| File name: | Contract_6588.doc |
| Full analysis: | https://app.any.run/tasks/580aa295-111c-4123-957a-ed6c325b0b7f |
| Verdict: | Malicious activity |
| Analysis date: | November 13, 2020, 12:37:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 1252, Author: User, Template: Normal.dotm, Last Saved By: kirin, Revision Number: 7, Name of Creating Application: Microsoft Office Word, Total Editing Time: 20:00, Create Time/Date: Sun May 10 01:31:00 2020, Last Saved Time/Date: Wed Oct 28 04:44:00 2020, Number of Pages: 2, Number of Words: 89482, Number of Characters: 510049, Security: 0 |
| MD5: | 7DBD8ECFADA1D39A81A58C9468B91039 |
| SHA1: | 0D21E2742204D1F98F6FCABE0544570FD6857DD3 |
| SHA256: | DC40E48D2EB0E57CD16B1792BDCCC185440F632783C7BCC87C955E1D4E88FC95 |
| SSDEEP: | 12288:emkTbAui+yjlKtAMgWffRtpqgnydr6YqVPCspBZZLFLIx/mBDOq1a:emkvVW9gnyQxtN9eEBDOQa |
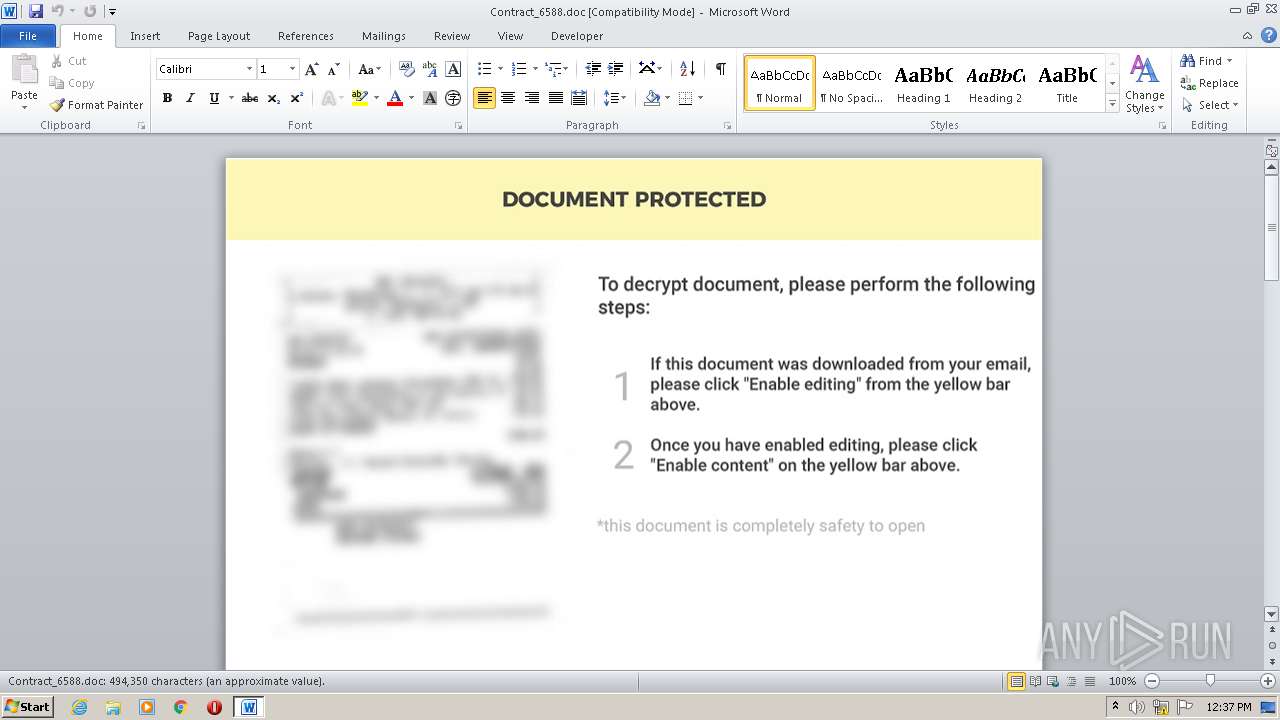
MALICIOUS
Loads dropped or rewritten executable
- Rundll32.exe (PID: 1656)
Application was dropped or rewritten from another process
- tmp_e473b4.exe (PID: 2576)
SUSPICIOUS
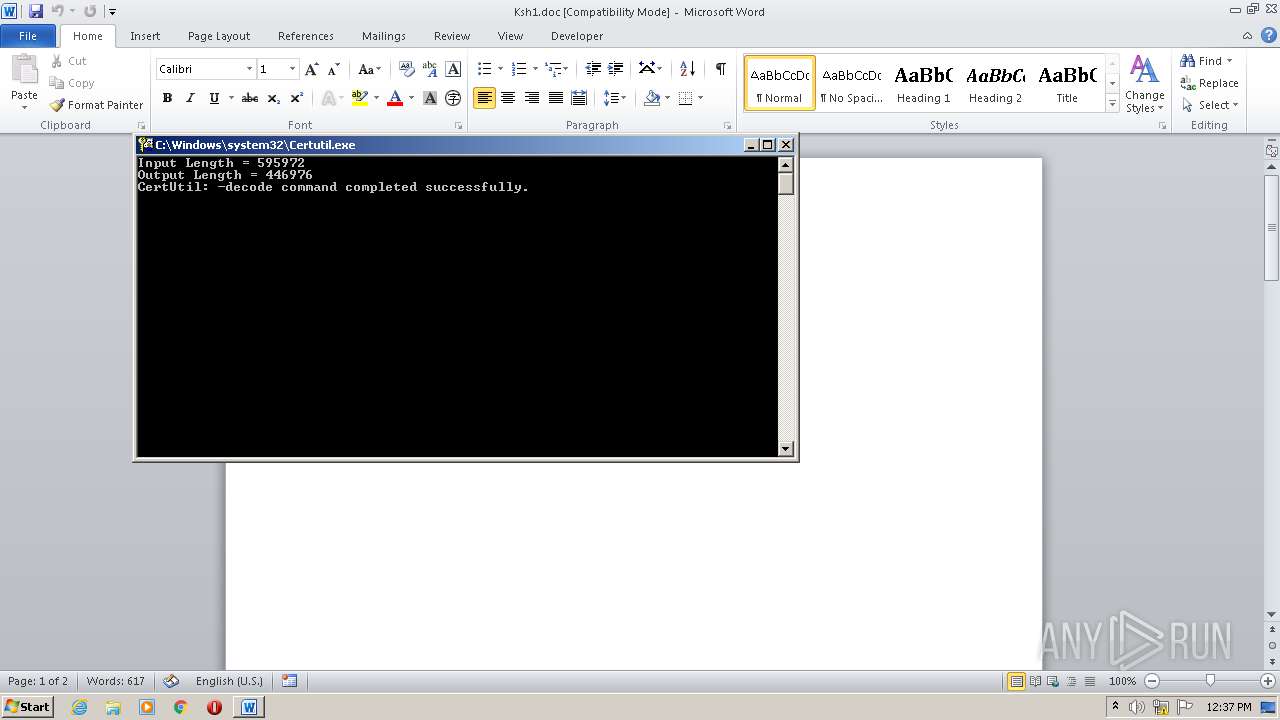
Executed via WMI
- Certutil.exe (PID: 464)
- Rundll32.exe (PID: 1656)
Executable content was dropped or overwritten
- Certutil.exe (PID: 464)
- Rundll32.exe (PID: 1656)
Creates files in the user directory
- Rundll32.exe (PID: 1656)
Reads Internet Cache Settings
- Rundll32.exe (PID: 1656)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2840)
Creates files in the user directory
- WINWORD.EXE (PID: 2840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | - |
|---|---|
| Subject: | - |
| Author: | User |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| LastModifiedBy: | kirin |
| RevisionNumber: | 7 |
| Software: | Microsoft Office Word |
| TotalEditTime: | 20.0 minutes |
| CreateDate: | 2020:05:10 00:31:00 |
| ModifyDate: | 2020:10:28 04:44:00 |
| Pages: | 2 |
| Words: | 89482 |
| Characters: | 510049 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | - |
| Lines: | 4250 |
| Paragraphs: | 1196 |
| CharCountWithSpaces: | 598335 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
41
Monitored processes
4
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 464 | Certutil -decode C:\Users\Public\Ksh1.xls C:\Users\Public\Ksh1.pdf | C:\Windows\system32\Certutil.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: CertUtil.exe Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1656 | Rundll32 C:\Users\Public\Ksh1.pdf,In | C:\Windows\system32\Rundll32.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2576 | C:\Users\admin\AppData\Local\Temp/tmp_e473b4.exe | C:\Users\admin\AppData\Local\Temp\tmp_e473b4.exe | — | Rundll32.exe | |||||||||||
User: admin Company: Twenty Squares Integrity Level: MEDIUM Description: Addictedsarah chaturbate iree token Exit code: 0 Version: 1.00 Modules
| |||||||||||||||
| 2840 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Contract_6588.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
1 530
Read events
1 100
Write events
235
Delete events
195
Modification events
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | y)3 |
Value: 79293300180B0000010000000000000000000000 | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2840) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
8
Text files
11
Unknown types
14
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR59E9.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0001.doc | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0003.doc | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0002.doc | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\Public\~WRD0000.tmp | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD0005.doc | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD3945.doc | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRD3922.doc | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\Public\~WRD0004.tmp | — | |
MD5:— | SHA256:— | |||
| 2840 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF1DCDC0A70FAA5BA7.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
5
DNS requests
5
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1656 | Rundll32.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEQCTi7COYph7T3X5jLalBFyW | US | der | 728 b | whitelisted |
1656 | Rundll32.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQS14tALDViBvqCf47YkiQRtKz1BAQUpc436uuwdQ6UZ4i0RfrZJBCHlh8CEAjKSzrqHlGx8XC%2FpYpj8LQ%3D | US | der | 279 b | whitelisted |
1656 | Rundll32.exe | GET | 200 | 151.139.128.14:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRyyuDOSqb8BtprWZSAvBT9kFoYdwQU%2BftQxItnu2dk%2FoMhpqnOP1WEk5kCEBl1KfDoE6Kd%2B9KkjaxXnpA%3D | US | der | 471 b | whitelisted |
1656 | Rundll32.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEAo3h2ReX7SMIk79G%2B0UDDw%3D | US | der | 1.47 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1656 | Rundll32.exe | 104.28.19.220:443 | pornthash.mobi | Cloudflare Inc | US | suspicious |
1656 | Rundll32.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
1656 | Rundll32.exe | 89.40.211.3:443 | ip115038968.ahcdn.com | Sc Rexnet Srl | RO | unknown |
1656 | Rundll32.exe | 151.139.128.14:80 | ocsp.usertrust.com | Highwinds Network Group, Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
pornthash.mobi |
| suspicious |
ocsp.digicert.com |
| whitelisted |
mov.pornthash.mobi |
| suspicious |
ip115038968.ahcdn.com |
| unknown |
ocsp.usertrust.com |
| whitelisted |