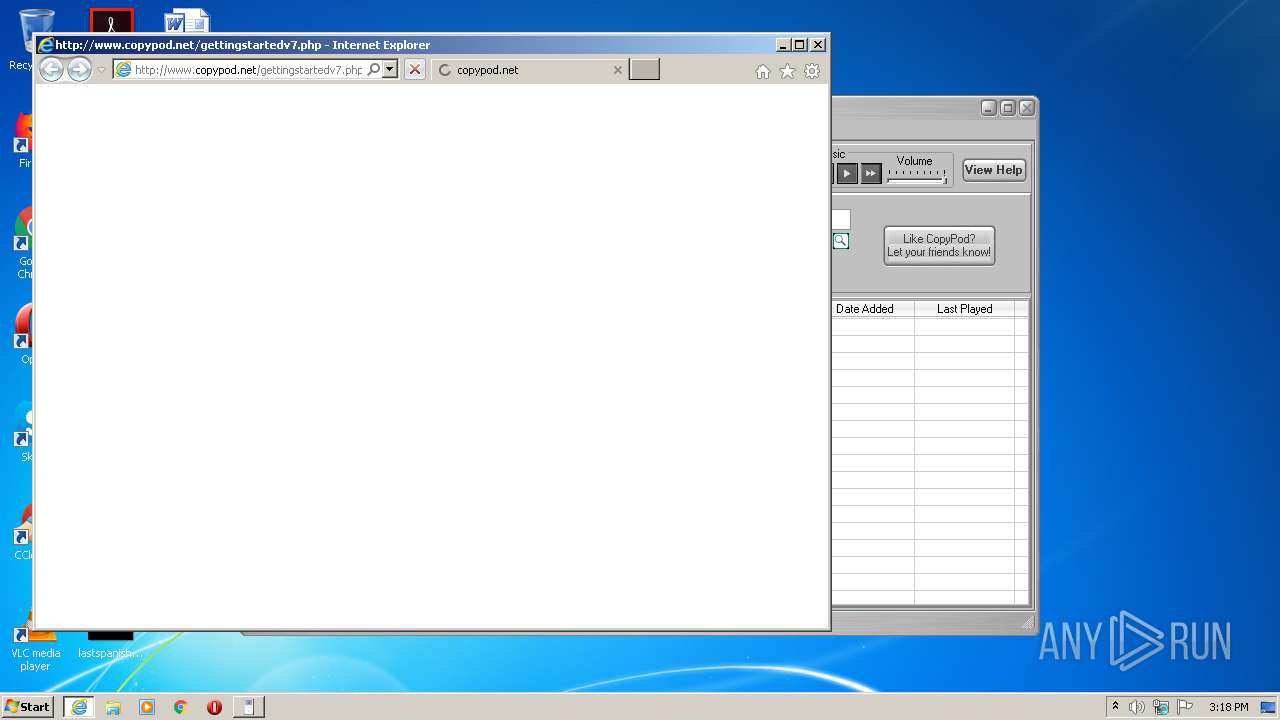
Starts Internet Explorer
- CopyPod.exe (PID: 3540)
Reads Internet Cache Settings
- CopyPod.exe (PID: 3540)
INFO
Application launched itself
- iexplore.exe (PID: 3828)
Reads Internet Cache Settings
- iexplore.exe (PID: 3828)
- iexplore.exe (PID: 2108)
Changes internet zones settings
- iexplore.exe (PID: 3828)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2108)
- iexplore.exe (PID: 3828)
Changes settings of System certificates
- iexplore.exe (PID: 2108)
- iexplore.exe (PID: 3828)
Reads settings of System Certificates
- iexplore.exe (PID: 3828)
- iexplore.exe (PID: 2108)
Reads internet explorer settings
- iexplore.exe (PID: 2108)
Creates files in the user directory
- iexplore.exe (PID: 2108)
Manual execution by user
- explorer.exe (PID: 2544)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2005:07:23 17:09:52+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 165376 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x31a7 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 23-Jul-2005 15:09:52 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 23-Jul-2005 15:09:52 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005B70 | 0x00005C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4565 |
.rdata | 0x00007000 | 0x000011D8 | 0x00001200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.23287 |
.data | 0x00009000 | 0x000260D4 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.21557 |
.ndata | 0x00030000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00039000 | 0x00003000 | 0x00002400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.34799 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.10276 | 533 | UNKNOWN | English - United States | RT_MANIFEST |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
103 | 1.5789 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
104 | 2.65946 | 280 | UNKNOWN | English - United States | RT_DIALOG |
105 | 2.73893 | 514 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
110 | 2.82633 | 1638 | UNKNOWN | English - United States | RT_BITMAP |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
49
Monitored processes
6
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2108 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3828 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2544 | "C:\Windows\explorer.exe" | C:\Windows\explorer.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2716 | "C:\Users\admin\AppData\Local\Temp\CopyPod_v7.63.exe" | C:\Users\admin\AppData\Local\Temp\CopyPod_v7.63.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
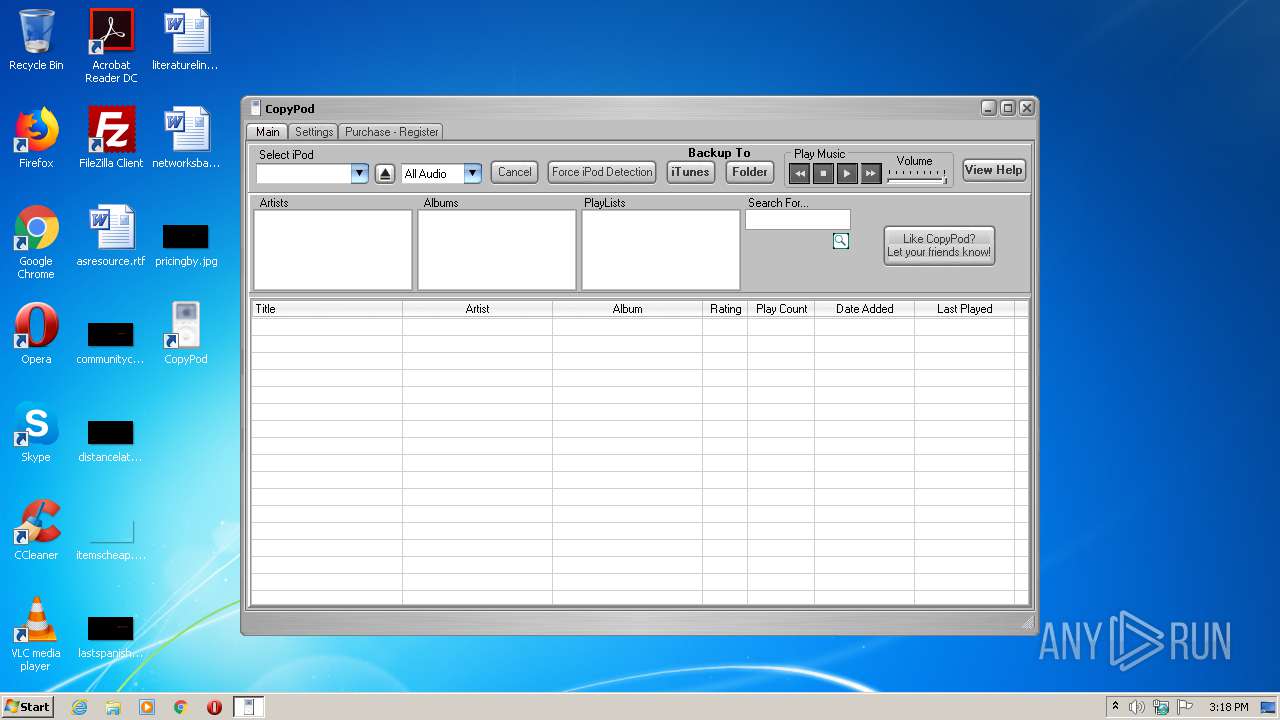
| 3540 | "C:\Program Files\CopyPod\CopyPod.exe" | C:\Program Files\CopyPod\CopyPod.exe | CopyPod_v7.63.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3700 | "C:\Users\admin\AppData\Local\Temp\CopyPod_v7.63.exe" | C:\Users\admin\AppData\Local\Temp\CopyPod_v7.63.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3828 | "C:\Program Files\Internet Explorer\iexplore.exe" http://www.copypod.net/gettingstartedv7.php | C:\Program Files\Internet Explorer\iexplore.exe | CopyPod.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
734
Read events
602
Write events
127
Delete events
5
Modification events
| (PID) Process: | (3700) CopyPod_v7.63.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\CopyPod |
| Operation: | write | Name: | 7_timing |
Value: -975704062 | |||
| (PID) Process: | (3700) CopyPod_v7.63.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CopyPod |
| Operation: | write | Name: | DisplayName |
Value: CopyPod (remove only) | |||
| (PID) Process: | (3700) CopyPod_v7.63.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\CopyPod |
| Operation: | write | Name: | UninstallString |
Value: "C:\Program Files\CopyPod\uninstall.exe" | |||
| (PID) Process: | (3540) CopyPod.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\AudioCompressionManager\DriverCache\msacm.imaadpcm |
| Operation: | write | Name: | fdwSupport |
Value: 1 | |||
| (PID) Process: | (3540) CopyPod.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\AudioCompressionManager\DriverCache\msacm.imaadpcm |
| Operation: | write | Name: | cFormatTags |
Value: 2 | |||
| (PID) Process: | (3540) CopyPod.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\AudioCompressionManager\DriverCache\msacm.imaadpcm |
| Operation: | write | Name: | aFormatTagCache |
Value: 01000000100000001100000014000000 | |||
| (PID) Process: | (3540) CopyPod.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\AudioCompressionManager\DriverCache\msacm.imaadpcm |
| Operation: | write | Name: | cFilterTags |
Value: 0 | |||
| (PID) Process: | (3540) CopyPod.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\AudioCompressionManager\DriverCache\msacm.msg711 |
| Operation: | write | Name: | fdwSupport |
Value: 1 | |||
| (PID) Process: | (3540) CopyPod.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\AudioCompressionManager\DriverCache\msacm.msg711 |
| Operation: | write | Name: | cFormatTags |
Value: 3 | |||
| (PID) Process: | (3540) CopyPod.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\AudioCompressionManager\DriverCache\msacm.msg711 |
| Operation: | write | Name: | aFormatTagCache |
Value: 010000001000000006000000120000000700000012000000 | |||
Executable files
4
Suspicious files
27
Text files
60
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2108 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Cab35F0.tmp | — | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Tar35F1.tmp | — | |
MD5:— | SHA256:— | |||
| 3700 | CopyPod_v7.63.exe | C:\Users\admin\AppData\Local\Temp\nsdC5C2.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 3700 | CopyPod_v7.63.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\CopyPod\Uninstall.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3700 | CopyPod_v7.63.exe | C:\Users\Administrator\Desktop\CopyPod.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3700 | CopyPod_v7.63.exe | C:\ProgramData\Microsoft\Windows\Start Menu\Programs\CopyPod\CopyPod.lnk | lnk | |
MD5:— | SHA256:— | |||
| 3700 | CopyPod_v7.63.exe | C:\Users\admin\Desktop\CopyPod.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | binary | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | der | |
MD5:— | SHA256:— | |||
| 2108 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\autoptimize_single_944b0d0fbe251a30191882d84e4431ee[1].css | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
29
DNS requests
15
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2108 | iexplore.exe | GET | 304 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEArLKLpGXuU5CHZ0cPPNxhI%3D | US | — | — | whitelisted |
2108 | iexplore.exe | GET | 304 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEArLKLpGXuU5CHZ0cPPNxhI%3D | US | der | 471 b | whitelisted |
2108 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEArLKLpGXuU5CHZ0cPPNxhI%3D | US | der | 471 b | whitelisted |
2108 | iexplore.exe | GET | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/gsr2/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBTgXIsxbvr2lBkPpoIEVRE6gHlCnAQUm%2BIHV2ccHsBqBt5ZtJot39wZhi4CDQHjtJqhjYqpgSVpULg%3D | US | der | 468 b | whitelisted |
2108 | iexplore.exe | GET | 304 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTnvAI%2FnN49qPTJY2qTQtfkLxjvEAQUo53mH%2FnaOU%2FAbuiRy5Wl2jHiCp8CEAFlK6jKOKePWQ%2BgvKM%2B9nQ%3D | US | der | 314 b | whitelisted |
2108 | iexplore.exe | GET | 304 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTnvAI%2FnN49qPTJY2qTQtfkLxjvEAQUo53mH%2FnaOU%2FAbuiRy5Wl2jHiCp8CEAFlK6jKOKePWQ%2BgvKM%2B9nQ%3D | US | — | — | whitelisted |
2108 | iexplore.exe | GET | 200 | 216.58.206.3:80 | http://ocsp.pki.goog/gts1o1core/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEQDM9j8%2B94pW6ggAAAAATZ8E | US | der | 472 b | whitelisted |
3828 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8sEMlbBsCTf7jUSfg%2BhWk%3D | US | der | 1.47 Kb | whitelisted |
3540 | CopyPod.exe | GET | 301 | 54.149.145.98:80 | http://www.copypod.net/CopyPod.vs | US | html | 233 b | suspicious |
2108 | iexplore.exe | GET | 200 | 2.16.107.114:80 | http://ocsp.int-x3.letsencrypt.org/MFMwUTBPME0wSzAJBgUrDgMCGgUABBR%2B5mrncpqz%2FPiiIGRsFqEtYHEIXQQUqEpqYwR93brm0Tm3pkVl7%2FOo7KECEgNcrH2LAkXnIHgRXfVeiORn6w%3D%3D | unknown | der | 527 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2108 | iexplore.exe | 54.149.145.98:80 | www.copypod.net | Amazon.com, Inc. | US | suspicious |
2108 | iexplore.exe | 52.47.178.141:443 | www.copytrans.jp | Amazon.com, Inc. | FR | suspicious |
2108 | iexplore.exe | 2.16.107.73:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | — | suspicious |
2108 | iexplore.exe | 2.16.107.114:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | — | suspicious |
2108 | iexplore.exe | 104.17.78.107:443 | cdnjs.cloudflare.com | Cloudflare Inc | US | unknown |
2108 | iexplore.exe | 172.217.22.104:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2108 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2108 | iexplore.exe | 216.58.206.3:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
3828 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2108 | iexplore.exe | 216.58.207.78:443 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.copypod.net |
| suspicious |
www.copytrans.jp |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
www.google-analytics.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2108 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS - Landing Page Requested - 15Alpha1Digit.php |