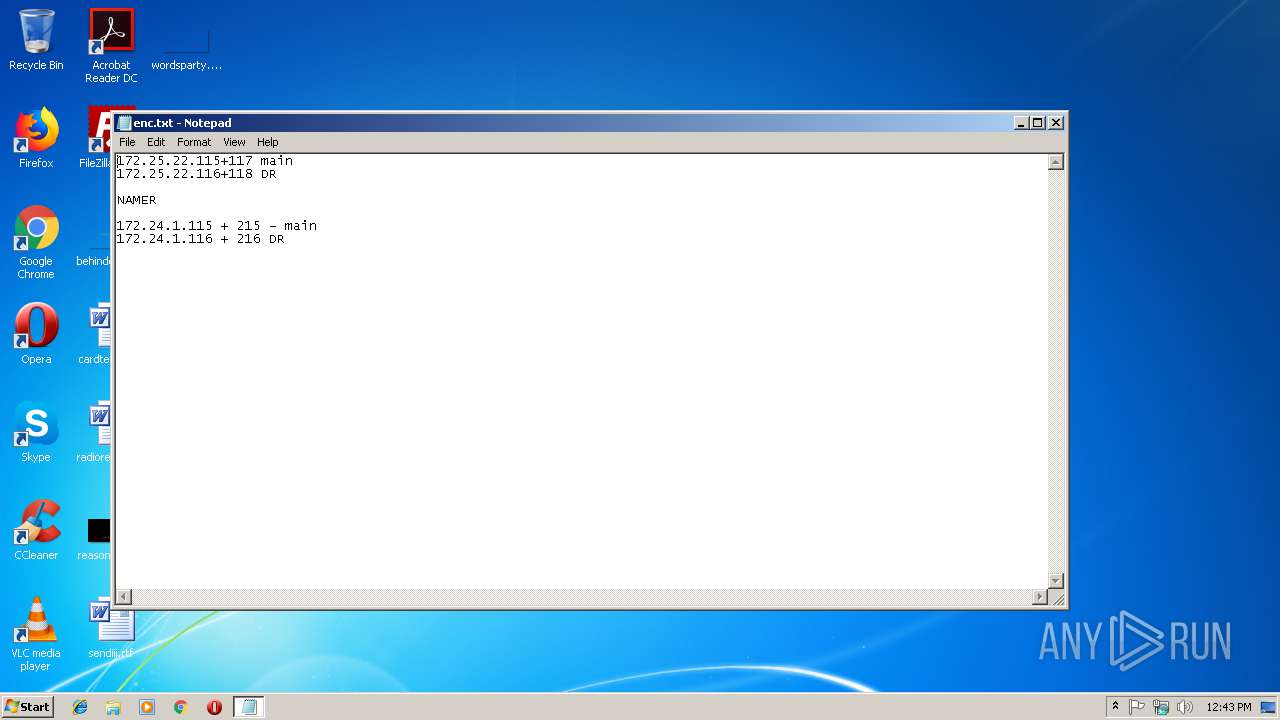
| File name: | enc.txt |
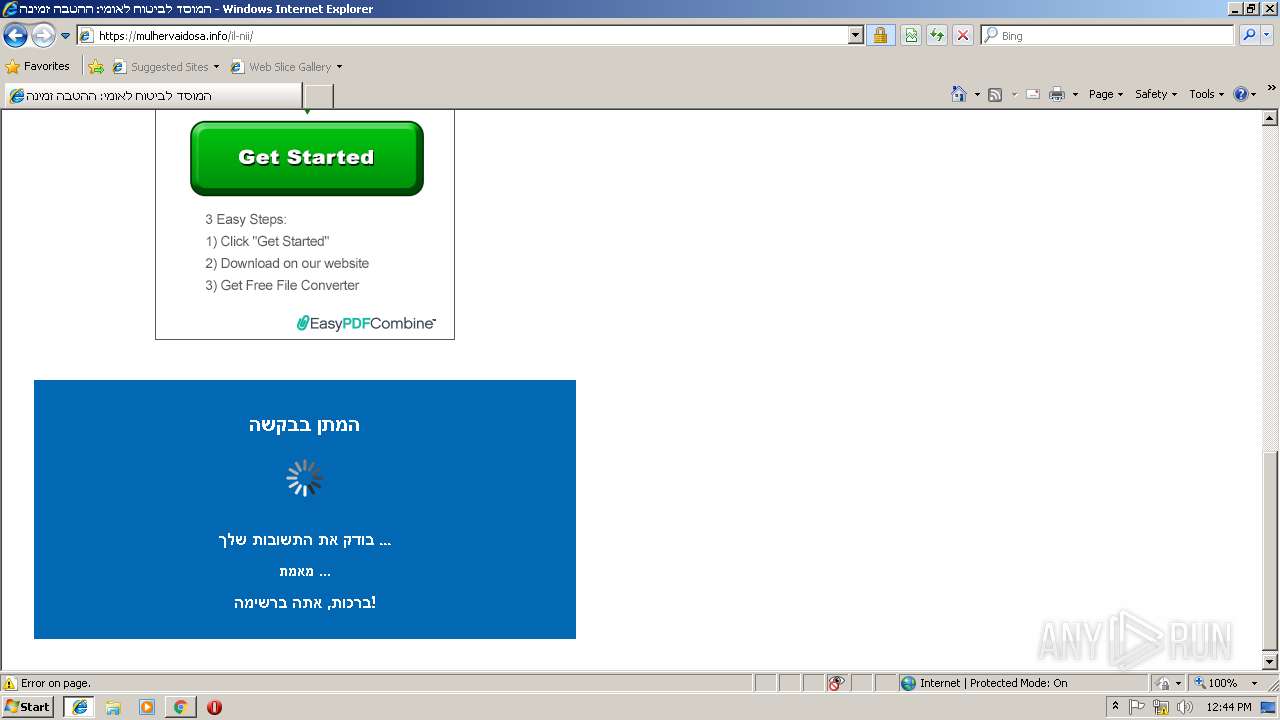
| Full analysis: | https://app.any.run/tasks/676905b1-d39c-4387-91b5-9544da6a469e |
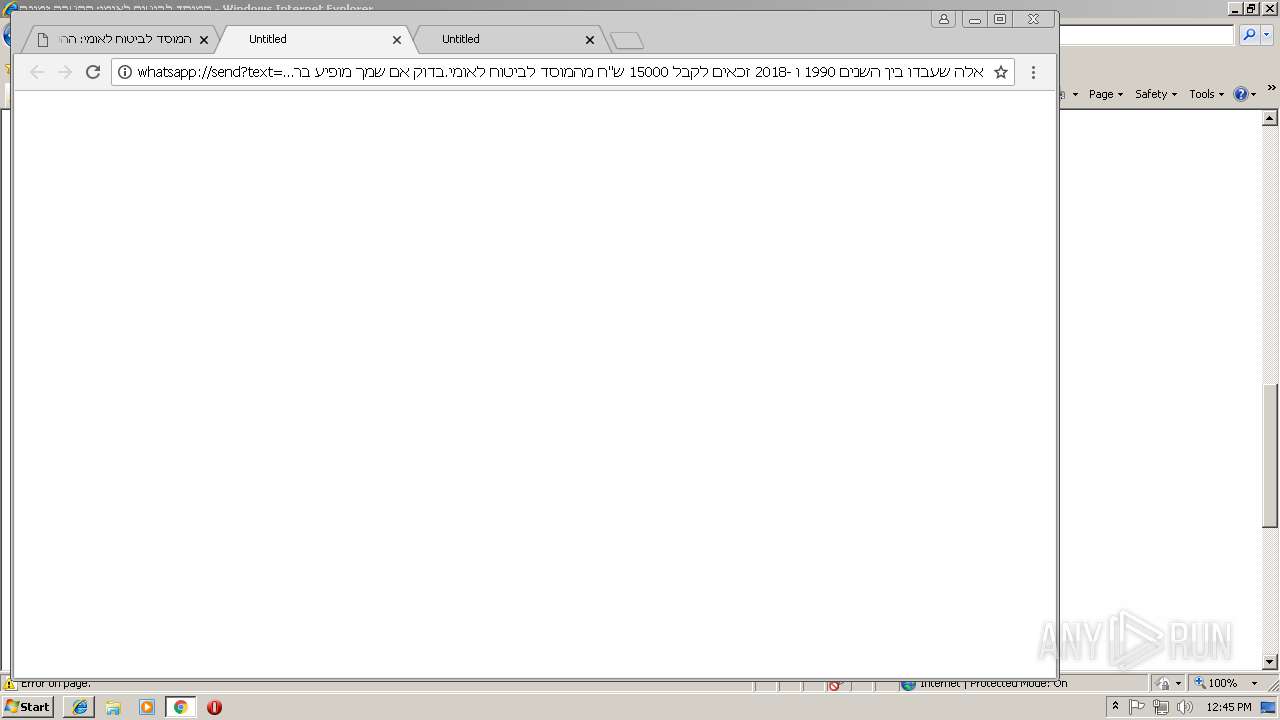
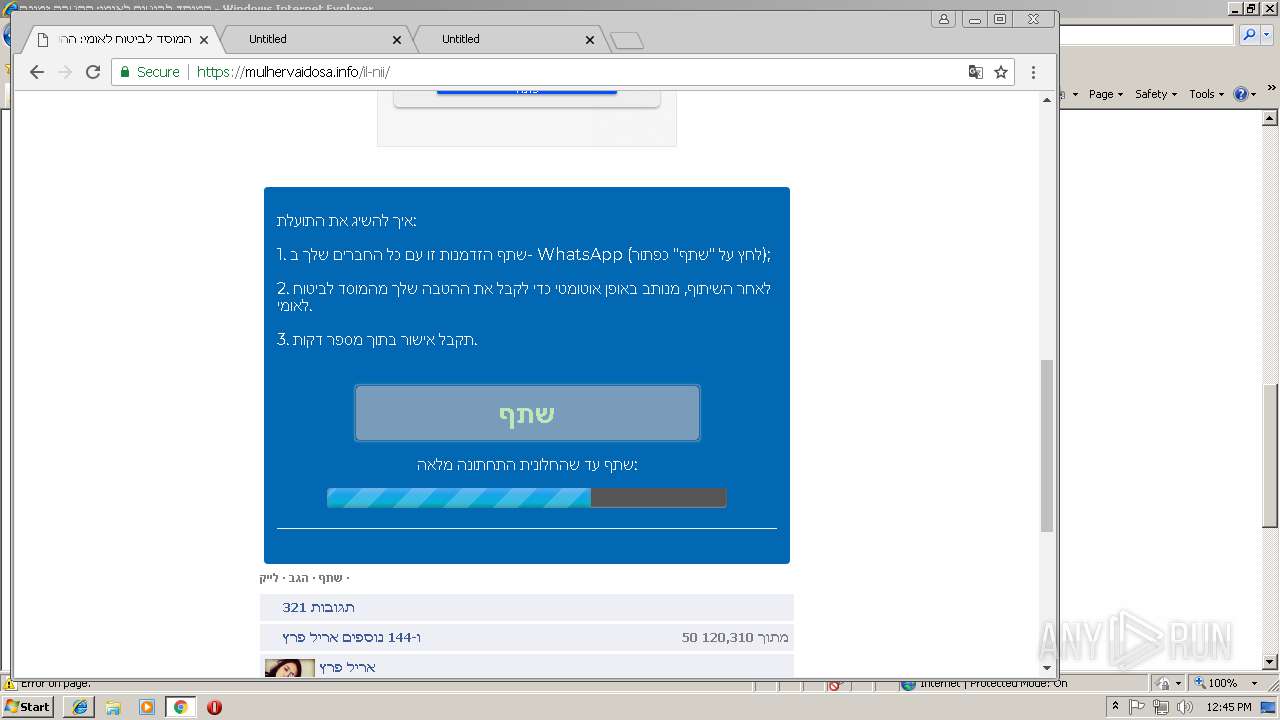
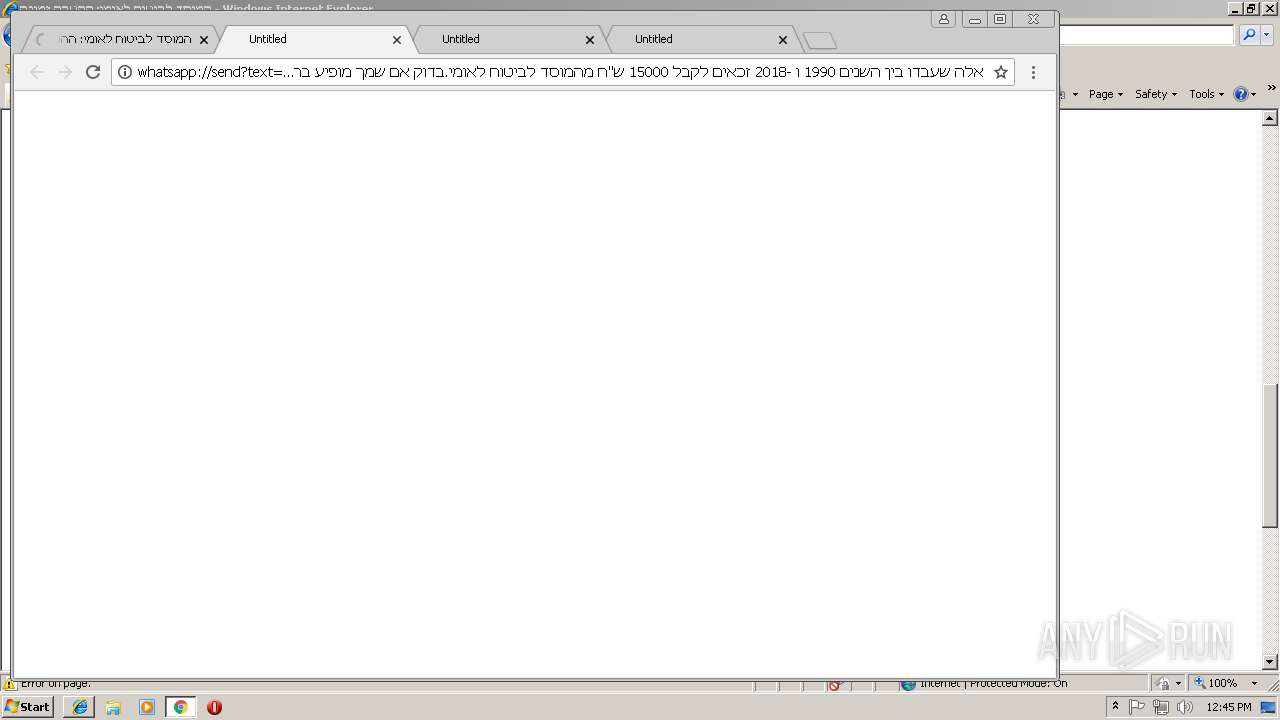
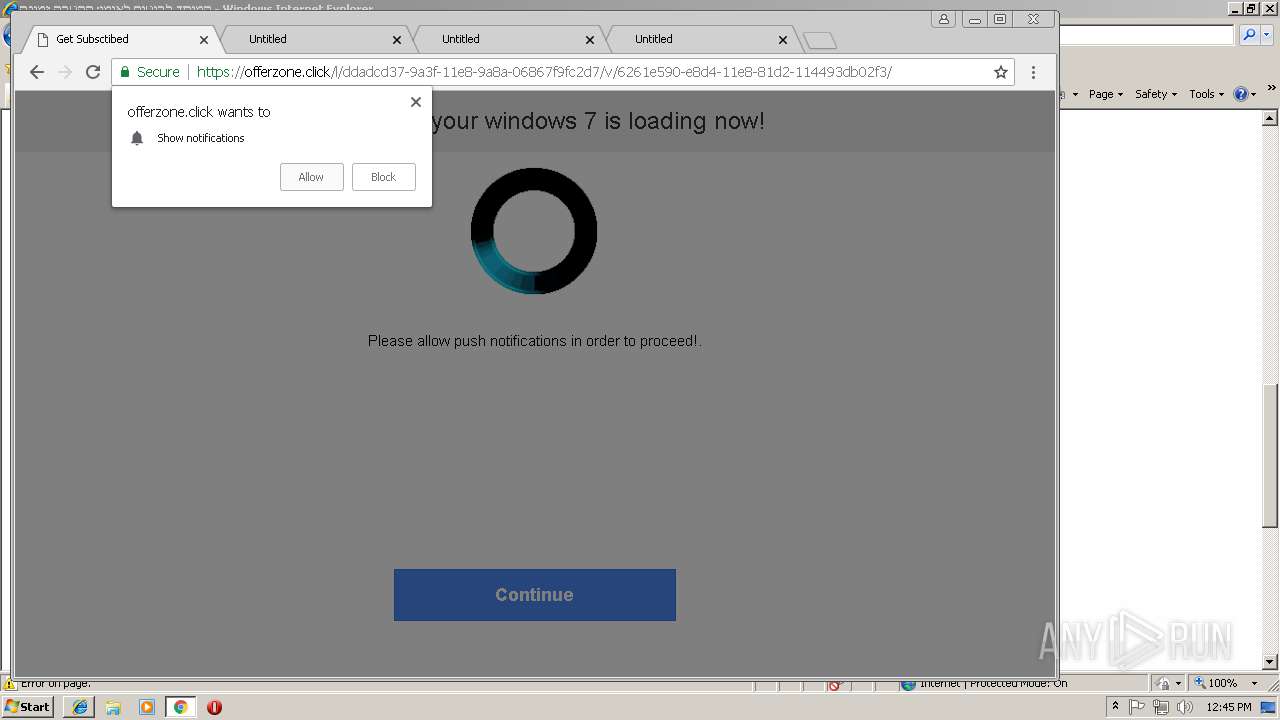
| Verdict: | Malicious activity |
| Analysis date: | November 15, 2018, 12:43:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with CRLF line terminators |
| MD5: | EBFE9851D68BEBCF06B8FE00D7576B49 |
| SHA1: | 5074317157B24A93BC56B1C9FC8D31CF1BC7BA86 |
| SHA256: | DCAA8CC76A2A55FC865CCD1D4A9583CC71C2D6765E60F408836293E8897414A8 |
| SSDEEP: | 3:LbXeXXRQHF5McT8LXXRTOD37zh8p/s8XMLy9uYvn:3XqOSp1W7+/sTouCn |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
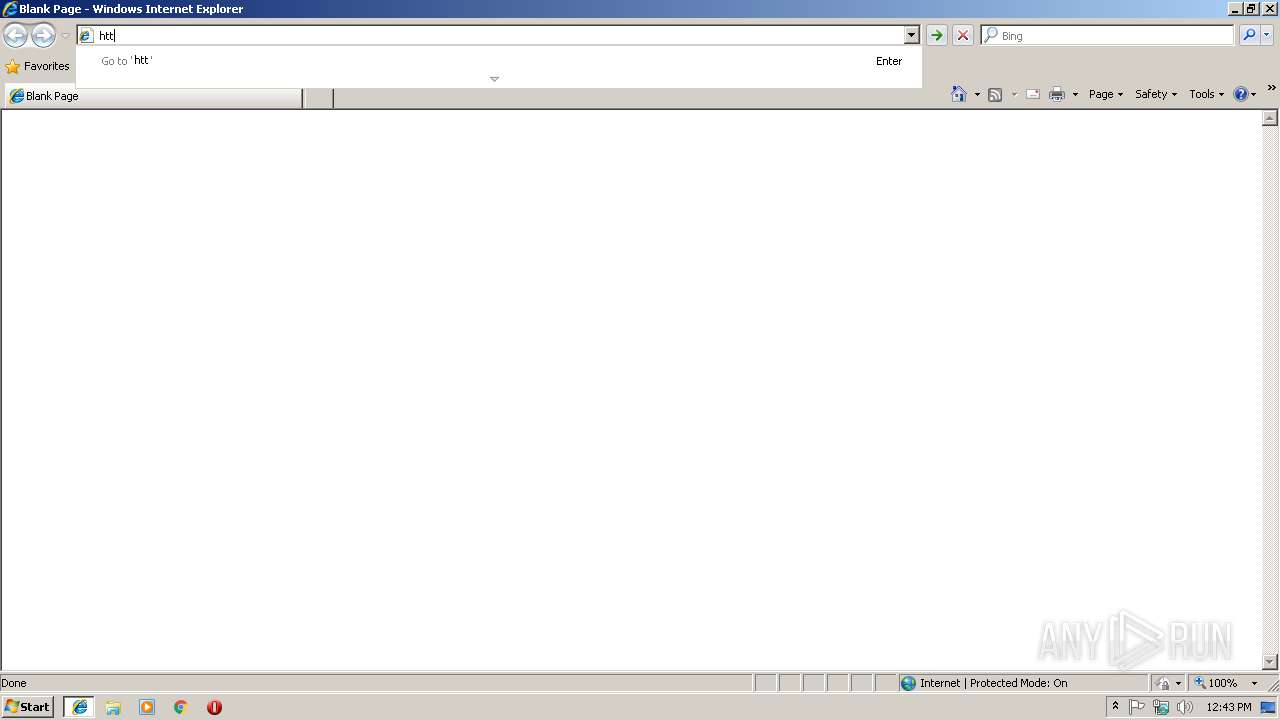
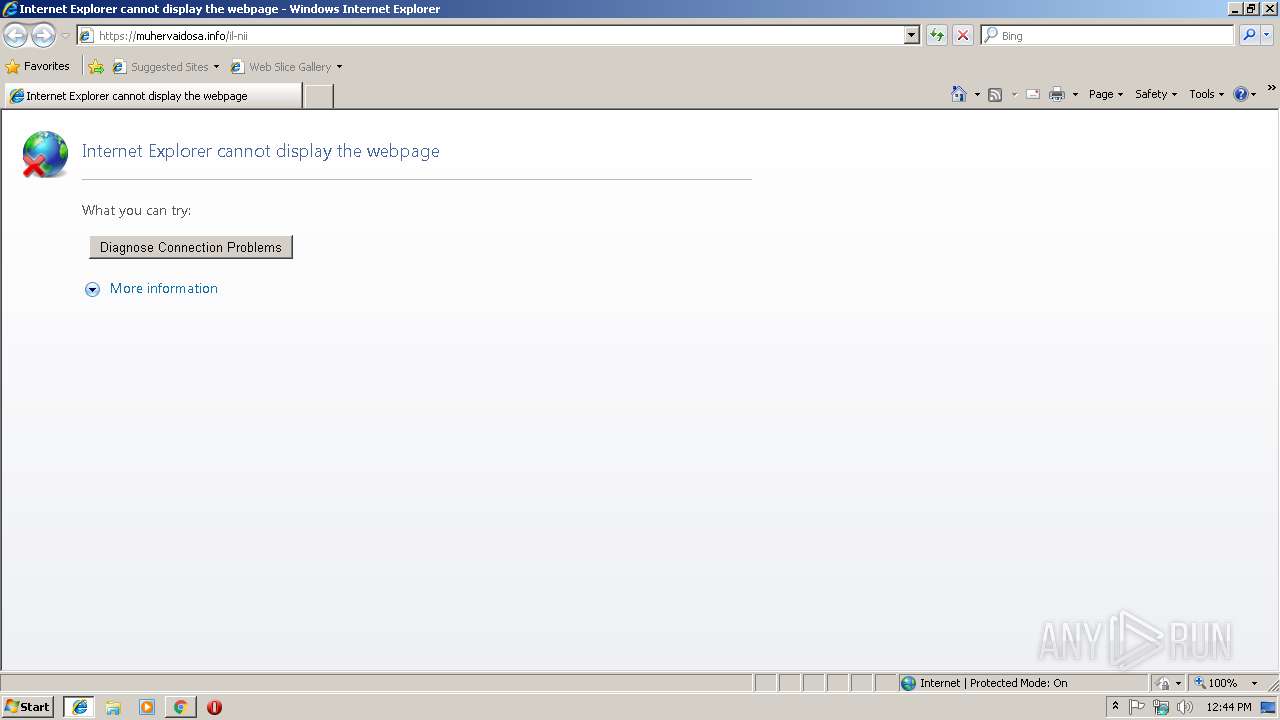
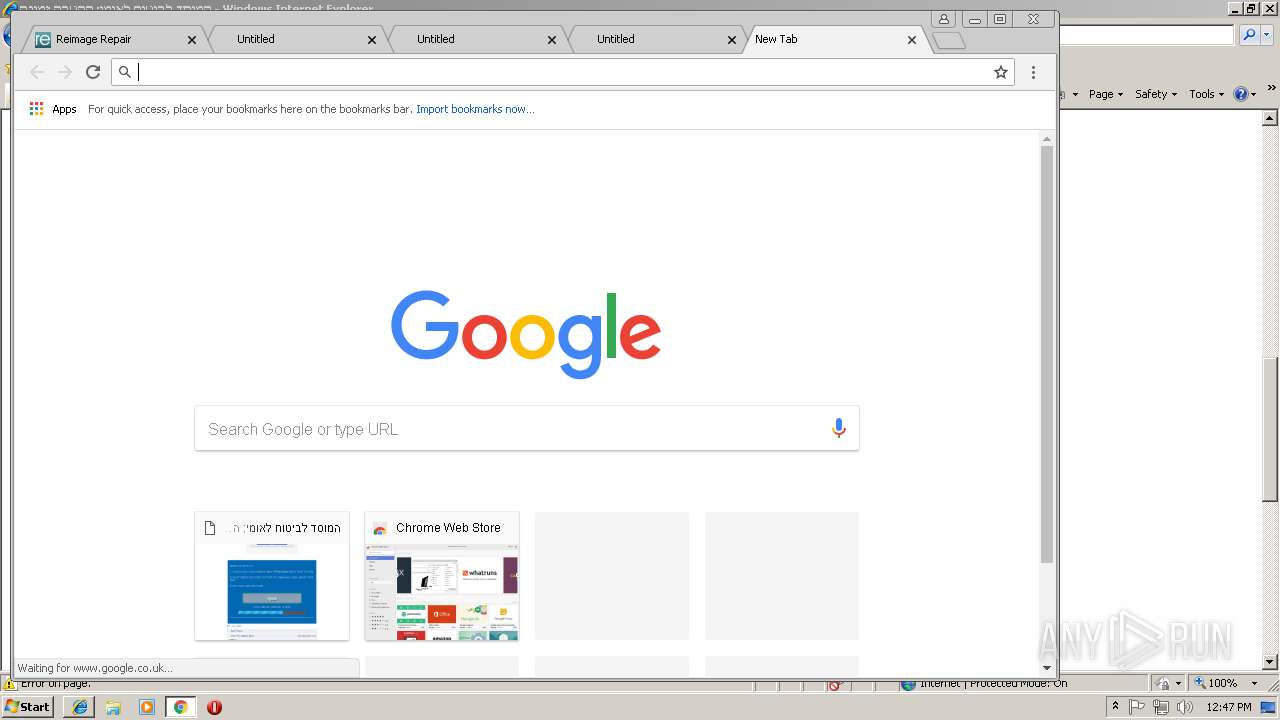
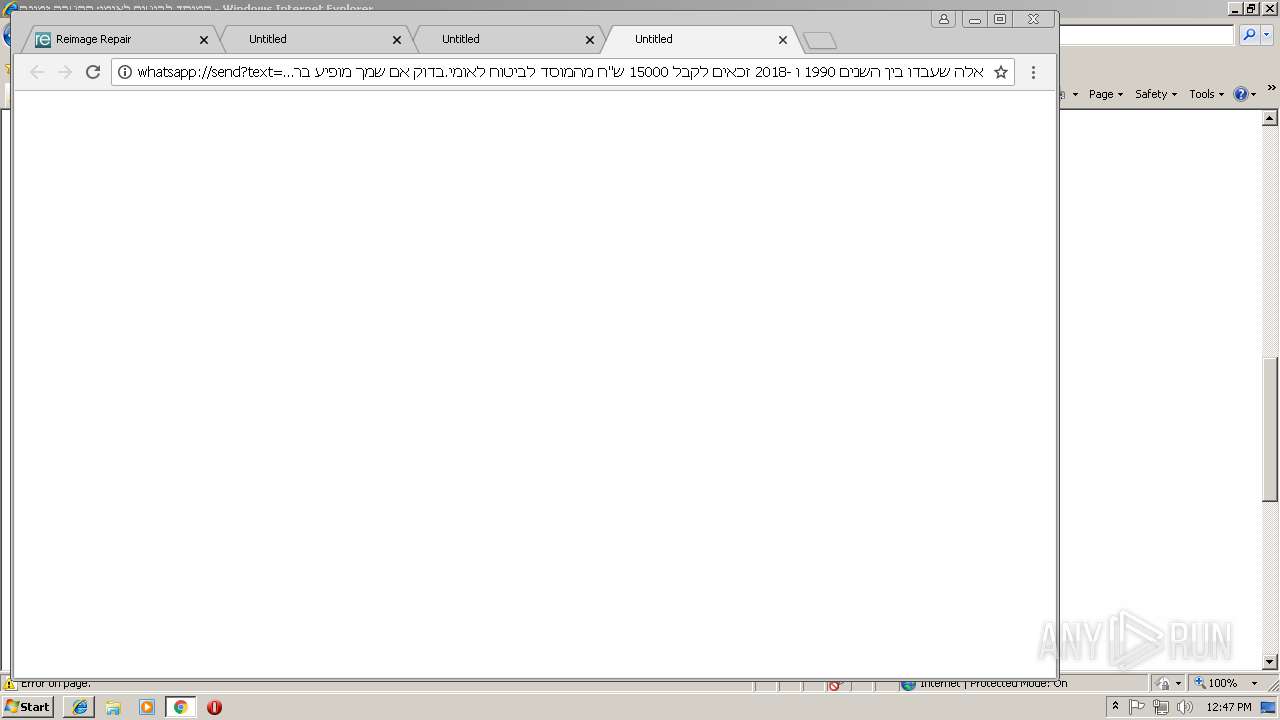
Application launched itself
- iexplore.exe (PID: 2460)
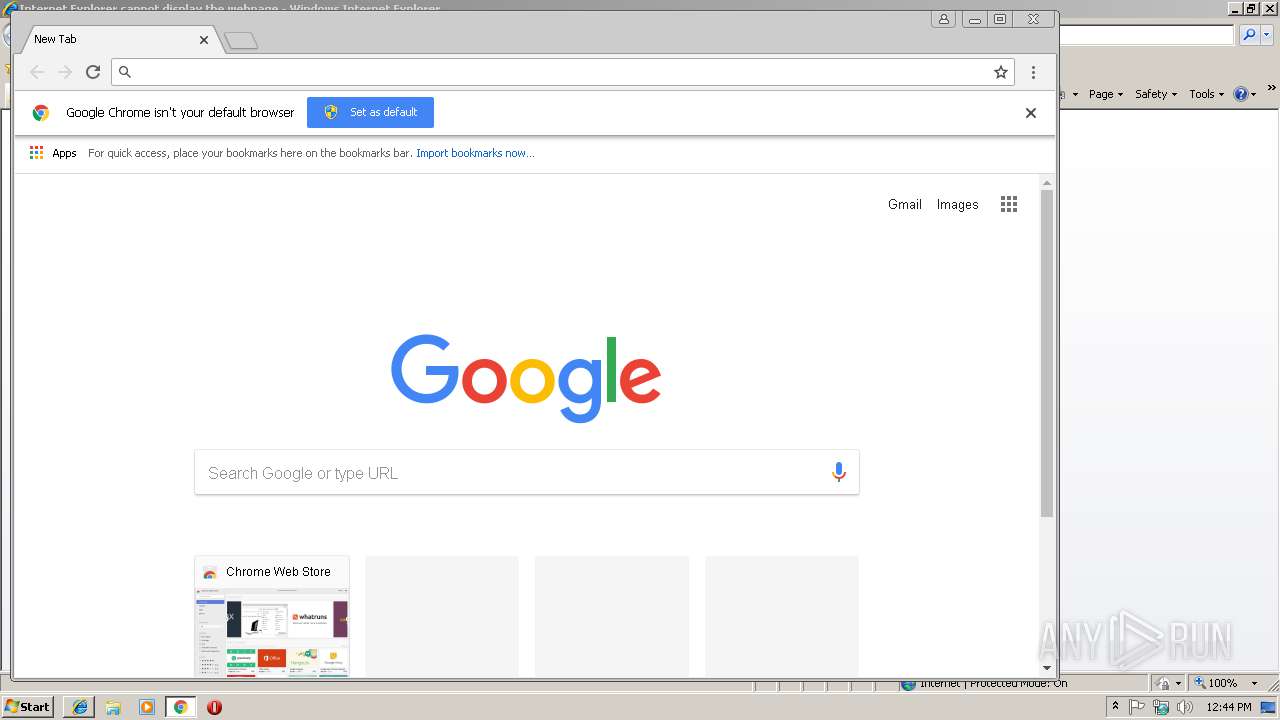
- chrome.exe (PID: 2612)
Changes internet zones settings
- iexplore.exe (PID: 2460)
Reads internet explorer settings
- iexplore.exe (PID: 3096)
Reads Internet Cache Settings
- iexplore.exe (PID: 3096)
- iexplore.exe (PID: 2460)
Creates files in the user directory
- iexplore.exe (PID: 3096)
- FlashUtil32_26_0_0_131_ActiveX.exe (PID: 2848)
- iexplore.exe (PID: 2460)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2460)
Reads settings of System Certificates
- iexplore.exe (PID: 2460)
Changes settings of System certificates
- iexplore.exe (PID: 2460)
Connects to unusual port
- chrome.exe (PID: 2612)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
52
Monitored processes
20
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 292 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,15401196795830850087,2884917718834361239,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6124EBE1E2E41F83E5CE2A0157FC24AF --mojo-platform-channel-handle=3792 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,15401196795830850087,2884917718834361239,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=40F33CF0565E65BB00BDB1F808A9D414 --mojo-platform-channel-handle=2668 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1436 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,15401196795830850087,2884917718834361239,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=A03989690C217132159BADBAD62B3003 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A03989690C217132159BADBAD62B3003 --renderer-client-id=14 --mojo-platform-channel-handle=2336 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1988 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=948,15401196795830850087,2884917718834361239,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=02EE18ADAAFB27A21476D6B4F0E81405 --mojo-platform-channel-handle=984 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,15401196795830850087,2884917718834361239,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=62689C3EB3DB618BD810BFE2F87D39F7 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=62689C3EB3DB618BD810BFE2F87D39F7 --renderer-client-id=9 --mojo-platform-channel-handle=3900 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2460 | "C:\Program Files\Internet Explorer\iexplore.exe" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2484 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,15401196795830850087,2884917718834361239,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=9A139DEBD7C13A96CA7DDDE985E3DDD6 --mojo-platform-channel-handle=3120 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2588 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,15401196795830850087,2884917718834361239,131072 --enable-features=PasswordImport --service-pipe-token=BED32BCFC8D38B01F4C041A69A91AB71 --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=BED32BCFC8D38B01F4C041A69A91AB71 --renderer-client-id=3 --mojo-platform-channel-handle=2084 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2612 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2780 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=948,15401196795830850087,2884917718834361239,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=E533662F3C533A769CD348F8B11E33A2 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=E533662F3C533A769CD348F8B11E33A2 --renderer-client-id=8 --mojo-platform-channel-handle=3928 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 086
Read events
921
Write events
158
Delete events
7
Modification events
| (PID) Process: | (3172) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosX |
Value: 110 | |||
| (PID) Process: | (3172) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosY |
Value: 110 | |||
| (PID) Process: | (3172) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDX |
Value: 960 | |||
| (PID) Process: | (3172) NOTEPAD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Notepad |
| Operation: | write | Name: | iWindowPosDY |
Value: 501 | |||
| (PID) Process: | (2460) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2460) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2460) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2460) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2460) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2460) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000069000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
Executable files
0
Suspicious files
119
Text files
188
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2460 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2460 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2460 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
| 2460 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\favicon[3].png | image | |
MD5:9FB559A691078558E77D6848202F6541 | SHA256:6D8A01DC7647BC218D003B58FE04049E24A9359900B7E0CEBAE76EDF85B8B914 | |||
| 2612 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:— | SHA256:— | |||
| 2612 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\d5b37cf3-b3ab-43ed-84e8-0373be7903cc.tmp | — | |
MD5:— | SHA256:— | |||
| 2612 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Download Service\EntryDB\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\PP6KS563\errorPageStrings[1] | text | |
MD5:1A0563F7FB85A678771450B131ED66FD | SHA256:EB5678DE9D8F29CA6893D4E6CA79BD5AB4F312813820FE4997B009A2B1A1654C | |||
| 2612 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000016.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3096 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\BWPPCY0O\httpErrorPagesScripts[1] | text | |
MD5:E7CA76A3C9EE0564471671D500E3F0F3 | SHA256:58268CA71A28973B756A48BBD7C9DC2F6B87B62AE343E582CE067C725275B63C | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
43
TCP/UDP connections
114
DNS requests
70
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
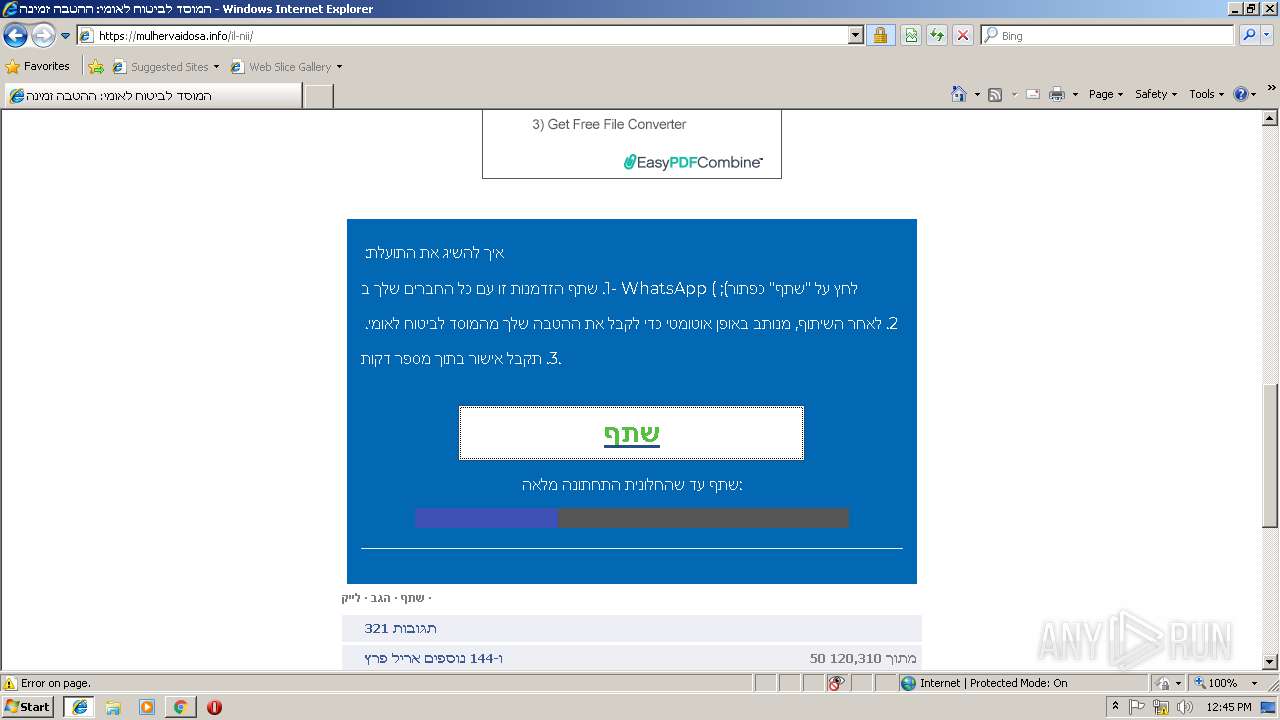
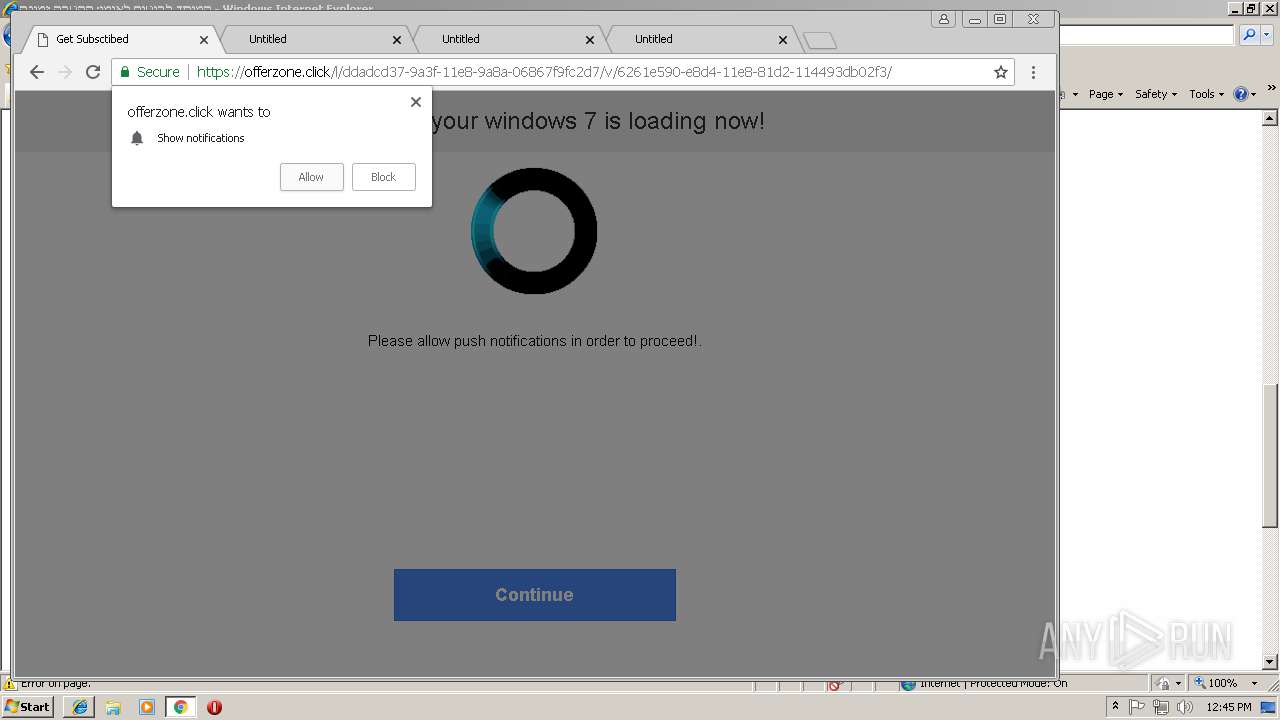
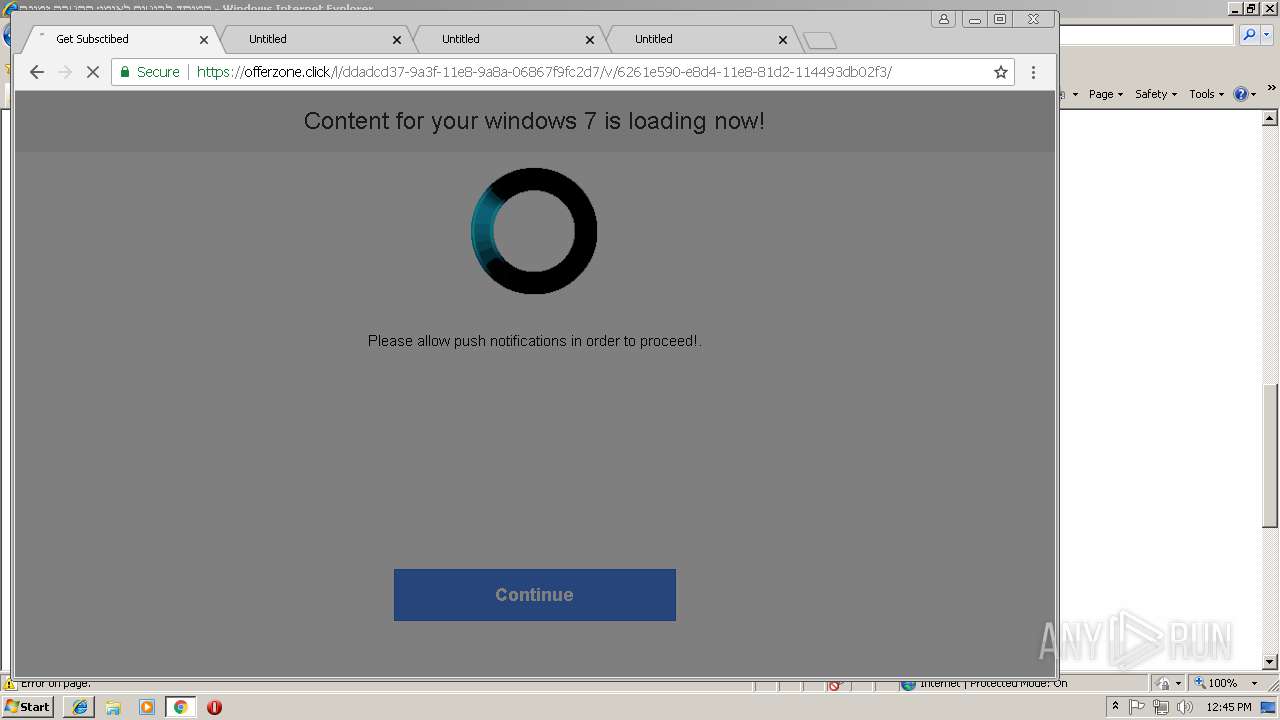
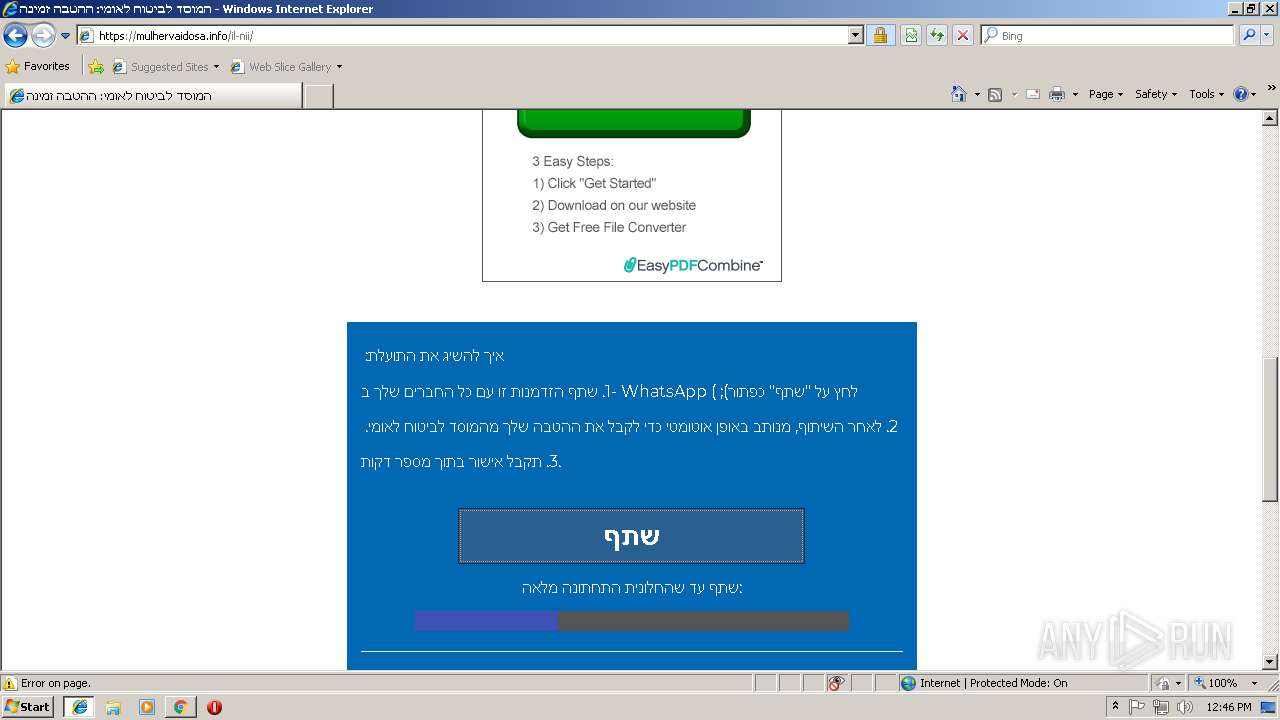
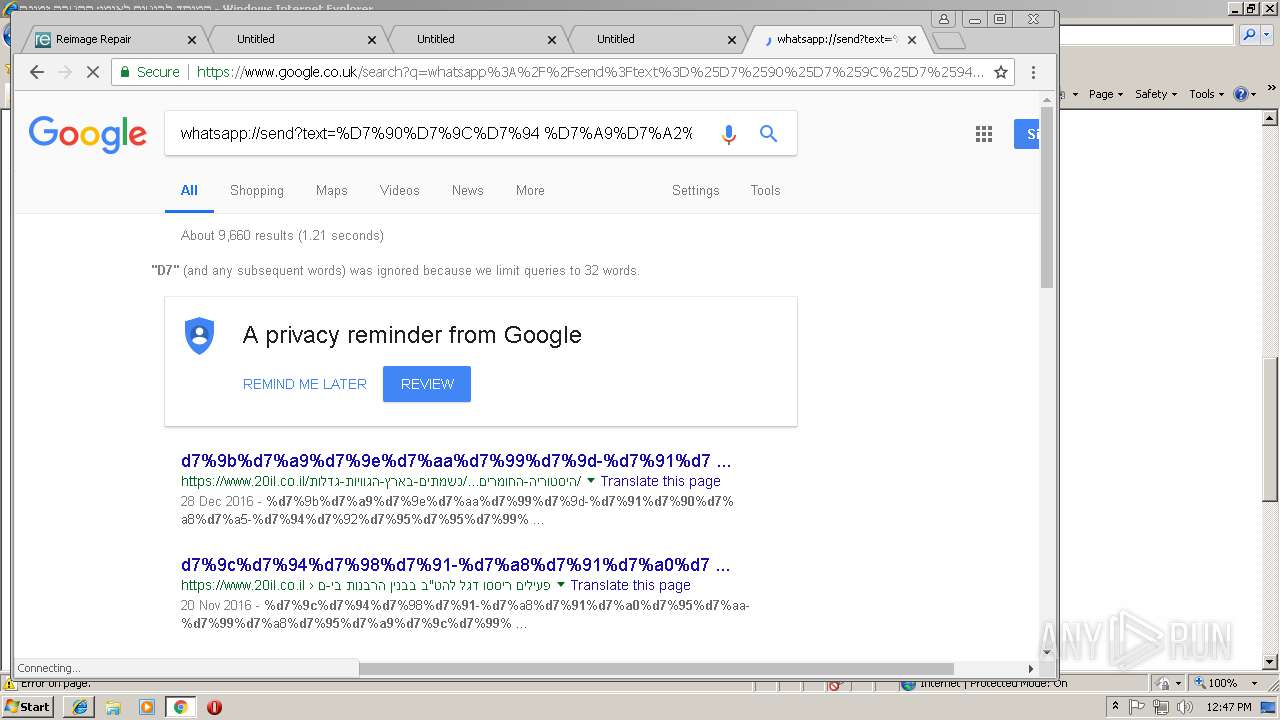
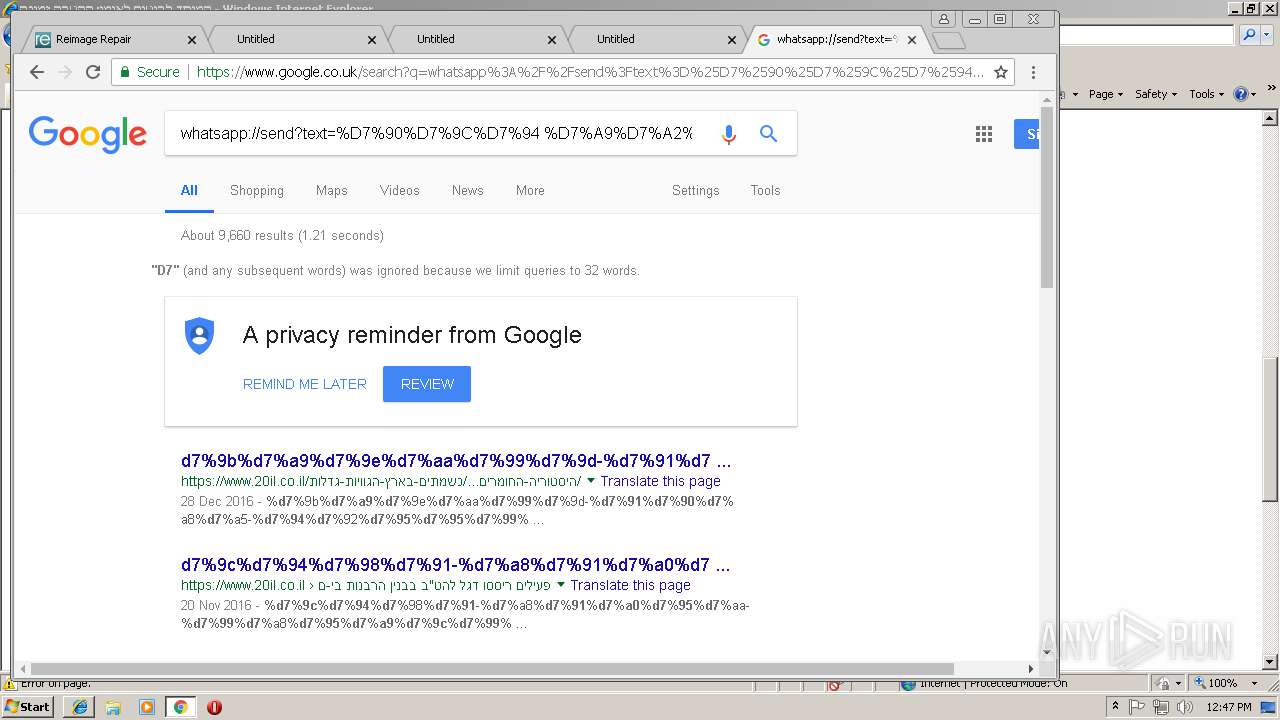
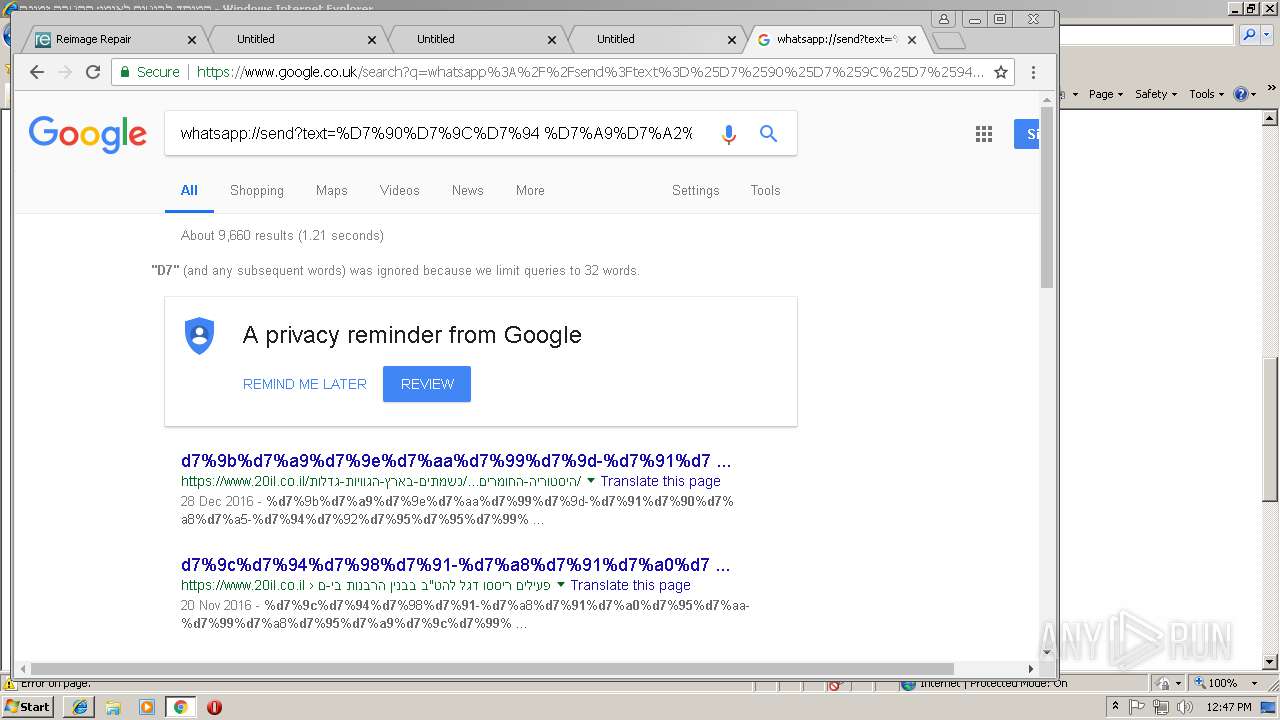
2612 | chrome.exe | GET | 302 | 191.96.104.10:80 | http://j1ti2.5515385.com/?s1=6261e590-e8d4-11e8-81d2-114493db02f3&noaudio=1&noalert=1&noexit=1&nodl=nodl&nopc=nopc&kw=370_c6f4be782b4b&_uu= | US | — | — | suspicious |
2612 | chrome.exe | GET | 200 | 52.85.245.199:80 | http://normour.com/r/6261e590-e8d4-11e8-81d2-114493db02f3/0/?_rh=6680uvW7QFSC0bOfJiXI0o4YLOjkauGWrBwbPZT21RKb8eZI3_954A7GkeqLgvkUn79cnagHkLTgg3K5UZhyUIFuucizm4mkJESnIuiznu4DVx69vykH3GpOyFsXKQdWtRGqhsVQv5Mdv38DoWqLoKiS3i6B-TRxvzEXtbUdEd1DlXHENXMABV_5stu0nnMGkoAgpDEfdCbiD18a-W9pFYR6L2IMoTqlh03zYrqsWFxk5s2wWNCLPcmsTB6cRCPhKeoBLD-fBTJSb0Nk7ymmJ8yAcyUNMv7zHLeKTibGq6t4Jy9cEELoPSda_dncXIfVL7UdjQbWo6AxixEBZg88nEF8EuWy_QqOjciF5LT-sG5d-t7AoKNLXHSHyX8TOJ6Kumywnw | US | html | 1.29 Kb | whitelisted |
2612 | chrome.exe | GET | 200 | 67.26.137.254:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | compressed | 54.4 Kb | whitelisted |
2612 | chrome.exe | GET | 200 | 52.85.245.199:80 | http://normour.com/r/6261e590-e8d4-11e8-81d2-114493db02f3/1/?_rh=9e31lVc_KLV8IZv8Z9QqNKBVwkfauGoUBkV_-B0ZNZ9mM-T6WNiexhUufmHwdd0Ok_o7xiIZ0rT6usJfPa5J__BCOMTqIMR5KJeFkdl4cbb_wgFeolOAMeAJ5p5_4mhWI523aH8e5HQecFLvoapWeTIPZZKAPbatbm66YxuYh6ZKUI8OK4owxKI7E3cT_-uKW1LYRlzgFIiwJIIEPkdly8Thlt0r9TS0djwkJFpu2pBMi5uWXdfRuYRZBQub7rlOMiYUOu2hSdAi_PEBBjQdtRWMO7pkwrc1OE8Mu4xP68eRHEoBHJIBg8dQacgKMIqSVCUY7Zh1s5NIuAU5WDjLE6QRqeQrxho3FSkCR_Ybf_hqpEAAIodDlGc9FhBUiKGdO-hJRQ | US | html | 89 b | whitelisted |
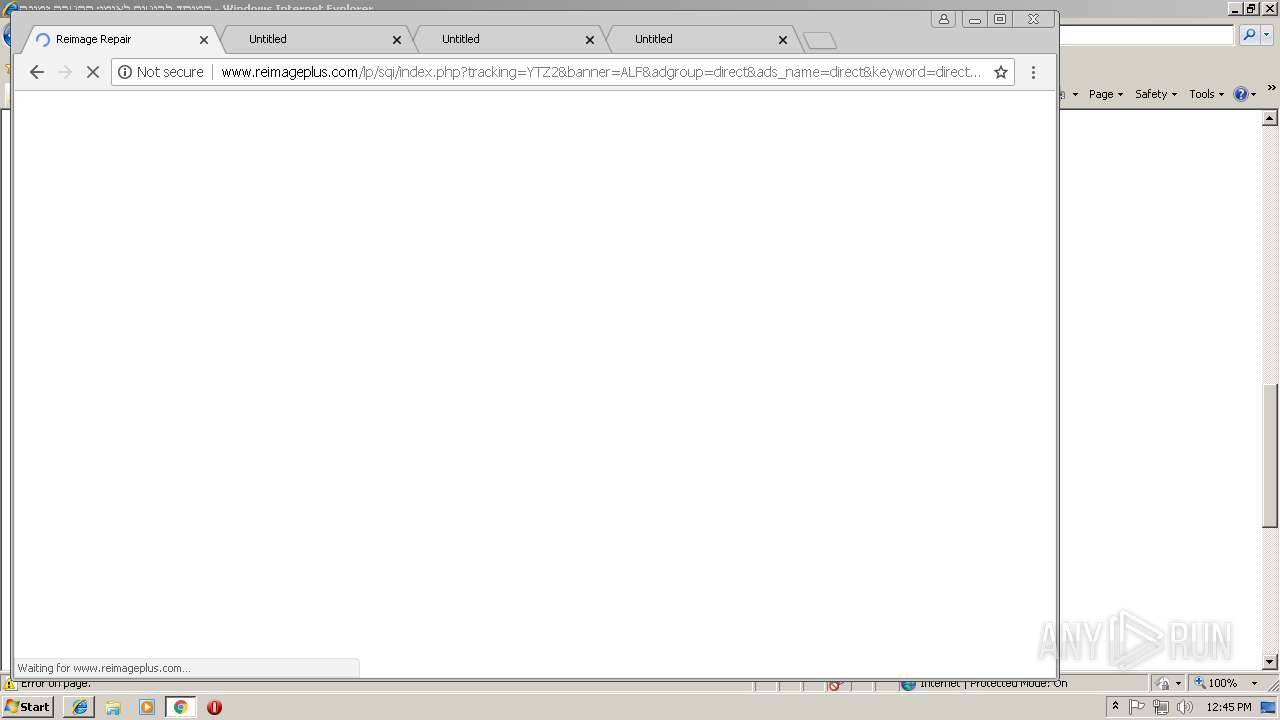
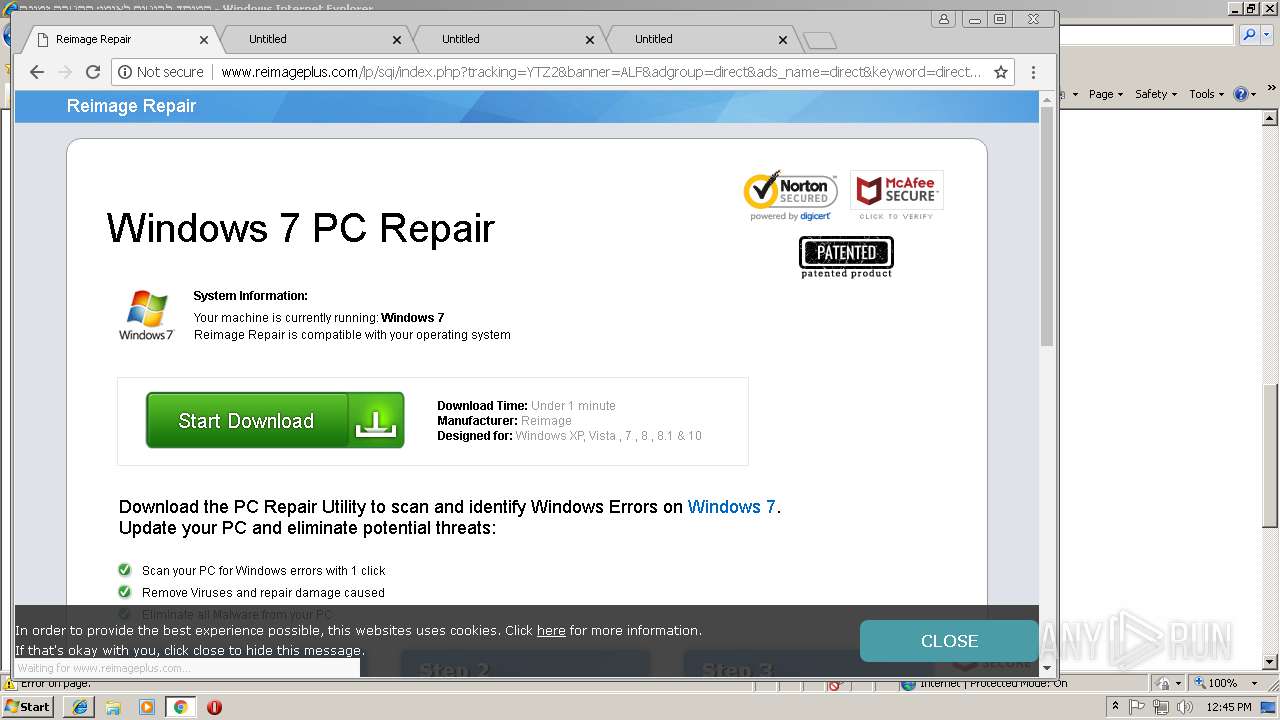
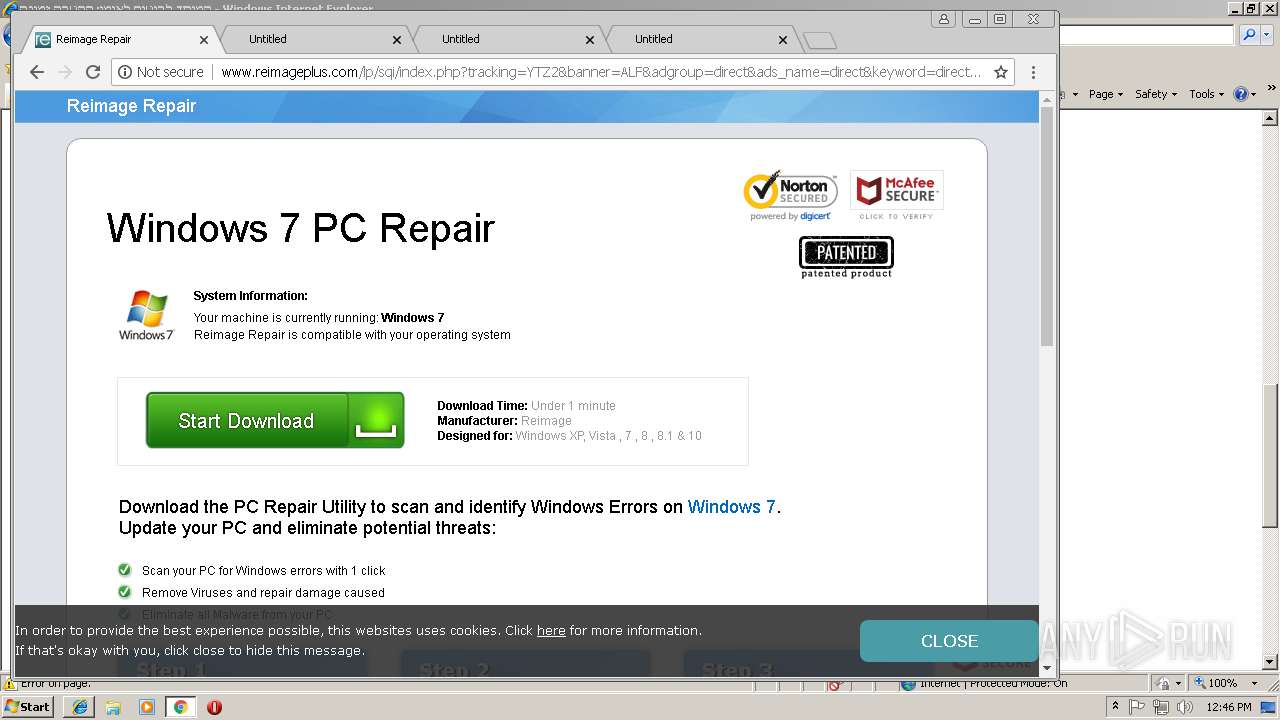
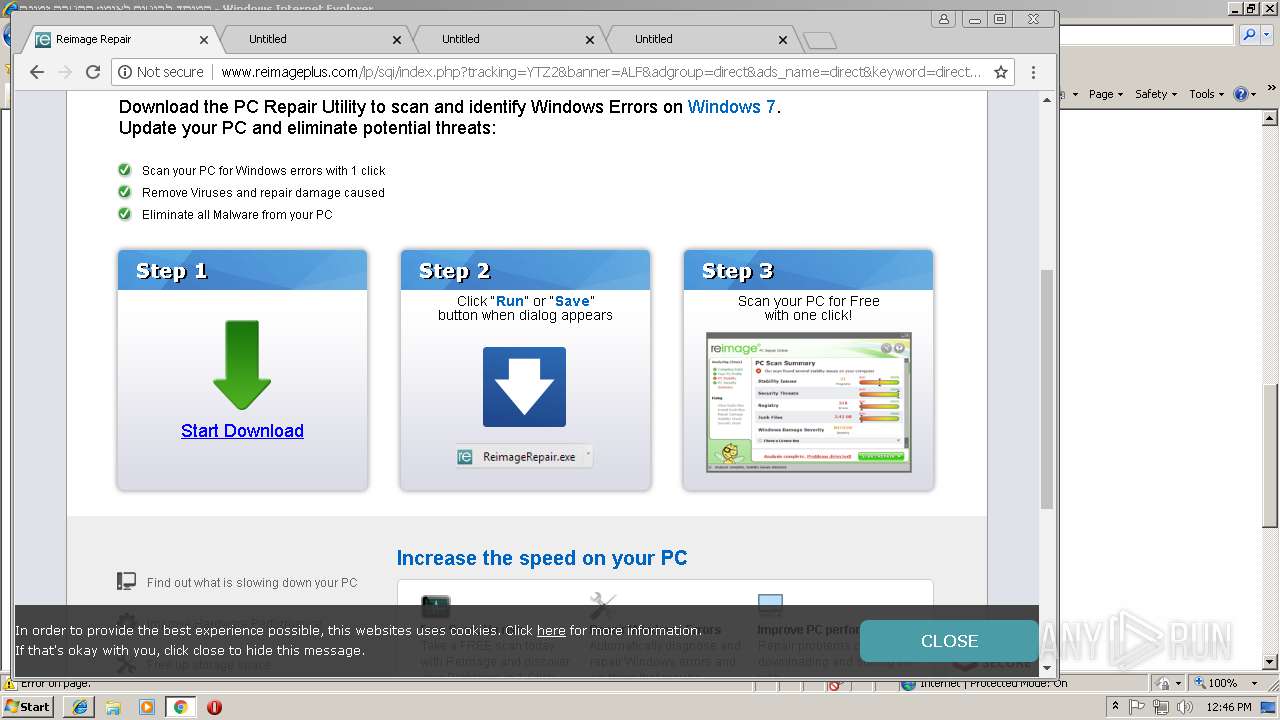
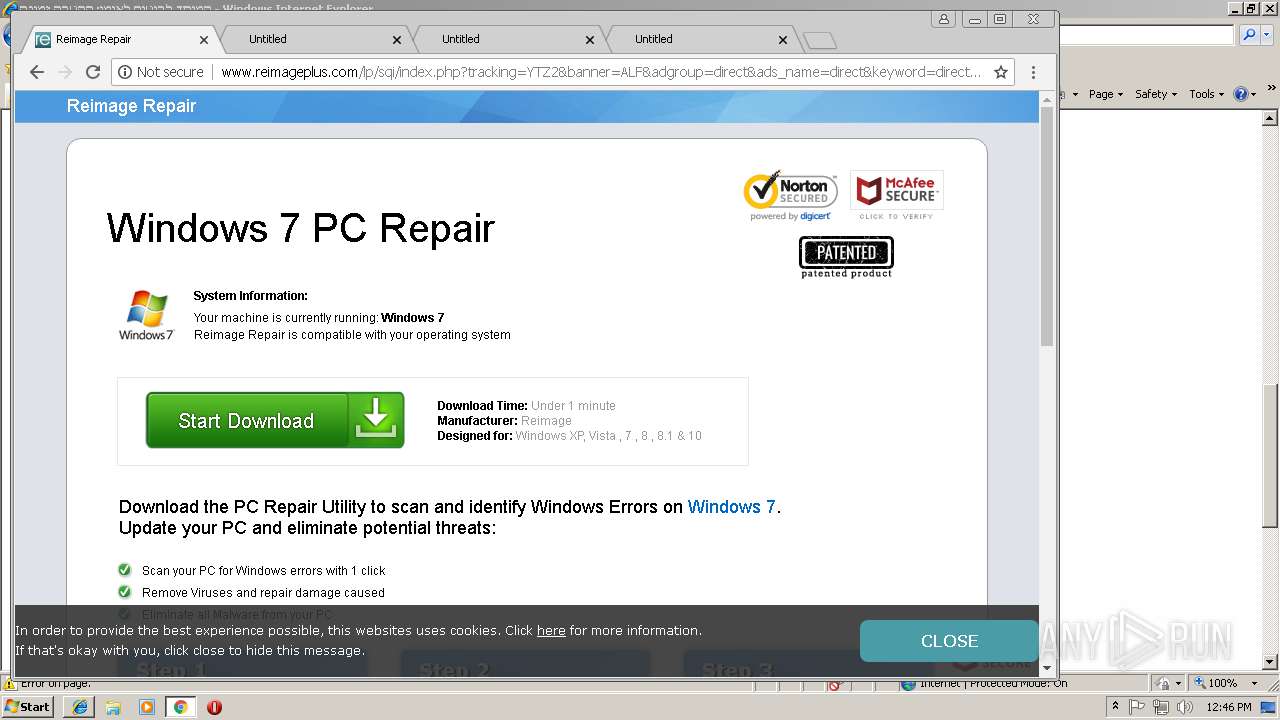
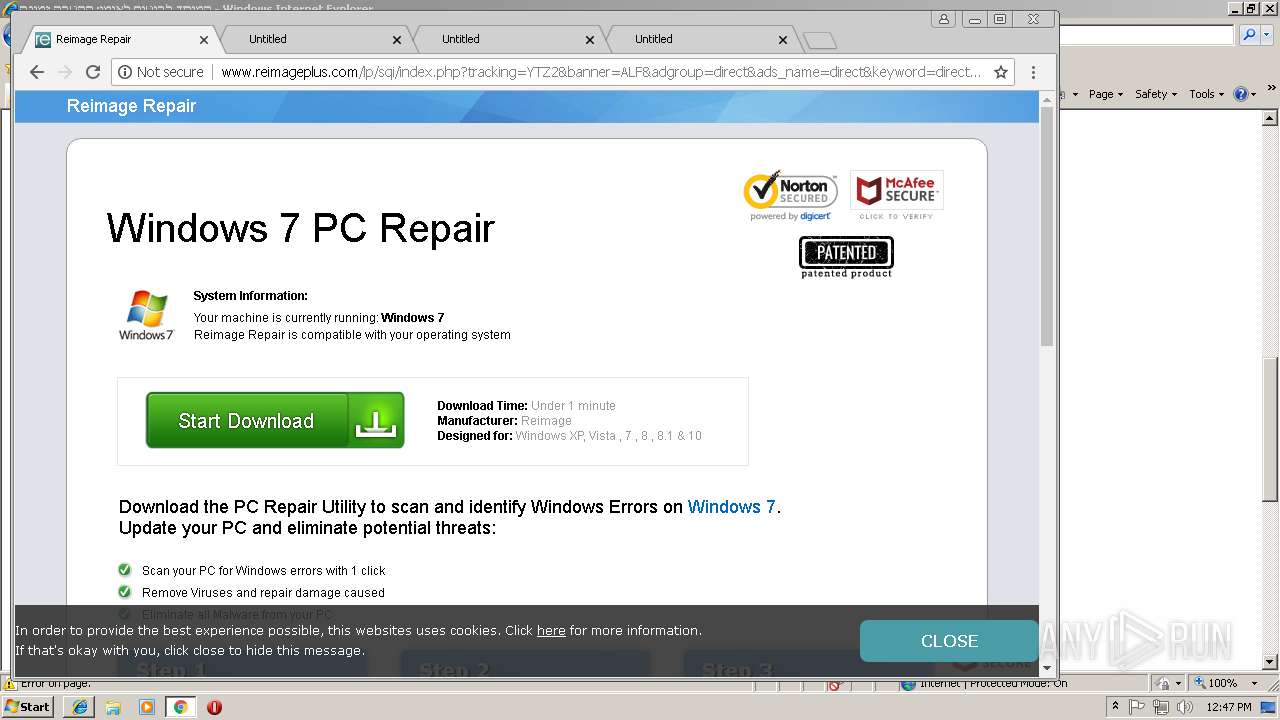
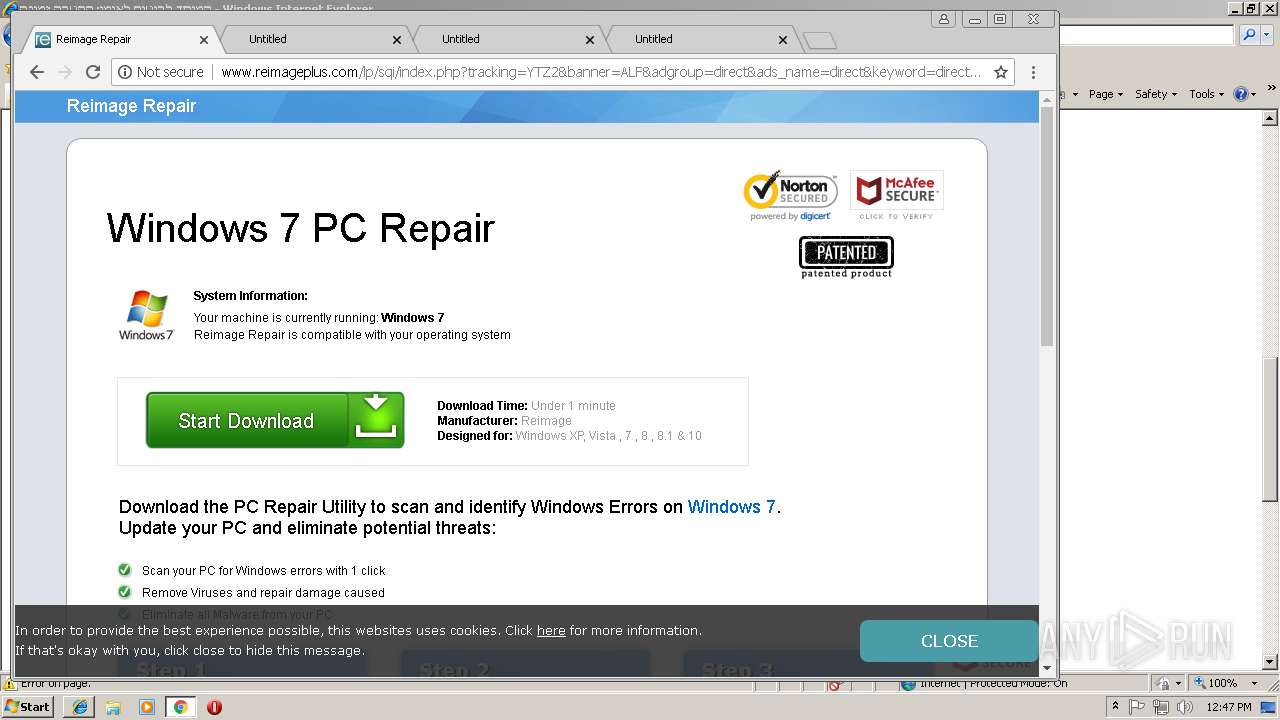
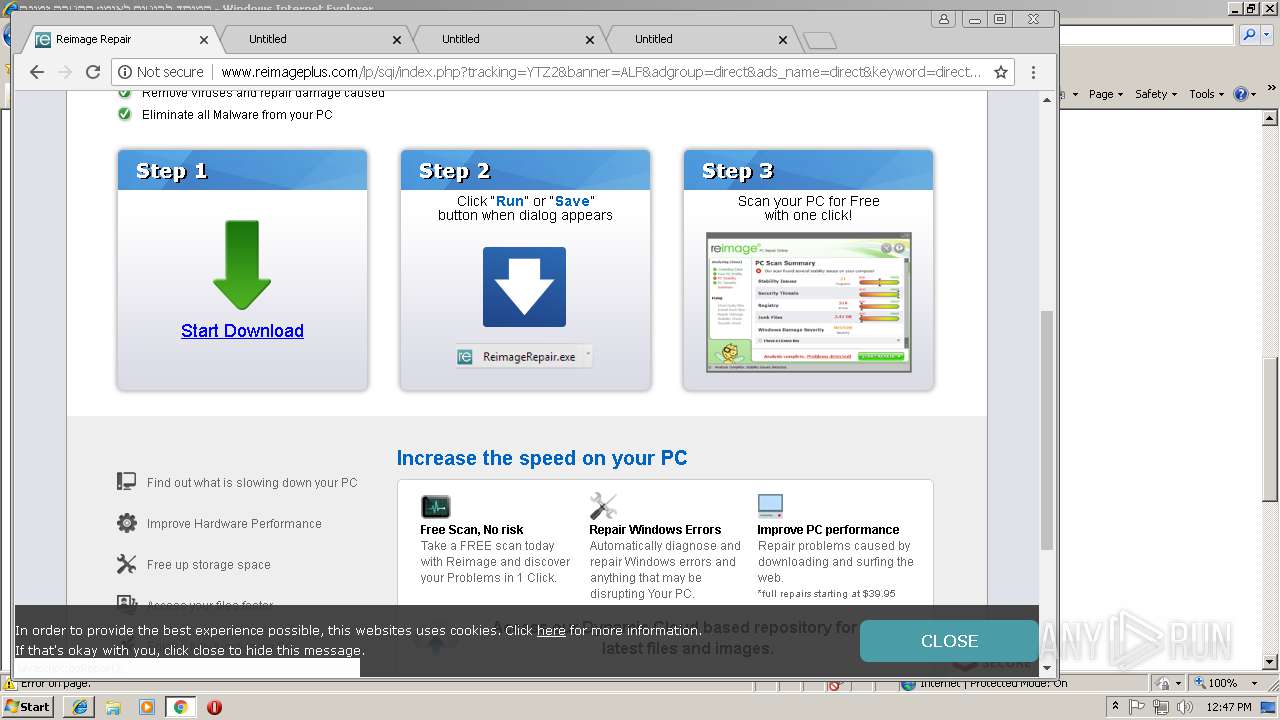
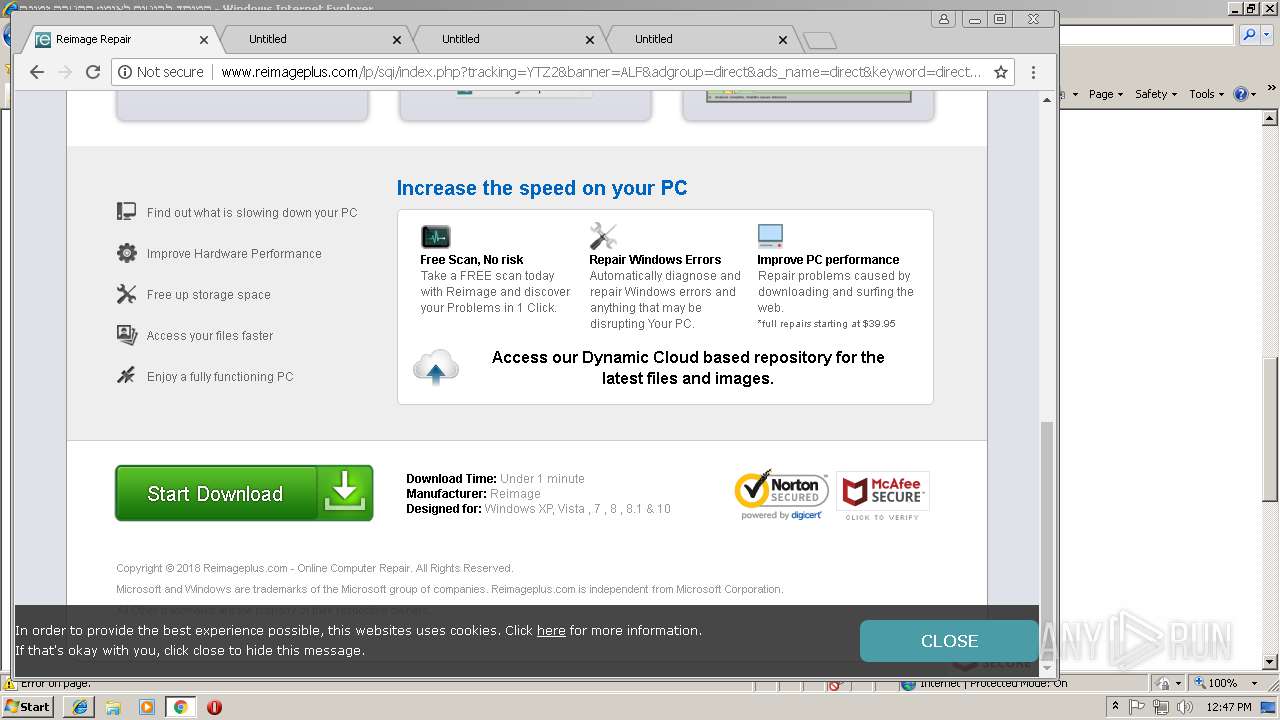
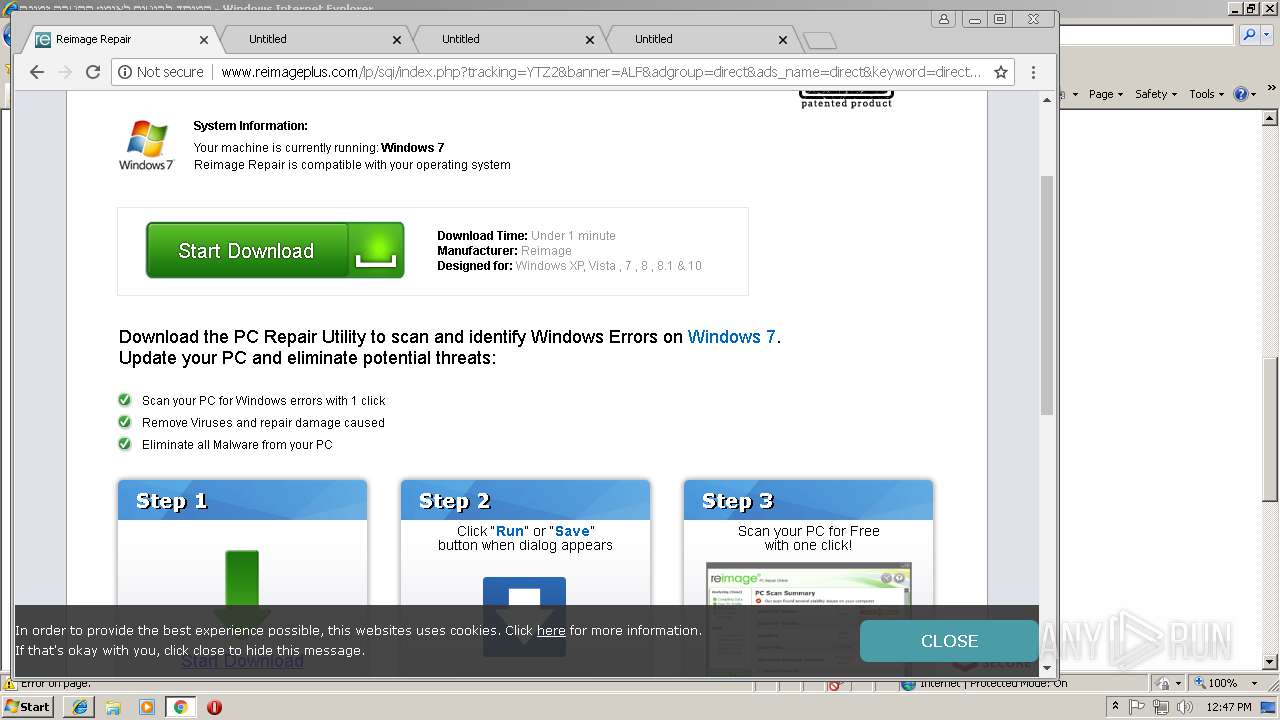
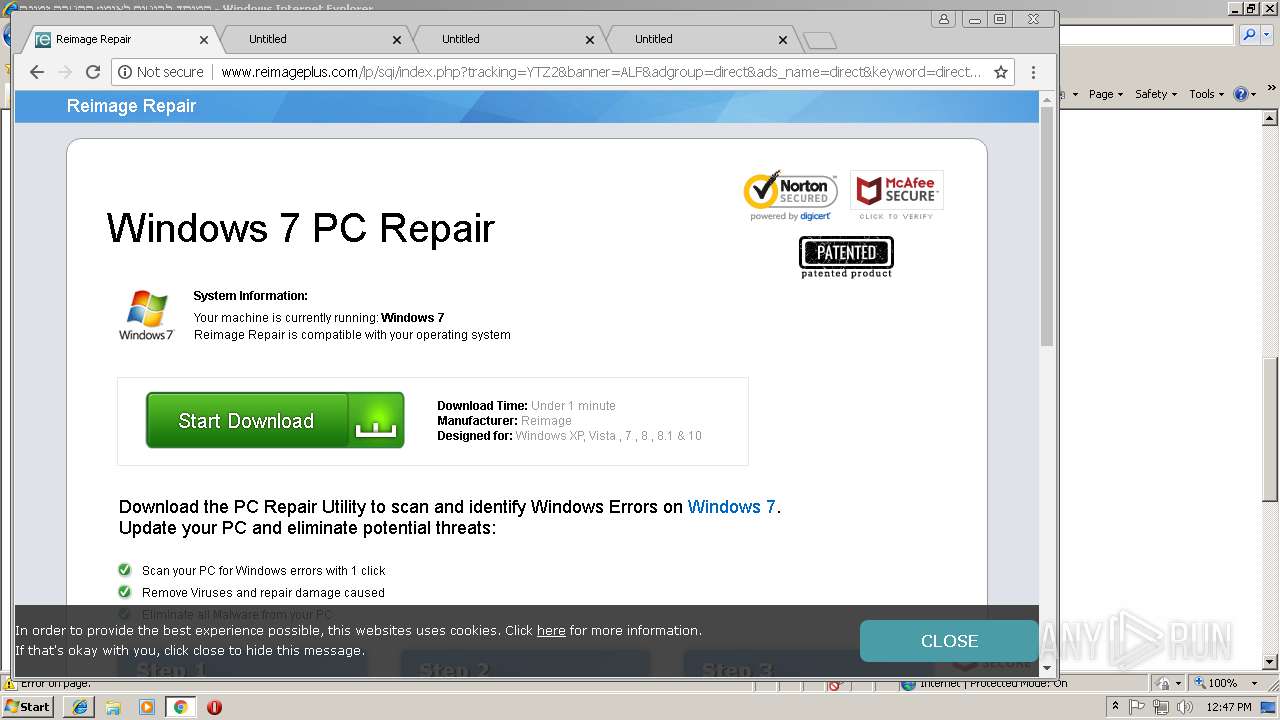
2612 | chrome.exe | GET | 200 | 161.47.7.14:80 | http://www.reimageplus.com/lp/sqi/index_src.php?tracking=YTZ2&banner=ALF&adgroup=direct&ads_name=direct&keyword=direct&nms=1&lpx=slm | US | html | 7.54 Kb | suspicious |
2612 | chrome.exe | GET | 200 | 216.58.208.34:80 | http://www.googleadservices.com/pagead/conversion.js | US | text | 8.97 Kb | whitelisted |
2612 | chrome.exe | GET | 200 | 161.47.7.14:80 | http://www.reimageplus.com/lp/sqi/index.php?tracking=YTZ2&banner=ALF&adgroup=direct&ads_name=direct&keyword=direct&nms=1&lpx=slm | US | html | 3.84 Kb | suspicious |
2612 | chrome.exe | GET | 200 | 161.47.7.14:80 | http://www.reimageplus.com/lp/sqi/css/style.css | US | text | 2.33 Kb | suspicious |
2612 | chrome.exe | GET | 200 | 161.47.7.14:80 | http://www.reimageplus.com/assets/styles/jquery.fancybox/jquery.fancybox-2.css | US | text | 1.57 Kb | suspicious |
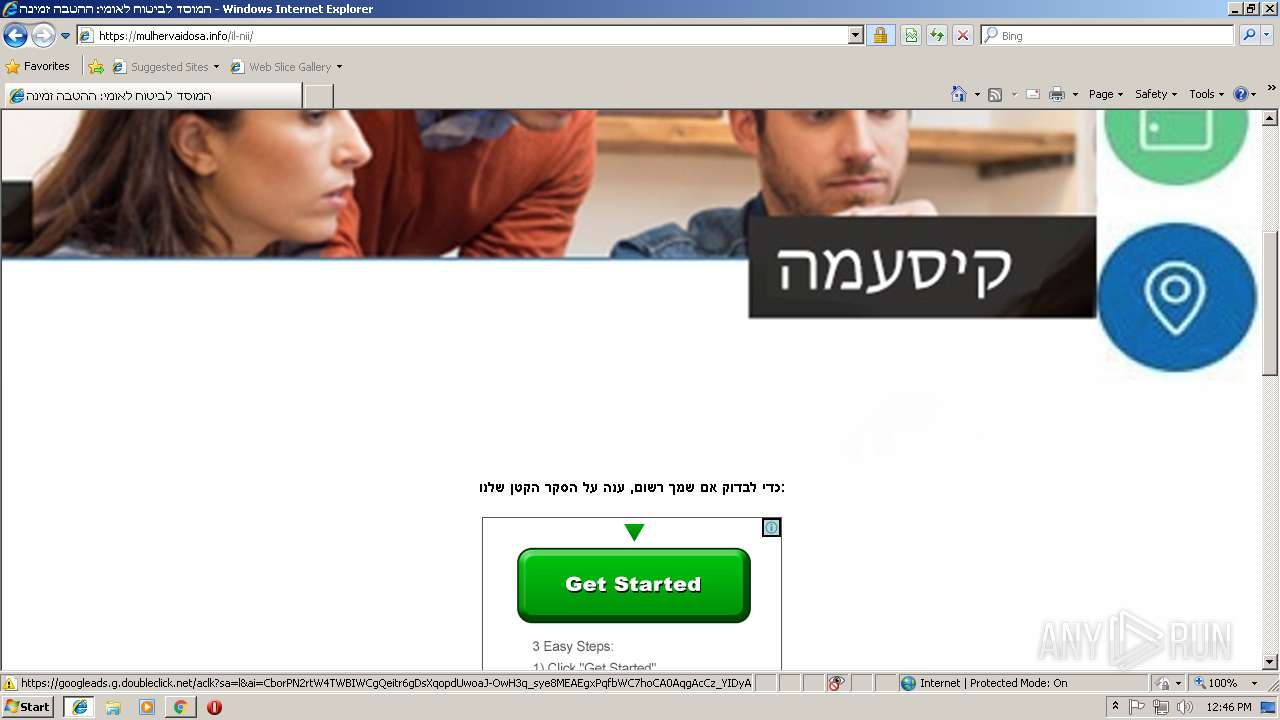
2612 | chrome.exe | GET | 200 | 205.185.208.80:80 | http://cdnrep.reimageplus.com/website/newwebsite/lp/sqh/page-header.png | US | image | 27.5 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3096 | iexplore.exe | 104.16.206.165:443 | cdn.onesignal.com | Cloudflare Inc | US | shared |
2612 | chrome.exe | 209.197.3.15:443 | maxcdn.bootstrapcdn.com | Highwinds Network Group, Inc. | US | whitelisted |
2612 | chrome.exe | 216.58.206.8:443 | www.googletagmanager.com | Google Inc. | US | whitelisted |
2460 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2612 | chrome.exe | 216.58.206.3:443 | www.gstatic.com | Google Inc. | US | whitelisted |
2612 | chrome.exe | 172.217.18.3:443 | www.google.de | Google Inc. | US | whitelisted |
2612 | chrome.exe | 216.58.206.10:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2612 | chrome.exe | 216.58.206.14:443 | apis.google.com | Google Inc. | US | whitelisted |
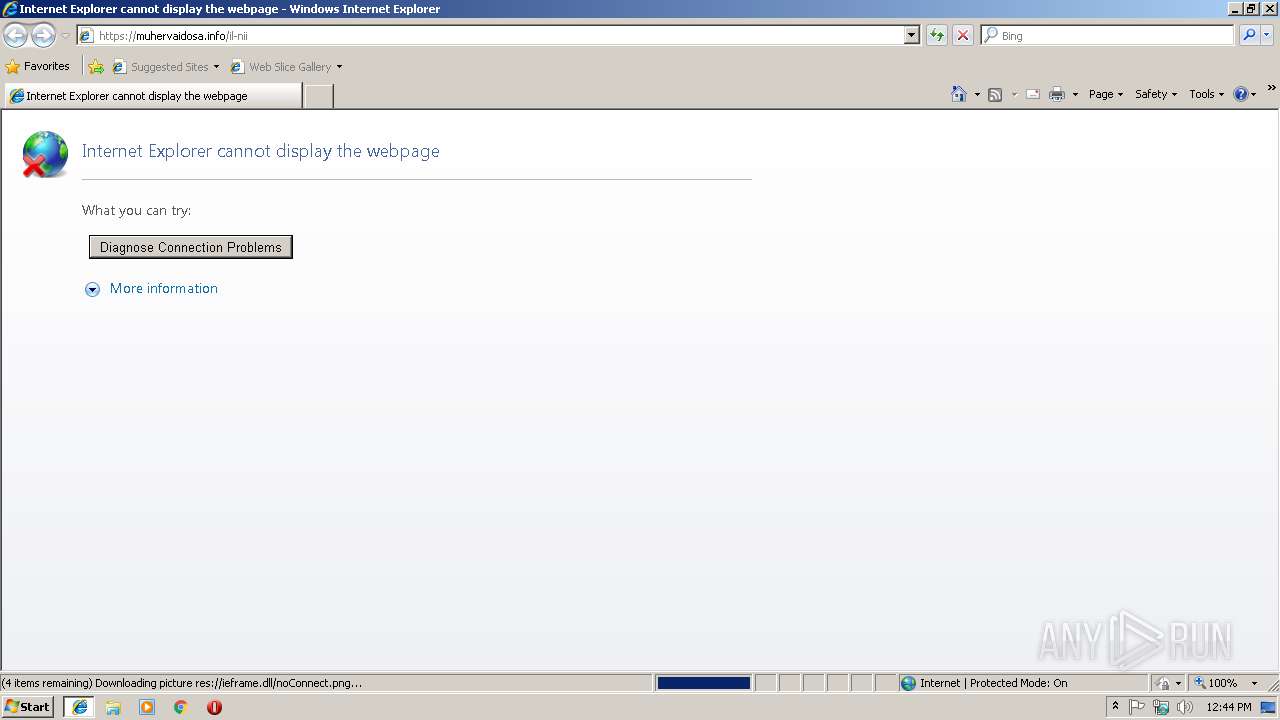
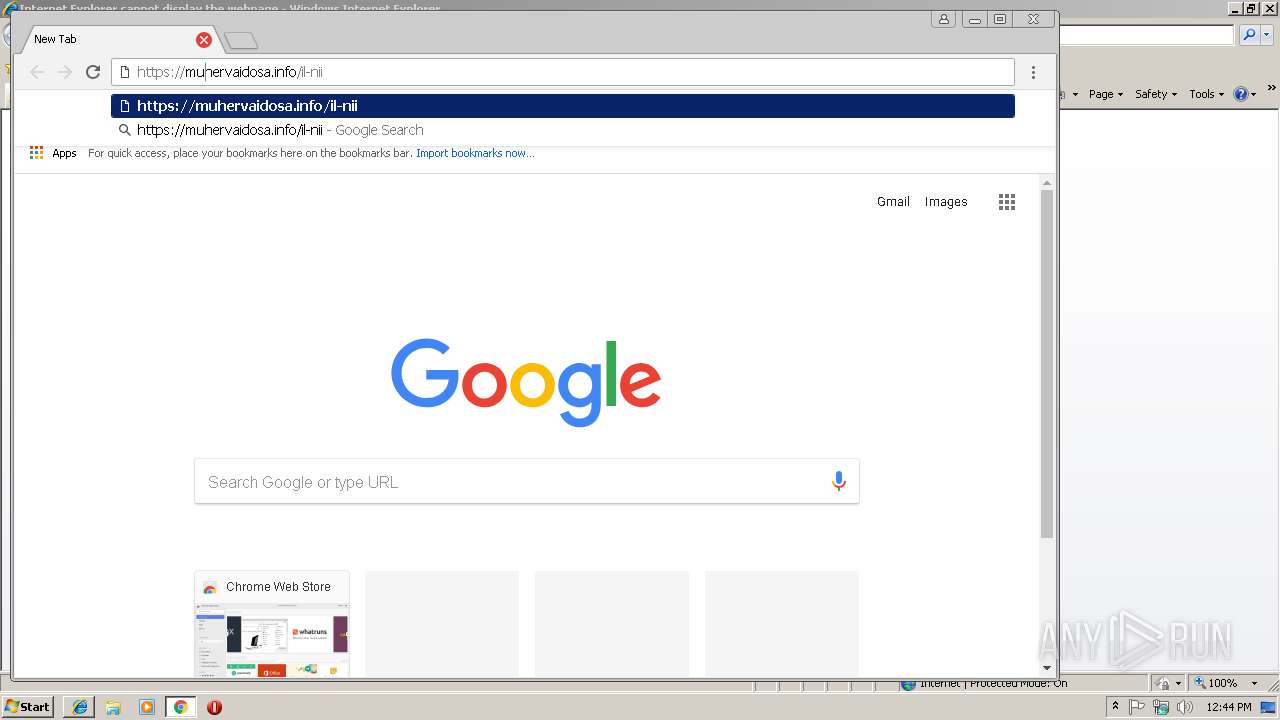
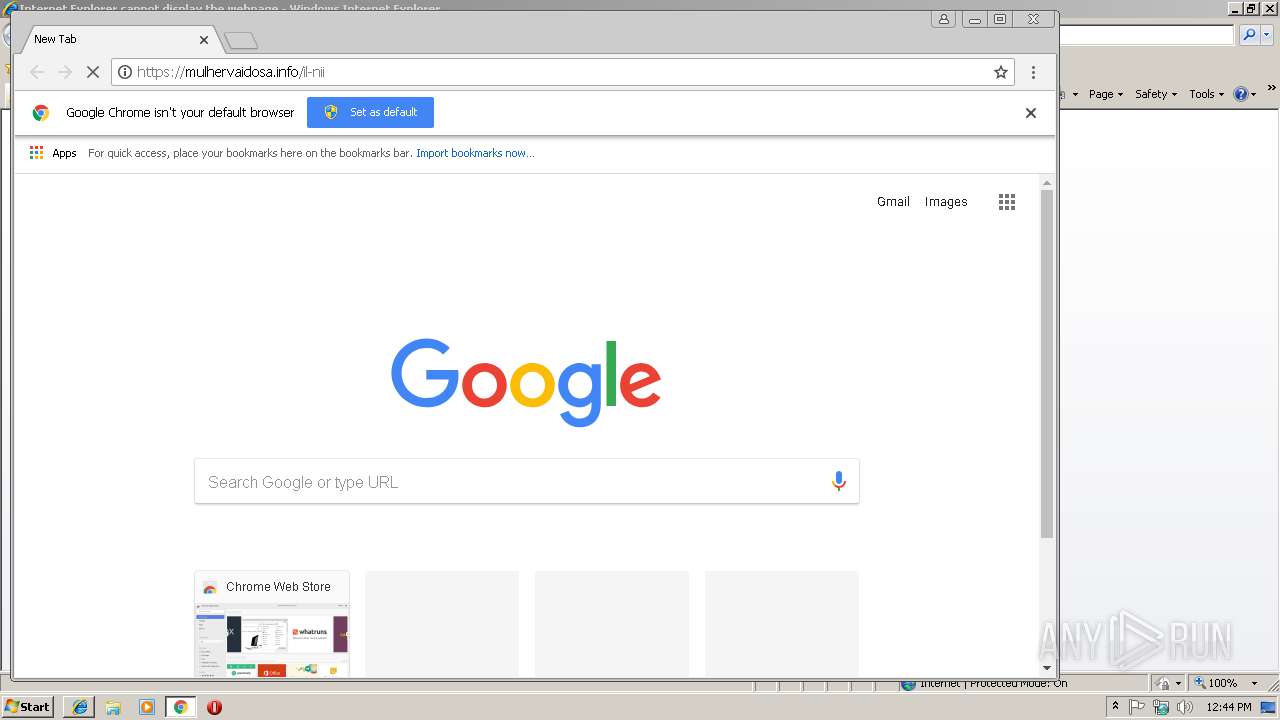
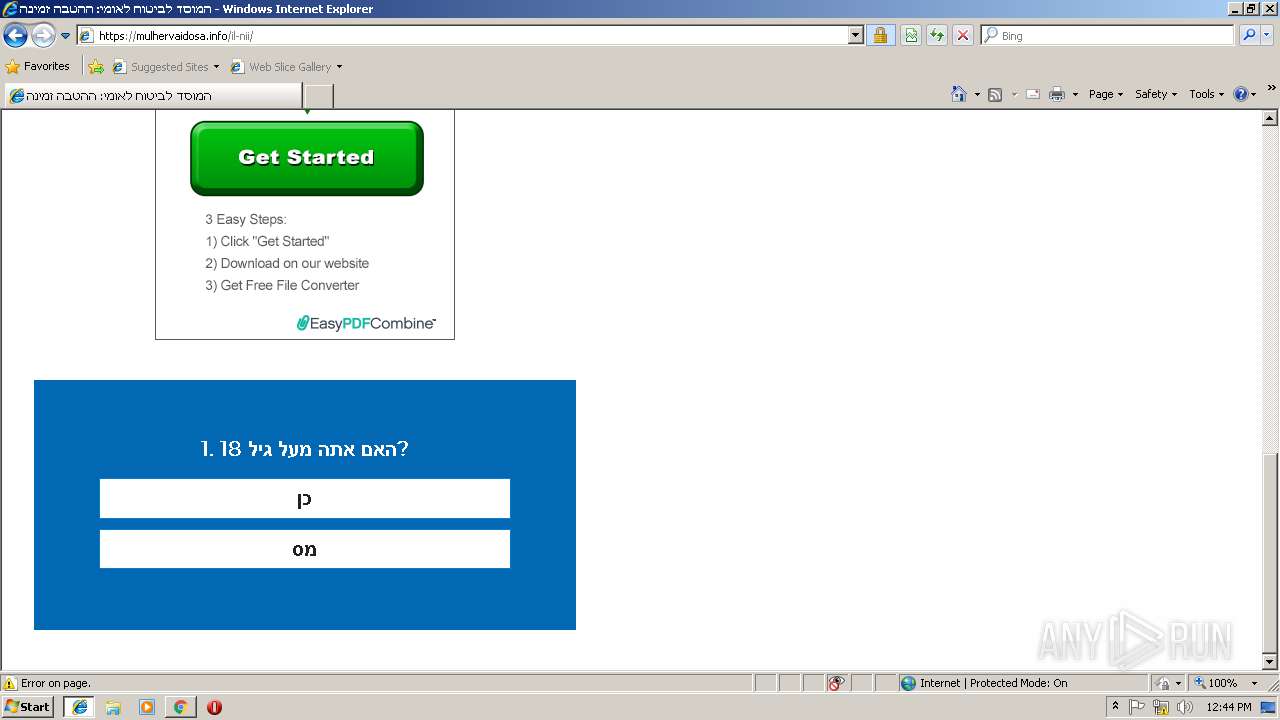
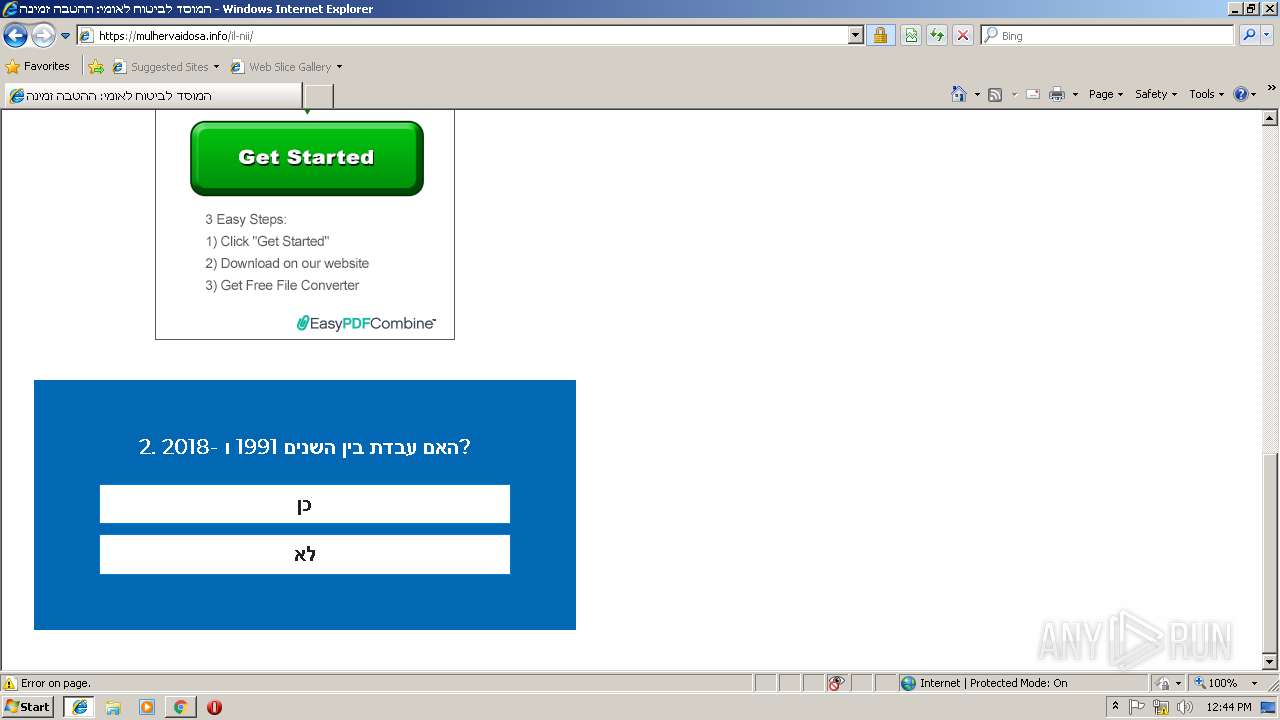
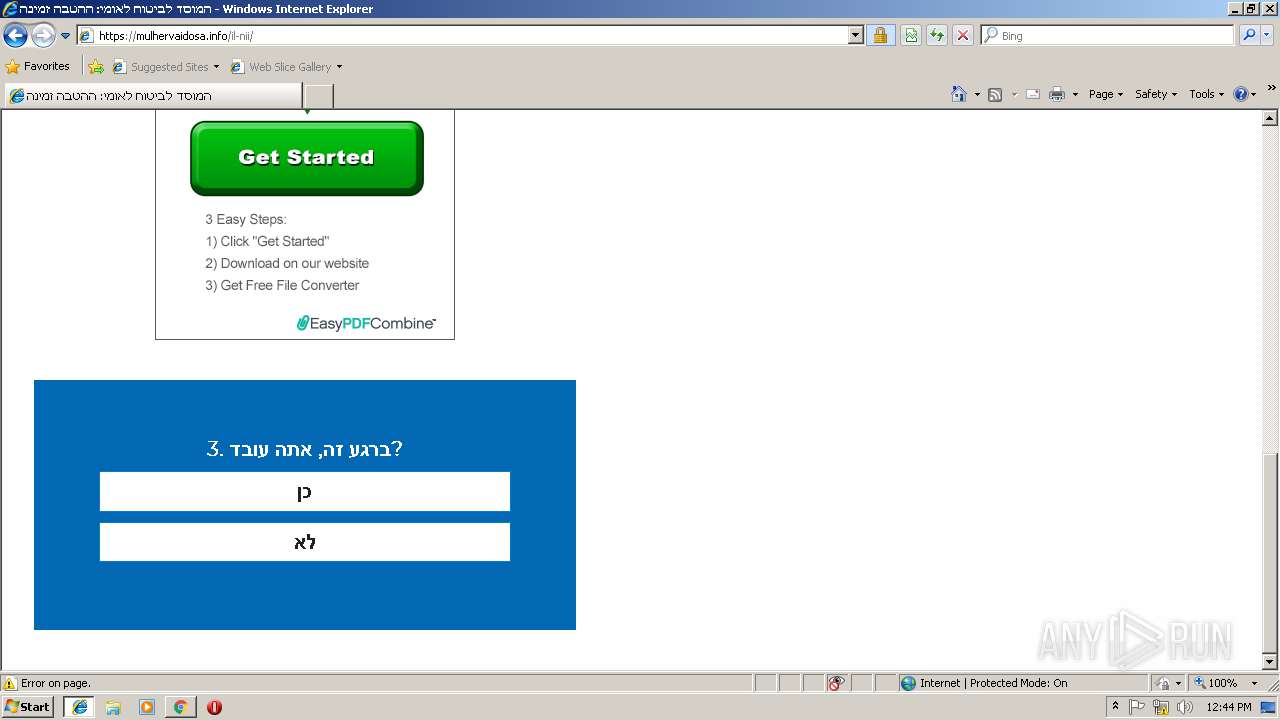
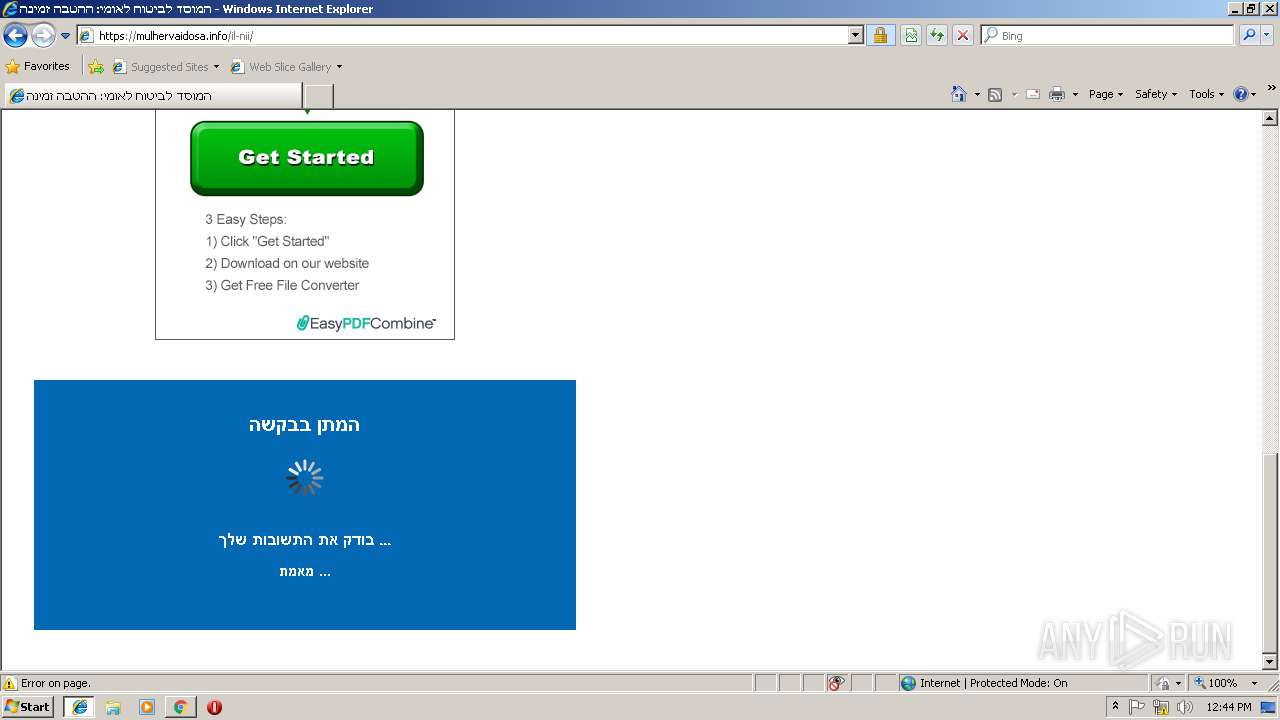
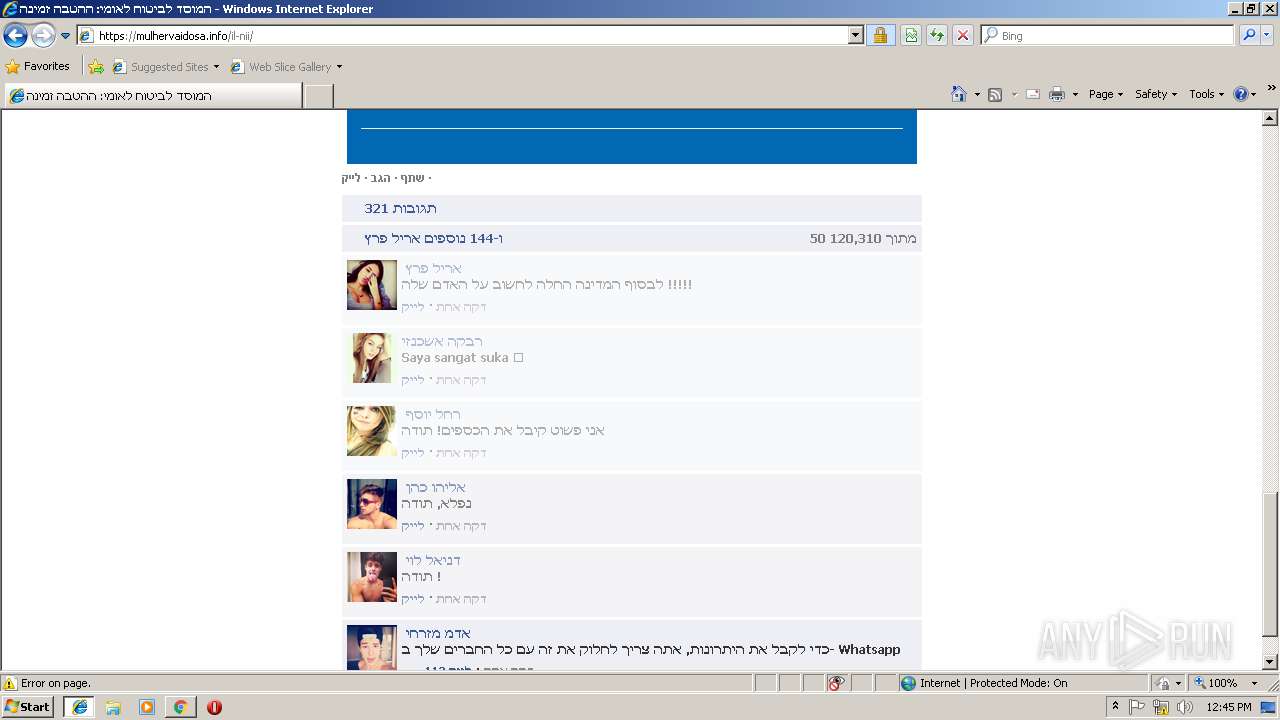
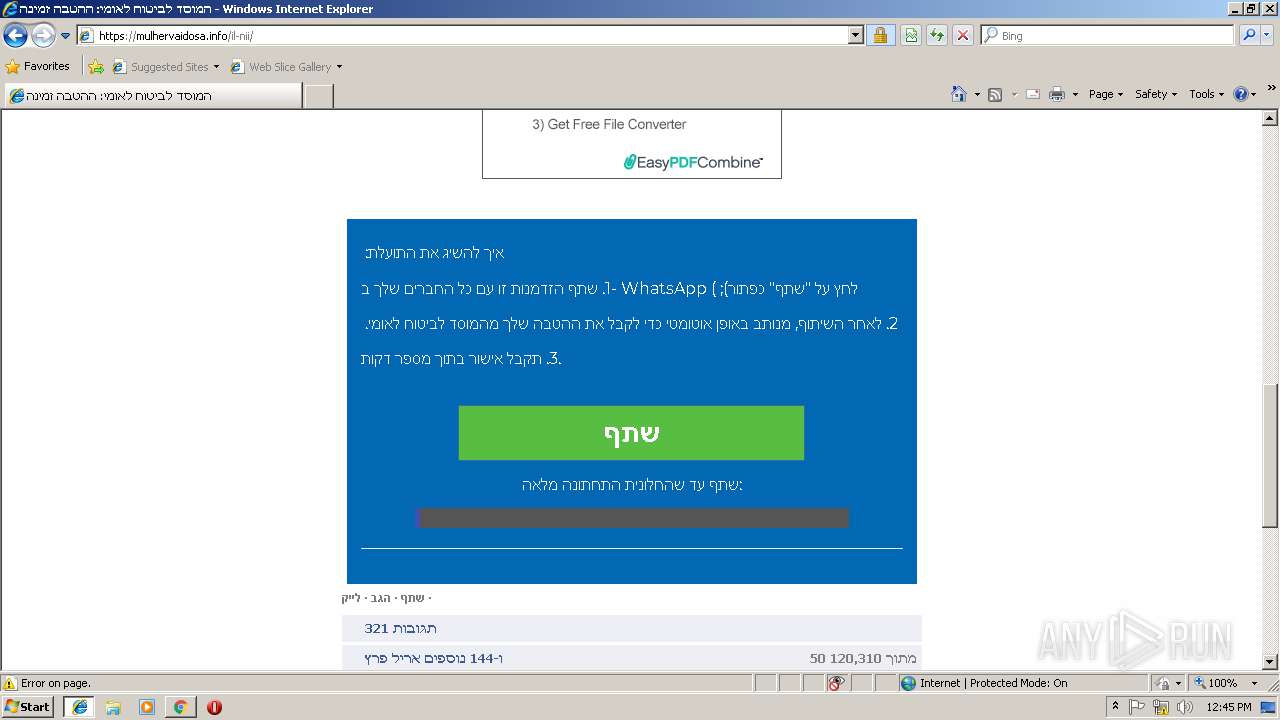
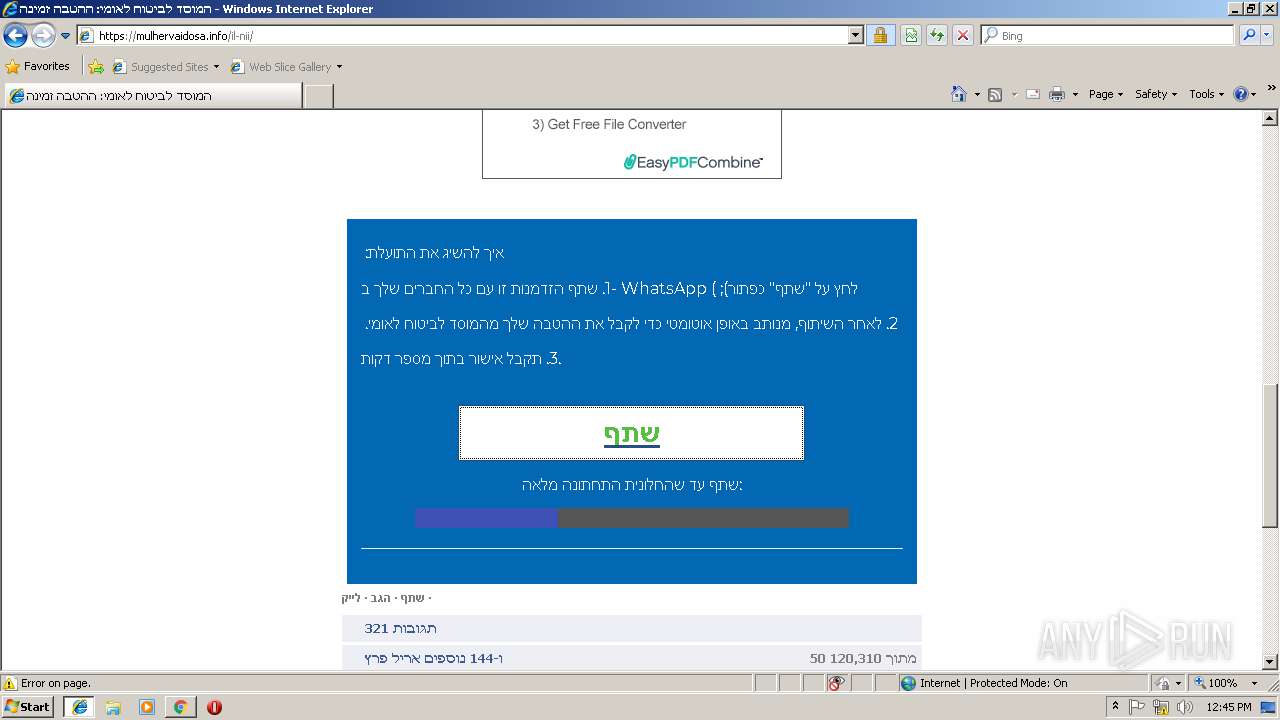
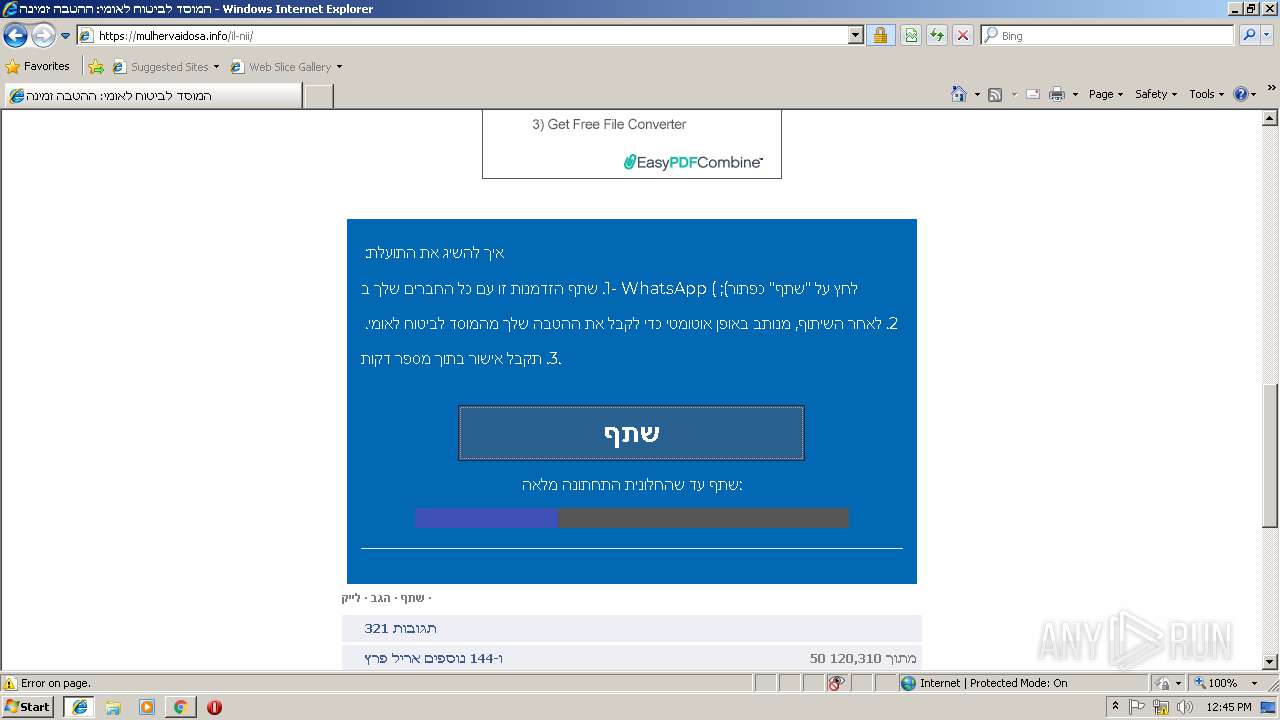
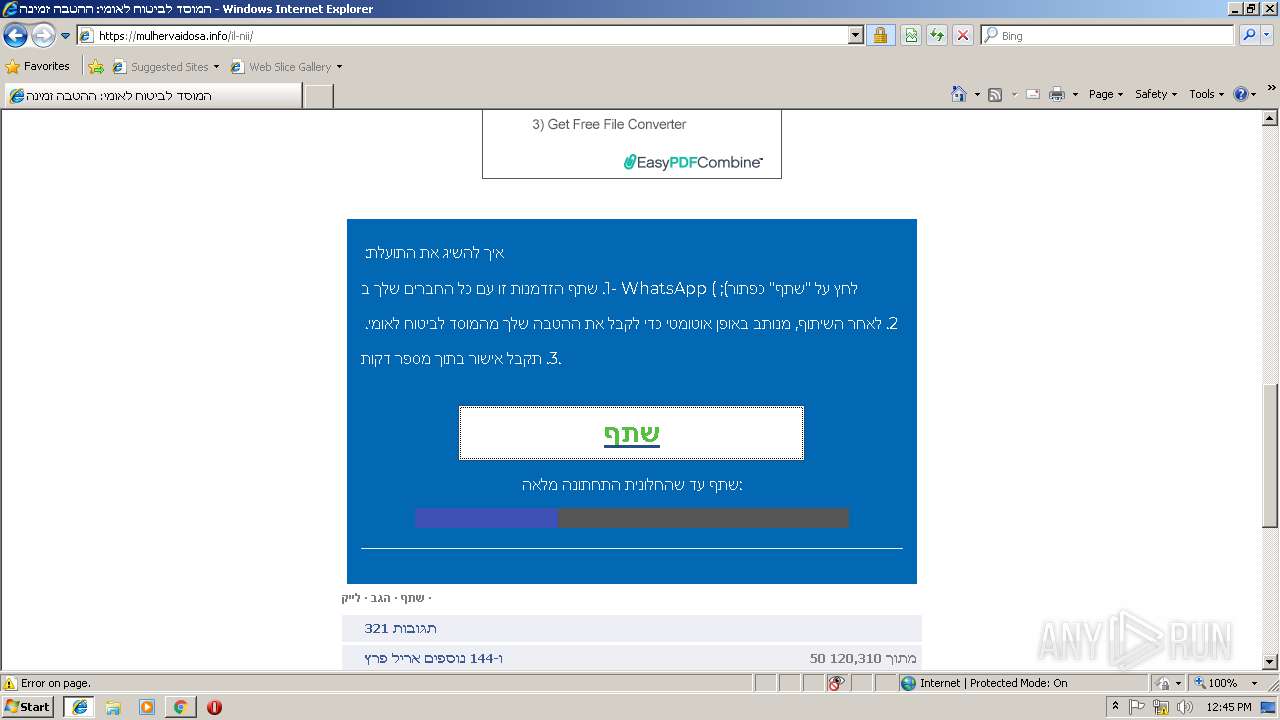
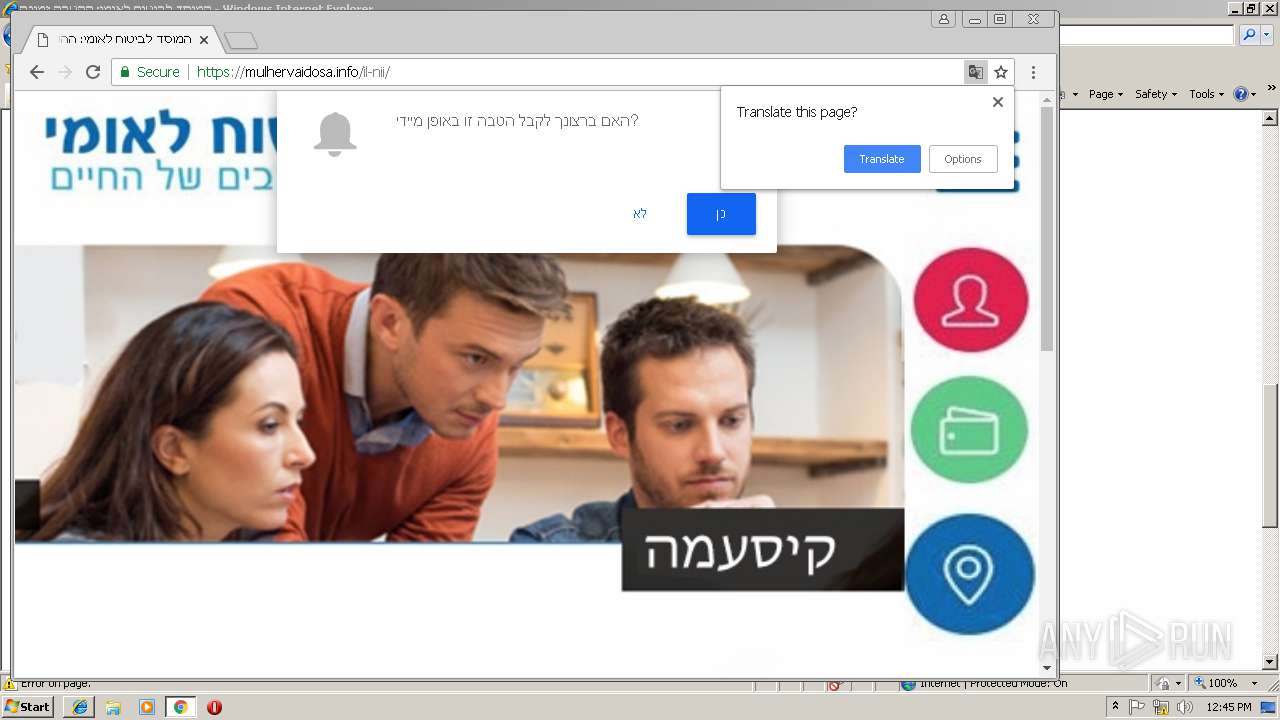
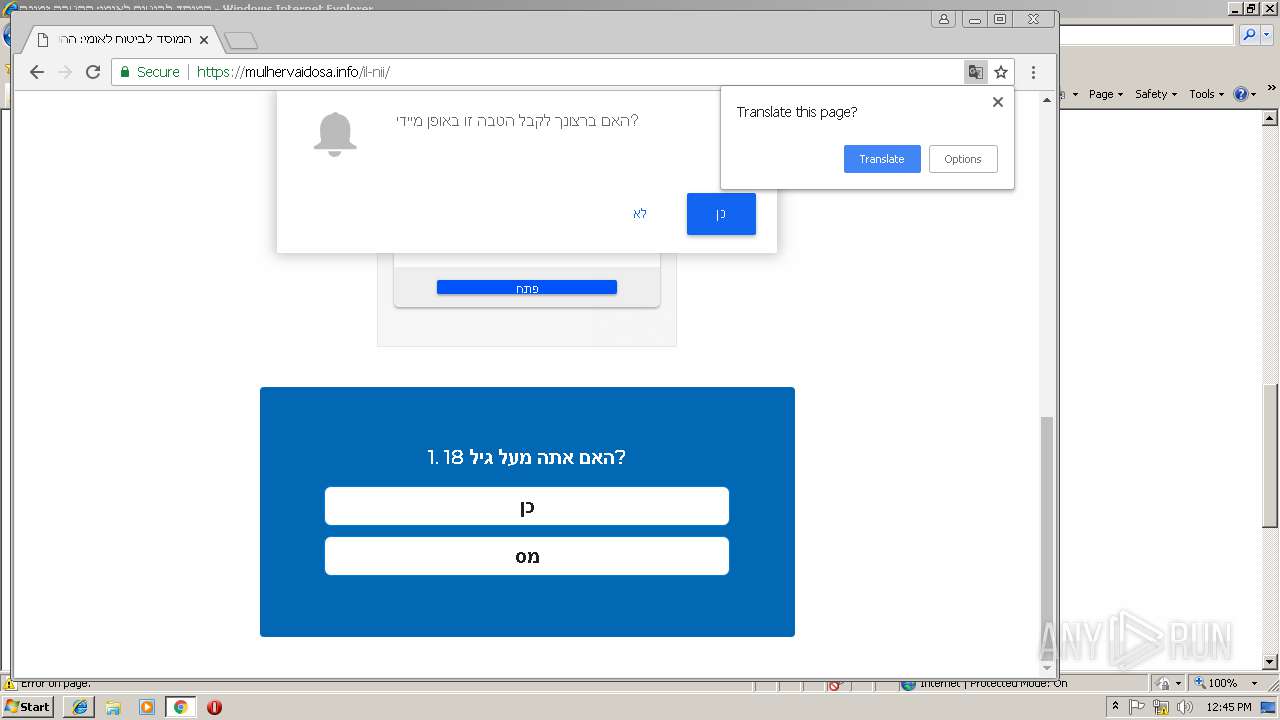
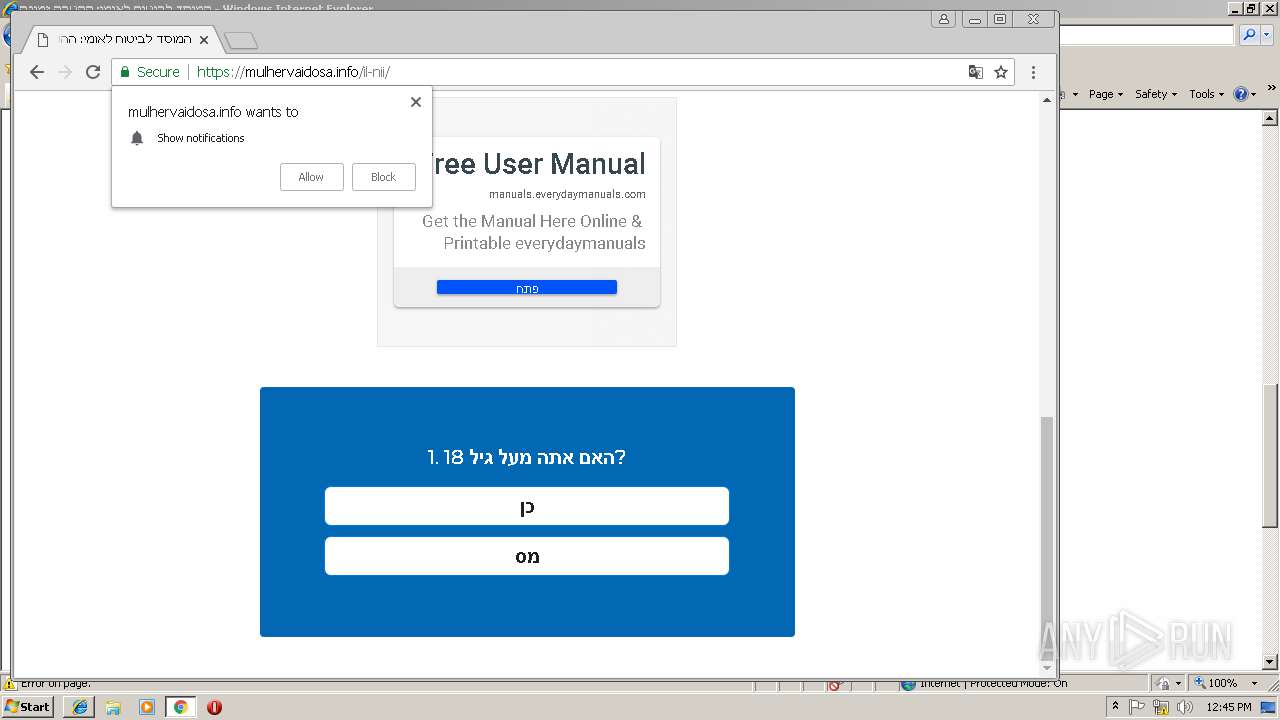
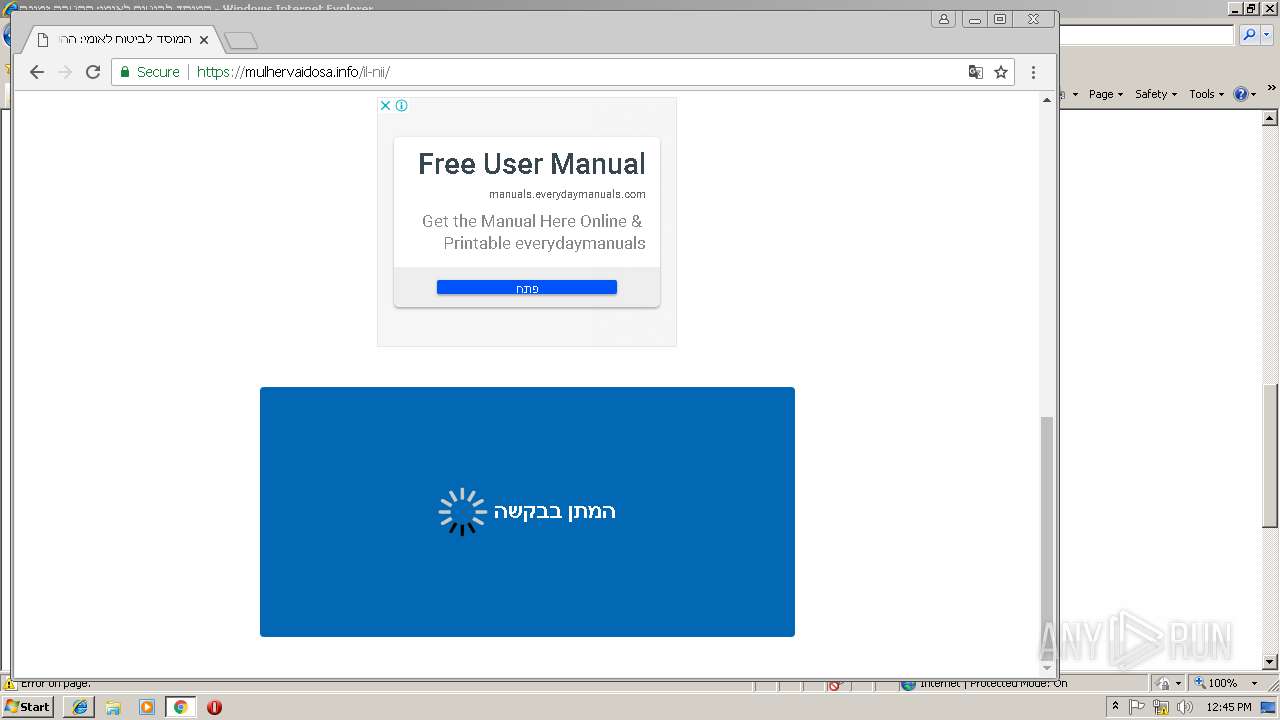
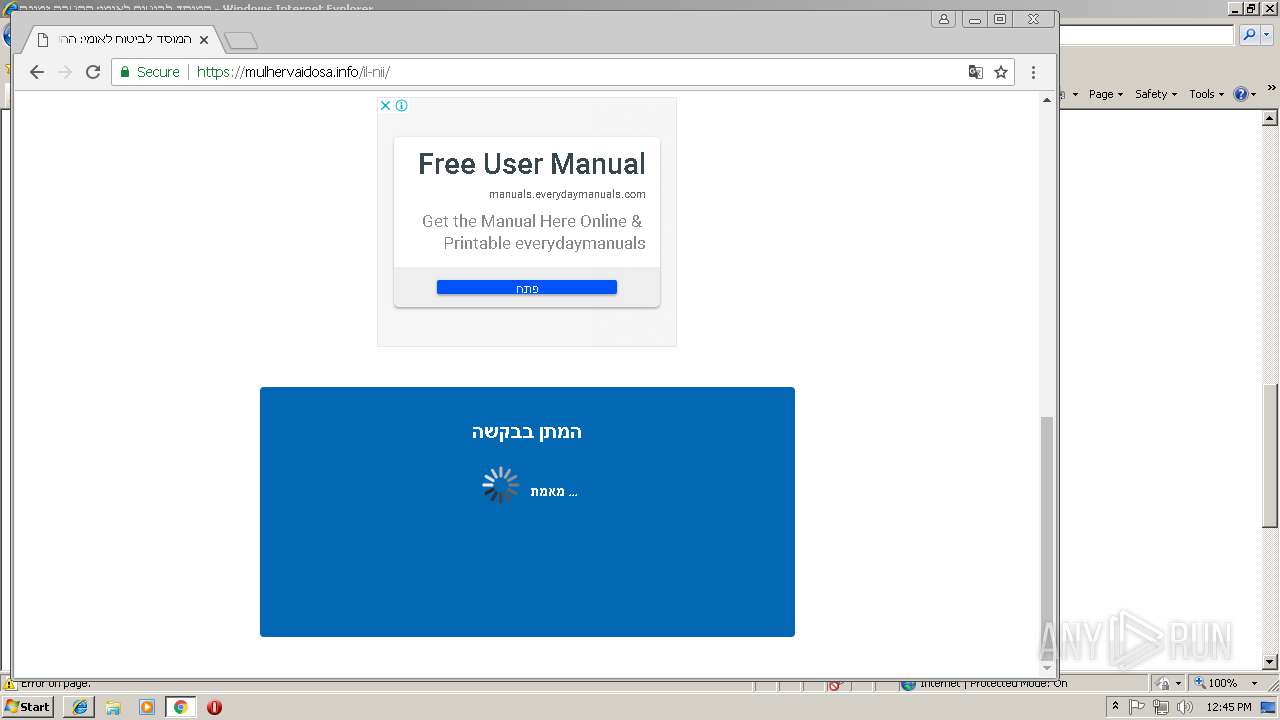
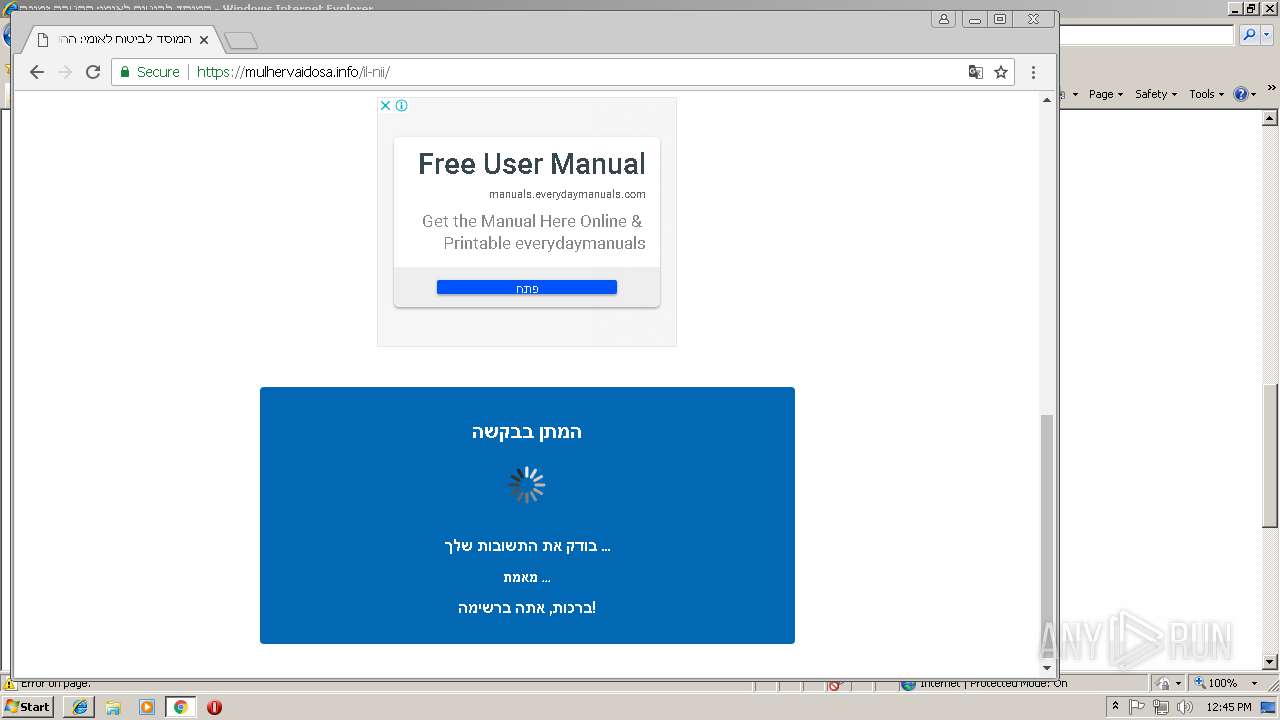
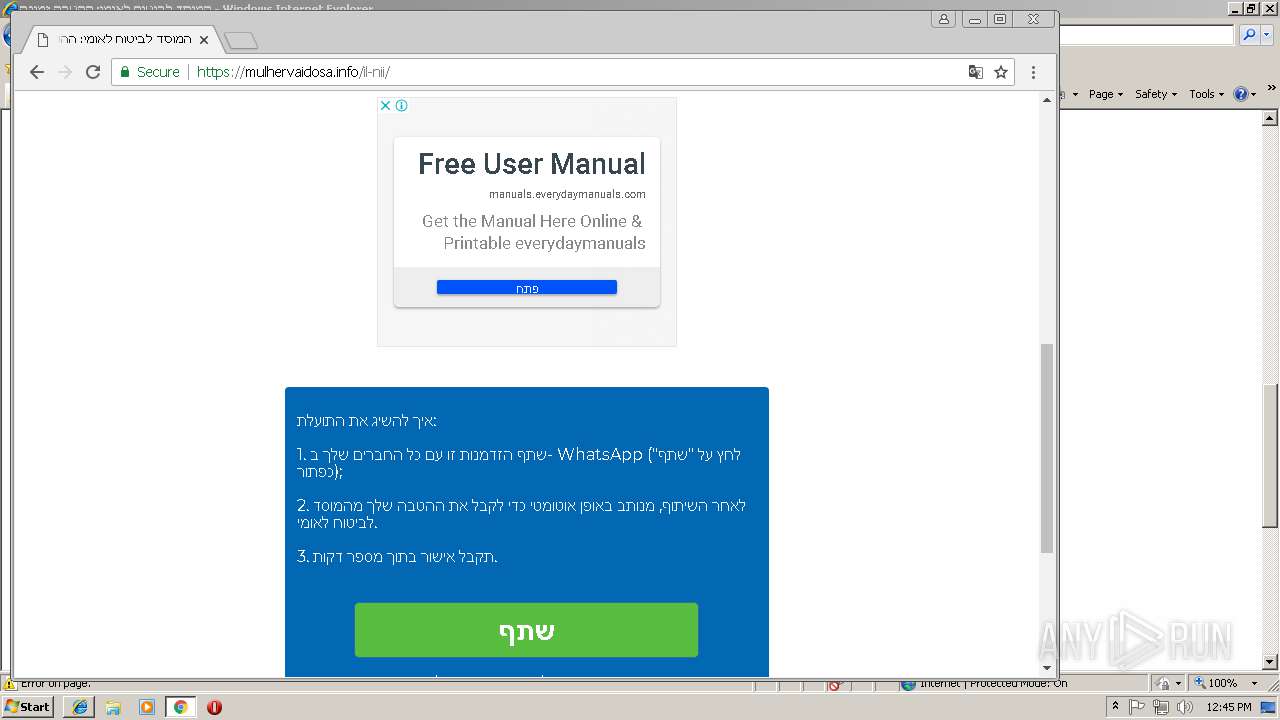
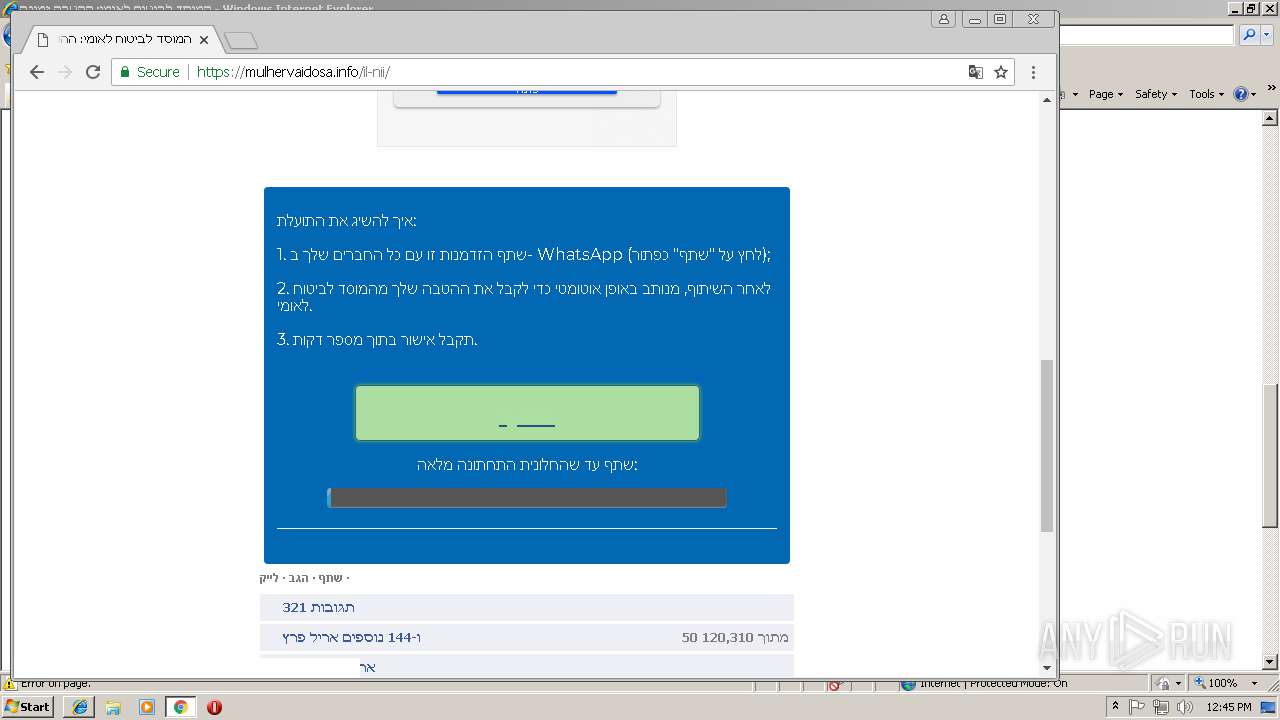
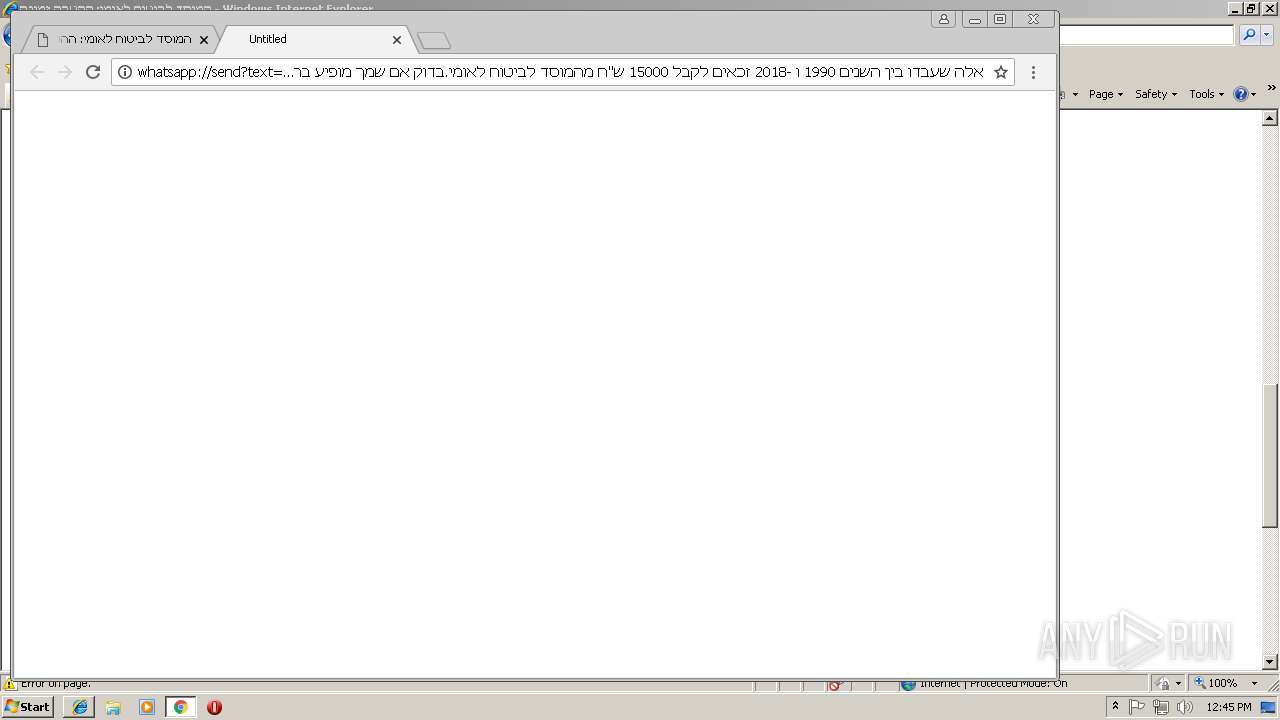
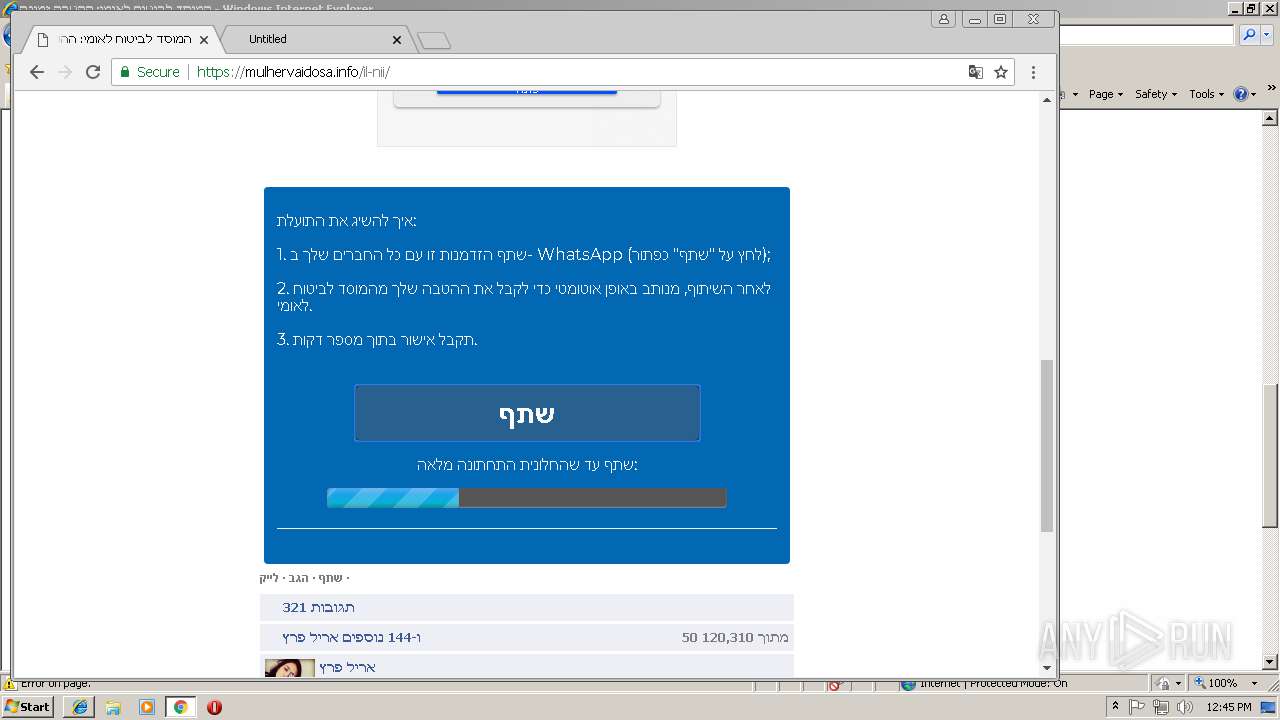
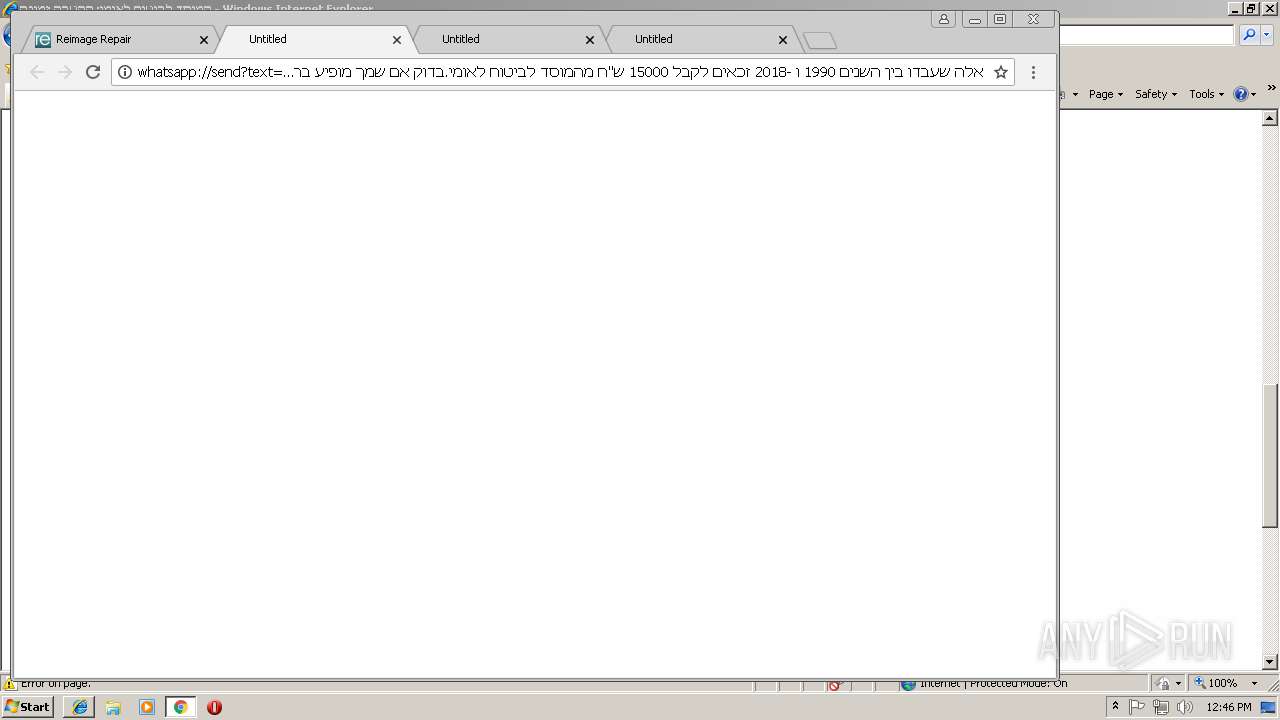
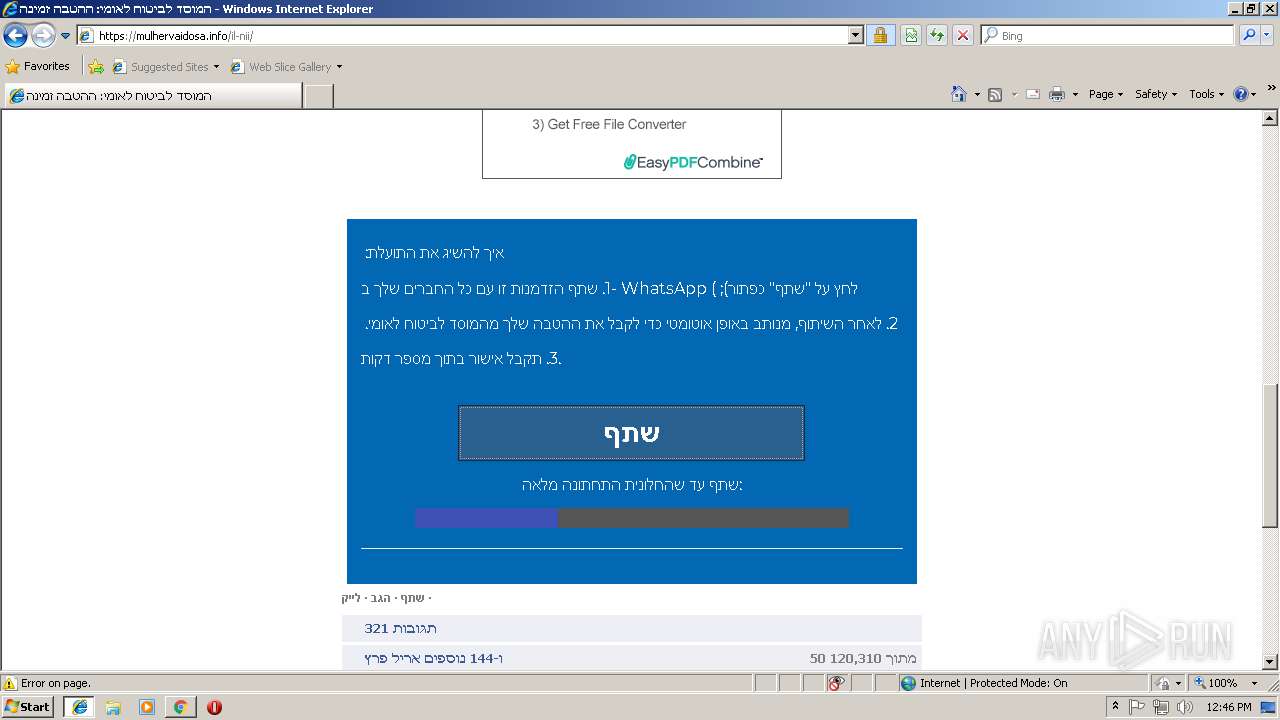
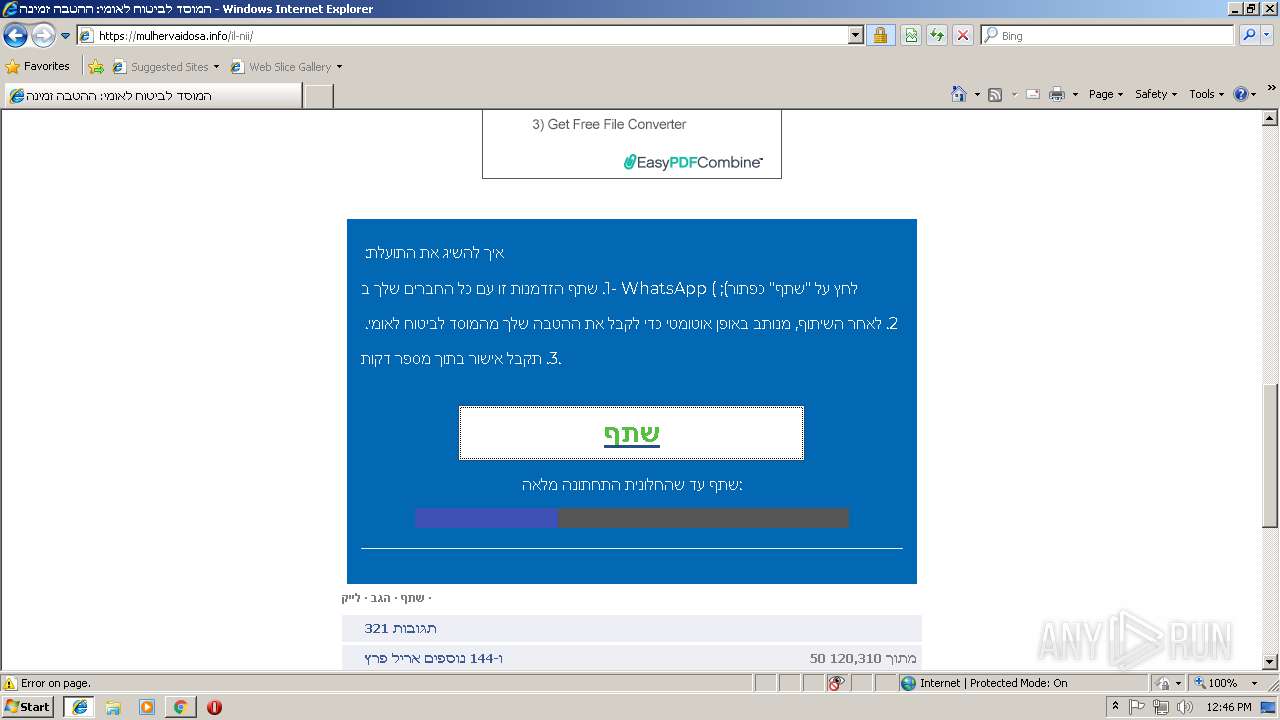
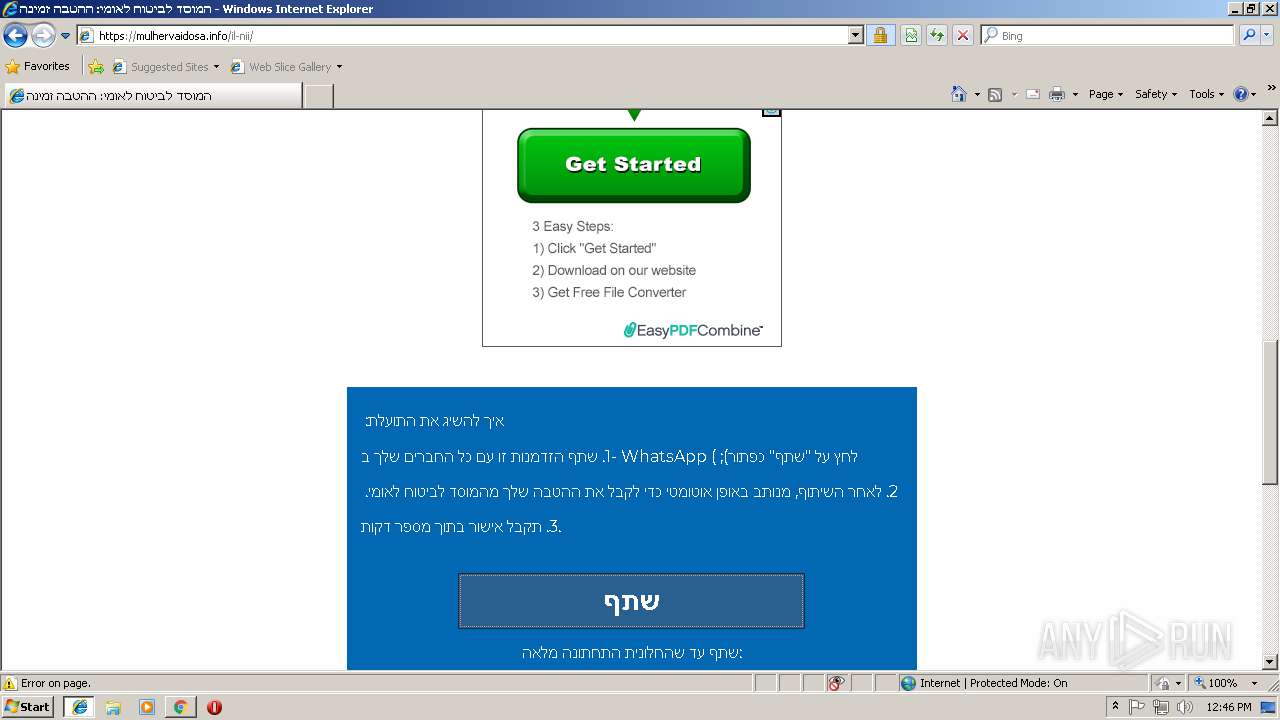
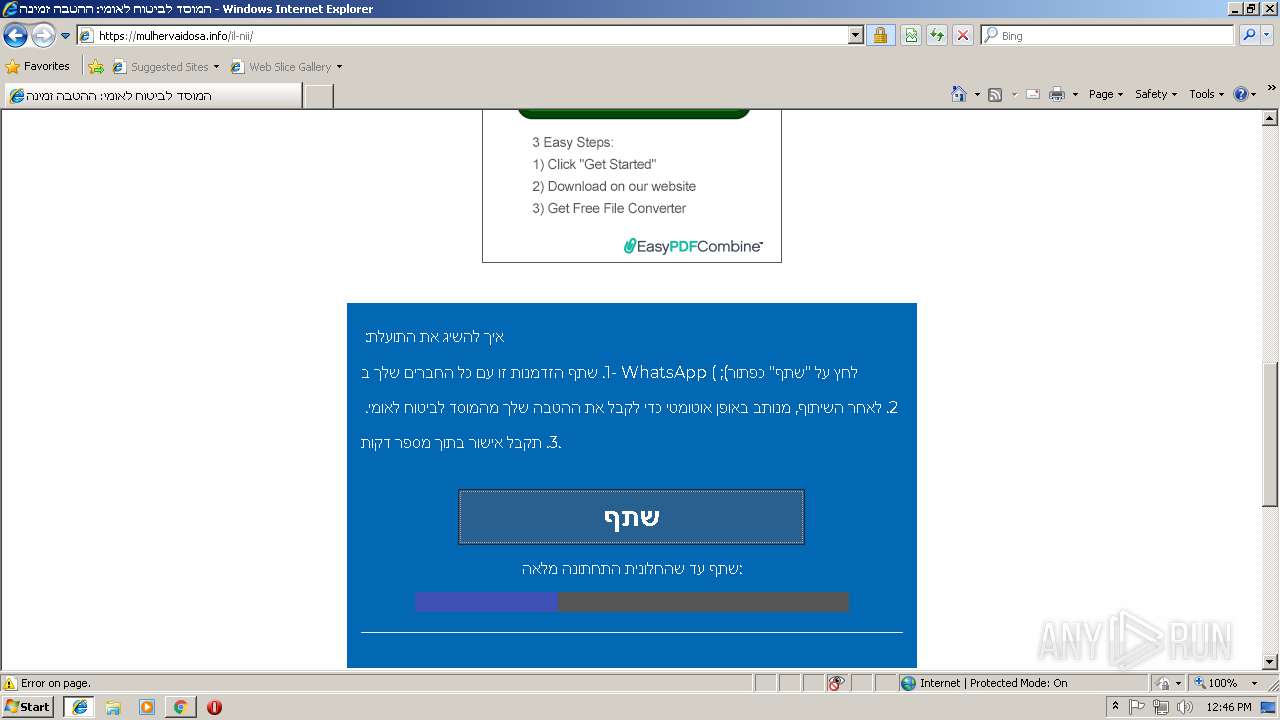
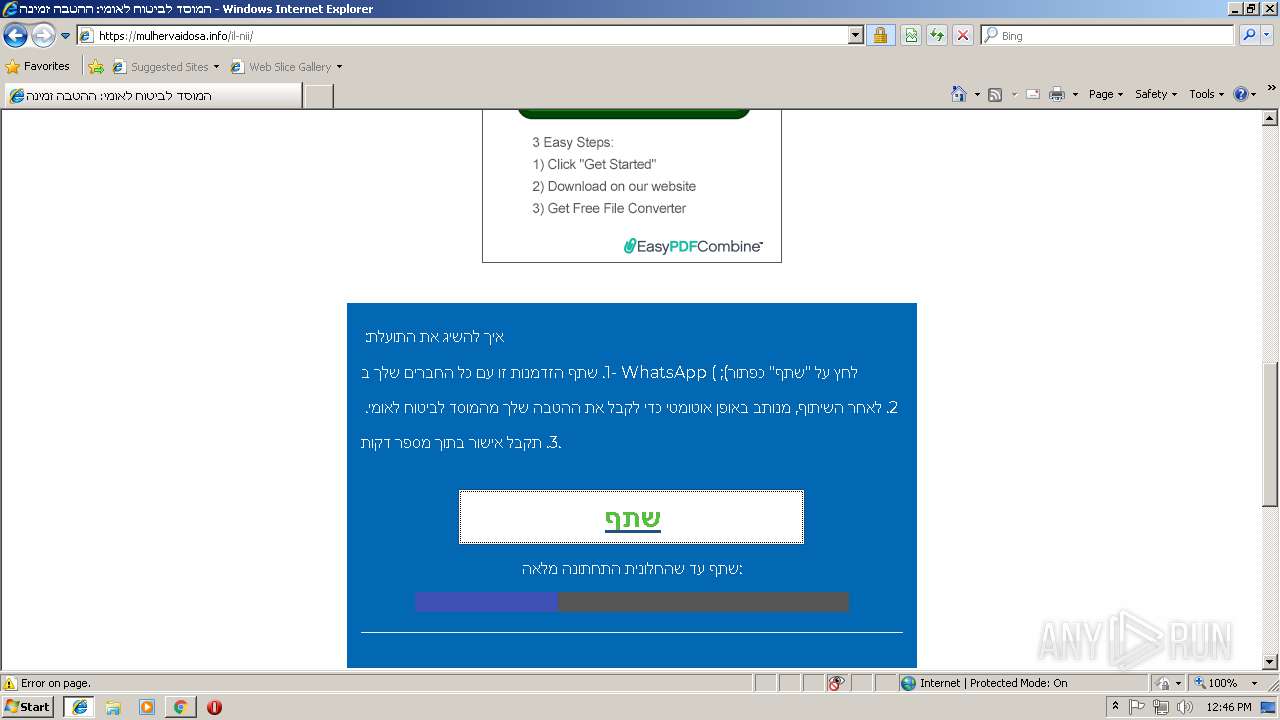
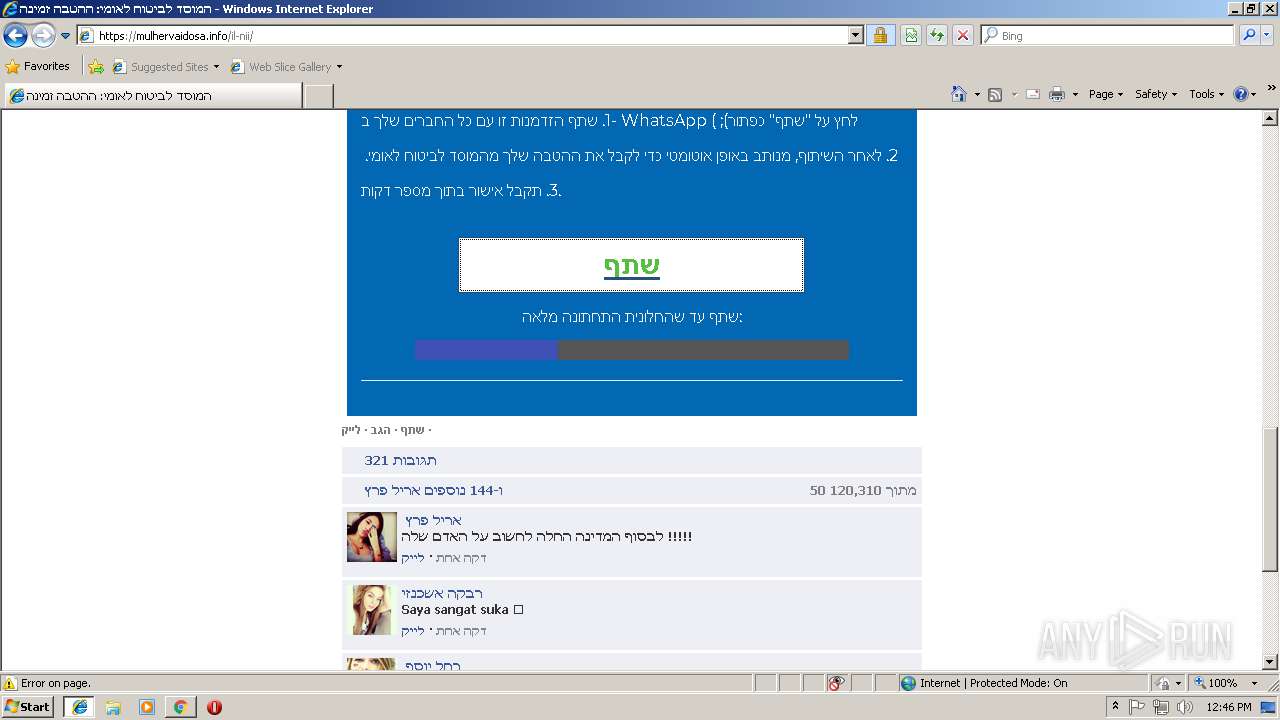
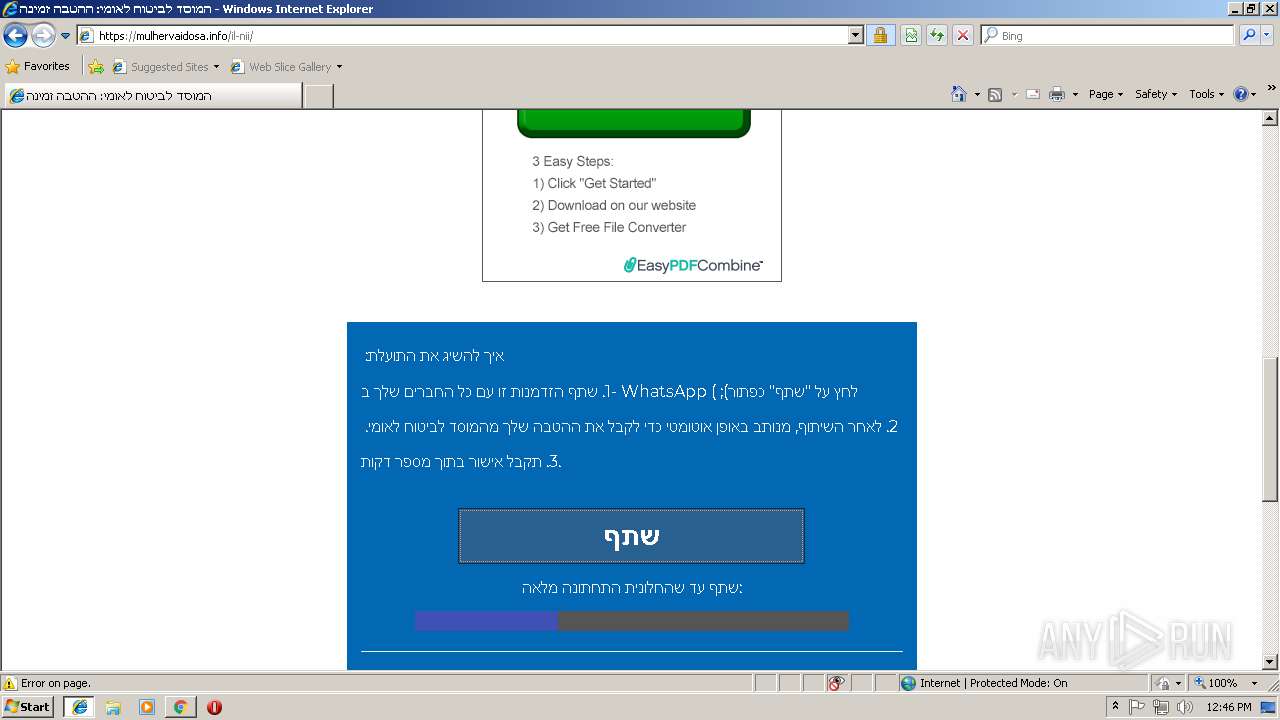
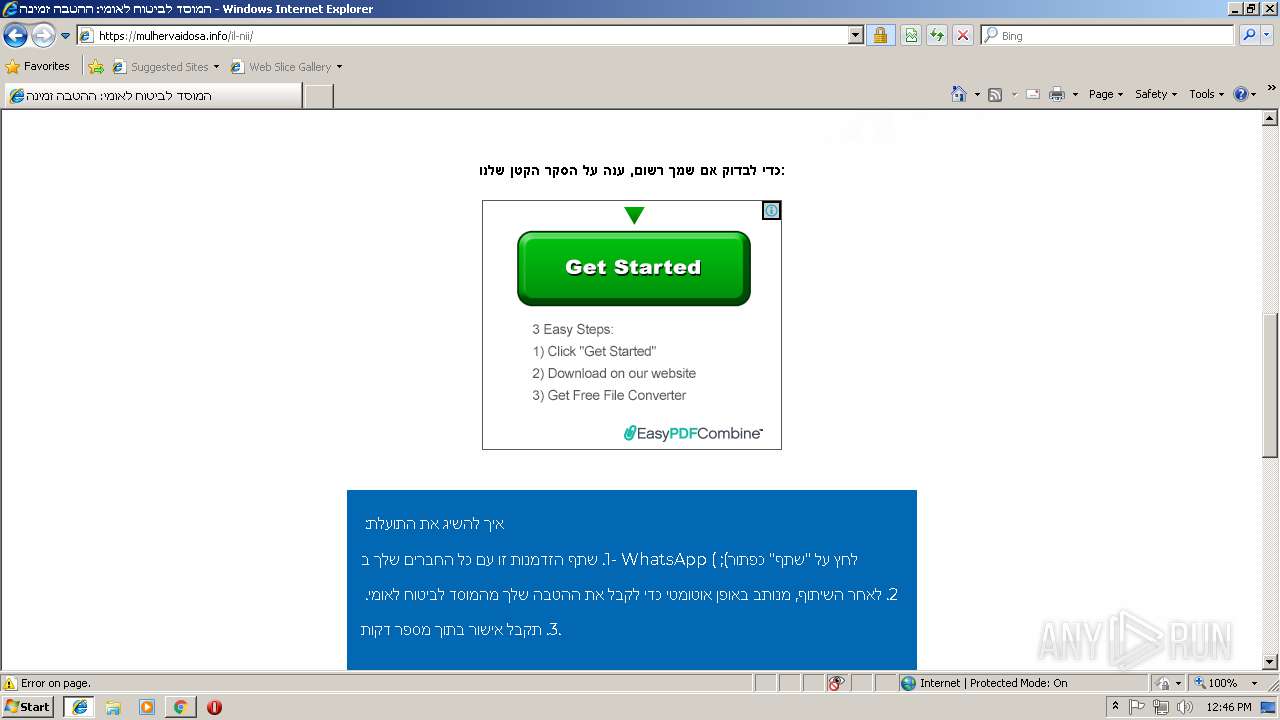
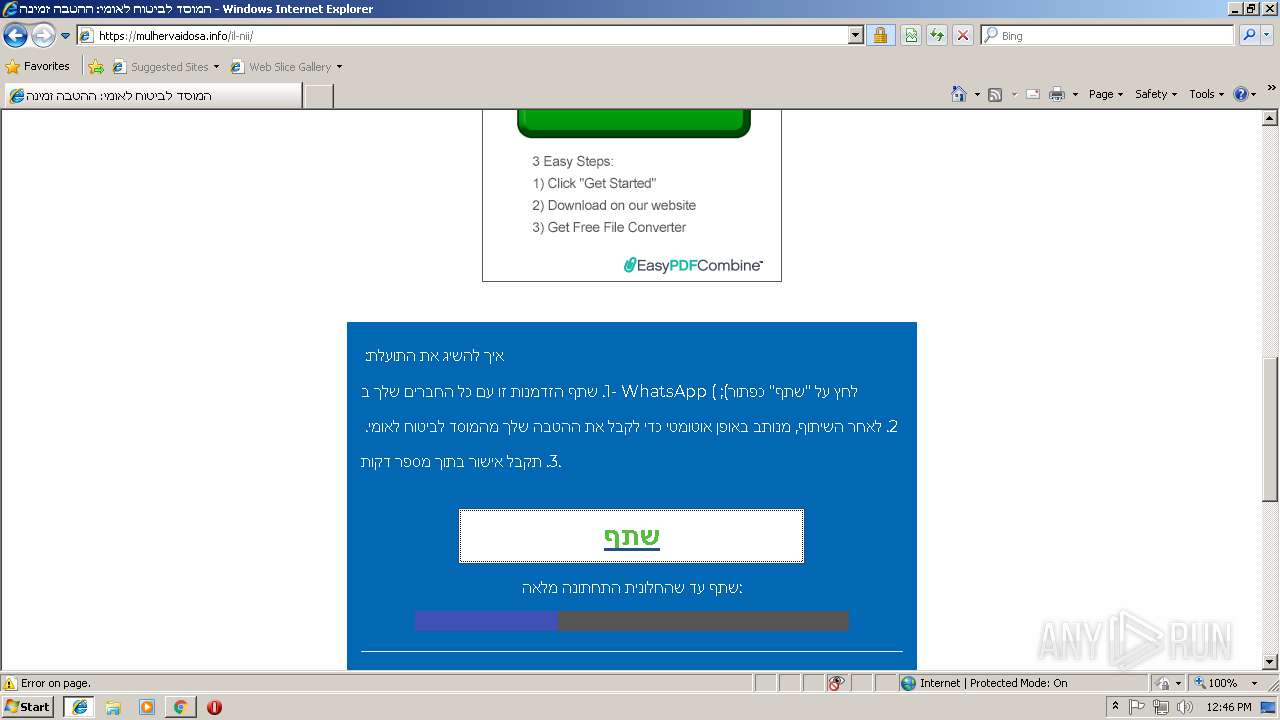
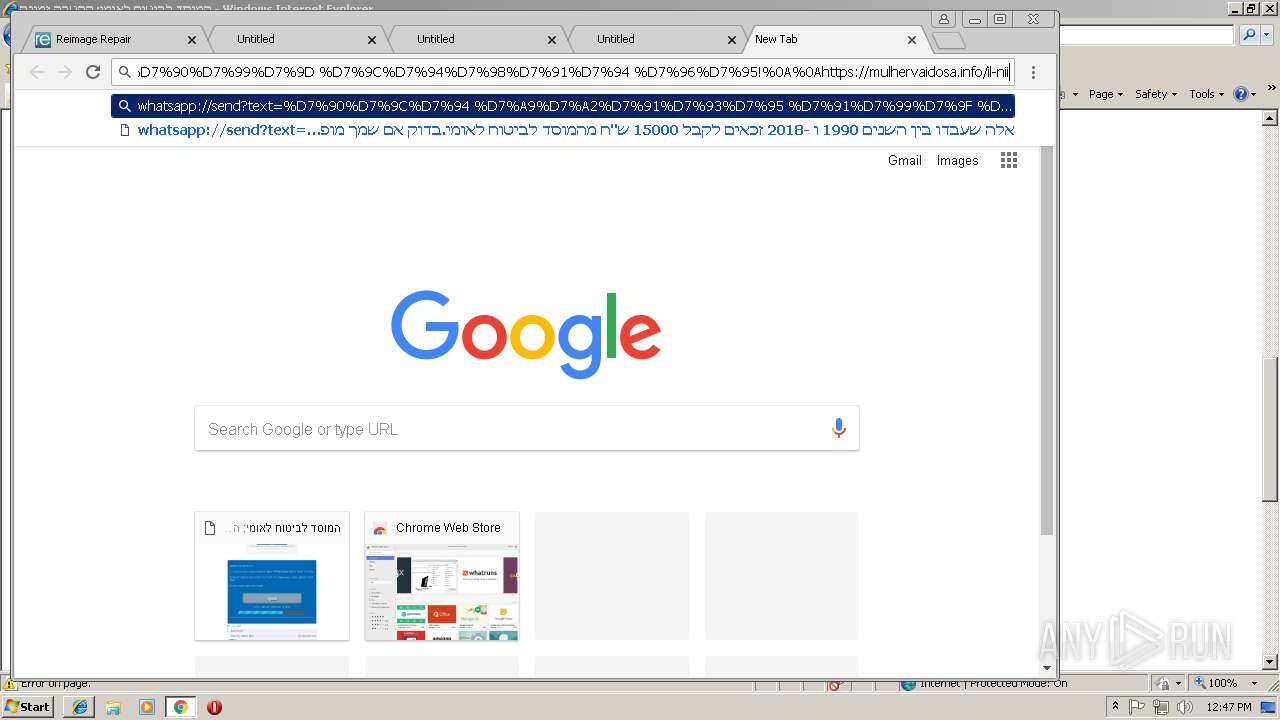
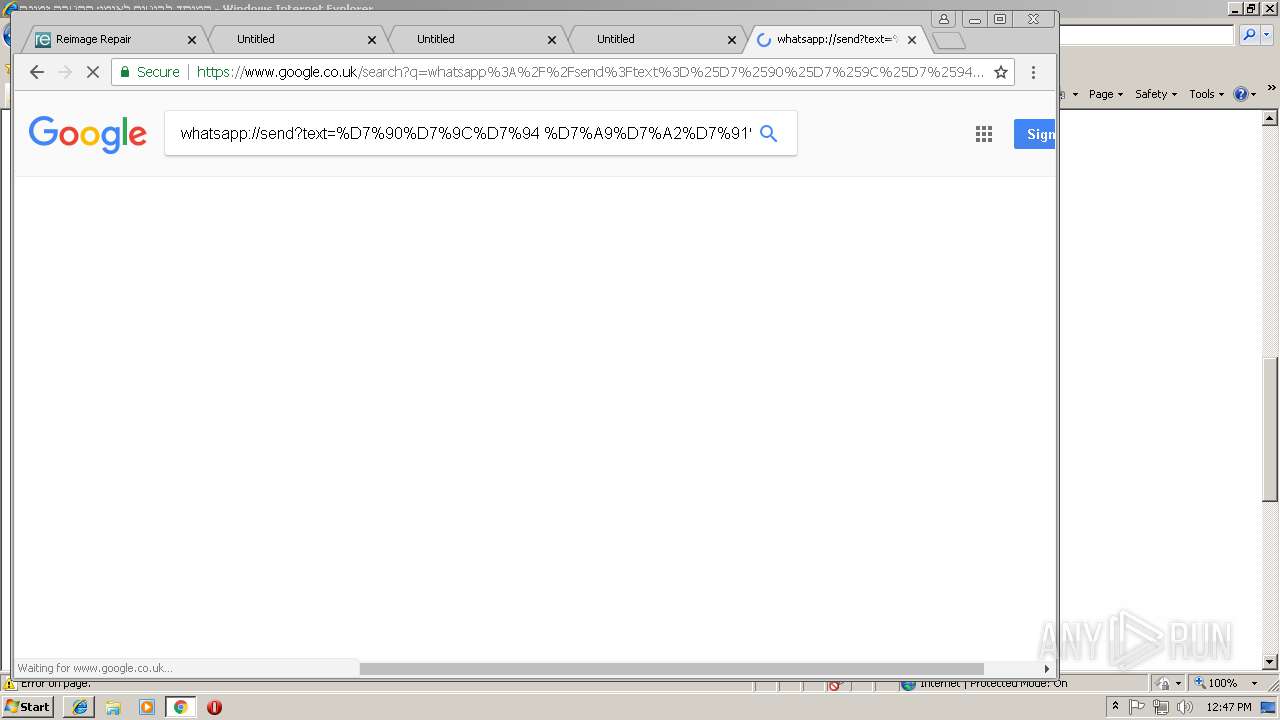
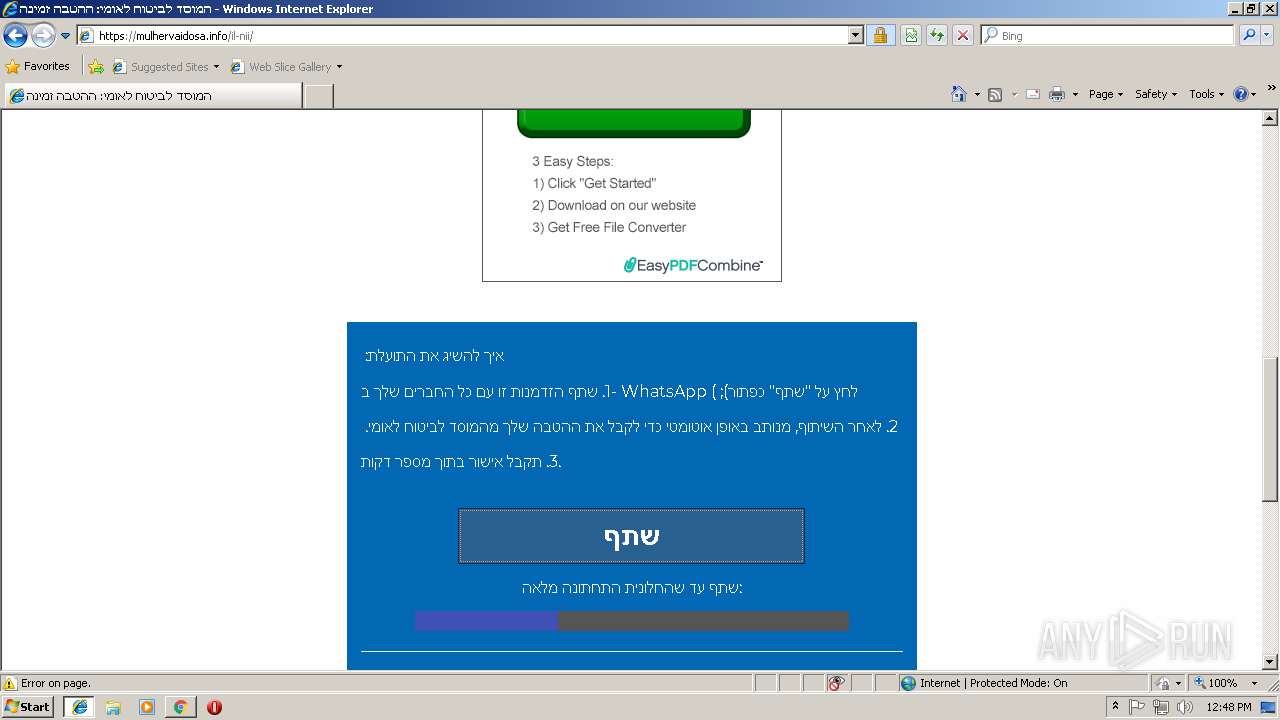
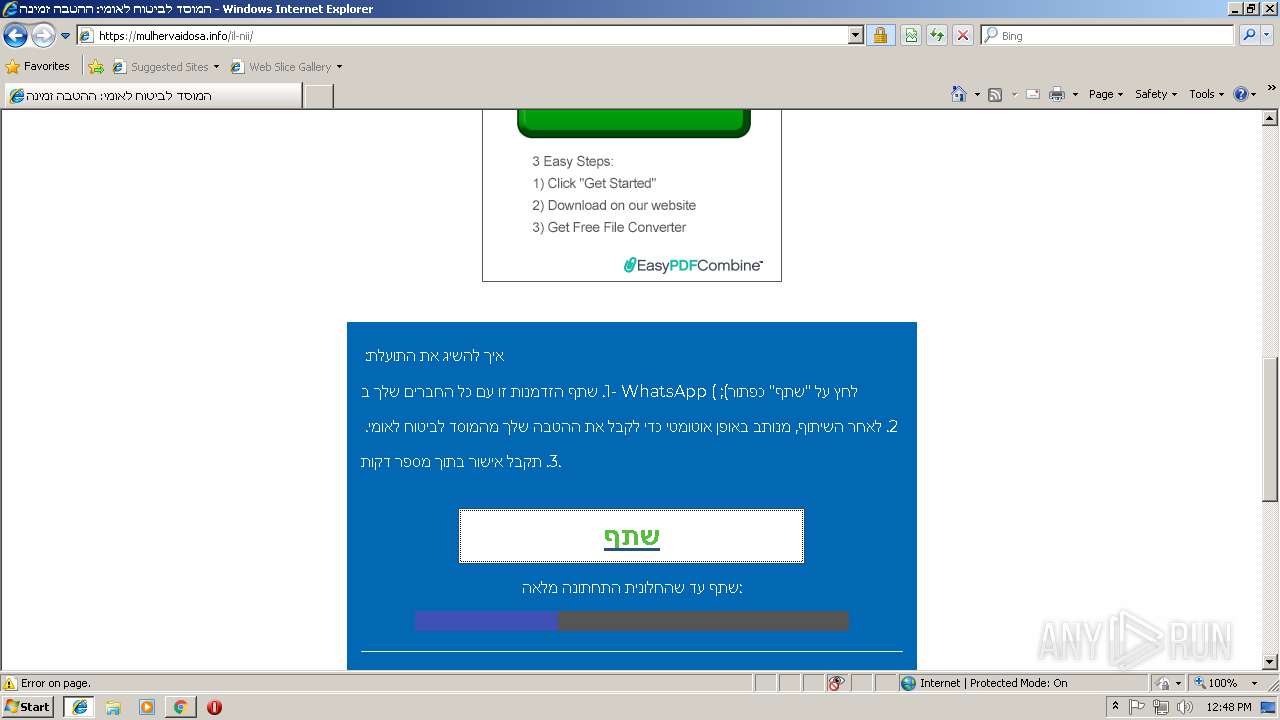
2612 | chrome.exe | 104.31.75.100:443 | mulhervaidosa.info | Cloudflare Inc | US | shared |
2612 | chrome.exe | 172.217.21.226:443 | pagead2.googlesyndication.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
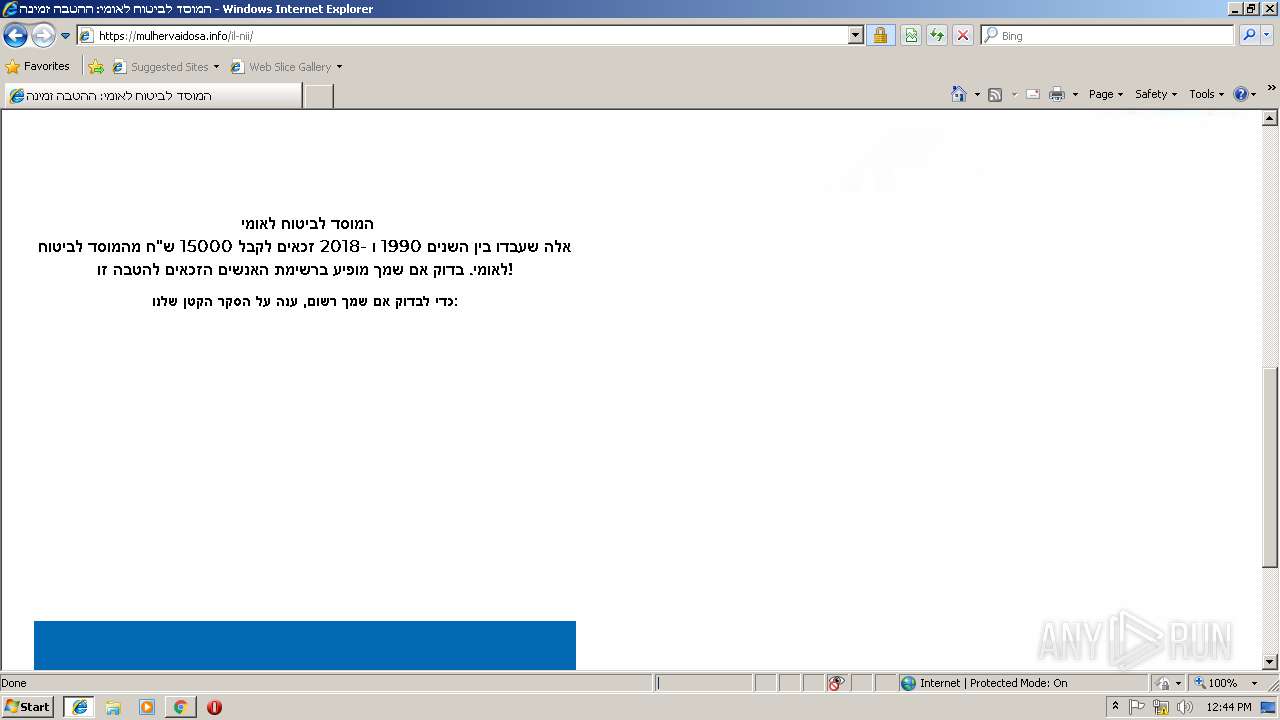
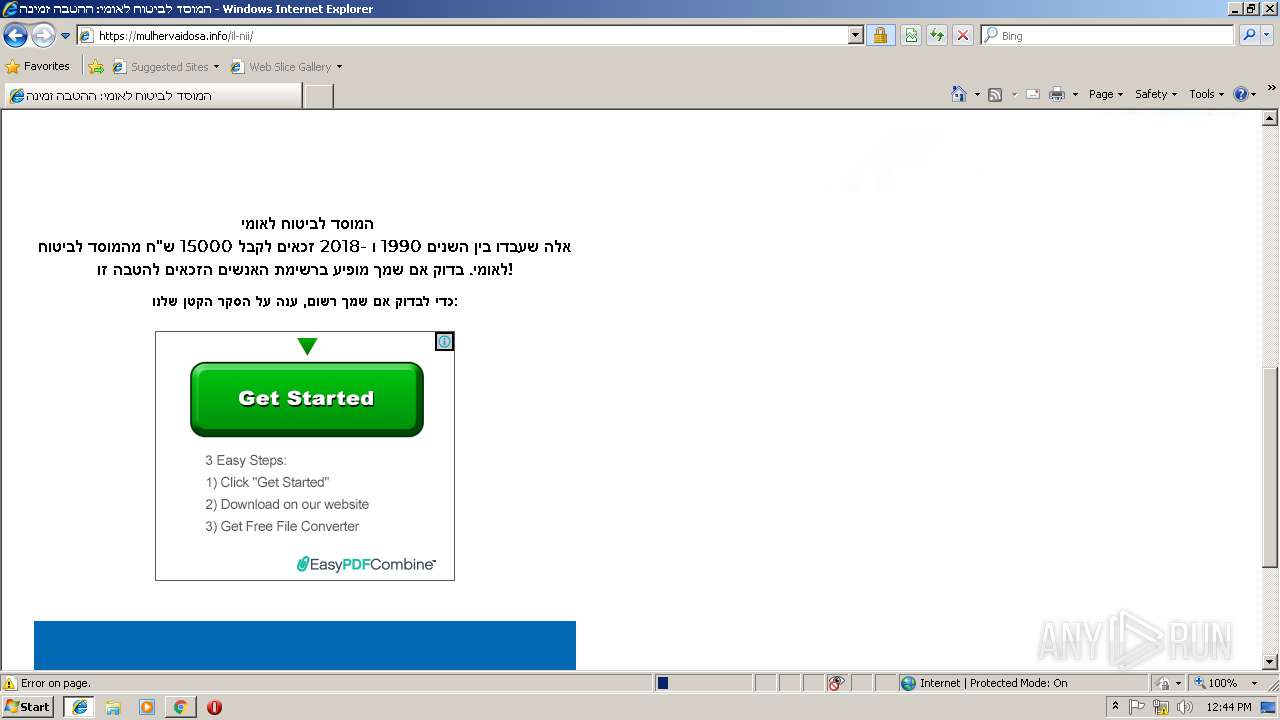
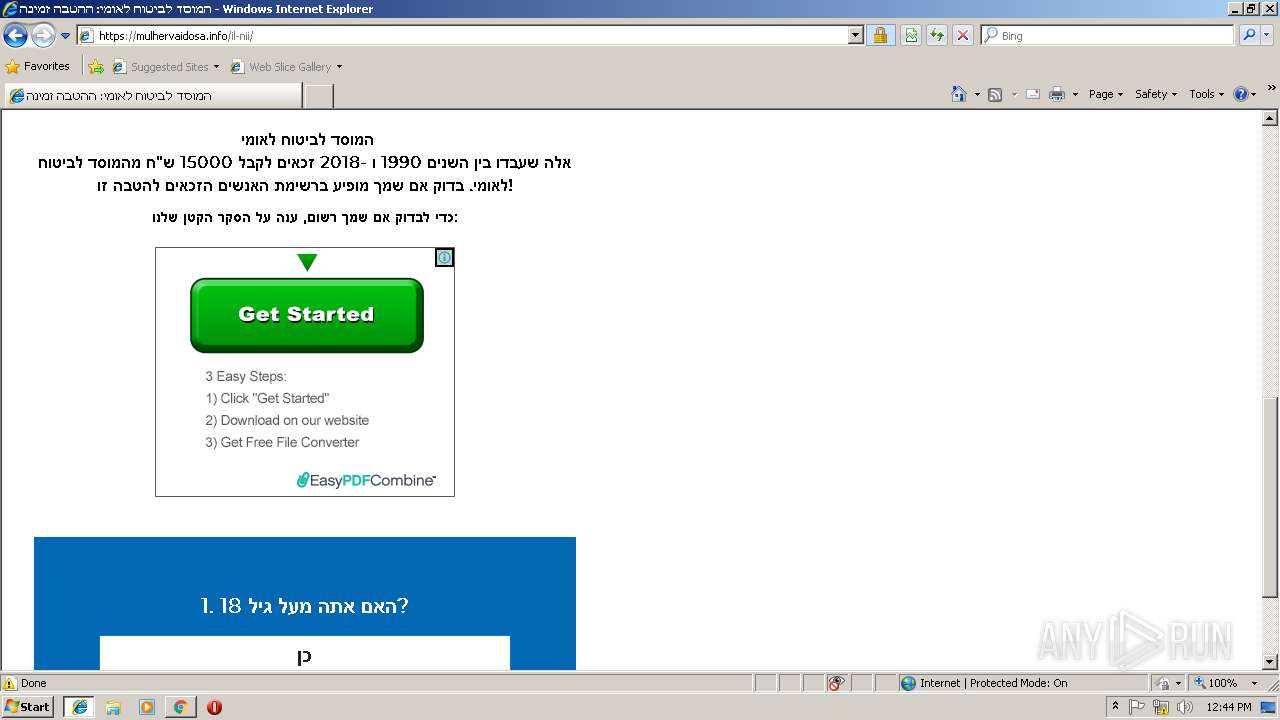
muhervaidosa.info |
| unknown |
www.google.de |
| whitelisted |
www.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
ssl.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2612 | chrome.exe | Generic Protocol Command Decode | SURICATA Applayer Wrong direction first Data |