| File name: | sample_54.exe |
| Full analysis: | https://app.any.run/tasks/213607c6-048f-43ee-958c-f6adb156e6ea |
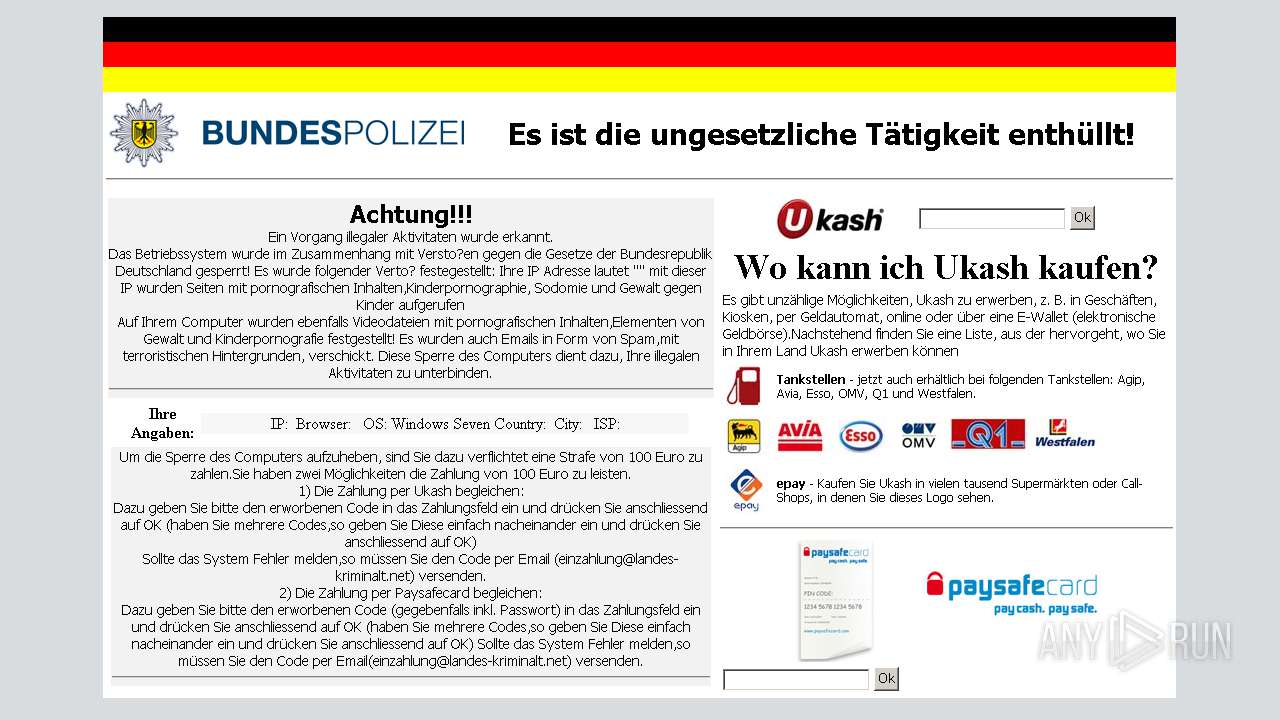
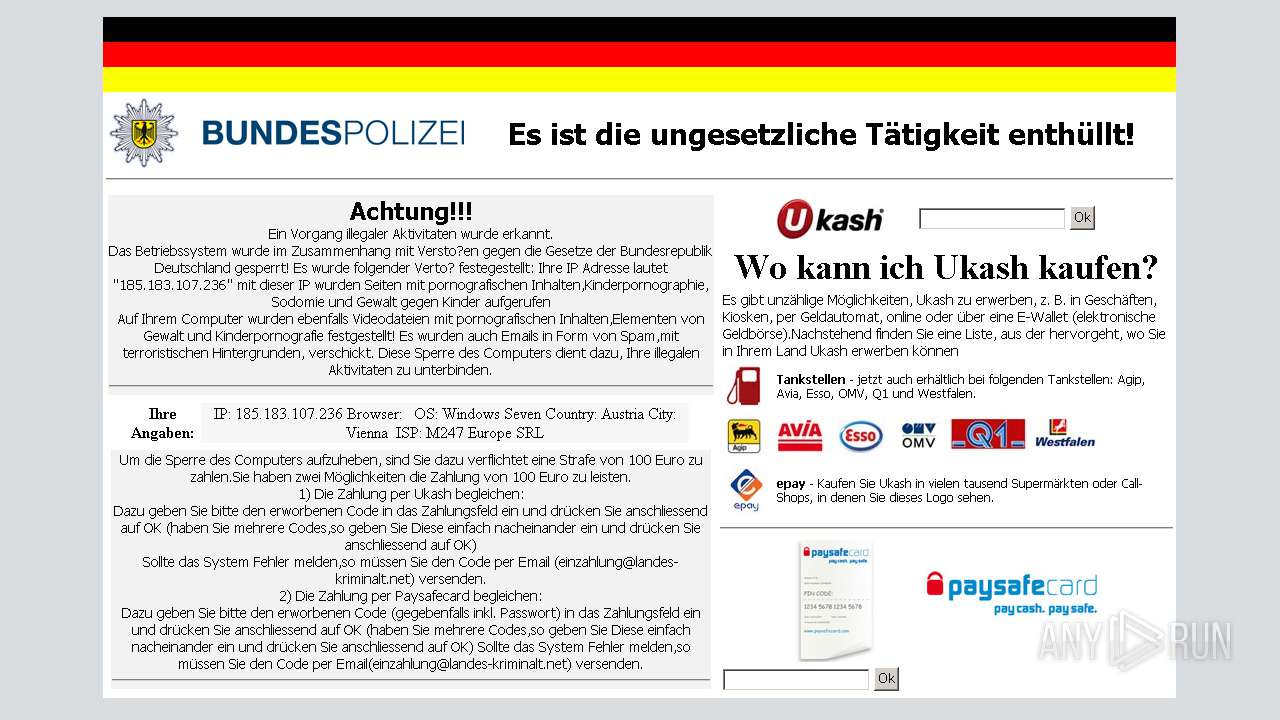
| Verdict: | Malicious activity |
| Analysis date: | June 12, 2019, 07:21:26 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, UPX compressed |
| MD5: | FDE9986FE61AE7CE1D477C510D0B671E |
| SHA1: | A6859895B070C54E964C716E2E6D5E11DDE99509 |
| SHA256: | DC4A9B1AB1FEDDF13EF3AA0AA181D903014256D365BA93390C7B367D4B436B7E |
| SSDEEP: | 3072:jpHy7Nr7MpCGbgqzOFr0FcgSfhsMtmrucAmOn5+7Z68bVaFnZQIQT5MKairkMYzP:jJy7hoHzOJ0qgSf2prucDO5+cFZncMdg |
MALICIOUS
Changes the autorun value in the registry
- mahmud.exe (PID: 3204)
SUSPICIOUS
Executable content was dropped or overwritten
- sample_54.exe (PID: 572)
Creates files in the user directory
- sample_54.exe (PID: 572)
Starts CMD.EXE for commands execution
- sample_54.exe (PID: 572)
Checks for external IP
- mahmud.exe (PID: 3204)
Reads internet explorer settings
- mahmud.exe (PID: 3204)
Starts itself from another location
- sample_54.exe (PID: 572)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | UPX compressed Win32 Executable (39.3) |
|---|---|---|
| .exe | | | Win32 EXE Yoda's Crypter (38.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (9.5) |
| .exe | | | Win32 Executable (generic) (6.5) |
| .exe | | | Generic Win/DOS Executable (2.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:04:07 05:20:29+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 7.3 |
| CodeSize: | 180224 |
| InitializedDataSize: | 8192 |
| UninitializedDataSize: | 57344 |
| EntryPoint: | 0x3a650 |
| OSVersion: | 10.3 |
| ImageVersion: | 7.2 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 7.8.0.0 |
| ProductVersionNumber: | 7.8.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | NEC Computers International |
| FileDescription: | Riggs Sub Faint Force |
| FileVersion: | 7.8 |
| InternalName: | Okay Wow Don |
| LegalCopyright: | Botch Muses © Chit Her 1995-2010 |
| OriginalFileName: | Radish.exe |
| ProductName: | Wrap Inc Loyal |
| ProductVersion: | 7.8 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Apr-2011 03:20:29 |
| Detected languages: |
|
| CompanyName: | NEC Computers International |
| FileDescription: | Riggs Sub Faint Force |
| FileVersion: | 7.8 |
| InternalName: | Okay Wow Don |
| LegalCopyright: | Botch Muses © Chit Her 1995-2010 |
| OriginalFilename: | Radish.exe |
| ProductName: | Wrap Inc Loyal |
| ProductVersion: | 7.8 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000F0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 3 |
| Time date stamp: | 07-Apr-2011 03:20:29 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
UPX0 | 0x00001000 | 0x0000E000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
UPX1 | 0x0000F000 | 0x0002C000 | 0x0002B800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.95363 |
.rsrc | 0x0003B000 | 0x00002000 | 0x00001C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.6192 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.52878 | 1617 | UNKNOWN | English - United States | RT_MANIFEST |
1012 | 3.64022 | 15 | UNKNOWN | English - United States | RT_STRING |
1017 | 3.32193 | 10 | UNKNOWN | English - United States | RT_DIALOG |
1027 | 7.55696 | 597 | UNKNOWN | English - United States | UNKNOWN |
1047 | 3.875 | 16 | UNKNOWN | English - United States | UNKNOWN |
1048 | 3.58496 | 12 | UNKNOWN | English - United States | RT_STRING |
1051 | 3.80735 | 14 | UNKNOWN | English - United States | UNKNOWN |
1065 | 3.70044 | 13 | UNKNOWN | English - United States | UNKNOWN |
1068 | 3.96982 | 17 | UNKNOWN | English - United States | RT_STRING |
1082 | 3.9477 | 18 | UNKNOWN | English - United States | UNKNOWN |
Imports
KERNEL32.DLL |
advapi32.dll |
comctl32.dll |
gdi32.dll |
msvcrt.dll |
shell32.dll |
user32.dll |
winmm.dll |
Total processes
35
Monitored processes
3
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 572 | "C:\Users\admin\AppData\Local\Temp\sample_54.exe" | C:\Users\admin\AppData\Local\Temp\sample_54.exe | explorer.exe | ||||||||||||
User: admin Company: NEC Computers International Integrity Level: MEDIUM Description: Riggs Sub Faint Force Exit code: 0 Version: 7.8 Modules
| |||||||||||||||
| 3204 | "C:\Users\admin\AppData\Roaming\mahmud.exe" | C:\Users\admin\AppData\Roaming\mahmud.exe | sample_54.exe | ||||||||||||
User: admin Company: NEC Computers International Integrity Level: MEDIUM Description: Riggs Sub Faint Force Exit code: 0 Version: 7.8 Modules
| |||||||||||||||
| 3388 | "C:\Windows\system32\cmd.exe" /c "for /L %i in (0,1,100000000) do (del "C:\Users\admin\AppData\Local\Temp\sample_54.exe" && if not exist "C:\Users\admin\AppData\Local\Temp\sample_54.exe" exit 1)" | C:\Windows\system32\cmd.exe | — | sample_54.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
436
Read events
413
Write events
23
Delete events
0
Modification events
| (PID) Process: | (572) sample_54.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (572) sample_54.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3204) mahmud.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mahmud_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3204) mahmud.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mahmud_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (3204) mahmud.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mahmud_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3204) mahmud.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mahmud_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (3204) mahmud.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mahmud_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (3204) mahmud.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mahmud_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (3204) mahmud.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mahmud_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (3204) mahmud.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\mahmud_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
1
Suspicious files
0
Text files
7
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3204 | mahmud.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\ib2[1].txt | — | |
MD5:— | SHA256:— | |||
| 3204 | mahmud.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\main[1] | html | |
MD5:1AA4A8102F15E0EBB42DCC4A0BC81ACD | SHA256:136460859AFE66D6CBBEE4430B5661B52C690650B4415D5B8840E372A36CF974 | |||
| 3204 | mahmud.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\bpol_logo[1] | image | |
MD5:737A56206E245CC6E9DB01AA7E6DB088 | SHA256:43A747CE7AF8BBE3279E34FC90CED4F887DC99B39A8185BE142D6278D25DD62F | |||
| 572 | sample_54.exe | C:\Users\admin\AppData\Roaming\mahmud.exe | executable | |
MD5:FDE9986FE61AE7CE1D477C510D0B671E | SHA256:DC4A9B1AB1FEDDF13EF3AA0AA181D903014256D365BA93390C7B367D4B436B7E | |||
| 3204 | mahmud.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\ukash[1] | image | |
MD5:5C0DDE9B26AA79F81F848BDDC37CE473 | SHA256:7F5E254DD2ED4C447ADD6863E547DB0D40E9E912DCBFA9D81CBDF0443A193652 | |||
| 3204 | mahmud.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\pay[1] | image | |
MD5:527A37488396E62995F76CF3487F8985 | SHA256:04FAC3F2D0743E0045F813AC49A207777268804BFADC0BA1DC15911C3292DF69 | |||
| 3204 | mahmud.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\petrol[1] | image | |
MD5:E4E138DFC37B550ECBE1E0F5E87BCF4C | SHA256:AC32FC9FFDA439FAC9AB3F50EE2C7197B427E171450250CBF83F78CFF5DE93AD | |||
| 3204 | mahmud.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\petrolstations[1] | image | |
MD5:DB956606BC0B1FC2DF846145C9540A6D | SHA256:599B7E358B2935EF7655F243BD6740867D2D0F4281ECC46505868045A4CD2948 | |||
| 3204 | mahmud.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\paysafe[1] | image | |
MD5:6567A5122FE1275B1AEEA76059B7501C | SHA256:FEFCB747EB01FB2C6F49666DC35E5A641C628F120C3EA2052975E30F707140E8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
1
DNS requests
2
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3204 | mahmud.exe | GET | 200 | 108.61.217.56:80 | http://tools.ip2location.com/ib2/ | US | html | 631 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3204 | mahmud.exe | 108.61.217.56:80 | tools.ip2location.com | Choopa, LLC | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
annner2y.com |
| unknown |
tools.ip2location.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3204 | mahmud.exe | Potential Corporate Privacy Violation | ET POLICY External IP Lookup - ip2location.com |
3204 | mahmud.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
1 ETPRO signatures available at the full report