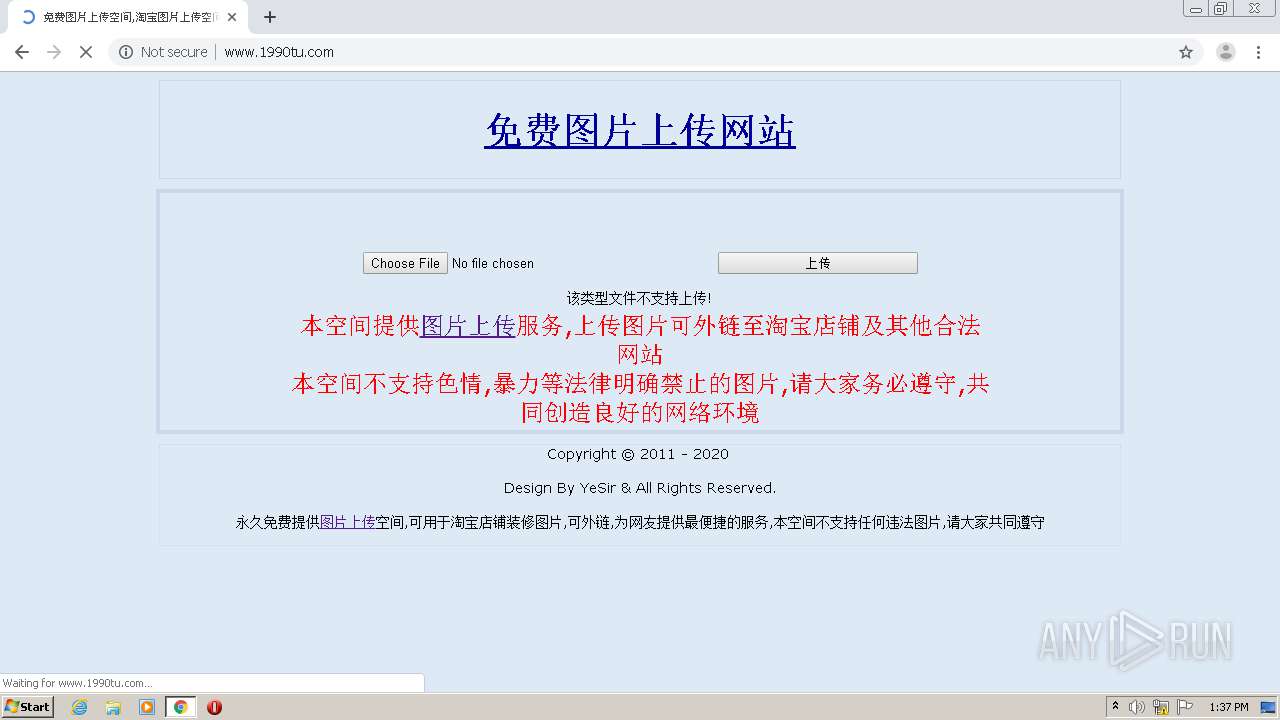
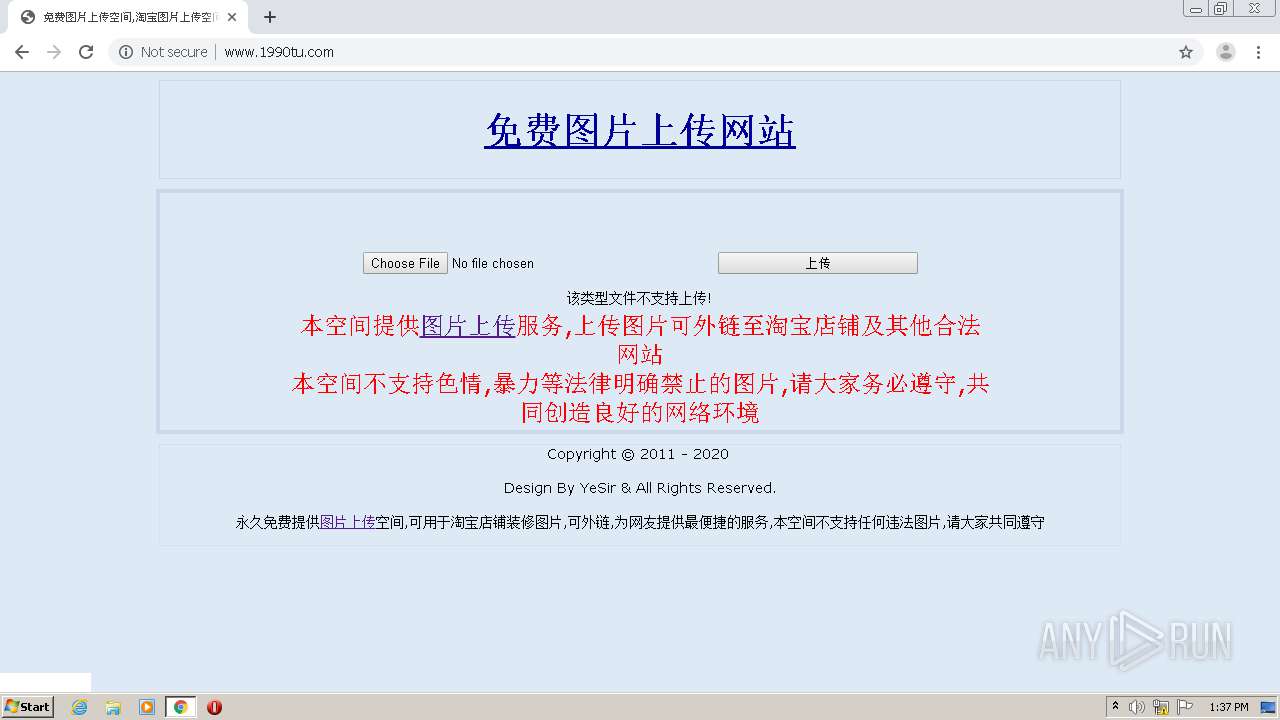
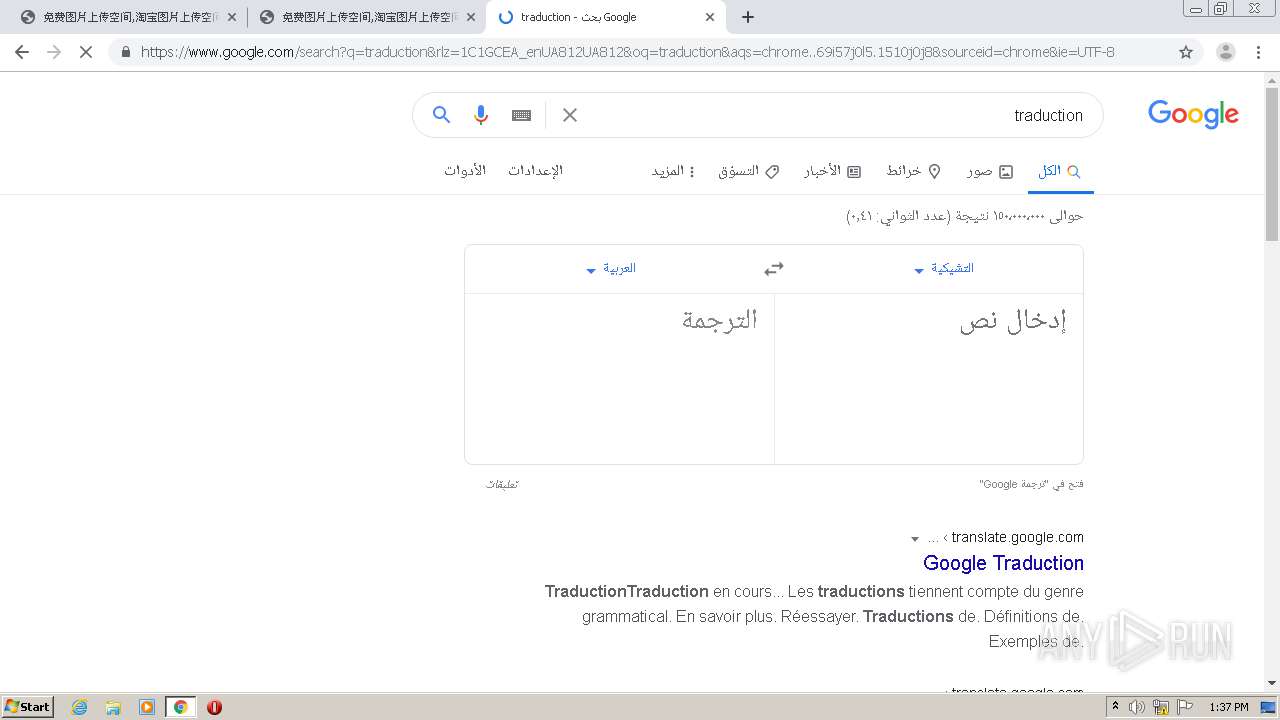
| URL: | http://www.1990tu.com/ |
| Full analysis: | https://app.any.run/tasks/07410757-e677-44b0-8876-37b1c7ad9a06 |
| Verdict: | Malicious activity |
| Analysis date: | September 30, 2020, 12:36:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 1D7AC689306CE1A078D110D20A2C3F92 |
| SHA1: | 53334B7F8CDAA2CC61D9C29D76FC71B65D085C6A |
| SHA256: | DC5D44AF599D7AD9499B04AF6B499AAE985B1385FE9535D8027F237CA3F0B50D |
| SSDEEP: | 3:N1KJS4DLGK3:Cc4DZ3 |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 1396)
Reads the hosts file
- chrome.exe (PID: 1396)
- chrome.exe (PID: 3276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
53
Monitored processes
17
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,8078916075532586911,725716743603362866,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=12866818721924879470 --mojo-platform-channel-handle=3468 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 700 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,8078916075532586911,725716743603362866,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=4170025066139194954 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2160 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 760 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,8078916075532586911,725716743603362866,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=6173455681324454045 --mojo-platform-channel-handle=3388 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1236 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,8078916075532586911,725716743603362866,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2342864637408821477 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2264 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" "http://www.1990tu.com/" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1844 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,8078916075532586911,725716743603362866,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=18126752339974698744 --mojo-platform-channel-handle=3412 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2444 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,8078916075532586911,725716743603362866,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15775118772815538093 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2664 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2576 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,8078916075532586911,725716743603362866,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=8248587419105962434 --mojo-platform-channel-handle=3576 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2676 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,8078916075532586911,725716743603362866,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=15694768759960826191 --renderer-client-id=10 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1088 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3036 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,8078916075532586911,725716743603362866,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=4349617671367644924 --mojo-platform-channel-handle=2620 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
1 202
Read events
1 062
Write events
135
Delete events
5
Modification events
| (PID) Process: | (1396) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (1396) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (1396) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (1396) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (1396) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3916) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 1396-13245943013446500 |
Value: 259 | |||
| (PID) Process: | (1396) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (1396) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (1396) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3228-13245745346152343 |
Value: 0 | |||
| (PID) Process: | (1396) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
23
Text files
79
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1396 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5F747BE5-574.pma | — | |
MD5:— | SHA256:— | |||
| 1396 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\651d4d13-31ee-4fed-8fbd-f057fcb08295.tmp | — | |
MD5:— | SHA256:— | |||
| 1396 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000046.dbtmp | — | |
MD5:— | SHA256:— | |||
| 1396 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 1396 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\BudgetDatabase\LOG.old | text | |
MD5:— | SHA256:— | |||
| 1396 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF3bbfb7.TMP | text | |
MD5:— | SHA256:— | |||
| 1396 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 1396 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF3bbfc6.TMP | text | |
MD5:— | SHA256:— | |||
| 4092 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:B59113C2DCD2D346F31A64F231162ADA | SHA256:1D97C69AEA85D3B06787458EA47576B192CE5C5DB9940E5EAA514FF977CE2DC2 | |||
| 1396 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:1A89A1BEBE6C843C4FF582E7ED33CA1F | SHA256:65099CA087B66AA8CA420AB121DAAD713E1DB5A61C5A574D9B1C0DF24F012520 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
32
DNS requests
21
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3276 | chrome.exe | GET | 200 | 183.131.207.66:80 | http://ia.51.la/go1?id=1168767&rt=1601469419550&rl=1280*720&lang=en-US&ct=unknow&pf=1&ins=1&vd=1&ce=1&cd=24&ds=%25E6%25B0%25B8%25E4%25B9%2585%25E5%2585%258D%25E8%25B4%25B9%25E6%258F%2590%25E4%25BE%259B%25E5%259B%25BE%25E7%2589%2587%25E4%25B8%258A%25E4%25BC%25A0%25E7%25A9%25BA%25E9%2597%25B4%252C%25E5%258F%25AF%25E5%25A4%2596%25E9%2593%25BE%252C%25E6%2597%25A0%25E9%2599%2590%25E6%25B5%2581%25E9%2587%258F&ing=1&ekc=&sid=1601469419550&tt=%25E5%2585%258D%25E8%25B4%25B9%25E5%259B%25BE%25E7%2589%2587%25E4%25B8%258A%25E4%25BC%25A0%25E7%25A9%25BA%25E9%2597%25B4%252C%25E6%25B7%2598%25E5%25AE%259D%25E5%259B%25BE%25E7%2589%2587%25E4%25B8%258A%25E4%25BC%25A0%25E7%25A9%25BA%25E9%2597%25B4%252C%25E6%2594%25AF%25E6%258C%2581%25E5%25A4%2596%25E9%2593%25BE%2520-%25201990%25E5%259B%25BE%25E7%2589%2587%25E4%25B8%258A%25E4%25BC%25A0%25E7%25BD%2591&kw=%25E5%259B%25BE%25E7%2589%2587%25E4%25B8%258A%25E4%25BC%25A0%252C%25E5%2585%258D%25E8%25B4%25B9%25E5%259B%25BE%25E5%25BA%258A%252C%25E5%25A4%2596%25E9%2593%25BE%25E5%259B%25BE%25E7%2589%2587%252C%25E6%25B7%2598%25E5%25AE%259D%25E5%259B%25BE%25E7%2589%2587%25E7%25A9%25BA%25E9%2597%25B4&cu=http%253A%252F%252Fwww.1990tu.com%252F&pu= | CN | — | — | whitelisted |
3276 | chrome.exe | GET | 200 | 183.131.207.66:80 | http://ia.51.la/go1?id=1168767&rt=1601469440152&rl=1280*720&lang=en-US&ct=unknow&pf=1&ins=0&vd=2&ce=1&cd=24&ds=%25E6%25B0%25B8%25E4%25B9%2585%25E5%2585%258D%25E8%25B4%25B9%25E6%258F%2590%25E4%25BE%259B%25E5%259B%25BE%25E7%2589%2587%25E4%25B8%258A%25E4%25BC%25A0%25E7%25A9%25BA%25E9%2597%25B4%252C%25E5%258F%25AF%25E5%25A4%2596%25E9%2593%25BE%252C%25E6%2597%25A0%25E9%2599%2590%25E6%25B5%2581%25E9%2587%258F&ing=2&ekc=&sid=1601469419550&tt=%25E5%2585%258D%25E8%25B4%25B9%25E5%259B%25BE%25E7%2589%2587%25E4%25B8%258A%25E4%25BC%25A0%25E7%25A9%25BA%25E9%2597%25B4%252C%25E6%25B7%2598%25E5%25AE%259D%25E5%259B%25BE%25E7%2589%2587%25E4%25B8%258A%25E4%25BC%25A0%25E7%25A9%25BA%25E9%2597%25B4%252C%25E6%2594%25AF%25E6%258C%2581%25E5%25A4%2596%25E9%2593%25BE%2520-%25201990%25E5%259B%25BE%25E7%2589%2587%25E4%25B8%258A%25E4%25BC%25A0%25E7%25BD%2591&kw=%25E5%259B%25BE%25E7%2589%2587%25E4%25B8%258A%25E4%25BC%25A0%252C%25E5%2585%258D%25E8%25B4%25B9%25E5%259B%25BE%25E5%25BA%258A%252C%25E5%25A4%2596%25E9%2593%25BE%25E5%259B%25BE%25E7%2589%2587%252C%25E6%25B7%2598%25E5%25AE%259D%25E5%259B%25BE%25E7%2589%2587%25E7%25A9%25BA%25E9%2597%25B4&cu=http%253A%252F%252Fwww.1990tu.com%252F&pu=http%253A%252F%252Fwww.1990tu.com%252F | CN | — | — | whitelisted |
3276 | chrome.exe | GET | 200 | 183.131.207.66:80 | http://ia.51.la/go1?id=1168767&rt=1601469445355&rl=1280*720&lang=en-US&ct=unknow&pf=1&ins=0&vd=3&ce=1&cd=24&ds=%25E6%25B0%25B8%25E4%25B9%2585%25E5%2585%258D%25E8%25B4%25B9%25E6%258F%2590%25E4%25BE%259B%25E5%259B%25BE%25E7%2589%2587%25E4%25B8%258A%25E4%25BC%25A0%25E7%25A9%25BA%25E9%2597%25B4%252C%25E5%258F%25AF%25E5%25A4%2596%25E9%2593%25BE%252C%25E6%2597%25A0%25E9%2599%2590%25E6%25B5%2581%25E9%2587%258F&ing=3&ekc=&sid=1601469419550&tt=%25E5%2585%258D%25E8%25B4%25B9%25E5%259B%25BE%25E7%2589%2587%25E4%25B8%258A%25E4%25BC%25A0%25E7%25A9%25BA%25E9%2597%25B4%252C%25E6%25B7%2598%25E5%25AE%259D%25E5%259B%25BE%25E7%2589%2587%25E4%25B8%258A%25E4%25BC%25A0%25E7%25A9%25BA%25E9%2597%25B4%252C%25E6%2594%25AF%25E6%258C%2581%25E5%25A4%2596%25E9%2593%25BE%2520-%25201990%25E5%259B%25BE%25E7%2589%2587%25E4%25B8%258A%25E4%25BC%25A0%25E7%25BD%2591&kw=%25E5%259B%25BE%25E7%2589%2587%25E4%25B8%258A%25E4%25BC%25A0%252C%25E5%2585%258D%25E8%25B4%25B9%25E5%259B%25BE%25E5%25BA%258A%252C%25E5%25A4%2596%25E9%2593%25BE%25E5%259B%25BE%25E7%2589%2587%252C%25E6%25B7%2598%25E5%25AE%259D%25E5%259B%25BE%25E7%2589%2587%25E7%25A9%25BA%25E9%2597%25B4&cu=http%253A%252F%252Fwww.1990tu.com%252F&pu=http%253A%252F%252Fwww.1990tu.com%252F | CN | — | — | whitelisted |
3276 | chrome.exe | GET | 200 | 115.223.15.254:80 | http://s14.cnzz.com/stat.php?id=867553&web_id=867553 | CN | text | 3.99 Kb | suspicious |
3276 | chrome.exe | GET | 200 | 122.228.91.91:80 | http://js.users.51.la/1168767.js | CN | html | 2.48 Kb | whitelisted |
3276 | chrome.exe | GET | 200 | 115.223.15.254:80 | http://c.cnzz.com/core.php?web_id=867553&t=z | CN | html | 620 b | whitelisted |
3276 | chrome.exe | GET | 200 | 203.119.215.3:80 | http://hzs14.cnzz.com/stat.htm?id=867553&r=http%3A%2F%2Fwww.1990tu.com%2F&lg=en-us&ntime=1601469422&cnzz_eid=854616692-1601469422-&showp=1280x720&p=http%3A%2F%2Fwww.1990tu.com%2F&t=%E5%85%8D%E8%B4%B9%E5%9B%BE%E7%89%87%E4%B8%8A%E4%BC%A0%E7%A9%BA%E9%97%B4%2C%E6%B7%98%E5%AE%9D%E5%9B%BE%E7%89%87%E4%B8%8A%E4%BC%A0%E7%A9%BA%E9%97%B4%2C%E6%94%AF%E6%8C%81%E5%A4%96%E9%93%BE%20-%201990%E5%9B%BE%E7%89%87%E4%B8%8A%E4%BC%A0%E7%BD%91&umuuid=174df041d4d326-0fc4fb11cfccb9-516d3e71-e1000-174df041d50637&h=1&rnd=1899452555 | CN | text | 22 b | suspicious |
3276 | chrome.exe | GET | 200 | 203.119.215.3:80 | http://hzs14.cnzz.com/stat.htm?id=867553&r=&lg=en-us&ntime=none&cnzz_eid=854616692-1601469422-&showp=1280x720&p=http%3A%2F%2Fwww.1990tu.com%2F&t=%E5%85%8D%E8%B4%B9%E5%9B%BE%E7%89%87%E4%B8%8A%E4%BC%A0%E7%A9%BA%E9%97%B4%2C%E6%B7%98%E5%AE%9D%E5%9B%BE%E7%89%87%E4%B8%8A%E4%BC%A0%E7%A9%BA%E9%97%B4%2C%E6%94%AF%E6%8C%81%E5%A4%96%E9%93%BE%20-%201990%E5%9B%BE%E7%89%87%E4%B8%8A%E4%BC%A0%E7%BD%91&umuuid=174df041d4d326-0fc4fb11cfccb9-516d3e71-e1000-174df041d50637&h=1&rnd=381635700 | CN | text | 22 b | suspicious |
3276 | chrome.exe | GET | 200 | 203.119.215.3:80 | http://hzs14.cnzz.com/stat.htm?id=867553&r=http%3A%2F%2Fwww.1990tu.com%2F&lg=en-us&ntime=1601469422&cnzz_eid=854616692-1601469422-&showp=1280x720&p=http%3A%2F%2Fwww.1990tu.com%2F&t=%E5%85%8D%E8%B4%B9%E5%9B%BE%E7%89%87%E4%B8%8A%E4%BC%A0%E7%A9%BA%E9%97%B4%2C%E6%B7%98%E5%AE%9D%E5%9B%BE%E7%89%87%E4%B8%8A%E4%BC%A0%E7%A9%BA%E9%97%B4%2C%E6%94%AF%E6%8C%81%E5%A4%96%E9%93%BE%20-%201990%E5%9B%BE%E7%89%87%E4%B8%8A%E4%BC%A0%E7%BD%91&umuuid=174df041d4d326-0fc4fb11cfccb9-516d3e71-e1000-174df041d50637&h=1&rnd=1564487049 | CN | text | 22 b | suspicious |
3276 | chrome.exe | GET | 302 | 205.204.101.182:80 | http://cnzz.mmstat.com/9.gif?abc=1&rnd=1036126642 | US | image | 43 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3276 | chrome.exe | 142.250.74.195:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3276 | chrome.exe | 104.31.12.161:80 | www.1990tu.com | Cloudflare Inc | US | unknown |
3276 | chrome.exe | 122.228.91.91:80 | js.users.51.la | CHINANET Sichuan province Chengdu MAN network | CN | unknown |
3276 | chrome.exe | 115.223.15.254:80 | s14.cnzz.com | No.31,Jin-rong Street | CN | unknown |
3276 | chrome.exe | 183.131.207.66:80 | ia.51.la | DaLi | CN | malicious |
3276 | chrome.exe | 104.31.13.161:80 | www.1990tu.com | Cloudflare Inc | US | unknown |
3276 | chrome.exe | 172.217.16.202:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
3276 | chrome.exe | 216.58.207.46:443 | ogs.google.com | Google Inc. | US | whitelisted |
3276 | chrome.exe | 172.217.22.98:443 | adservice.google.com | Google Inc. | US | whitelisted |
3276 | chrome.exe | 172.217.22.110:443 | clients1.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.1990tu.com |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
js.users.51.la |
| whitelisted |
s14.cnzz.com |
| suspicious |
ia.51.la |
| whitelisted |
www.51.la |
| suspicious |
c.cnzz.com |
| whitelisted |
hzs14.cnzz.com |
| suspicious |
cnzz.mmstat.com |
| whitelisted |