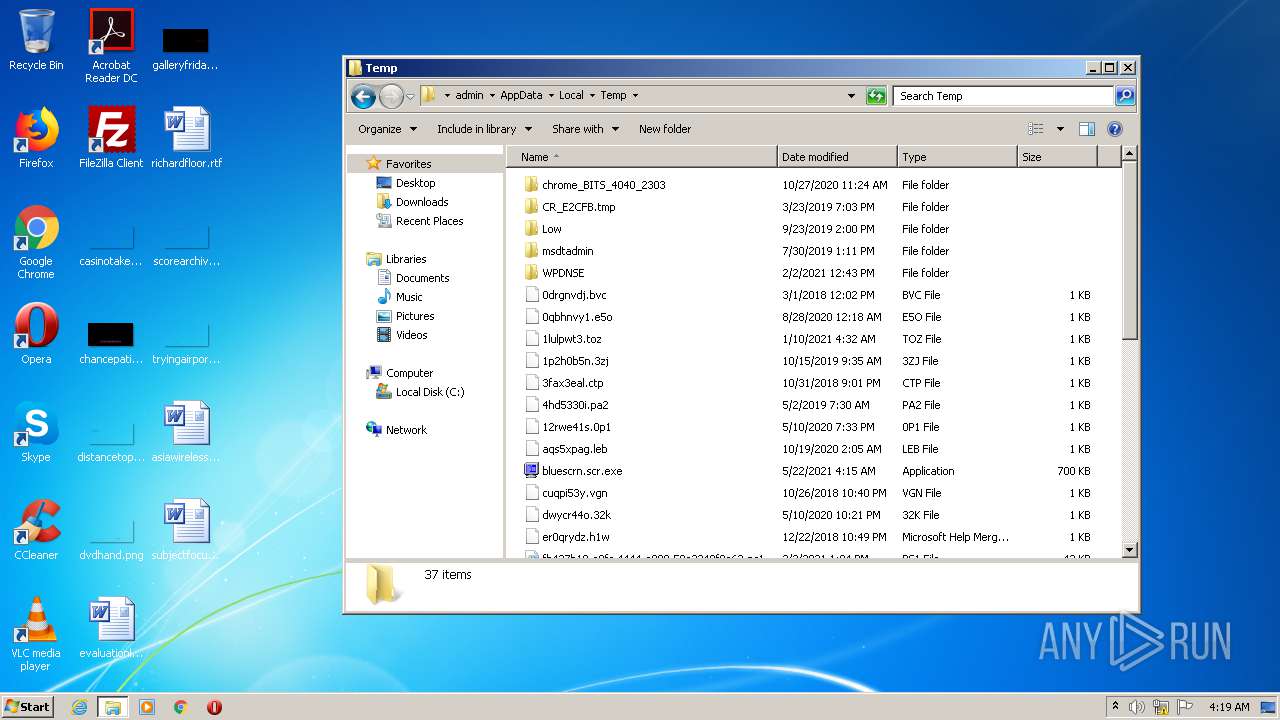
| File name: | bluescrn.scr |
| Full analysis: | https://app.any.run/tasks/67f383c3-50a2-406a-b901-ef5f09d68c23 |
| Verdict: | Malicious activity |
| Analysis date: | May 22, 2021, 03:14:49 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | AC269D8CF5B8FEFCCE0D1FB0BA1122EA |
| SHA1: | A12F5DA02C847ED7F528F0CD517D7CDA21C2E507 |
| SHA256: | DCC79D97307ED95111D9D7641052D9FE702EFBACDA80B29EF63B6050F7F63EDF |
| SSDEEP: | 1536:uVAcyzb7mABGHqFFmS/Tg8J6PpxO9HtYCInndkmVnTA6uvld2XPwdniI:aAcOf1NoY6PqBtm9Pe |
MALICIOUS
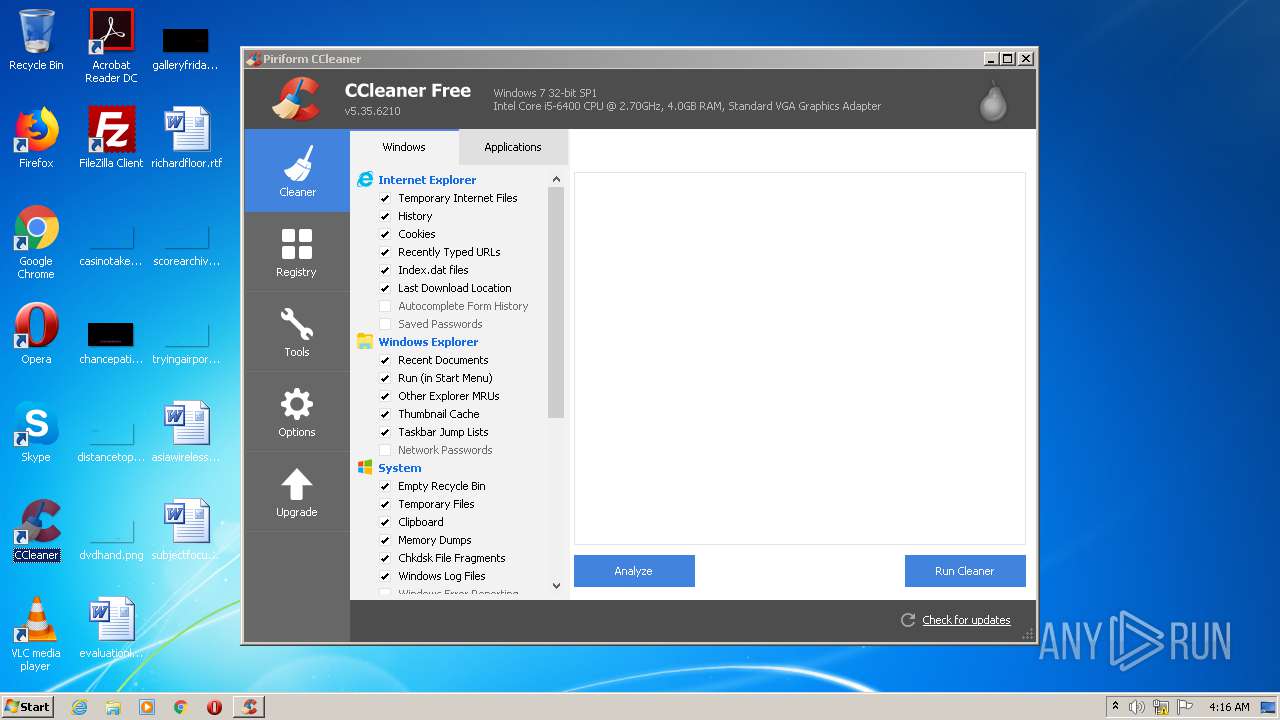
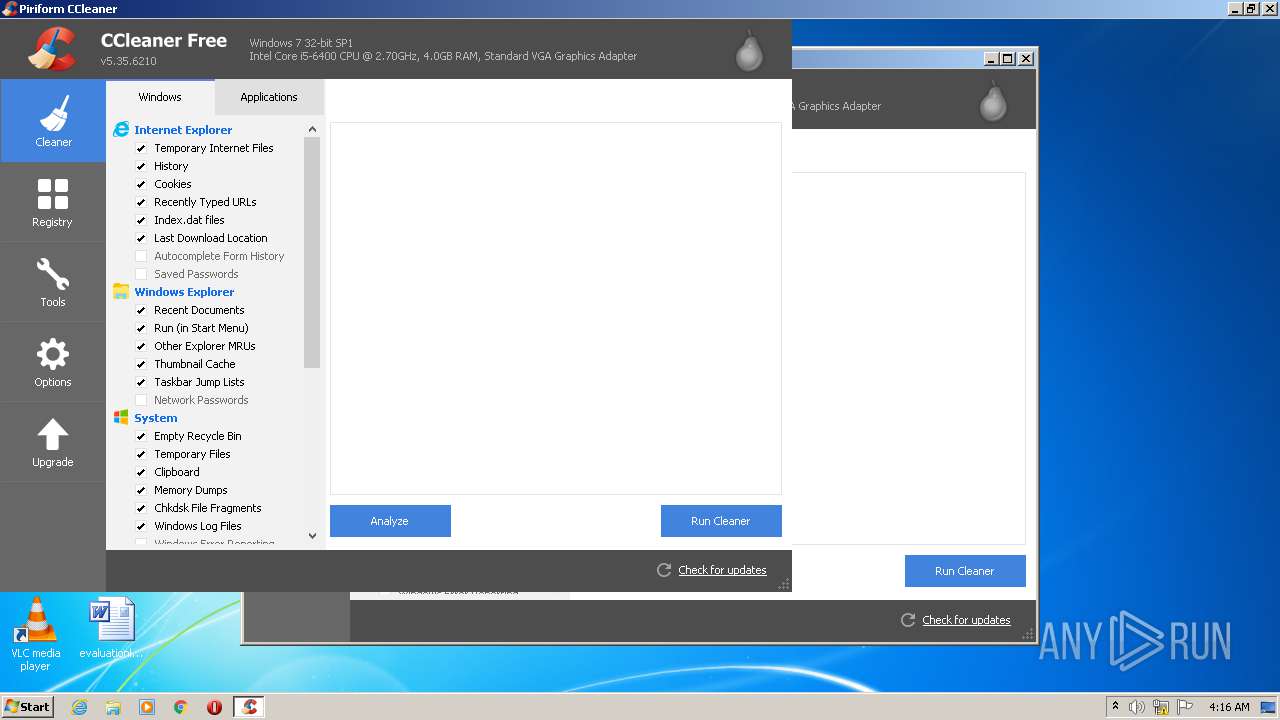
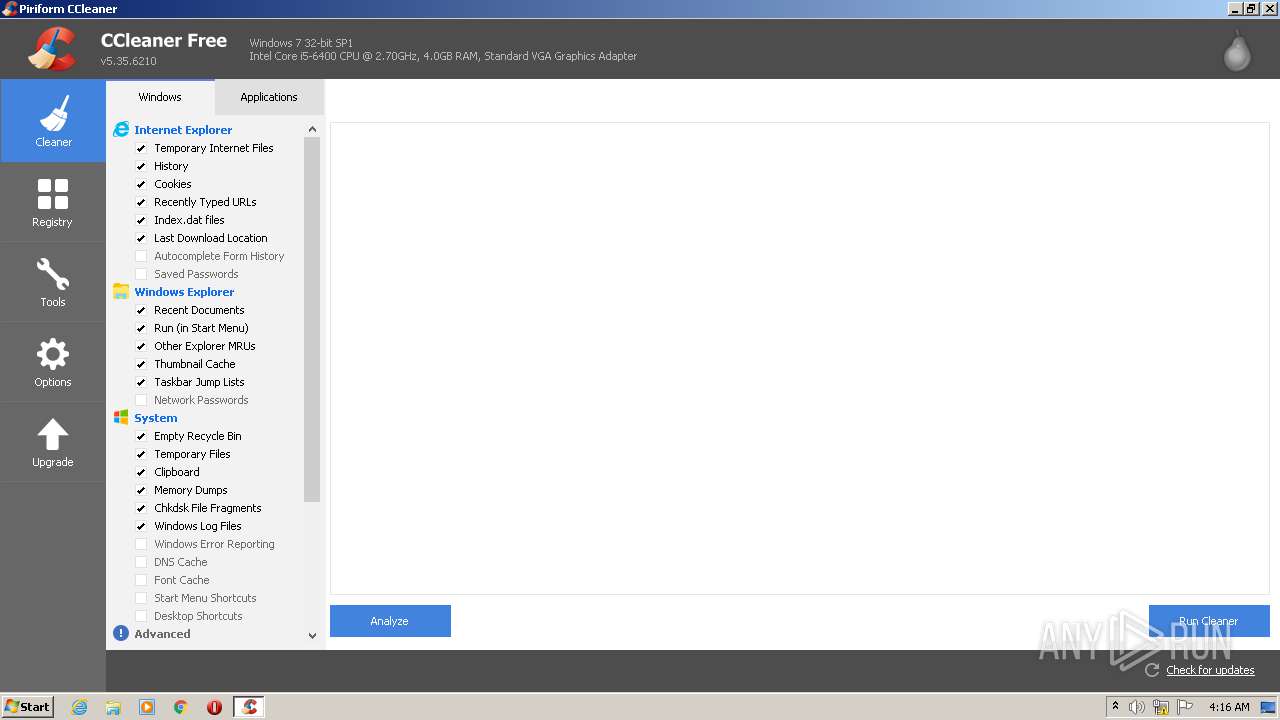
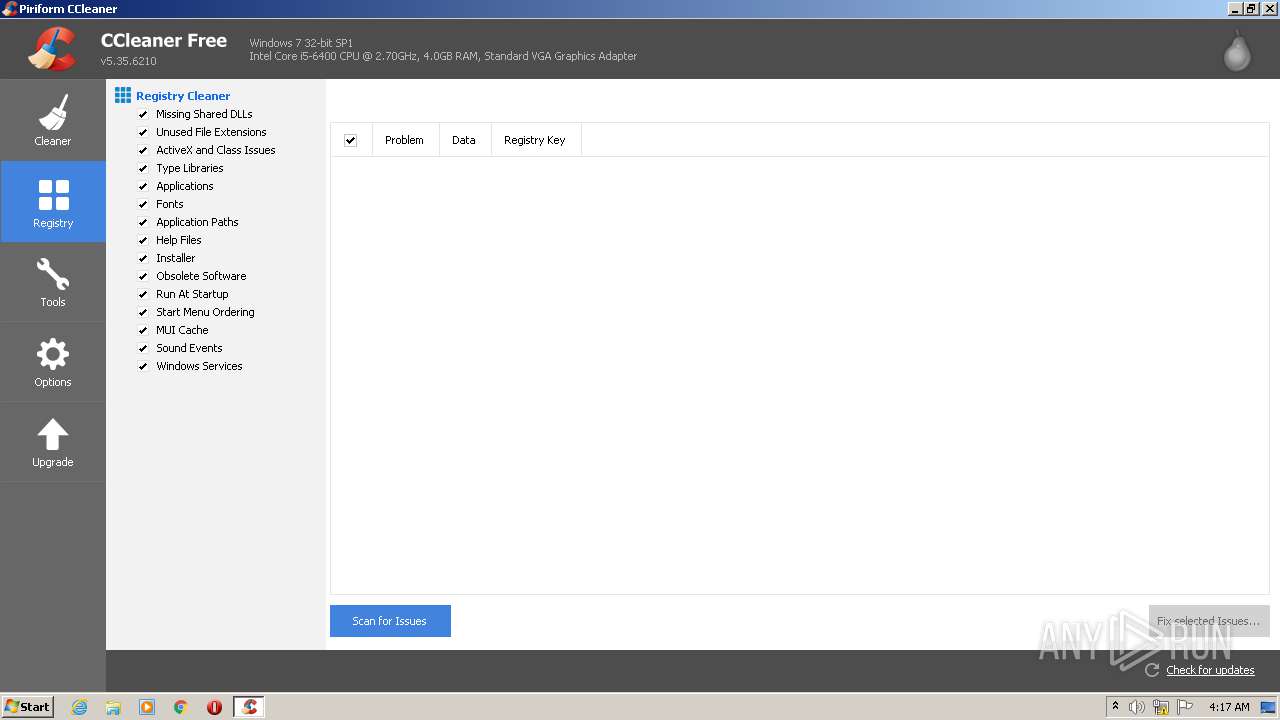
Loads the Task Scheduler COM API
- CCleaner.exe (PID: 3192)
Actions looks like stealing of personal data
- CCleaner.exe (PID: 2572)
Steals credentials from Web Browsers
- CCleaner.exe (PID: 2572)
SUSPICIOUS
Low-level read access rights to disk partition
- CCleaner.exe (PID: 2572)
Reads internet explorer settings
- CCleaner.exe (PID: 2572)
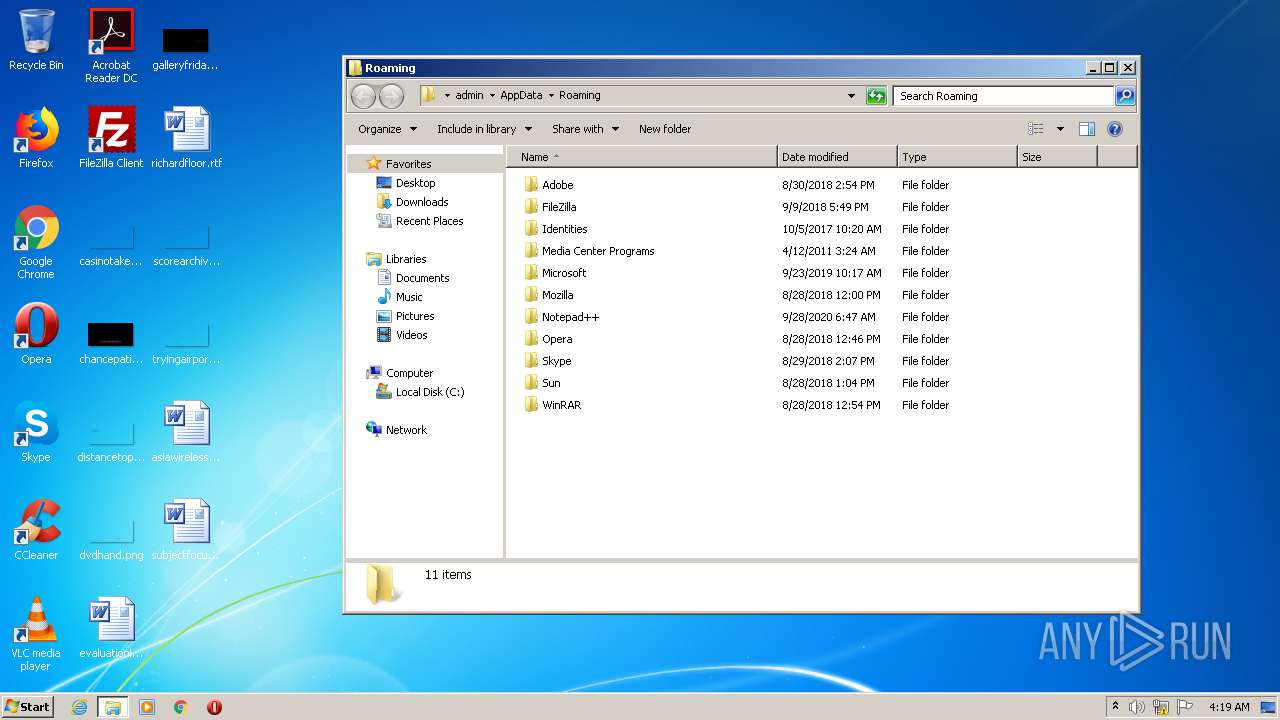
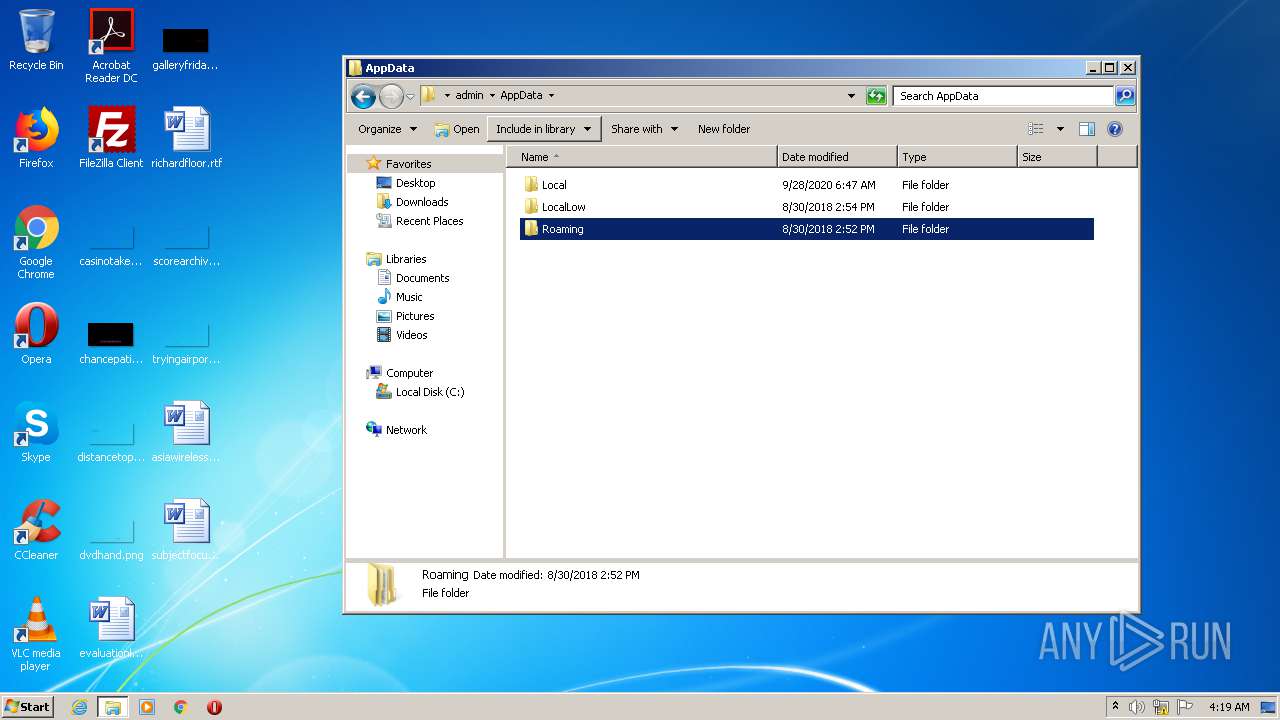
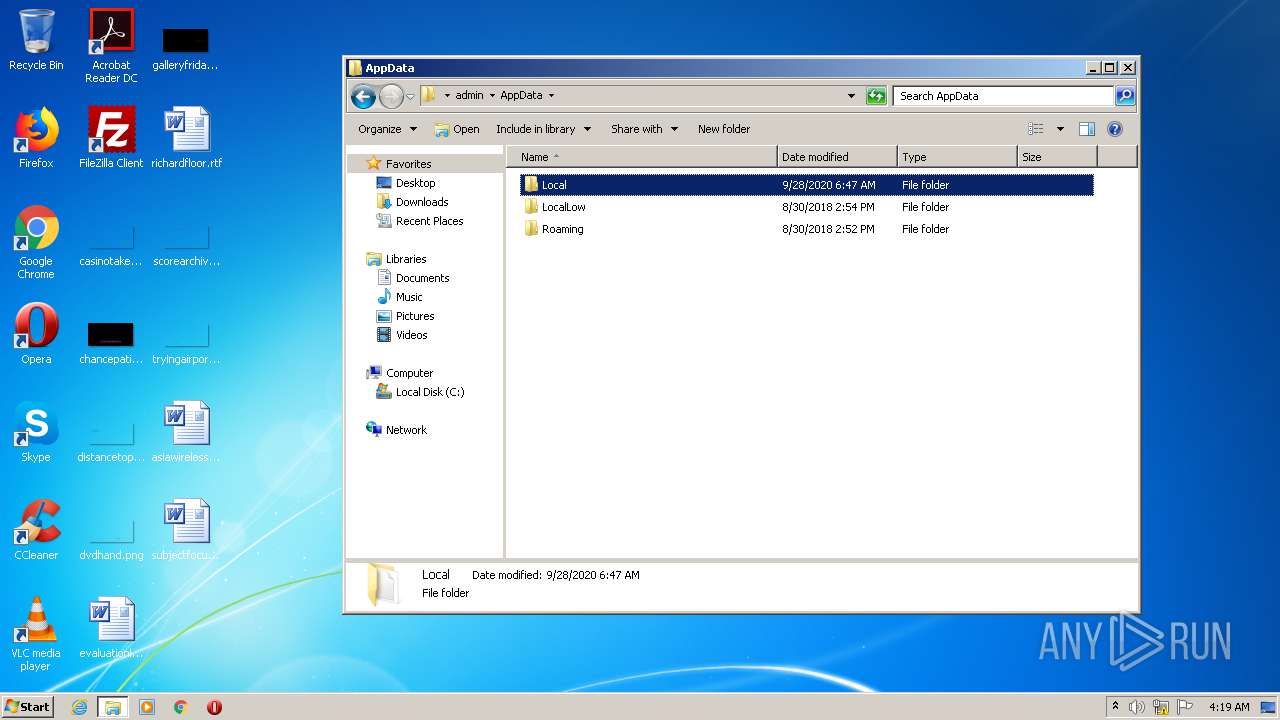
Creates files in the user directory
- CCleaner.exe (PID: 2572)
Executed via Task Scheduler
- CCleaner.exe (PID: 2572)
INFO
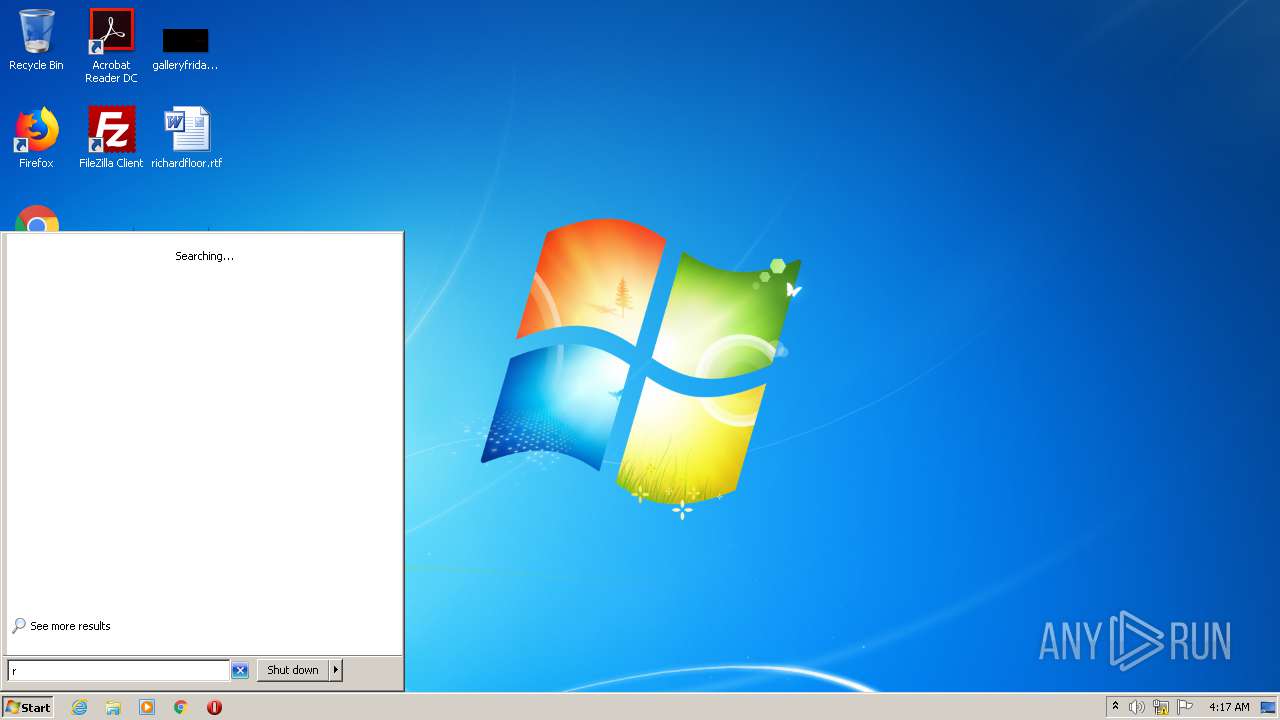
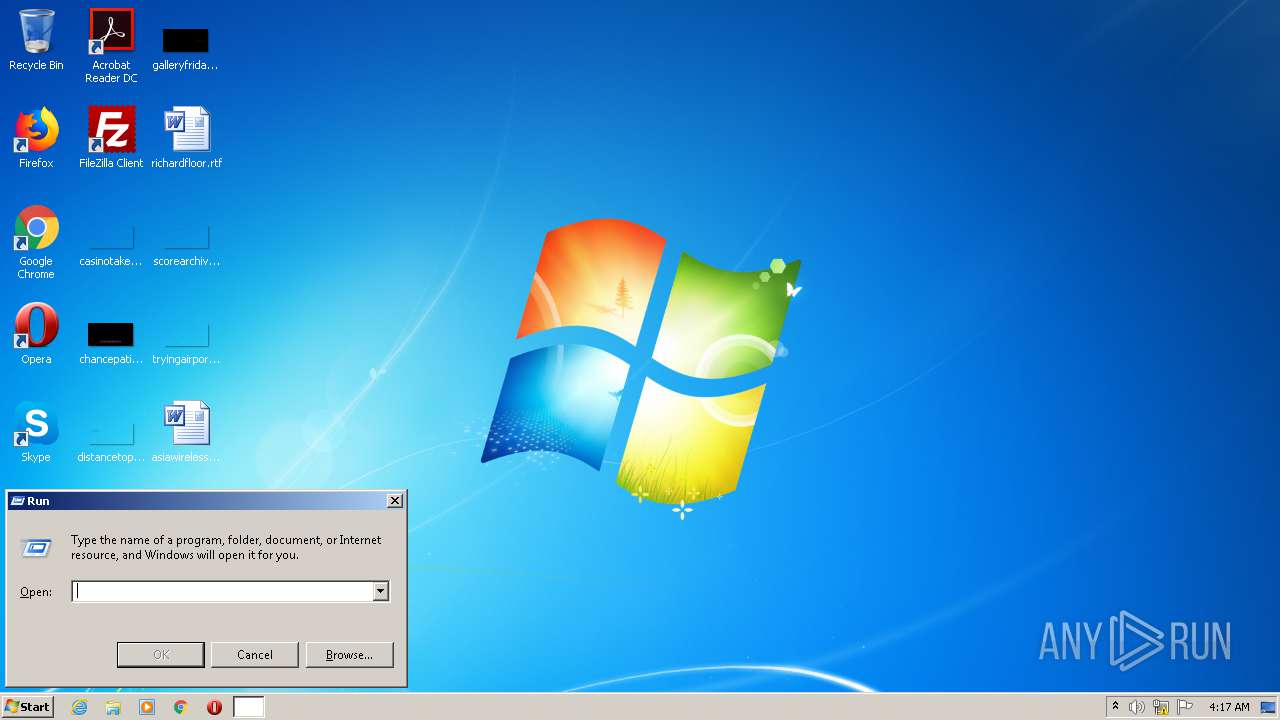
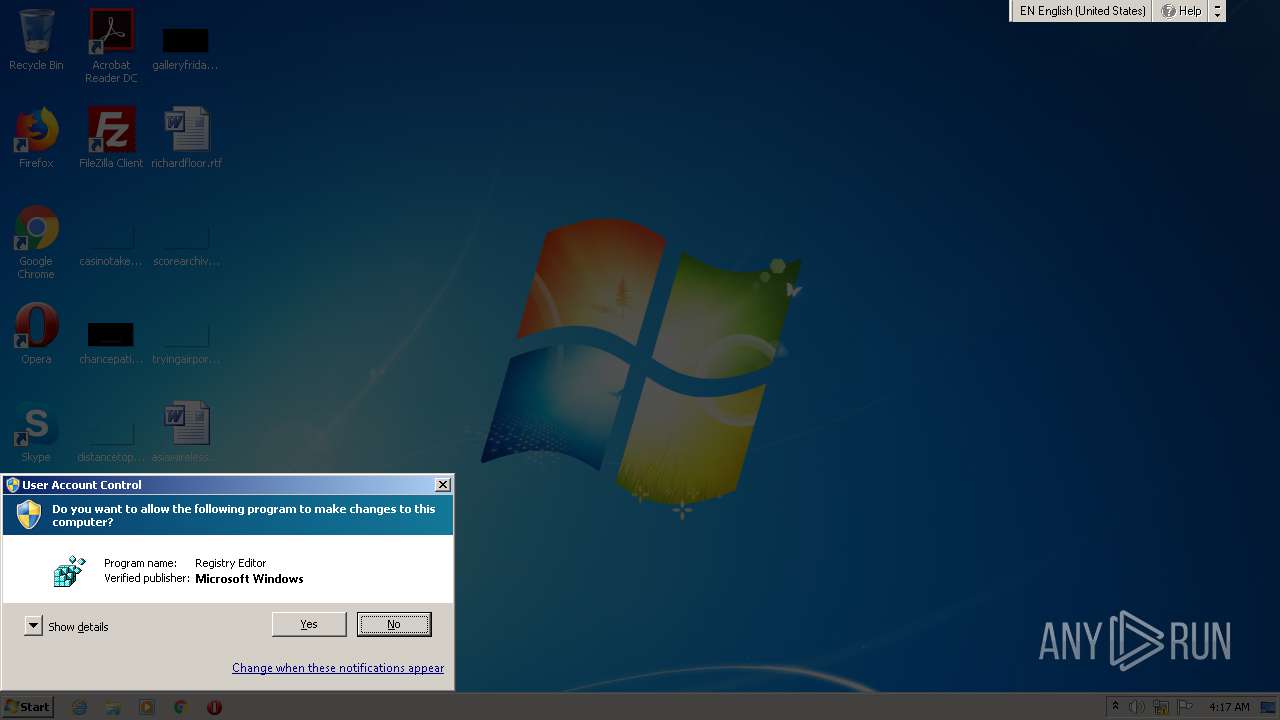
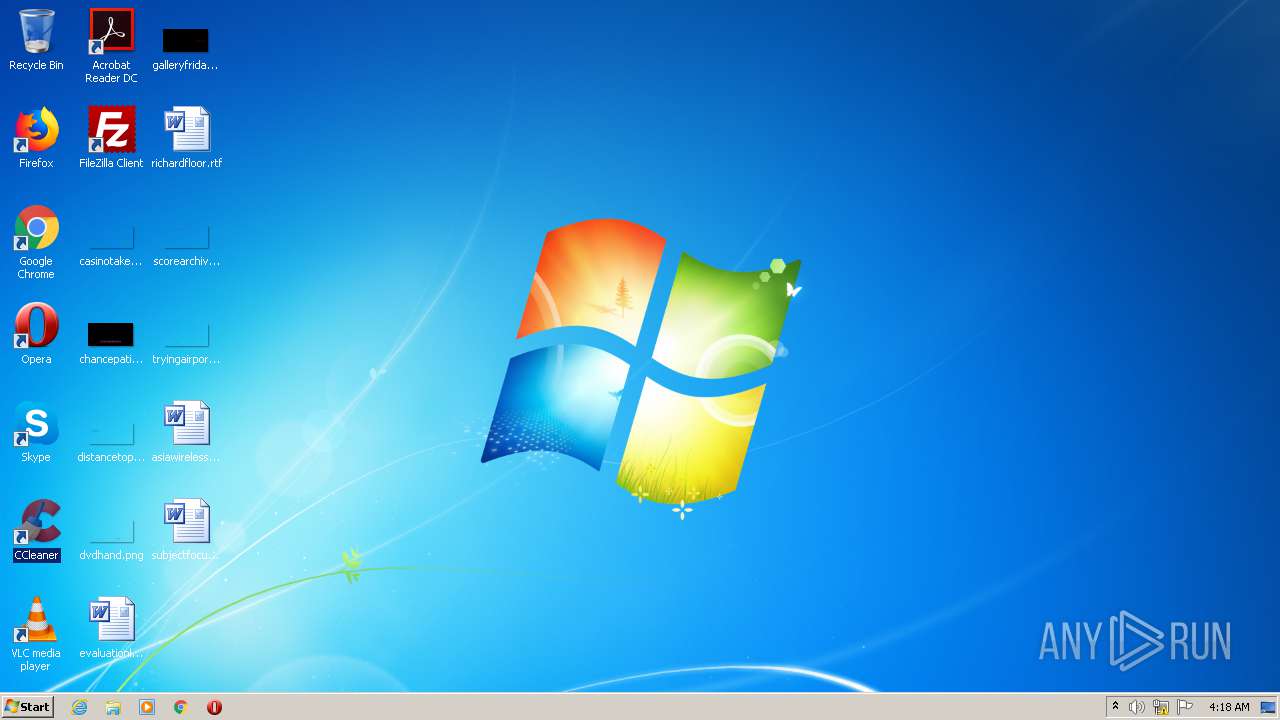
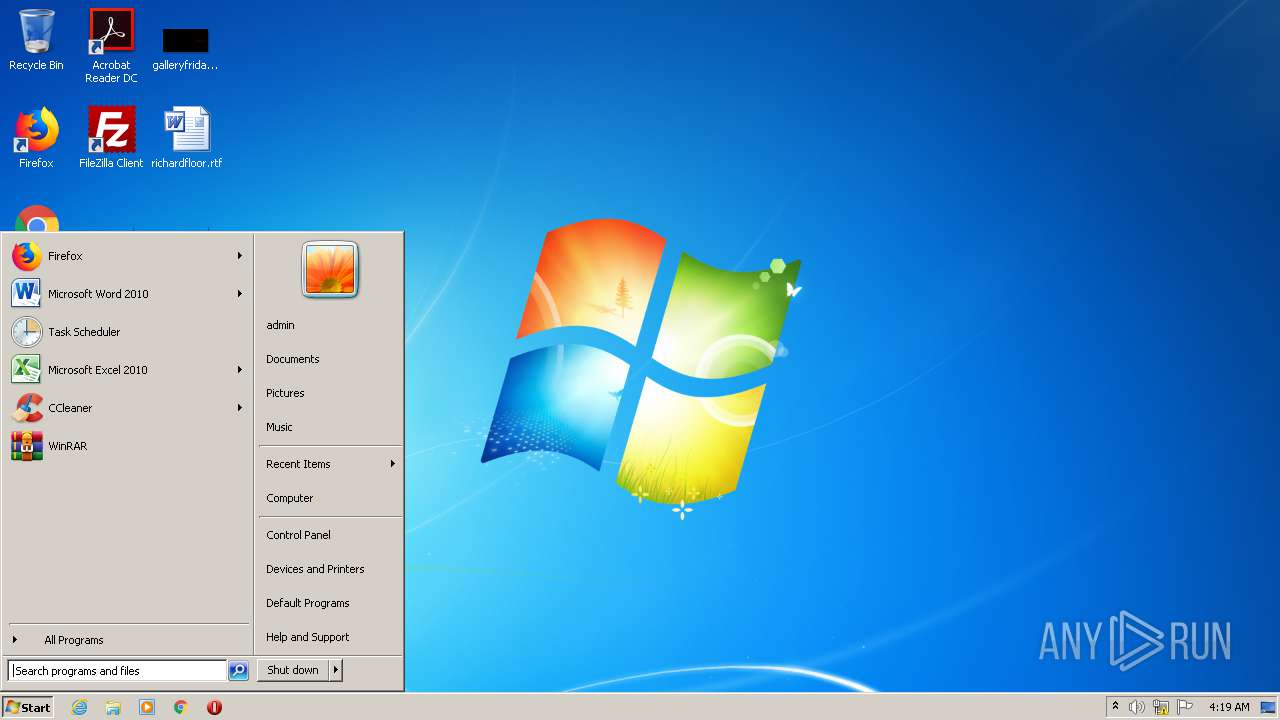
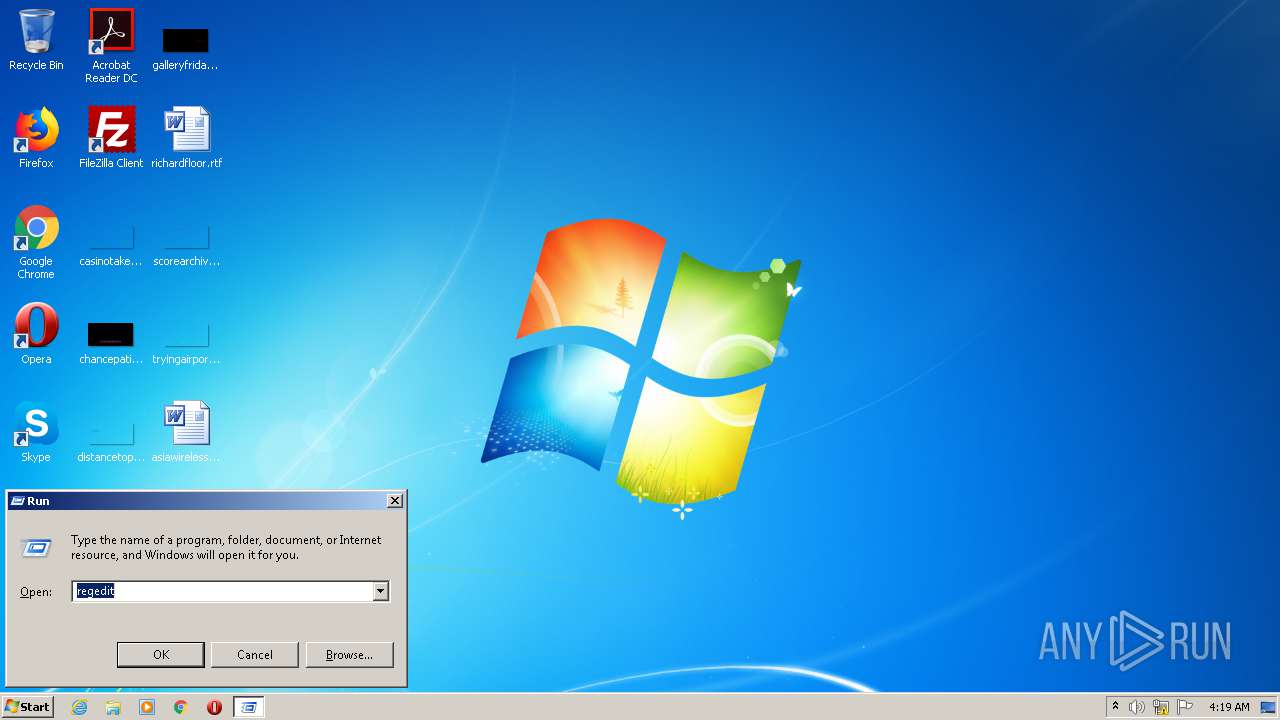
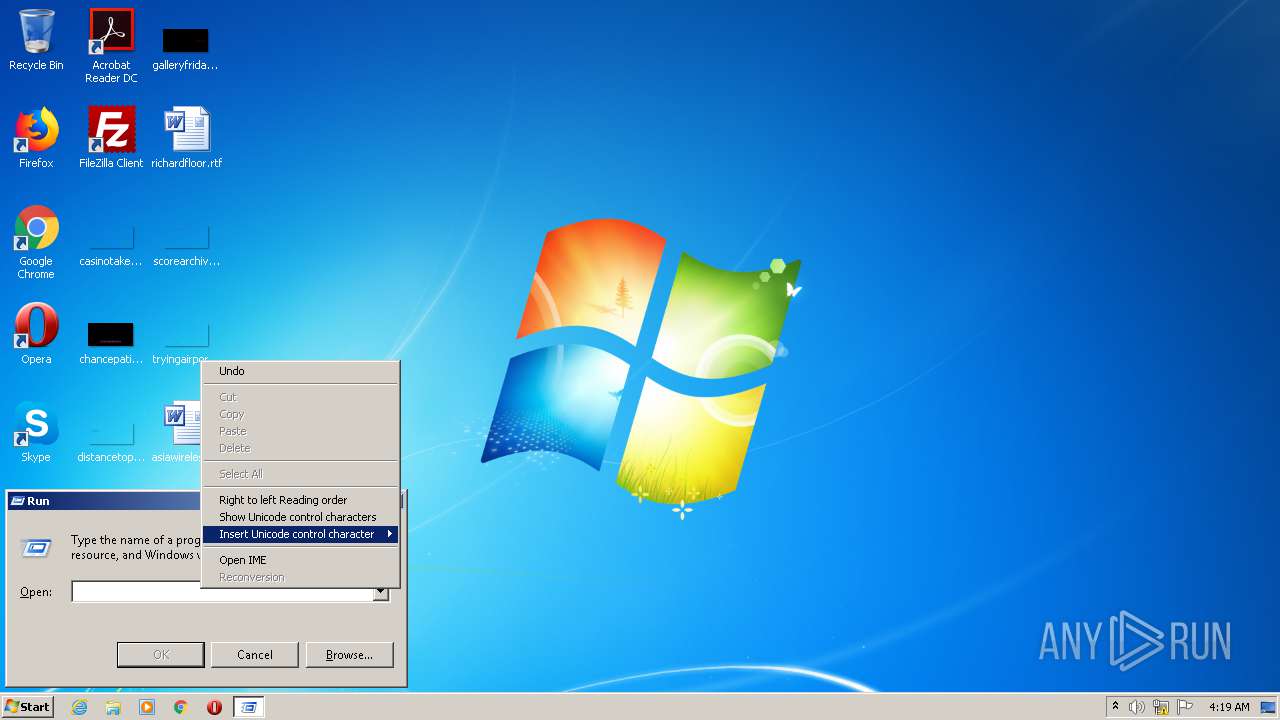
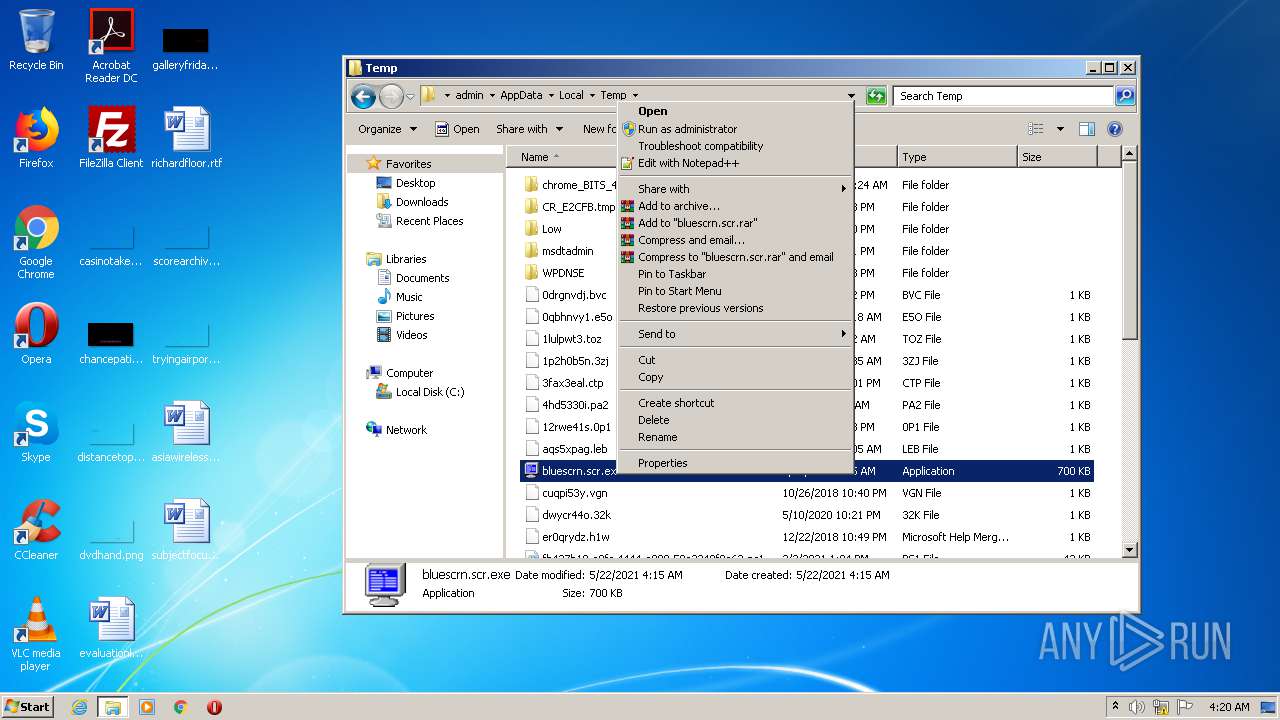
Manual execution by user
- CCleaner.exe (PID: 3192)
- regedit.exe (PID: 2940)
- bluescrn.scr.exe (PID: 2688)
- regedit.exe (PID: 3820)
Reads settings of System Certificates
- CCleaner.exe (PID: 2572)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (35.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (31.7) |
| .scr | | | Windows screen saver (15) |
| .dll | | | Win32 Dynamic Link Library (generic) (7.5) |
| .exe | | | Win32 Executable (generic) (5.1) |
EXIF
EXE
| SpecialBuild: | - |
|---|---|
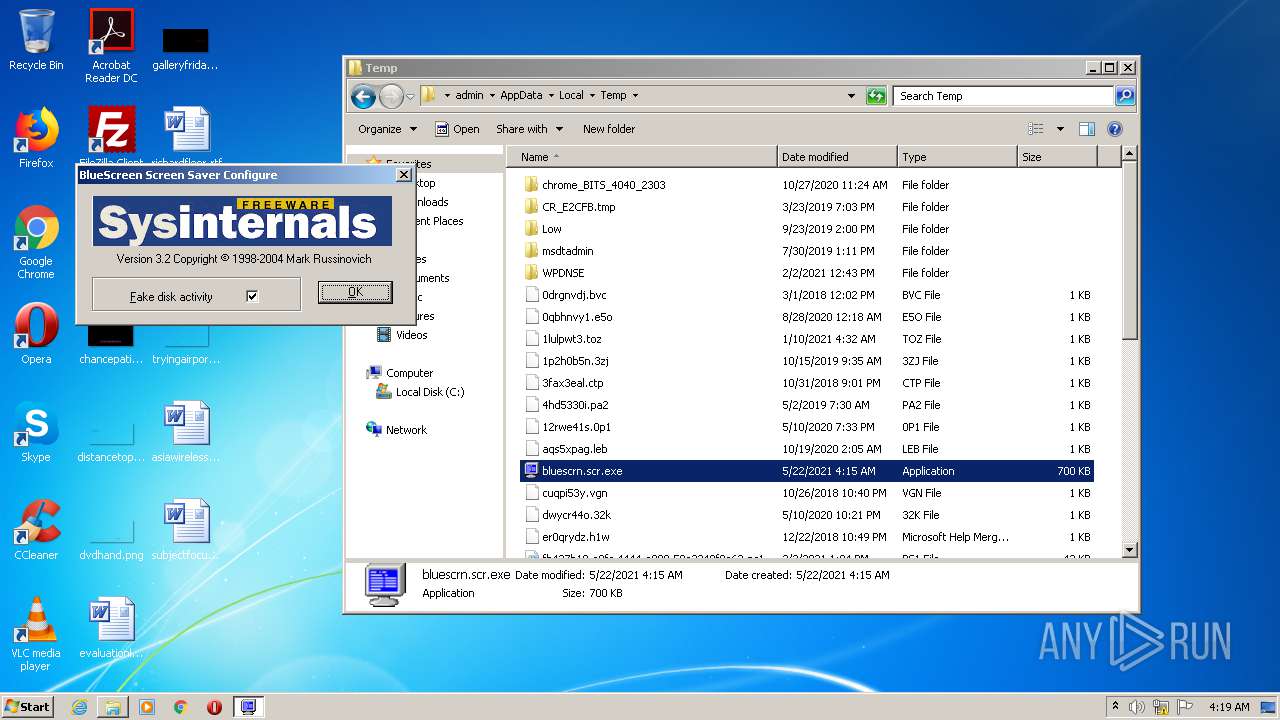
| ProductVersion: | 3.2 |
| ProductName: | Sysinternals Blue Screen |
| PrivateBuild: | - |
| OriginalFileName: | bluescrn.scr |
| LegalTrademarks: | - |
| LegalCopyright: | Copyright © 1998-2004 Mark Russinovich |
| InternalName: | bluescrn |
| FileVersion: | 3.2 |
| FileDescription: | Sysinternals Bluescreen Screen Saver |
| CompanyName: | Sysinternals |
| Comments: | - |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Executable application |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 3.2.0.0 |
| FileVersionNumber: | 3.2.0.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x6ddf |
| UninitializedDataSize: | - |
| InitializedDataSize: | 675840 |
| CodeSize: | 45056 |
| LinkerVersion: | 6 |
| PEType: | PE32 |
| TimeStamp: | 2006:10:12 18:40:08+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 12-Oct-2006 16:40:08 |
| Detected languages: |
|
| Comments: | - |
| CompanyName: | Sysinternals |
| FileDescription: | Sysinternals Bluescreen Screen Saver |
| FileVersion: | 3.2 |
| InternalName: | bluescrn |
| LegalCopyright: | Copyright © 1998-2004 Mark Russinovich |
| LegalTrademarks: | - |
| OriginalFilename: | bluescrn.scr |
| PrivateBuild: | - |
| ProductName: | Sysinternals Blue Screen |
| ProductVersion: | 3.2 |
| SpecialBuild: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000110 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 12-Oct-2006 16:40:08 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000AF26 | 0x0000B000 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.60815 |
.rdata | 0x0000C000 | 0x00001863 | 0x00002000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.53995 |
.data | 0x0000E000 | 0x0001F280 | 0x0001E000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.29126 |
.sxdata | 0x0002E000 | 0x00000004 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_LNK_INFO, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.00656364 |
.rsrc | 0x0002F000 | 0x00081748 | 0x00082000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.75965 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.32005 | 928 | UNKNOWN | English - United States | RT_VERSION |
7 | 2.02548 | 78 | UNKNOWN | English - United States | RT_STRING |
100 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
2003 | 3.60487 | 406 | UNKNOWN | English - United States | RT_DIALOG |
BLUESCRN | 0.0094053 | 153704 | UNKNOWN | English - United States | RT_BITMAP |
FONT | 1.66905 | 49868 | UNKNOWN | English - United States | RT_BITMAP |
LOGO | 2.98674 | 16064 | UNKNOWN | English - United States | RT_BITMAP |
LOGON | 0.0094053 | 153704 | UNKNOWN | English - United States | RT_BITMAP |
LOGON1 | 0.014223 | 153704 | UNKNOWN | English - United States | RT_BITMAP |
PALETTE | 3.37158 | 120 | UNKNOWN | English - United States | RT_BITMAP |
Imports
ADVAPI32.dll |
COMCTL32.dll |
DDRAW.dll |
GDI32.dll |
KERNEL32.dll |
USER32.dll |
WINMM.dll |
comdlg32.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
ScreenSaverConfigureDialog | 1 | 0x000022F0 |
ScreenSaverProc | 2 | 0x00002060 |
Total processes
49
Monitored processes
6
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
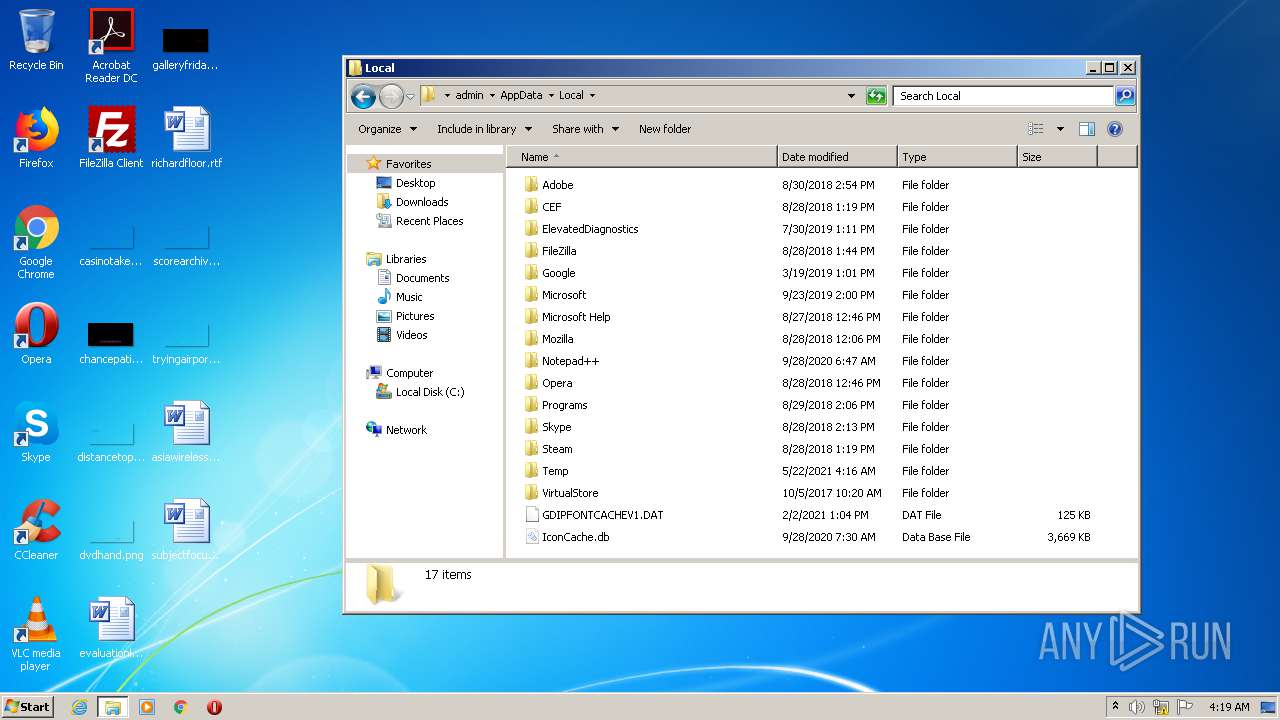
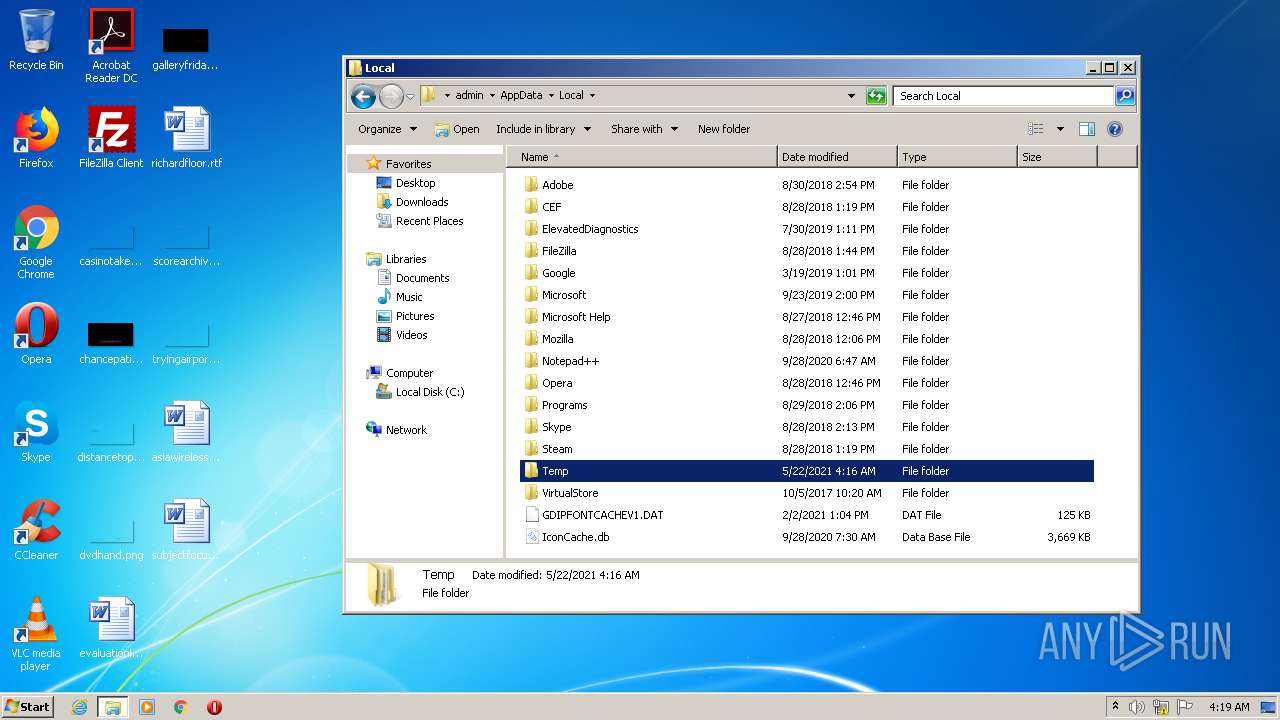
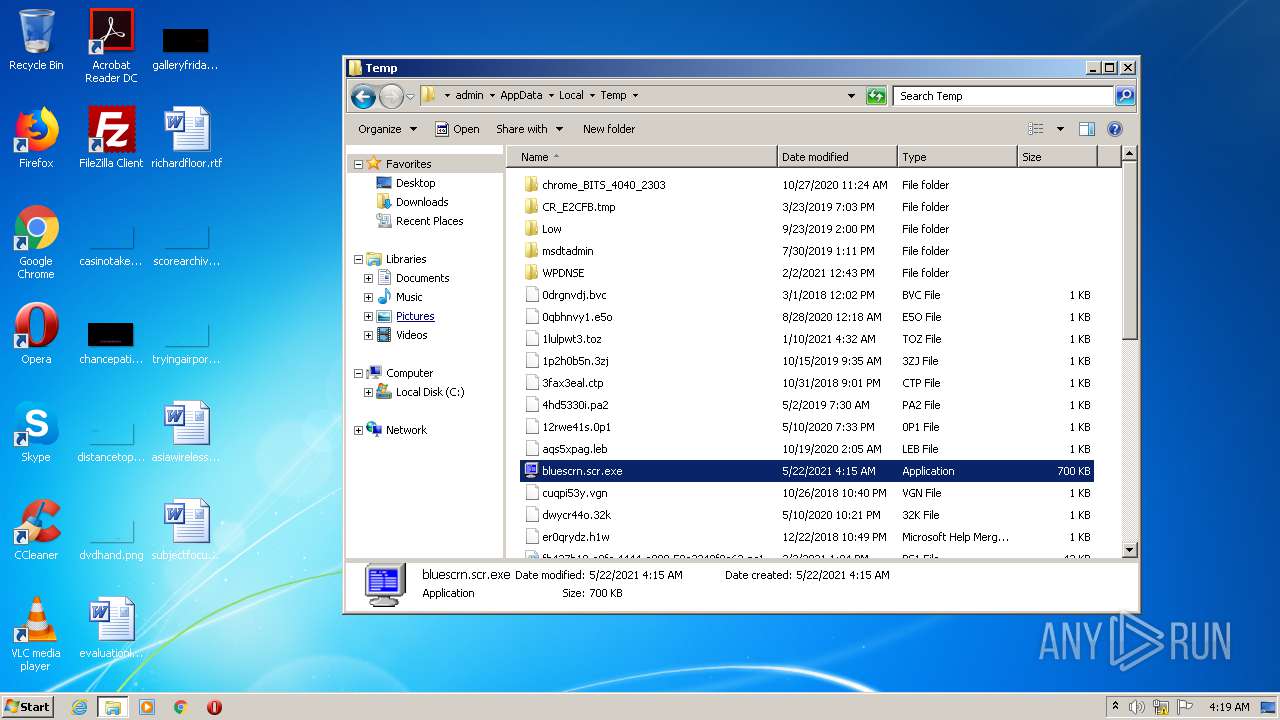
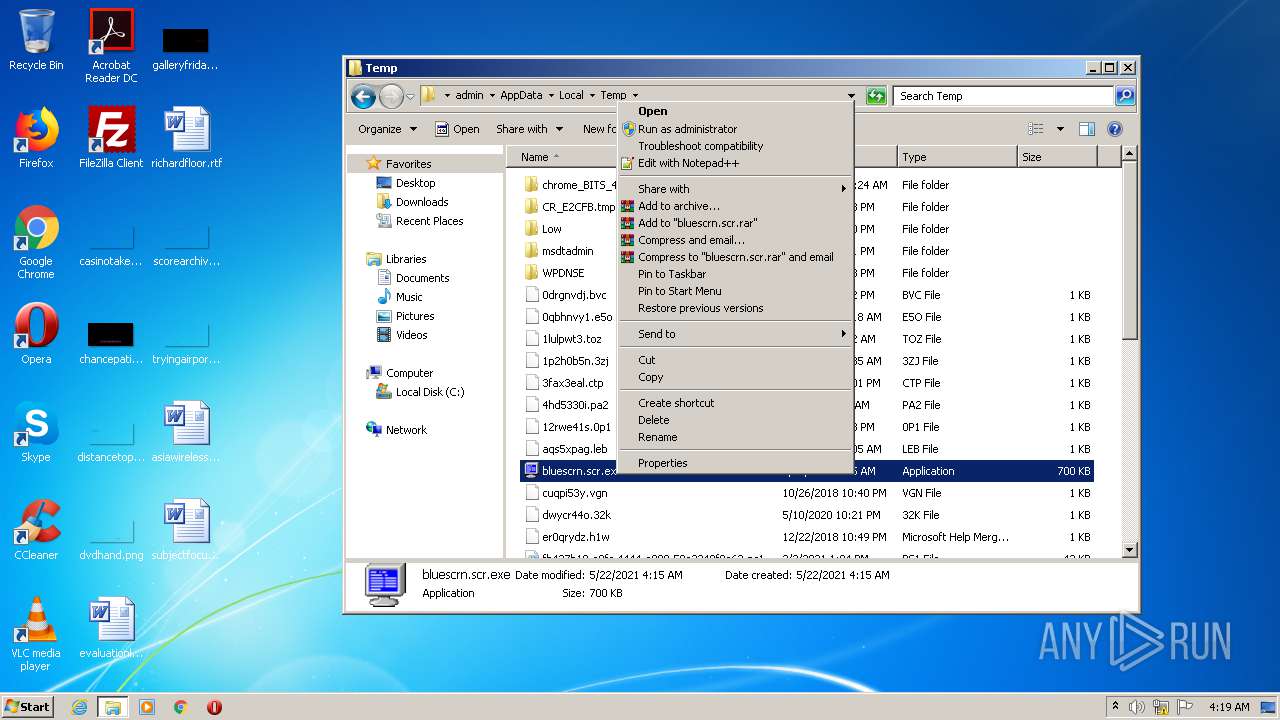
| 2088 | "C:\Users\admin\AppData\Local\Temp\bluescrn.scr.exe" | C:\Users\admin\AppData\Local\Temp\bluescrn.scr.exe | — | explorer.exe | |||||||||||
User: admin Company: Sysinternals Integrity Level: MEDIUM Description: Sysinternals Bluescreen Screen Saver Exit code: 0 Version: 3.2 Modules
| |||||||||||||||
| 2572 | "C:\Program Files\CCleaner\CCleaner.exe" /uac | C:\Program Files\CCleaner\CCleaner.exe | taskeng.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
| 2688 | "C:\Users\admin\AppData\Local\Temp\bluescrn.scr.exe" | C:\Users\admin\AppData\Local\Temp\bluescrn.scr.exe | — | explorer.exe | |||||||||||
User: admin Company: Sysinternals Integrity Level: MEDIUM Description: Sysinternals Bluescreen Screen Saver Exit code: 0 Version: 3.2 Modules
| |||||||||||||||
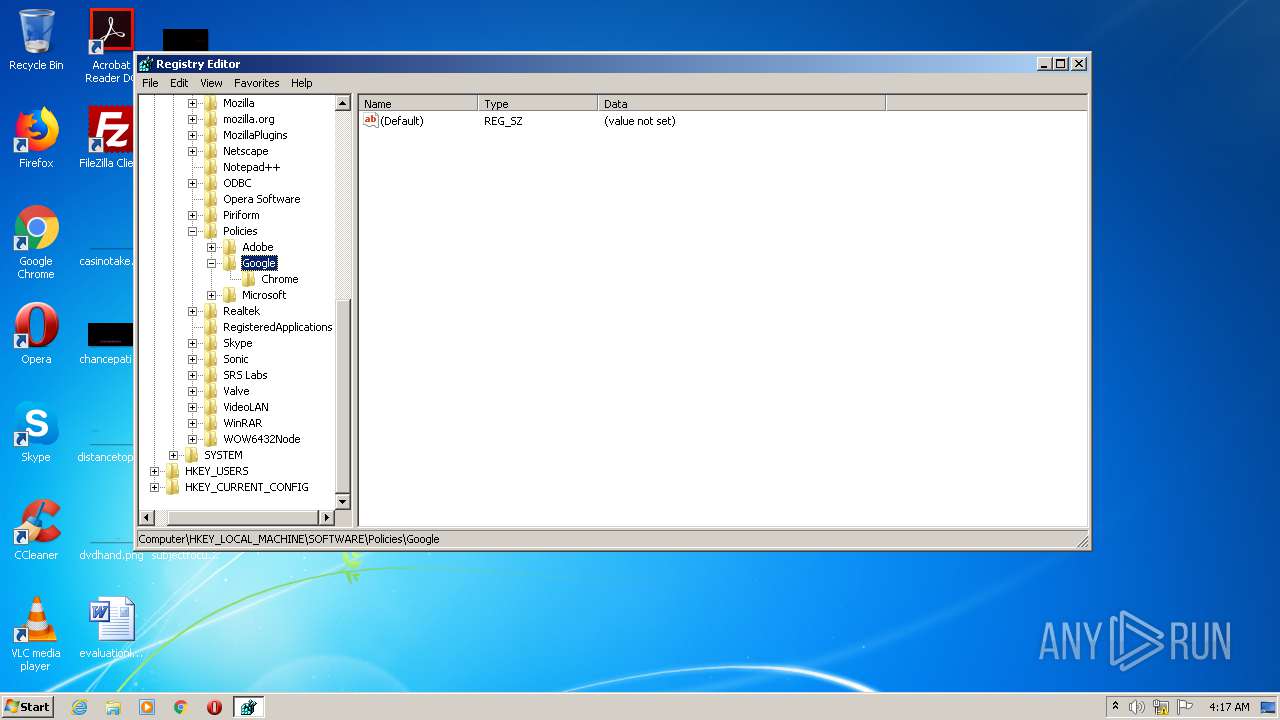
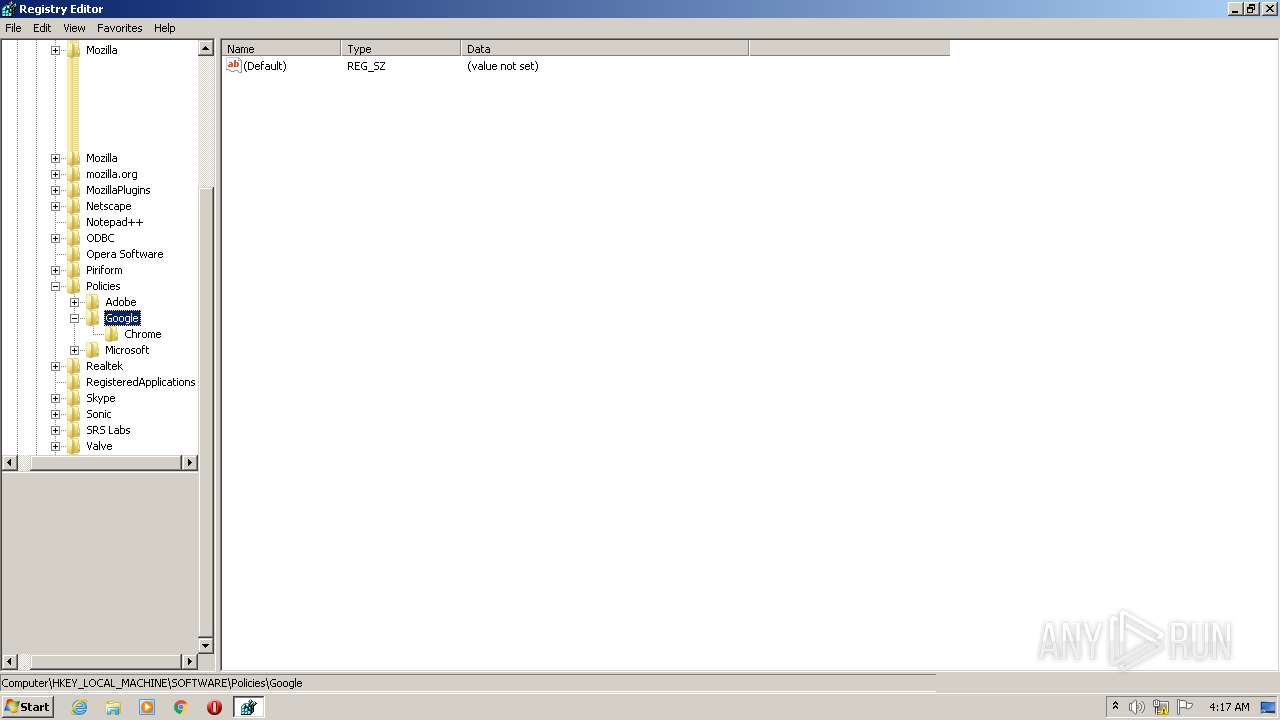
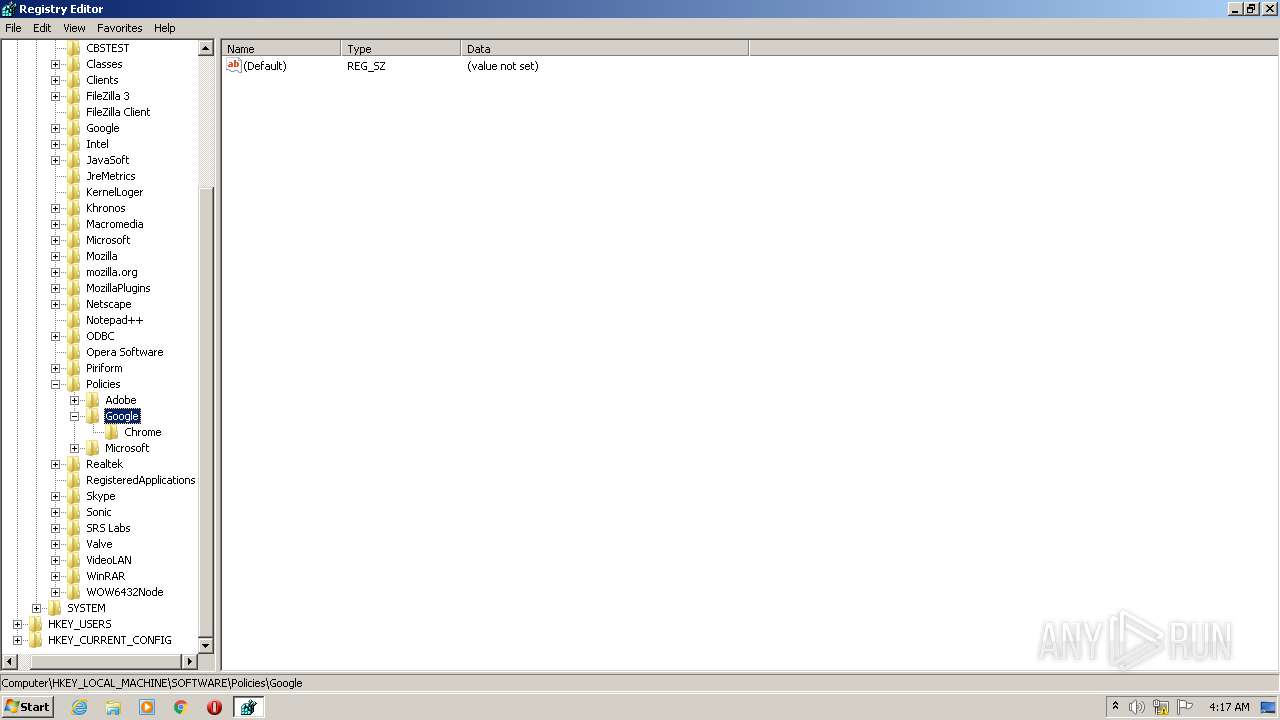
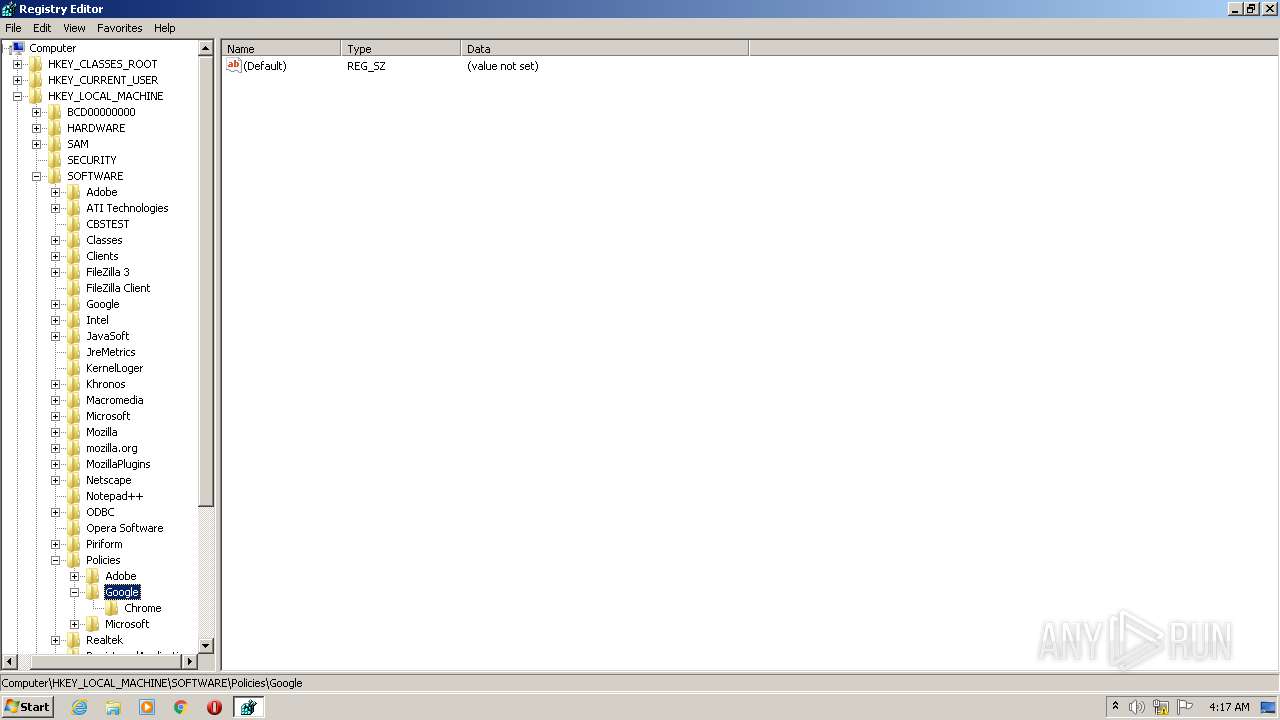
| 2940 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3192 | "C:\Program Files\CCleaner\CCleaner.exe" | C:\Program Files\CCleaner\CCleaner.exe | — | explorer.exe | |||||||||||
User: admin Company: Piriform Ltd Integrity Level: MEDIUM Description: CCleaner Exit code: 0 Version: 5, 35, 0, 6210 Modules
| |||||||||||||||
| 3820 | "C:\Windows\regedit.exe" | C:\Windows\regedit.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
456
Read events
315
Write events
141
Delete events
0
Modification events
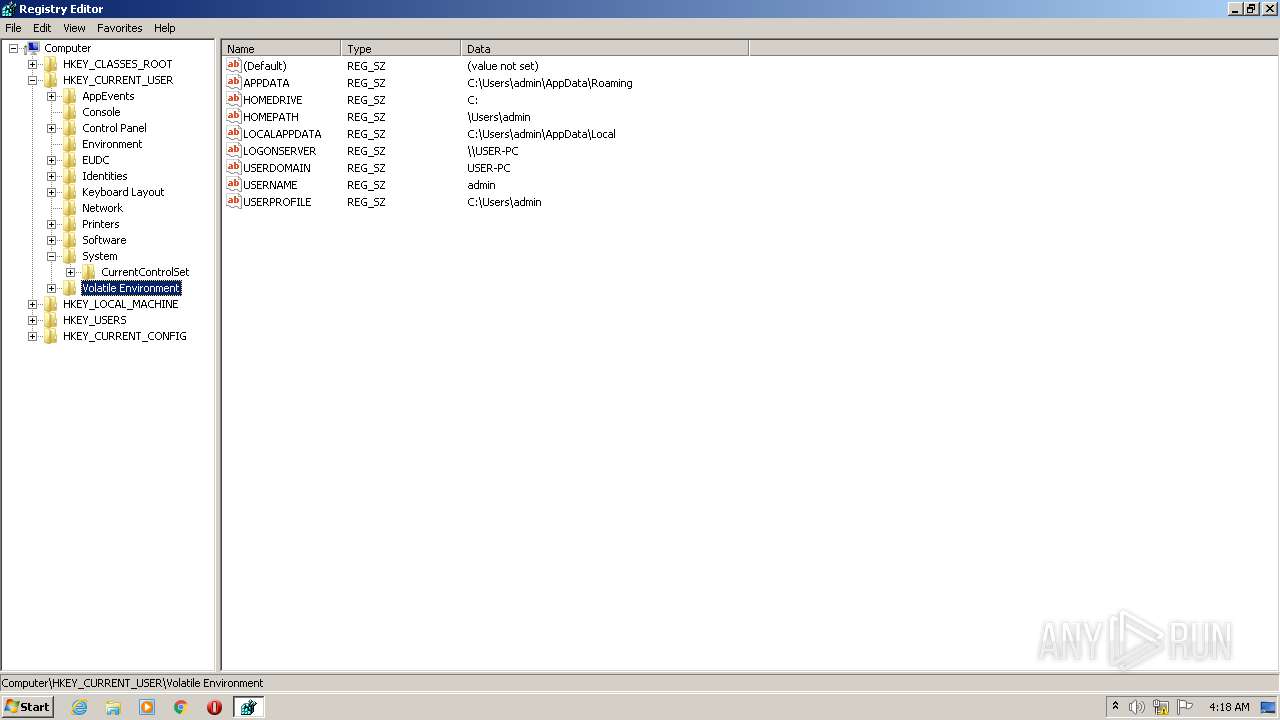
| (PID) Process: | (2088) bluescrn.scr.exe | Key: | HKEY_CURRENT_USER\Software\SysInternals\BlueScreen |
| Operation: | write | Name: | DoDiskWrites |
Value: 1 | |||
| (PID) Process: | (2572) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Piriform\CCleaner |
| Operation: | write | Name: | NewVersion |
Value: | |||
| (PID) Process: | (2572) CCleaner.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\13D\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2572) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2572) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2572) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2572) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2572) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2572) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2572) CCleaner.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
2
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2572 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\N8CTB28CPO4YWFRRI95L.temp | — | |
MD5:— | SHA256:— | |||
| 2572 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\DOAMRDW30B4BJBIIPGSW.temp | — | |
MD5:— | SHA256:— | |||
| 2572 | CCleaner.exe | C:\Users\admin\AppData\Local\Temp\CabFC8F.tmp | — | |
MD5:— | SHA256:— | |||
| 2572 | CCleaner.exe | C:\Users\admin\AppData\Local\Temp\TarFC90.tmp | — | |
MD5:— | SHA256:— | |||
| 2572 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ed7a5cc3cca8d52a.customDestinations-ms~RF14fc7f.TMP | binary | |
MD5:— | SHA256:— | |||
| 2572 | CCleaner.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\ed7a5cc3cca8d52a.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2572 | CCleaner.exe | GET | 404 | 151.101.0.64:80 | http://www.piriform.com/auto?a=0&p=cc&v=5.35.6210&l=1033&lk=&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-VAKU&o=6.1W3&au=1&mx=97B7721C4994E2556FF6A439510F665DB45337A341A47E15F4997584423BF714&gu=00000000-0000-4000-8000-d6f7f2be5127 | US | xml | 341 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2572 | CCleaner.exe | 151.101.0.64:443 | www.piriform.com | Fastly | US | whitelisted |
2572 | CCleaner.exe | 151.101.0.64:80 | www.piriform.com | Fastly | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.piriform.com |
| whitelisted |