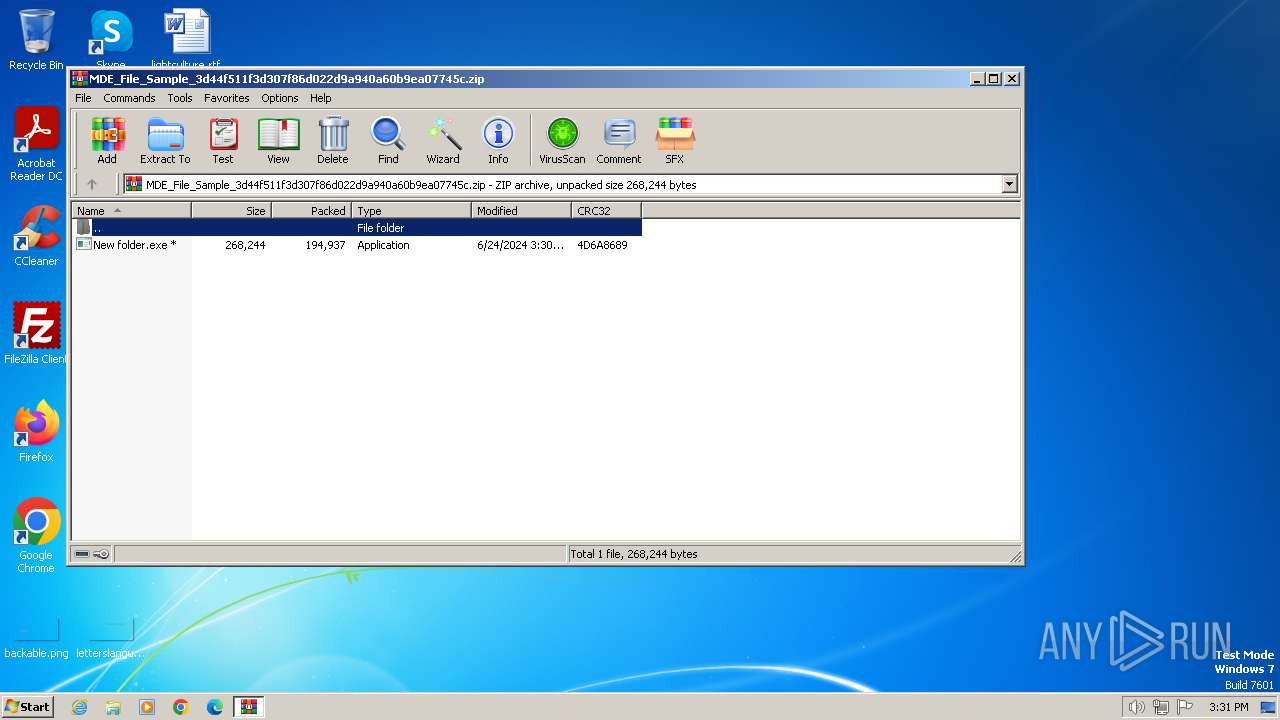
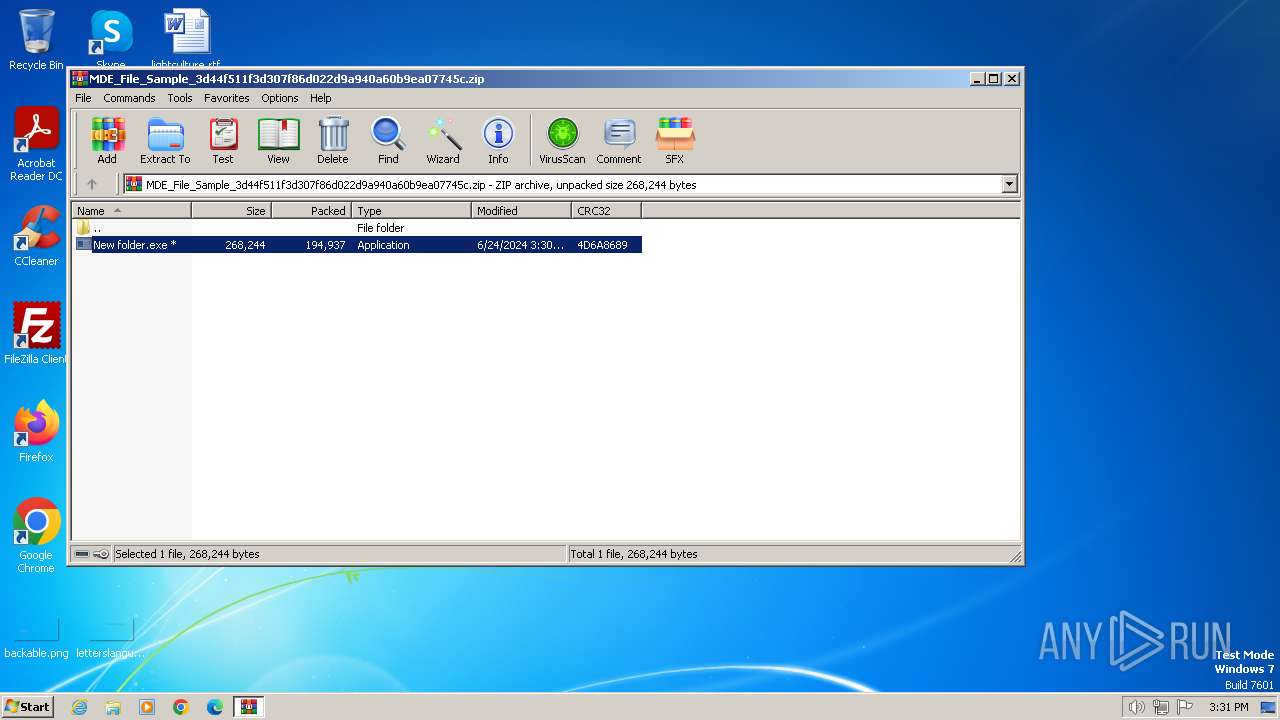
| File name: | MDE_File_Sample_3d44f511f3d307f86d022d9a940a60b9ea07745c.zip |
| Full analysis: | https://app.any.run/tasks/f5683955-db47-4b4e-b83f-19f146c95714 |
| Verdict: | Malicious activity |
| Analysis date: | June 24, 2024, 14:31:15 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 23C3E799AC583AEC62F0C6E7AE2E3B08 |
| SHA1: | 7BB0D673EA5B7B9EA5CF8BB11669BB22E97C62FD |
| SHA256: | DCA27BD6346A7D4420D8139116B3A7571B0CB706E4B7D2DCCFCC55E959C60918 |
| SSDEEP: | 6144:soQAfNPXoA8c0/x0Z7SFbhISKxcPVziSueyROWSLx:soQAxozv/x0ZSFbavxKiSueyROPLx |
MALICIOUS
Drops the executable file immediately after the start
- WinRAR.exe (PID: 3264)
Changes the login/logoff helper path in the registry
- New folder.exe (PID: 2936)
Changes the autorun value in the registry
- New folder.exe (PID: 2936)
SUSPICIOUS
Starts CMD.EXE for commands execution
- New folder.exe (PID: 2936)
Reads the Internet Settings
- New folder.exe (PID: 2936)
Reads security settings of Internet Explorer
- New folder.exe (PID: 2936)
INFO
Checks supported languages
- New folder.exe (PID: 2936)
- wmpnscfg.exe (PID: 3072)
Reads the computer name
- New folder.exe (PID: 2936)
- wmpnscfg.exe (PID: 3072)
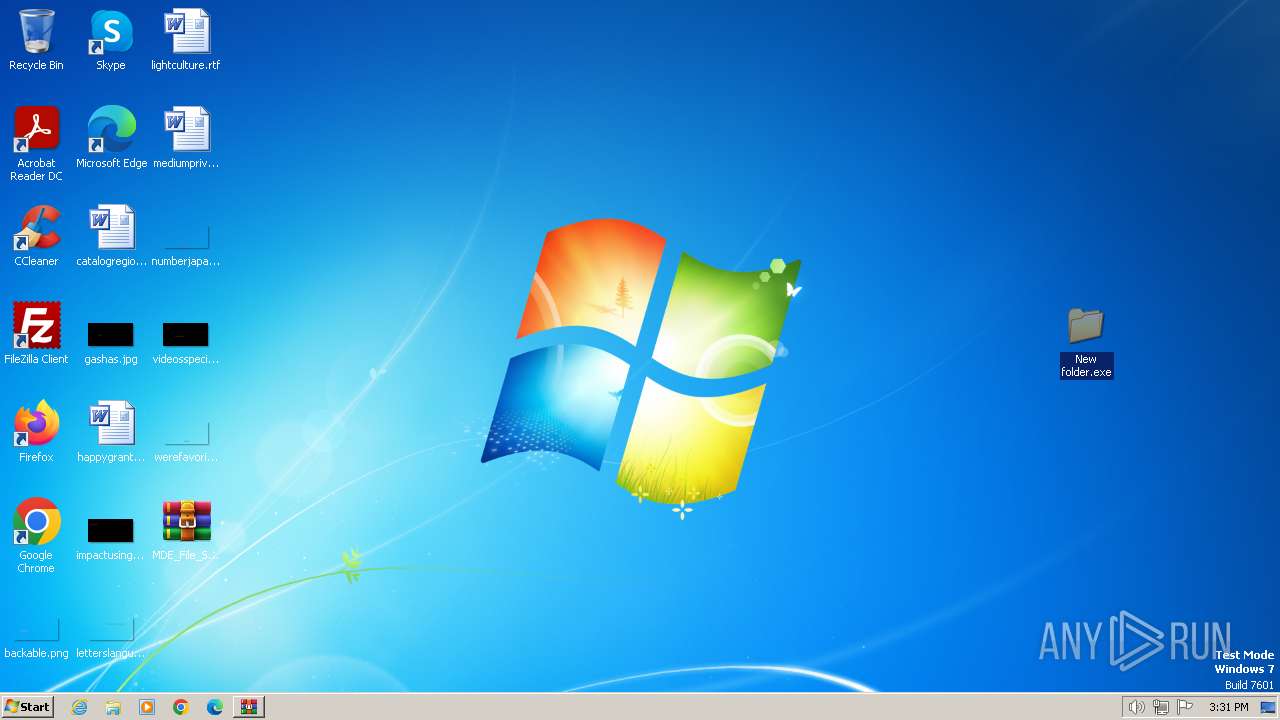
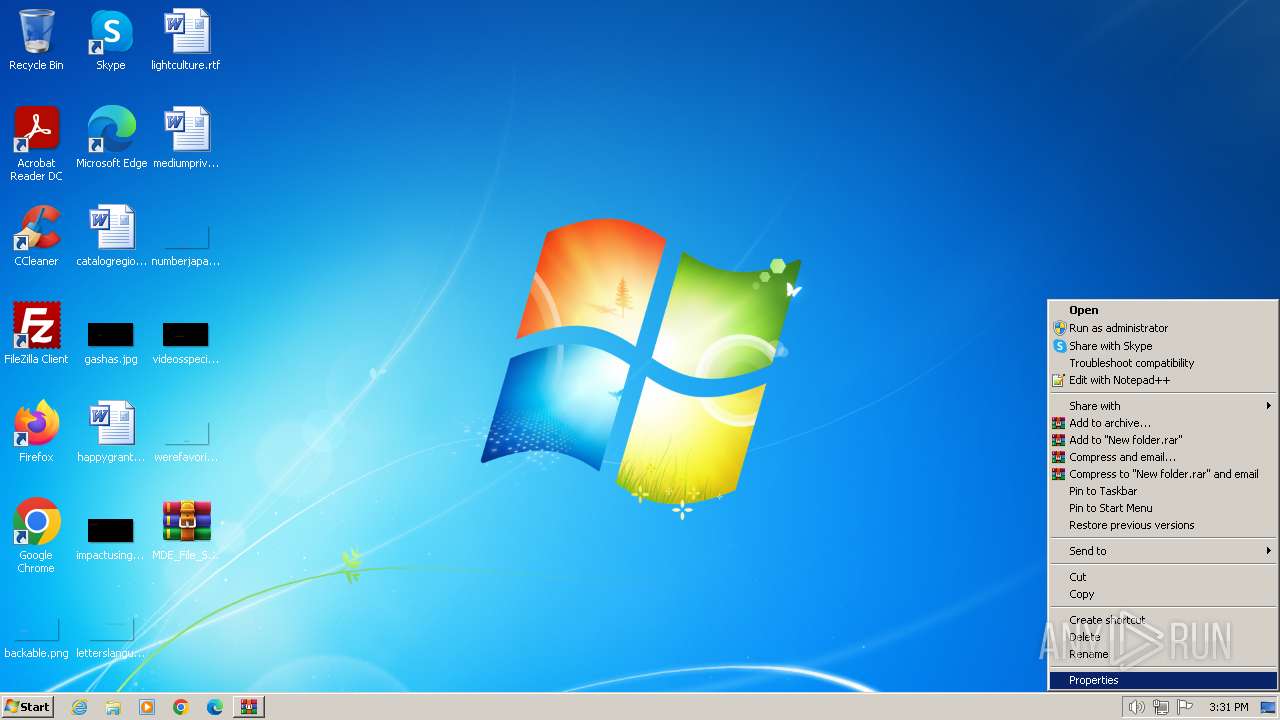
Manual execution by a user
- New folder.exe (PID: 2936)
- wmpnscfg.exe (PID: 3072)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3264)
Checks proxy server information
- New folder.exe (PID: 2936)
Reads the machine GUID from the registry
- New folder.exe (PID: 2936)
UPX packer has been detected
- New folder.exe (PID: 2936)
Creates files or folders in the user directory
- New folder.exe (PID: 2936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
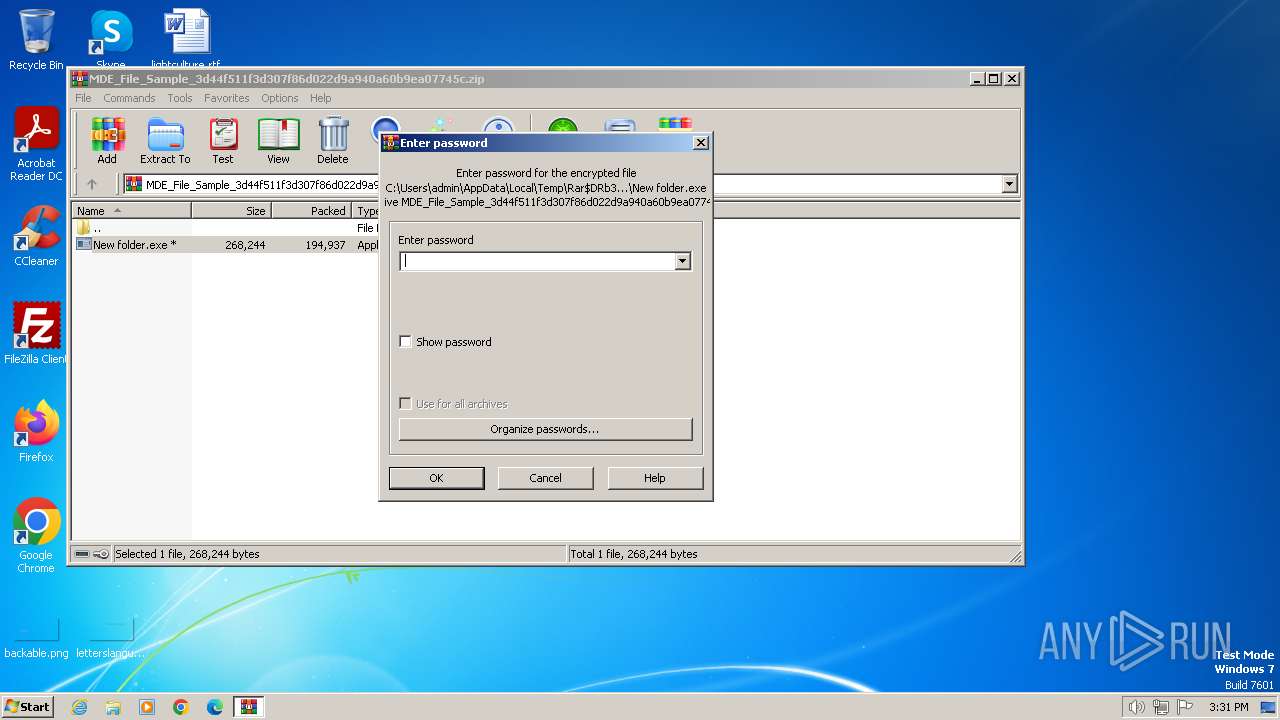
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:06:24 14:30:20 |
| ZipCRC: | 0x4d6a8689 |
| ZipCompressedSize: | 194937 |
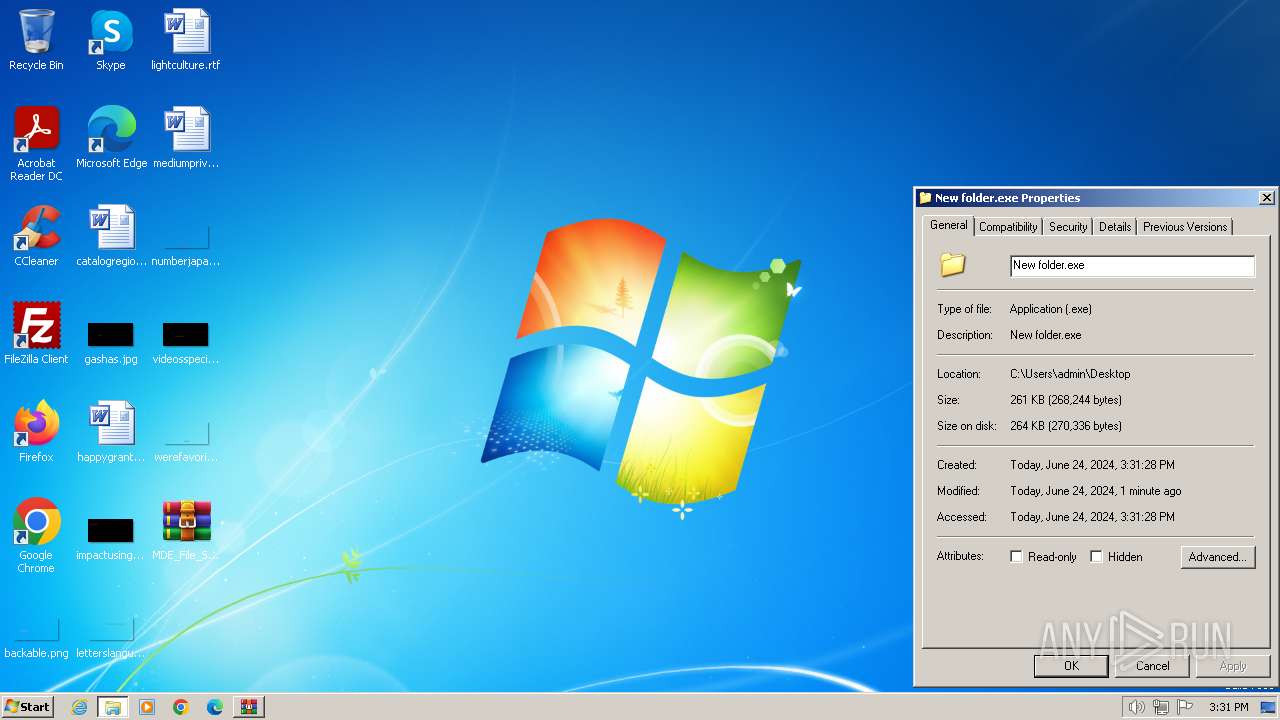
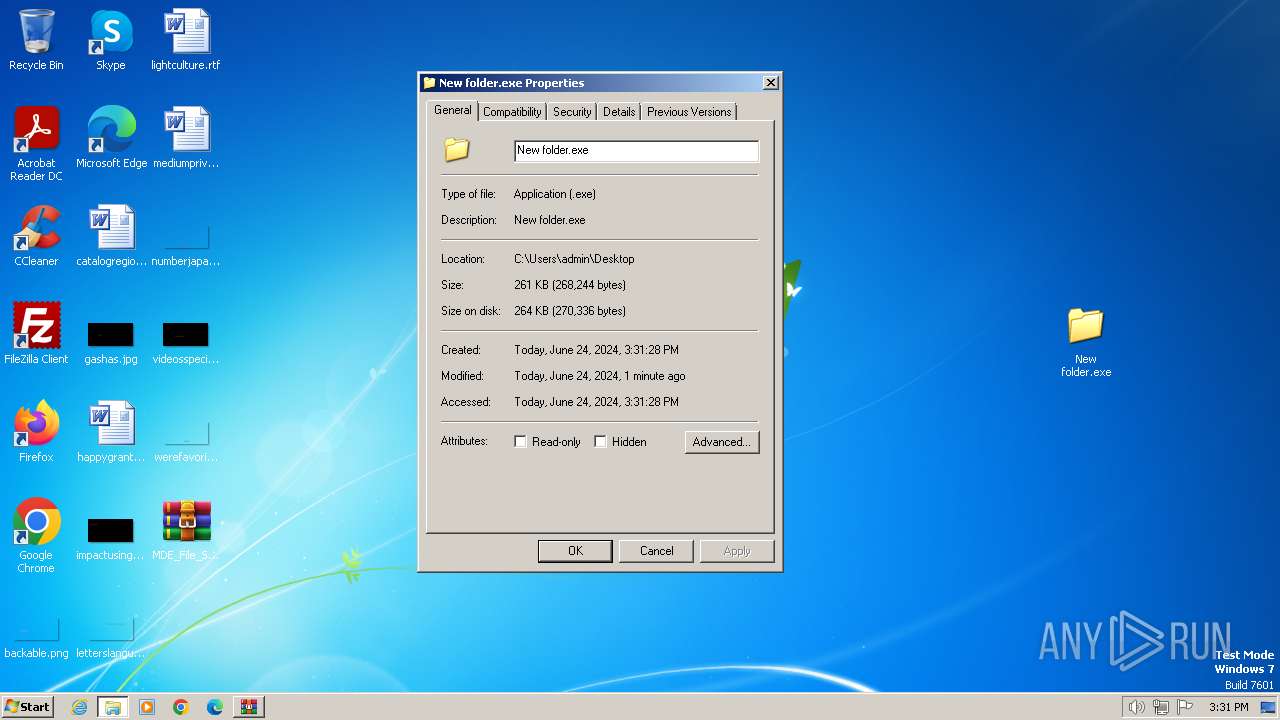
| ZipUncompressedSize: | 268244 |
| ZipFileName: | New folder.exe |
Total processes
51
Monitored processes
7
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
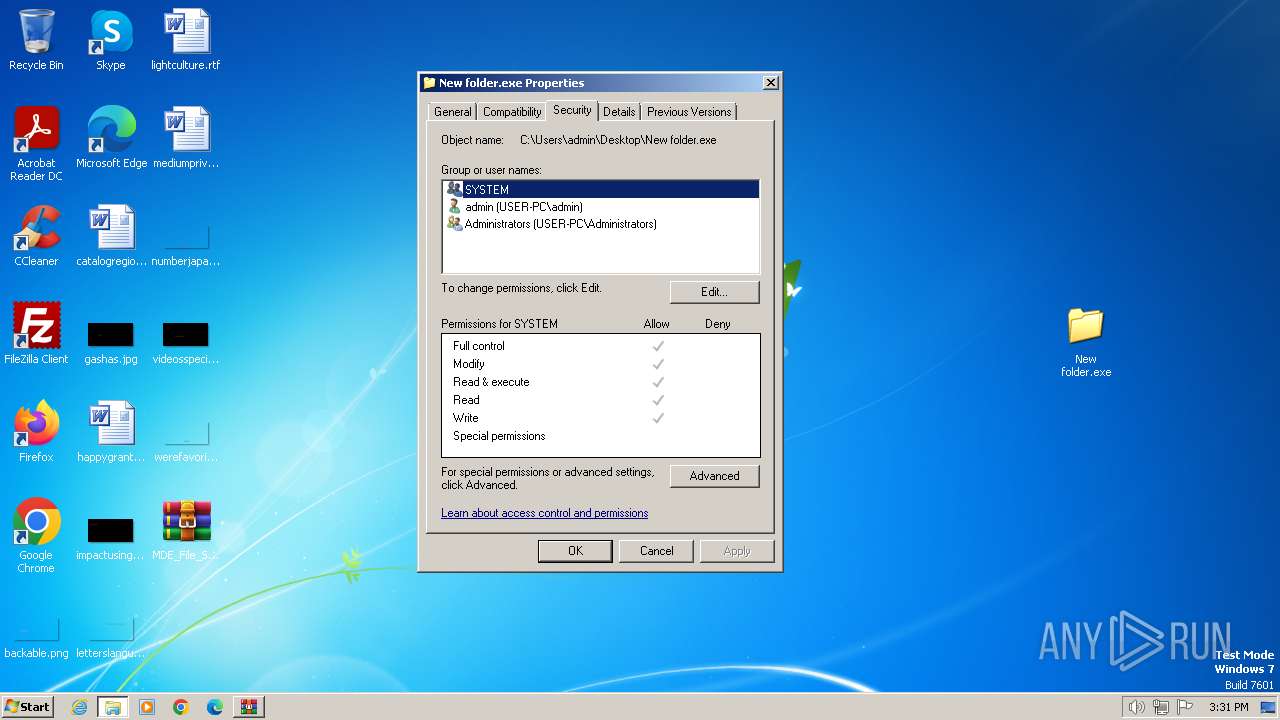
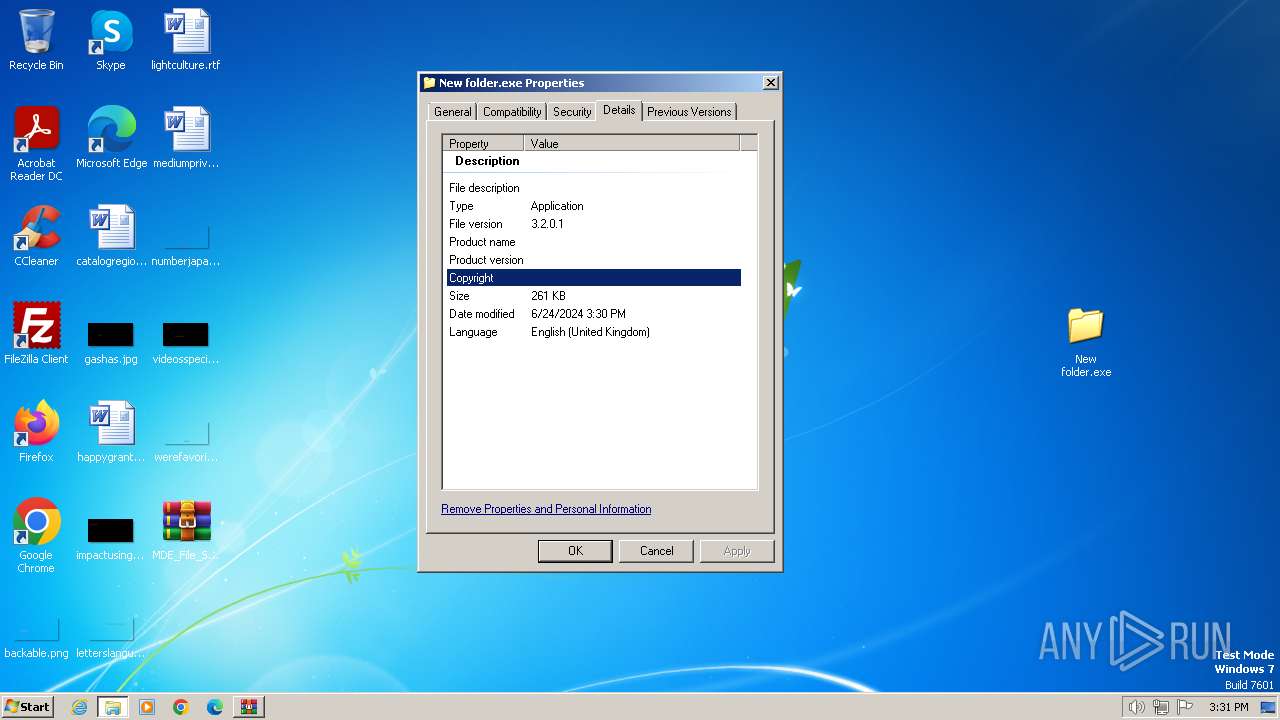
| 2936 | "C:\Users\admin\Desktop\New folder.exe" | C:\Users\admin\Desktop\New folder.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 3, 2, 0, 1 Modules
| |||||||||||||||
| 2948 | C:\Windows\system32\cmd.exe /C AT 09:00 /interactive /EVERY:m,t,w,th,f,s,su C:\Windows\system32\RVHOST.exe | C:\Windows\System32\cmd.exe | — | New folder.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2956 | C:\Windows\system32\cmd.exe /C AT /delete /yes | C:\Windows\System32\cmd.exe | — | New folder.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3072 | "C:\Program Files\Windows Media Player\wmpnscfg.exe" | C:\Program Files\Windows Media Player\wmpnscfg.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Media Player Network Sharing Service Configuration Application Exit code: 0 Version: 12.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3144 | AT /delete /yes | C:\Windows\System32\at.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Schedule service command line interface Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3164 | AT 09:00 /interactive /EVERY:m,t,w,th,f,s,su C:\Windows\system32\RVHOST.exe | C:\Windows\System32\at.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Schedule service command line interface Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3264 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\MDE_File_Sample_3d44f511f3d307f86d022d9a940a60b9ea07745c.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
Total events
3 643
Read events
3 568
Write events
63
Delete events
12
Modification events
| (PID) Process: | (3264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3264) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\phacker.zip | |||
| (PID) Process: | (3264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (3264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (3264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\MDE_File_Sample_3d44f511f3d307f86d022d9a940a60b9ea07745c.zip | |||
| (PID) Process: | (3264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3264) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
1
Suspicious files
0
Text files
2
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2936 | New folder.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\setting[1].htm | html | |
MD5:0104C301C5E02BD6148B8703D19B3A73 | SHA256:446A6087825FA73EADB045E5A2E9E2ADF7DF241B571228187728191D961DDA1F | |||
| 2936 | New folder.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\setting[1].htm | html | |
MD5:0104C301C5E02BD6148B8703D19B3A73 | SHA256:446A6087825FA73EADB045E5A2E9E2ADF7DF241B571228187728191D961DDA1F | |||
| 3264 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb3264.29425\New folder.exe | executable | |
MD5:B16A49EB03050DB6B78990A128B84D81 | SHA256:D768DCD930175ED77DFDFD0236C311A626725B144958C5043A6DE4D030F76787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
19
DNS requests
8
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 23.50.131.216:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 23.48.23.156:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
2936 | New folder.exe | GET | 301 | 104.18.38.120:80 | http://www.freewebs.com/nhattruongquang/setting.nql | unknown | — | — | unknown |
2936 | New folder.exe | GET | 301 | 104.18.38.120:80 | http://www.freewebs.com/nhattruongquang/setting.xls | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 23.50.131.208:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?fbe613066ac7852b | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1372 | svchost.exe | 4.231.128.59:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2936 | New folder.exe | 49.13.77.253:80 | nhatquanglan2.0catch.com | Hetzner Online GmbH | DE | unknown |
1372 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1372 | svchost.exe | 23.50.131.216:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 23.48.23.156:80 | crl.microsoft.com | Akamai International B.V. | DE | unknown |
1372 | svchost.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | unknown |
1060 | svchost.exe | 23.50.131.208:80 | ctldl.windowsupdate.com | Akamai International B.V. | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
nhatquanglan2.0catch.com |
| unknown |
settings-win.data.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.freewebs.com |
| whitelisted |
www.vistaprint.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2936 | New folder.exe | A Network Trojan was detected | ET WORM Possible Worm Sohanad.Z or Other Infection Request for setting.nql |
2936 | New folder.exe | A Network Trojan was detected | ET MALWARE Possible Worm W32.Svich or Other Infection Request for setting.xls |