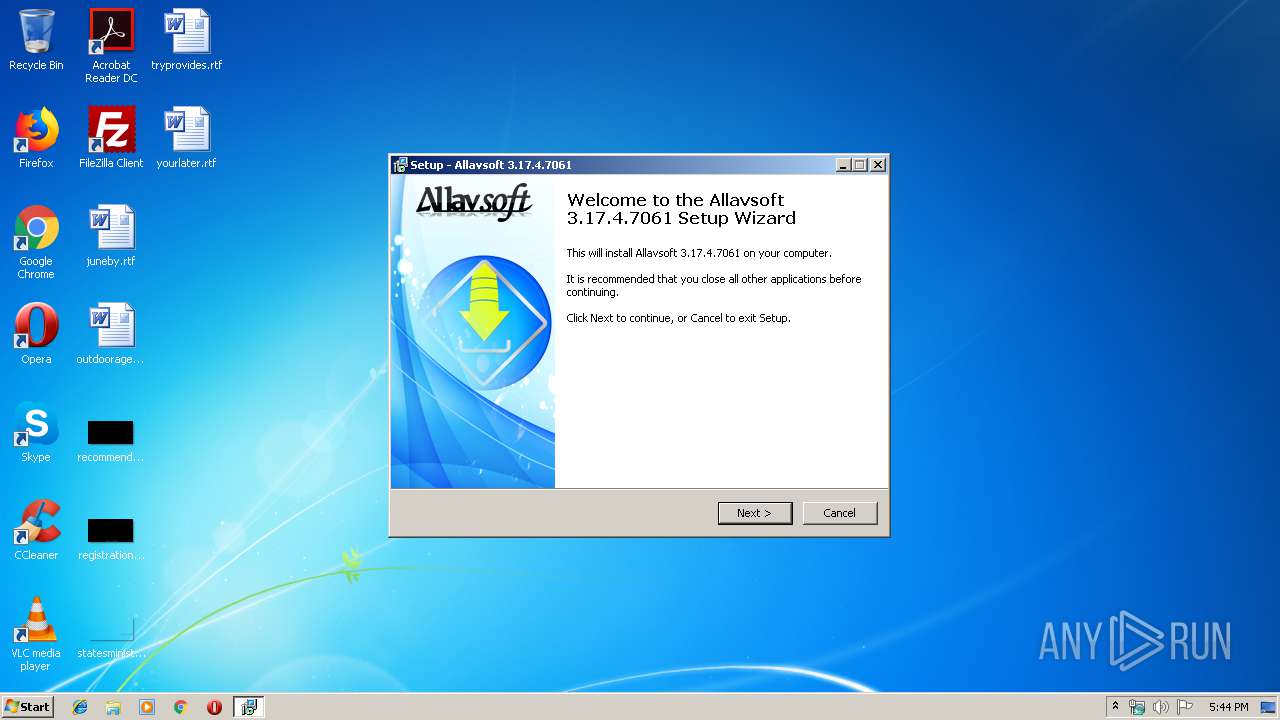
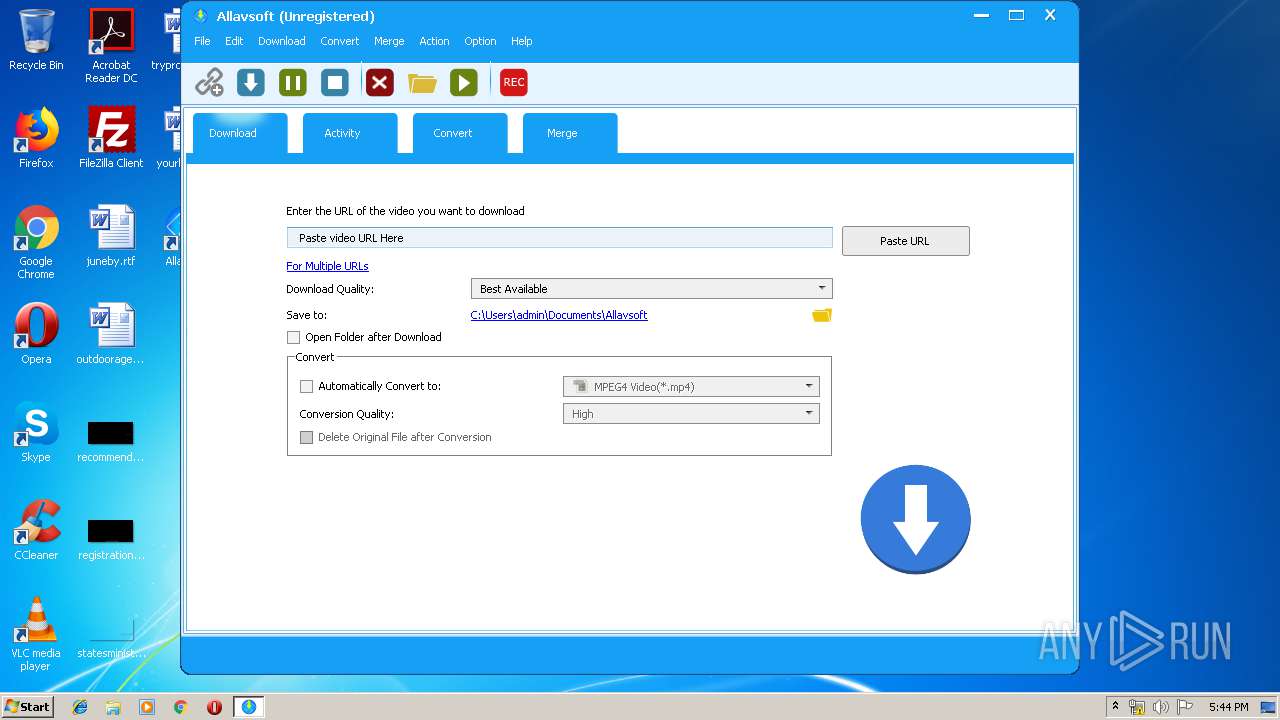
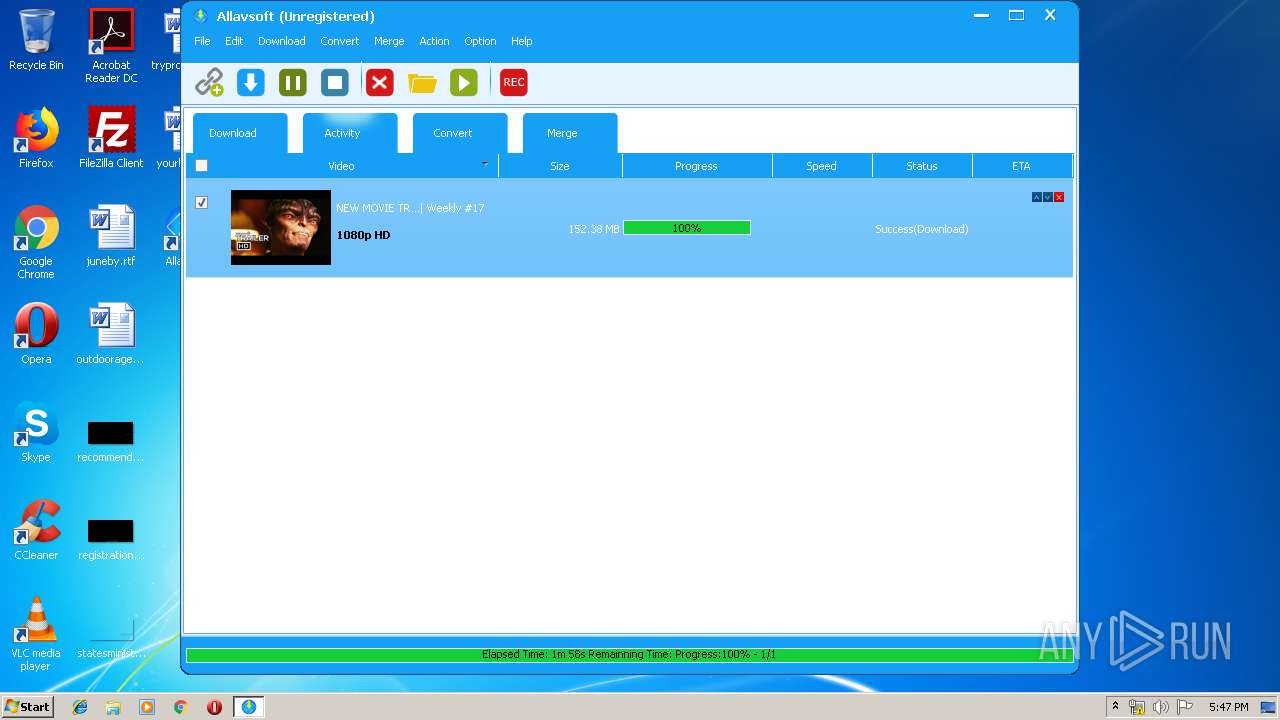
| download: | allavsoft.exe |
| Full analysis: | https://app.any.run/tasks/84c2e616-ea24-4979-b8b2-10052eefec1e |
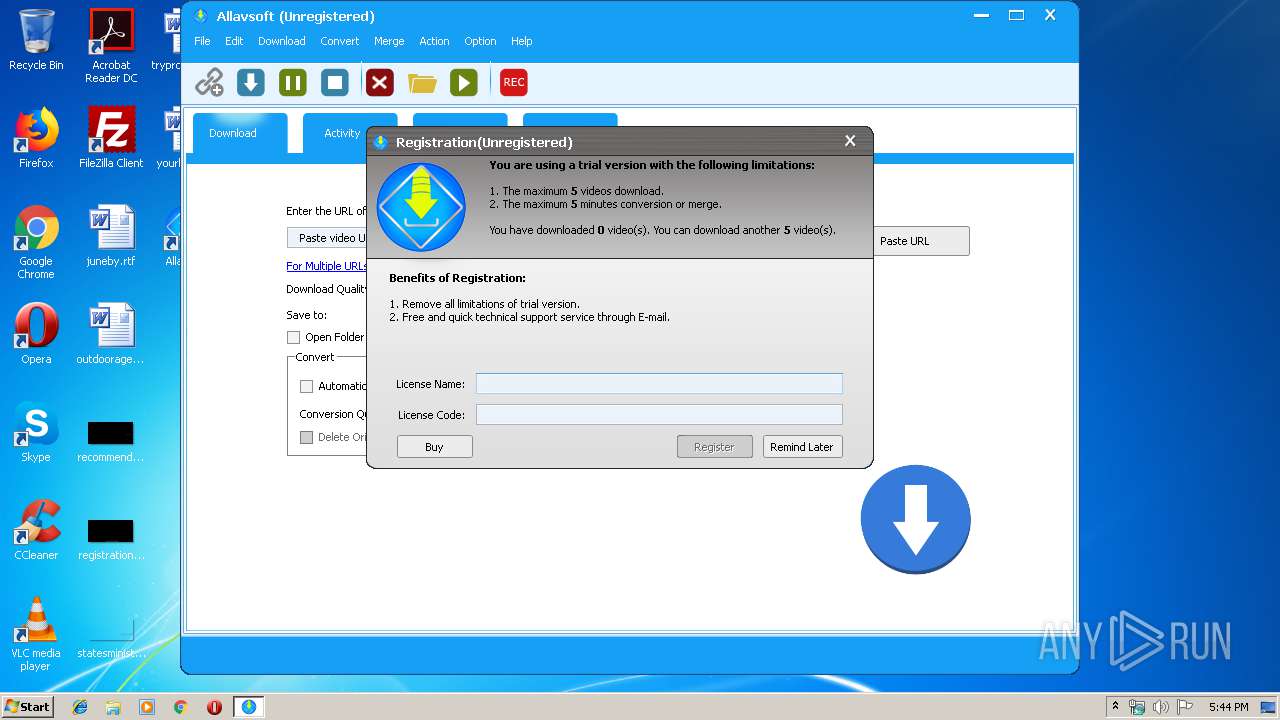
| Verdict: | Malicious activity |
| Analysis date: | May 06, 2019, 16:43:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 14363A6B62F2F1F1EC0298EC4ED82CB6 |
| SHA1: | CE59574F7839858AFBC4D8346337D7C9EB107BC8 |
| SHA256: | DC949D0B79A45367A1B11251B052F99253BBBD3E4805794D0A3A15D8B9981E05 |
| SSDEEP: | 786432:ml+Hnob+zh85IGZxig2PI1JkbeID5lzkeHSu:THnzh8OKEo1zIDfzN |
MALICIOUS
Registers / Runs the DLL via REGSVR32.EXE
- allavsoft.tmp (PID: 2132)
- videodownloader.exe (PID: 3192)
Application was dropped or rewritten from another process
- videodownloader.exe (PID: 3192)
- videodownloader.exe (PID: 2812)
- ffmpeg.exe (PID: 896)
Loads dropped or rewritten executable
- videodownloader.exe (PID: 3192)
- regsvr32.exe (PID: 3800)
- regsvr32.exe (PID: 3000)
- regsvr32.exe (PID: 3196)
- videodownloader.exe (PID: 2812)
- regsvr32.exe (PID: 2236)
- ffmpeg.exe (PID: 896)
SUSPICIOUS
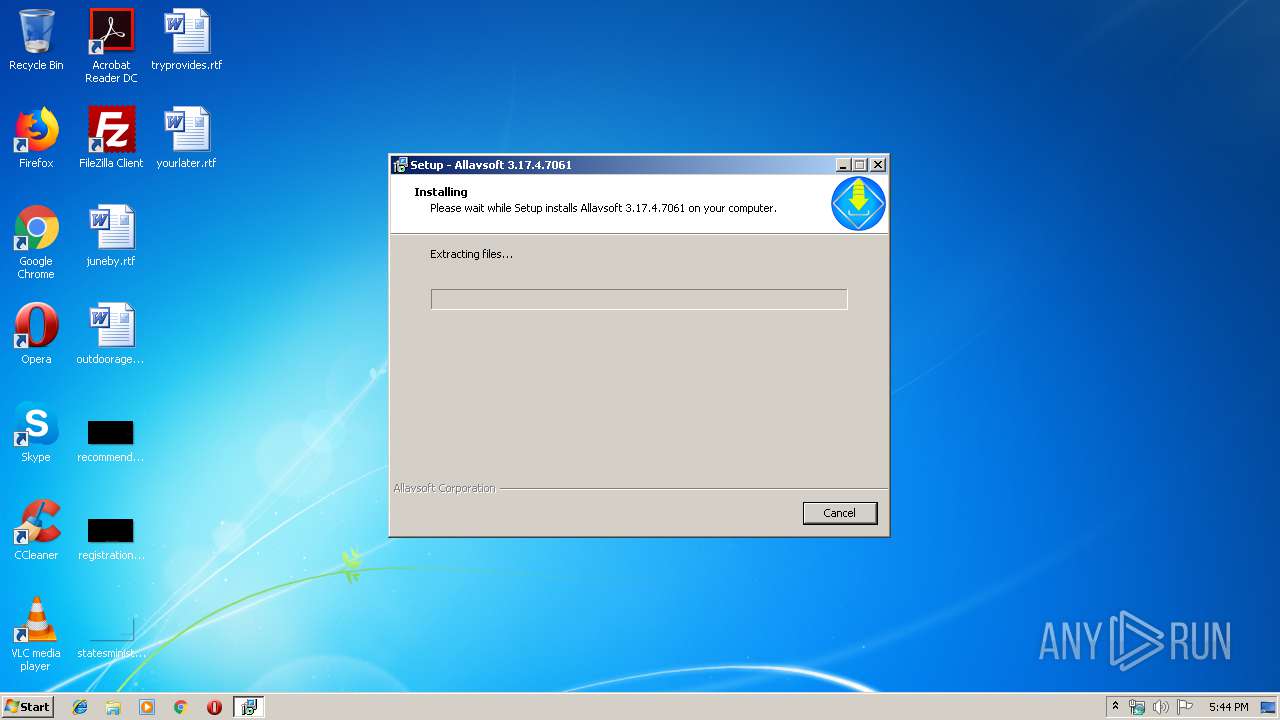
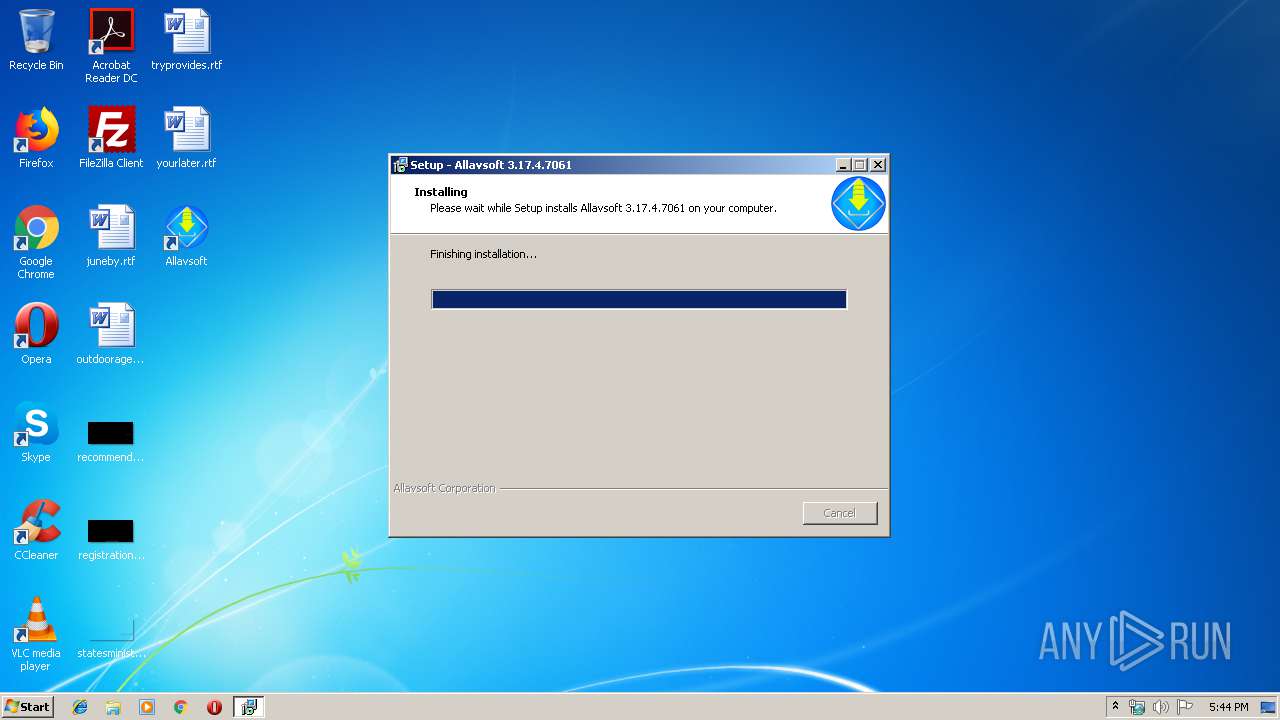
Executable content was dropped or overwritten
- allavsoft.exe (PID: 1092)
- allavsoft.exe (PID: 2856)
- allavsoft.tmp (PID: 2132)
Reads the Windows organization settings
- allavsoft.tmp (PID: 2132)
Reads Windows owner or organization settings
- allavsoft.tmp (PID: 2132)
Creates files in the user directory
- allavsoft.tmp (PID: 2132)
- videodownloader.exe (PID: 2812)
- vlc.exe (PID: 2832)
Creates COM task schedule object
- regsvr32.exe (PID: 3196)
- regsvr32.exe (PID: 2236)
- regsvr32.exe (PID: 3800)
- regsvr32.exe (PID: 3000)
Modifies files in Chrome extension folder
- chrome.exe (PID: 352)
INFO
Application was dropped or rewritten from another process
- allavsoft.tmp (PID: 2756)
- allavsoft.tmp (PID: 2132)
Loads dropped or rewritten executable
- allavsoft.tmp (PID: 2132)
Dropped object may contain Bitcoin addresses
- allavsoft.tmp (PID: 2132)
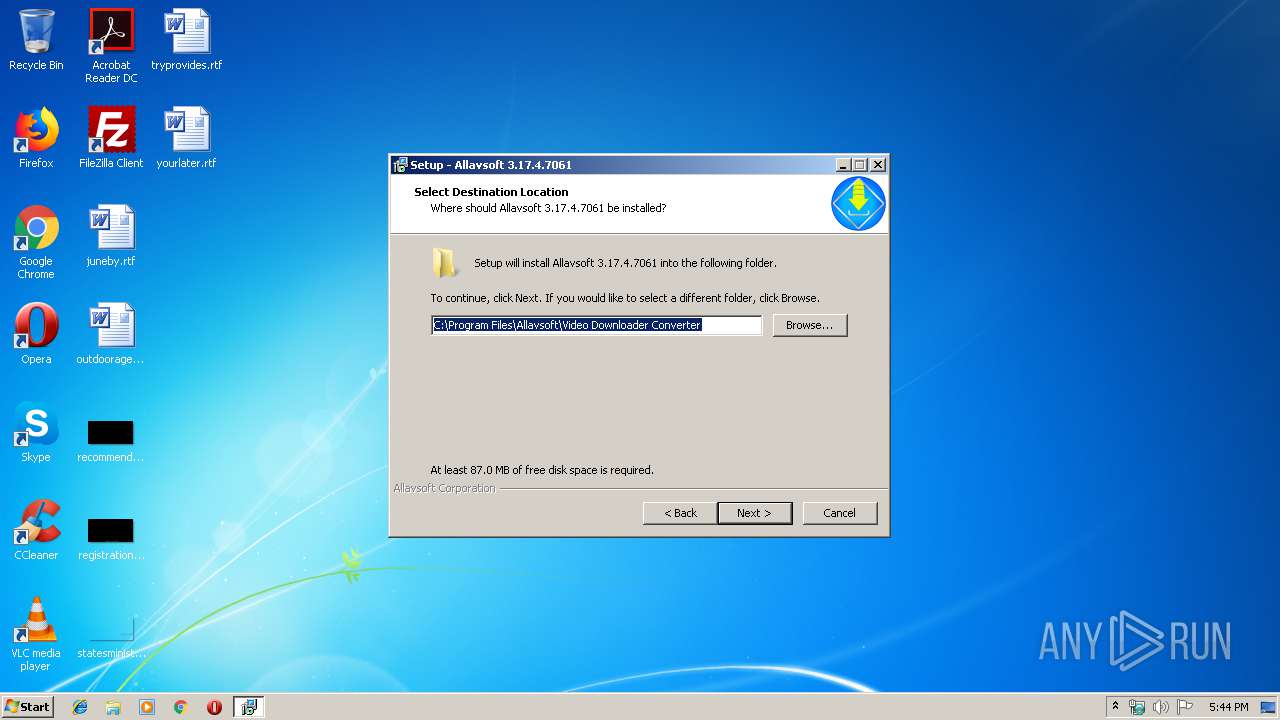
Creates files in the program directory
- allavsoft.tmp (PID: 2132)
Creates a software uninstall entry
- allavsoft.tmp (PID: 2132)
Application launched itself
- chrome.exe (PID: 352)
- chrome.exe (PID: 1356)
Reads settings of System Certificates
- chrome.exe (PID: 352)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Delphi generic (45.2) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (20.9) |
| .exe | | | Win32 Executable (generic) (14.3) |
| .exe | | | Win16/32 Executable Delphi generic (6.6) |
| .exe | | | Generic Win/DOS Executable (6.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:10:13 10:19:32+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 65024 |
| InitializedDataSize: | 53248 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x113bc |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
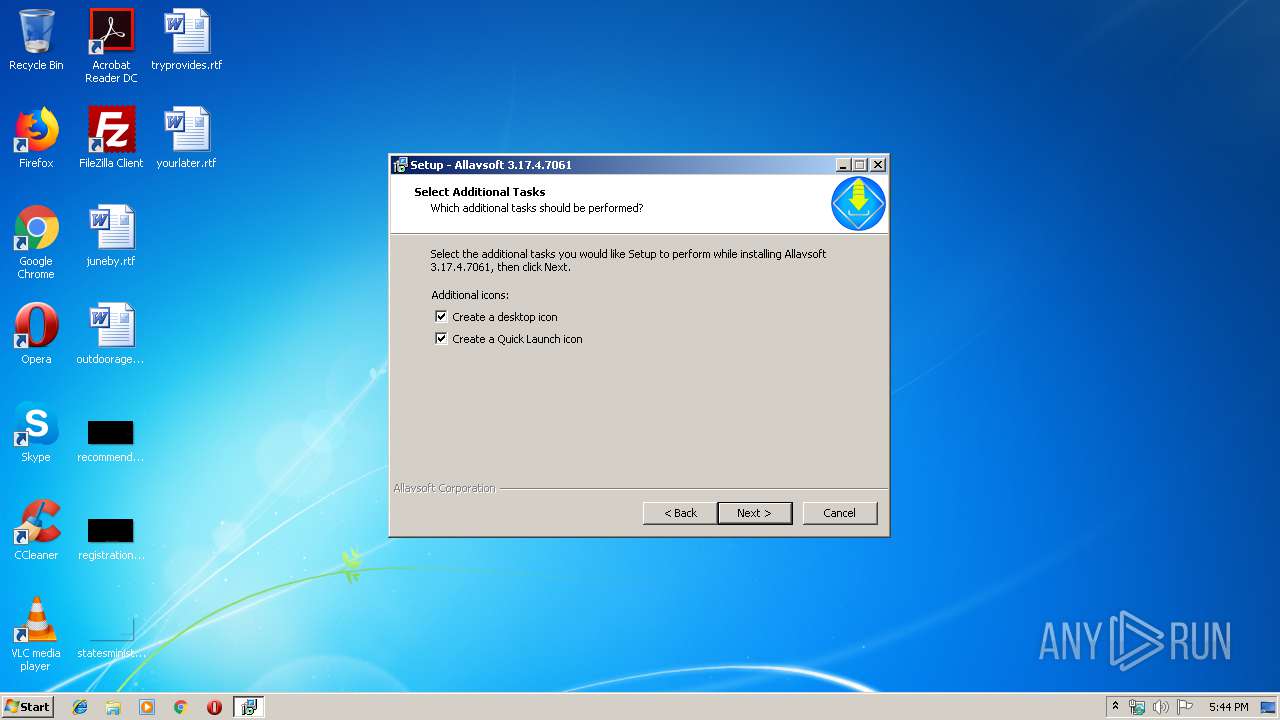
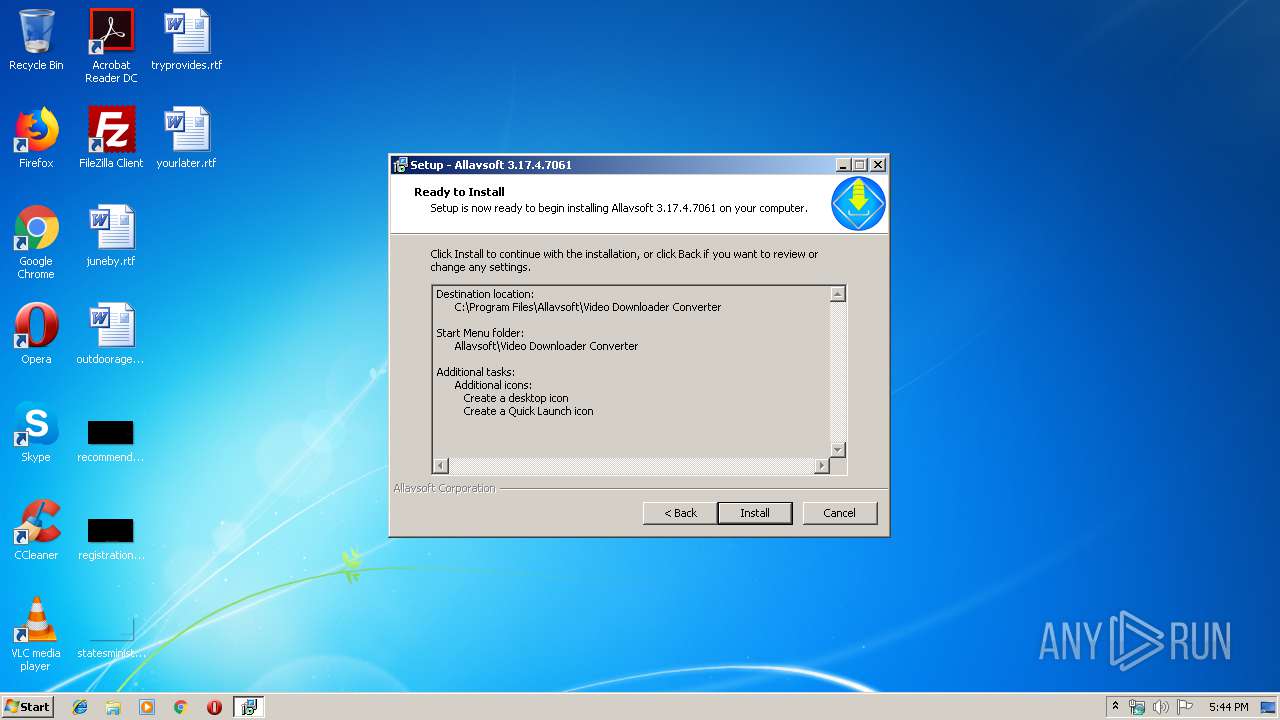
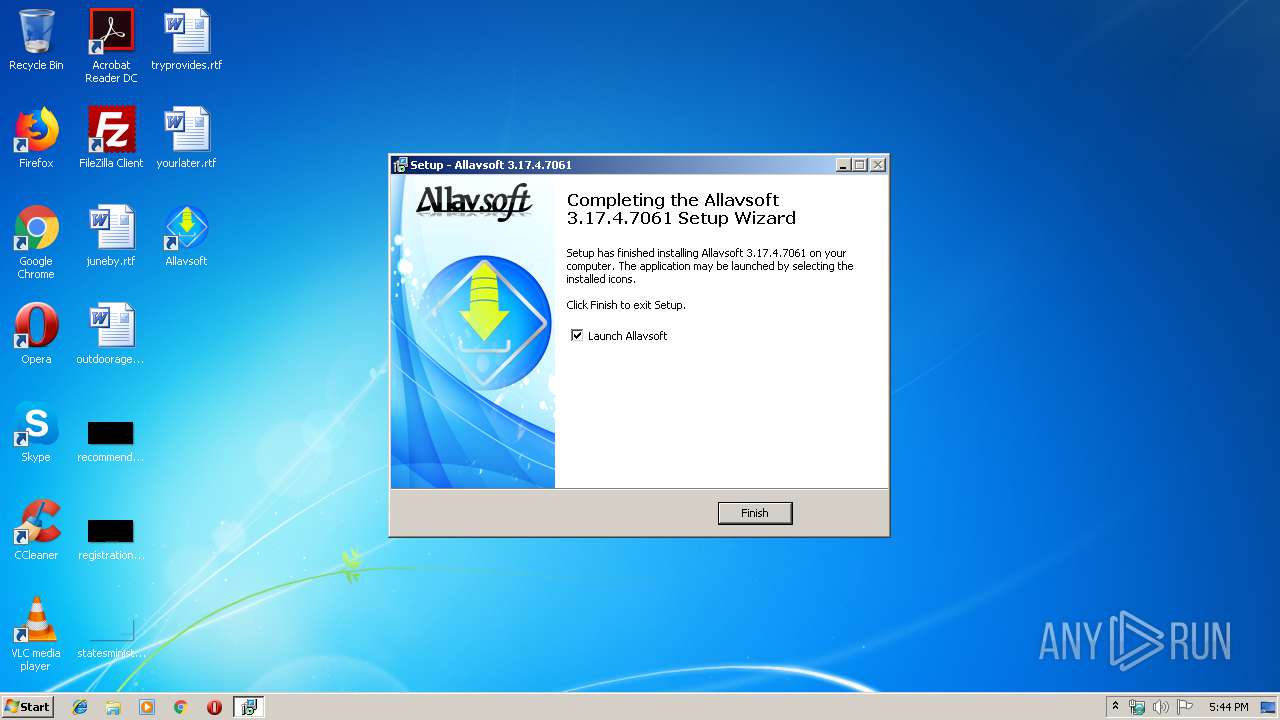
| FileVersionNumber: | 3.17.4.7061 |
| ProductVersionNumber: | 3.17.4.7061 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
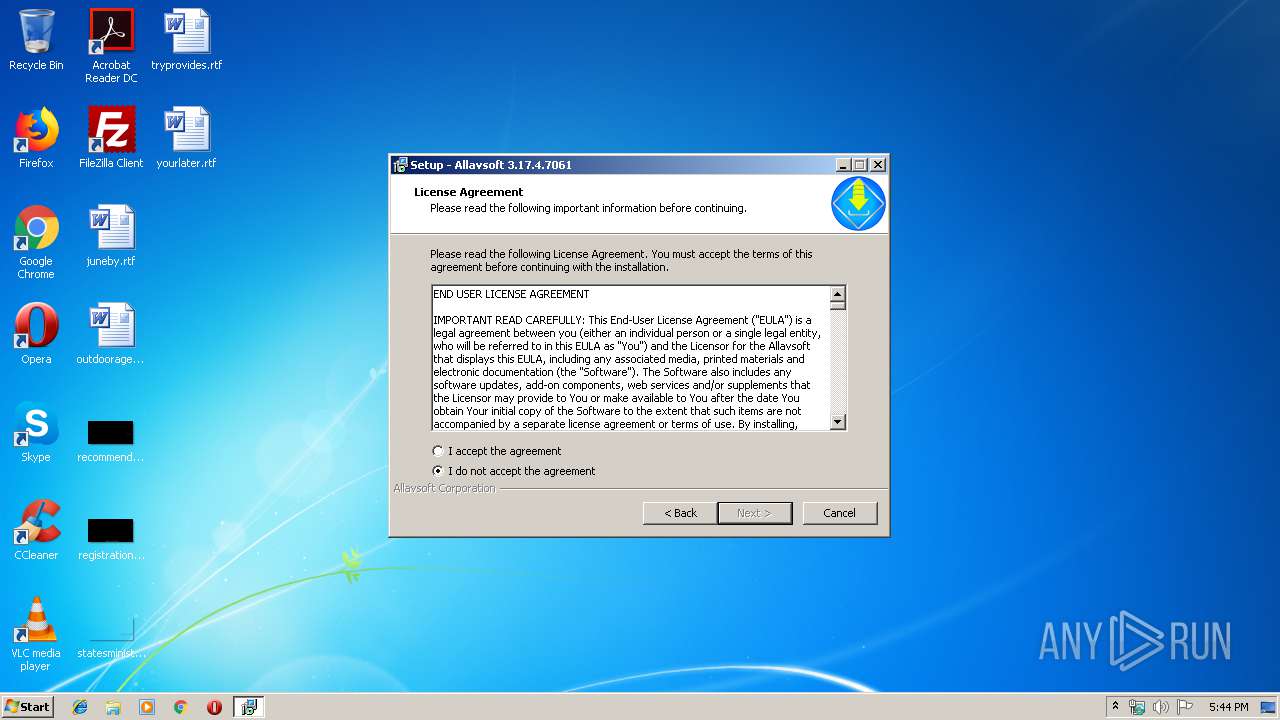
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Allavsoft Corporation |
| FileDescription: | Allavsoft 3.17.4.7061 Setup |
| FileVersion: | 3.17.4.7061 |
| LegalCopyright: | Copyright © 2019 Allavsoft Corporation, All Rights Reserved. |
| ProductName: | Allavsoft 3.17.4.7061 |
| ProductVersion: | 3.17.4.7061 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 13-Oct-2013 08:19:32 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Allavsoft Corporation |
| FileDescription: | Allavsoft 3.17.4.7061 Setup |
| FileVersion: | 3.17.4.7061 |
| LegalCopyright: | Copyright © 2019 Allavsoft Corporation, All Rights Reserved. |
| ProductName: | Allavsoft 3.17.4.7061 |
| ProductVersion: | 3.17.4.7061 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 13-Oct-2013 08:19:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0000F12C | 0x0000F200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.39148 |
.itext | 0x00011000 | 0x00000B44 | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.73207 |
.data | 0x00012000 | 0x00000C88 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.24631 |
.bss | 0x00013000 | 0x000056B4 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x00019000 | 0x00000DD0 | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.97188 |
.tls | 0x0001A000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x0001B000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.204488 |
.rsrc | 0x0001C000 | 0x0000B200 | 0x0000B200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.13715 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.11919 | 1512 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4091 | 2.56031 | 104 | UNKNOWN | UNKNOWN | RT_STRING |
4092 | 3.25287 | 212 | UNKNOWN | UNKNOWN | RT_STRING |
4093 | 3.26919 | 164 | UNKNOWN | UNKNOWN | RT_STRING |
4094 | 3.33268 | 684 | UNKNOWN | UNKNOWN | RT_STRING |
4095 | 3.34579 | 844 | UNKNOWN | UNKNOWN | RT_STRING |
4096 | 3.28057 | 660 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
90
Monitored processes
48
Malicious processes
7
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
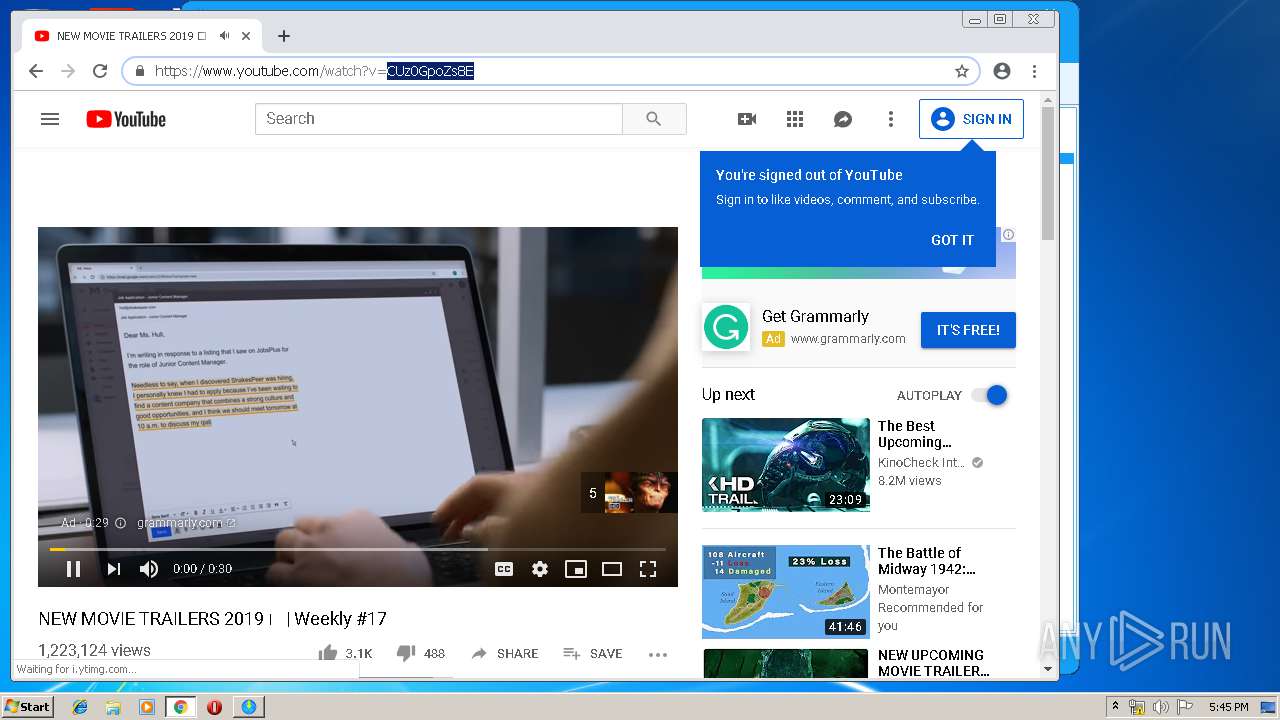
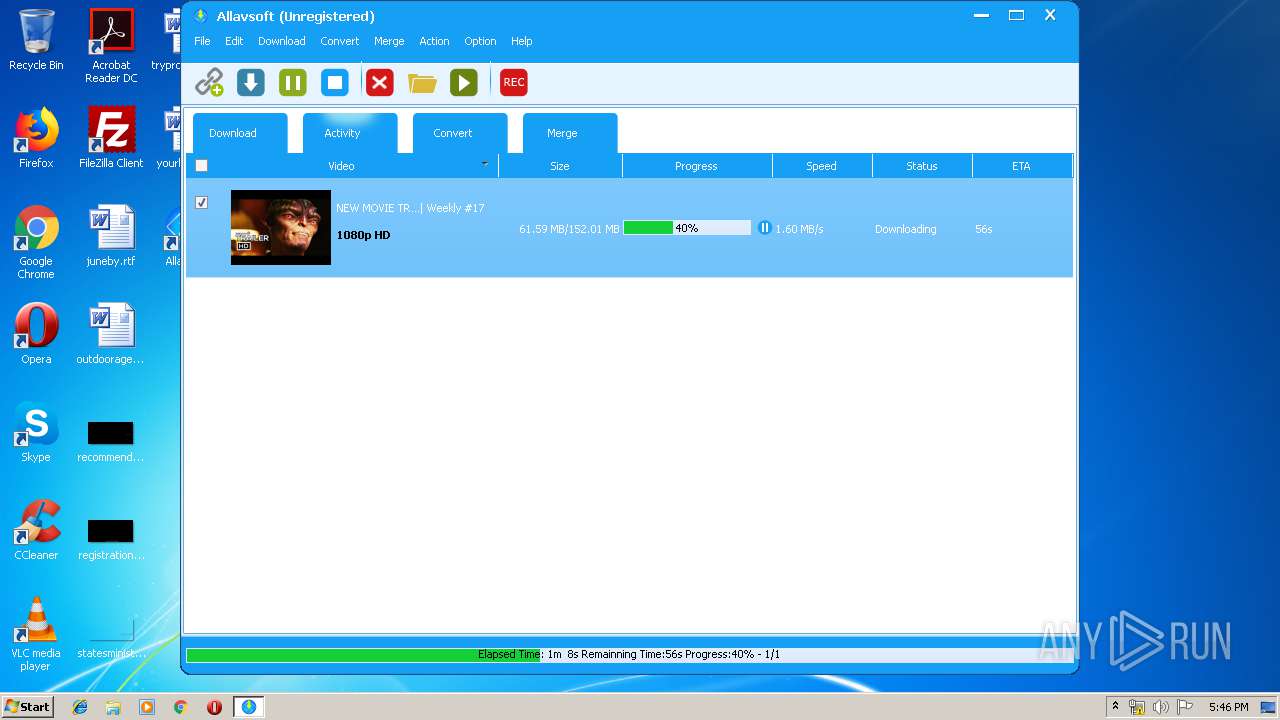
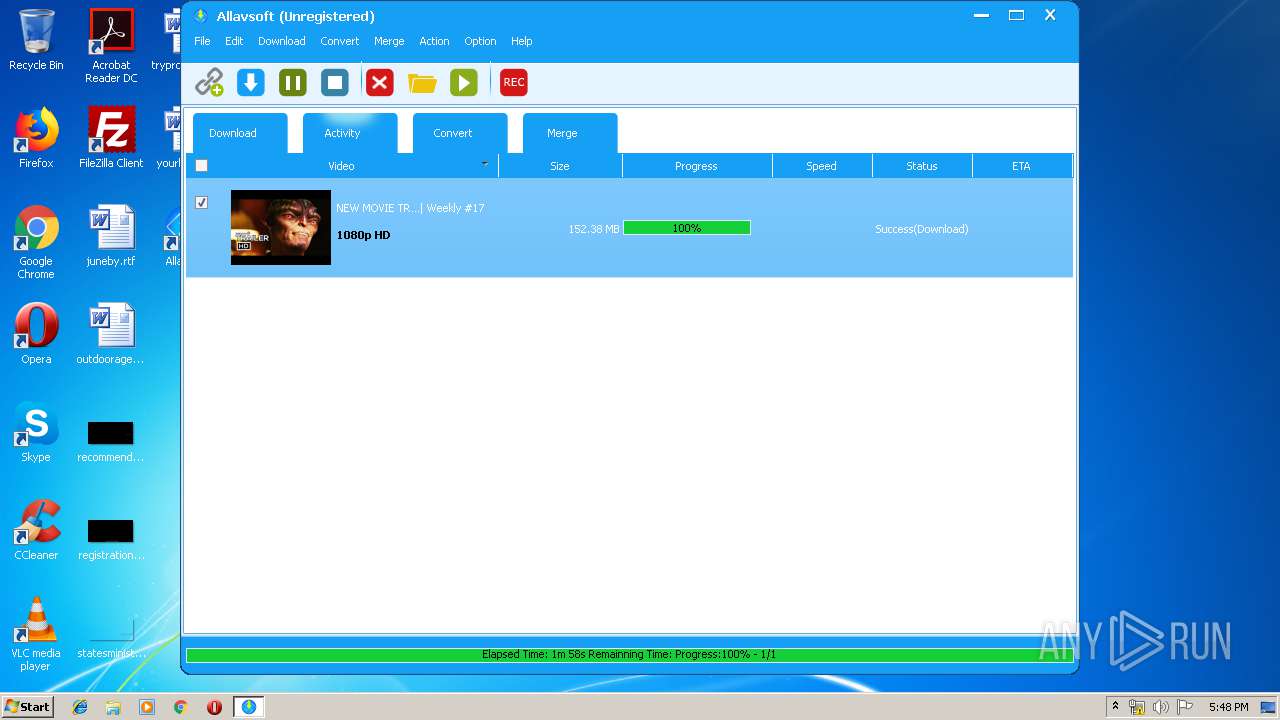
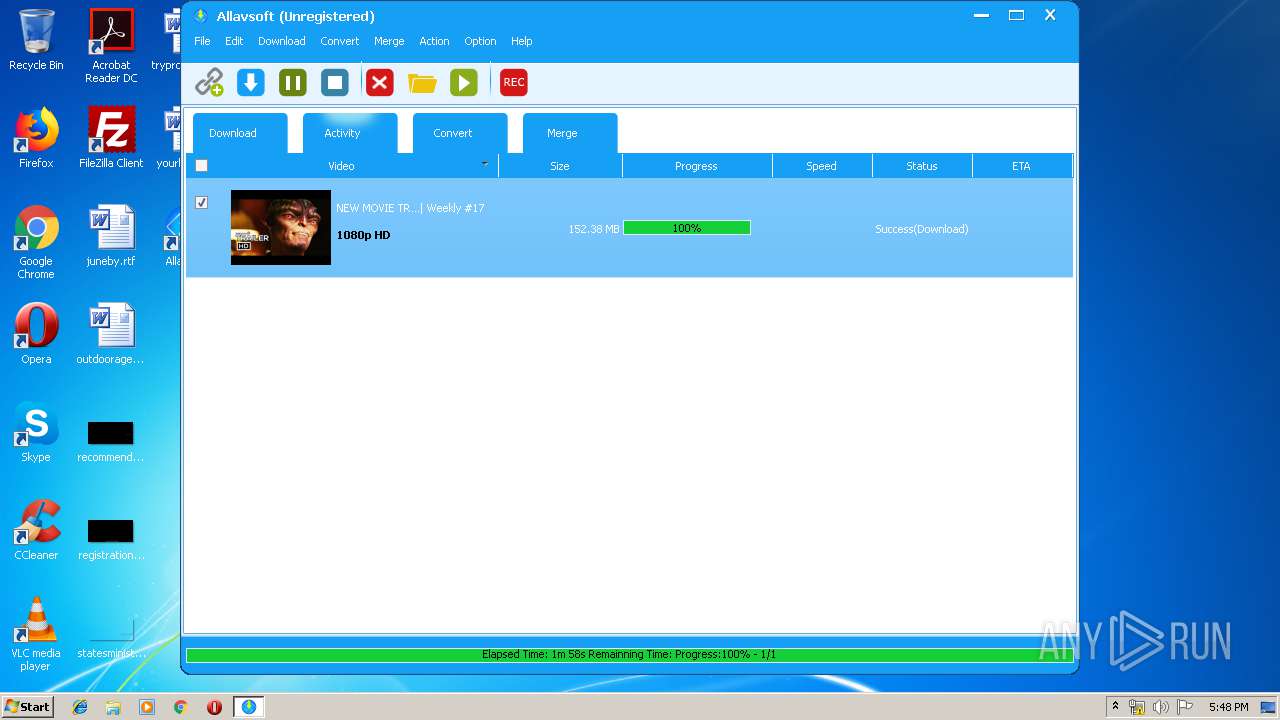
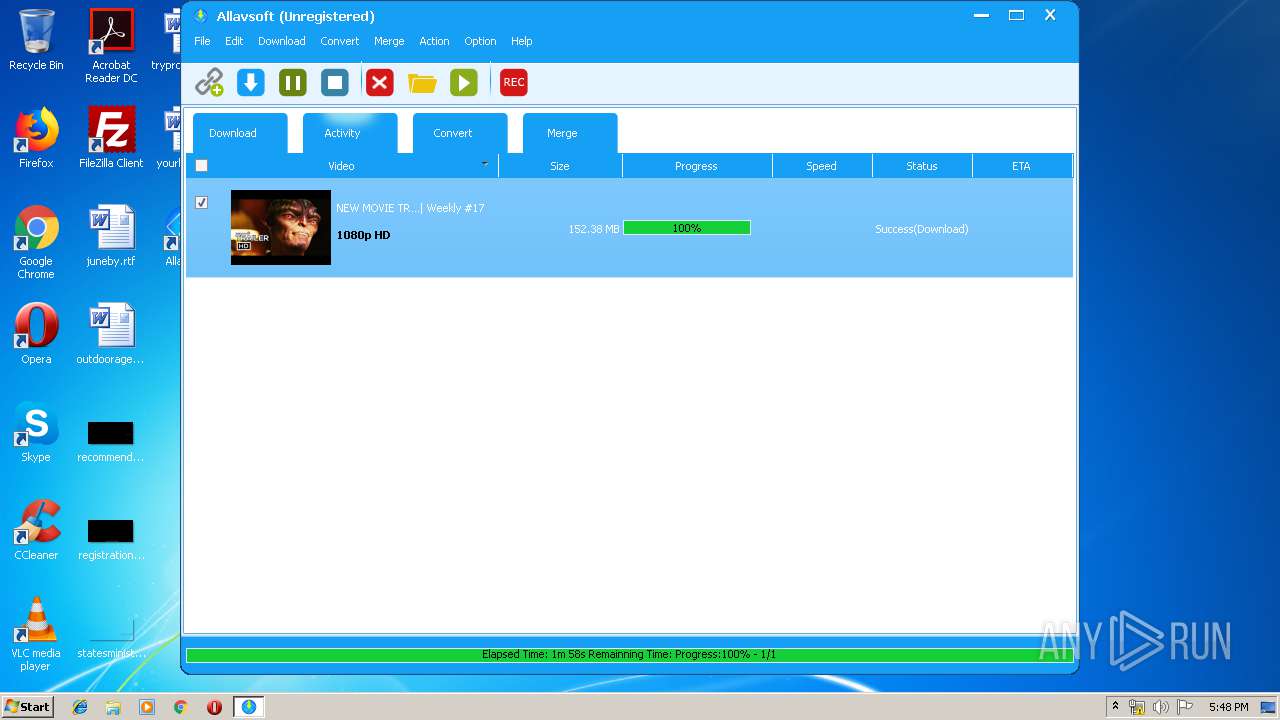
| 896 | "C:\Program Files\Allavsoft\Video Downloader Converter\ffmpeg.exe" -y -i "C:/Users/admin/Documents/Allavsoft/Download/Merge/DashVideo_CUz0GpoZs8ENEW MOVIE TRAILERS 2019 Weekly #17.mp4" -i "C:/Users/admin/Documents/Allavsoft/Download/Merge/DashAudio_CUz0GpoZs8ENEW MOVIE TRAILERS 2019 Weekly #17.m4a" -strict experimental -f mp4 -map 0:v:0 -map 1:a:0 -codec copy "C:/Users/admin/Documents/Allavsoft/Download/Merge/Merged_CUz0GpoZs8ENEW MOVIE TRAILERS 2019 Weekly #17.mp4" | C:\Program Files\Allavsoft\Video Downloader Converter\ffmpeg.exe | — | videodownloader.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=948,14643787614811948620,17698391149872733691,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=10838628765504744227 --mojo-platform-channel-handle=960 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1060 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,13383185714003246134,5713647549519968947,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=11488216315180700399 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11488216315180700399 --renderer-client-id=24 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=4648 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,13383185714003246134,5713647549519968947,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4663280911460573810 --mojo-platform-channel-handle=3944 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1092 | "C:\Users\admin\AppData\Local\Temp\allavsoft.exe" | C:\Users\admin\AppData\Local\Temp\allavsoft.exe | explorer.exe | ||||||||||||
User: admin Company: Allavsoft Corporation Integrity Level: MEDIUM Description: Allavsoft 3.17.4.7061 Setup Exit code: 0 Version: 3.17.4.7061 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=948,14643787614811948620,17698391149872733691,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=14315850592690666440 --mojo-platform-channel-handle=1524 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1664 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=952,13383185714003246134,5713647549519968947,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=13267787658448385158 --mojo-platform-channel-handle=4408 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1768 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=952,13383185714003246134,5713647549519968947,131072 --enable-features=PasswordImport --service-pipe-token=12906442833701149923 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12906442833701149923 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1912 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
1 769
Read events
1 533
Write events
222
Delete events
14
Modification events
| (PID) Process: | (2132) allavsoft.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 5408000070D26AE82A04D501 | |||
| (PID) Process: | (2132) allavsoft.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 4528266B452B390C0B255132EAB1D26CBCC0F53C17CA85D0D030276C09A399A0 | |||
| (PID) Process: | (2132) allavsoft.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (2132) allavsoft.tmp | Key: | HKEY_CURRENT_USER\Software\Allavsoft\Video Downloader Converter |
| Operation: | write | Name: | PackageName |
Value: allavsoft.exe | |||
| (PID) Process: | (2132) allavsoft.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Allavsoft\Video Downloader Converter |
| Operation: | write | Name: | PackageName |
Value: allavsoft.exe | |||
| (PID) Process: | (2132) allavsoft.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\Allavsoft\Video Downloader Converter\videodownloader.exe | |||
| (PID) Process: | (2132) allavsoft.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: 0483E25EFF54142FD5E536F8B516417579A16B1AA446C46CB832D0DF2A7740A0 | |||
| (PID) Process: | (2132) allavsoft.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{6EBED4D8-13D9-4270-8D44-B57DDB7A787C}_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.4 (u) | |||
| (PID) Process: | (2132) allavsoft.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{6EBED4D8-13D9-4270-8D44-B57DDB7A787C}_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\Allavsoft\Video Downloader Converter | |||
| (PID) Process: | (2132) allavsoft.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\{6EBED4D8-13D9-4270-8D44-B57DDB7A787C}_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\Allavsoft\Video Downloader Converter\ | |||
Executable files
56
Suspicious files
147
Text files
243
Unknown types
36
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2132 | allavsoft.tmp | C:\Program Files\Allavsoft\Video Downloader Converter\is-KPF1T.tmp | — | |
MD5:— | SHA256:— | |||
| 2132 | allavsoft.tmp | C:\Program Files\Allavsoft\Video Downloader Converter\is-C48UN.tmp | — | |
MD5:— | SHA256:— | |||
| 2132 | allavsoft.tmp | C:\Program Files\Allavsoft\Video Downloader Converter\is-PBDBV.tmp | — | |
MD5:— | SHA256:— | |||
| 2132 | allavsoft.tmp | C:\Program Files\Allavsoft\Video Downloader Converter\is-A9Q0H.tmp | — | |
MD5:— | SHA256:— | |||
| 2132 | allavsoft.tmp | C:\Program Files\Allavsoft\Video Downloader Converter\is-M1I2H.tmp | — | |
MD5:— | SHA256:— | |||
| 2132 | allavsoft.tmp | C:\Program Files\Allavsoft\Video Downloader Converter\is-BQEKP.tmp | — | |
MD5:— | SHA256:— | |||
| 2132 | allavsoft.tmp | C:\Program Files\Allavsoft\Video Downloader Converter\is-GHQP9.tmp | — | |
MD5:— | SHA256:— | |||
| 2132 | allavsoft.tmp | C:\Program Files\Allavsoft\Video Downloader Converter\is-PUHU2.tmp | — | |
MD5:— | SHA256:— | |||
| 2132 | allavsoft.tmp | C:\Program Files\Allavsoft\Video Downloader Converter\is-EBHT7.tmp | — | |
MD5:— | SHA256:— | |||
| 2132 | allavsoft.tmp | C:\Program Files\Allavsoft\Video Downloader Converter\is-MUMT7.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
7
TCP/UDP connections
89
DNS requests
36
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
352 | chrome.exe | GET | 302 | 172.217.23.174:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 504 b | whitelisted |
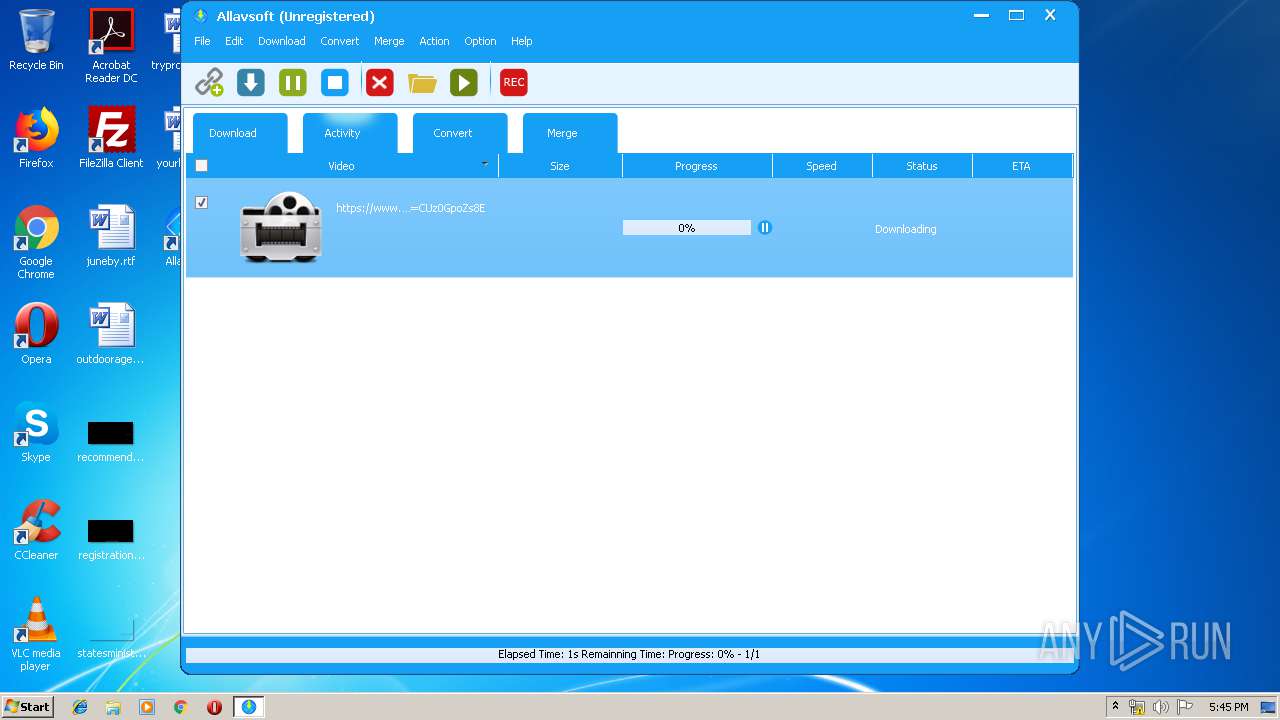
2812 | videodownloader.exe | GET | 200 | 172.217.21.206:80 | http://www.youtube.com/get_video_info?&video_id=CUz0GpoZs8E&el=vevo&ps=default&eurl=&gl=US&hl=en | US | text | 50 b | whitelisted |
2812 | videodownloader.exe | GET | 200 | 172.217.21.206:80 | http://www.youtube.com/get_video_info?&video_id=CUz0GpoZs8E&ps=default&eurl=&gl=US&hl=en | US | text | 23.4 Kb | whitelisted |
2812 | videodownloader.exe | GET | 200 | 172.217.21.206:80 | http://www.youtube.com/get_video_info?&video_id=CUz0GpoZs8E&el=detailpage&ps=default&eurl=&gl=US&hl=en | US | text | 84.1 Kb | whitelisted |
2812 | videodownloader.exe | GET | 200 | 172.217.21.206:80 | http://www.youtube.com/get_video_info?&video_id=CUz0GpoZs8E&el=embedded&ps=default&eurl=&gl=US&hl=en | US | text | 23.3 Kb | whitelisted |
352 | chrome.exe | GET | 200 | 173.194.5.234:80 | http://r5---sn-aigzrn7l.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=185.43.110.12&mm=28&mn=sn-aigzrn7l&ms=nvh&mt=1557161000&mv=m&pl=23&shardbypass=yes | US | crx | 842 Kb | whitelisted |
2812 | videodownloader.exe | GET | 200 | 172.217.21.206:80 | http://www.youtube.com/yts/jsbin/player_ias-vfl61X81T/en_US/base.js | US | text | 1.10 Mb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
352 | chrome.exe | 216.58.206.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
352 | chrome.exe | 216.58.206.14:443 | clients1.google.com | Google Inc. | US | whitelisted |
352 | chrome.exe | 216.58.205.227:443 | www.gstatic.com | Google Inc. | US | whitelisted |
352 | chrome.exe | 172.217.18.110:443 | ogs.google.com | Google Inc. | US | whitelisted |
352 | chrome.exe | 172.217.18.14:443 | apis.google.com | Google Inc. | US | whitelisted |
352 | chrome.exe | 172.217.16.161:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
352 | chrome.exe | 172.217.23.174:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
352 | chrome.exe | 173.194.5.234:80 | r5---sn-aigzrn7l.gvt1.com | Google Inc. | US | whitelisted |
352 | chrome.exe | 216.58.206.4:443 | www.google.com | Google Inc. | US | whitelisted |
352 | chrome.exe | 172.217.23.138:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.allavsoft.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
ogs.google.com |
| whitelisted |
clients2.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
352 | chrome.exe | Generic Protocol Command Decode | SURICATA STREAM excessive retransmissions |
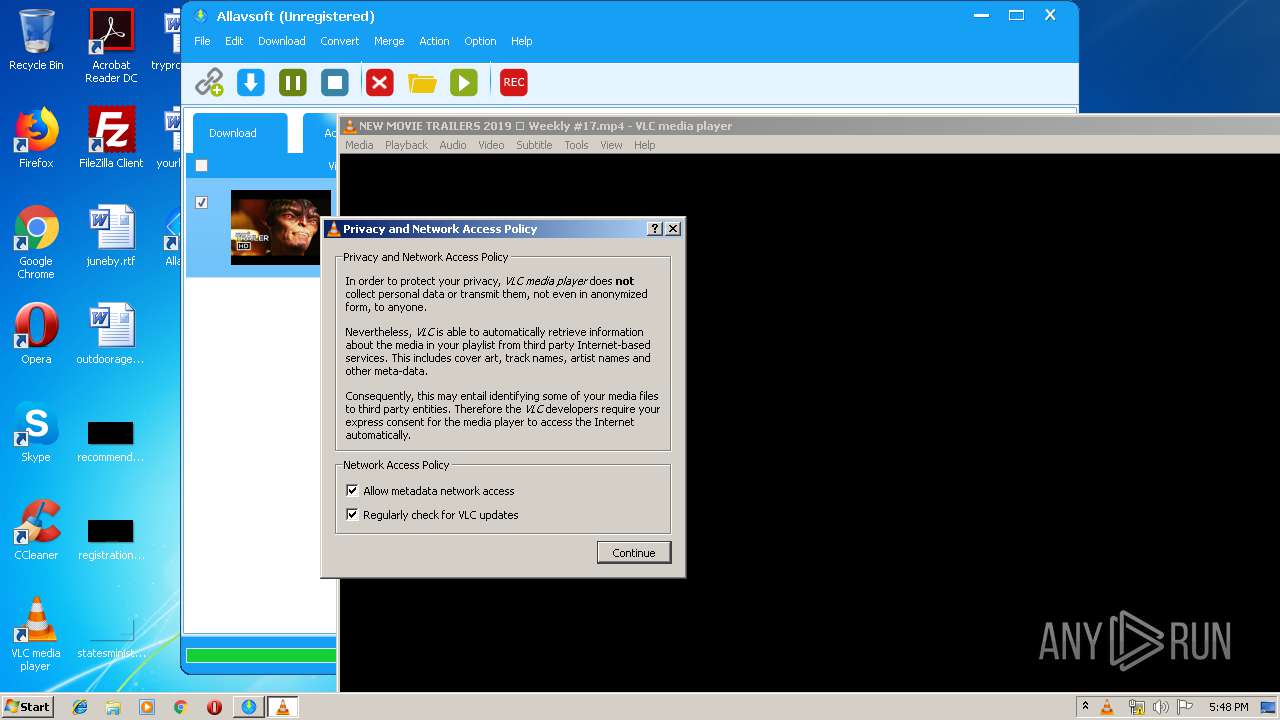
Process | Message |
|---|---|
vlc.exe | core libvlc: one instance mode ENABLED
|
vlc.exe | core libvlc: Running vlc with the default interface. Use 'cvlc' to use vlc without interface.
|
vlc.exe | direct3d vout display error: Could not read adapter capabilities. (hr=0x8876086A)
|
vlc.exe | direct3d vout display error: Direct3D could not be initialized
|