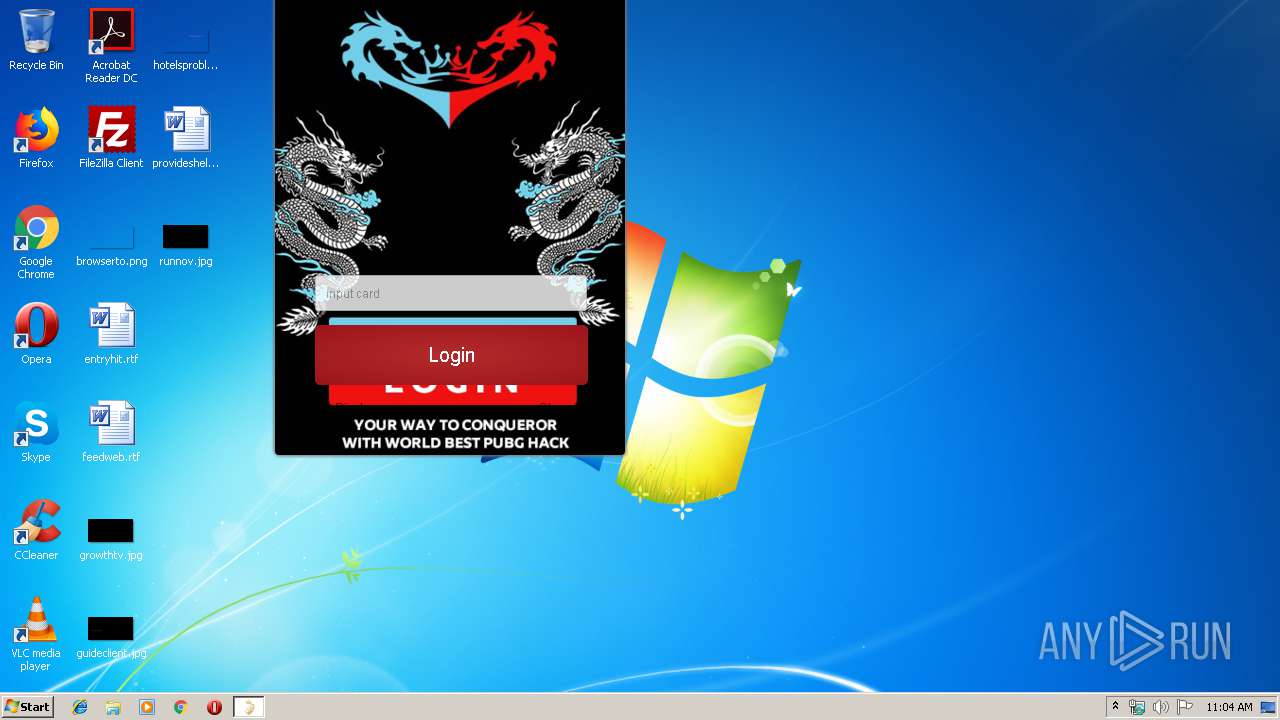
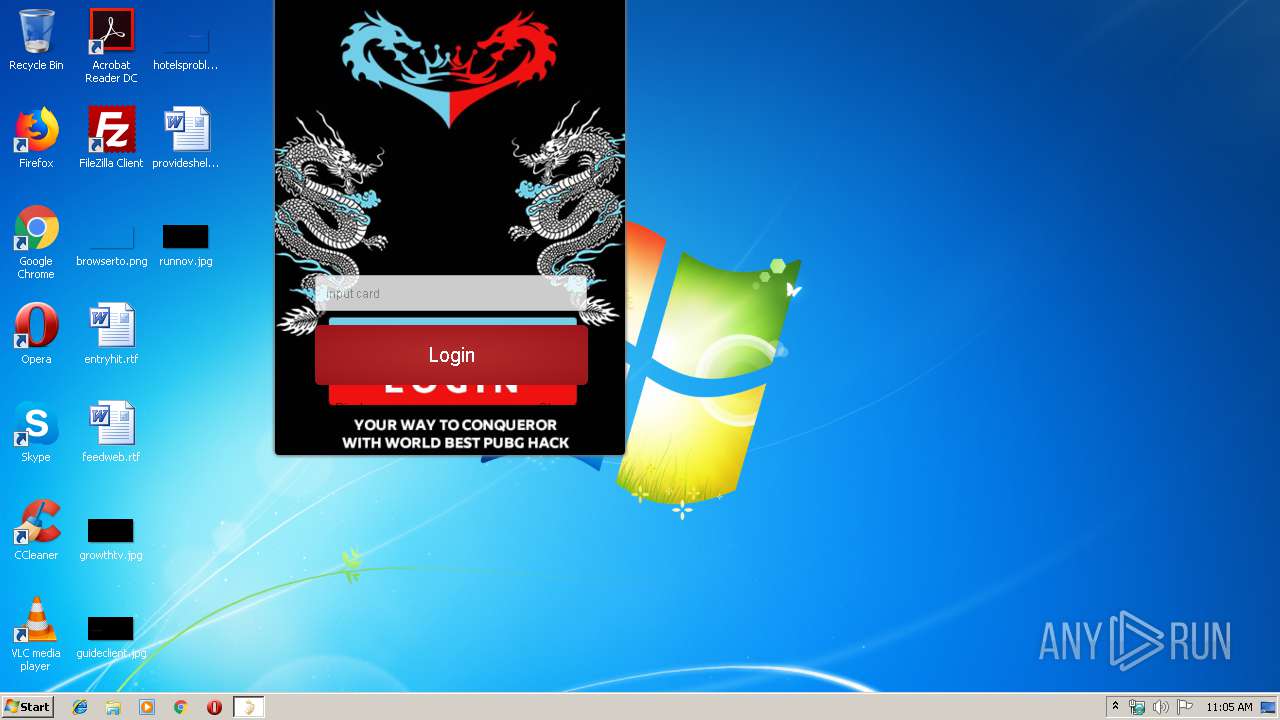
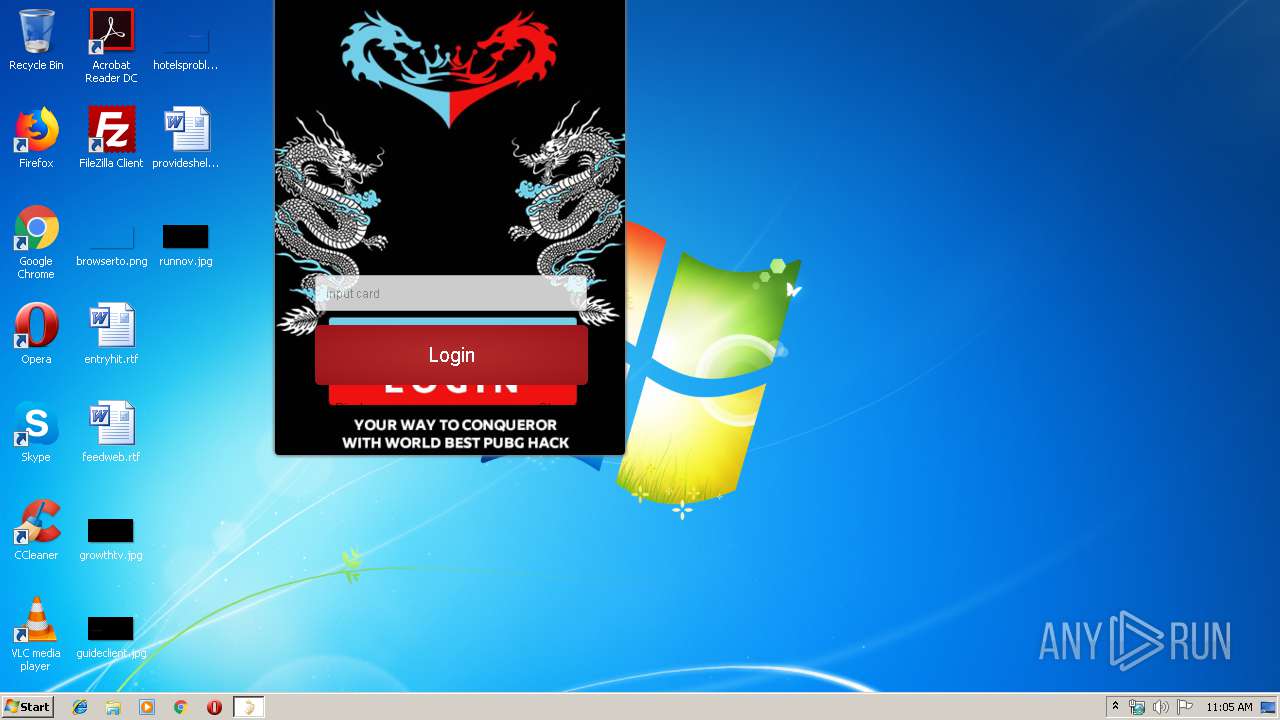
| File name: | Dragon King.mapo.exe |
| Full analysis: | https://app.any.run/tasks/a6c99903-603e-48fa-88a4-71351c9b2b1f |
| Verdict: | Malicious activity |
| Analysis date: | August 17, 2019, 10:04:22 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 79FDDF3EE5B656487857456A5AD936C9 |
| SHA1: | 7F7A87DF01DCCC4479F63A62669049A6563844A9 |
| SHA256: | DC87362BEB5EE41B65CDE750950A69DD0C15C7A091371908022438F9D1C1D821 |
| SSDEEP: | 196608:uVuMjcVaa0LJG4otpRDXAU9lKeHb3dlhr1ksBFyeSMeM/DckeIX:uVu5VBBtpRDQU/LHb33CjVMQ1q |
MALICIOUS
Loads dropped or rewritten executable
- Dragon King.mapo.exe (PID: 3908)
SUSPICIOUS
Executable content was dropped or overwritten
- Dragon King.mapo.exe (PID: 3908)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (64.6) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (15.4) |
| .exe | | | Win32 Executable (generic) (10.5) |
| .exe | | | Generic Win/DOS Executable (4.6) |
| .exe | | | DOS Executable Generic (4.6) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:06:30 14:30:44+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 802816 |
| InitializedDataSize: | 606208 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x4e3184 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Chinese (Simplified) |
| CharacterSet: | Unicode |
| FileVersion: | 1.0.0.0 |
| FileDescription: | 易语言程序 |
| ProductName: | 易语言程序 |
| ProductVersion: | 1.0.0.0 |
| LegalCopyright: | 作者版权所有 请尊重并使用正版 |
| Comments: | 本程序使用易语言编写(http://www.dywt.com.cn) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 30-Jun-2019 12:30:44 |
| Detected languages: |
|
| FileVersion: | 1.0.0.0 |
| FileDescription: | 易语言程序 |
| ProductName: | 易语言程序 |
| ProductVersion: | 1.0.0.0 |
| LegalCopyright: | 作者版权所有 请尊重并使用正版 |
| Comments: | 本程序使用易语言编写(http://www.dywt.com.cn) |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000118 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 30-Jun-2019 12:30:44 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00346000 | 0x00000000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.mapo | 0x004F5000 | 0x00023000 | 0x000220EC | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.38708 |
.rsrc | 0x004E5000 | 0x00010000 | 0x00010000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.88116 |
.mapo2 | 0x00518000 | 0x0065C000 | 0x0065B41B | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.94505 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.07695 | 461 | Latin 1 / Western European | UNKNOWN | RT_MANIFEST |
2 | 2.18858 | 296 | Latin 1 / Western European | Chinese - PRC | RT_ICON |
3 | 5.51925 | 1128 | Latin 1 / Western European | UNKNOWN | RT_ICON |
4 | 4.94792 | 2440 | Latin 1 / Western European | UNKNOWN | RT_ICON |
5 | 4.69054 | 4264 | Latin 1 / Western European | UNKNOWN | RT_ICON |
6 | 4.29227 | 9640 | Latin 1 / Western European | UNKNOWN | RT_ICON |
7 | 3.4568 | 16936 | Latin 1 / Western European | UNKNOWN | RT_ICON |
127 | 1.4183 | 12 | Latin 1 / Western European | Chinese - PRC | RT_MENU |
150 | 3.06278 | 152 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
286 | 3.5561 | 378 | Latin 1 / Western European | Chinese - PRC | RT_DIALOG |
Imports
ADVAPI32.dll |
AVIFIL32.dll |
COMCTL32.dll |
GDI32.dll |
IPHLPAPI.DLL |
MSIMG32.dll |
MSVFW32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
Total processes
32
Monitored processes
1
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3908 | "C:\Users\admin\AppData\Local\Temp\Dragon King.mapo.exe" | C:\Users\admin\AppData\Local\Temp\Dragon King.mapo.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: 易语言程序 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
Total events
3
Read events
3
Write events
0
Delete events
0
Modification events
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3908 | Dragon King.mapo.exe | C:\Users\admin\AppData\Local\Temp\1489218\11981.dll | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3908 | Dragon King.mapo.exe | POST | — | 120.41.41.9:80 | http://ieqgmccbgb66pn86.soft.maposafe.com/wx.php | CN | — | — | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3908 | Dragon King.mapo.exe | 120.41.41.9:80 | ieqgmccbgb66pn86.soft.maposafe.com | Xiamen | CN | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ieqgmccbgb66pn86.soft.maposafe.com |
| unknown |
Threats
Process | Message |
|---|---|
Dragon King.mapo.exe | scrt_initialize_thread_safe_statics
|
Dragon King.mapo.exe | WebPageImpl::init: 0200B7C0
|
Dragon King.mapo.exe | Console:[1],[Uncaught SyntaxError: missing ) after argument list],[cwebview::runJS]
|