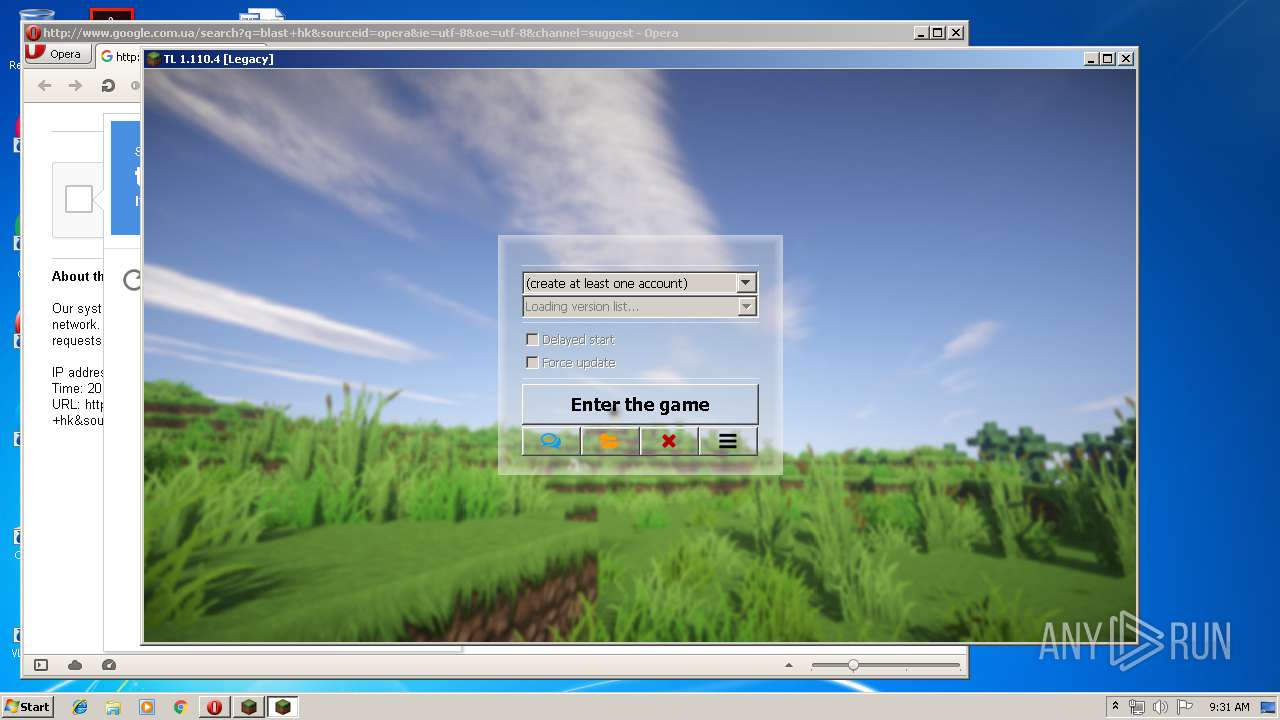
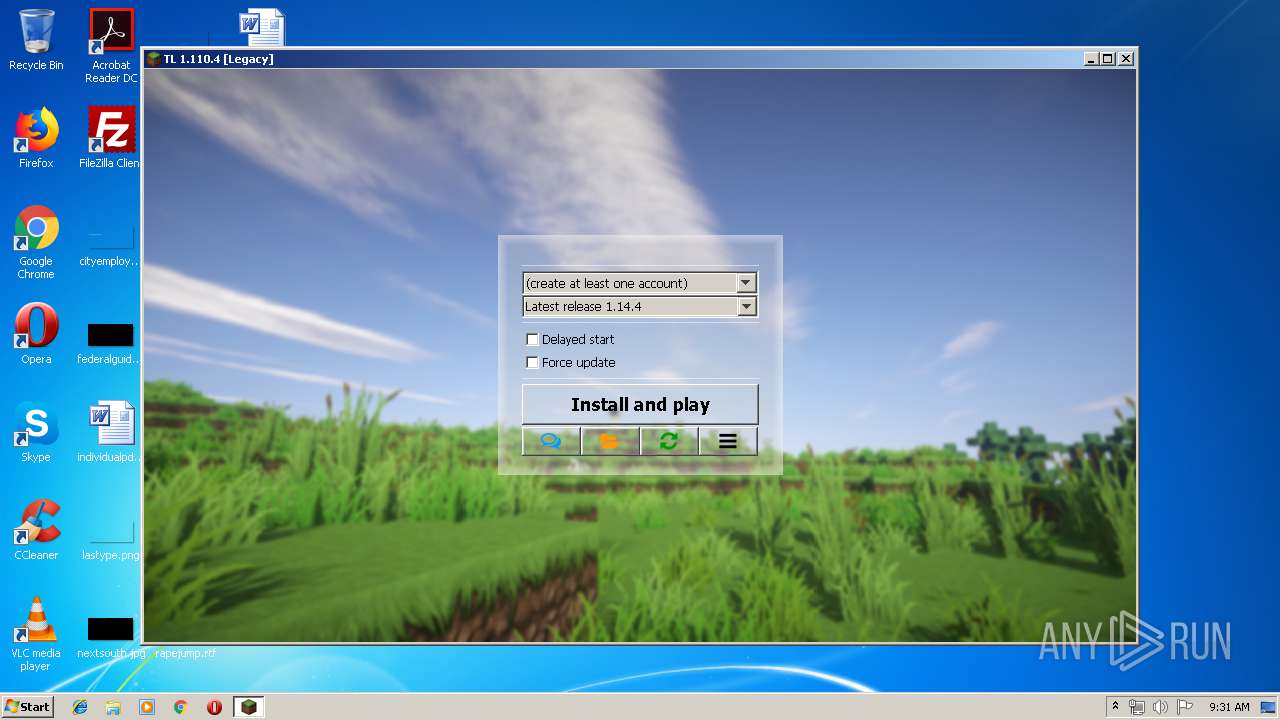
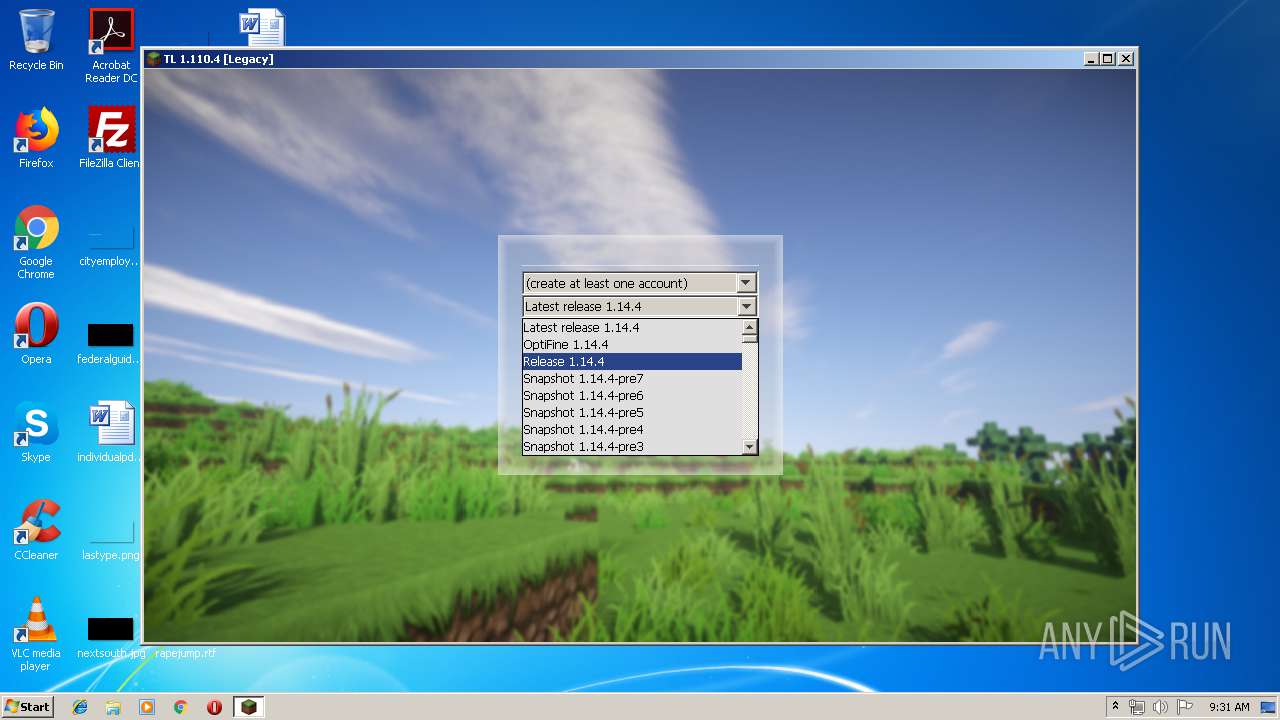
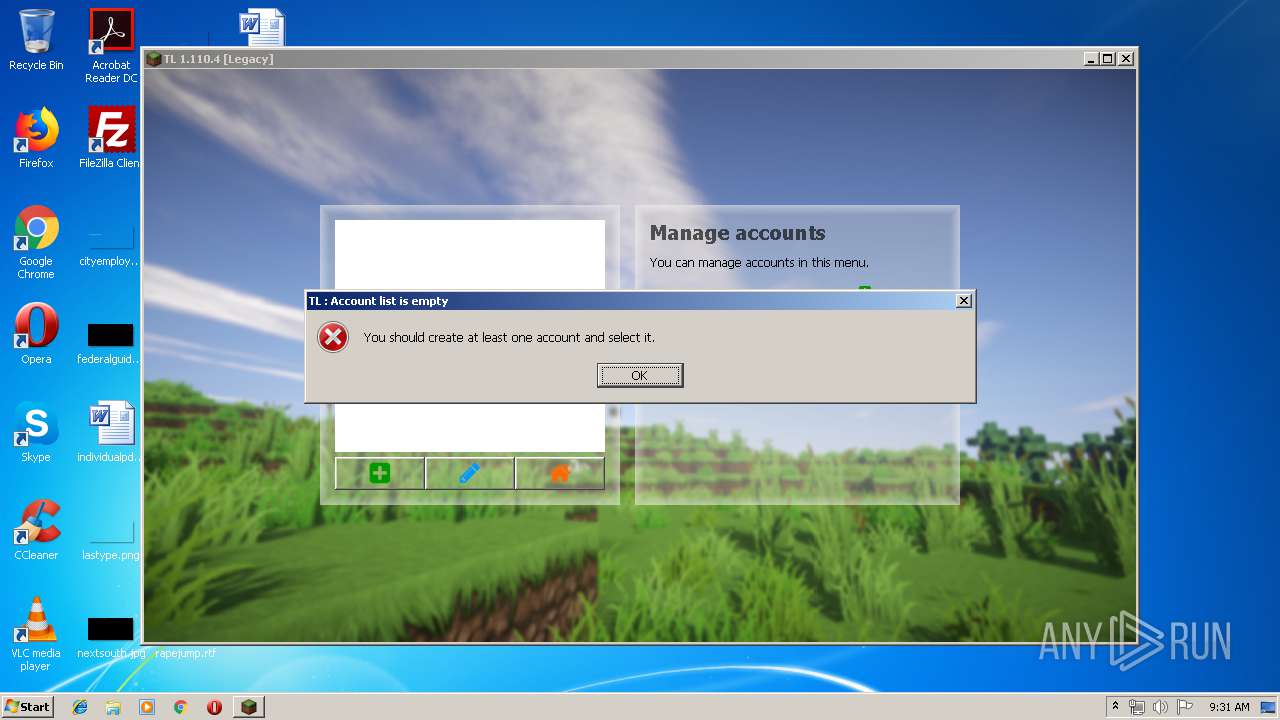
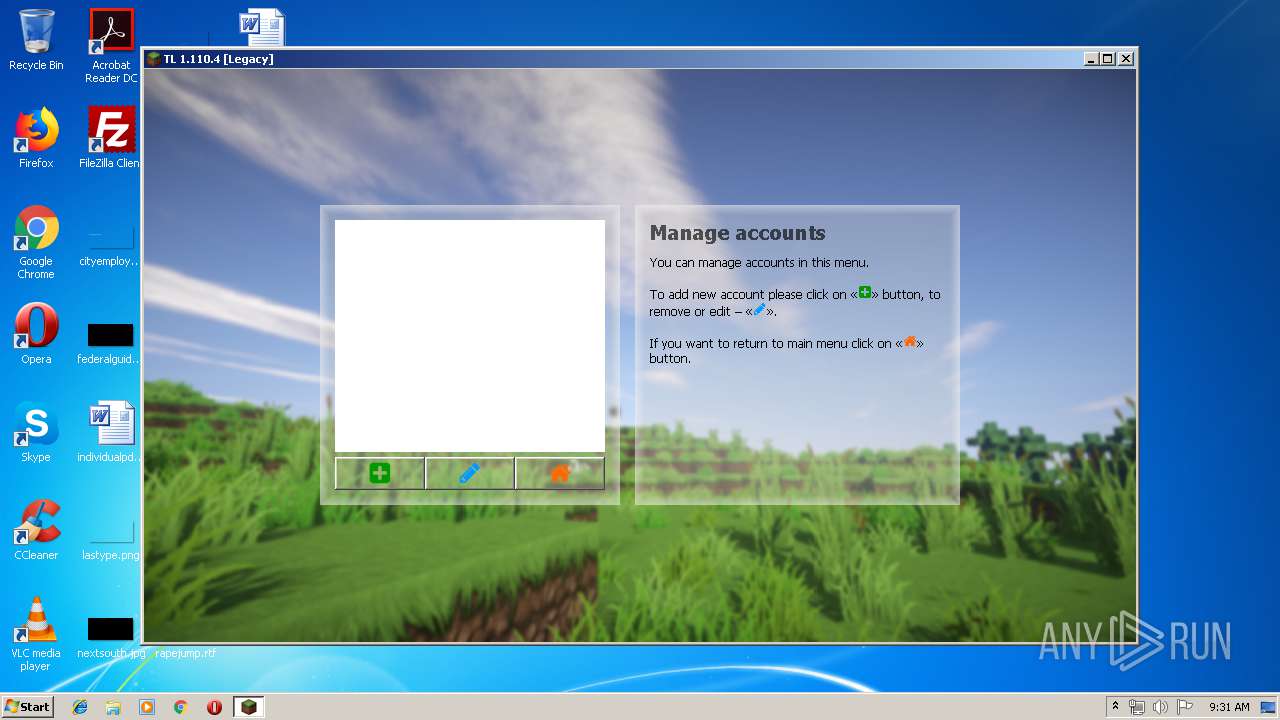
| File name: | TL.exe |
| Full analysis: | https://app.any.run/tasks/9470bbce-76c3-4659-bed0-55a8df33fe49 |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 08:29:31 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | A50730498B316308FADD725493D09A90 |
| SHA1: | FE1C096D34EB1223AC6AD1F17A9F8200E5408E63 |
| SHA256: | DCAEBF3D2F935887AF06DF9820886775FA3D31C1EA24025A585D2B03D3FFD328 |
| SSDEEP: | 24576:CvVjAexEh3ibqIjk2cvplZwPLdcnNtfomqdQYddBgyHKAZqYSgr2VOAexEhu:CitibqIZcBlkuGBgyHKAZqYRs |
MALICIOUS
Application was dropped or rewritten from another process
- javaw.exe (PID: 1296)
- javaw.exe (PID: 3932)
Loads dropped or rewritten executable
- TL.exe (PID: 3144)
- javaw.exe (PID: 1296)
- javaw.exe (PID: 3932)
SUSPICIOUS
Executable content was dropped or overwritten
- TL.exe (PID: 872)
- TL.exe (PID: 3144)
Starts itself from another location
- TL.exe (PID: 872)
Creates files in the program directory
- javaw.exe (PID: 1296)
Reads Environment values
- TL.exe (PID: 3144)
Uses ICACLS.EXE to modify access control list
- javaw.exe (PID: 1296)
Creates files in the user directory
- javaw.exe (PID: 3932)
- TL.exe (PID: 3144)
INFO
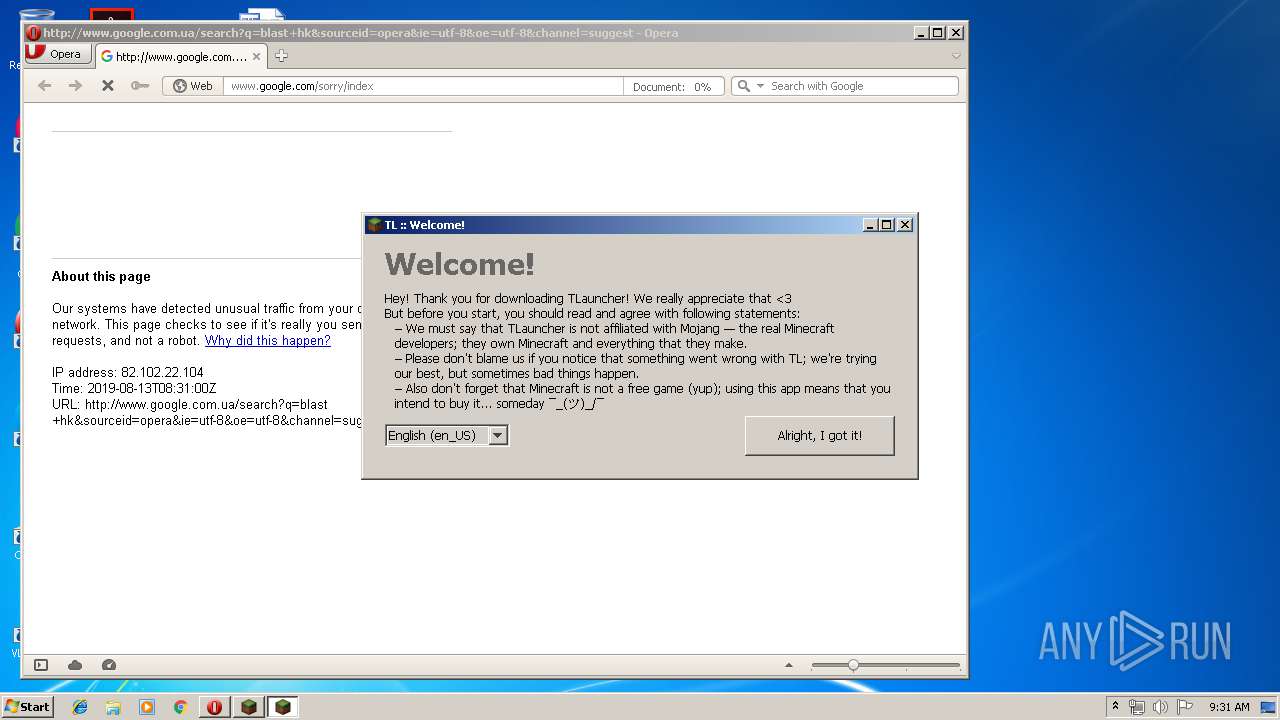
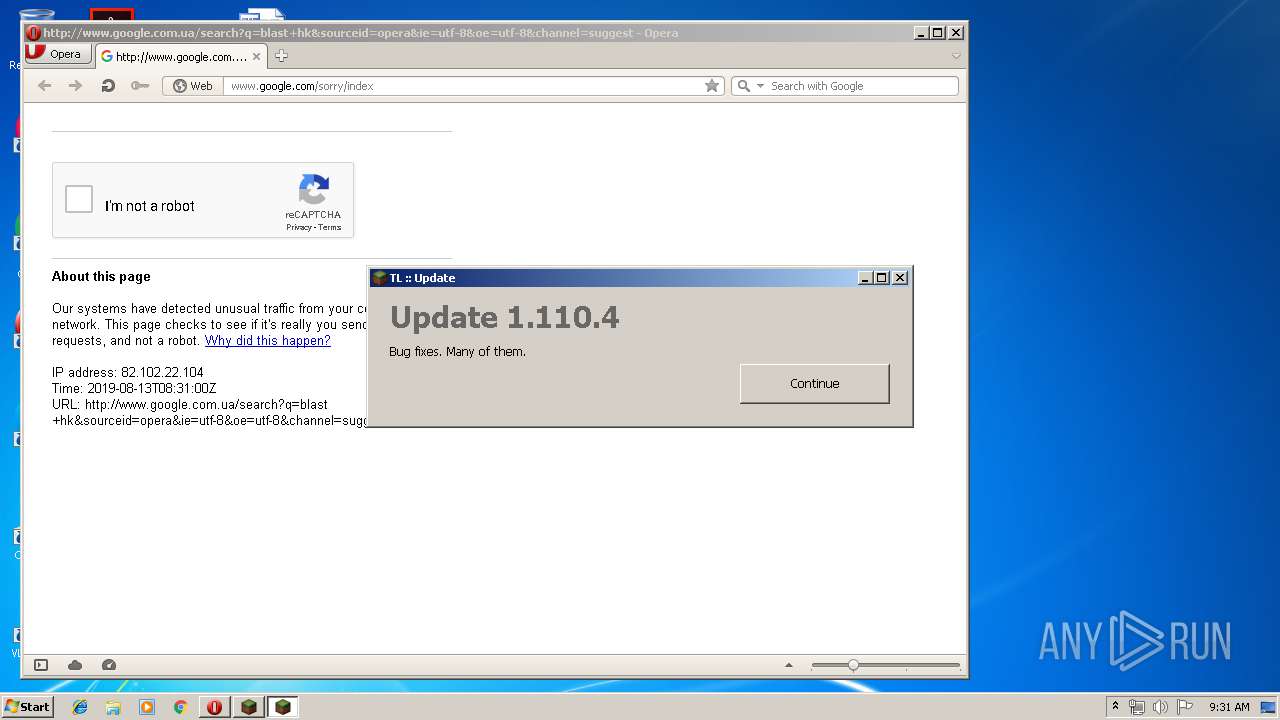
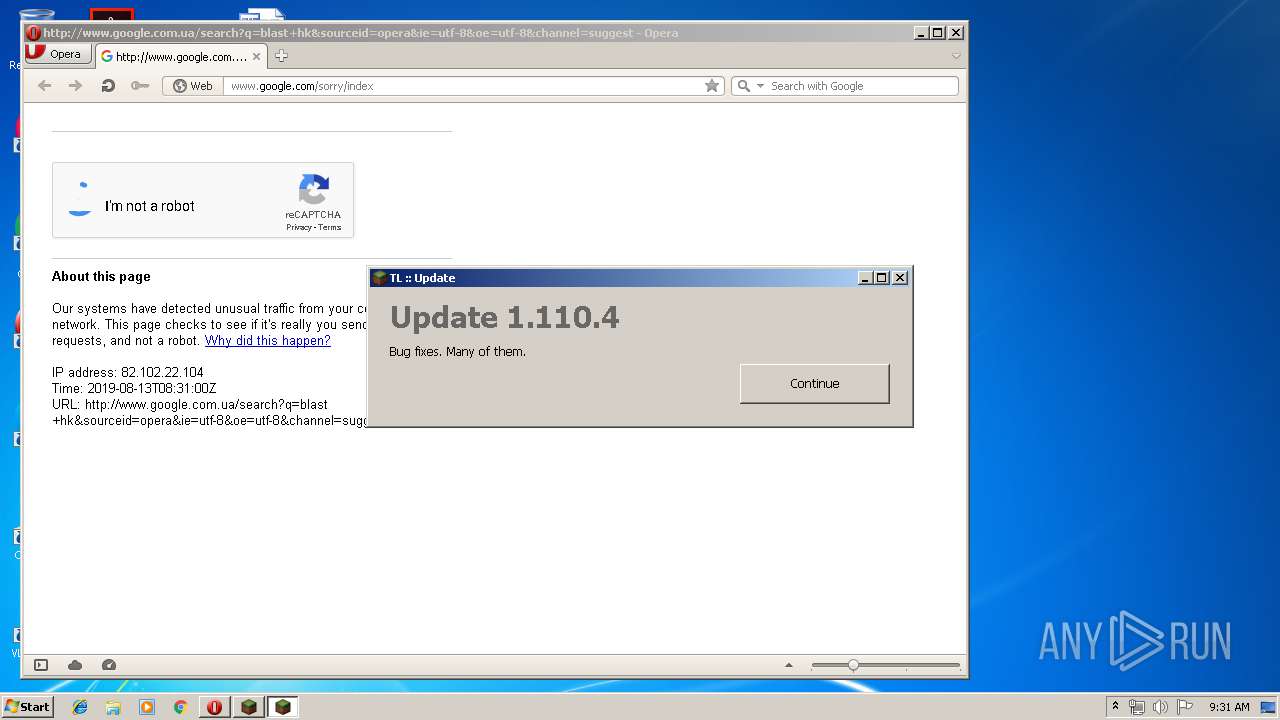
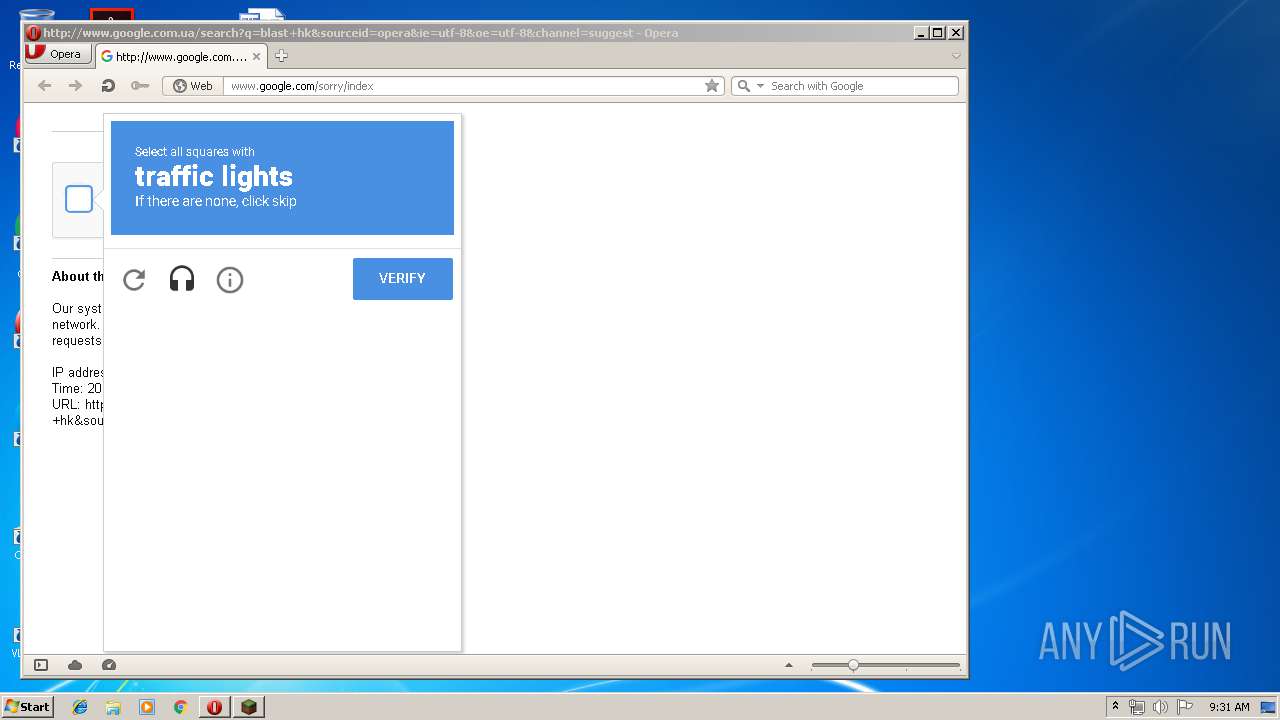
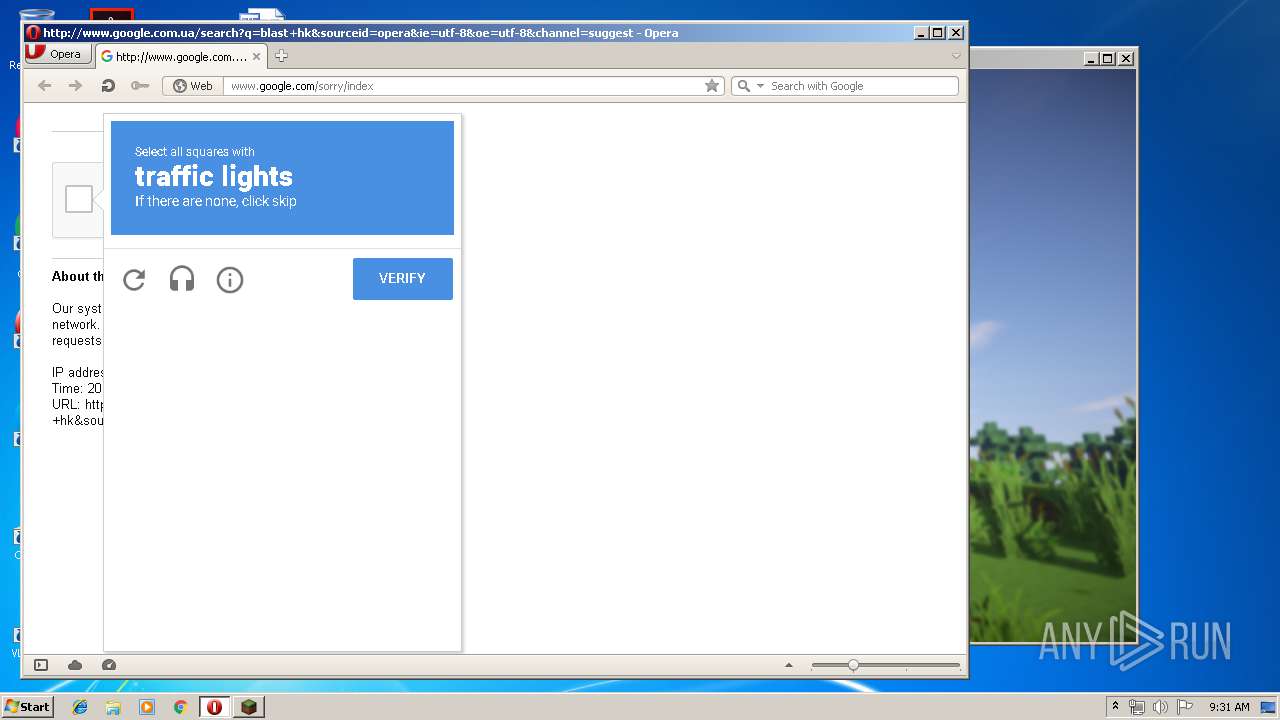
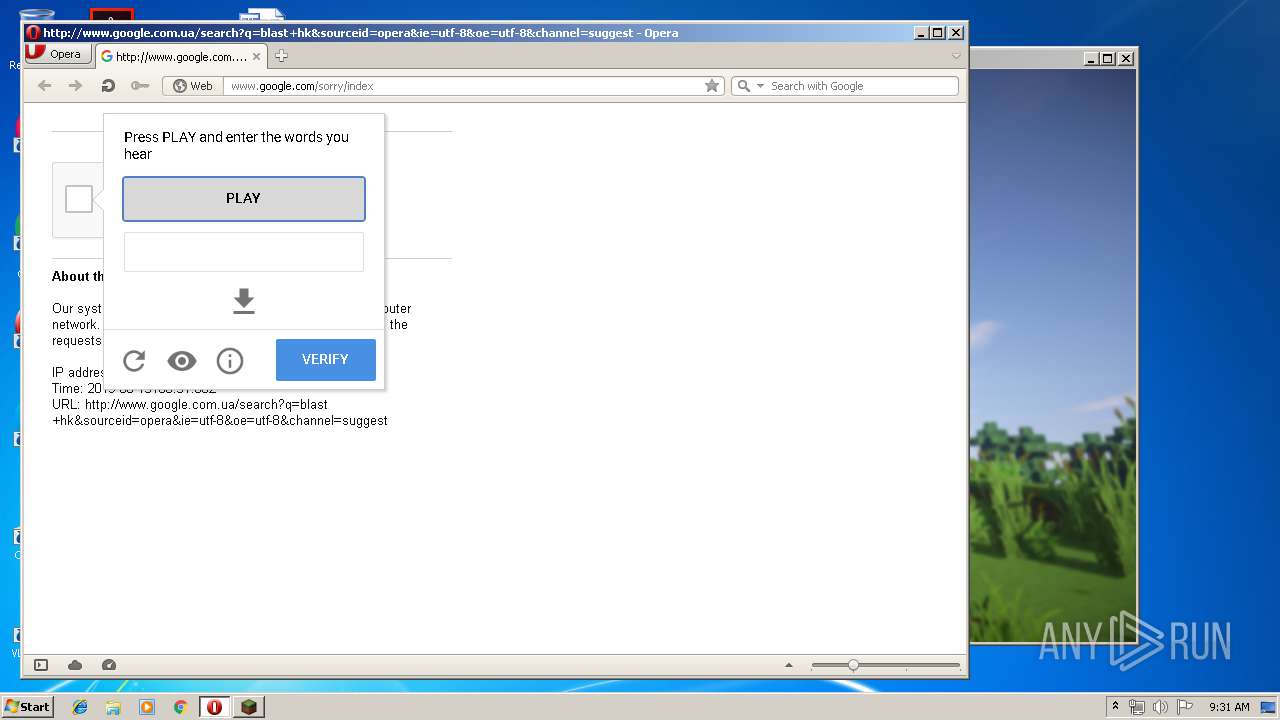
Manual execution by user
- SndVol.exe (PID: 3228)
- opera.exe (PID: 2928)
Reads settings of System Certificates
- TL.exe (PID: 3144)
Creates files in the user directory
- opera.exe (PID: 2928)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (62) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (23.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (5.5) |
| .exe | | | Win32 Executable (generic) (3.8) |
| .exe | | | Win16/32 Executable Delphi generic (1.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:11:25 12:53:22+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 1938944 |
| InitializedDataSize: | 376320 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1db48e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
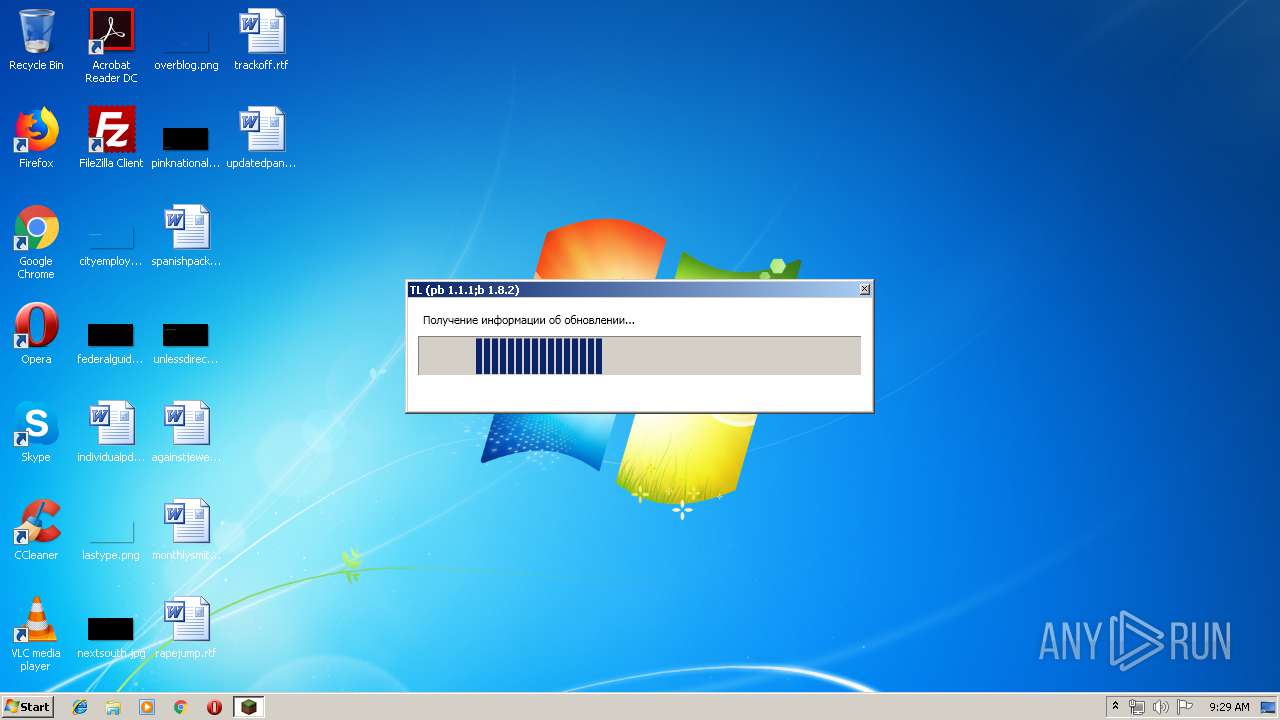
| FileVersionNumber: | 1.1.1.0 |
| ProductVersionNumber: | 1.1.1.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
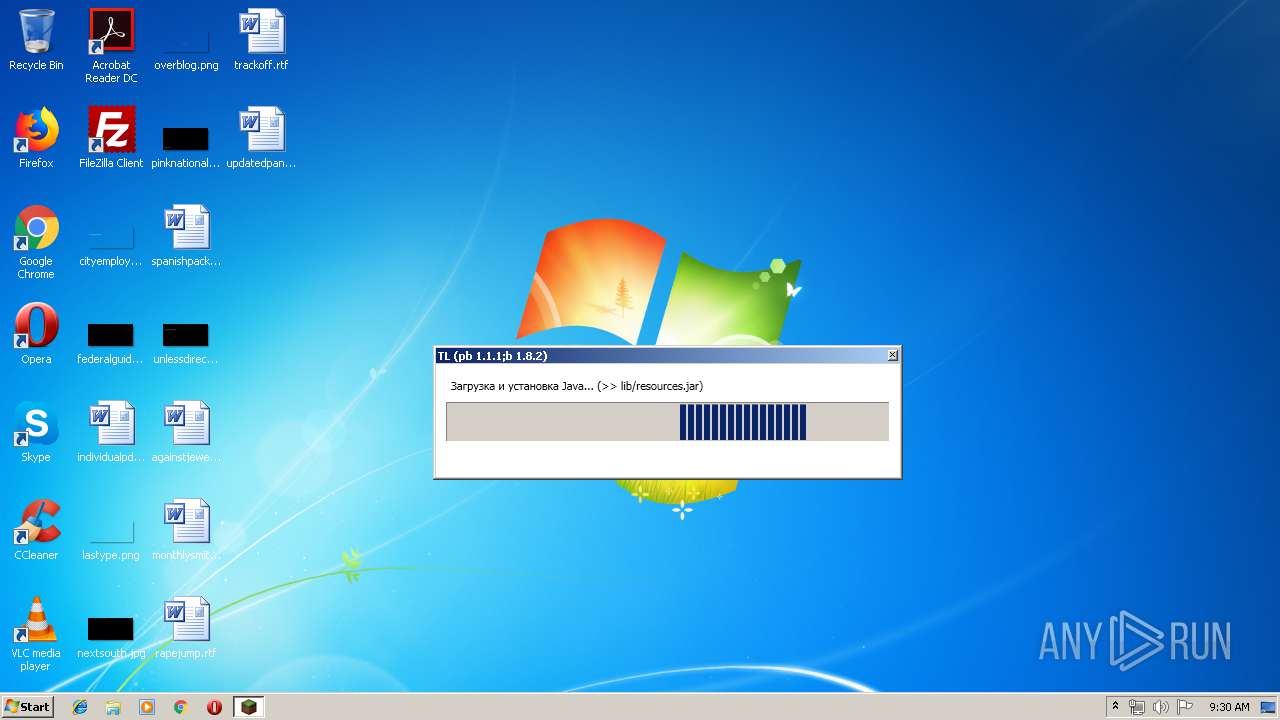
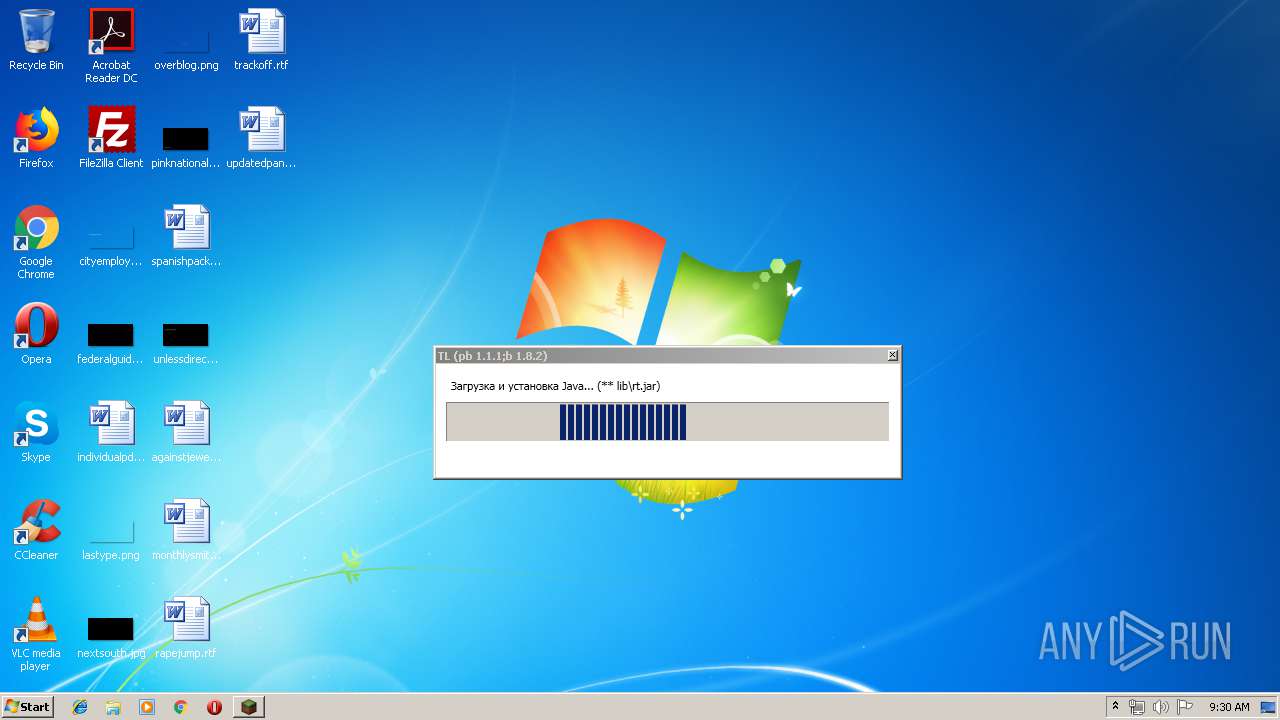
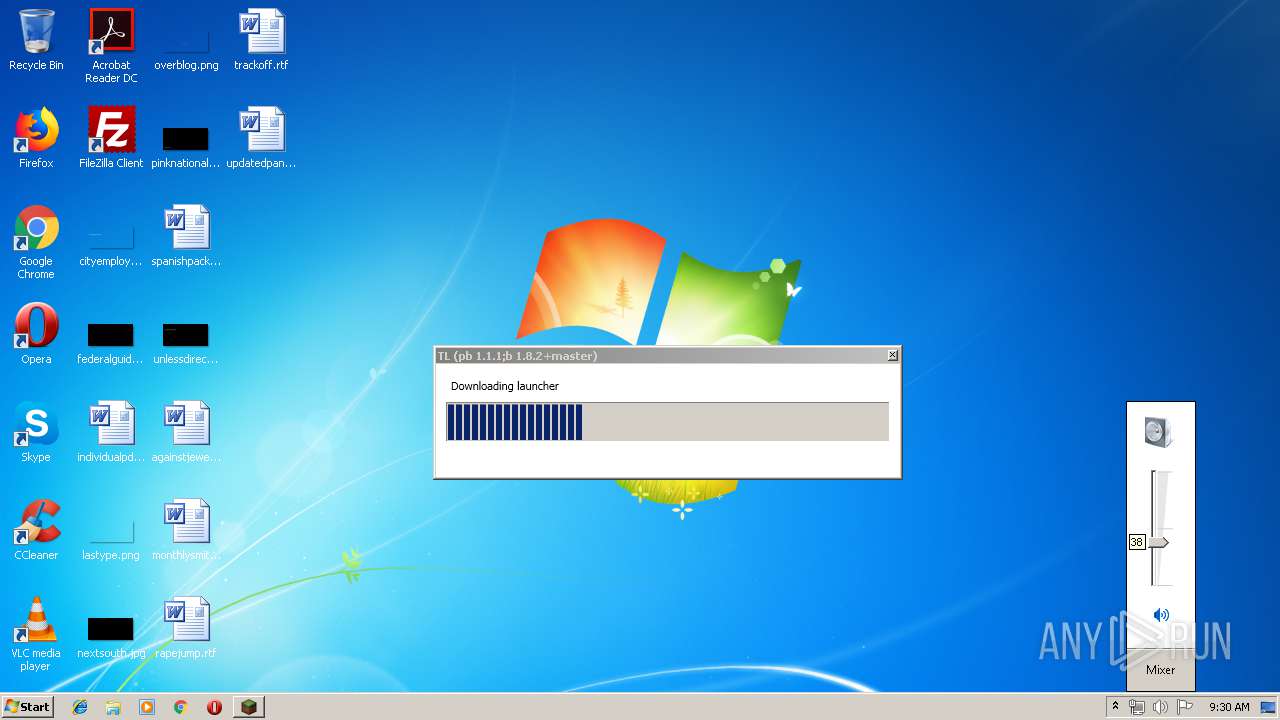
| Comments: | Pre-bootstrap executable. Downloads and verifies JRE, then launches bootstrap for TL. |
| CompanyName: | TL |
| FileDescription: | TL Pre-bootstrap |
| FileVersion: | 1.1.1.0 |
| InternalName: | java-launcher-wpf.exe |
| LegalCopyright: | © 2018 |
| LegalTrademarks: | - |
| OriginalFileName: | java-launcher-wpf.exe |
| ProductName: | tl-pb-wpf |
| ProductVersion: | 1.1.1.0 |
| AssemblyVersion: | 1.1.1.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 25-Nov-2018 11:53:22 |
| Debug artifacts: |
|
| Comments: | Pre-bootstrap executable. Downloads and verifies JRE, then launches bootstrap for TL. |
| CompanyName: | TL |
| FileDescription: | TL Pre-bootstrap |
| FileVersion: | 1.1.1.0 |
| InternalName: | java-launcher-wpf.exe |
| LegalCopyright: | © 2018 |
| LegalTrademarks: | - |
| OriginalFilename: | java-launcher-wpf.exe |
| ProductName: | tl-pb-wpf |
| ProductVersion: | 1.1.1.0 |
| Assembly Version: | 1.1.1.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 25-Nov-2018 11:53:22 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x001D9494 | 0x001D9600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.67673 |
.rsrc | 0x001DC000 | 0x0005BC00 | 0x0005BC00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.32548 |
.reloc | 0x00238000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.43207 | 3957 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 5.54565 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.46449 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 5.39665 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.29937 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.24859 | 270376 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.76511 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
41
Monitored processes
7
Malicious processes
4
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 872 | "C:\Users\admin\AppData\Local\Temp\TL.exe" | C:\Users\admin\AppData\Local\Temp\TL.exe | explorer.exe | ||||||||||||
User: admin Company: TL Integrity Level: MEDIUM Description: TL Pre-bootstrap Exit code: 0 Version: 1.1.1.0 Modules
| |||||||||||||||
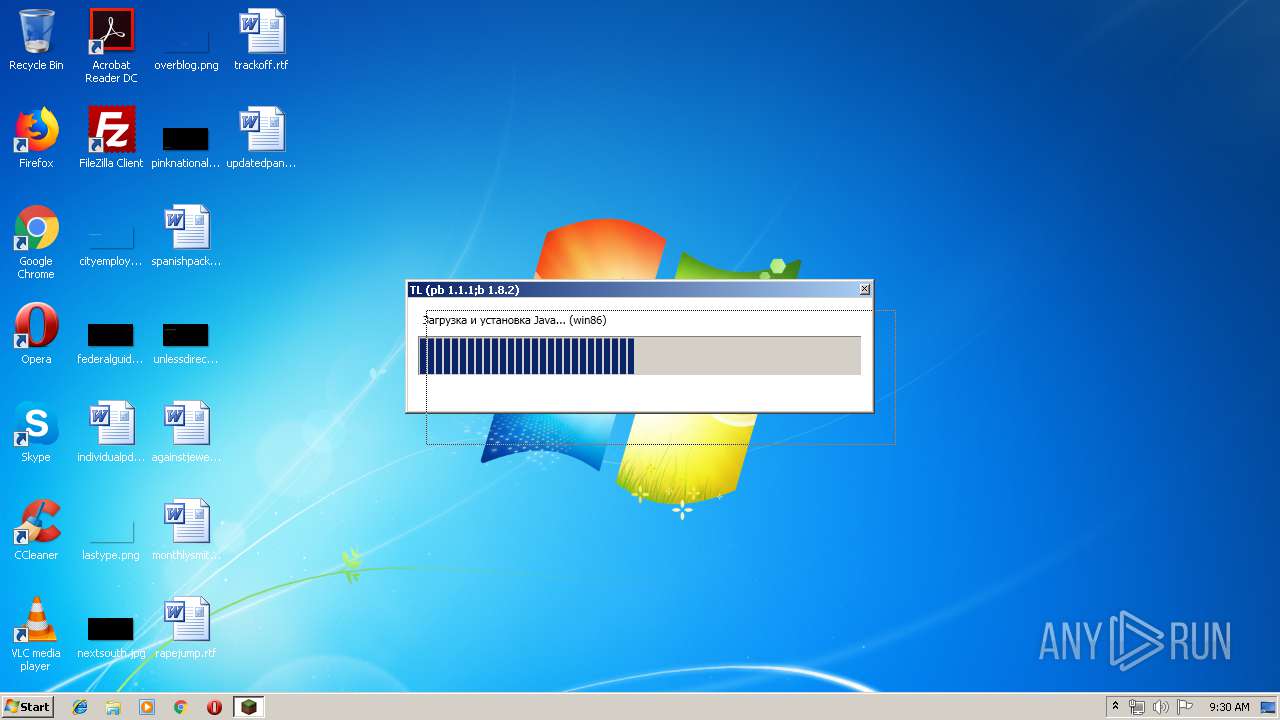
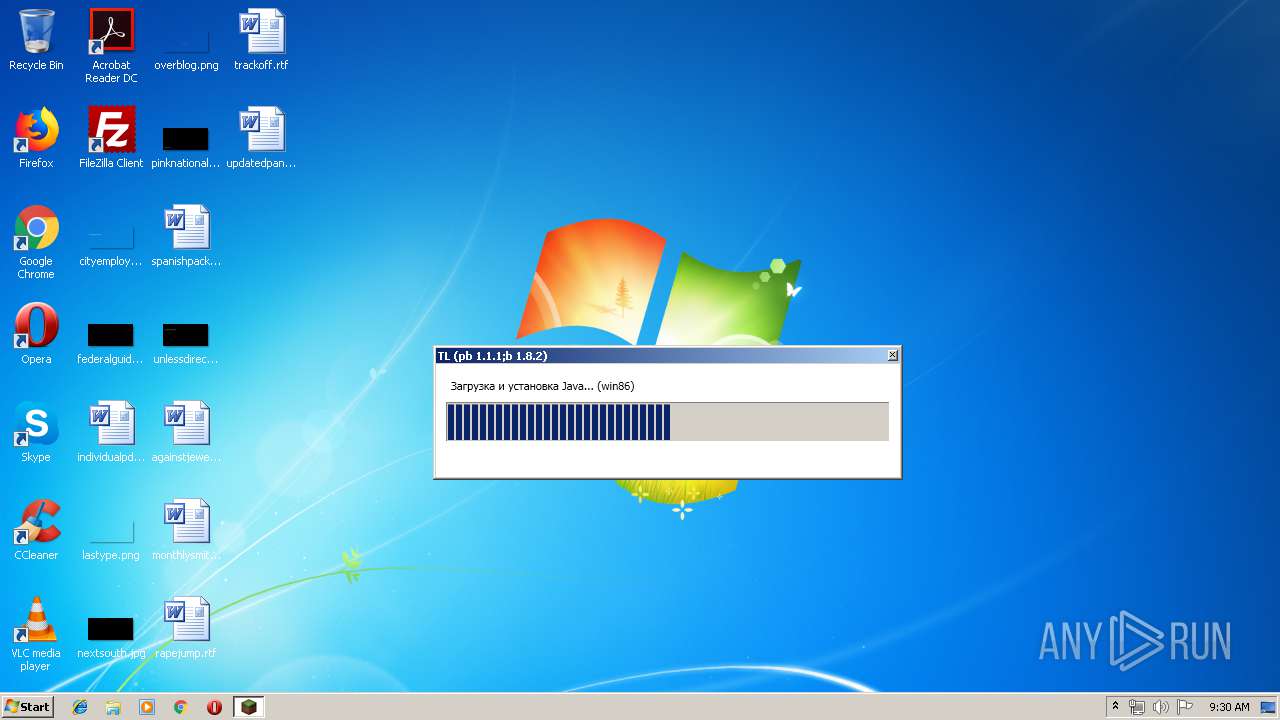
| 1296 | "C:\Users\admin\AppData\Roaming\.tlauncher\jre\win86\bin\javaw.exe" -version | C:\Users\admin\AppData\Roaming\.tlauncher\jre\win86\bin\javaw.exe | — | TL.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.1810.13 Modules
| |||||||||||||||
| 2928 | "C:\Program Files\Opera\opera.exe" | C:\Program Files\Opera\opera.exe | explorer.exe | ||||||||||||
User: admin Company: Opera Software Integrity Level: MEDIUM Description: Opera Internet Browser Exit code: 0 Version: 1748 Modules
| |||||||||||||||
| 3144 | "C:\Users\admin\AppData\Local\Temp\tlpbdcaebf3d2f935887af06df9820886775fa3d31c1ea24025a585d2b03d3ffd328\TL.exe" --sourceExe "C:\Users\admin\AppData\Local\Temp\TL.exe" | C:\Users\admin\AppData\Local\Temp\tlpbdcaebf3d2f935887af06df9820886775fa3d31c1ea24025a585d2b03d3ffd328\TL.exe | TL.exe | ||||||||||||
User: admin Company: TL Integrity Level: MEDIUM Description: TL Pre-bootstrap Exit code: 0 Version: 1.1.1.0 Modules
| |||||||||||||||
| 3228 | SndVol.exe -f 46466185 3186 | C:\Windows\system32\SndVol.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Volume Mixer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3756 | C:\Windows\system32\icacls.exe C:\ProgramData\Oracle\Java\.oracle_jre_usage /grant "everyone":(OI)(CI)M | C:\Windows\system32\icacls.exe | — | javaw.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3932 | "C:\Users\admin\AppData\Roaming\.tlauncher\jre\win86\bin\javaw.exe" -Xmx128m -Dfile.encoding="UTF-8" -Dtlauncher.bootstrap.headlessMode="true" -Dtlauncher.bootstrap.ignoreSelfUpdate="true" -Dtlauncher.bootstrap.updateMetaFile="C:\Users\admin\AppData\Local\Temp\tmpDA2C.tmp" -cp "C:\Users\admin\AppData\Roaming\.tlauncher\bin\bootstrap\legacy.jar" ru.turikhay.tlauncher.bootstrap.Bootstrap | C:\Users\admin\AppData\Roaming\.tlauncher\jre\win86\bin\javaw.exe | TL.exe | ||||||||||||
User: admin Company: Oracle Corporation Integrity Level: MEDIUM Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.1810.13 Modules
| |||||||||||||||
Total events
1 086
Read events
941
Write events
145
Delete events
0
Modification events
| (PID) Process: | (872) TL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (872) TL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3144) TL.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: TL.exe | |||
| (PID) Process: | (3144) TL.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\TL_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3144) TL.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\TL_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3144) TL.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\TL_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3144) TL.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\TL_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3144) TL.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\TL_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3144) TL.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\TL_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3144) TL.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\TL_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
Executable files
169
Suspicious files
78
Text files
107
Unknown types
27
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3144 | TL.exe | C:\Users\admin\AppData\Local\Temp\tl2-7dfb0260-1092-42ea-af62-d6bc9d287ef3 | — | |
MD5:— | SHA256:— | |||
| 3144 | TL.exe | C:\Users\admin\AppData\Local\Temp\tmpDBB4.tmp | — | |
MD5:— | SHA256:— | |||
| 3144 | TL.exe | C:\Users\admin\AppData\Local\Temp\tmpDCBF.tmp | — | |
MD5:— | SHA256:— | |||
| 3144 | TL.exe | C:\Users\admin\AppData\Local\Temp\tmpDA2C.tmp | binary | |
MD5:— | SHA256:— | |||
| 3144 | TL.exe | C:\Users\admin\AppData\Roaming\.tlauncher\jre\win86\bin\api-ms-win-core-errorhandling-l1-1-0.dll | executable | |
MD5:E553577D0DD4686EDB488AD9A2BA0859 | SHA256:8A23E01FFB6B0D6B6A8674C427AC31EB4903A4B788B7F250D14574E71CC88E0B | |||
| 3144 | TL.exe | C:\Users\admin\AppData\Roaming\.tlauncher\jre\win86\bin\api-ms-win-core-file-l1-2-0.dll | executable | |
MD5:930E91E6D6194DB50733DCB57D4022A2 | SHA256:30F570E7FCA225CEFD7B9A0B40EC8D2AAD758931753964E02C447DF9281B4129 | |||
| 3144 | TL.exe | C:\Users\admin\AppData\Roaming\.tlauncher\jre\win86\bin\api-ms-win-core-console-l1-1-0.dll | executable | |
MD5:F0D8A941B243DFA19440D0CE01566E14 | SHA256:E80E97AE534151F473CF9538CC7677939C43098B78DE7881AD6731D33533FC52 | |||
| 3144 | TL.exe | C:\Users\admin\AppData\Roaming\.tlauncher\jre\win86\bin\api-ms-win-core-file-l1-1-0.dll | executable | |
MD5:941C4BA57CD6E0665A4758971F8CDE6F | SHA256:835CF5AEAB4E99B6448E5724C056678B42316EE36C48AB56CD263FD74096A2E9 | |||
| 3144 | TL.exe | C:\Users\admin\AppData\Roaming\.tlauncher\jre\win86\bin\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:E1A16C08F684C03DDBFA98578D5BF25D | SHA256:59F675DAA7D38C32252AC488EE4EA5472FCA891017A429E8F84C66B56AEA7D99 | |||
| 3144 | TL.exe | C:\Users\admin\AppData\Roaming\.tlauncher\jre\win86\bin\api-ms-win-core-interlocked-l1-1-0.dll | executable | |
MD5:C25FEB9FF9CC47963A77DE4DF1FA3614 | SHA256:8835BCBC977C06B037E85576924F0AEA75E00C9747D81851D6A8646E8C19D8A7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
41
TCP/UDP connections
34
DNS requests
19
Threats
20
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3144 | TL.exe | GET | 200 | 5.254.23.67:80 | http://cdn.turikhay.ru/tlauncher/legacy/bootstrap.json.mgz.signed | RO | binary | 54.5 Kb | suspicious |
3144 | TL.exe | GET | 200 | 87.236.16.53:80 | http://turikhay.ru/tlauncher/legacy/bootstrap/0ecc197e9366c74deace72c5eb351d54372e178b6bffb5865b6e16f6bf657b4a.jar | RU | compressed | 709 Kb | malicious |
3932 | javaw.exe | GET | 200 | 213.186.33.186:80 | http://tlauncherrepo.com/legacy/launcher/2de57dc49587f79aacee02cc44f81a90b0b03f70653b8cb0f2eda474a36ddd54.jar | FR | java | 2.63 Mb | suspicious |
3932 | javaw.exe | GET | 200 | 87.236.16.53:80 | http://turikhay.ru/tlauncher/repo/libraries/com/getsentry/raven/raven/7.8.1/raven-7.8.1.jar | RU | compressed | 120 Kb | malicious |
3932 | javaw.exe | GET | 200 | 87.236.16.53:80 | http://turikhay.ru/tlauncher/repo/libraries/org/jdom/jdom/2.0.2/jdom-2.0.2.jar | RU | java | 288 Kb | malicious |
3932 | javaw.exe | GET | 200 | 87.236.16.53:80 | http://turikhay.ru/tlauncher/repo/libraries/net/sf/jopt-simple/jopt-simple/4.9/jopt-simple-4.9.jar | RU | java | 64.9 Kb | malicious |
3932 | javaw.exe | GET | 200 | 87.236.16.53:80 | http://turikhay.ru/tlauncher/repo/libraries/org/apache/commons/commons-lang3/3.4/commons-lang3-3.4.jar | RU | compressed | 424 Kb | malicious |
3932 | javaw.exe | GET | 200 | 87.236.16.53:80 | http://turikhay.ru/tlauncher/repo/libraries/com/mojang/authlib/1.5.24/authlib-1.5.24.jar | RU | compressed | 62.8 Kb | malicious |
3932 | javaw.exe | GET | 200 | 87.236.16.53:80 | http://turikhay.ru/tlauncher/repo/libraries/org/apache/logging/log4j/log4j-core/2.8.1/log4j-core-2.8.1.jar | RU | compressed | 1.34 Mb | malicious |
3932 | javaw.exe | GET | 200 | 87.236.16.53:80 | http://turikhay.ru/tlauncher/repo/libraries/ru/turikhay/app/nstweaker/1.0/nstweaker-1.0.jar | RU | java | 498 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3144 | TL.exe | 5.254.23.67:80 | cdn.turikhay.ru | — | RO | unknown |
3144 | TL.exe | 213.186.33.186:443 | tlauncherrepo.com | OVH SAS | FR | suspicious |
3144 | TL.exe | 87.236.16.53:80 | turikhay.ru | Beget Ltd | RU | malicious |
3932 | javaw.exe | 213.186.33.186:80 | tlauncherrepo.com | OVH SAS | FR | suspicious |
3932 | javaw.exe | 87.236.16.53:80 | turikhay.ru | Beget Ltd | RU | malicious |
2928 | opera.exe | 185.26.182.94:443 | certs.opera.com | Opera Software AS | — | whitelisted |
2928 | opera.exe | 93.184.220.29:80 | crl4.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2928 | opera.exe | 172.217.22.14:80 | clients1.google.com | Google Inc. | US | whitelisted |
2928 | opera.exe | 172.217.23.131:80 | www.google.com.ua | Google Inc. | US | whitelisted |
2928 | opera.exe | 185.26.182.112:80 | sitecheck2.opera.com | Opera Software AS | — | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
cdn.turikhay.ru |
| suspicious |
tlauncherrepo.com |
| unknown |
turikhay.ru |
| malicious |
u.tlauncher.ru |
| suspicious |
repo.tlauncher.ru |
| suspicious |
certs.opera.com |
| whitelisted |
crl4.digicert.com |
| whitelisted |
clients1.google.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
sitecheck2.opera.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3932 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3932 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3932 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3932 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3932 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3932 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3932 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3932 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3932 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
3932 | javaw.exe | A Network Trojan was detected | ET INFO JAVA - Java Archive Download |
1 ETPRO signatures available at the full report