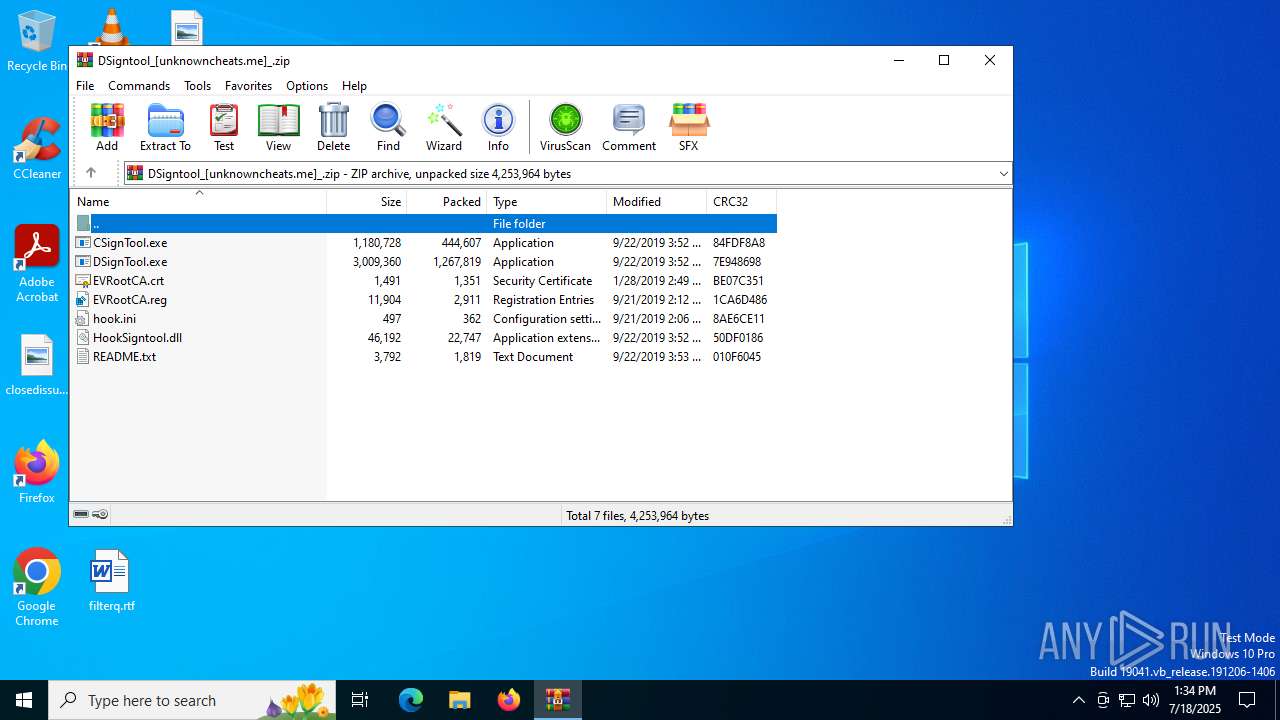
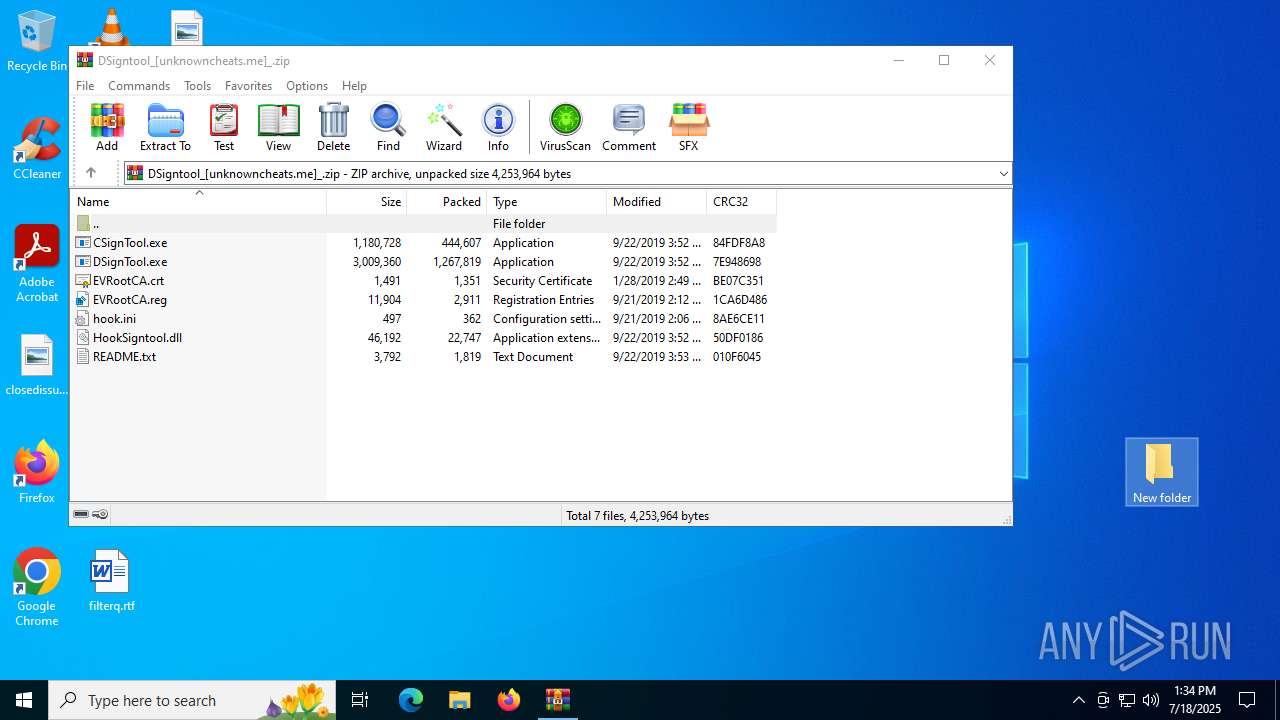
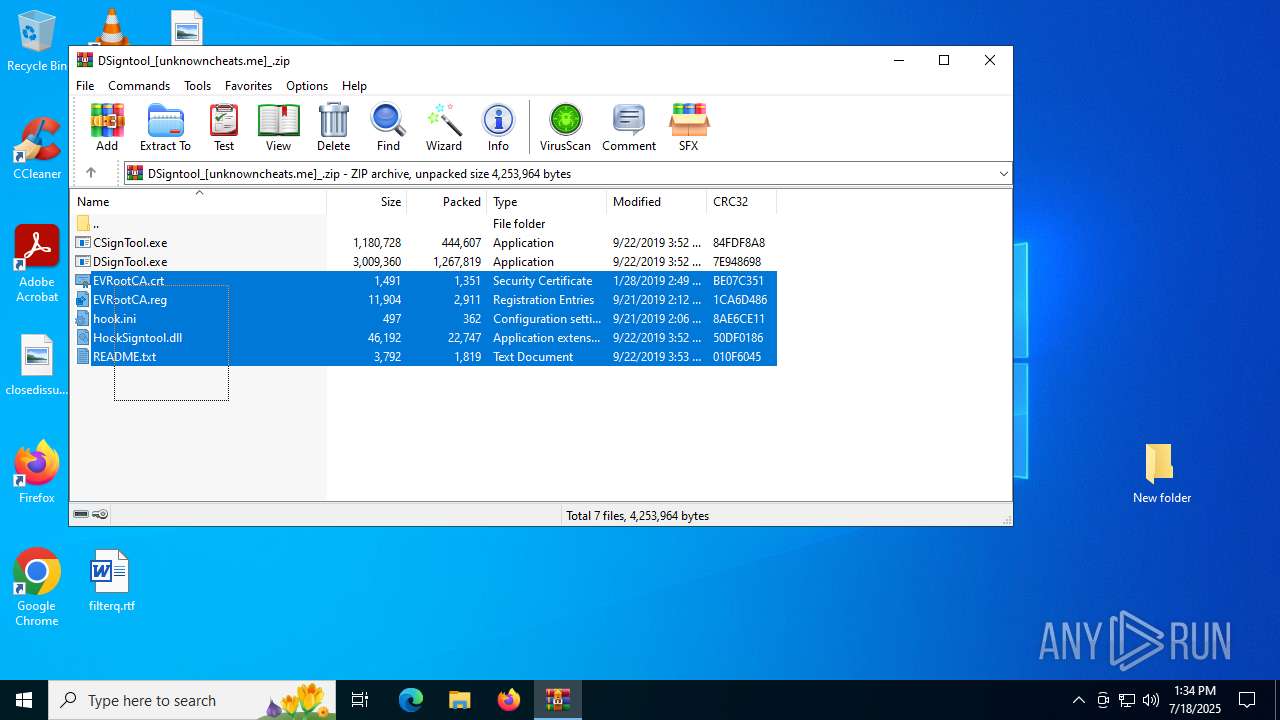
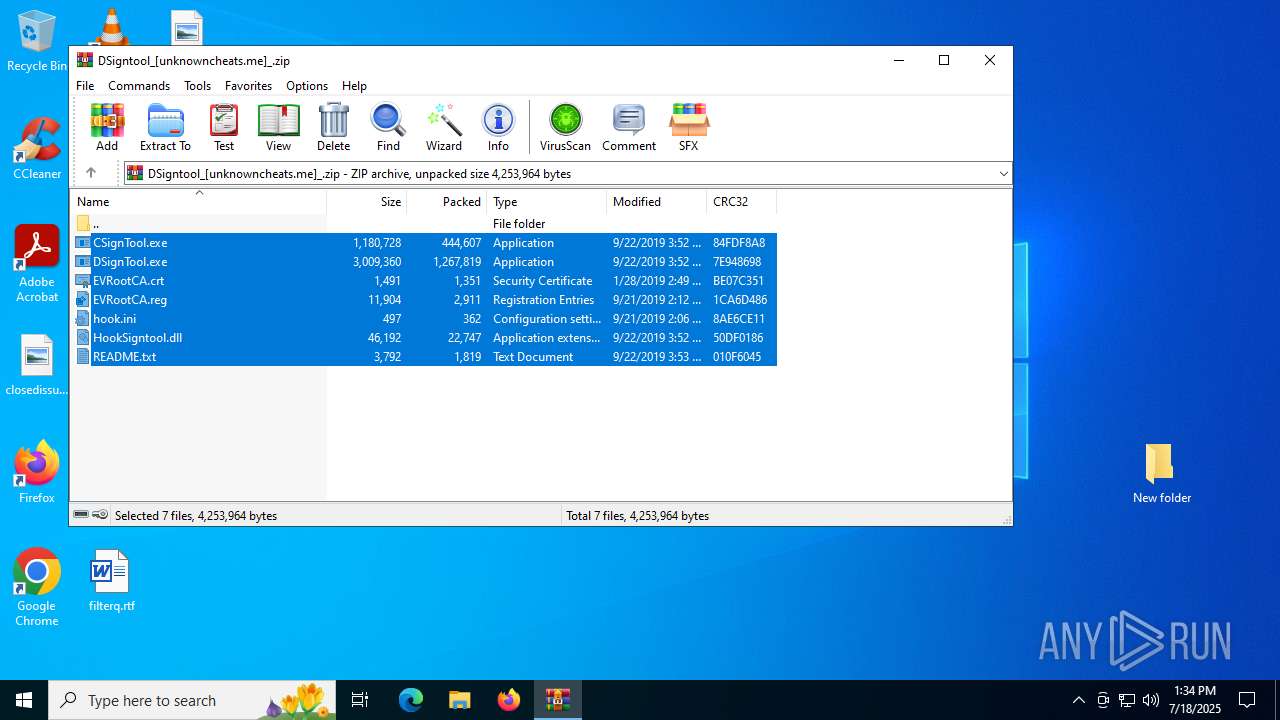
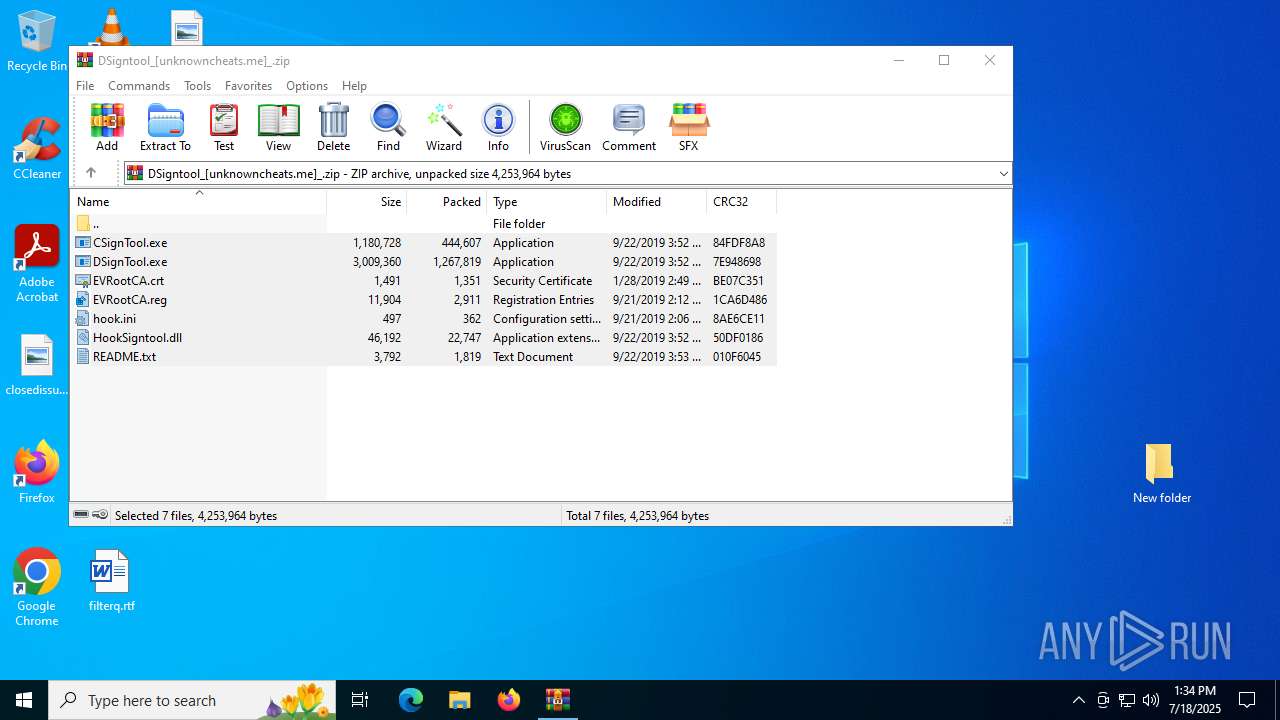
| File name: | DSigntool_[unknowncheats.me]_.zip |
| Full analysis: | https://app.any.run/tasks/fa9114cd-b166-4f56-ac4e-463f7b03f6d9 |
| Verdict: | Malicious activity |
| Analysis date: | July 18, 2025, 13:33:56 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 3300C92619C9B84607ABC9752A6BC291 |
| SHA1: | 0CBC7C8B181553891EB295B0C65C3CC68777096A |
| SHA256: | DC9DD00BE3CDCC0C90340E3430188965FBCAF378A6EEC30C15C627B4A3A80C90 |
| SSDEEP: | 98304:Pff+AR1GEvnSDE8Jk9d5P+NdhnVIXIvoyqMSAR39wuFYhuz+YhzFkrpFiQHkqTd/:YIjDH |
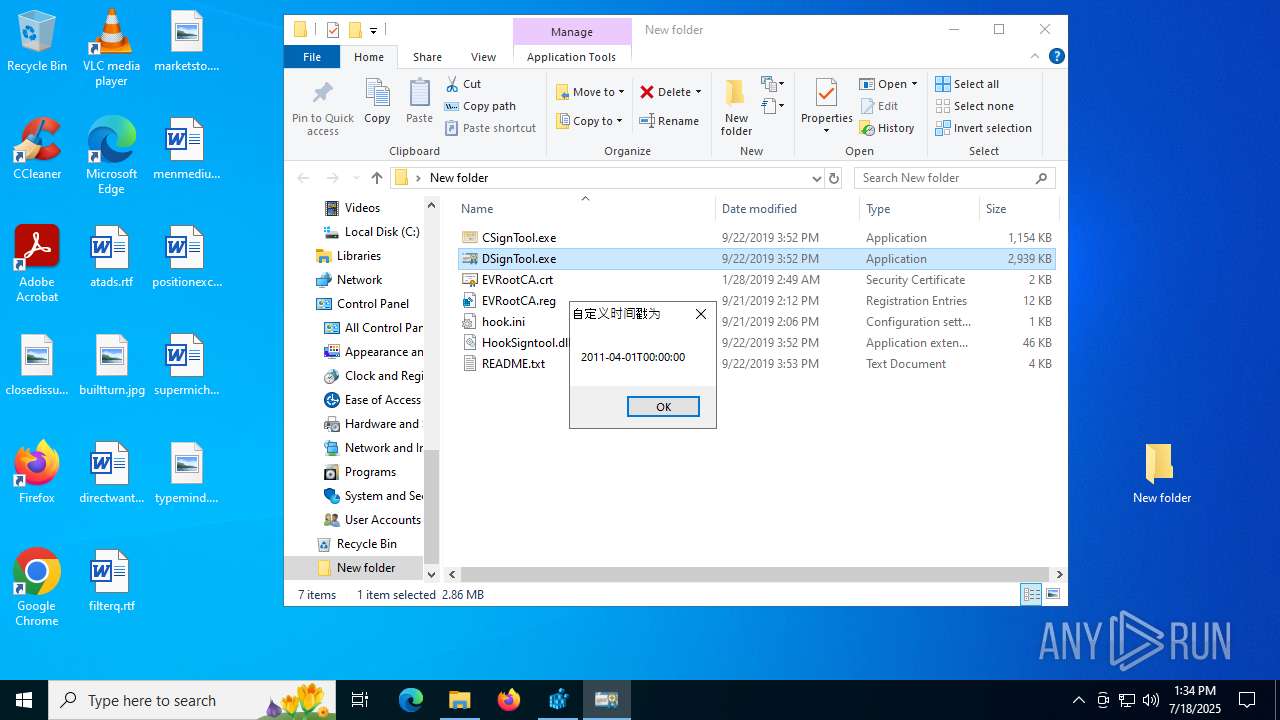
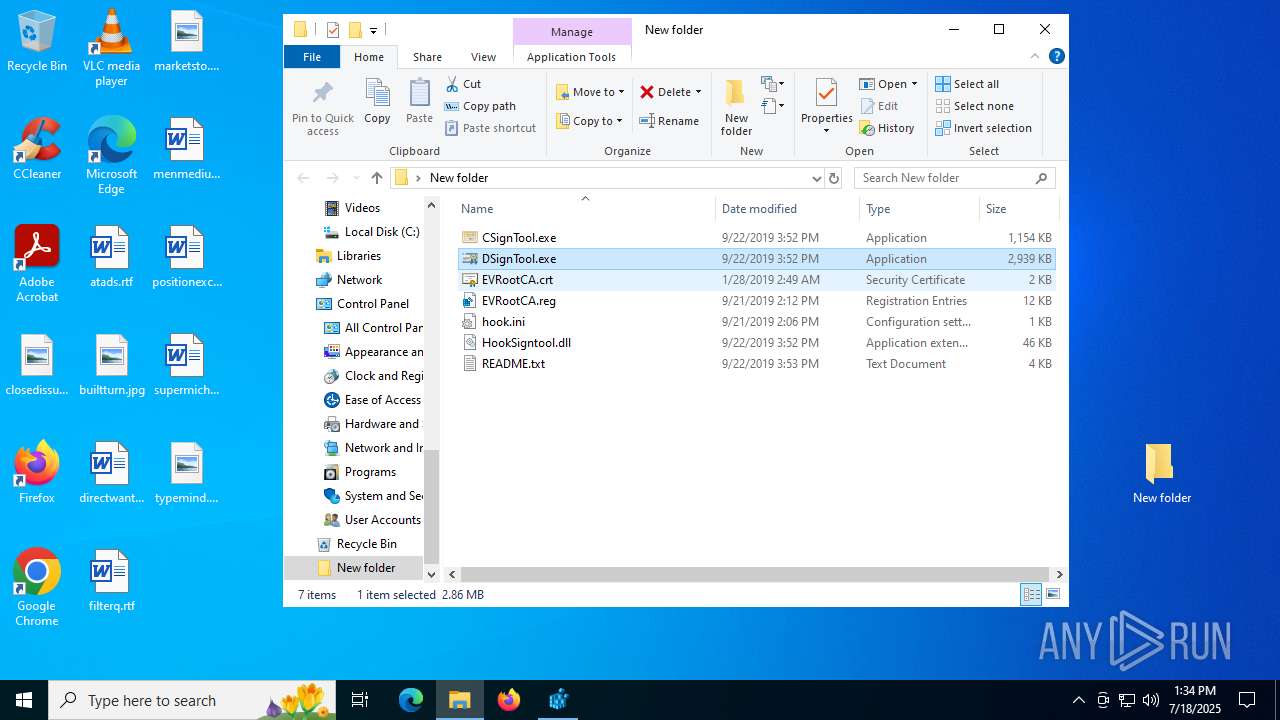
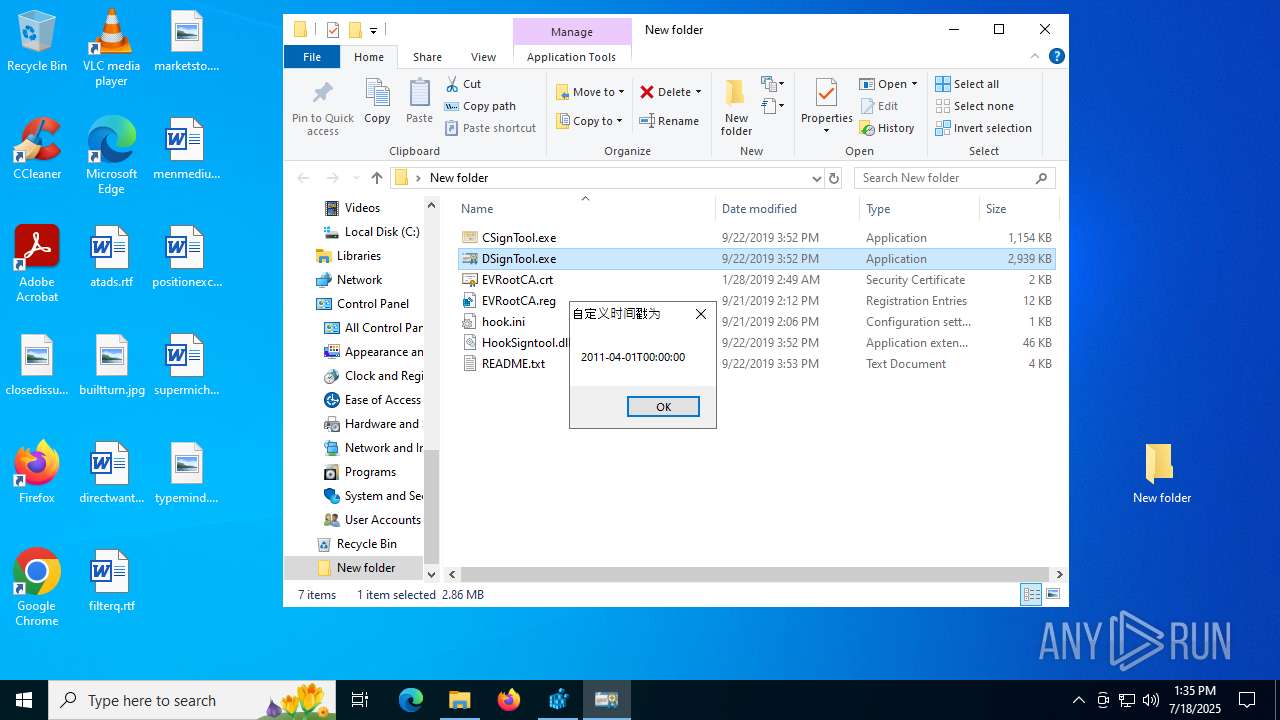
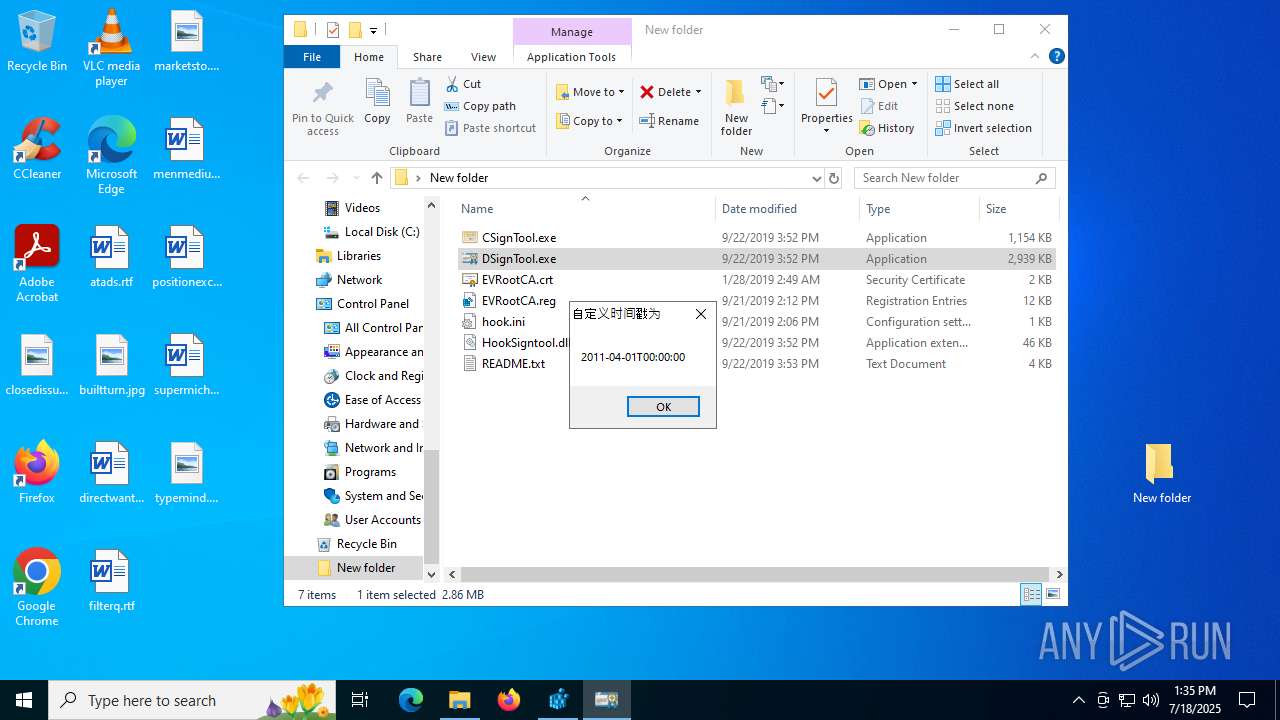
MALICIOUS
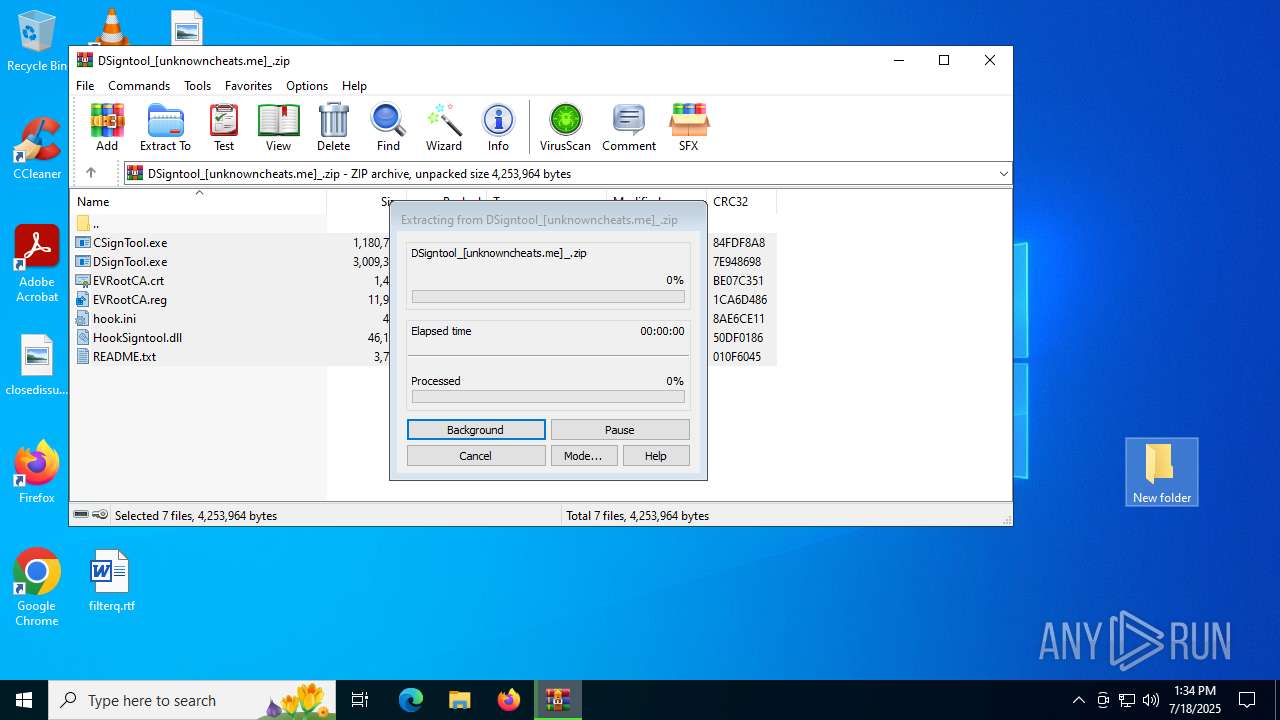
Generic archive extractor
- WinRAR.exe (PID: 3148)
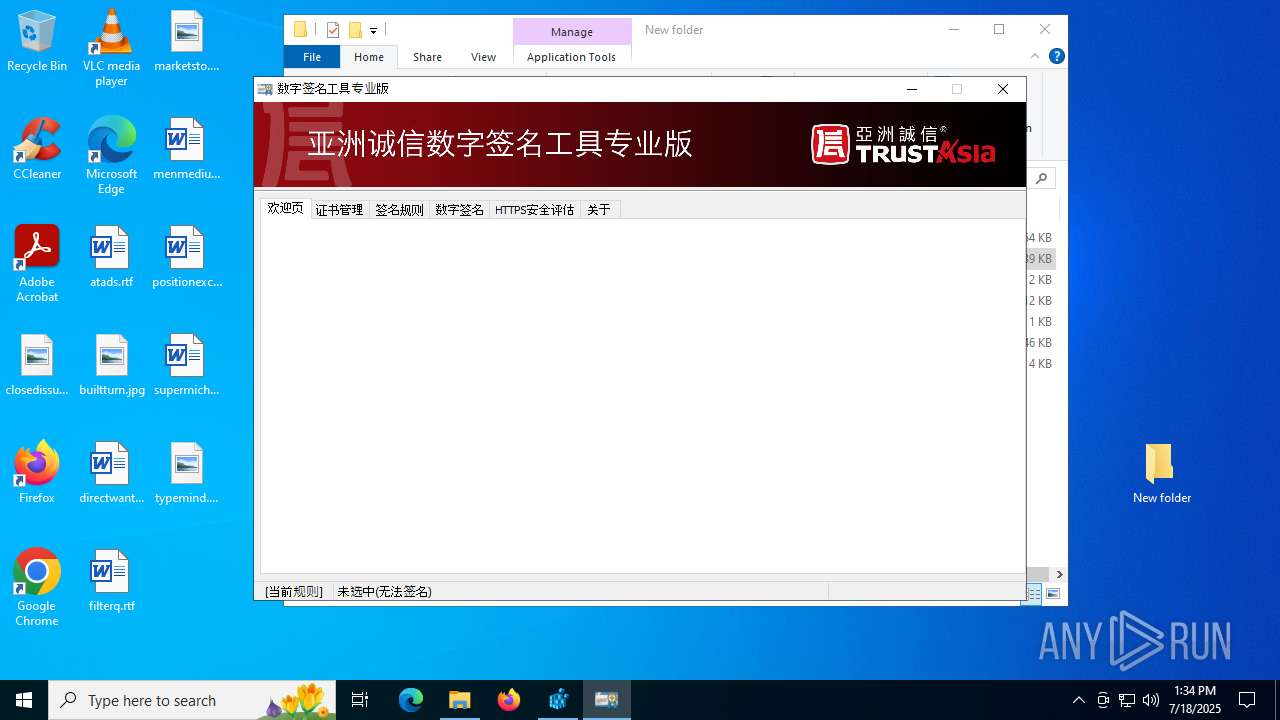
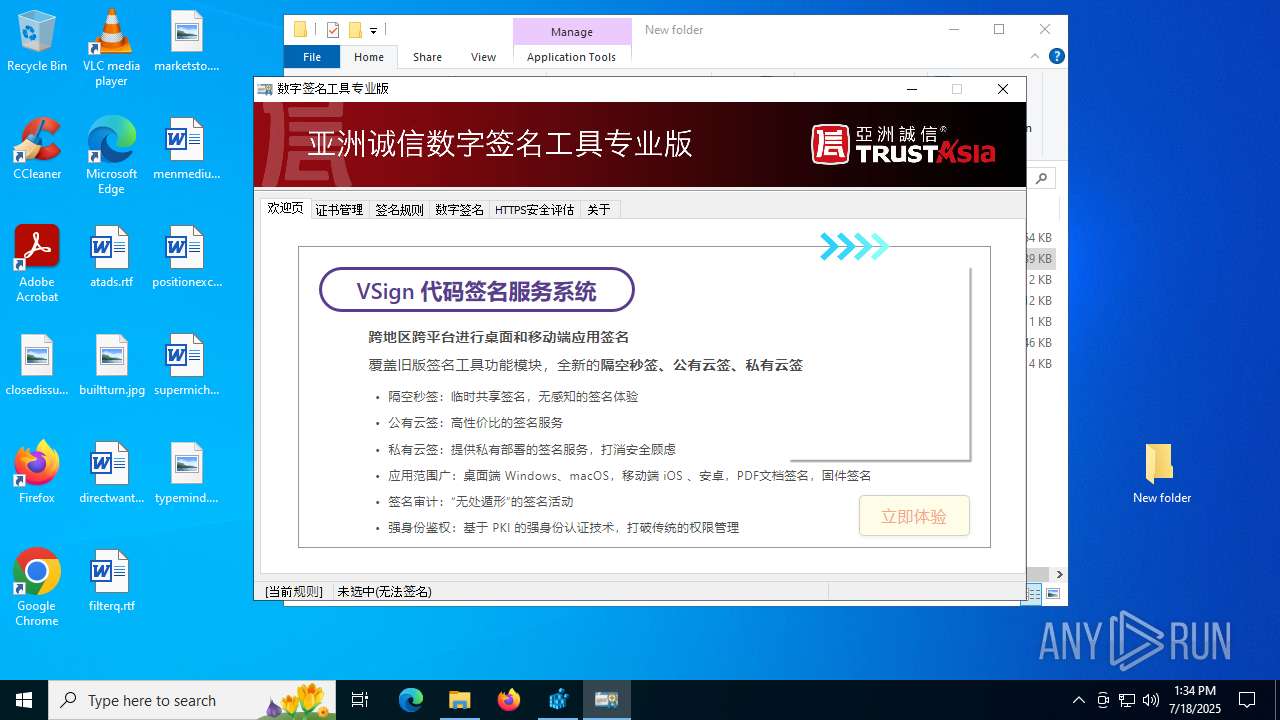
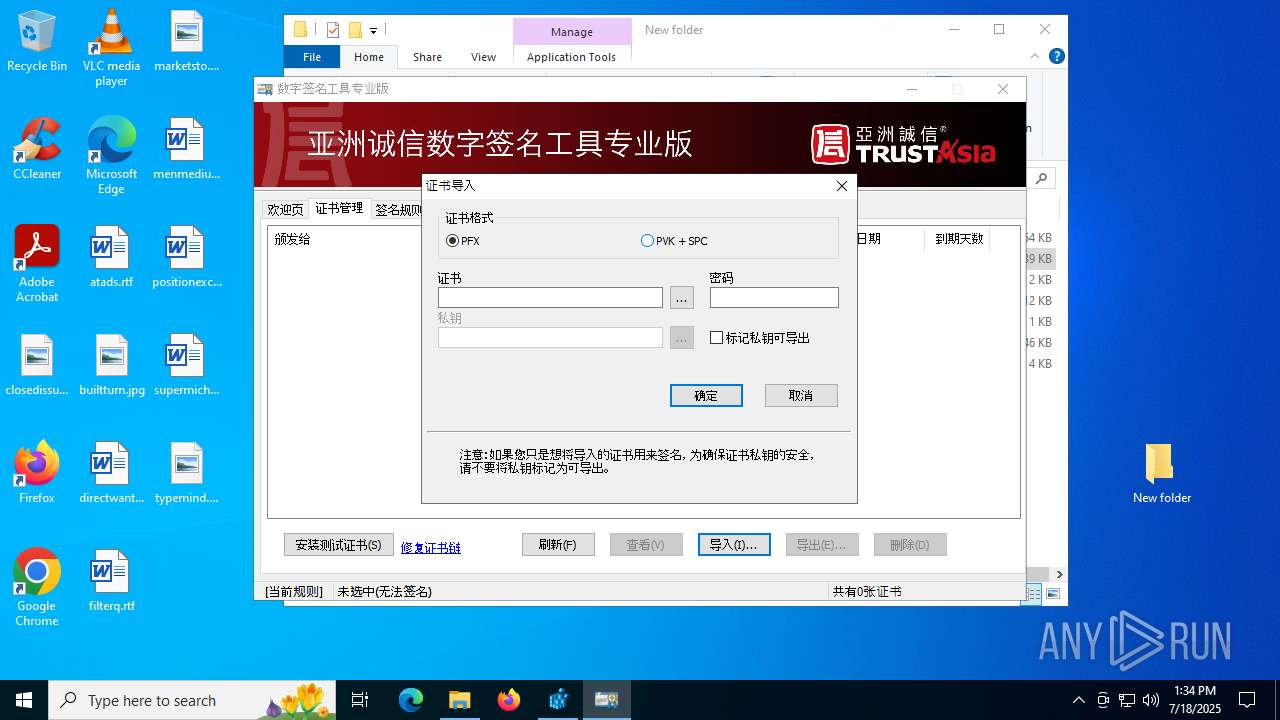
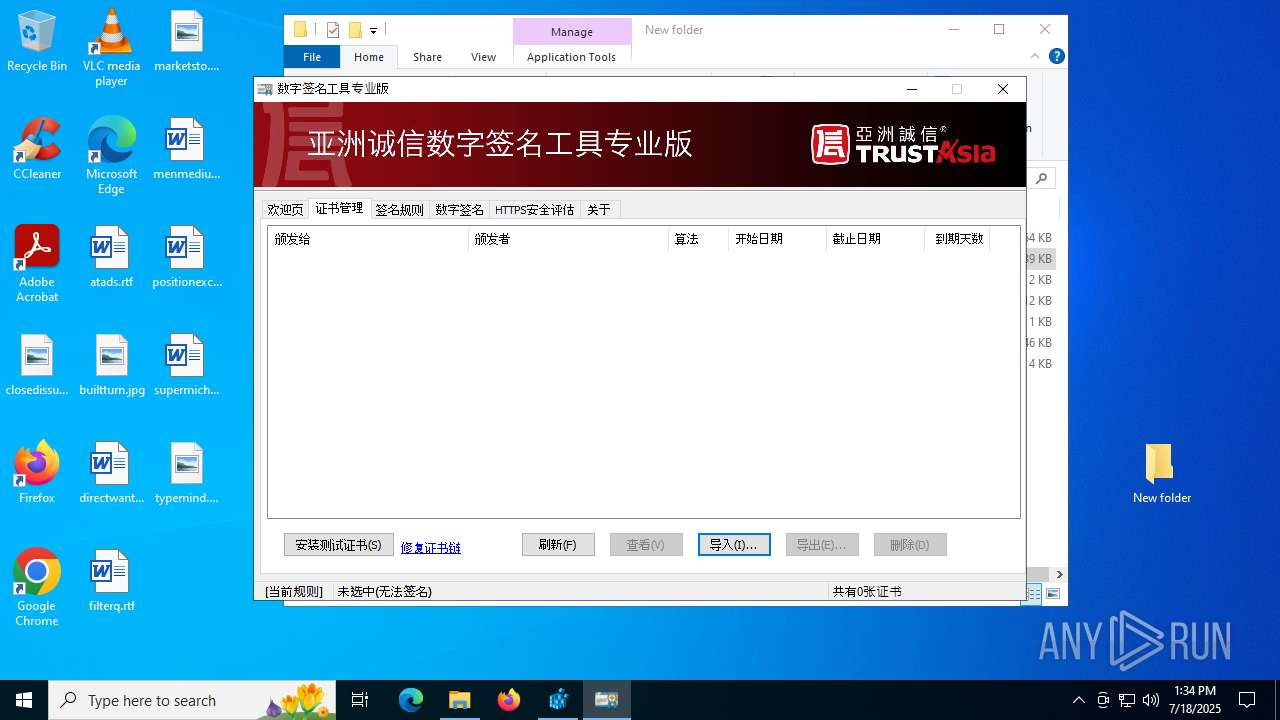
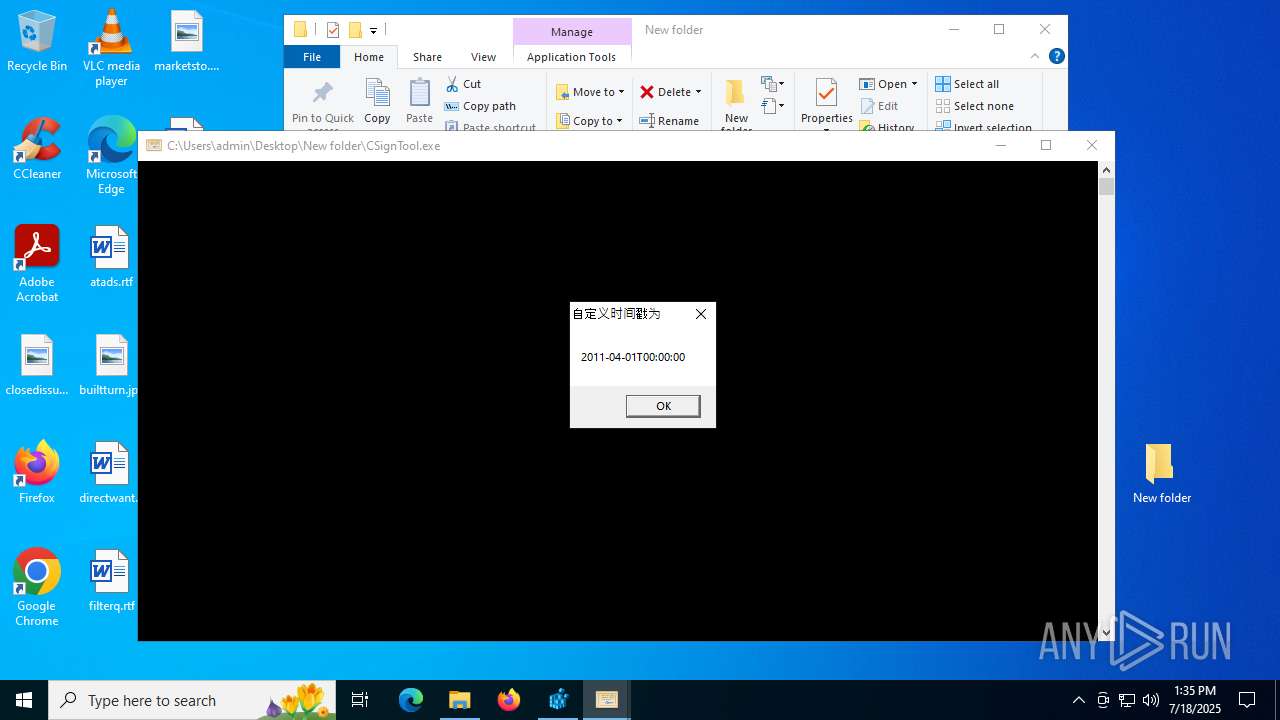
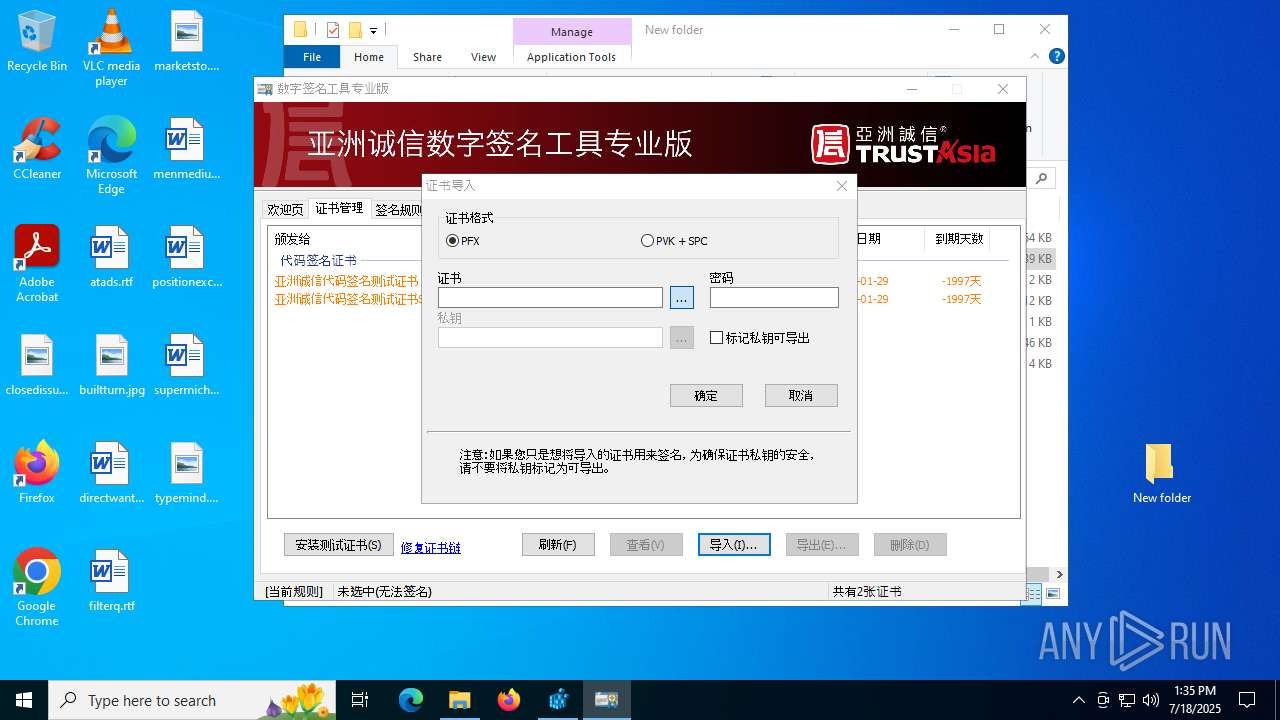
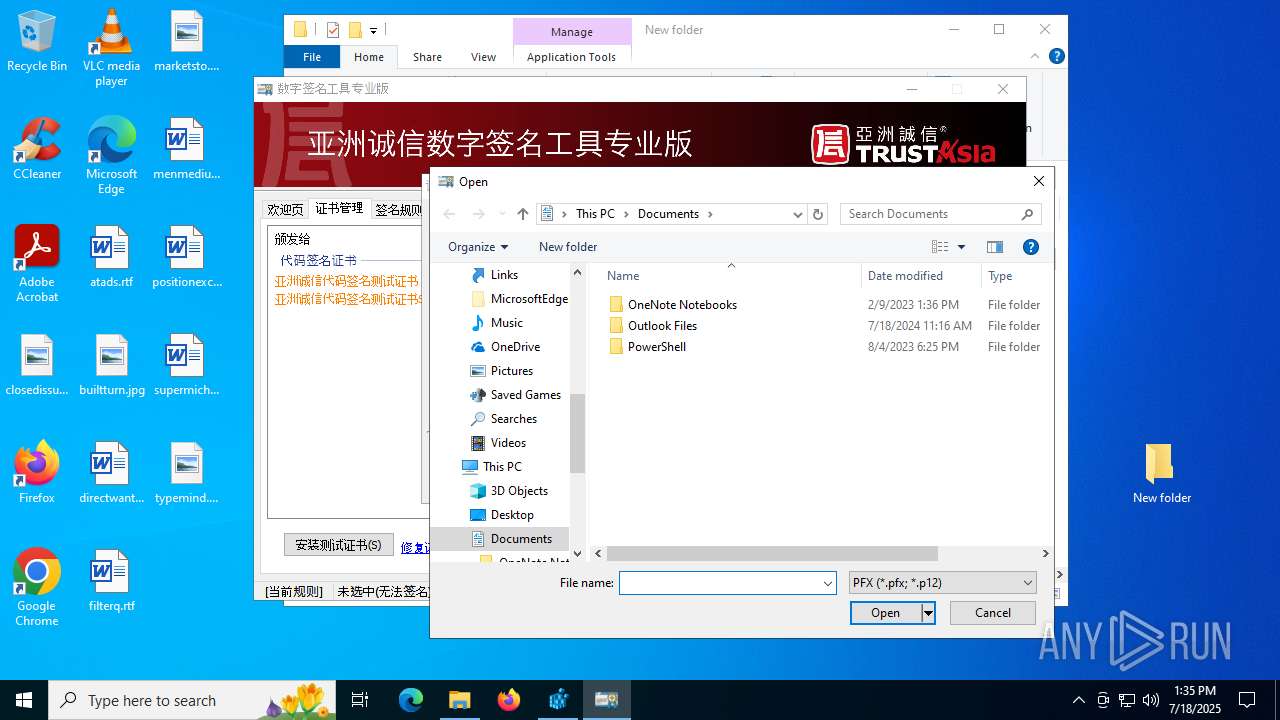
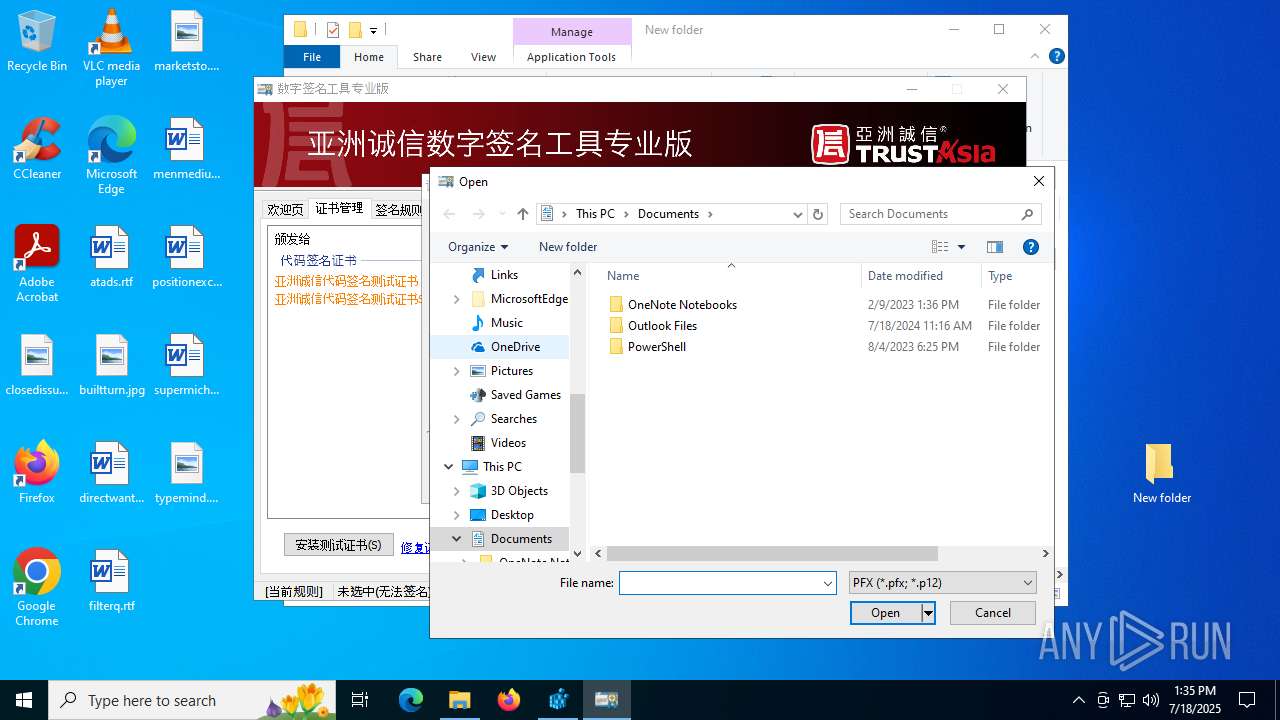
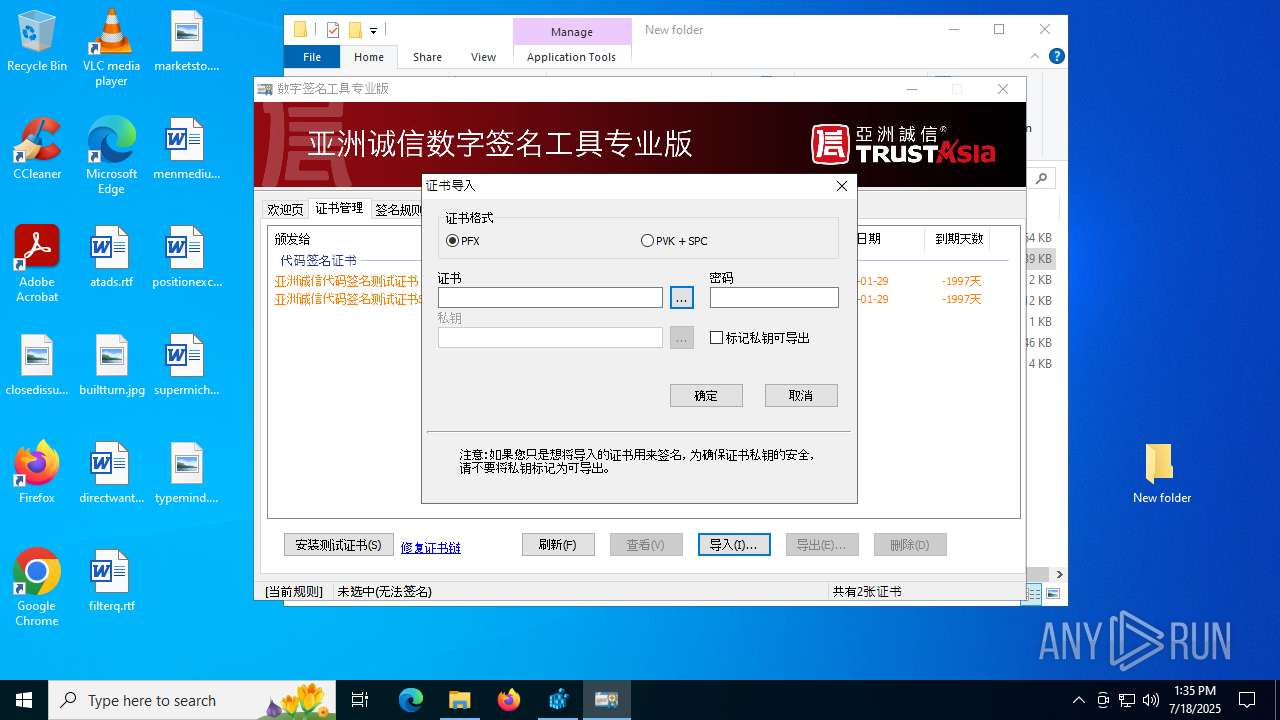
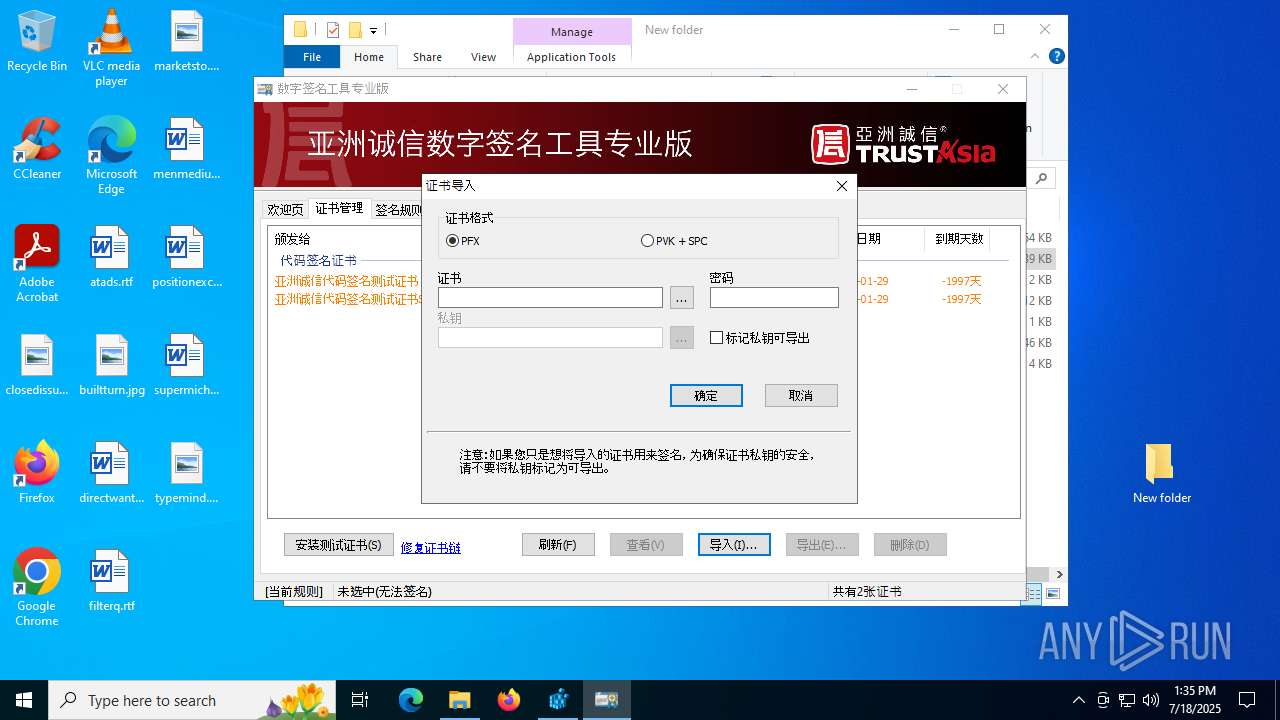
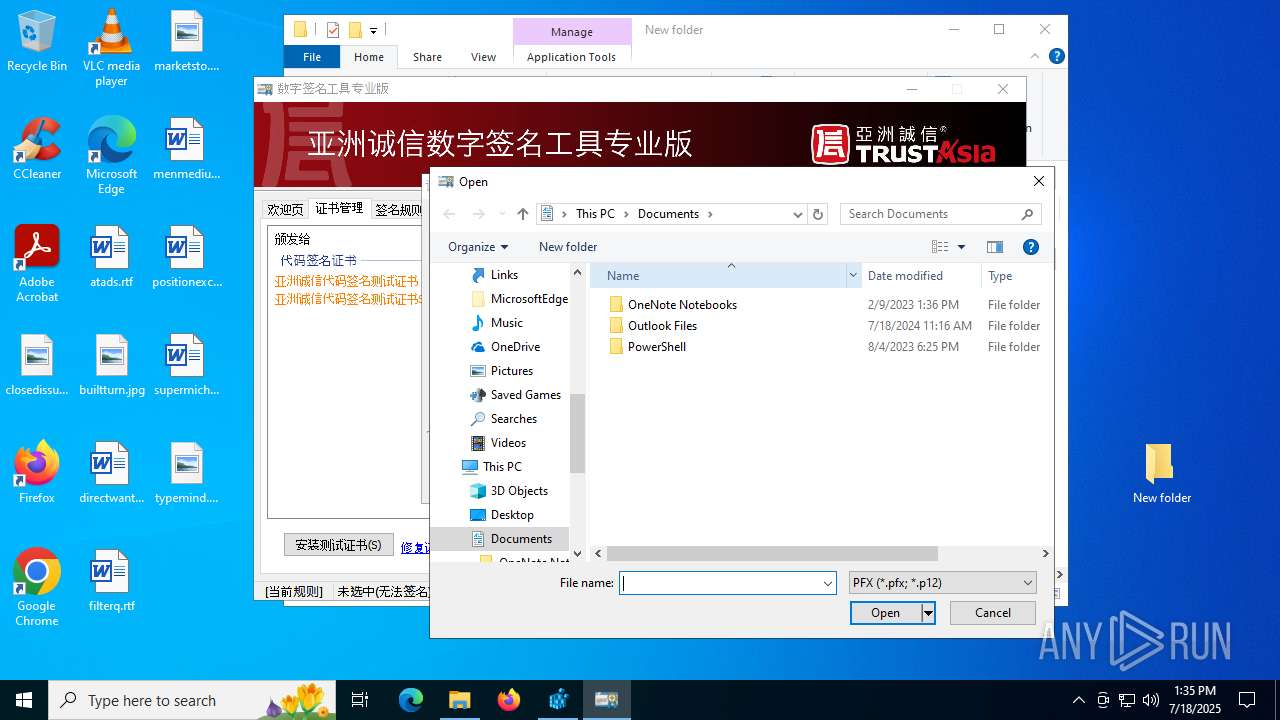
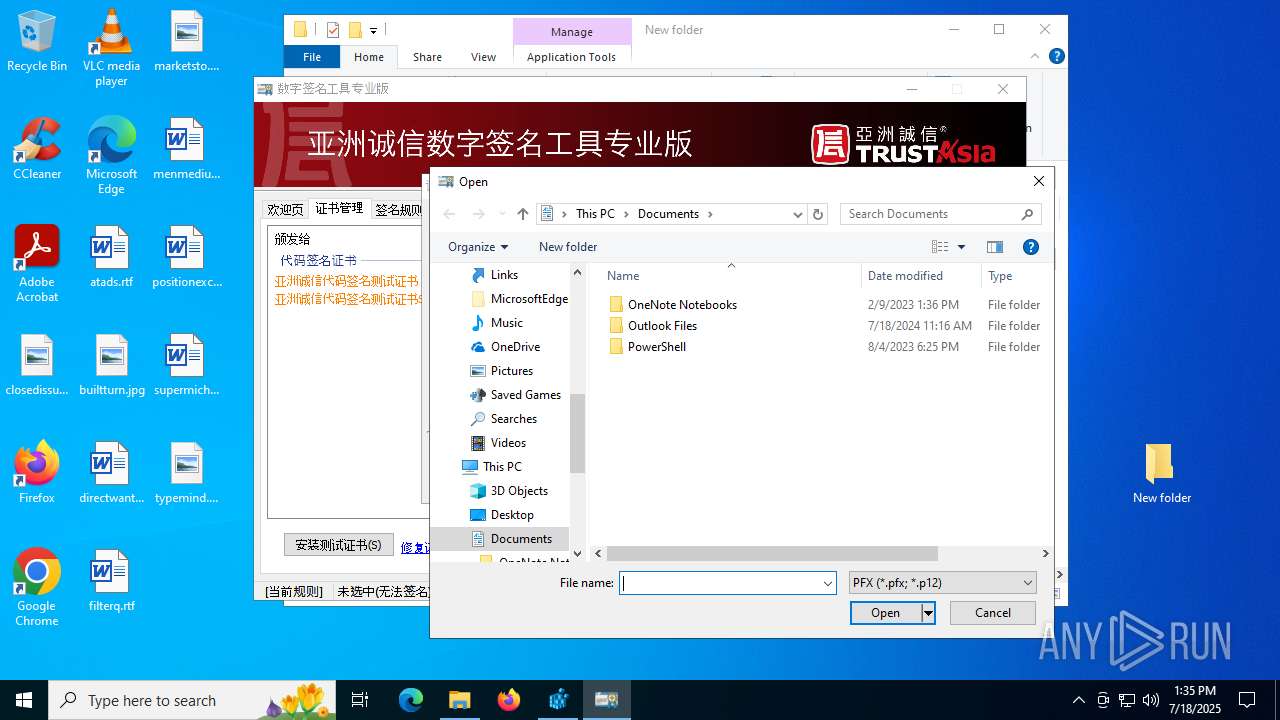
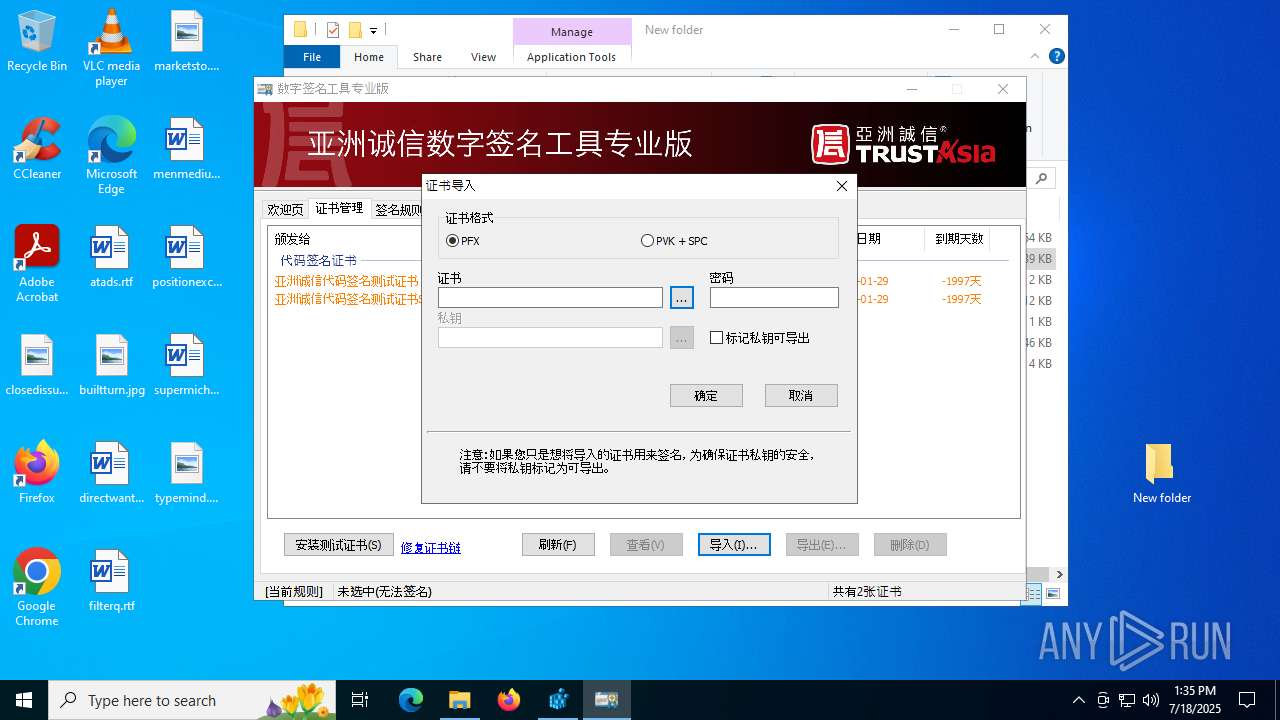
Executing a file with an untrusted certificate
- CSignTool.exe (PID: 2188)
- DSignTool.exe (PID: 436)
- DSignTool.exe (PID: 6764)
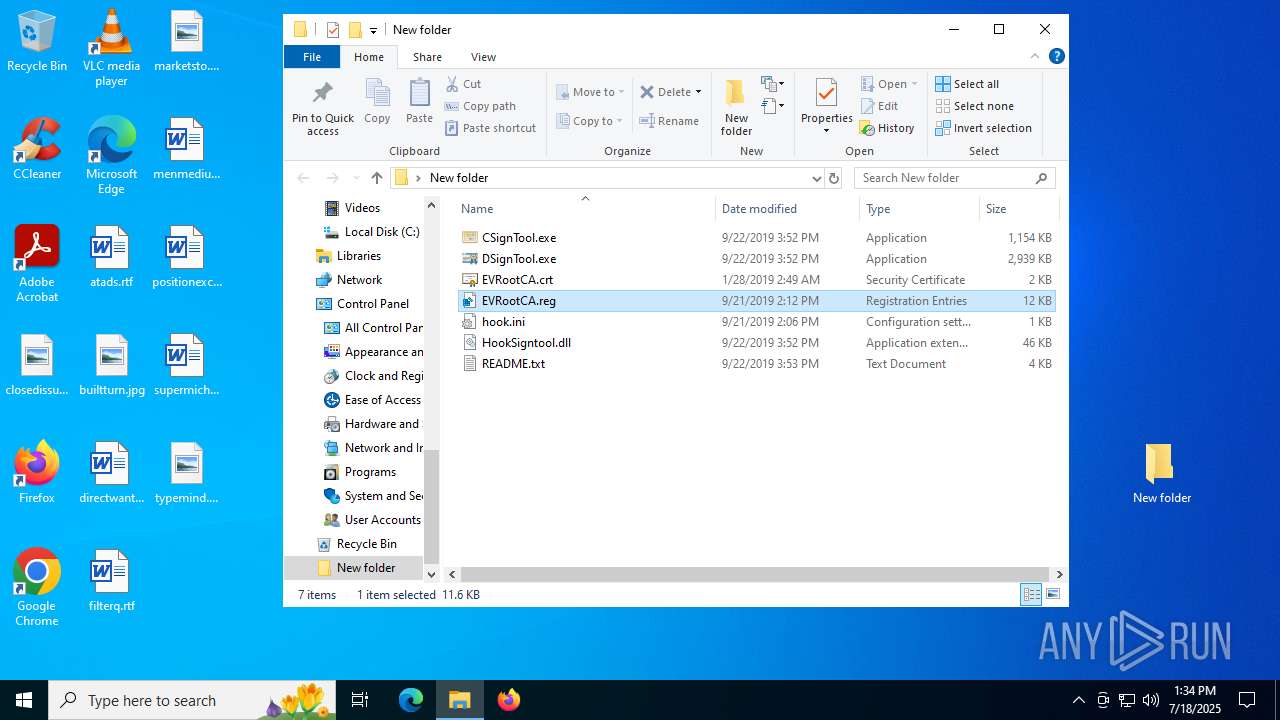
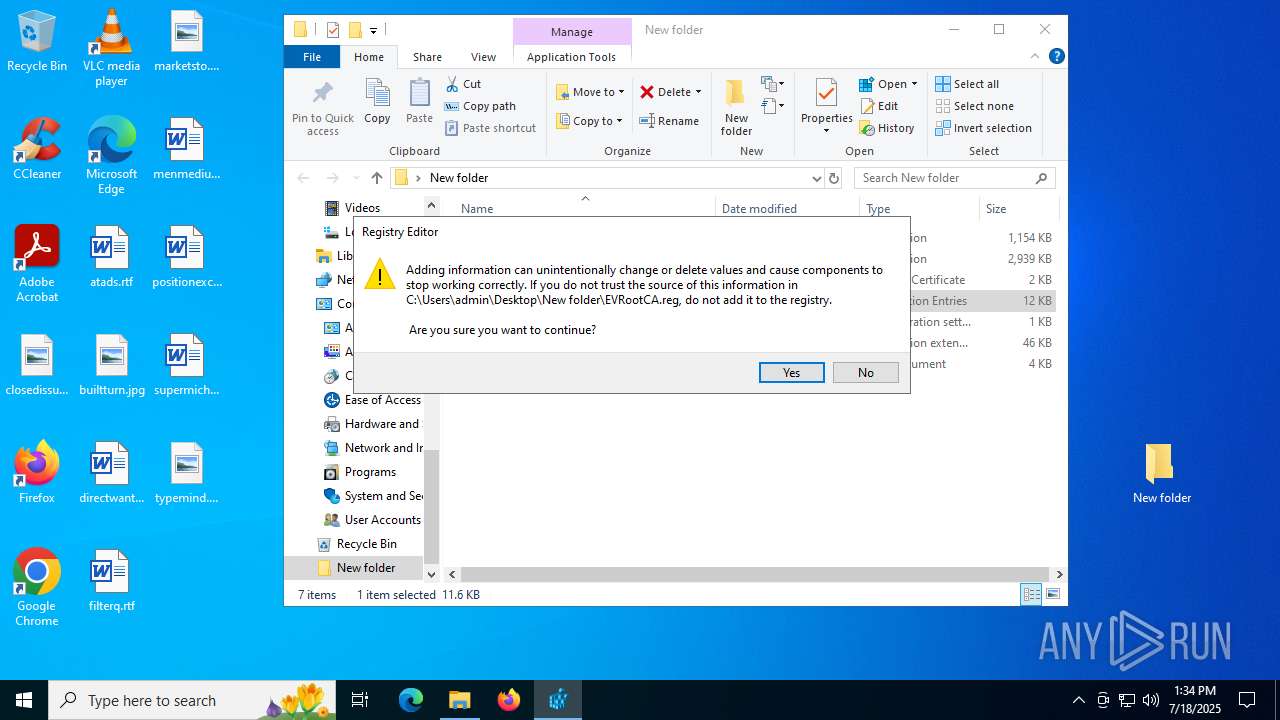
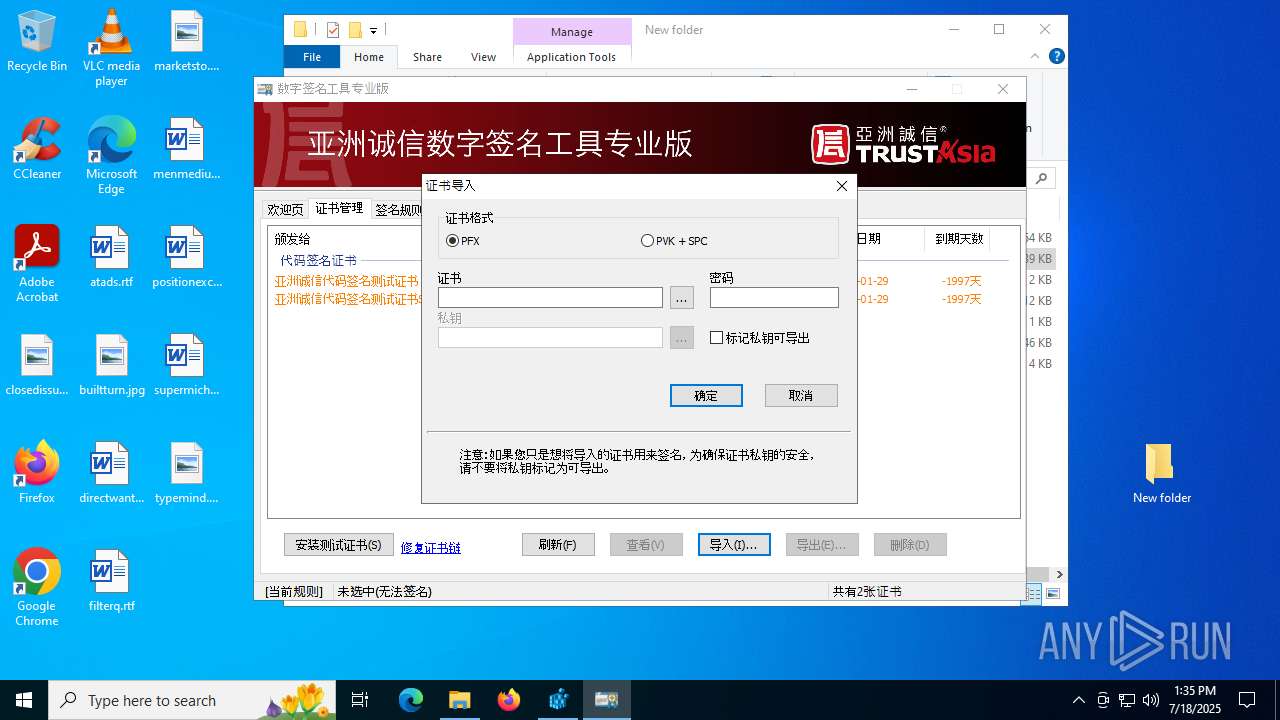
SUSPICIOUS
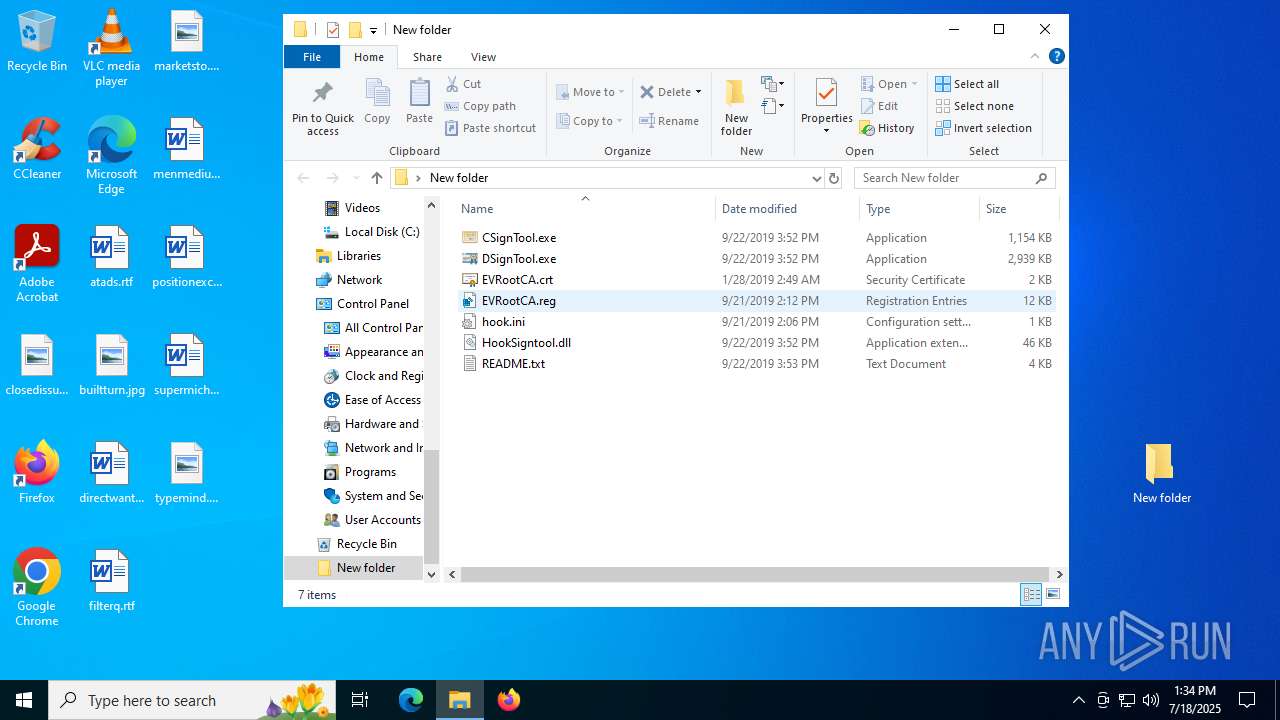
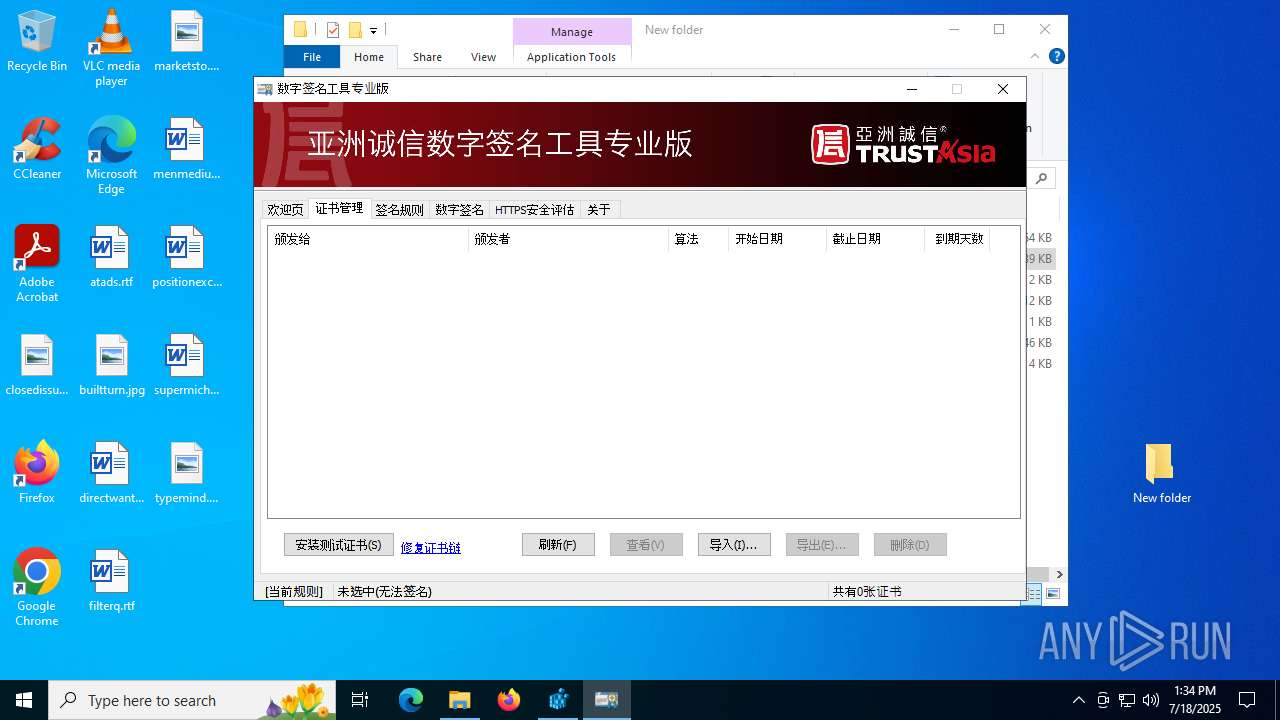
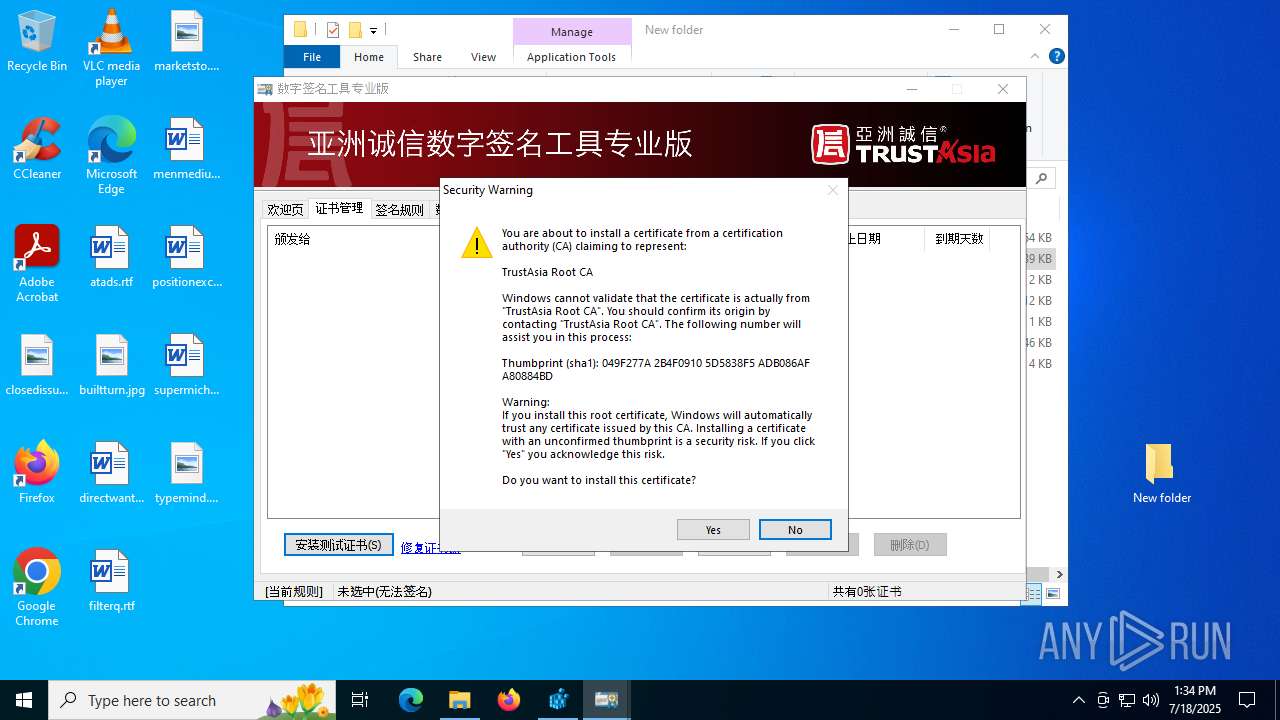
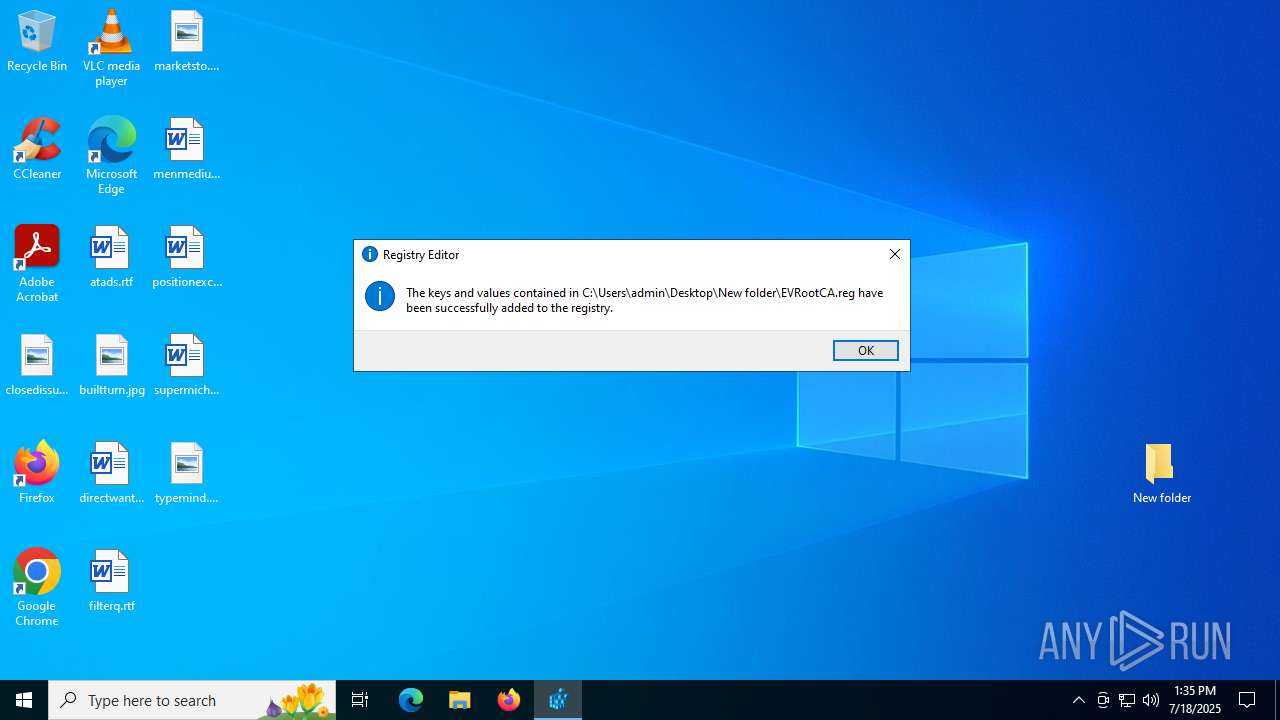
Adds/modifies Windows certificates
- regedit.exe (PID: 3556)
- DSignTool.exe (PID: 436)
There is functionality for taking screenshot (YARA)
- DSignTool.exe (PID: 436)
- DSignTool.exe (PID: 6764)
Reads Microsoft Outlook installation path
- DSignTool.exe (PID: 436)
- DSignTool.exe (PID: 6764)
Reads security settings of Internet Explorer
- DSignTool.exe (PID: 436)
- DSignTool.exe (PID: 6764)
Reads Internet Explorer settings
- DSignTool.exe (PID: 436)
- DSignTool.exe (PID: 6764)
INFO
Manual execution by a user
- DSignTool.exe (PID: 436)
- regedit.exe (PID: 4232)
- CSignTool.exe (PID: 2188)
- regedit.exe (PID: 3556)
- DSignTool.exe (PID: 6764)
Checks supported languages
- DSignTool.exe (PID: 436)
- CSignTool.exe (PID: 2188)
- ielowutil.exe (PID: 6868)
- DSignTool.exe (PID: 6764)
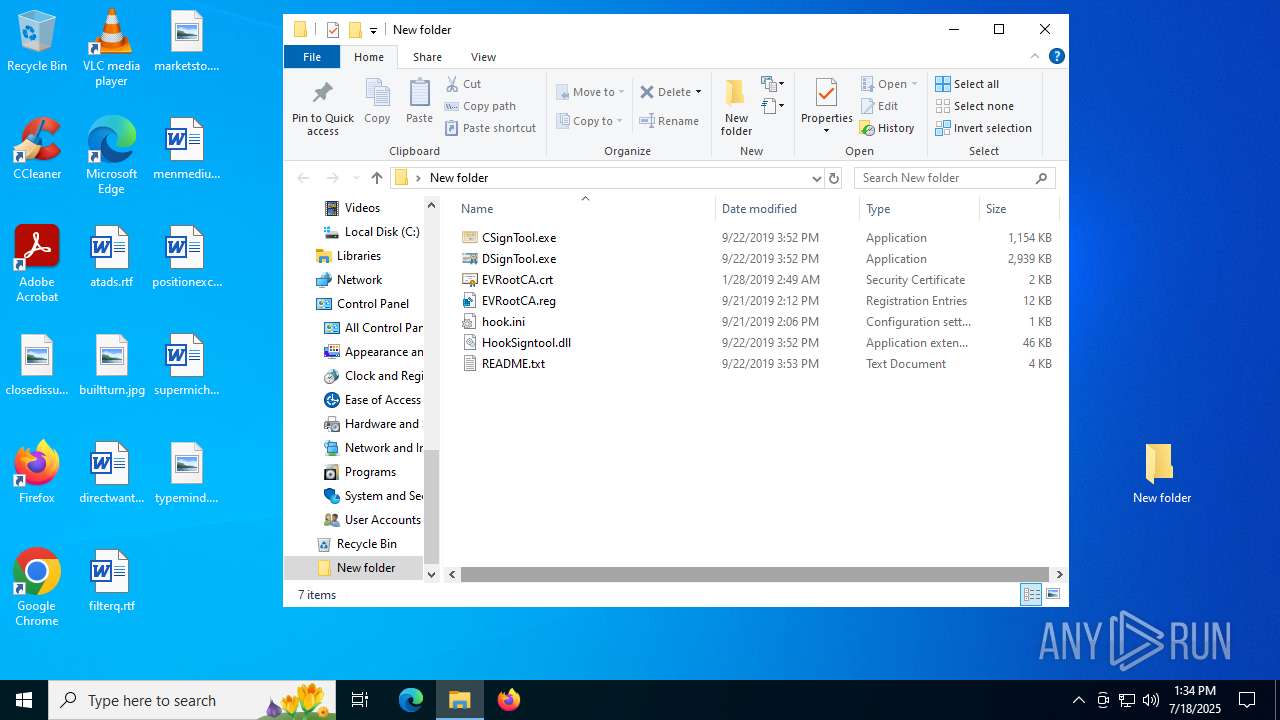
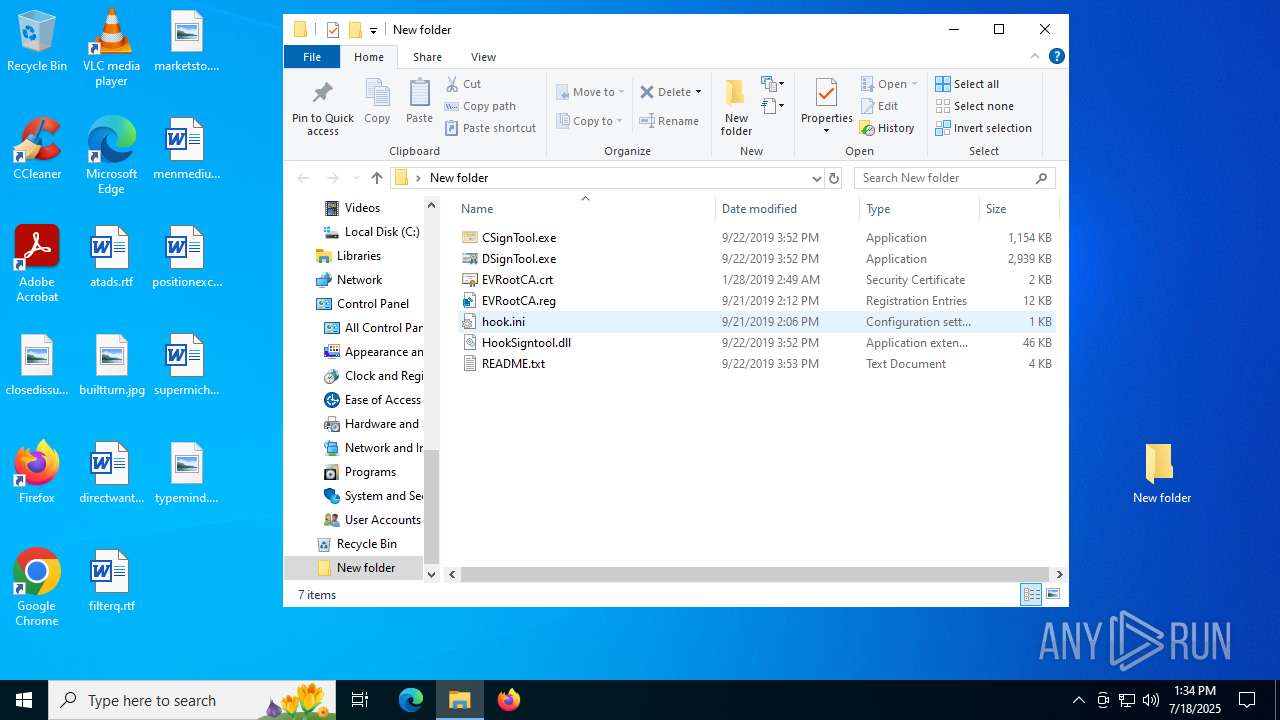
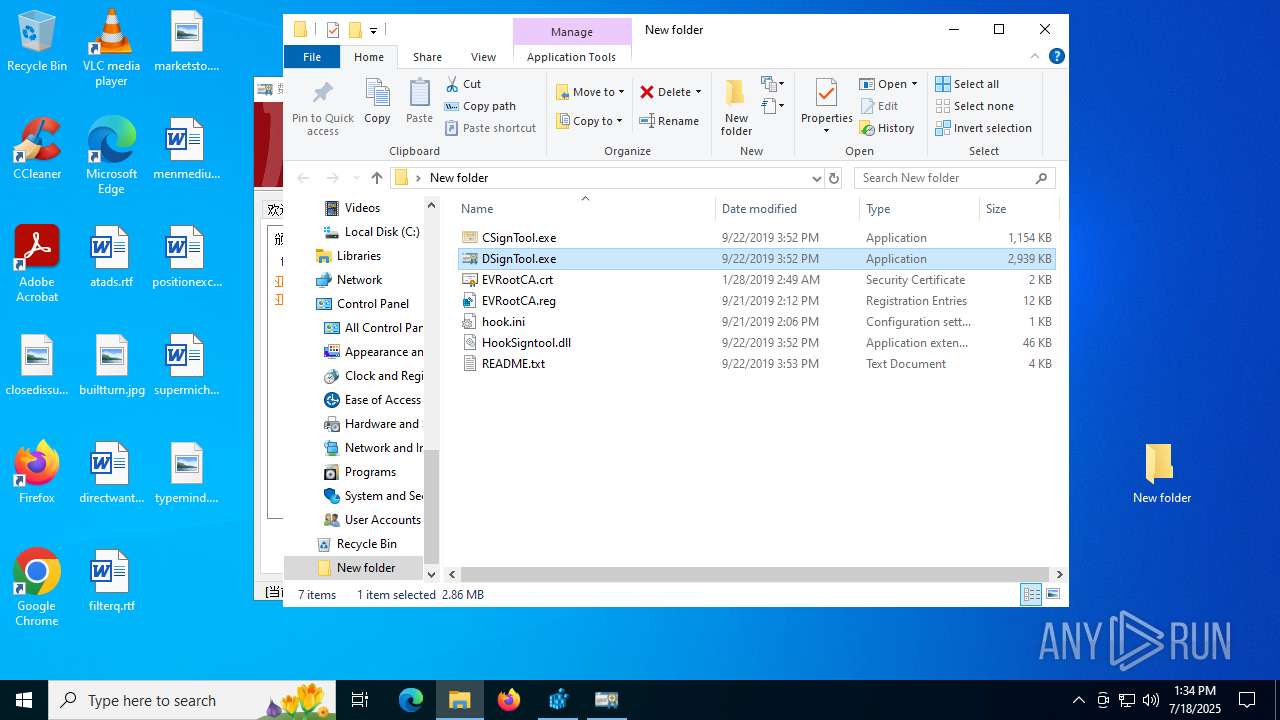
Executable content was dropped or overwritten
- WinRAR.exe (PID: 3148)
The sample compiled with english language support
- WinRAR.exe (PID: 3148)
Creates files or folders in the user directory
- DSignTool.exe (PID: 436)
- DSignTool.exe (PID: 6764)
- CSignTool.exe (PID: 2188)
Reads the computer name
- DSignTool.exe (PID: 436)
- ielowutil.exe (PID: 6868)
- DSignTool.exe (PID: 6764)
Checks proxy server information
- DSignTool.exe (PID: 436)
- DSignTool.exe (PID: 6764)
Reads the machine GUID from the registry
- DSignTool.exe (PID: 436)
- CSignTool.exe (PID: 2188)
- DSignTool.exe (PID: 6764)
Compiled with Borland Delphi (YARA)
- DSignTool.exe (PID: 436)
- DSignTool.exe (PID: 6764)
Process checks whether UAC notifications are on
- DSignTool.exe (PID: 436)
Reads the software policy settings
- DSignTool.exe (PID: 436)
- DSignTool.exe (PID: 6764)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:09:22 08:52:22 |
| ZipCRC: | 0x84fdf8a8 |
| ZipCompressedSize: | 444607 |
| ZipUncompressedSize: | 1180728 |
| ZipFileName: | CSignTool.exe |
Total processes
147
Monitored processes
12
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files (x86)\Internet Explorer\IEXPLORE.EXE" SCODEF:6392 CREDAT:9474 /prefetch:2 | C:\Program Files (x86)\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
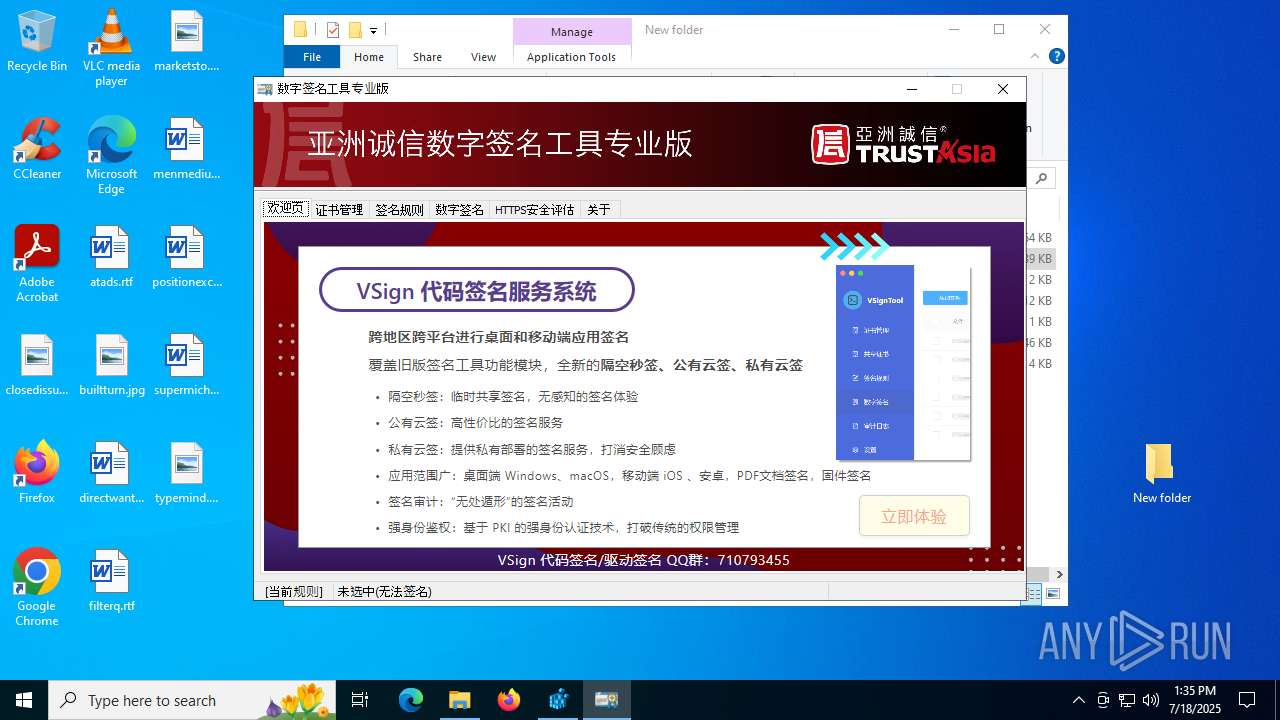
| 436 | "C:\Users\admin\Desktop\New folder\DSignTool.exe" | C:\Users\admin\Desktop\New folder\DSignTool.exe | explorer.exe | ||||||||||||
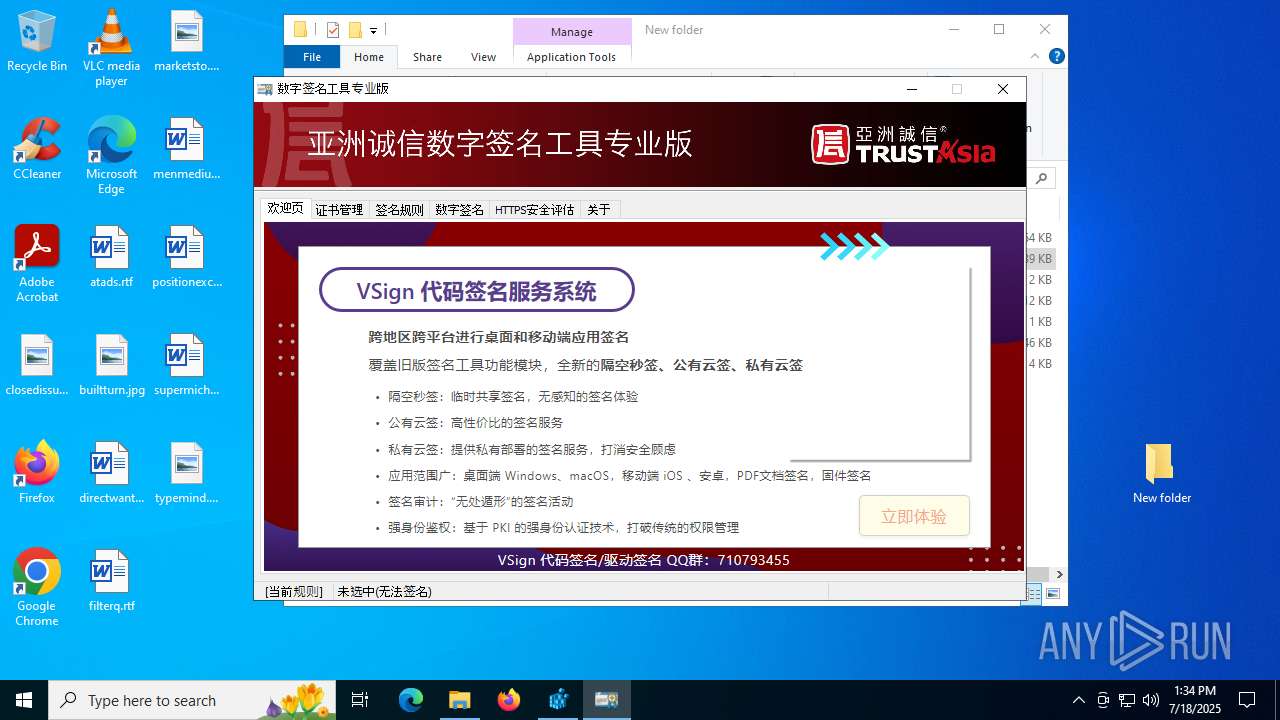
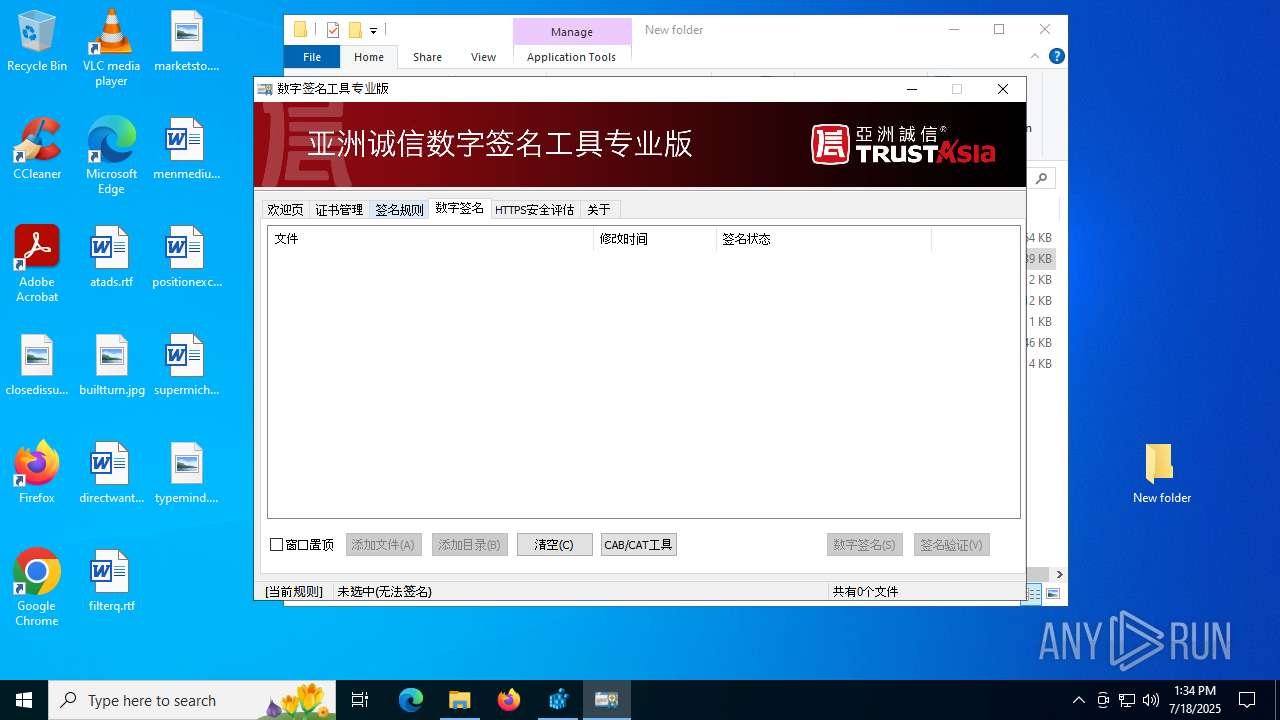
User: admin Company: 亚数信息科技(上海)有限公司 Integrity Level: MEDIUM Description: 数字签名工具 Exit code: 0 Version: 3.1.0.27 Modules
| |||||||||||||||
| 1180 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | CSignTool.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2188 | "C:\Users\admin\Desktop\New folder\CSignTool.exe" | C:\Users\admin\Desktop\New folder\CSignTool.exe | — | explorer.exe | |||||||||||
User: admin Company: 亚数信息科技(上海)有限公司 Integrity Level: MEDIUM Description: 数字签名工具(命令行) Exit code: 0 Version: 3.2.0.19 Modules
| |||||||||||||||
| 3148 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\DSigntool_[unknowncheats.me]_.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 3460 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3556 | "regedit.exe" "C:\Users\admin\Desktop\New folder\EVRootCA.reg" | C:\Windows\regedit.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Editor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3840 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4232 | "regedit.exe" "C:\Users\admin\Desktop\New folder\EVRootCA.reg" | C:\Windows\regedit.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Editor Exit code: 3221226540 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6392 | "C:\Program Files\Internet Explorer\IEXPLORE.EXE" -Embedding | C:\Program Files\Internet Explorer\iexplore.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
27 122
Read events
26 969
Write events
125
Delete events
28
Modification events
| (PID) Process: | (3148) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3148) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3148) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (3148) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (3148) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (3148) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\DSigntool_[unknowncheats.me]_.zip | |||
| (PID) Process: | (3148) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3148) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3148) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3148) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
3
Suspicious files
14
Text files
10
Unknown types
16
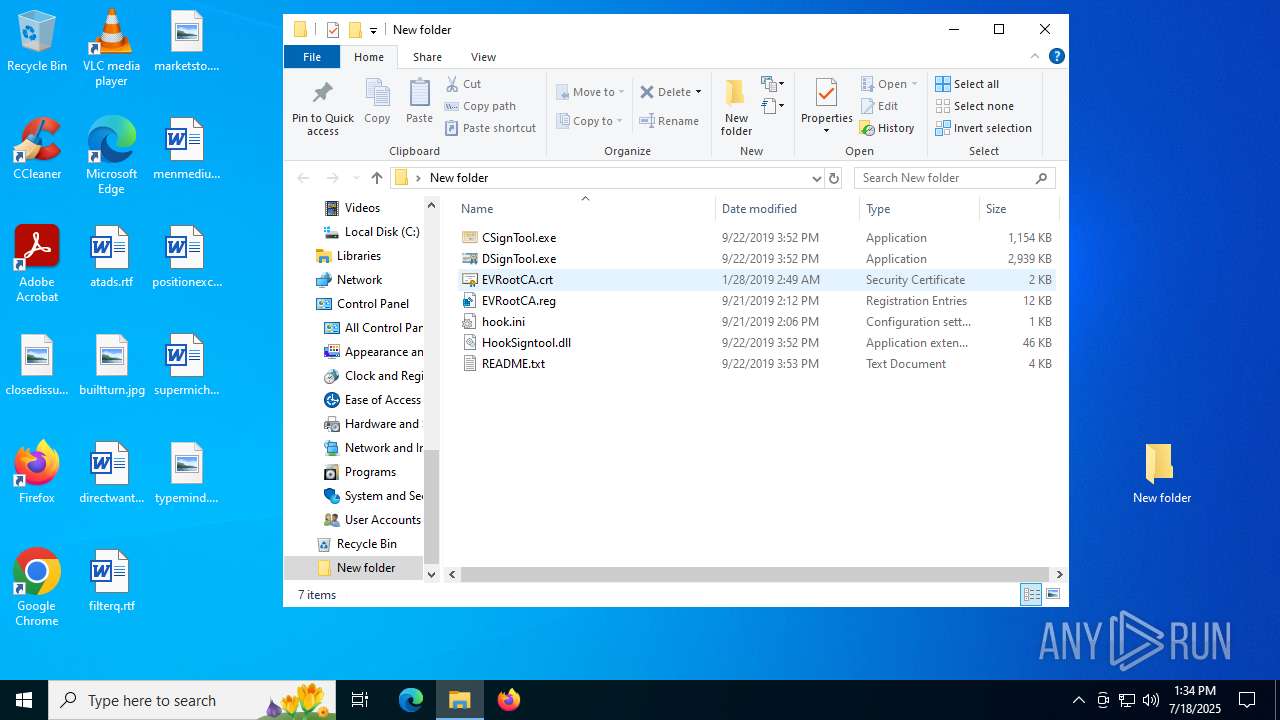
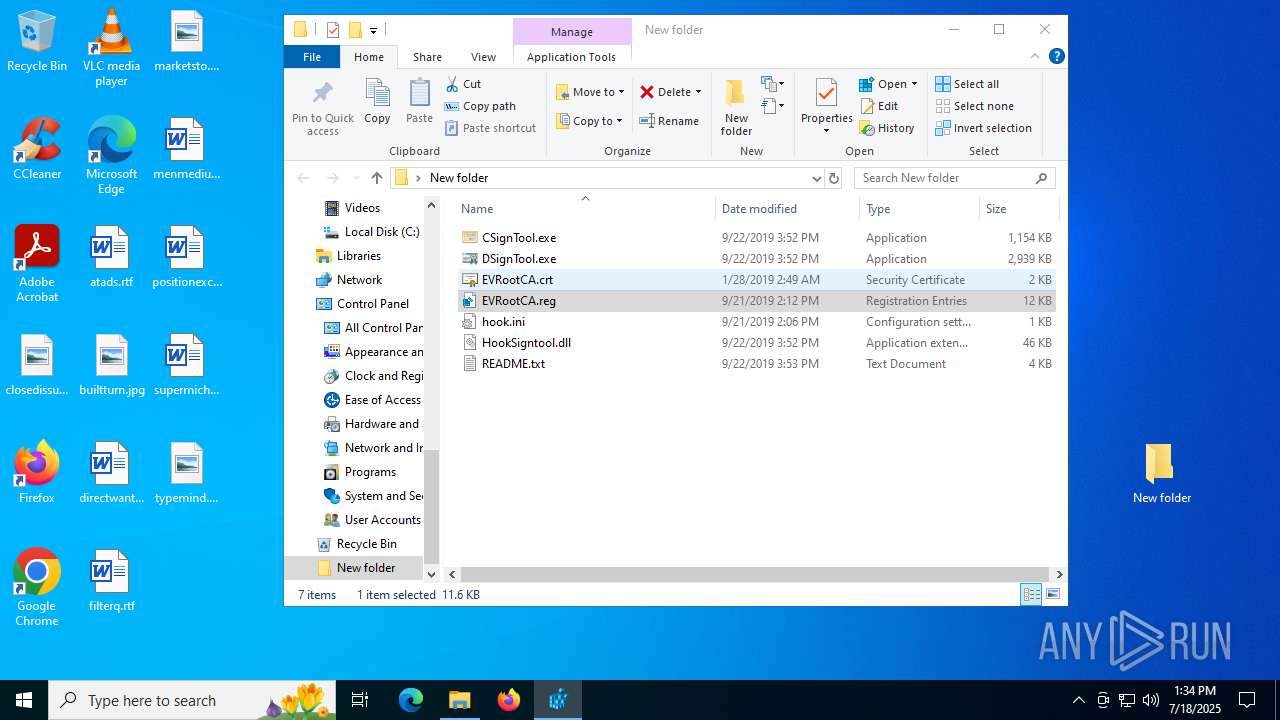
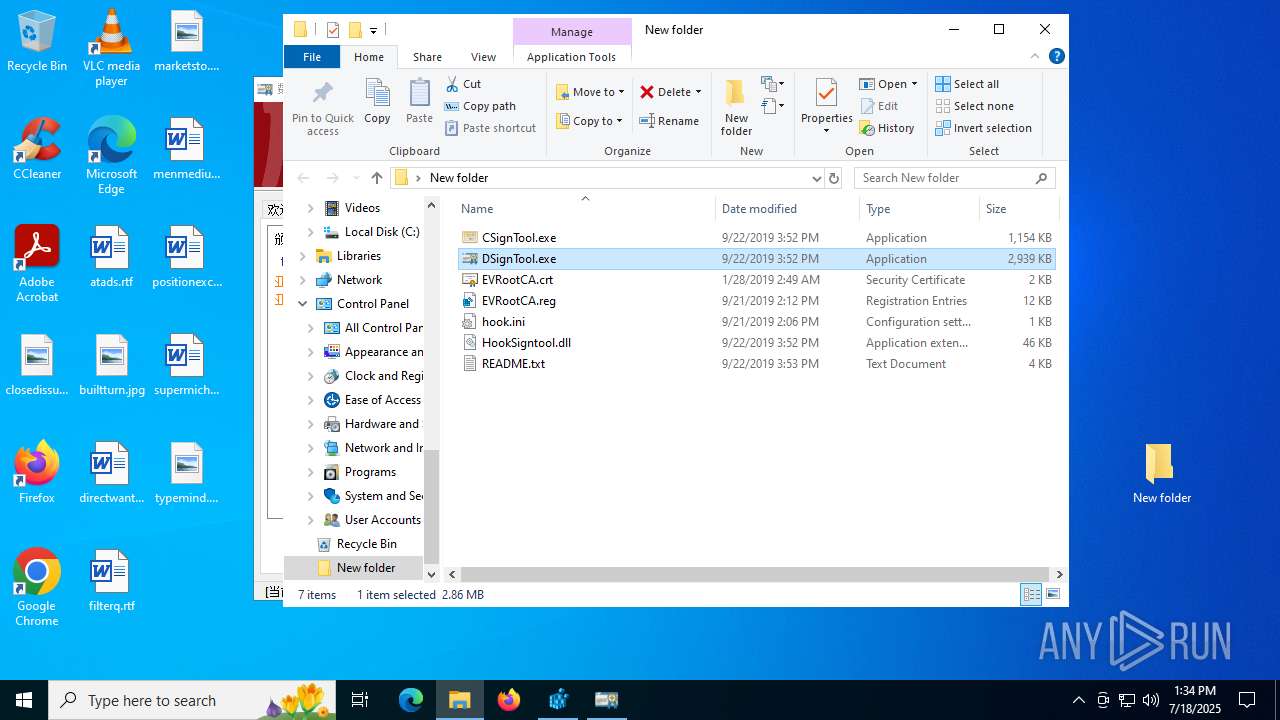
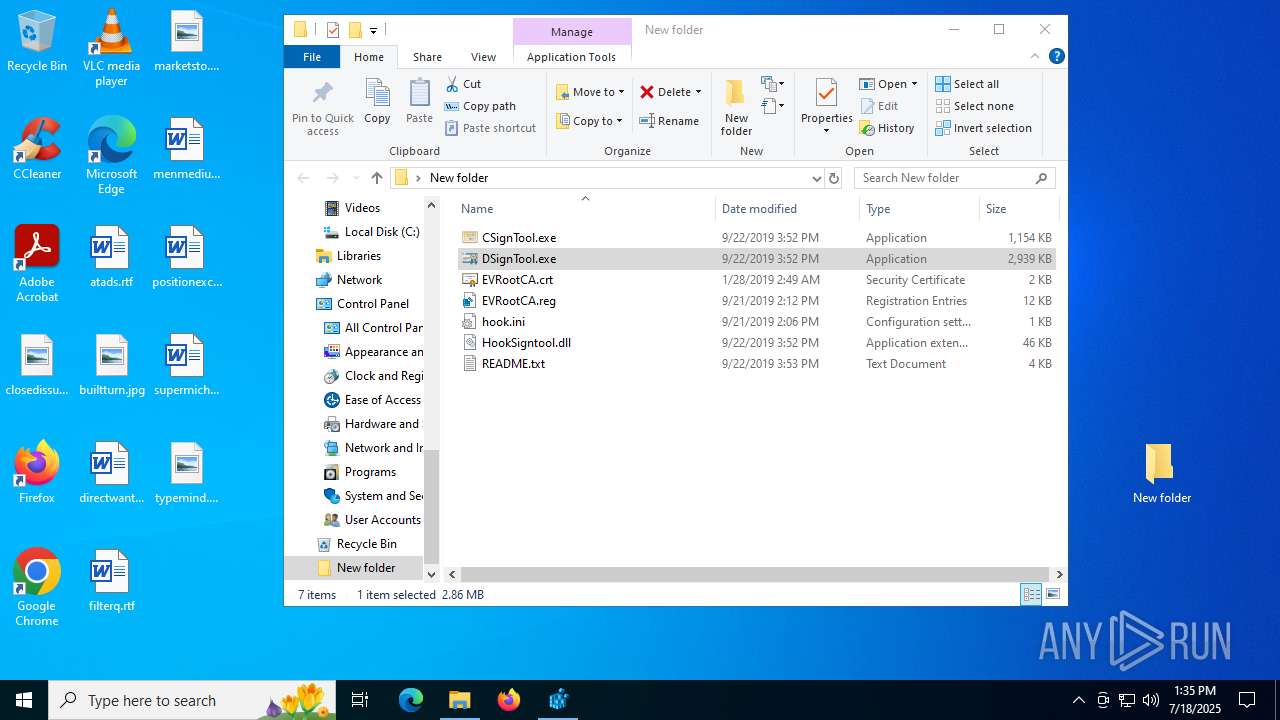
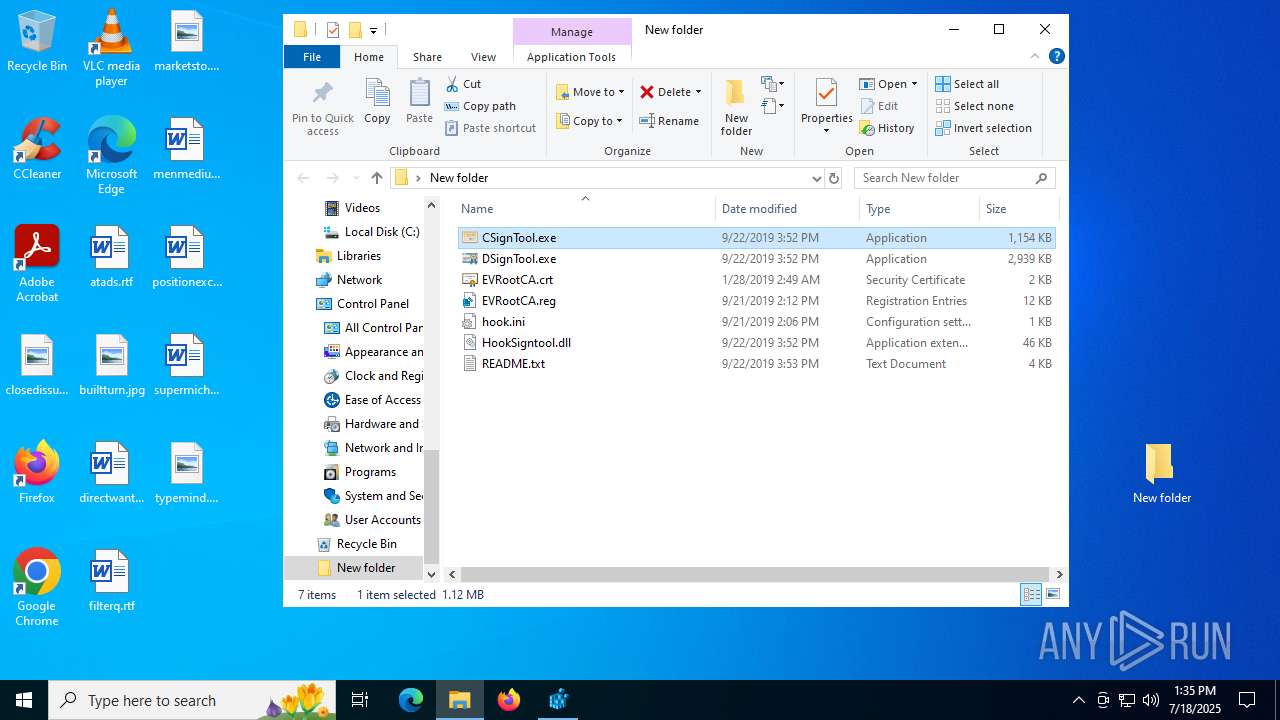
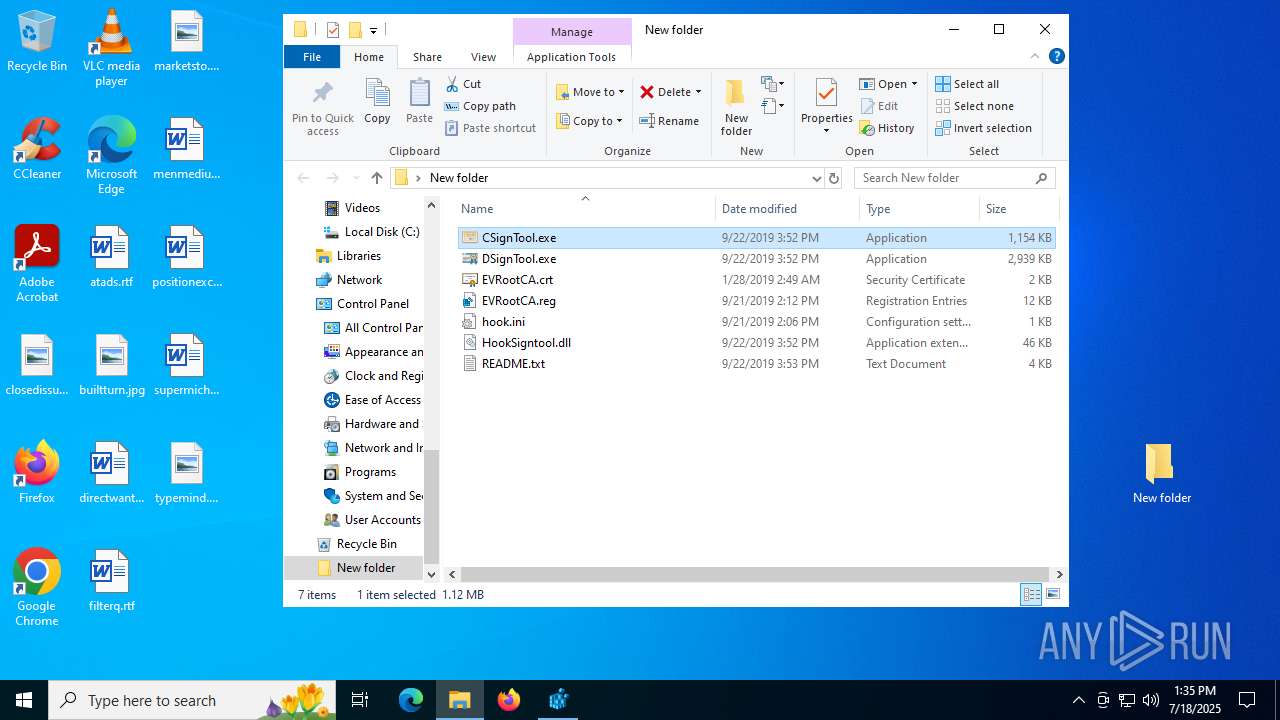
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 436 | DSignTool.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\5F263F63198568CED7739E17893D8775_CEF58D2319454483EFE1D7728290B1D7 | der | |
MD5:342FD9E406623BBC74882768D809F42C | SHA256:5F92D8D35235D98BC6ACA6BCC91824AFE3B97B600070B4BDD96E7A9B8F8A5E08 | |||
| 3148 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3148.46092\DSignTool.exe | executable | |
MD5:D31494C15F6D04F7BBA83BF76E64C849 | SHA256:0268BC99876354A91907D92B3AC0A2FFE16061D25DE12FE7589ACEF89873573D | |||
| 3148 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3148.46092\CSignTool.exe | executable | |
MD5:F933B4844D3CDC1C861F248DA8D48BA9 | SHA256:5DD5FE56BC2799300A9BF1AA6F01D26B144FF3844D121D5A51BE3696D63E81EB | |||
| 3148 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3148.46092\EVRootCA.crt | der | |
MD5:DC911E8DA3A186BB4D52EEC0E57B5155 | SHA256:1F0A7C723D98E4209F6B8A2F7B718A69C6B7AFF56F5D53A1A7760D73B6492F75 | |||
| 436 | DSignTool.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\E4DJRUXW\mini[1].htm | html | |
MD5:9856C5903A0BC451781A0A862F2CBB30 | SHA256:C67F26FEA2C2C78DEB5F486ADA4BC7BF410BDF8692CD7E6ABA9FF3CEF7DBF499 | |||
| 3148 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3148.46092\hook.ini | binary | |
MD5:9944AC1C6B45DBF04367D78E91097181 | SHA256:6D6EB571C11D3D56A9689C1200B8612929CA391739B85CEE70DE931226AC34E5 | |||
| 3148 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3148.46092\HookSigntool.dll | executable | |
MD5:4D0A6273742DCBAA0C109E4458AEB3B0 | SHA256:5434A9A6D953284F697BFAA80844AEF1A4439ECEF8C520B5903008FEABD3CAF9 | |||
| 436 | DSignTool.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\INetCache\IE\KCV3KQBA\arrow[1].png | image | |
MD5:968B31A19FA5655AA23996D9293F1FBE | SHA256:C534E18AF9EFF4D75E646B10D9B0A2D33744E5E68D9CBC87B887F5F7A78105A9 | |||
| 436 | DSignTool.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\5F263F63198568CED7739E17893D8775_CEF58D2319454483EFE1D7728290B1D7 | binary | |
MD5:DC555A04CD06E8BC8527CA4C8DBBA8FB | SHA256:82165755259F42F9725E30BA624ED0F50DEB9C8DD5BBAADFB52022C5C6CA9B1E | |||
| 3148 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa3148.46092\EVRootCA.reg | text | |
MD5:65E27255EB9CEBB76F398D345ACF6386 | SHA256:C8FD81746CB7F33A0400A1F4FC36F6D0F7A3A96880E6BBEA872601A72F4819C8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
43
DNS requests
25
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3624 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | NL | binary | 420 b | whitelisted |
436 | DSignTool.exe | GET | 200 | 163.181.243.188:80 | http://ocsp.digicert.cn/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAObQq3tALhV7xhgOAd3mBY%3D | US | binary | 471 b | whitelisted |
3624 | SIHClient.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | NL | binary | 408 b | whitelisted |
436 | DSignTool.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/rootr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCDQHuXxad%2F5c1K2Rl1mo%3D | unknown | binary | 1.41 Kb | whitelisted |
3540 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
436 | DSignTool.exe | GET | 200 | 104.18.20.226:80 | http://ocsp.globalsign.com/gsrsaovsslca2018/ME0wSzBJMEcwRTAJBgUrDgMCGgUABBRrcGT%2BanRD3C1tW3nsrKeuXC7DPwQU%2BO9%2F8s14Z6jeb48kjYjxhwMCs%2BsCDFdTWXs%2FMR045mKVKQ%3D%3D | unknown | binary | 1.40 Kb | whitelisted |
436 | DSignTool.exe | GET | 200 | 151.101.2.133:80 | http://ocsp2.globalsign.com/rootr3/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBT1nGh%2FJBjWKnkPdZIzB1bqhelHBwQUj%2FBLf6guRSSuTVD6Y5qL3uLdG7wCDQHuXyId%2FGI71DM6hVc%3D | US | binary | 1.40 Kb | whitelisted |
2940 | svchost.exe | GET | 200 | 2.23.197.184:80 | http://x1.c.lencr.org/ | GB | binary | 734 b | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.241.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 814 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
504 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 51.104.136.2:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 2.16.241.12:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 95.101.149.131:80 | www.microsoft.com | Akamai International B.V. | NL | whitelisted |
3540 | svchost.exe | 20.190.160.67:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3540 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
dsigntool.trustasia.com |
| whitelisted |
ocsp.digicert.cn |
| whitelisted |