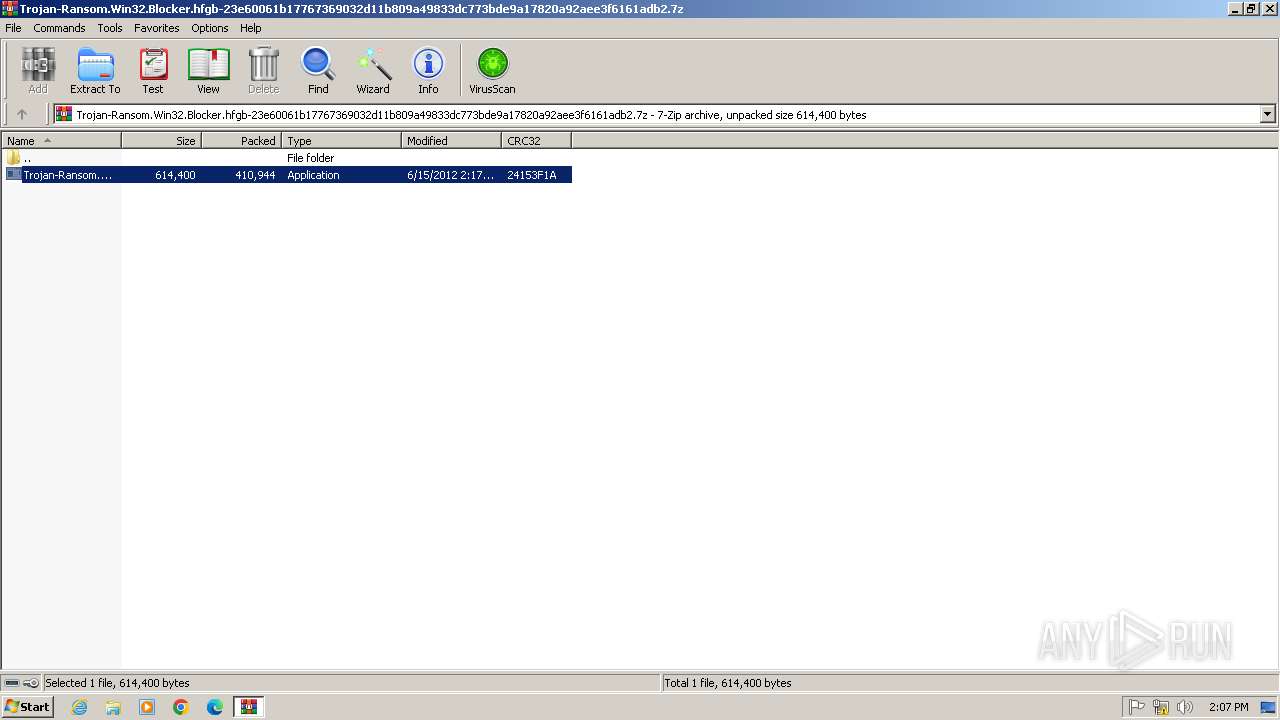
| File name: | Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.7z |
| Full analysis: | https://app.any.run/tasks/076e8654-323e-42c9-9232-408007bba8e8 |
| Verdict: | Malicious activity |
| Analysis date: | April 19, 2025, 13:07:14 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
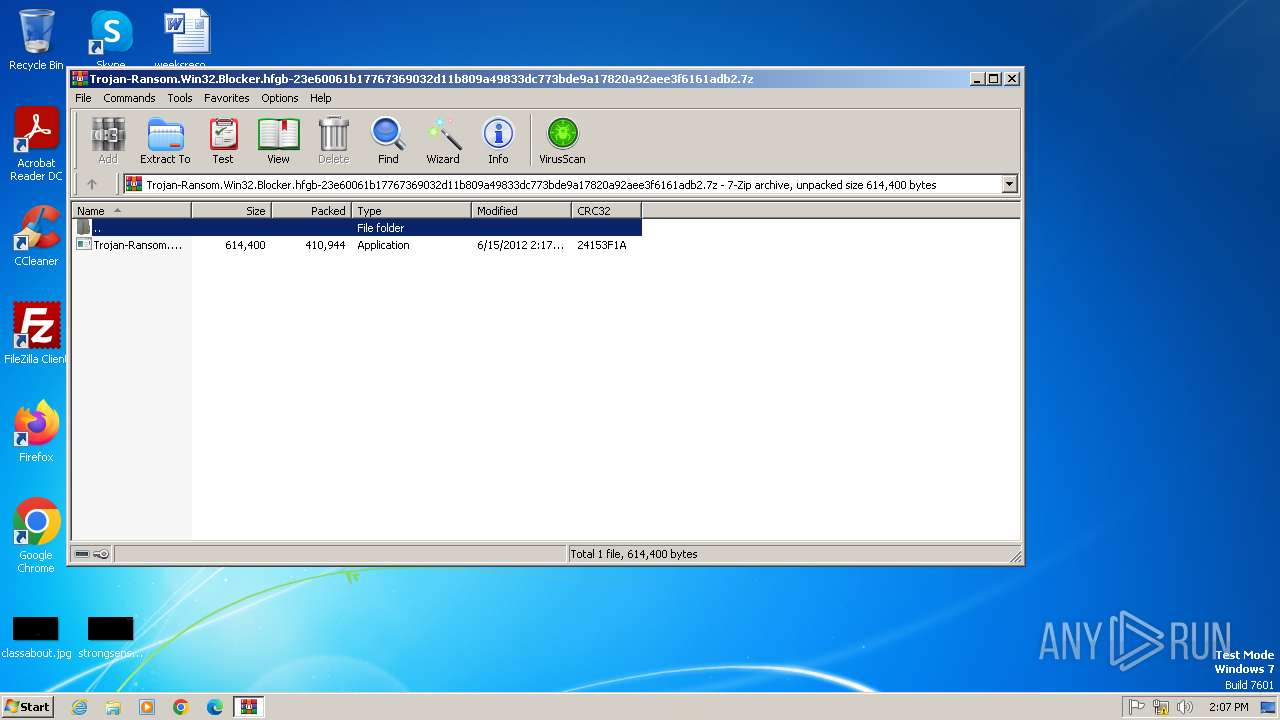
| MIME: | application/x-7z-compressed |
| File info: | 7-zip archive data, version 0.4 |
| MD5: | 92C305793D6B03F5CBAF5E40DF4A69A7 |
| SHA1: | DFD8CE547FCCBA0BFE49F2CC3E0DFE93AD312416 |
| SHA256: | DC6A0535E5CA21EE42303444680A75061821E501CADFB54B4231158292D9998C |
| SSDEEP: | 12288:gMeTQED8SHRevS2760qBkUZR3OstemfTy+66HL5Baw:gMeTT4cReB760qBkUZR3vte1+Fr5Baw |
MALICIOUS
Changes the login/logoff helper path in the registry
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
Changes the autorun value in the registry
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
Disables task manager
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
SUSPICIOUS
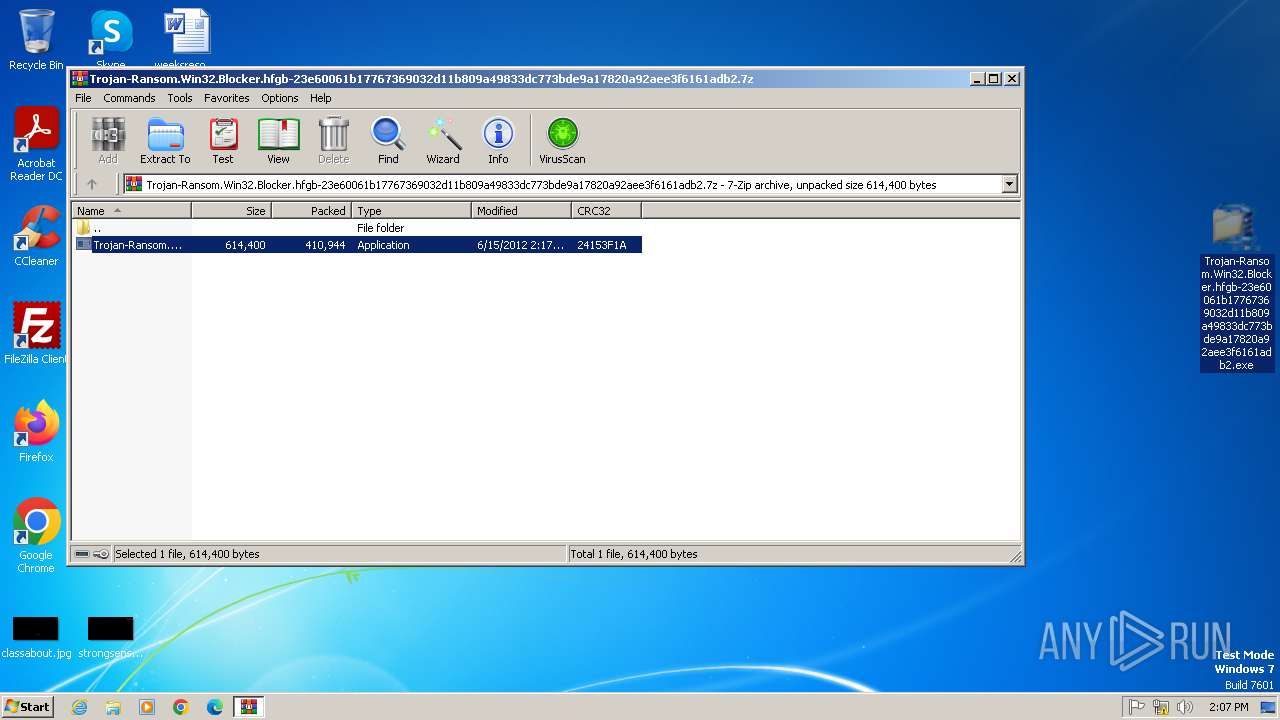
Process drops legitimate windows executable
- WinRAR.exe (PID: 2060)
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
Application launched itself
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2528)
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 892)
Changes internet zones settings
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
Executable content was dropped or overwritten
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
Reads Internet Explorer settings
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
Reads the Internet Settings
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
Reads security settings of Internet Explorer
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
There is functionality for taking screenshot (YARA)
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
Reads Microsoft Outlook installation path
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
INFO
The sample compiled with bulgarian language support
- WinRAR.exe (PID: 2060)
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2060)
Checks supported languages
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2528)
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 892)
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
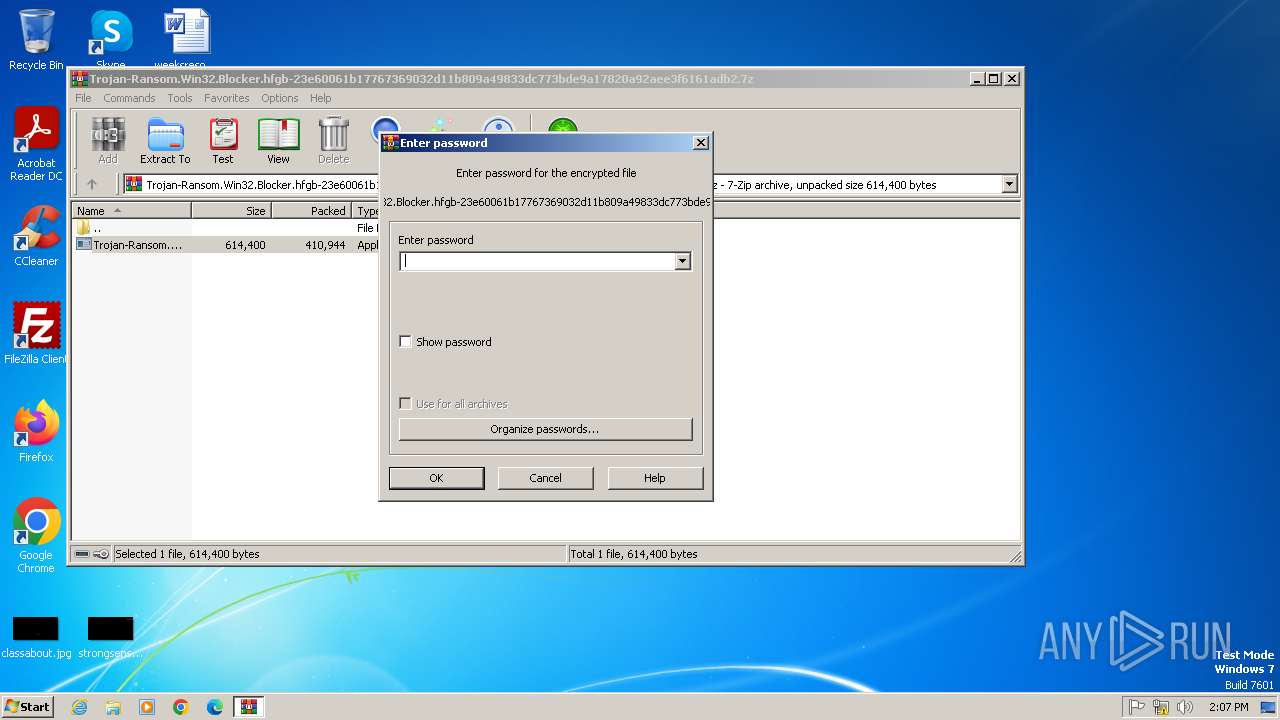
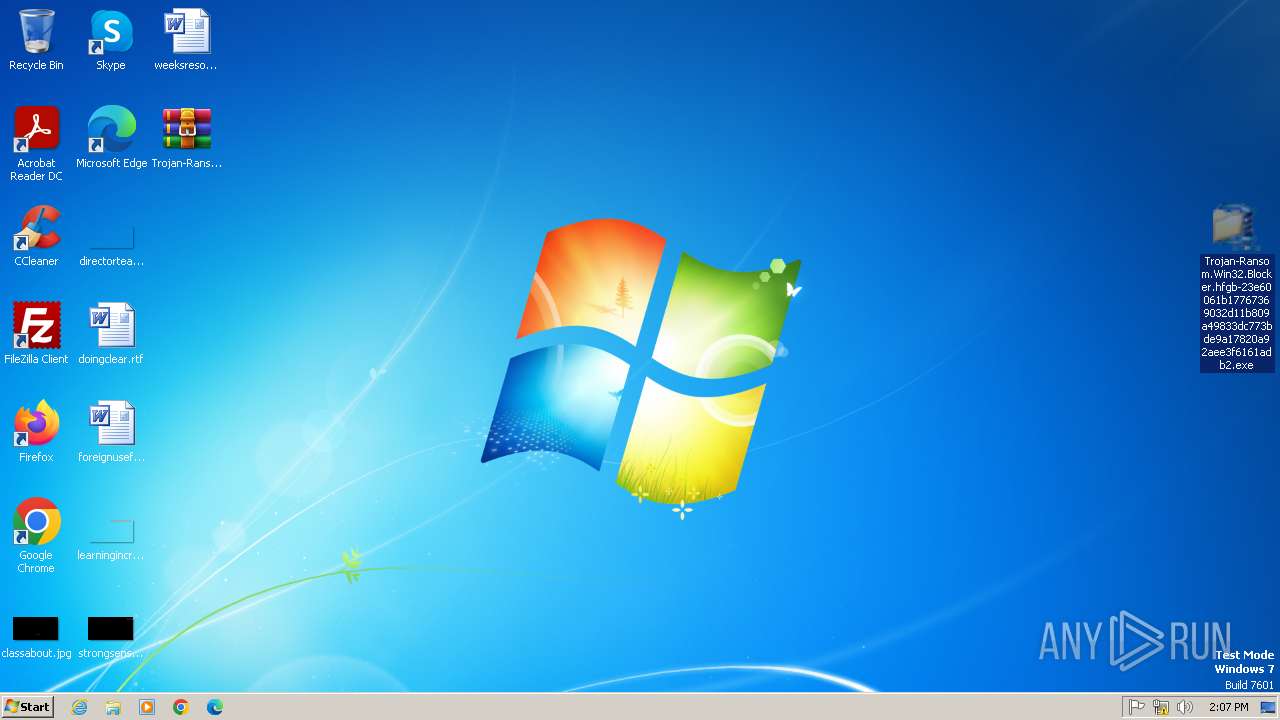
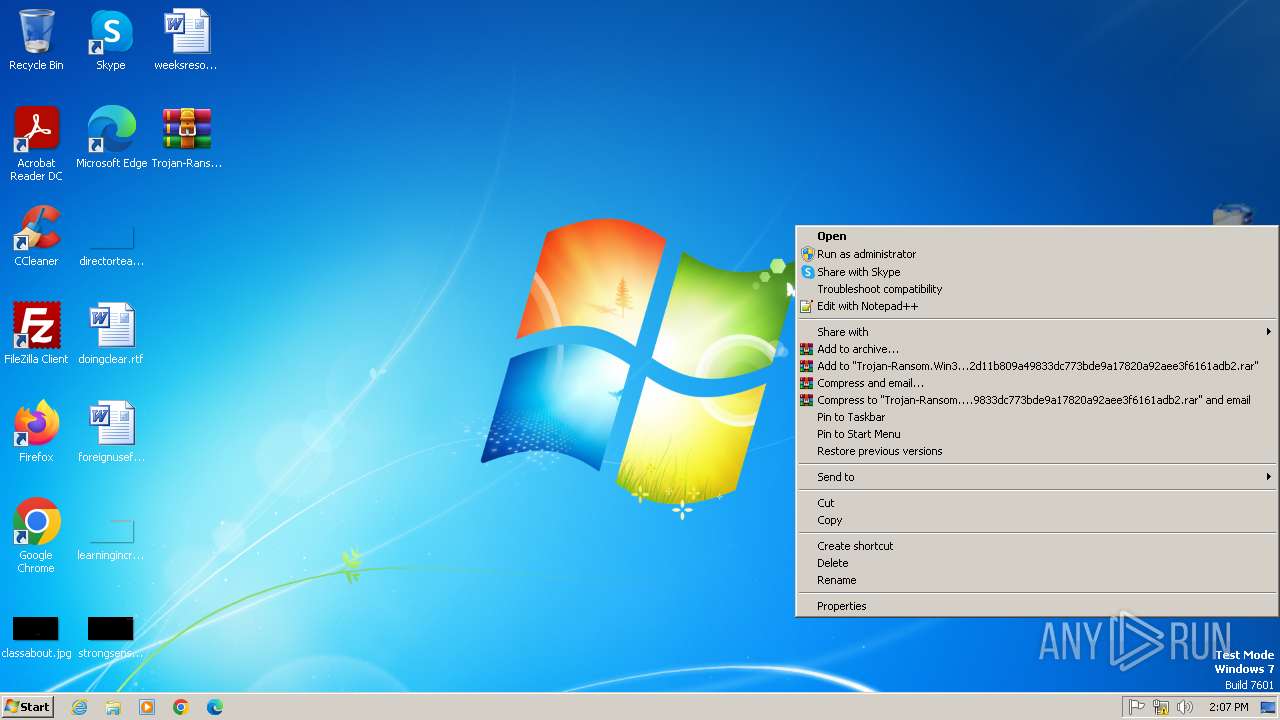
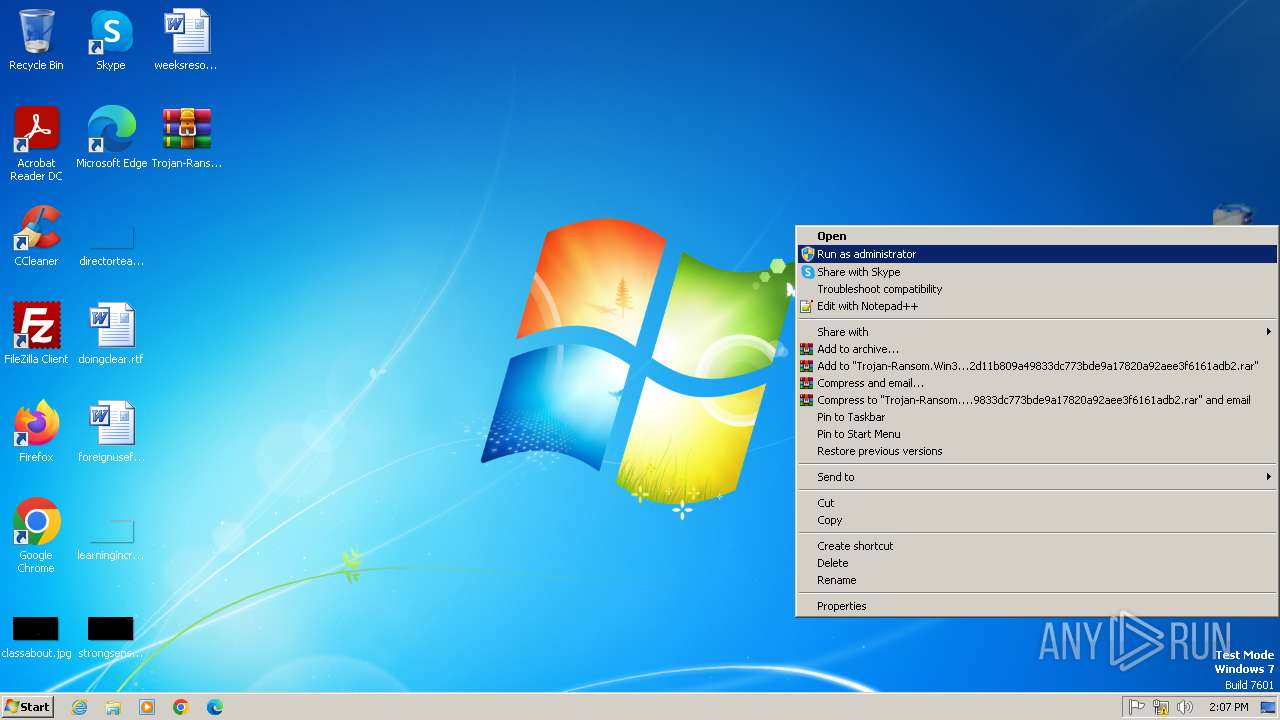
Manual execution by a user
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2528)
Reads the computer name
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 892)
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
The sample compiled with russian language support
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
Checks proxy server information
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
Reads the machine GUID from the registry
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
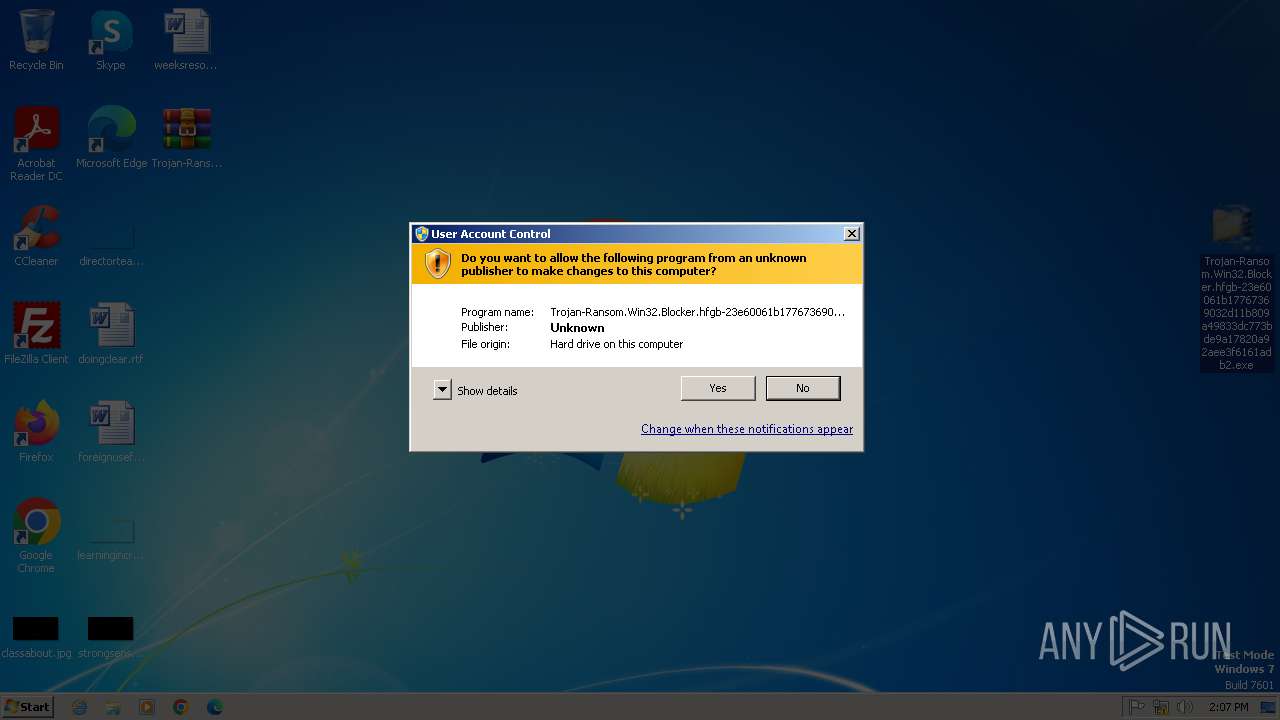
Process checks whether UAC notifications are on
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
UPX packer has been detected
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
Creates files or folders in the user directory
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
Compiled with Borland Delphi (YARA)
- Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe (PID: 2912)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .7z | | | 7-Zip compressed archive (v0.4) (57.1) |
|---|---|---|
| .7z | | | 7-Zip compressed archive (gen) (42.8) |
EXIF
ZIP
| FileVersion: | 7z v0.04 |
|---|---|
| ModifyDate: | 2012:06:15 01:17:34+00:00 |
| ArchivedFileName: | Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe |
Total processes
44
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 892 | "C:\Users\admin\Desktop\Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe" | C:\Users\admin\Desktop\Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe | — | Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2060 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.7z | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 2528 | "C:\Users\admin\Desktop\Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe" | C:\Users\admin\Desktop\Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2912 | "C:\Users\admin\Desktop\Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe" | C:\Users\admin\Desktop\Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe | Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
4 451
Read events
4 292
Write events
135
Delete events
24
Modification events
| (PID) Process: | (2060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (2060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (2060) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\182\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\Win7-KB3191566-x86.zip | |||
| (PID) Process: | (2060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\curl-8.5.0_1-win32-mingw.zip | |||
| (PID) Process: | (2060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.7z | |||
| (PID) Process: | (2060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2060) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
Executable files
3
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2060 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRb2060.34967\Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe | executable | |
MD5:D1D0EC2EB4572C8B819AF742E4443D0D | SHA256:23E60061B17767369032D11B809A49833DC773BDE9A17820A92AEE3F6161ADB2 | |||
| 2912 | Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe | C:\Users\admin\Desktop\dwlGina3.dll | executable | |
MD5:456F8BC05E54621C857F013AAAD94C9E | SHA256:C96E0C0E89DDDB8435A28F04662254241A3C7B96ED2626267112037BD0AF30DF | |||
| 2912 | Trojan-Ransom.Win32.Blocker.hfgb-23e60061b17767369032d11b809a49833dc773bde9a17820a92aee3f6161adb2.exe | C:\Users\admin\AppData\Roaming\aerhuy5e4u.exe | executable | |
MD5:D1D0EC2EB4572C8B819AF742E4443D0D | SHA256:23E60061B17767369032D11B809A49833DC773BDE9A17820A92AEE3F6161ADB2 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
6
DNS requests
2
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
www.huggibuggi.com |
| whitelisted |