| File name: | phish_alert_sp2_2.0.0.0.eml |
| Full analysis: | https://app.any.run/tasks/d2ba46ca-d4b5-431d-a84d-aefb8f6928bc |
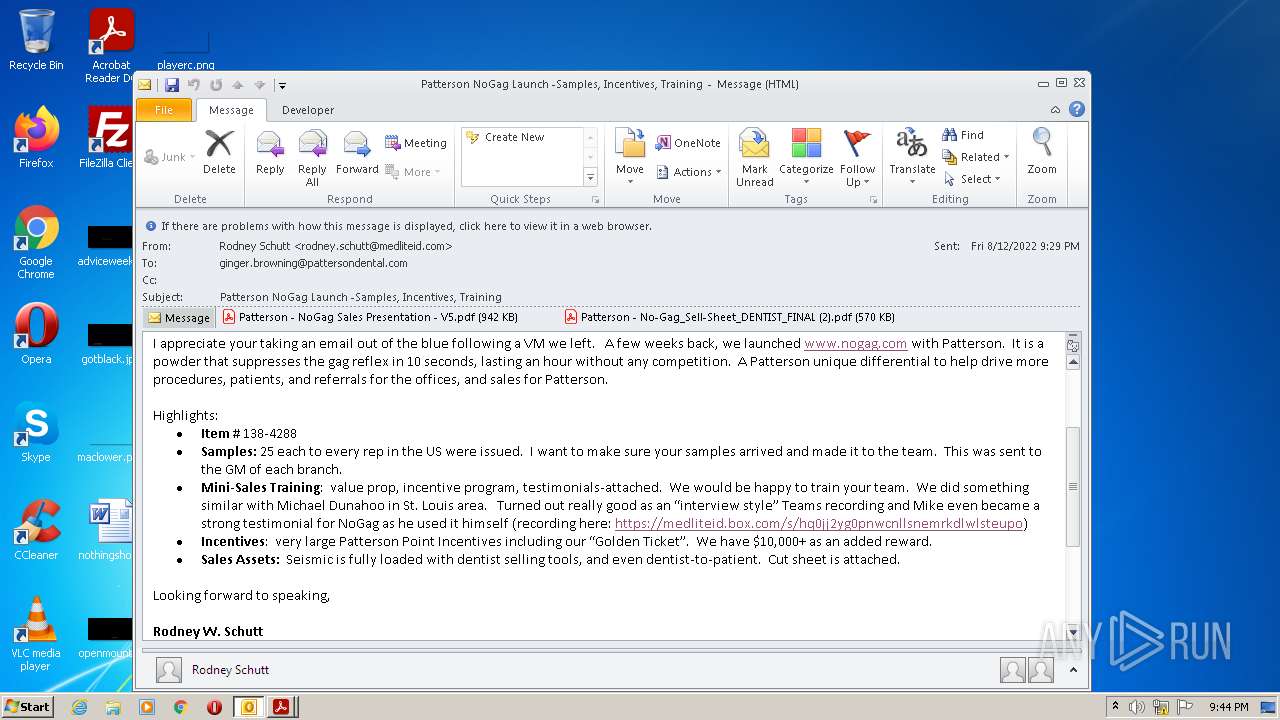
| Verdict: | Malicious activity |
| Analysis date: | August 12, 2022, 20:42:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | message/rfc822 |
| File info: | RFC 822 mail, ASCII text, with very long lines, with CRLF line terminators |
| MD5: | 03BE199C0FE0ED83E102B113B14C37C9 |
| SHA1: | 7561D868C3F06C36787C108B0192BAD8A0090645 |
| SHA256: | DC6FB3B8ED52FDA7455262A51BC9A4ADE2AC7477277383A5204901D461C1A7EA |
| SSDEEP: | 24576:KQs9mb/it2WZpQFHSg8YhWbGuH3Crp4mSAKarHqyBdr3JY+2ZG4ewIAMiGkiEfhd:Kbp2RHS1SOC5xrJ282IGiWhswEu |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 1984)
SUSPICIOUS
Reads the computer name
- OUTLOOK.EXE (PID: 3444)
- AdobeARM.exe (PID: 2160)
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3212)
Checks supported languages
- OUTLOOK.EXE (PID: 3444)
- AdobeARM.exe (PID: 2160)
- Reader_sl.exe (PID: 2940)
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3212)
Searches for installed software
- OUTLOOK.EXE (PID: 3444)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 1564)
- iexplore.exe (PID: 3736)
Modifies files in Chrome extension folder
- chrome.exe (PID: 1984)
Executed via COM
- FlashUtil32_32_0_0_453_ActiveX.exe (PID: 3212)
Creates files in the program directory
- AdobeARM.exe (PID: 2160)
Executable content was dropped or overwritten
- AdobeARM.exe (PID: 2160)
Drops a file with a compile date too recent
- chrome.exe (PID: 1984)
INFO
Searches for installed software
- AcroRd32.exe (PID: 2760)
- AcroRd32.exe (PID: 2952)
- AcroRd32.exe (PID: 1816)
Checks supported languages
- AcroRd32.exe (PID: 2952)
- RdrCEF.exe (PID: 2112)
- RdrCEF.exe (PID: 2768)
- AcroRd32.exe (PID: 2760)
- RdrCEF.exe (PID: 1168)
- RdrCEF.exe (PID: 3032)
- RdrCEF.exe (PID: 2220)
- RdrCEF.exe (PID: 3304)
- RdrCEF.exe (PID: 2832)
- RdrCEF.exe (PID: 3812)
- AcroRd32.exe (PID: 2344)
- iexplore.exe (PID: 4040)
- AcroRd32.exe (PID: 1816)
- RdrCEF.exe (PID: 3568)
- iexplore.exe (PID: 1564)
- chrome.exe (PID: 1984)
- chrome.exe (PID: 3032)
- chrome.exe (PID: 876)
- chrome.exe (PID: 3000)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 2476)
- chrome.exe (PID: 2184)
- chrome.exe (PID: 3484)
- chrome.exe (PID: 1032)
- chrome.exe (PID: 3056)
- chrome.exe (PID: 2616)
- chrome.exe (PID: 3488)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 3856)
- iexplore.exe (PID: 3216)
- iexplore.exe (PID: 3736)
- chrome.exe (PID: 2552)
Reads Microsoft Office registry keys
- AcroRd32.exe (PID: 2952)
- OUTLOOK.EXE (PID: 3444)
Reads the computer name
- AcroRd32.exe (PID: 2760)
- AcroRd32.exe (PID: 2952)
- RdrCEF.exe (PID: 1168)
- AcroRd32.exe (PID: 2344)
- AcroRd32.exe (PID: 1816)
- iexplore.exe (PID: 4040)
- iexplore.exe (PID: 1564)
- chrome.exe (PID: 1984)
- chrome.exe (PID: 3032)
- chrome.exe (PID: 2556)
- chrome.exe (PID: 2184)
- chrome.exe (PID: 2552)
- chrome.exe (PID: 3092)
- chrome.exe (PID: 3856)
- iexplore.exe (PID: 3216)
- iexplore.exe (PID: 3736)
Application launched itself
- AcroRd32.exe (PID: 2760)
- RdrCEF.exe (PID: 1168)
- AcroRd32.exe (PID: 1816)
- iexplore.exe (PID: 4040)
- chrome.exe (PID: 1984)
- iexplore.exe (PID: 3216)
Reads CPU info
- AcroRd32.exe (PID: 2952)
- AcroRd32.exe (PID: 2344)
- iexplore.exe (PID: 1564)
Checks Windows Trust Settings
- AcroRd32.exe (PID: 2760)
- iexplore.exe (PID: 1564)
- iexplore.exe (PID: 4040)
- AdobeARM.exe (PID: 2160)
- iexplore.exe (PID: 3736)
Reads settings of System Certificates
- AcroRd32.exe (PID: 2760)
- RdrCEF.exe (PID: 1168)
- iexplore.exe (PID: 1564)
- iexplore.exe (PID: 4040)
- chrome.exe (PID: 2556)
- AdobeARM.exe (PID: 2160)
- iexplore.exe (PID: 3736)
Changes internet zones settings
- iexplore.exe (PID: 4040)
- iexplore.exe (PID: 3216)
Reads internet explorer settings
- iexplore.exe (PID: 1564)
- iexplore.exe (PID: 3736)
Manual execution by user
- chrome.exe (PID: 1984)
Reads the date of Windows installation
- iexplore.exe (PID: 4040)
- iexplore.exe (PID: 3216)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .eml | | | E-Mail message (Var. 5) (100) |
|---|
Total processes
81
Monitored processes
36
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,15564090312582247334,14349882286775390486,131072 --enable-features=PasswordImport --lang=en-US --instant-process --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1032 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1036,15564090312582247334,14349882286775390486,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1920 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16514043 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 1564 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:4040 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1816 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\IK48P2WJ\Patterson - No-Gag_Sell-Sheet_DENTIST_FINAL (2).pdf" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 1984 | "C:\Program Files\Google\Chrome\Application\chrome.exe" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2112 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=gpu-process --field-trial-handle=1176,14107938441288782366,6689801816271041209,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --lang=en-US --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAABAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --use-gl=swiftshader-webgl --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --service-request-channel-token=15538970125948558982 --mojo-platform-channel-handle=1228 --allow-no-sandbox-job --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe" /PRODUCT:Reader /VERSION:20.0 /MODE:3 | C:\Program Files\Common Files\Adobe\ARM\1.0\AdobeARM.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Adobe Inc. Integrity Level: MEDIUM Description: Adobe Reader and Acrobat Manager Exit code: 0 Version: 1.824.39.9311 Modules
| |||||||||||||||
| 2184 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1036,15564090312582247334,14349882286775390486,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1032 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2220 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1176,14107938441288782366,6689801816271041209,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11064020808830326872 --renderer-client-id=2 --mojo-platform-channel-handle=1188 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
Total events
54 882
Read events
53 141
Write events
1 704
Delete events
37
Modification events
| (PID) Process: | (3444) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3444) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (3444) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (3444) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (3444) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (3444) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (3444) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (3444) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (3444) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
| (PID) Process: | (3444) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1055 |
Value: Off | |||
Executable files
1
Suspicious files
383
Text files
246
Unknown types
82
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3444 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVRD5A5.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3444 | OUTLOOK.EXE | C:\Users\admin\Documents\Outlook Files\Outlook Data File - NoMail.pst | — | |
MD5:— | SHA256:— | |||
| 3444 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\outlook logging\firstrun.log | text | |
MD5:— | SHA256:— | |||
| 3444 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmpD78B.tmp | binary | |
MD5:— | SHA256:— | |||
| 3444 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\tmpD77A.tmp | binary | |
MD5:— | SHA256:— | |||
| 3444 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
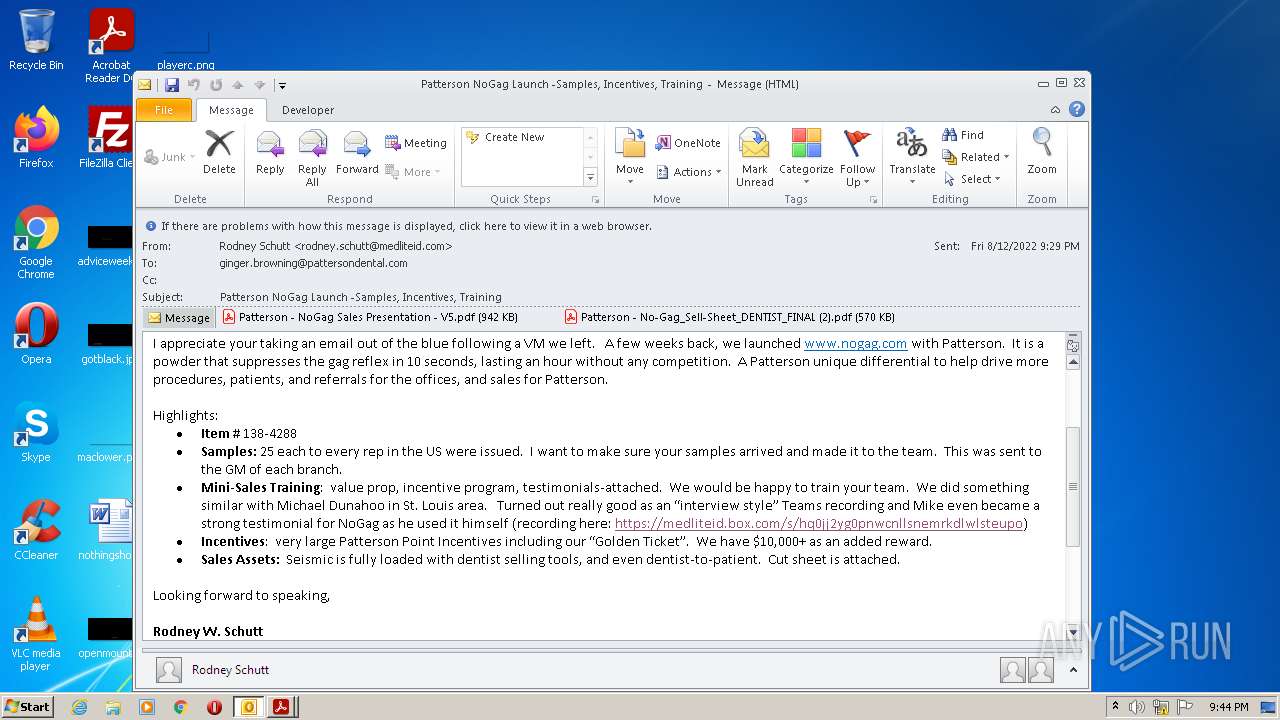
| 3444 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\IK48P2WJ\Patterson - NoGag Sales Presentation - V5.pdf | ||
MD5:— | SHA256:— | |||
| 1168 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\0786087c3c360803_0 | binary | |
MD5:— | SHA256:— | |||
| 3444 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\IK48P2WJ\Patterson - NoGag Sales Presentation - V5 (2).pdf | ||
MD5:— | SHA256:— | |||
| 1168 | RdrCEF.exe | C:\Users\admin\AppData\LocalLow\Adobe\AcroCef\DC\Acrobat\Cache\Code Cache\js\4a0e94571d979b3c_0 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
17
TCP/UDP connections
88
DNS requests
43
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2556 | chrome.exe | GET | 302 | 142.250.186.110:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvNzI0QUFXNV9zT2RvdUwyMERESEZGVmJnQQ/1.0.0.6_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 563 b | whitelisted |
1564 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTk45WiKdPUwcMf8JgMC07ACYqr2AQUt2ui6qiqhIx56rTaD5iyxZV2ufQCEA7ze%2BiSFHmYKH4I97FkjrU%3D | US | der | 471 b | whitelisted |
1564 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
3736 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDyjRAUcVc1IArKByftf8KS | US | der | 472 b | whitelisted |
3736 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAlrgulzmZS6%2FVWwIdvHyL8%3D | US | der | 279 b | whitelisted |
4040 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
3736 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | US | der | 1.41 Kb | whitelisted |
3736 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQDGaM9nfILxSxIGz%2Bm2TRwQ | US | der | 472 b | whitelisted |
3736 | iexplore.exe | GET | 200 | 142.250.185.131:80 | http://ocsp.pki.goog/gts1c3/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTHLnmK3f9hNLO67UdCuLvGwCQHYwQUinR%2Fr4XN7pXNPZzQ4kYU83E1HScCEQC7KoDMFPzdvBICsqCGvR0X | US | der | 472 b | whitelisted |
3736 | iexplore.exe | GET | 301 | 199.60.103.227:80 | http://www.nogag.com/ | CA | — | — | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3444 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
1168 | RdrCEF.exe | 18.207.85.246:443 | p13n.adobe.io | — | US | suspicious |
1168 | RdrCEF.exe | 184.51.8.204:443 | armmf.adobe.com | Akamai Technologies, Inc. | US | whitelisted |
2760 | AcroRd32.exe | 8.249.63.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
2760 | AcroRd32.exe | 23.6.112.41:443 | acroipm2.adobe.com | Akamai International B.V. | NL | suspicious |
2760 | AcroRd32.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
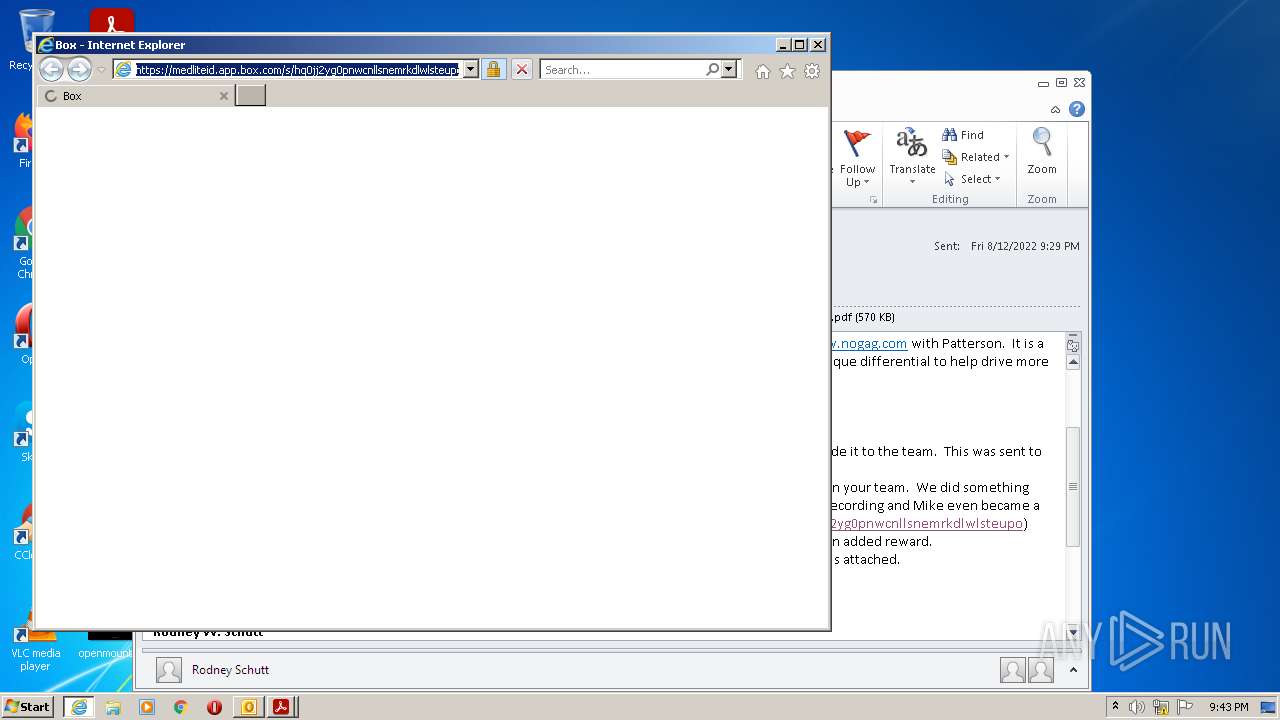
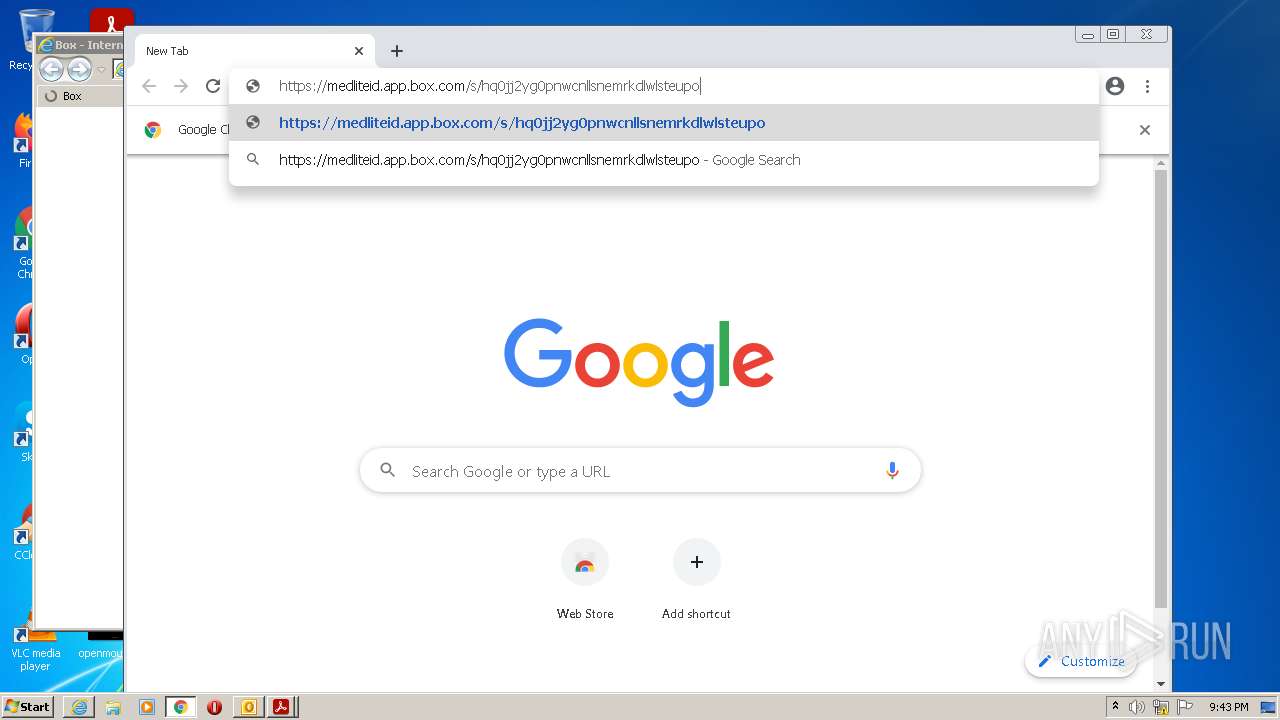
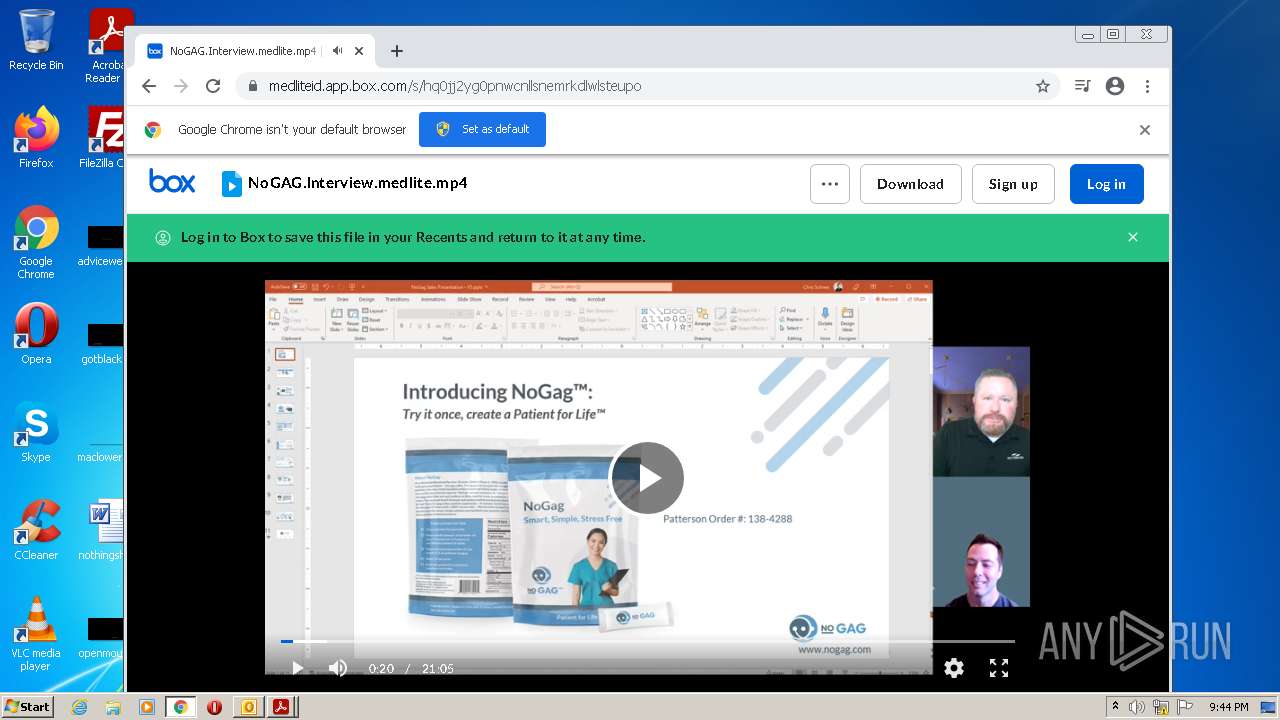
1564 | iexplore.exe | 185.235.236.197:443 | medliteid.box.com | — | — | suspicious |
1564 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1564 | iexplore.exe | 74.112.186.144:443 | medliteid.app.box.com | Box.com | US | suspicious |
4040 | iexplore.exe | 13.107.21.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
geo2.adobe.com |
| whitelisted |
p13n.adobe.io |
| whitelisted |
armmf.adobe.com |
| whitelisted |
acroipm2.adobe.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
medliteid.box.com |
| unknown |
medliteid.app.box.com |
| suspicious |
api.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
928 | svchost.exe | Potentially Bad Traffic | ET INFO TLS Handshake Failure |