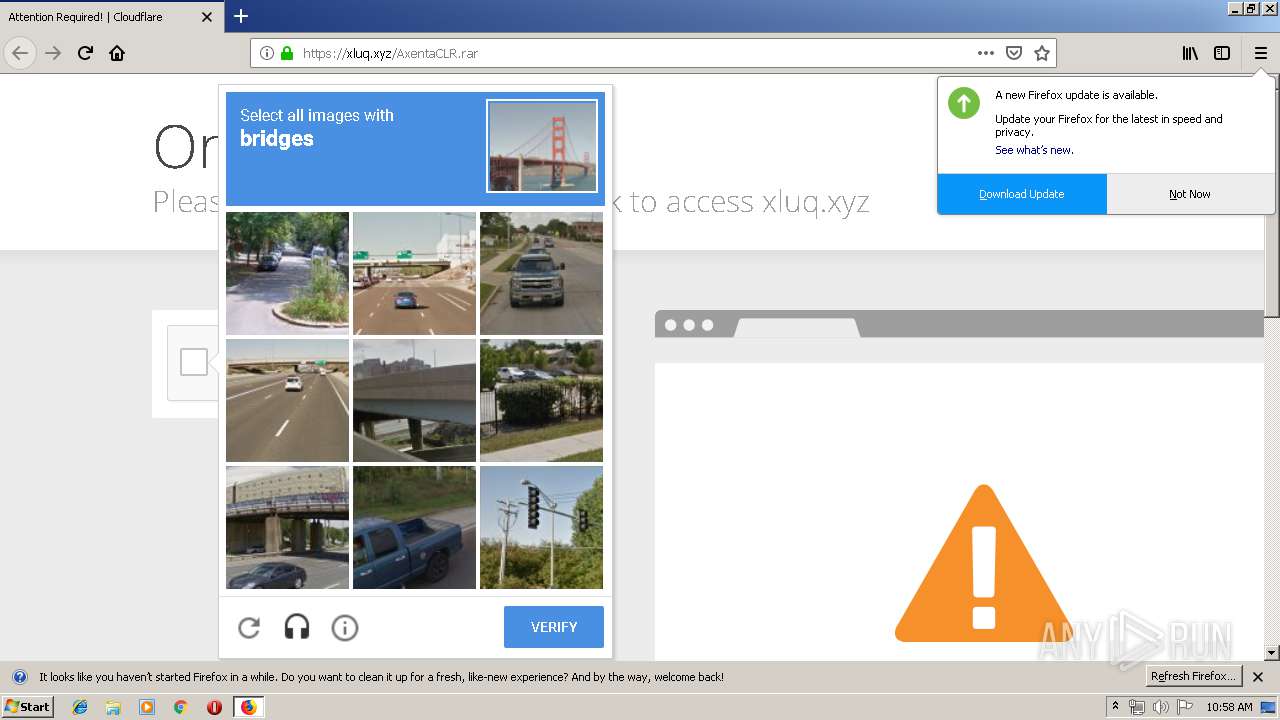
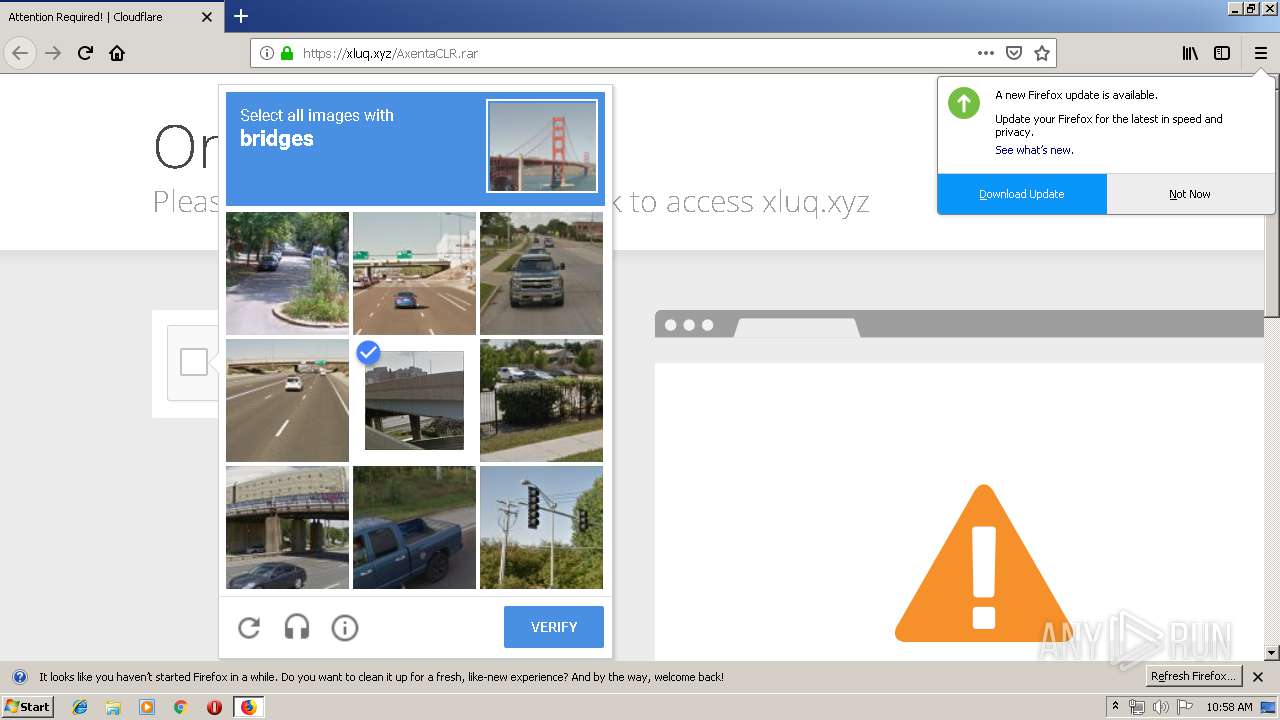
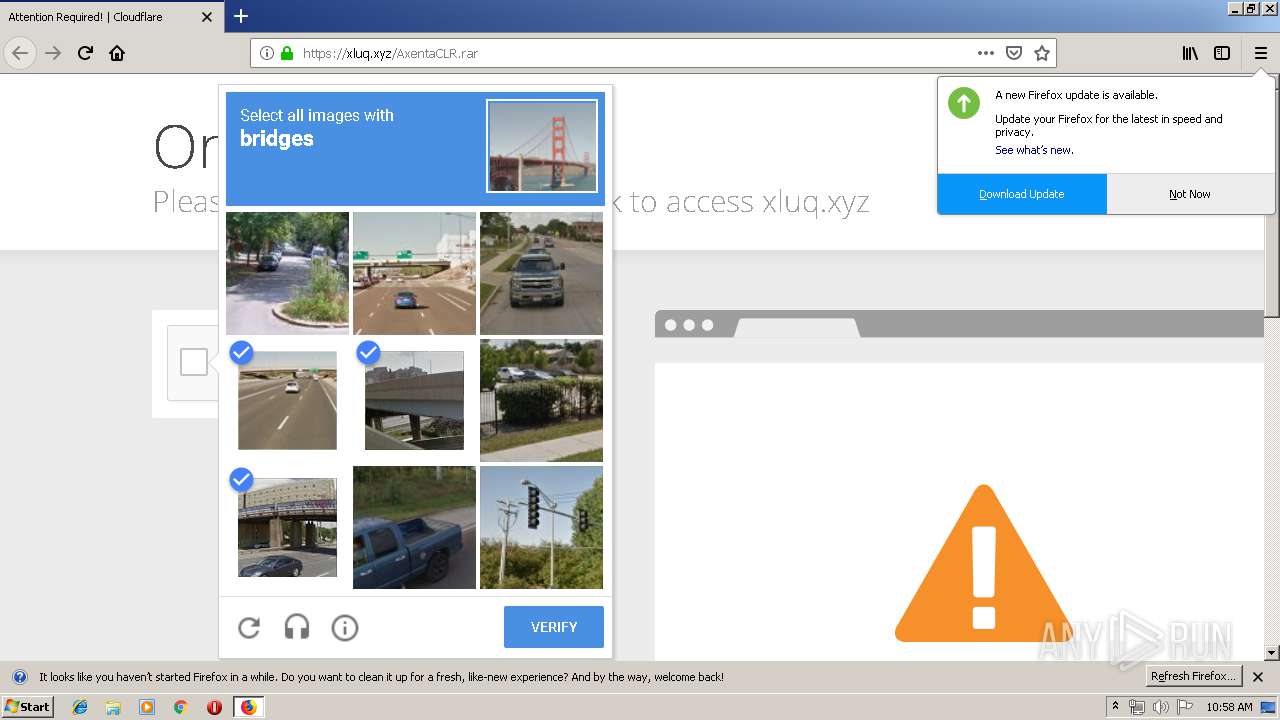
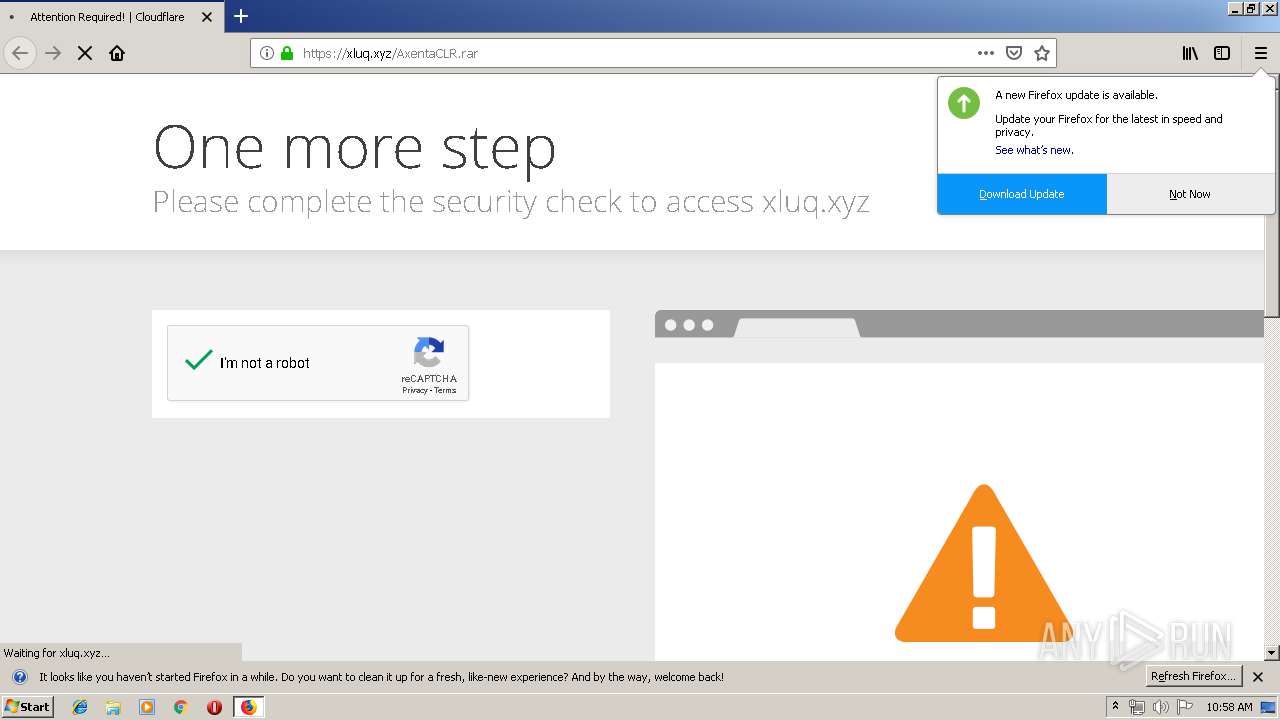
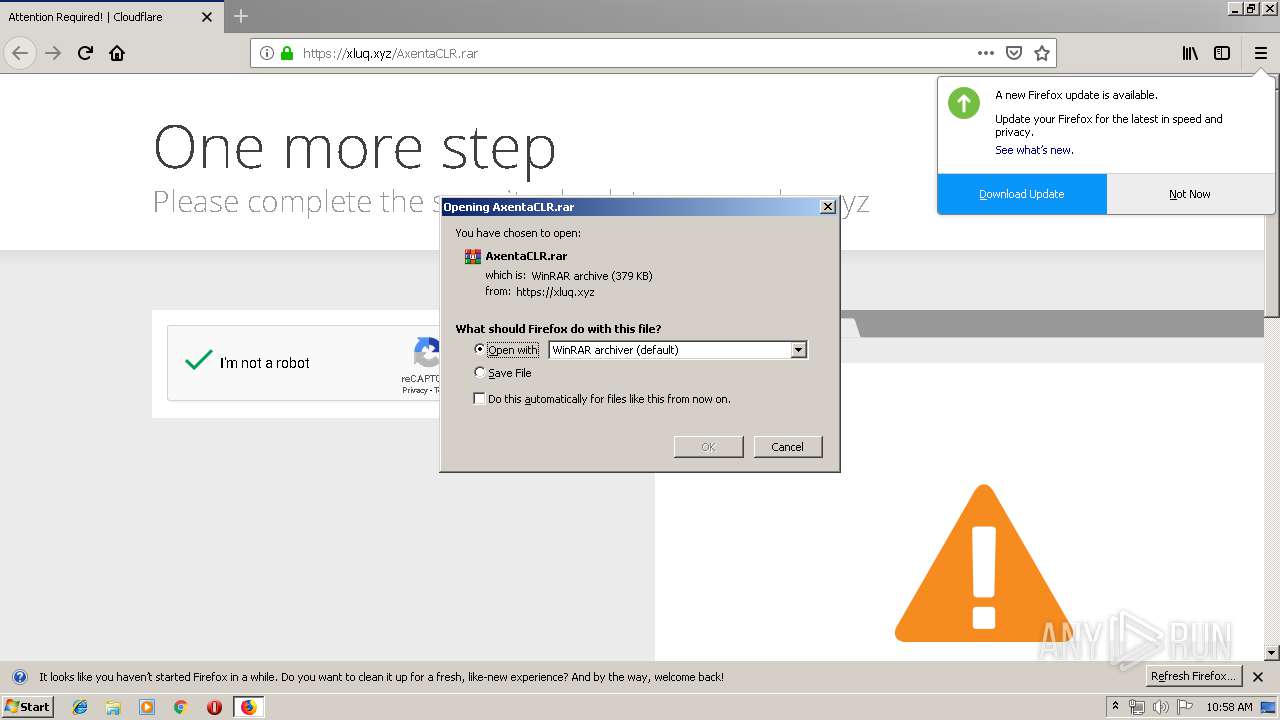
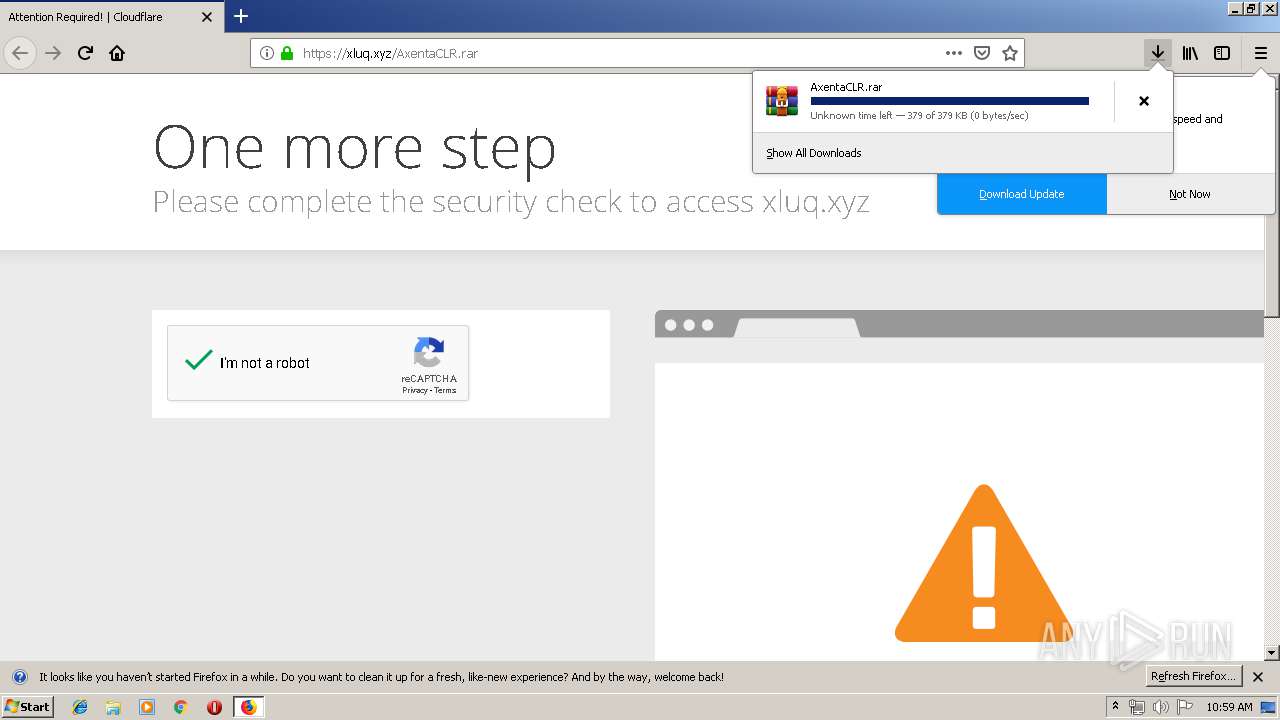
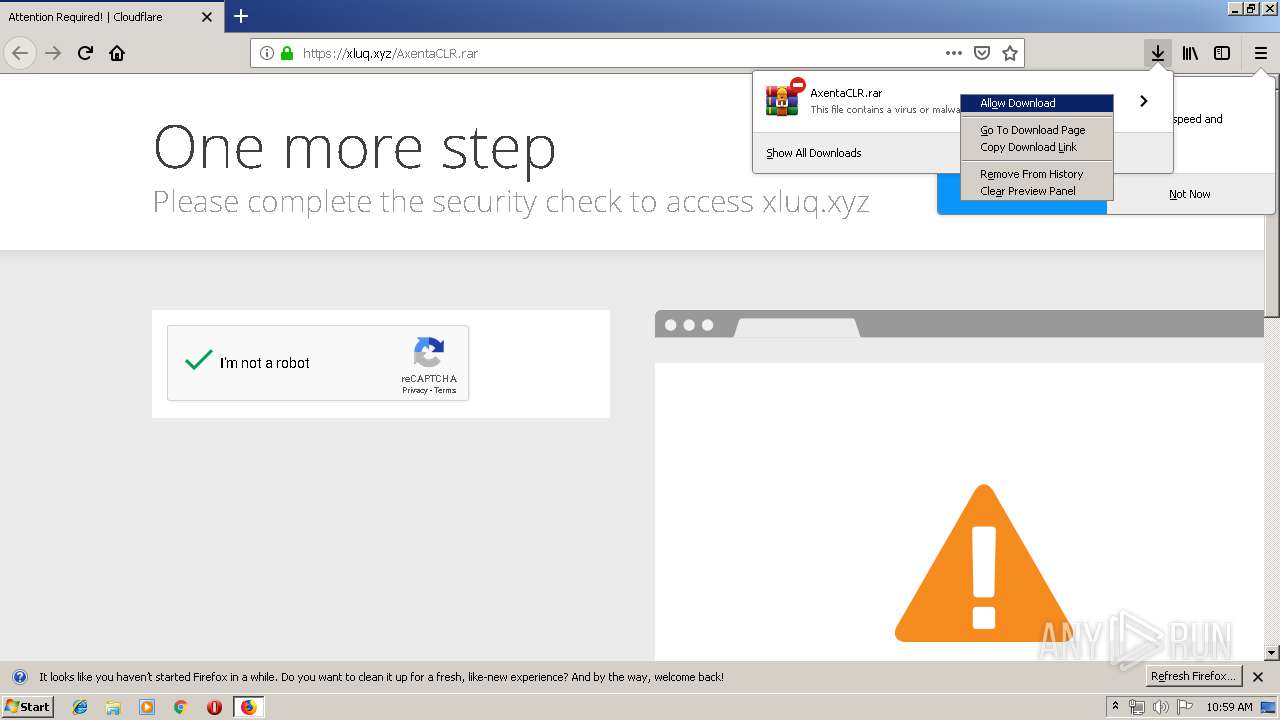
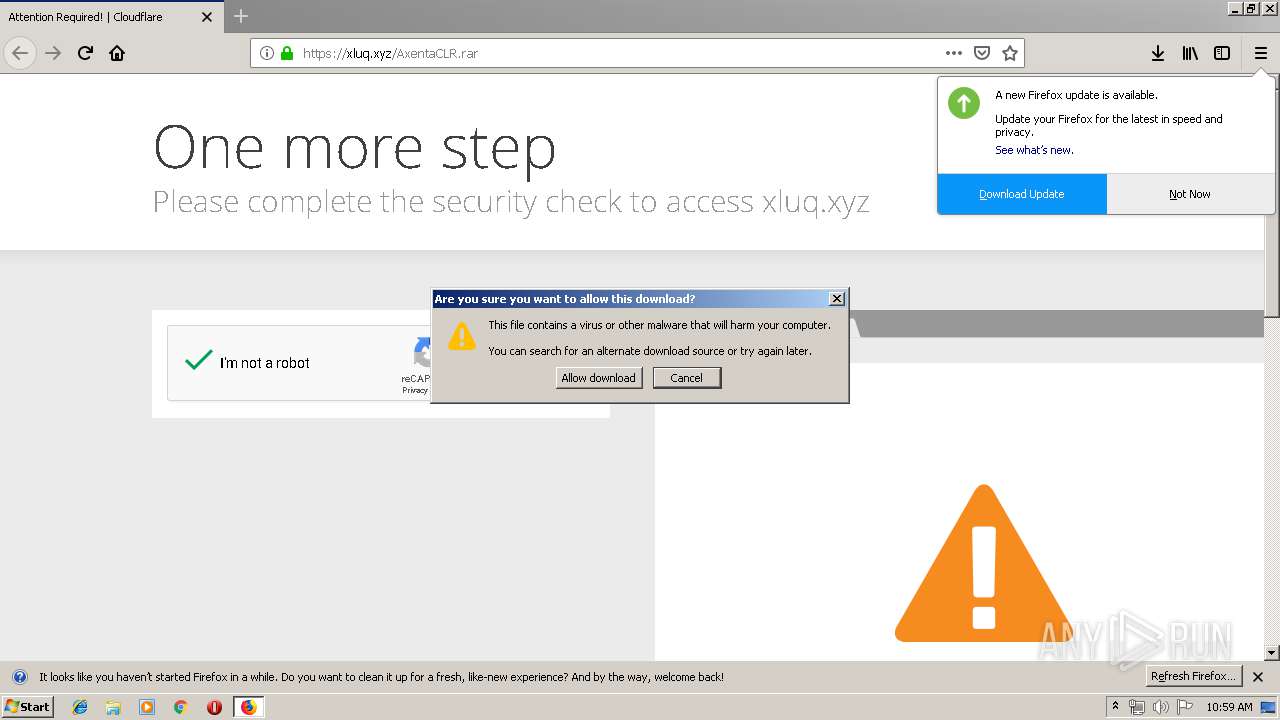
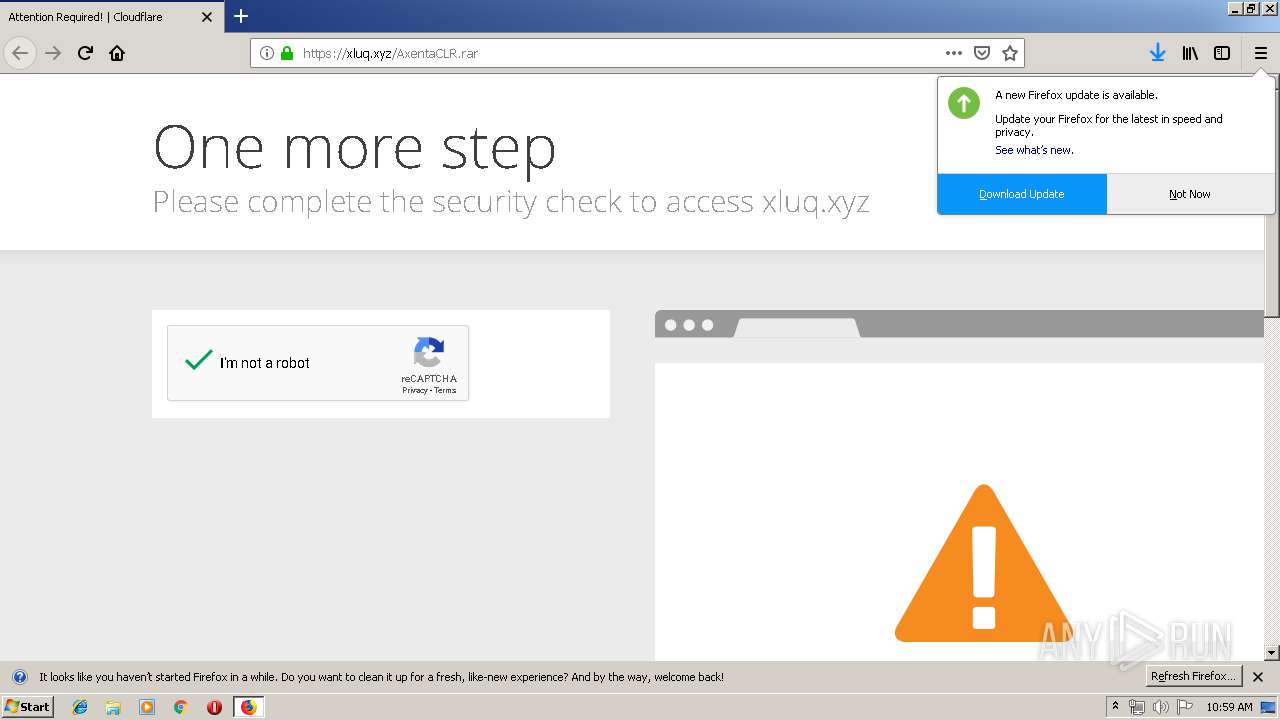
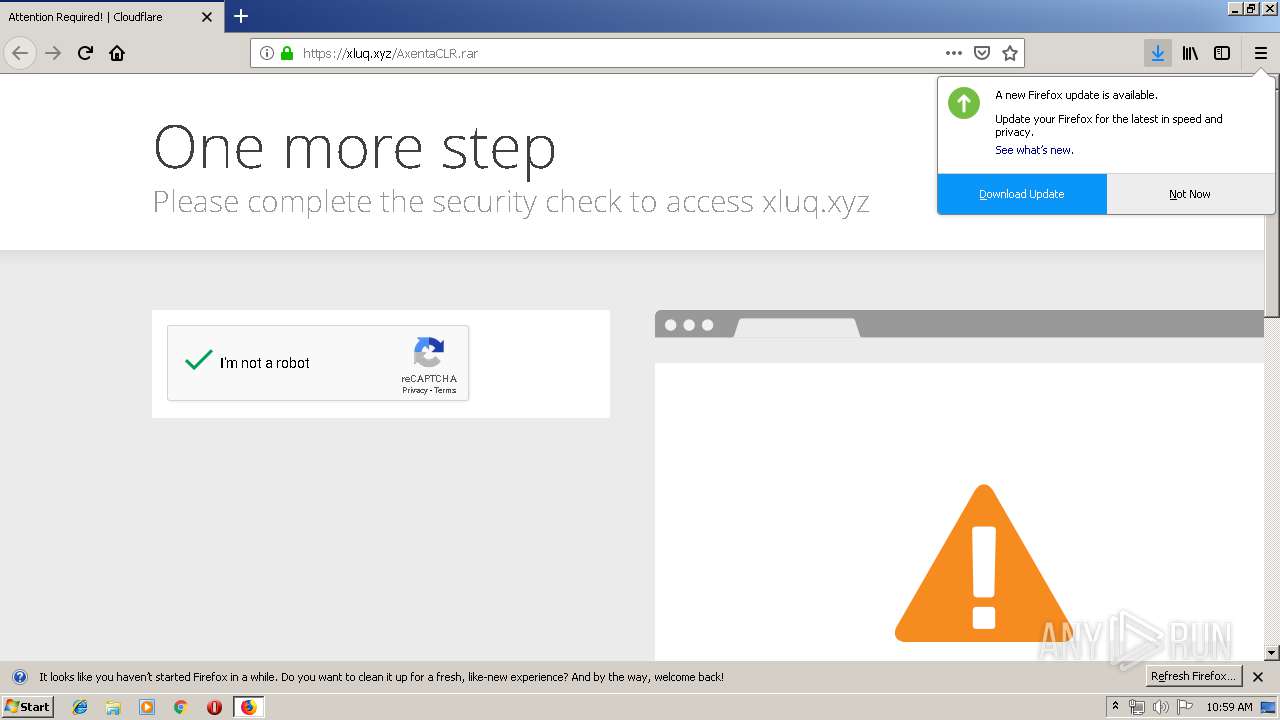
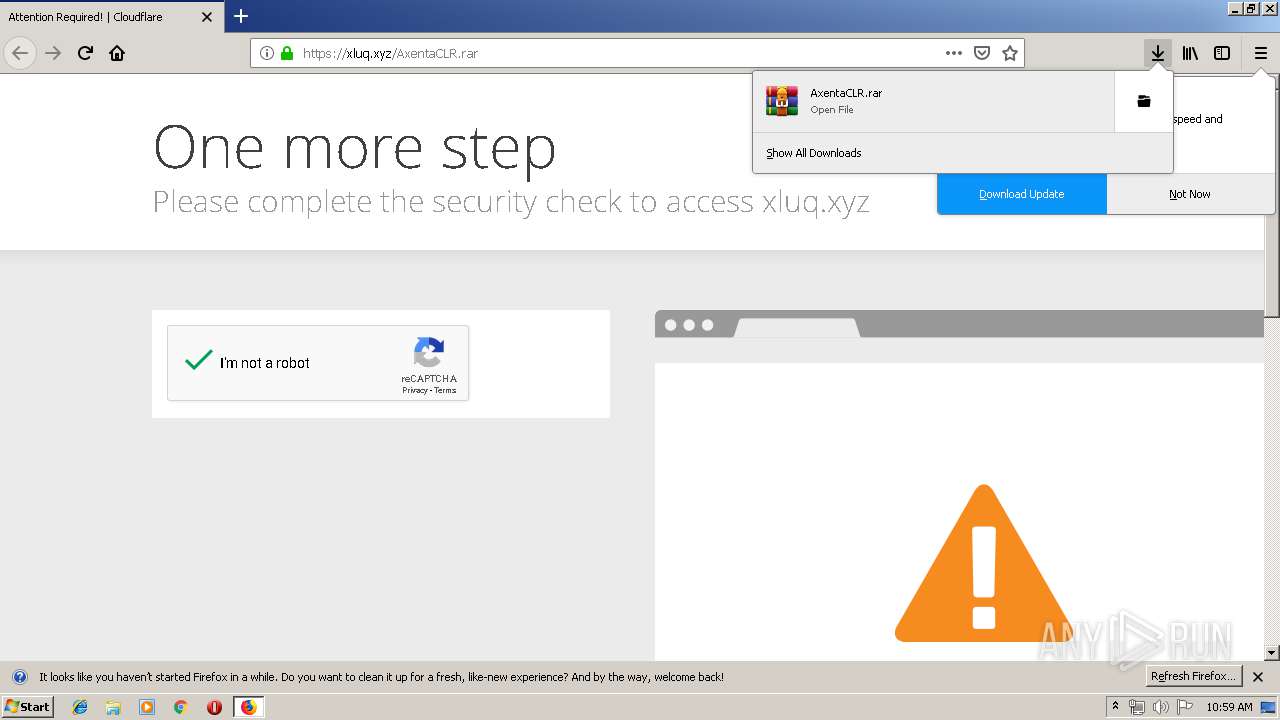
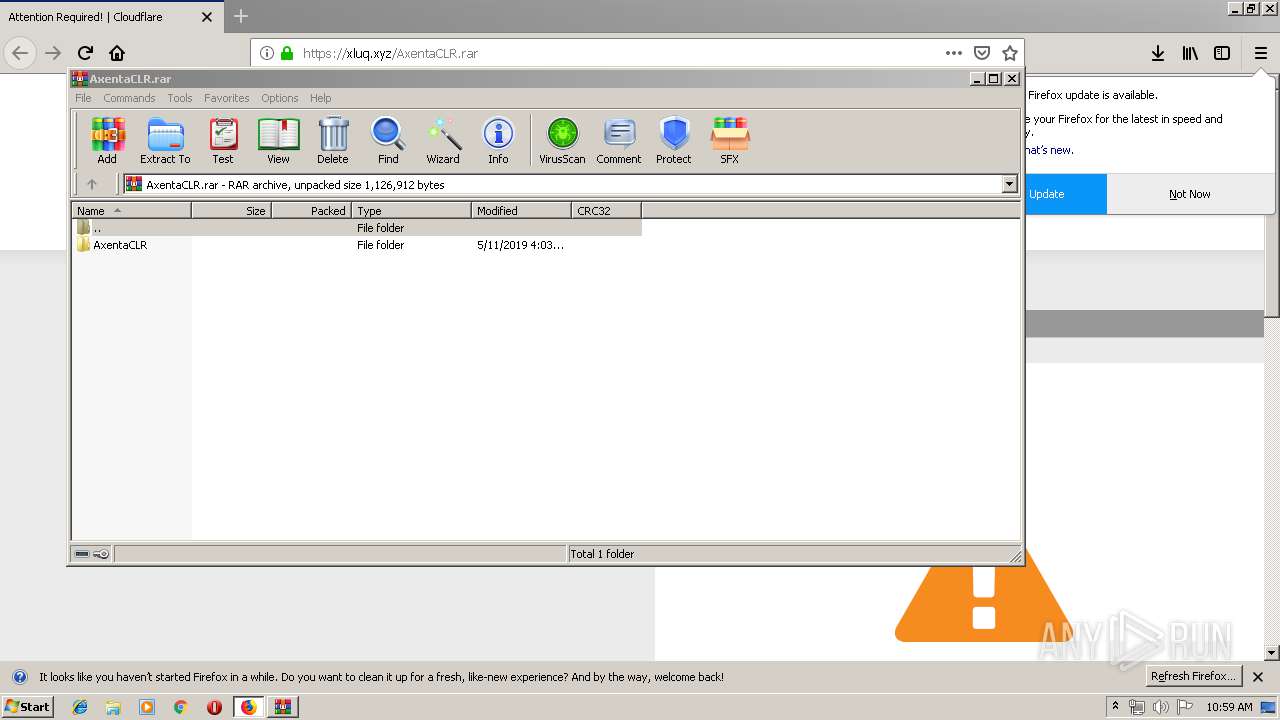
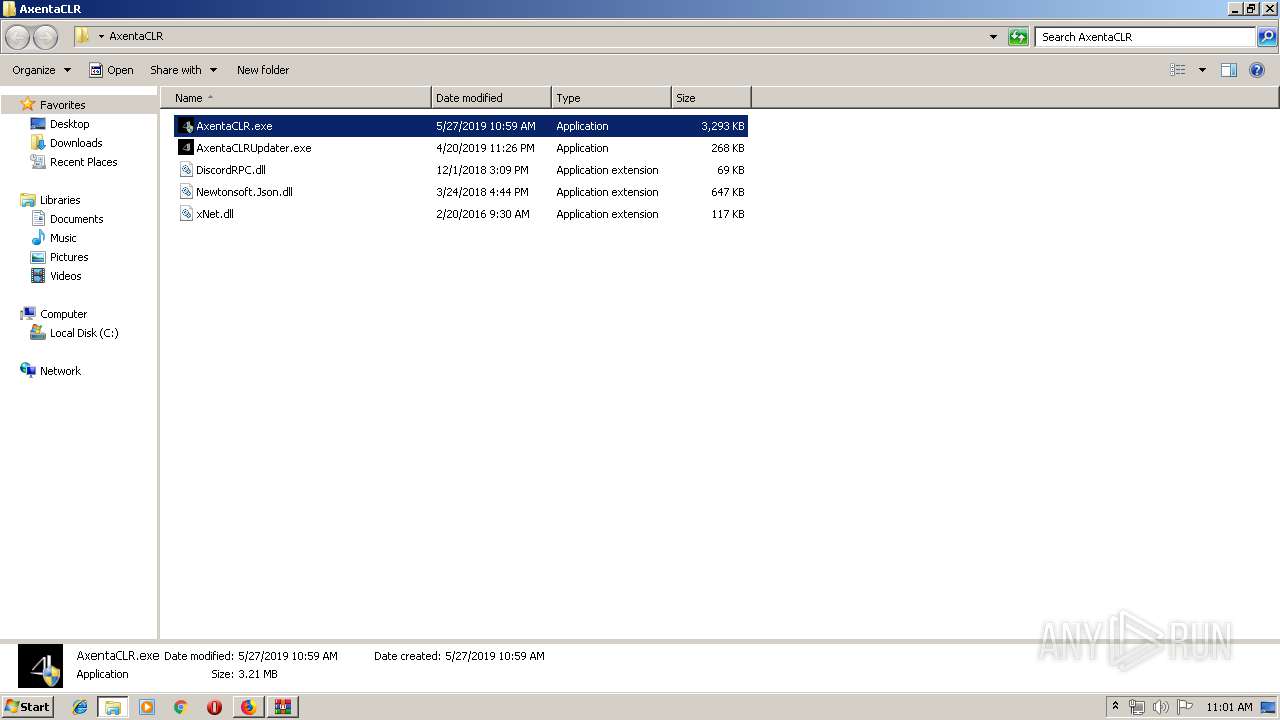
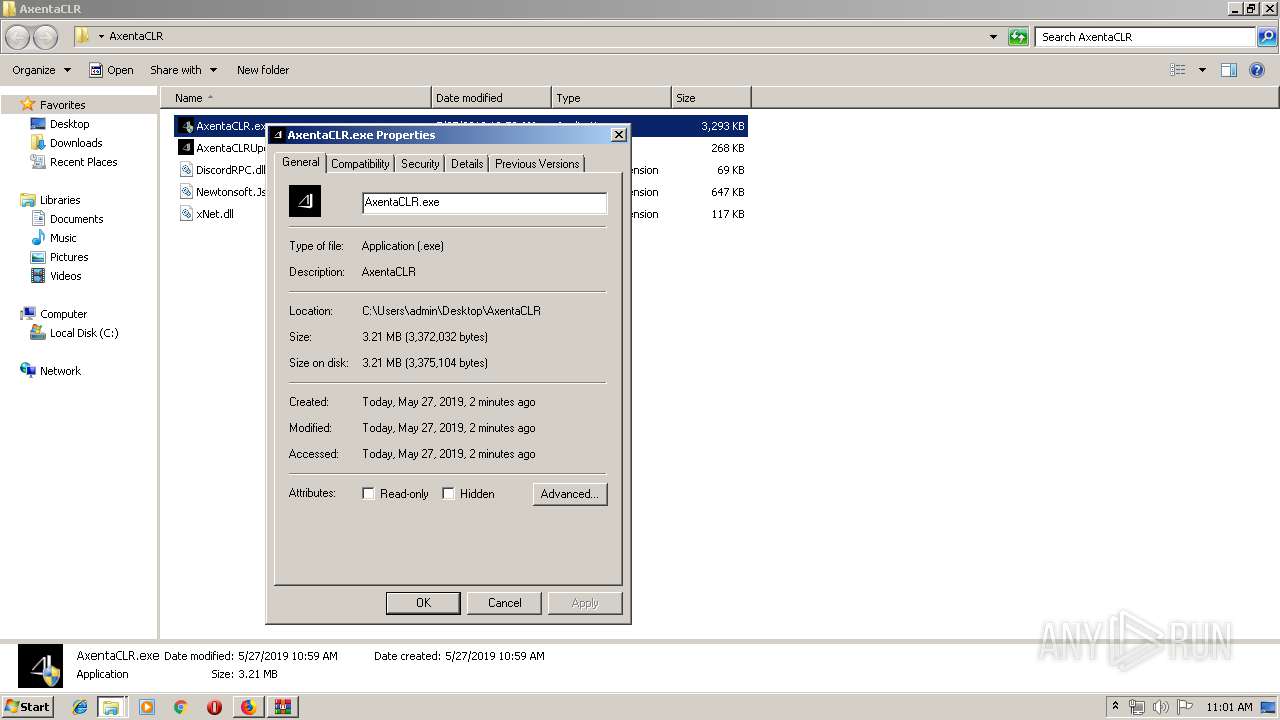
| URL: | https://xluq.xyz/AxentaCLR.rar |
| Full analysis: | https://app.any.run/tasks/b1cd7001-44bf-409c-9fd7-3b6369022bcf |
| Verdict: | Malicious activity |
| Analysis date: | May 27, 2019, 09:58:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 612BF2F0AEC12E104E229D50A92BCCFF |
| SHA1: | AE74A3D2746978D6D187945AB73D228A4BEF3B02 |
| SHA256: | DCD221A471DA4C634755AC44627AA397DA11E226D8A739C0571AAC8573FADD5E |
| SSDEEP: | 3:N8lUfKUALREWOn:2AAlEWOn |
MALICIOUS
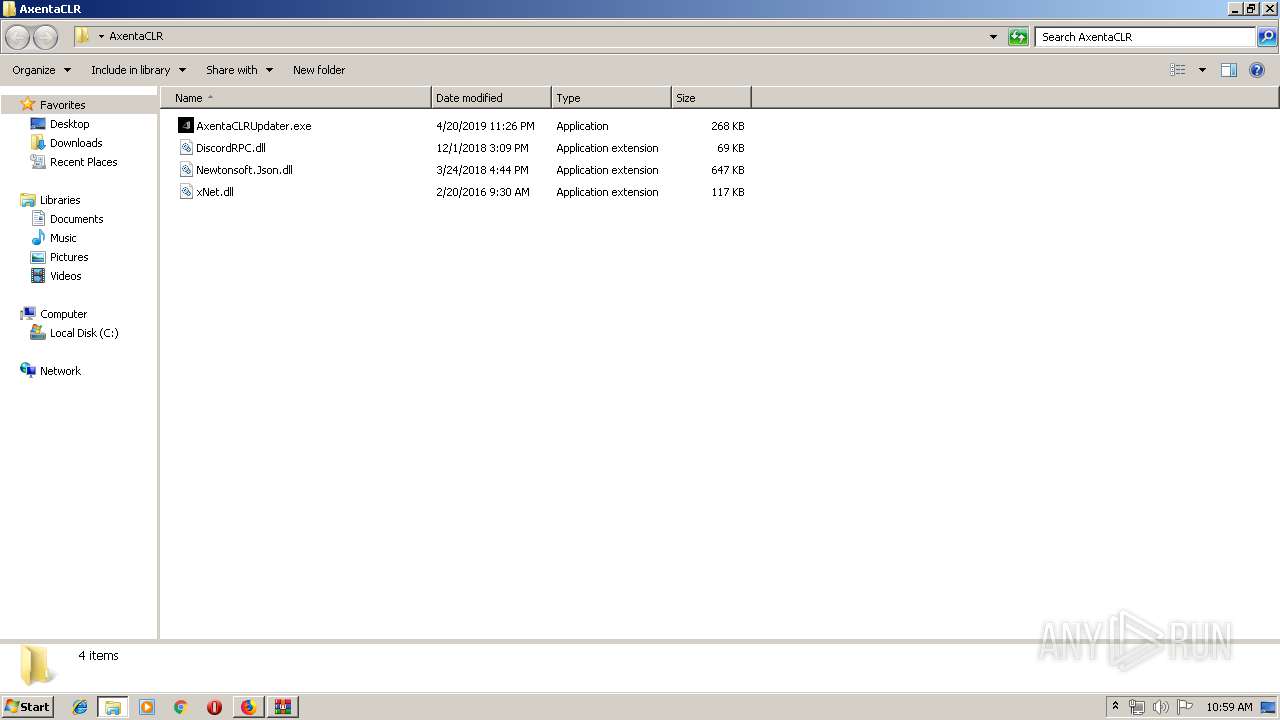
Application was dropped or rewritten from another process
- AxentaCLRUpdater.exe (PID: 3076)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3572)
- AxentaCLRUpdater.exe (PID: 3076)
- explorer.exe (PID: 2036)
Changes settings of System certificates
- AxentaCLRUpdater.exe (PID: 3076)
Starts Visual C# compiler
- sdiagnhost.exe (PID: 2432)
Loads the Task Scheduler COM API
- rundll32.exe (PID: 2504)
SUSPICIOUS
Creates files in the program directory
- firefox.exe (PID: 2824)
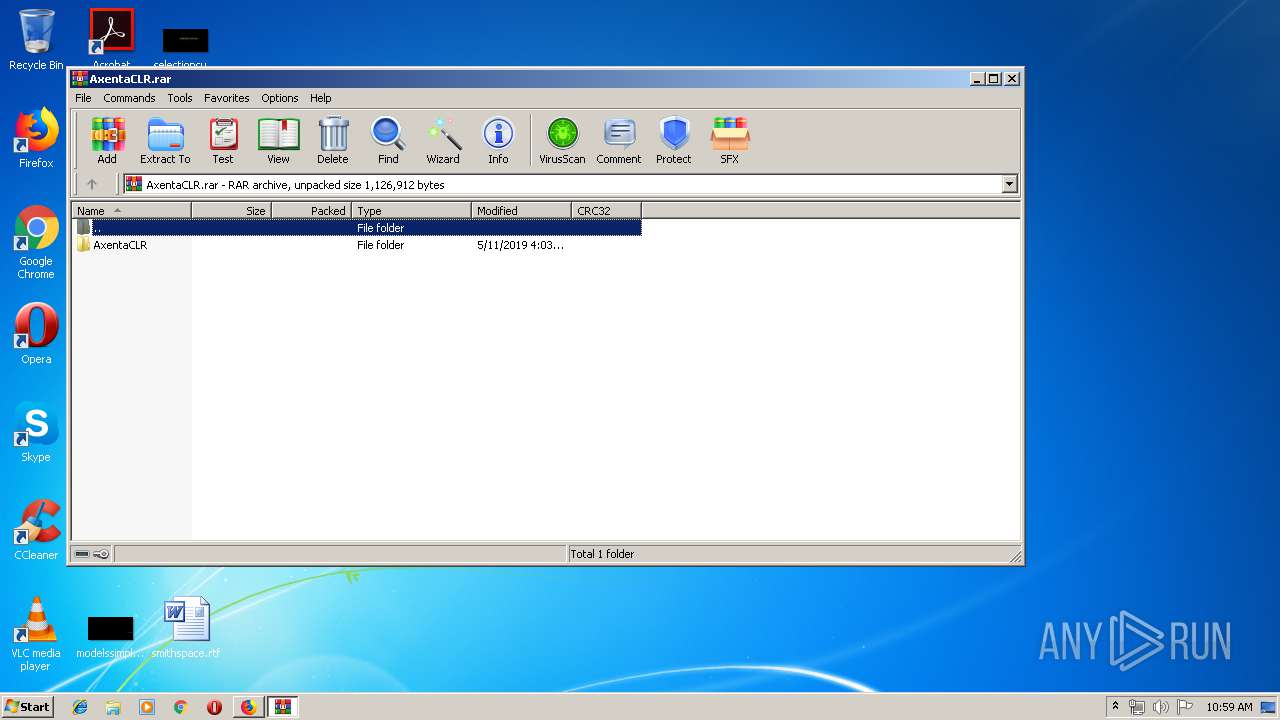
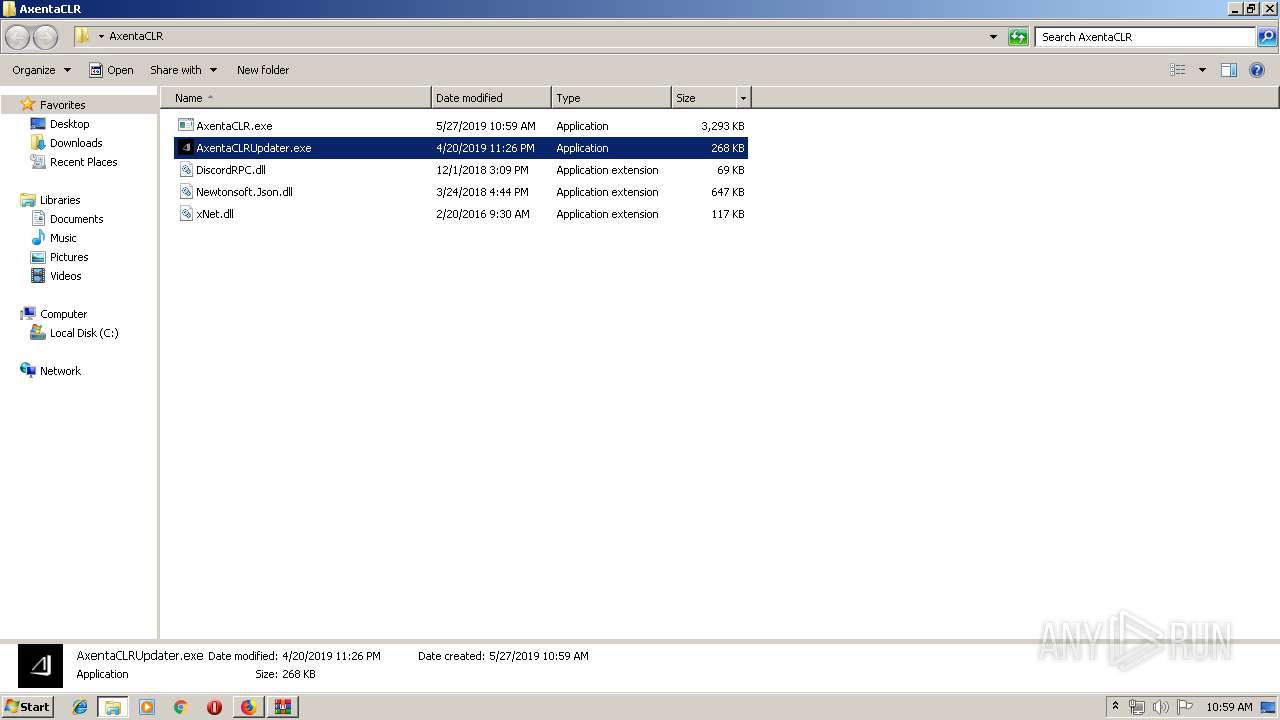
Executable content was dropped or overwritten
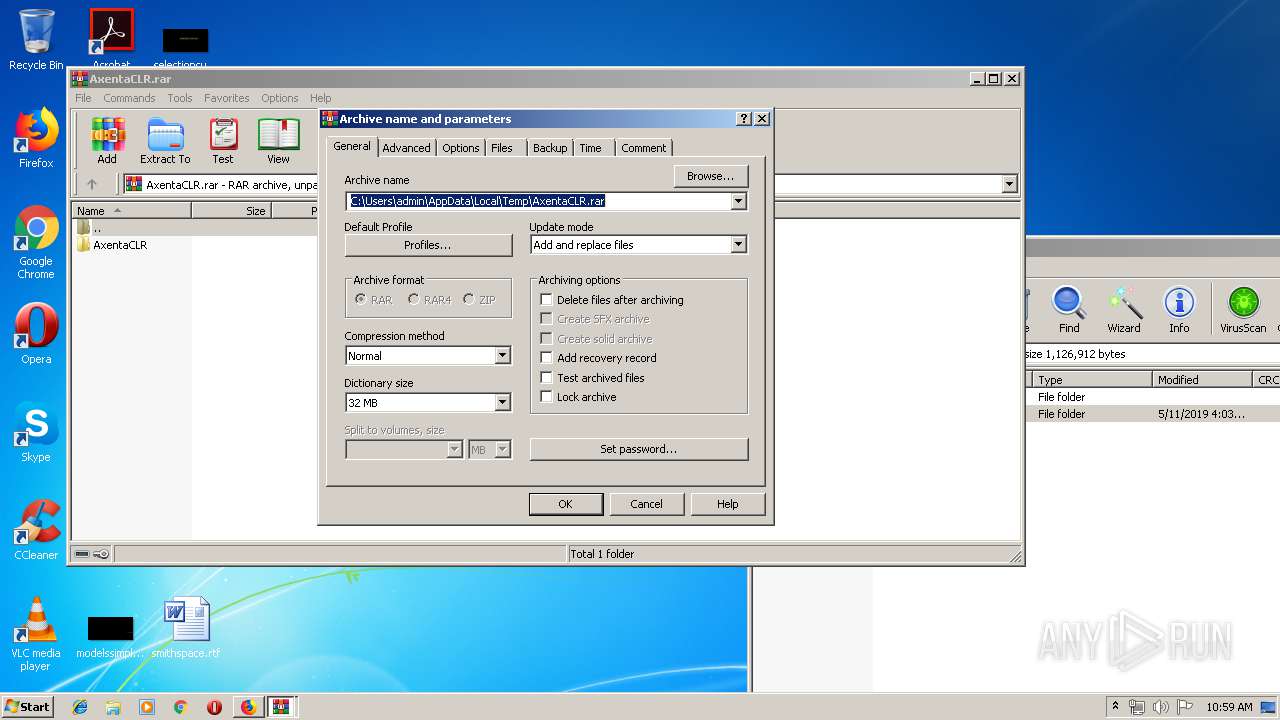
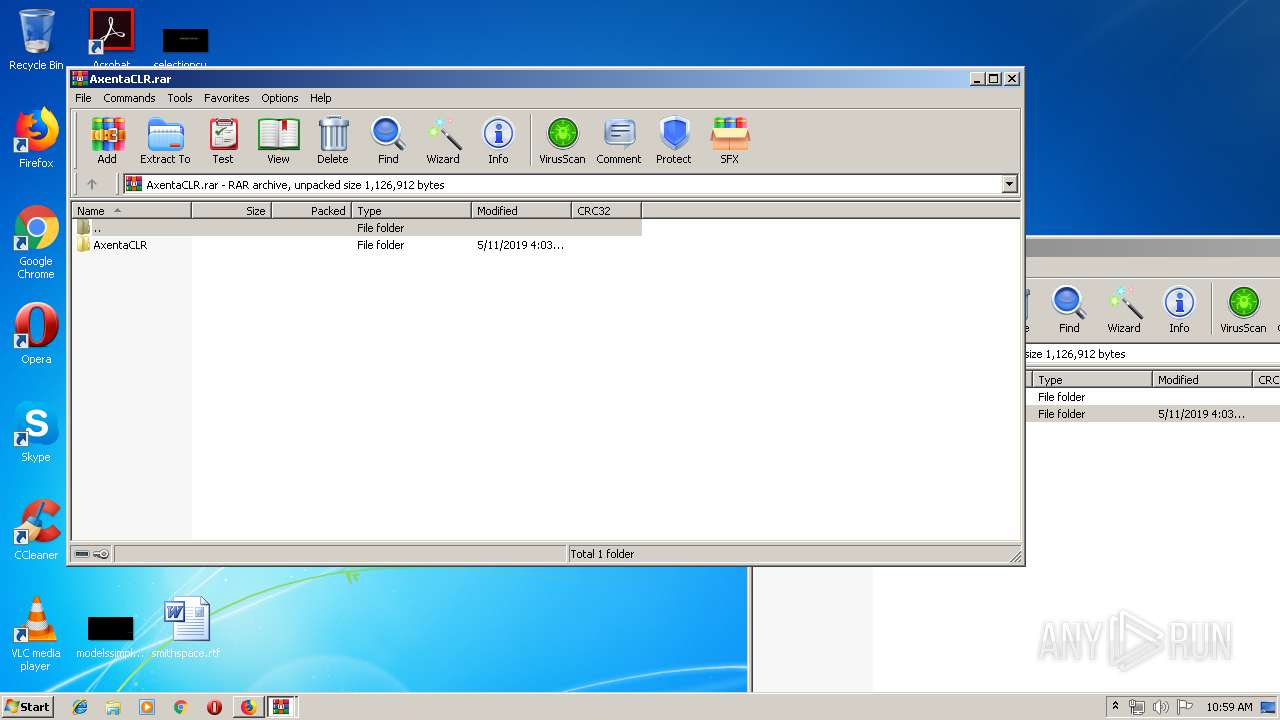
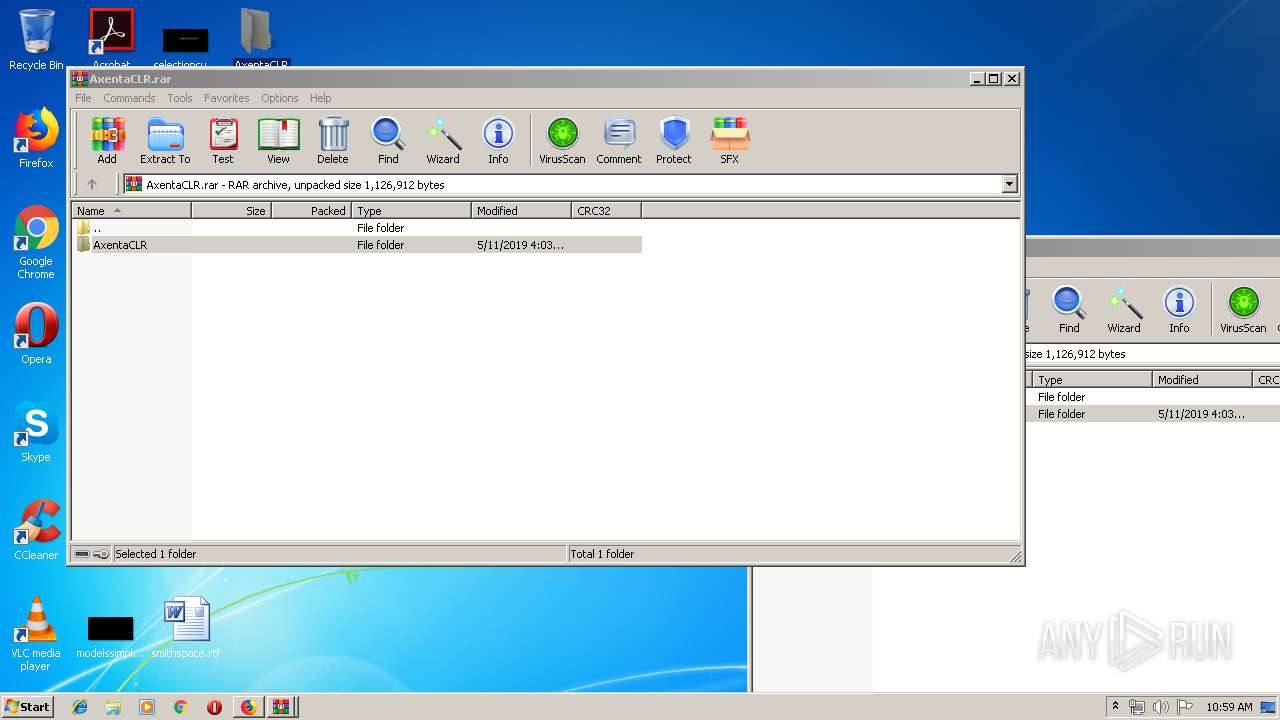
- WinRAR.exe (PID: 3652)
- AxentaCLRUpdater.exe (PID: 3076)
- msdt.exe (PID: 3960)
- firefox.exe (PID: 2824)
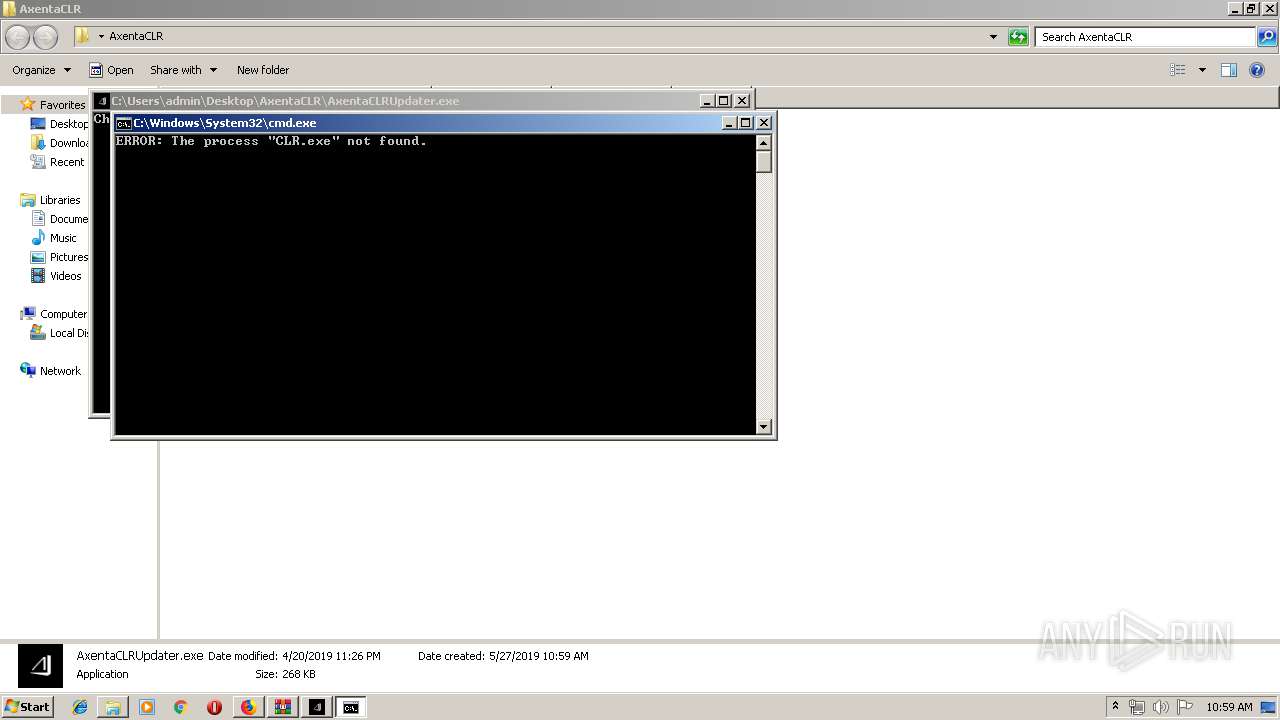
Starts CMD.EXE for commands execution
- AxentaCLRUpdater.exe (PID: 3076)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 3144)
Executed via COM
- sdiagnhost.exe (PID: 2432)
Uses RUNDLL32.EXE to load library
- msdt.exe (PID: 3960)
INFO
Application launched itself
- firefox.exe (PID: 2824)
Reads CPU info
- firefox.exe (PID: 2824)
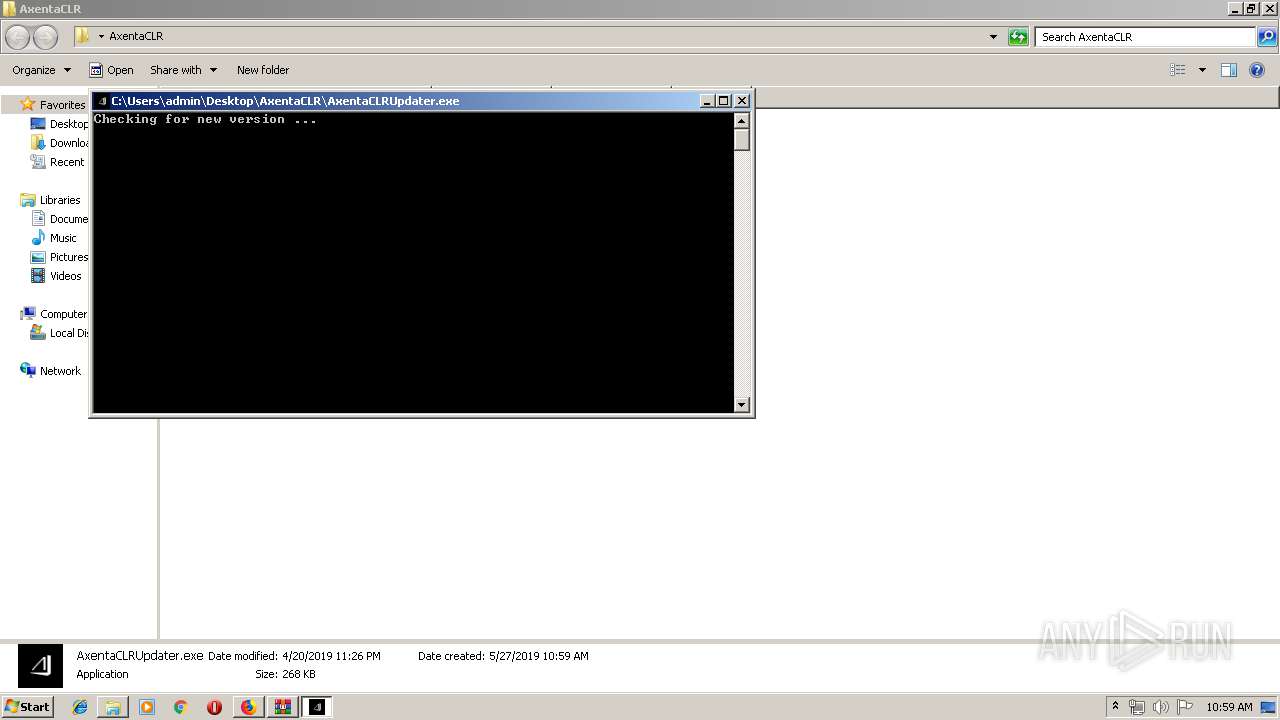
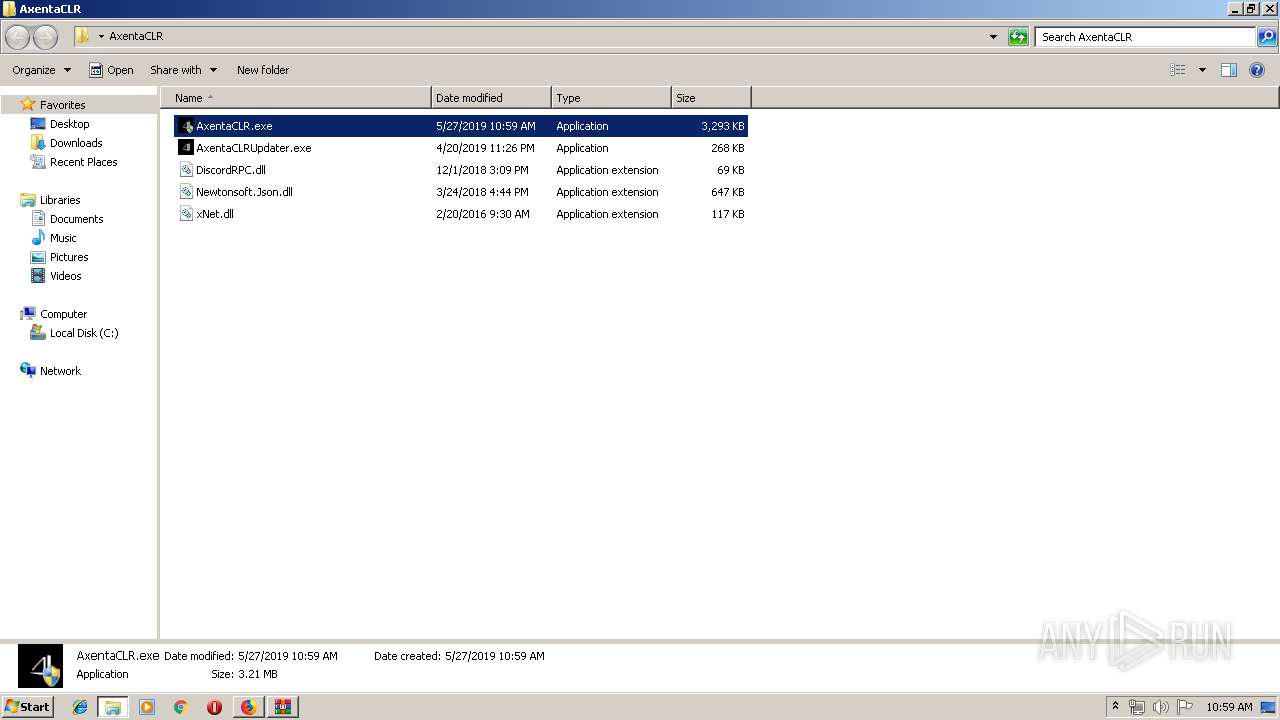
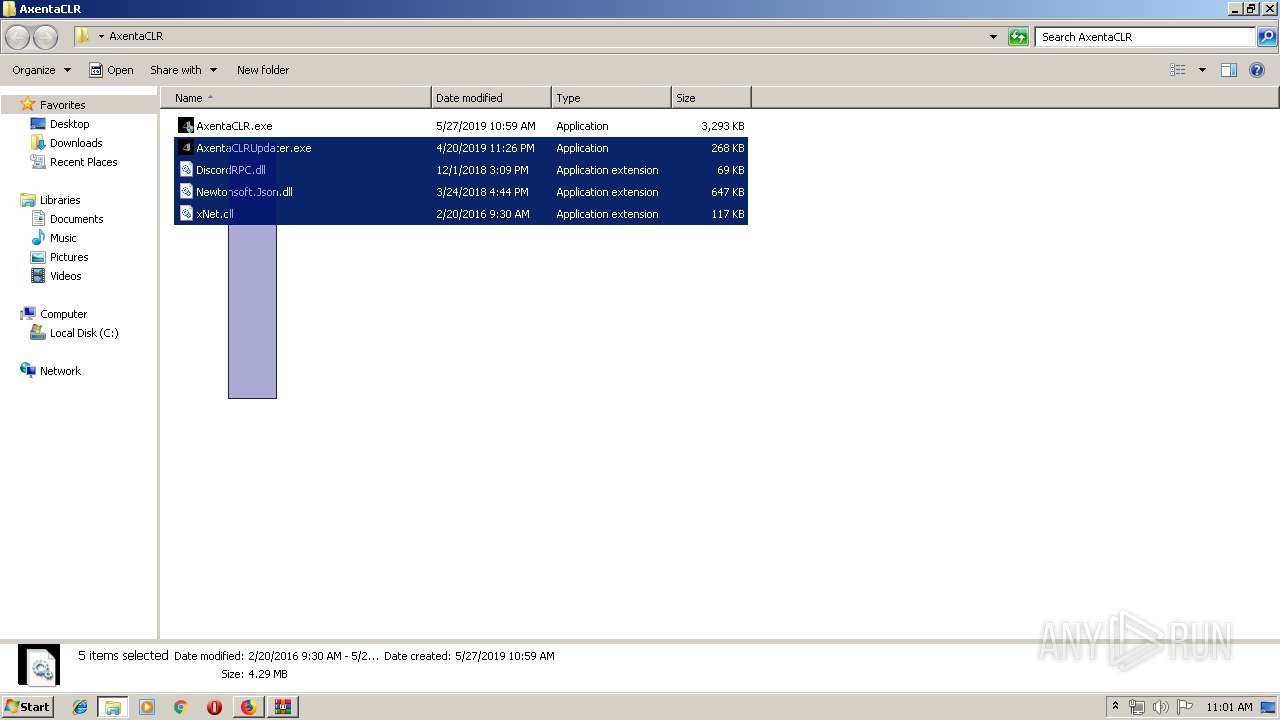
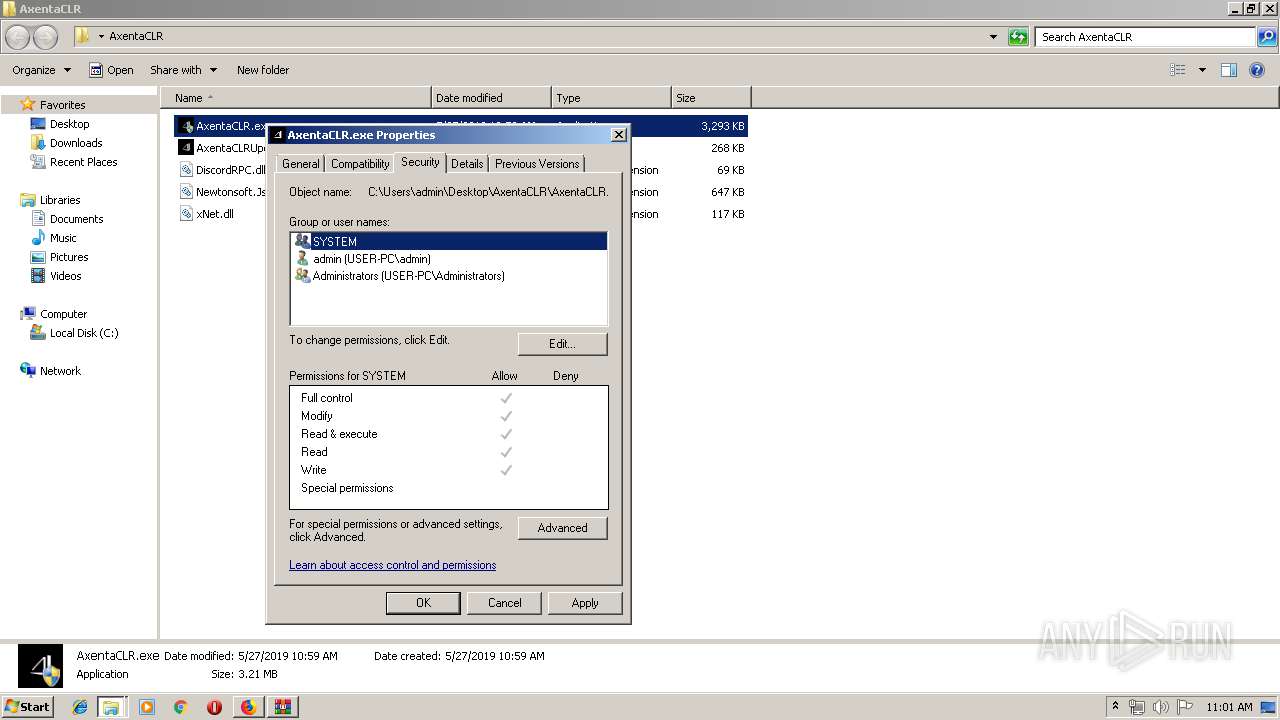
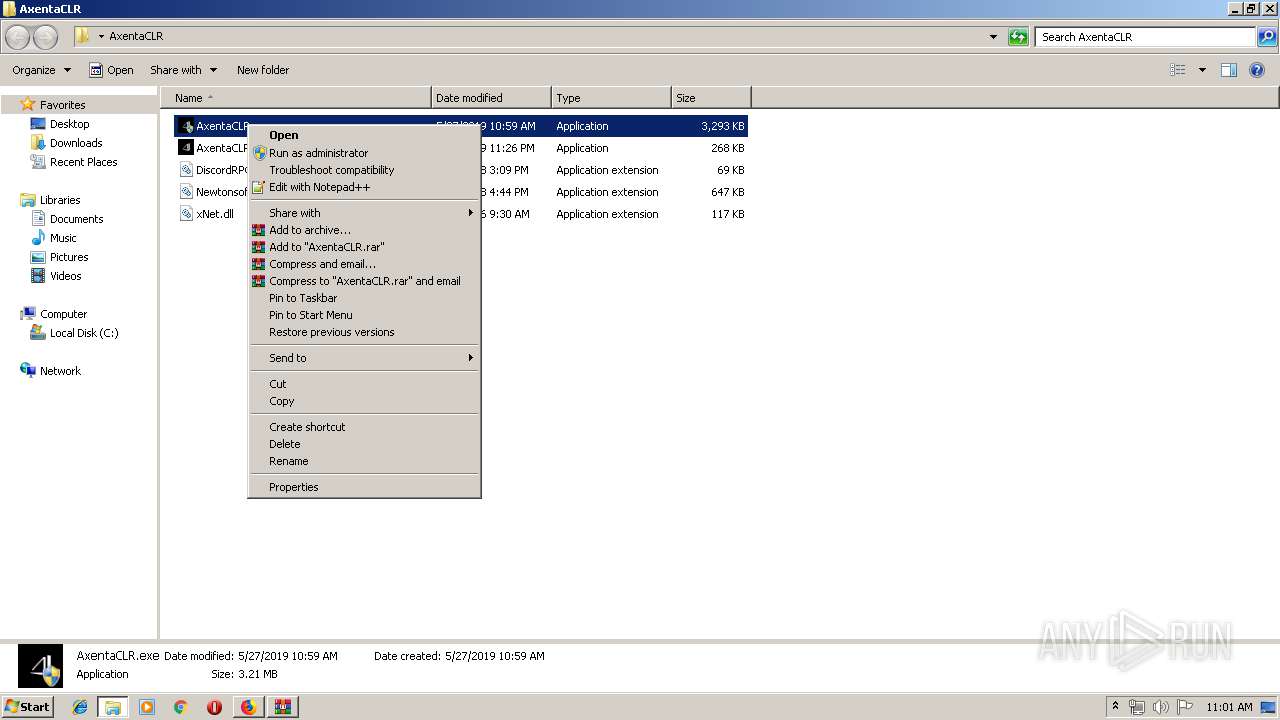
Manual execution by user
- AxentaCLRUpdater.exe (PID: 3076)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 2824)
Reads settings of System Certificates
- firefox.exe (PID: 2824)
Creates files in the user directory
- firefox.exe (PID: 2824)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
59
Monitored processes
22
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | TASKKILL /IM CLR.exe /F | C:\Windows\system32\taskkill.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1172 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES145D.tmp" "c:\Users\admin\AppData\Local\Temp\CSC145C.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 1332 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\quge0oat.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 1592 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES124A.tmp" "c:\Users\admin\AppData\Local\Temp\CSC1249.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2036 | C:\Windows\Explorer.EXE | C:\Windows\explorer.exe | — | — | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Explorer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2068 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2824.20.1865551541\408867389" -childID 3 -isForBrowser -prefsHandle 3476 -prefMapHandle 3480 -prefsLen 5824 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2824 "\\.\pipe\gecko-crash-server-pipe.2824" 3492 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2192 | "C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe" /noconfig /fullpaths @"C:\Users\admin\AppData\Local\Temp\aidwguck.cmdline" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\csc.exe | sdiagnhost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Visual C# Command Line Compiler Exit code: 0 Version: 8.0.50727.4927 (NetFXspW7.050727-4900) Modules
| |||||||||||||||
| 2316 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="2824.13.1675389390\2007500727" -childID 2 -isForBrowser -prefsHandle 1932 -prefMapHandle 2572 -prefsLen 216 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 2824 "\\.\pipe\gecko-crash-server-pipe.2824" 1984 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 2432 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
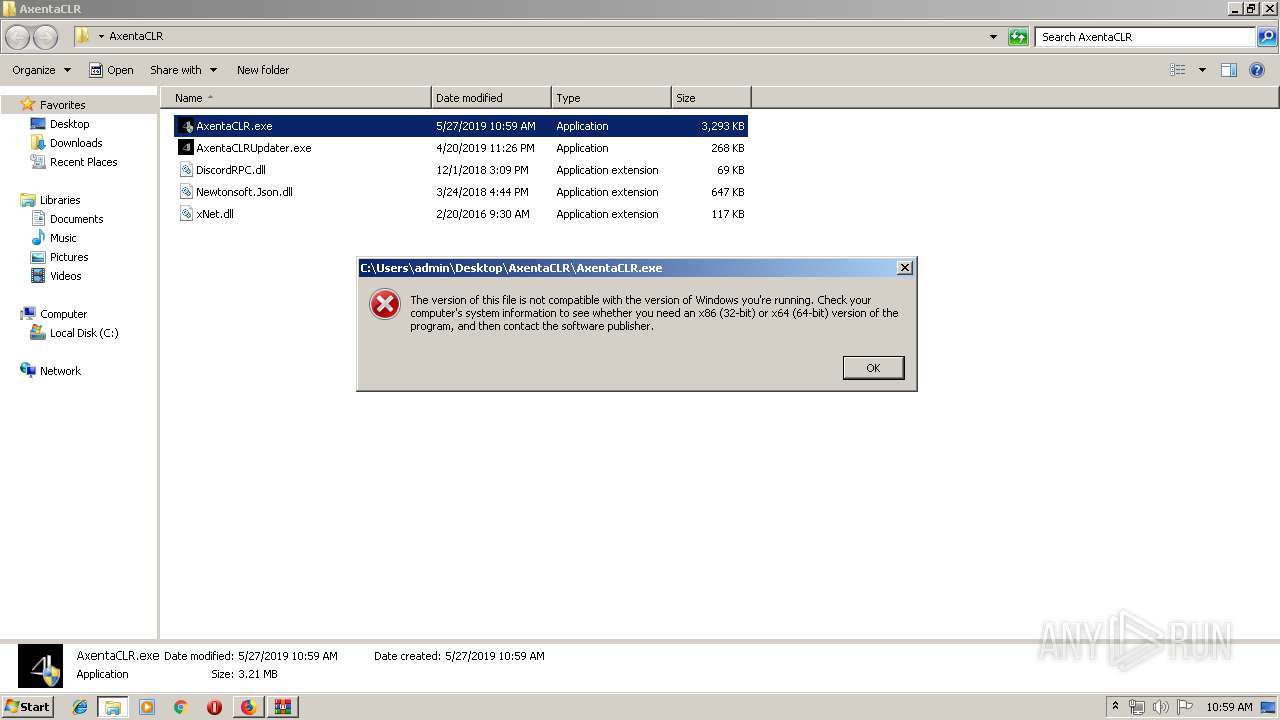
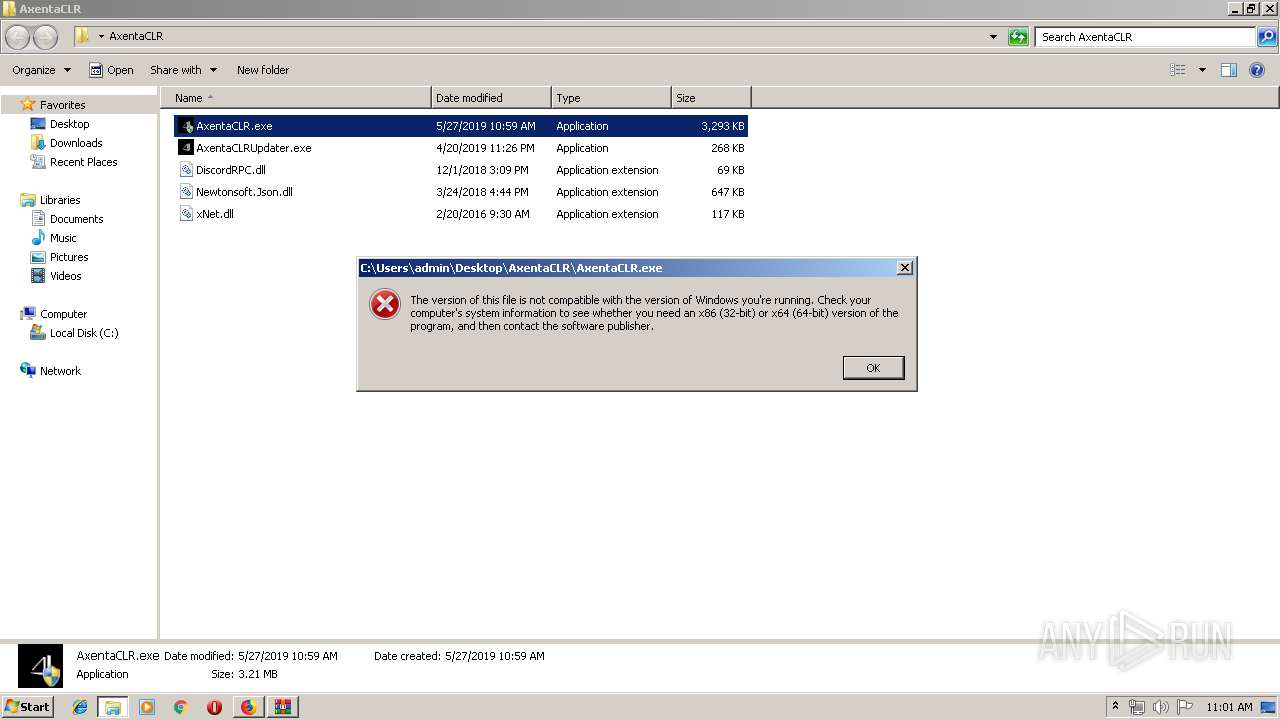
| 2504 | "C:\Windows\System32\rundll32.exe" C:\Windows\system32\pcwutl.dll,CreateAndRunTask -path "C:\Users\admin\Desktop\AxentaCLR\AxentaCLR.exe" | C:\Windows\System32\rundll32.exe | — | msdt.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
5 367
Read events
5 129
Write events
238
Delete events
0
Modification events
| (PID) Process: | (2824) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2824) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2036) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | 308046O0NS4N39PO |
Value: 000000000100000001000000E3160000000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BF000080BFFFFFFFFF008CB691DFDED40100000000 | |||
| (PID) Process: | (2036) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\UserAssist\{CEBFF5CD-ACE2-4F4F-9178-9926F41749EA}\Count |
| Operation: | write | Name: | HRZR_PGYFRFFVBA |
Value: 000000000500000003000000B0CD000003000000020000008F8F00004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D0000002402000000003CE8240201000000000000000000EA7510E82402FCE524025E7C63773CE82402787C6377030000008A018C012C6DD4022CE62402F77C63770100000010E82402847C63777CE6240270E6240288E6240200000000000000000000000078E6240210E82402000000000000000000000000B0E72402B0E7240200000000010000003CE82402B0E72402B2FE6377F270637785FC6377838C4F759A7C62772C6DD402A27E6277F4E7240218000000CCF92402006F62770000000000000000DCE724023C003E003CE82402C34EE5007CE6240200000000D846230000002402D8E62402C4E9240200000088C8000000C8000000C8000000C8000000F20103000000000000000769D8914D030106004000000000B0E92402105307697FEBE4752000000011000000B8452400B045240000000000C4E924020000000064E700001F3C892414E724028291097664E7240218E72402279509760000000024CDDE0240E72402CD94097624CDDE02ECE7240298C8DE02E19409760000000098C8DE02ECE7240248E7240203000000020000008F8F00004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D0000002402000000003CE8240201000000000000000000EA7510E82402FCE524025E7C63773CE82402787C6377030000008A018C012C6DD4022CE62402F77C63770100000010E82402847C63777CE6240270E6240288E6240200000000000000000000000078E6240210E82402000000000000000000000000B0E72402B0E7240200000000010000003CE82402B0E72402B2FE6377F270637785FC6377838C4F759A7C62772C6DD402A27E6277F4E7240218000000CCF92402006F62770000000000000000DCE724023C003E003CE82402C34EE5007CE6240200000000D846230000002402D8E62402C4E9240200000088C8000000C8000000C8000000C8000000F20103000000000000000769D8914D030106004000000000B0E92402105307697FEBE4752000000011000000B8452400B045240000000000C4E924020000000064E700001F3C892414E724028291097664E7240218E72402279509760000000024CDDE0240E72402CD94097624CDDE02ECE7240298C8DE02E19409760000000098C8DE02ECE7240248E7240203000000020000008F8F00004D006900630072006F0073006F00660074002E004100750074006F00470065006E006500720061007400650064002E007B00310035003900360032003100370035002D0037004400460043002D0042003100440037002D0042003000440031002D004500420034004300300038004600460044003700350034007D0000002402000000003CE8240201000000000000000000EA7510E82402FCE524025E7C63773CE82402787C6377030000008A018C012C6DD4022CE62402F77C63770100000010E82402847C63777CE6240270E6240288E6240200000000000000000000000078E6240210E82402000000000000000000000000B0E72402B0E7240200000000010000003CE82402B0E72402B2FE6377F270637785FC6377838C4F759A7C62772C6DD402A27E6277F4E7240218000000CCF92402006F62770000000000000000DCE724023C003E003CE82402C34EE5007CE6240200000000D846230000002402D8E62402C4E9240200000088C8000000C8000000C8000000C8000000F20103000000000000000769D8914D030106004000000000B0E92402105307697FEBE4752000000011000000B8452400B045240000000000C4E924020000000064E700001F3C892414E724028291097664E7240218E72402279509760000000024CDDE0240E72402CD94097624CDDE02ECE7240298C8DE02E19409760000000098C8DE02ECE7240248E72402 | |||
| (PID) Process: | (2824) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2824) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2824) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithProgids |
| Operation: | write | Name: | WinRAR |
Value: | |||
| (PID) Process: | (2036) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithList |
| Operation: | write | Name: | a |
Value: firefox.exe | |||
| (PID) Process: | (2036) explorer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.rar\OpenWithList |
| Operation: | write | Name: | MRUList |
Value: a | |||
| (PID) Process: | (3652) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
Executable files
9
Suspicious files
101
Text files
59
Unknown types
87
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2824 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 2824 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cookies.sqlite-shm | — | |
MD5:— | SHA256:— | |||
| 2824 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | — | |
MD5:— | SHA256:— | |||
| 2824 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | — | |
MD5:— | SHA256:— | |||
| 2824 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cert9.db-journal | — | |
MD5:— | SHA256:— | |||
| 2824 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\cert9.db | sqlite | |
MD5:— | SHA256:— | |||
| 2824 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\safebrowsing-updating\base-track-digest256.sbstore | binary | |
MD5:— | SHA256:— | |||
| 2824 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\urlCache-current.bin | binary | |
MD5:— | SHA256:— | |||
| 2824 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:— | SHA256:— | |||
| 2824 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-child-current.bin | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
34
DNS requests
96
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2824 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2824 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
2824 | firefox.exe | POST | 200 | 172.217.17.67:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
2824 | firefox.exe | POST | 200 | 172.217.17.67:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
2824 | firefox.exe | POST | 200 | 172.217.17.67:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
2824 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
3076 | AxentaCLRUpdater.exe | GET | 200 | 23.52.51.36:80 | http://cert.int-x3.letsencrypt.org/ | NL | der | 1.15 Kb | whitelisted |
2824 | firefox.exe | GET | 200 | 95.101.72.209:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
2824 | firefox.exe | GET | 200 | 95.101.72.209:80 | http://detectportal.firefox.com/success.txt | unknown | text | 8 b | whitelisted |
2824 | firefox.exe | POST | 200 | 172.217.17.67:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2824 | firefox.exe | 95.101.72.209:80 | detectportal.firefox.com | Akamai International B.V. | — | whitelisted |
2824 | firefox.exe | 104.31.88.47:443 | xluq.xyz | Cloudflare Inc | US | shared |
2824 | firefox.exe | 52.85.254.174:443 | snippets.cdn.mozilla.net | Amazon.com, Inc. | US | unknown |
2824 | firefox.exe | 35.165.116.96:443 | aus5.mozilla.org | Amazon.com, Inc. | US | unknown |
2824 | firefox.exe | 52.88.179.171:443 | search.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2824 | firefox.exe | 104.19.198.151:443 | ajax.cloudflare.com | Cloudflare Inc | US | shared |
2824 | firefox.exe | 172.217.17.67:80 | ocsp.pki.goog | Google Inc. | US | whitelisted |
2824 | firefox.exe | 52.25.98.1:443 | shavar.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2824 | firefox.exe | 52.222.167.125:443 | firefox.settings.services.mozilla.com | Amazon.com, Inc. | US | unknown |
2824 | firefox.exe | 13.35.253.97:443 | content-signature.cdn.mozilla.net | — | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
xluq.xyz |
| suspicious |
detectportal.firefox.com |
| whitelisted |
aus5.mozilla.org |
| whitelisted |
search.services.mozilla.com |
| whitelisted |
tiles.services.mozilla.com |
| whitelisted |
snippets.cdn.mozilla.net |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ajax.cloudflare.com |
| whitelisted |
www.google.com |
| malicious |
safebrowsing.googleapis.com |
| whitelisted |
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|