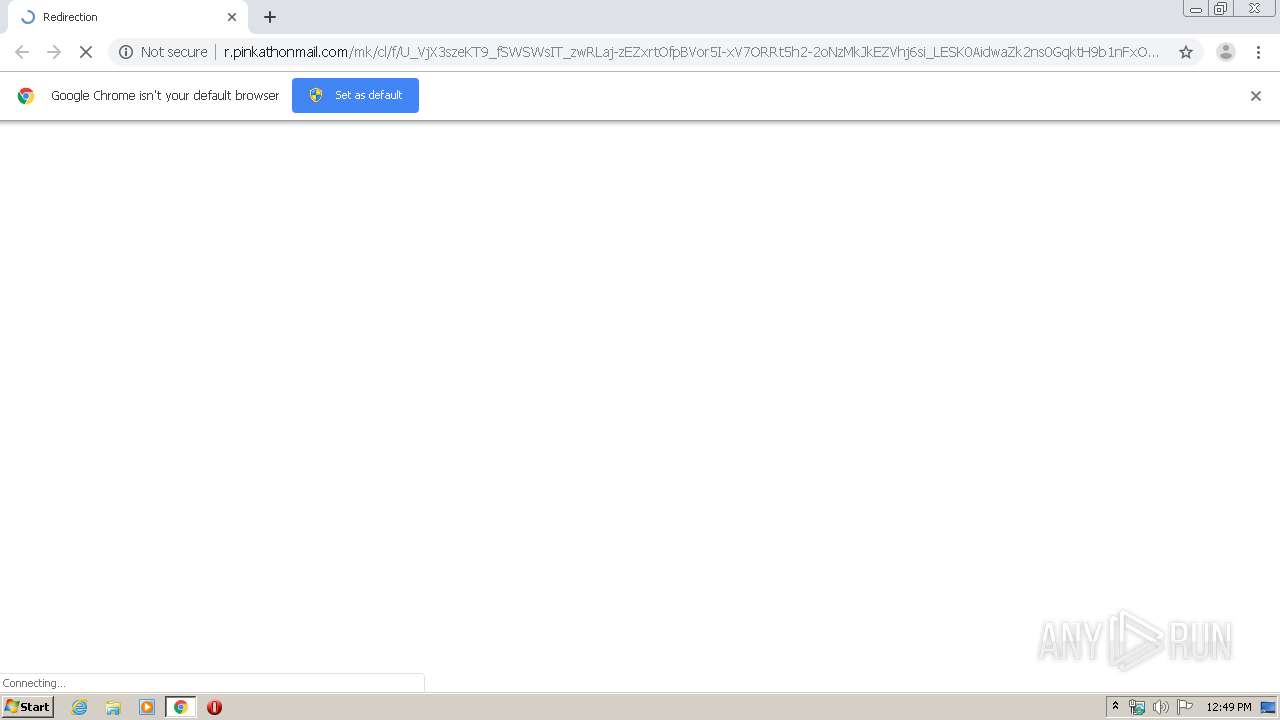
| URL: | http://r.pinkathonmail.com/mk/cl/f/U_VjX3szeKT9_fSWSWsIT_zwRLaj-zEZxrtOfpBVor5I-xV7ORRt5h2-2oNzMkJkEZVhj6si_LESK0AidwaZk2ns0GqktH9b1nFxOGno7O5H7_i9MwWxK2E_ECevprNRr8lS5_JLStu6hf9Jj2ZDWPYiAV4yhqnQ4ltpYVtMOgnSsyIUfw |
| Full analysis: | https://app.any.run/tasks/ec44b0aa-9093-4c0d-ada0-929bf43df157 |
| Verdict: | Malicious activity |
| Analysis date: | March 31, 2020, 11:48:53 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 3EE707E4E11BD5F7449526167549B11D |
| SHA1: | 3884C310075C9BDDD2F80DDBFCF88567E36D5689 |
| SHA256: | DC45F2EF178B01000447B8EE96719FE501A44819946C552327F9187F489035FE |
| SSDEEP: | 6:CMLf22KI4YcgZD/MNVzzS28XyyUk9MI5mRFROI:Zr22DZDmVzb8Xy3qMI5Ox |
MALICIOUS
No malicious indicators.SUSPICIOUS
Modifies files in Chrome extension folder
- chrome.exe (PID: 3096)
INFO
Reads the hosts file
- chrome.exe (PID: 3452)
- chrome.exe (PID: 3096)
Application launched itself
- chrome.exe (PID: 3096)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
63
Monitored processes
28
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 332 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1004,13122921986071910869,16698460852706446142,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=13293483626394939805 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1232 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1116 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,13122921986071910869,16698460852706446142,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5667284517980590048 --mojo-platform-channel-handle=4204 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,13122921986071910869,16698460852706446142,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4772436858597655750 --mojo-platform-channel-handle=4028 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1812 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,13122921986071910869,16698460852706446142,131072 --enable-features=PasswordImport --disable-gpu-sandbox --use-gl=disabled --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=1531389998791834944 --mojo-platform-channel-handle=3116 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,13122921986071910869,16698460852706446142,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=17255476697029765354 --mojo-platform-channel-handle=2832 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2056 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,13122921986071910869,16698460852706446142,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=10445030153835768672 --mojo-platform-channel-handle=3756 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2108 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,13122921986071910869,16698460852706446142,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=5069168932986491712 --mojo-platform-channel-handle=2604 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,13122921986071910869,16698460852706446142,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=15659686859374578672 --mojo-platform-channel-handle=4248 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2592 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1004,13122921986071910869,16698460852706446142,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=16200115700823862254 --mojo-platform-channel-handle=2708 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1004,13122921986071910869,16698460852706446142,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=5441031730174990297 --mojo-platform-channel-handle=1012 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
616
Read events
517
Write events
93
Delete events
6
Modification events
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2872) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 3096-13230128954506750 |
Value: 259 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3120-13213713943555664 |
Value: 0 | |||
| (PID) Process: | (3096) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
78
Text files
261
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E832E3B-C18.pma | — | |
MD5:— | SHA256:— | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ed2b40a3-12d5-417d-888a-824046be3829.tmp | — | |
MD5:— | SHA256:— | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000028.dbtmp | — | |
MD5:— | SHA256:— | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\AvailabilityDB\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFa67a58.TMP | text | |
MD5:— | SHA256:— | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\metadata\LOG.old | text | |
MD5:— | SHA256:— | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3096 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RFa67caa.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
75
TCP/UDP connections
34
DNS requests
20
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
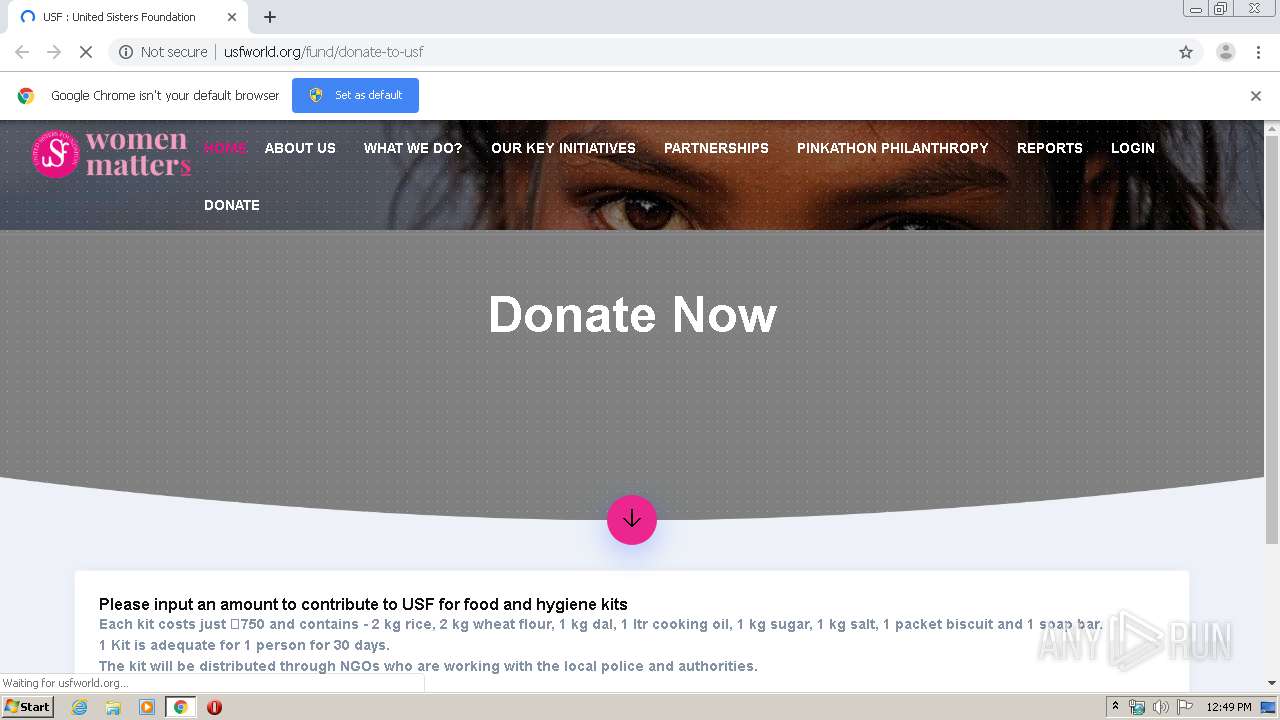
3452 | chrome.exe | GET | 200 | 148.72.201.193:80 | http://usfworld.org/fund/assets/css/typography.css | US | text | 3.84 Kb | suspicious |
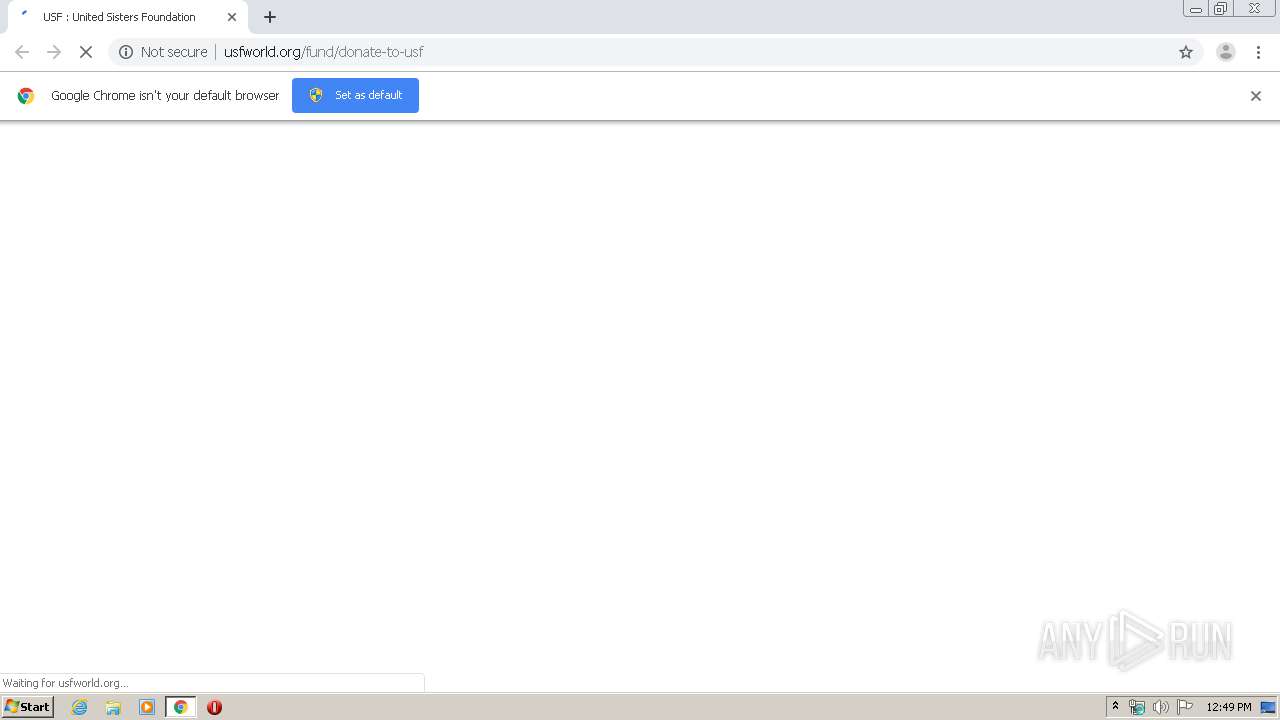
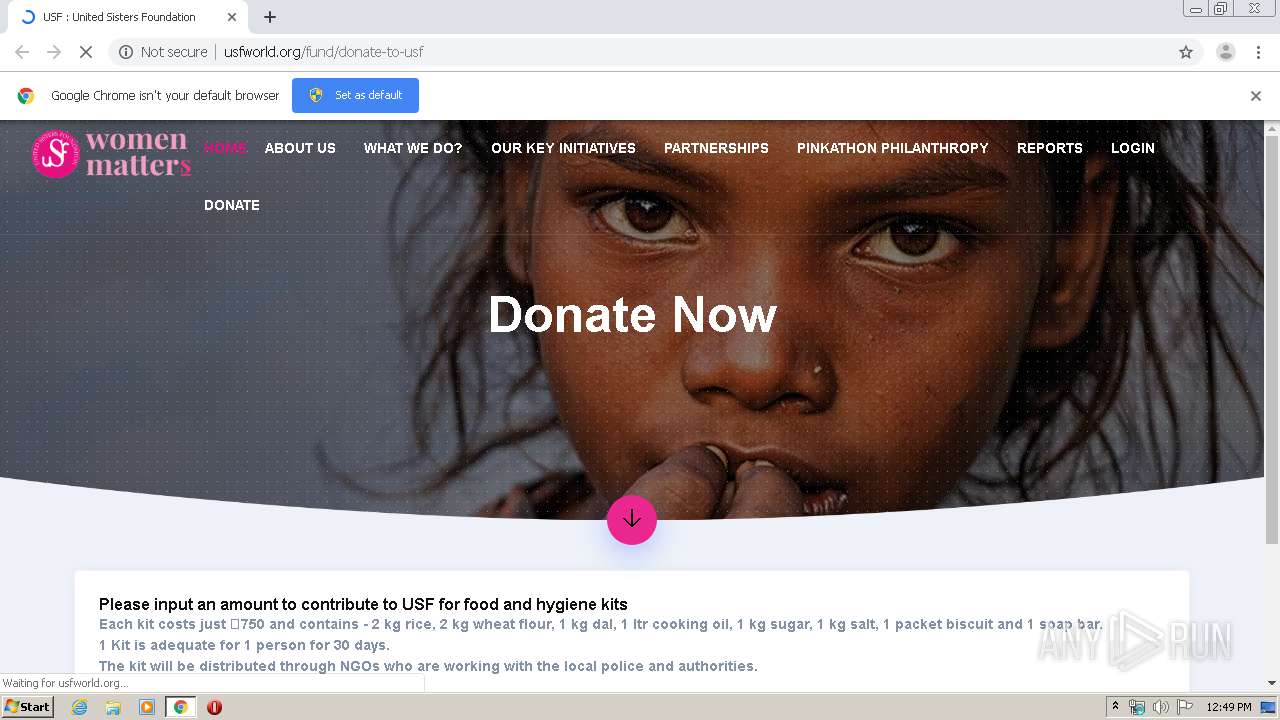
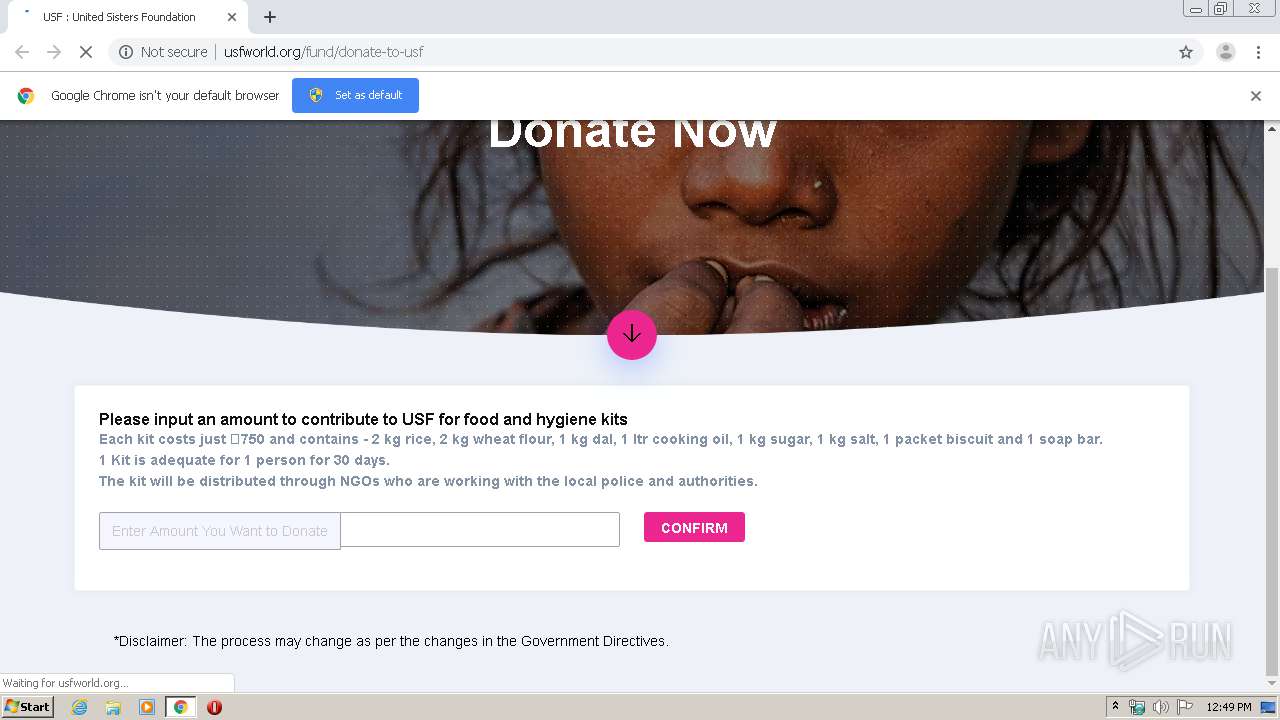
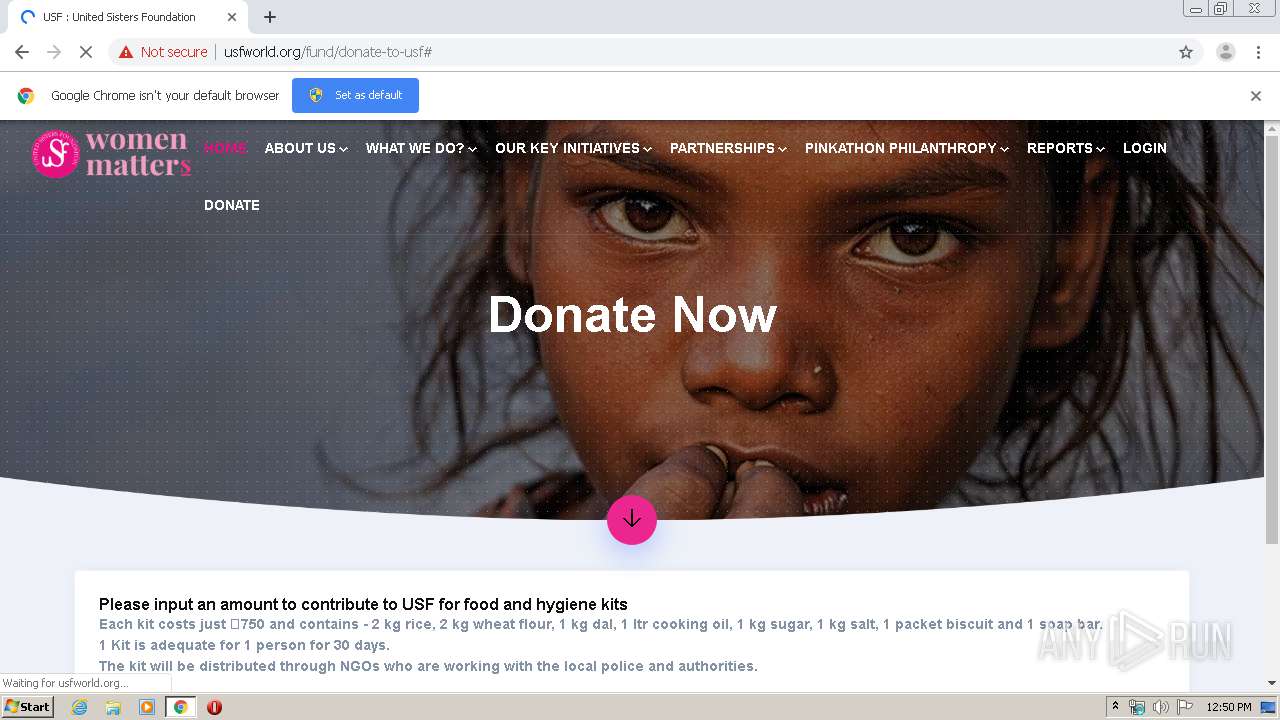
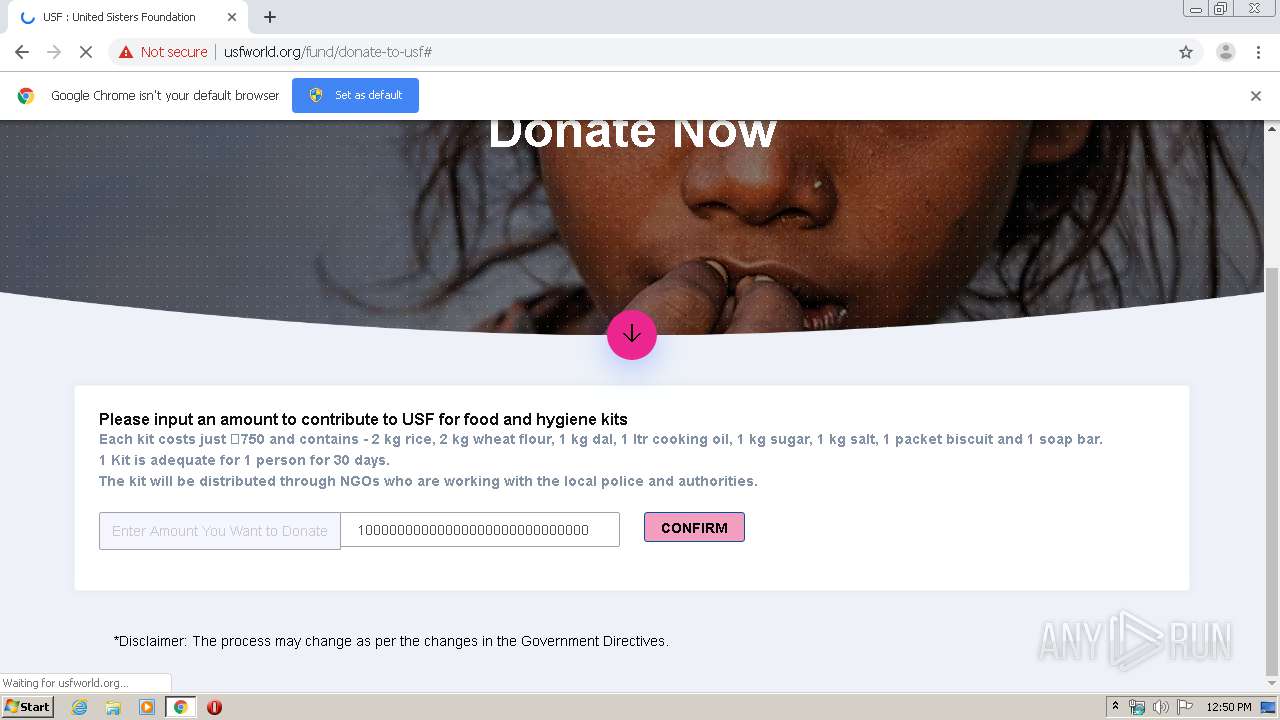
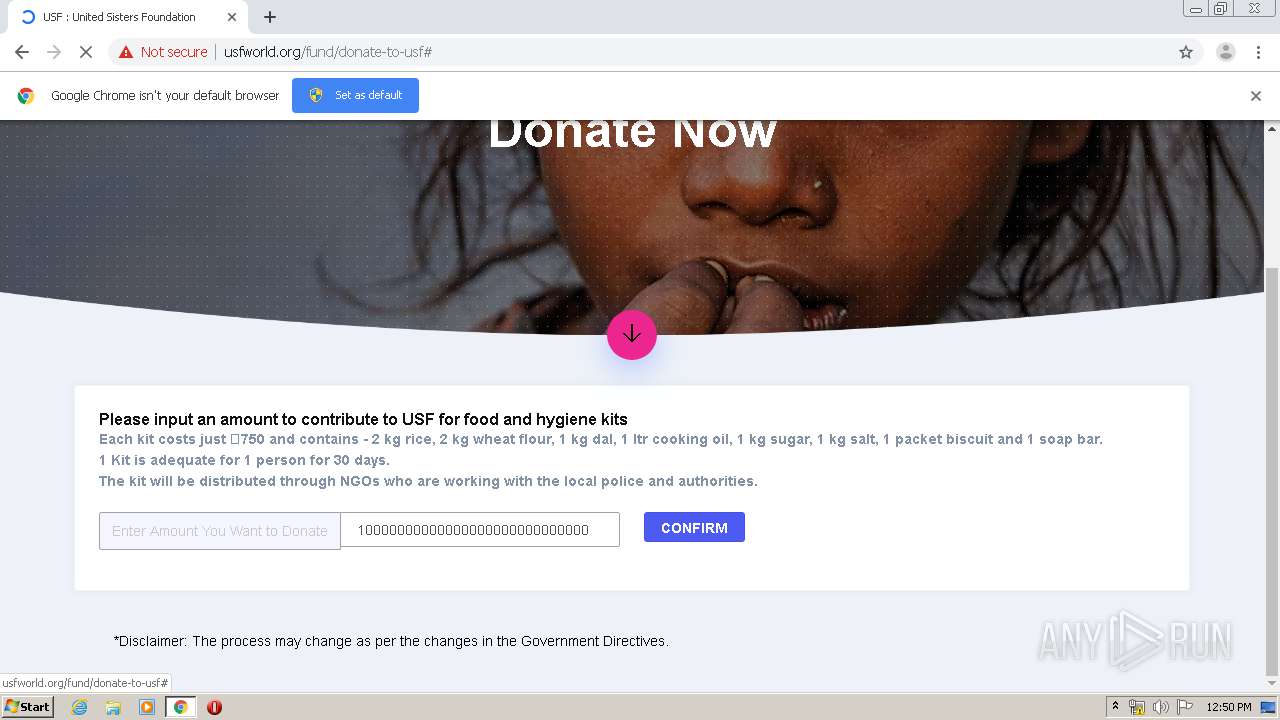
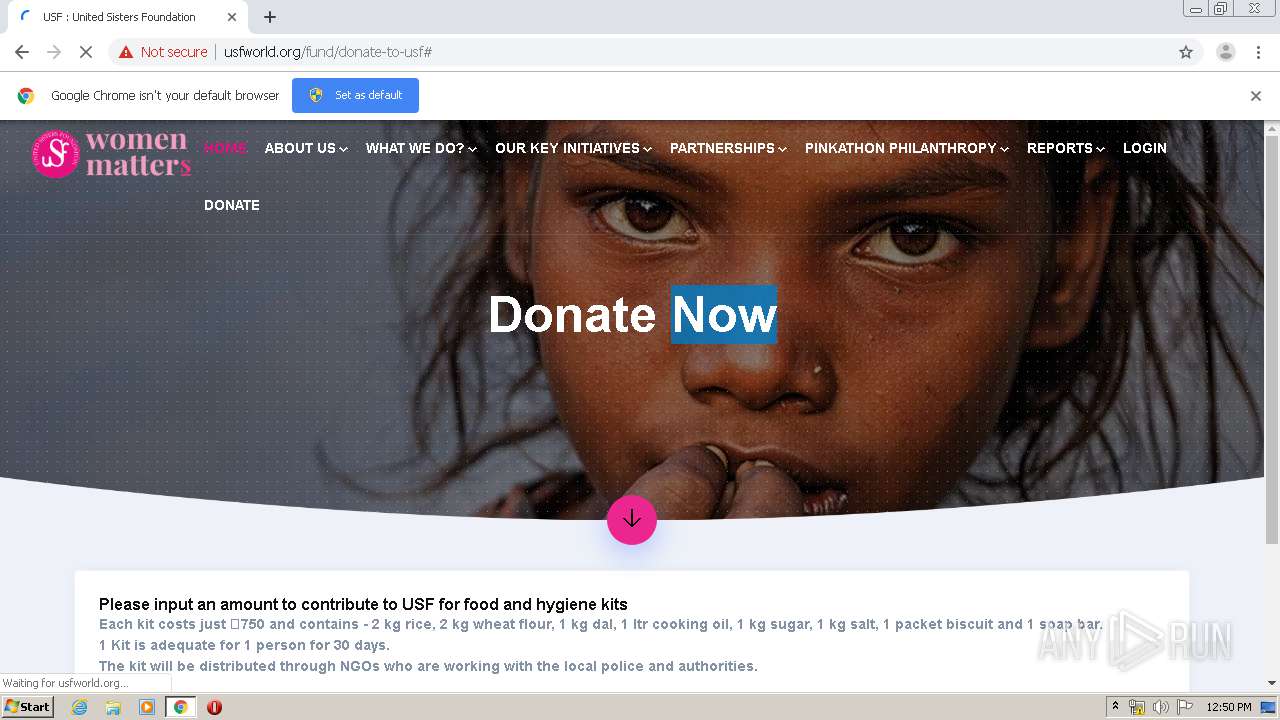
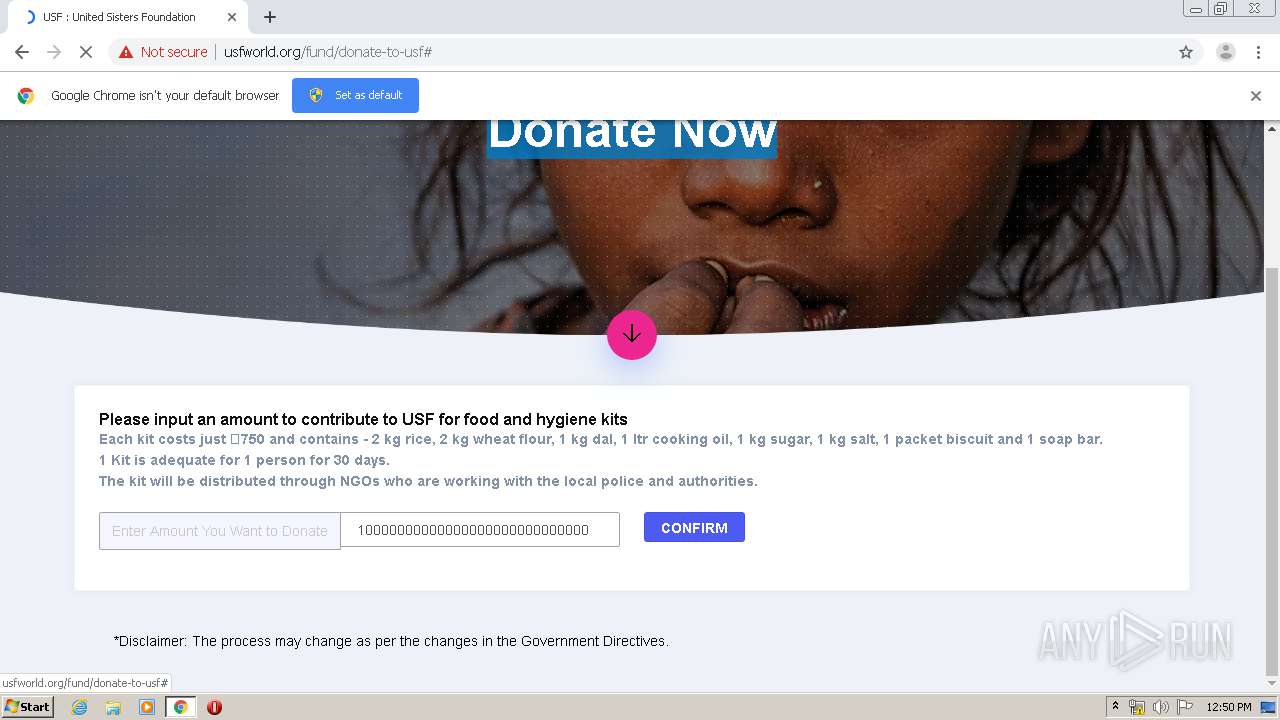
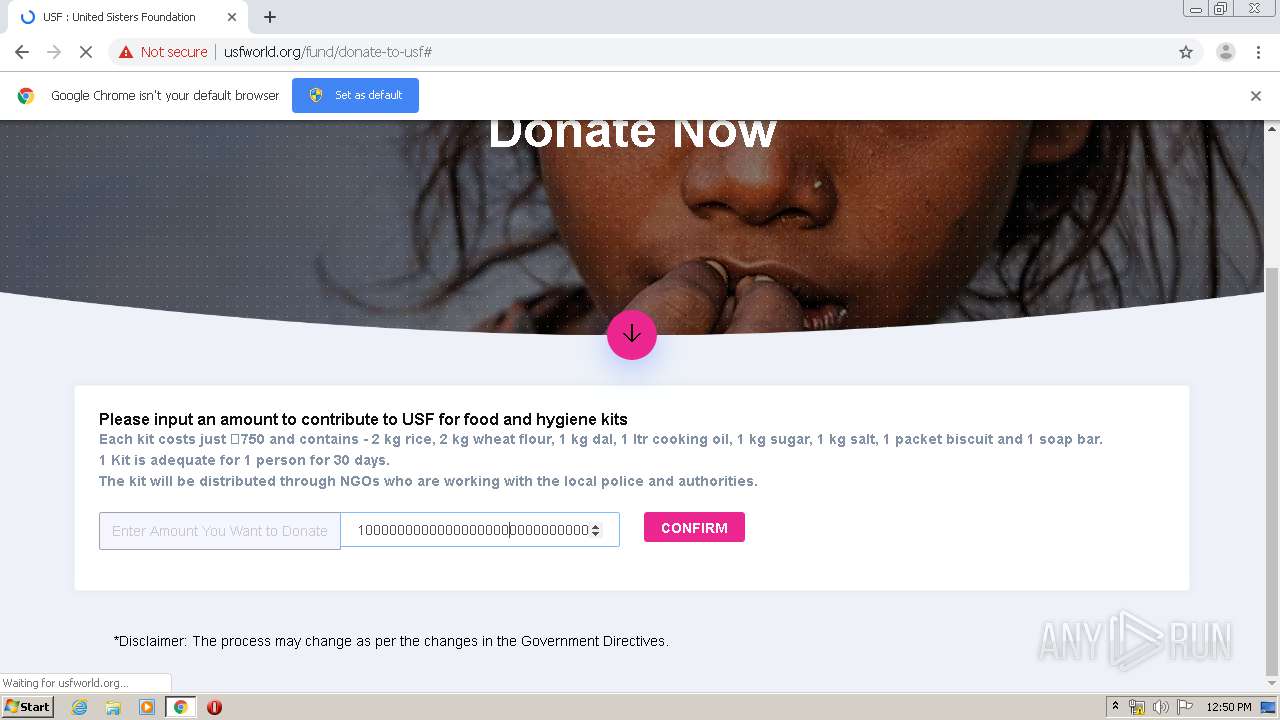
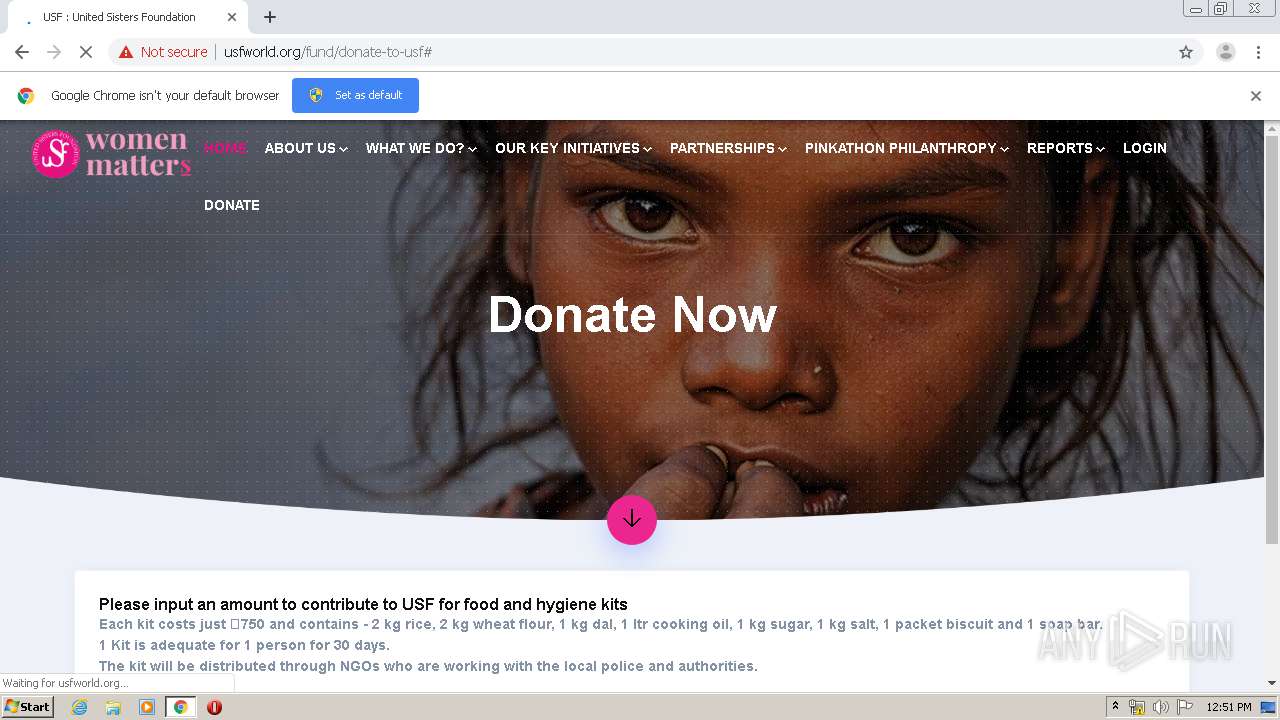
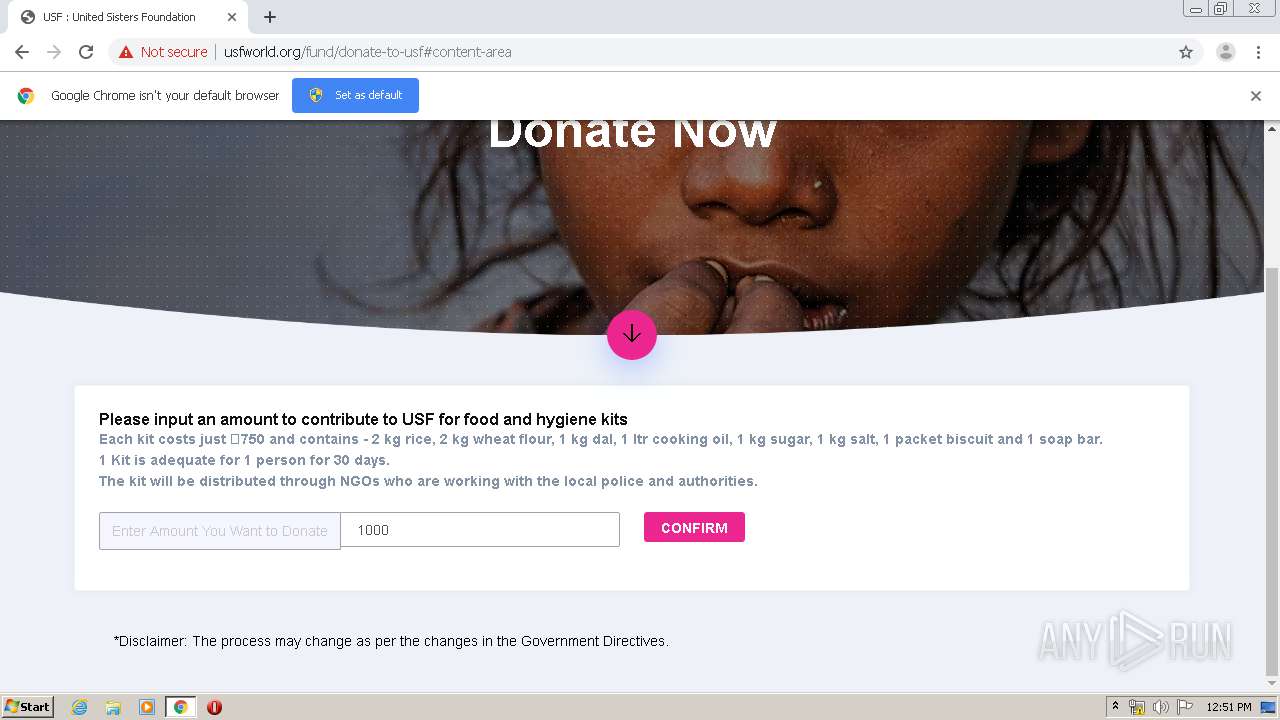
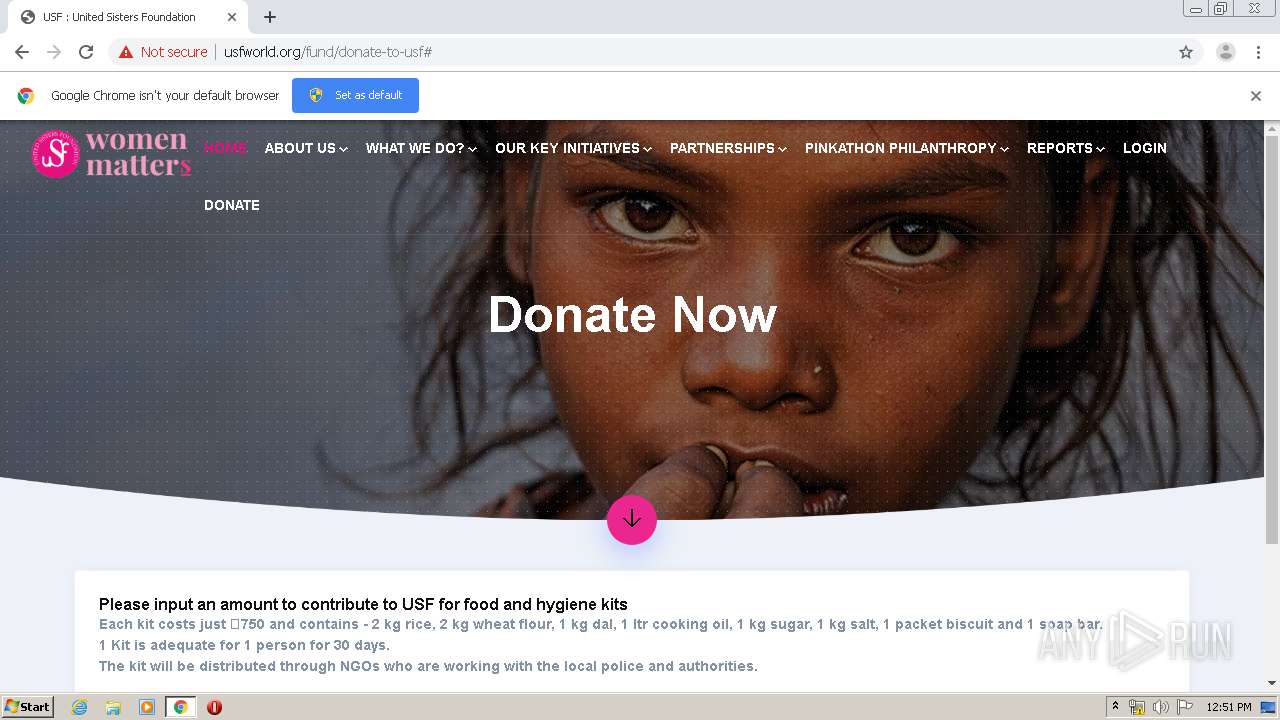
3452 | chrome.exe | GET | 200 | 148.72.201.193:80 | http://usfworld.org/fund/donate-to-usf | US | html | 5.41 Kb | suspicious |
3452 | chrome.exe | GET | 200 | 104.16.232.163:80 | http://r.pinkathonmail.com/mk/cl/f/U_VjX3szeKT9_fSWSWsIT_zwRLaj-zEZxrtOfpBVor5I-xV7ORRt5h2-2oNzMkJkEZVhj6si_LESK0AidwaZk2ns0GqktH9b1nFxOGno7O5H7_i9MwWxK2E_ECevprNRr8lS5_JLStu6hf9Jj2ZDWPYiAV4yhqnQ4ltpYVtMOgnSsyIUfw | US | html | 391 b | suspicious |
3452 | chrome.exe | GET | 200 | 148.72.201.193:80 | http://usfworld.org/fund/assets/css/assets.css | US | text | 200 b | suspicious |
3452 | chrome.exe | GET | 200 | 148.72.201.193:80 | http://usfworld.org/fund/assets/css/color/color-1.css | US | text | 1.18 Kb | suspicious |
3452 | chrome.exe | GET | 200 | 148.72.201.193:80 | http://usfworld.org/fund/assets/css/style.css | US | text | 28.2 Kb | suspicious |
3452 | chrome.exe | GET | 302 | 172.217.16.206:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvOTRmQUFXVHlhaGJaUTdMLWtCSkNJUl9ZQQ/1.0.0.5_nmmhkkegccagdldgiimedpiccmgmieda.crx | US | html | 518 b | whitelisted |
3452 | chrome.exe | GET | 200 | 148.72.201.193:80 | http://usfworld.org/fund/assets/vendors/jquery-steps/jquery.steps.css | US | text | 1.23 Kb | suspicious |
3452 | chrome.exe | GET | 200 | 148.72.201.193:80 | http://usfworld.org/fund/assets/vendors/scroll/scrollbar.css | US | text | 405 b | suspicious |
3452 | chrome.exe | GET | 200 | 148.72.201.193:80 | http://usfworld.org/fund/assets/css/shortcodes/shortcodes.css | US | text | 148 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3452 | chrome.exe | 104.16.232.163:80 | r.pinkathonmail.com | Cloudflare Inc | US | shared |
3452 | chrome.exe | 216.58.208.35:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3452 | chrome.exe | 172.217.22.45:443 | accounts.google.com | Google Inc. | US | whitelisted |
3452 | chrome.exe | 104.28.5.90:443 | sibautomation.com | Cloudflare Inc | US | unknown |
3452 | chrome.exe | 185.107.232.249:443 | in-automate.sendinblue.com | Sendinblue SAS | FR | unknown |
3452 | chrome.exe | 148.72.201.193:80 | usfworld.org | — | US | suspicious |
3452 | chrome.exe | 216.58.206.14:443 | clients2.google.com | Google Inc. | US | whitelisted |
3452 | chrome.exe | 172.217.16.206:80 | redirector.gvt1.com | Google Inc. | US | whitelisted |
3452 | chrome.exe | 216.58.207.36:443 | www.google.com | Google Inc. | US | whitelisted |
3452 | chrome.exe | 172.217.16.161:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
clientservices.googleapis.com |
| whitelisted |
r.pinkathonmail.com |
| suspicious |
accounts.google.com |
| shared |
sibautomation.com |
| whitelisted |
in-automate.sendinblue.com |
| whitelisted |
usfworld.org |
| suspicious |
clients2.google.com |
| whitelisted |
redirector.gvt1.com |
| whitelisted |
r1---sn-4g5ednle.gvt1.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
3452 | chrome.exe | Potentially Bad Traffic | ET HUNTING Suspicious GET Request with Possible COVID-19 URI M1 |