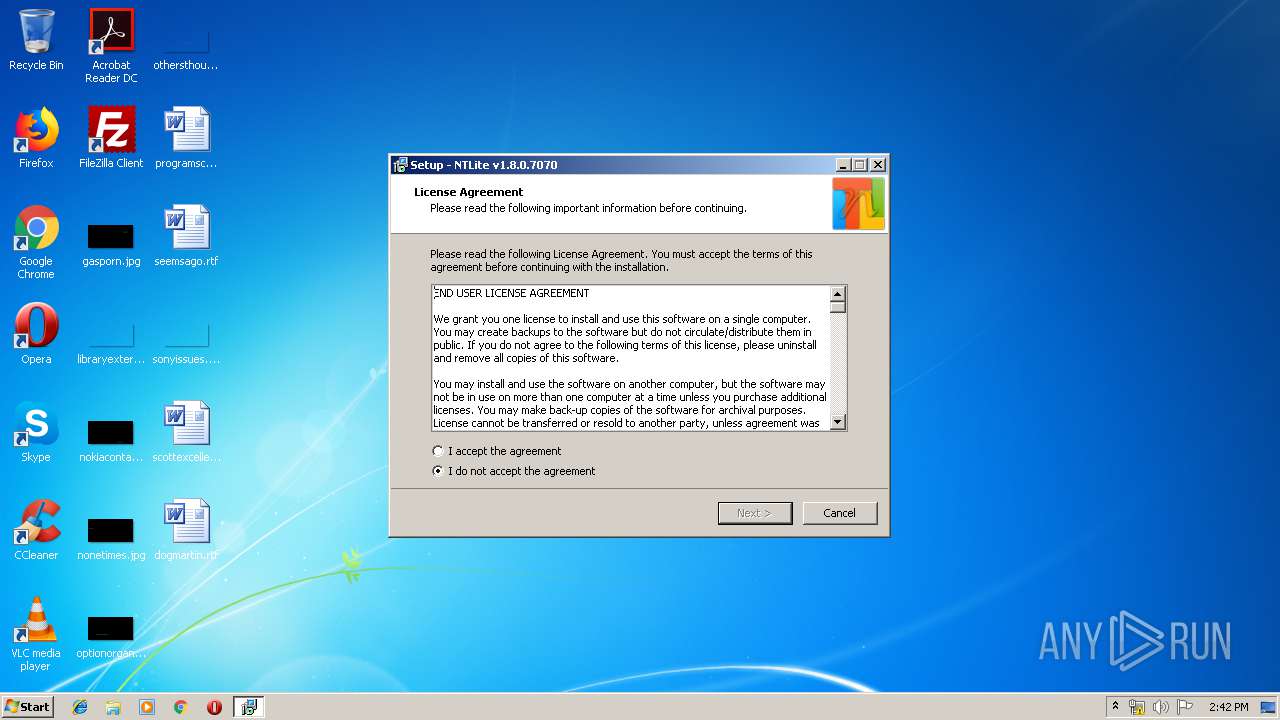
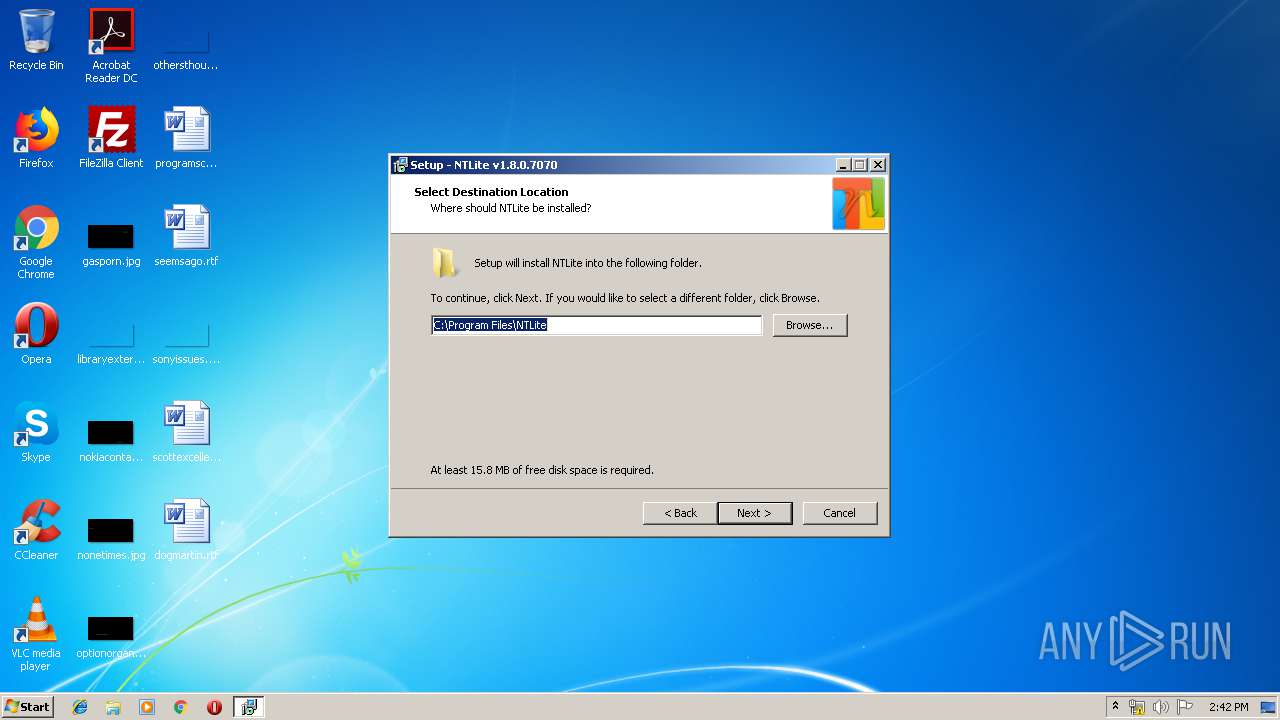
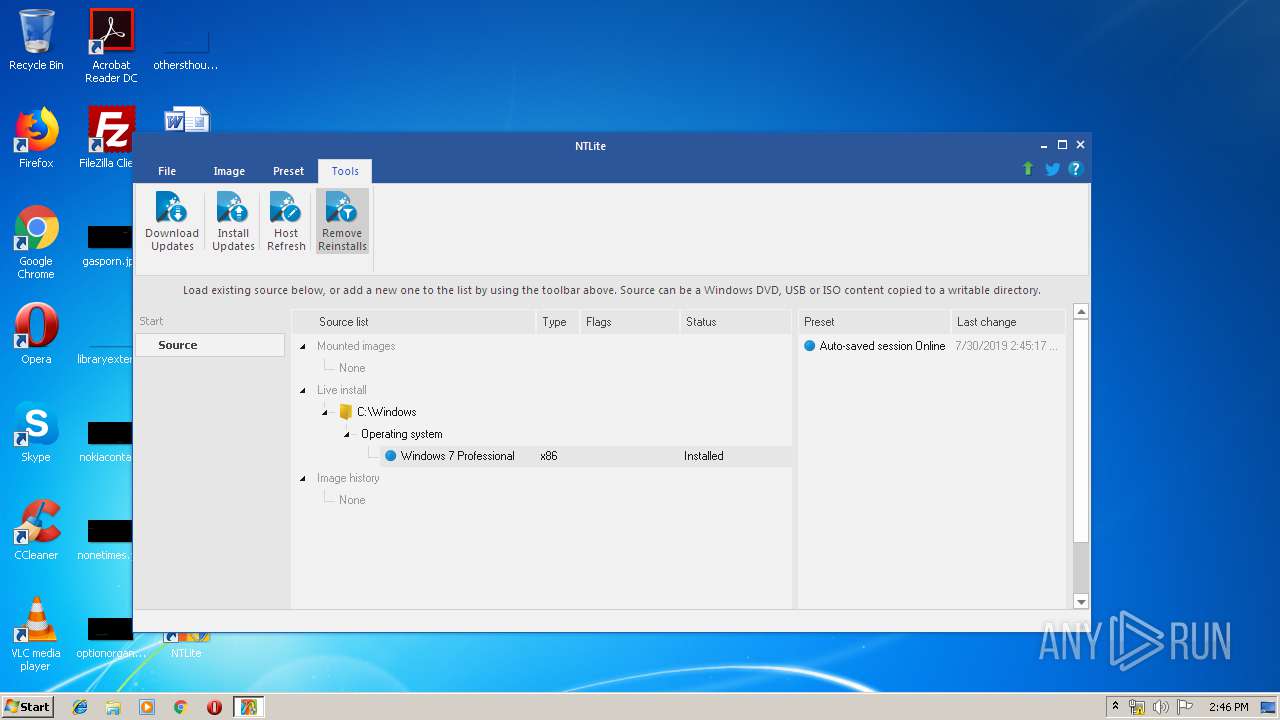
| File name: | NTLite_setup_x86.exe |
| Full analysis: | https://app.any.run/tasks/d2d33d5b-15e8-4c58-bbd6-4f2a4babd2f3 |
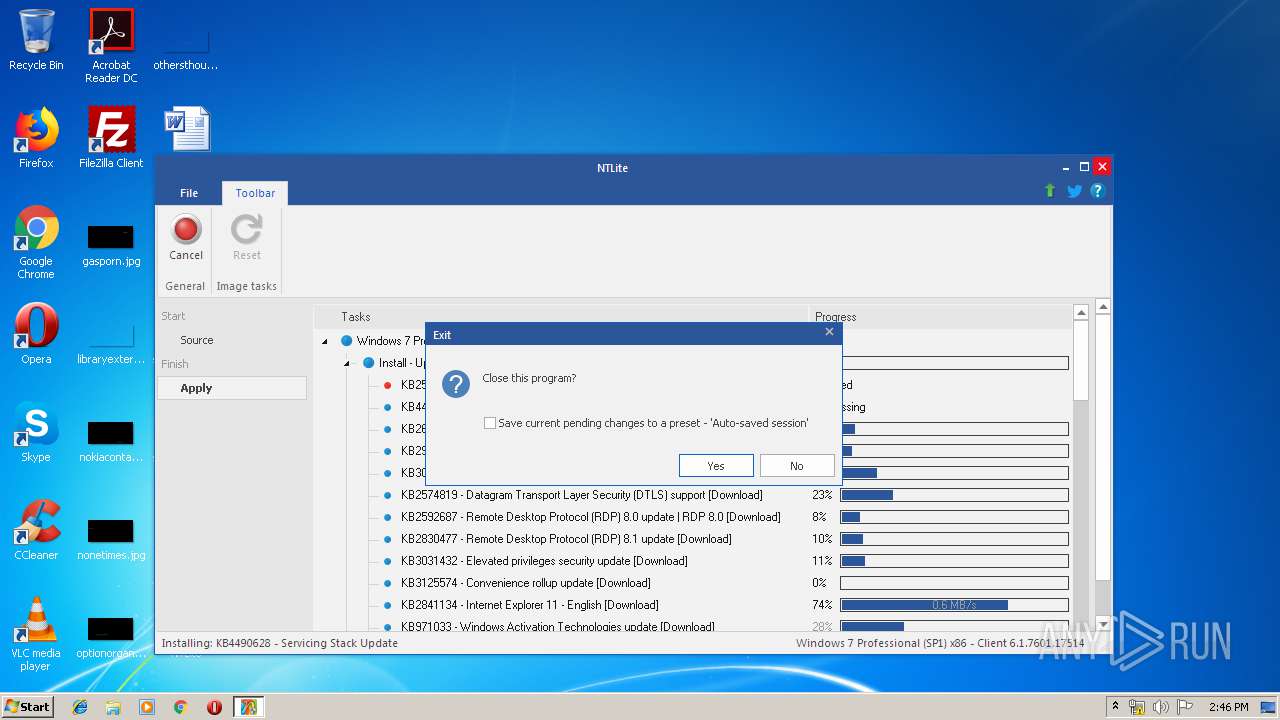
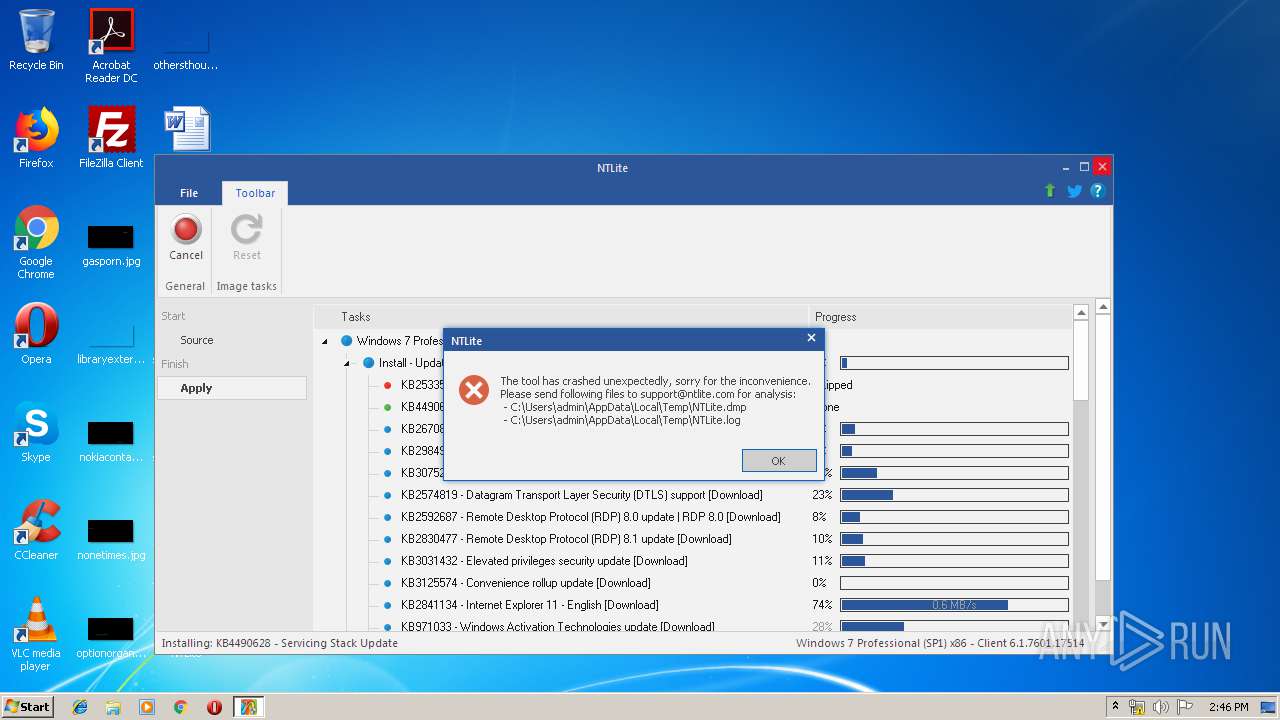
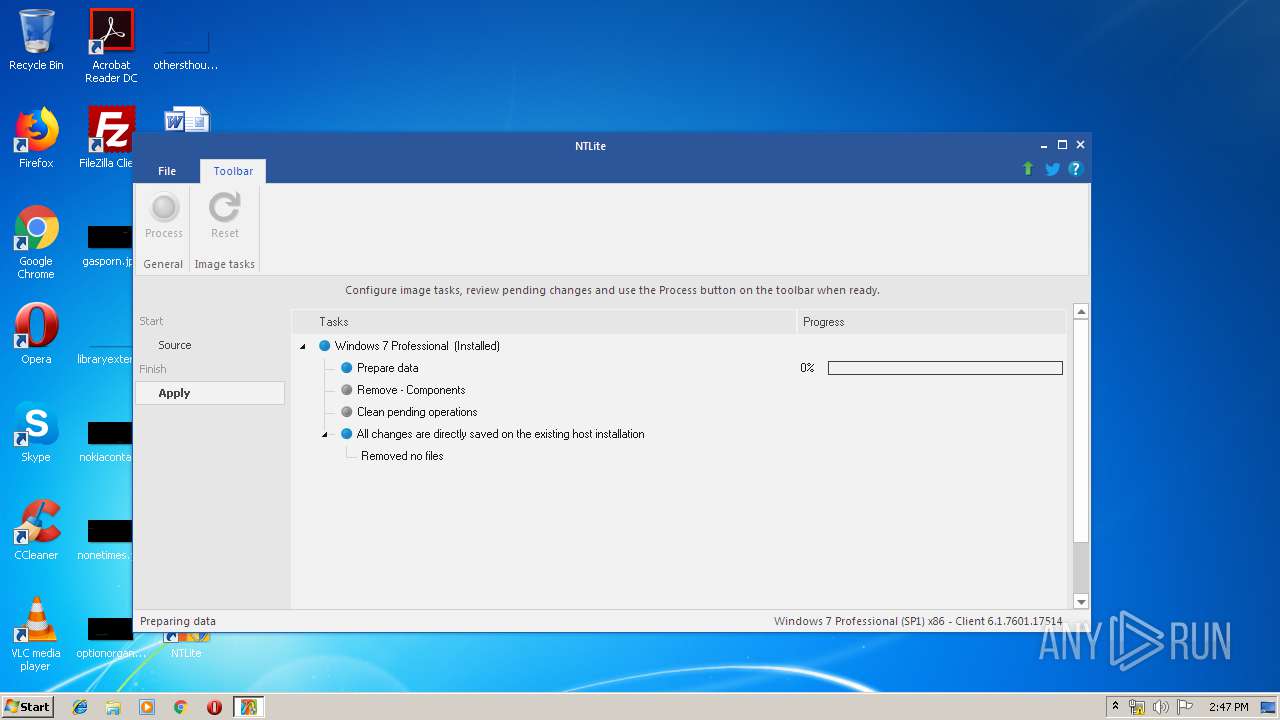
| Verdict: | Malicious activity |
| Analysis date: | July 30, 2019, 13:42:05 |
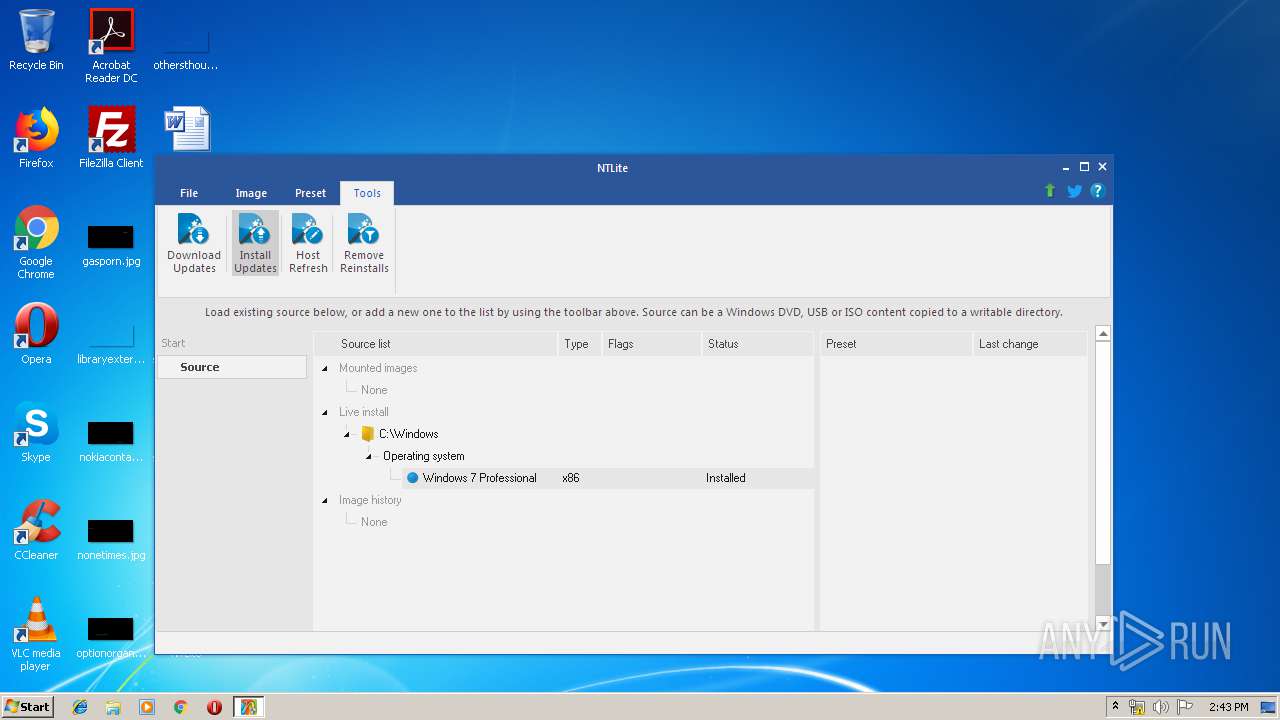
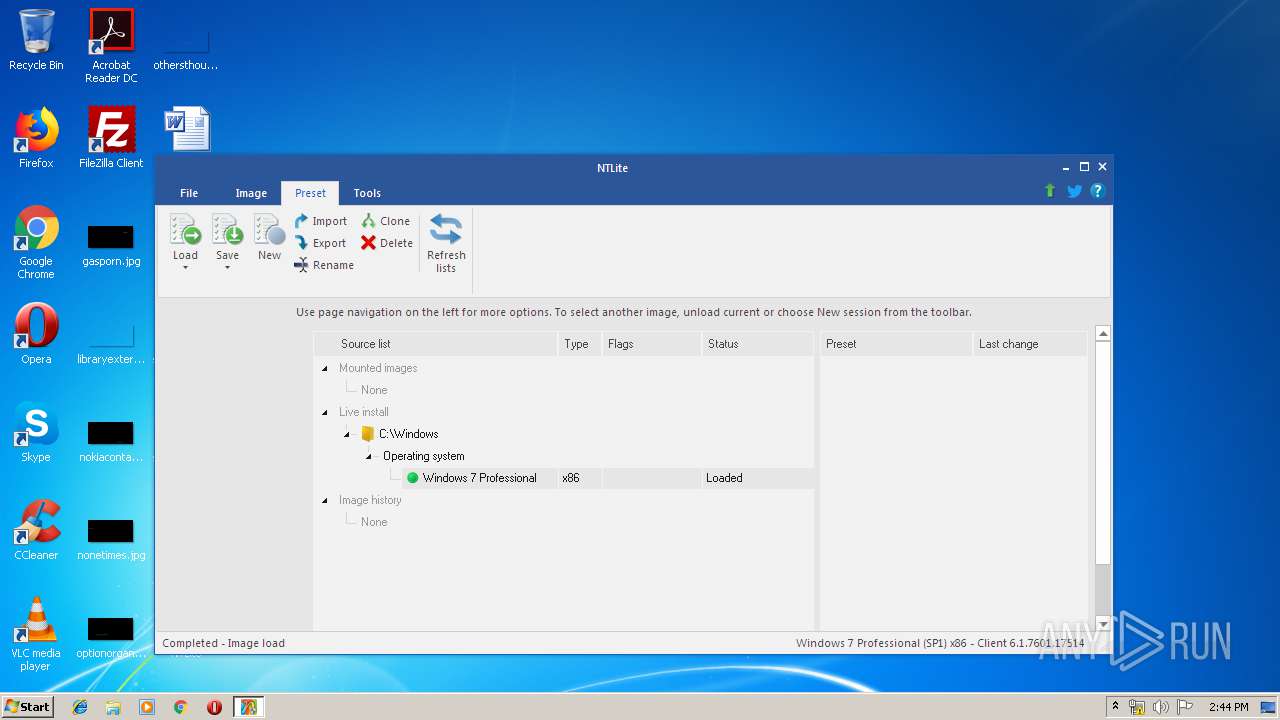
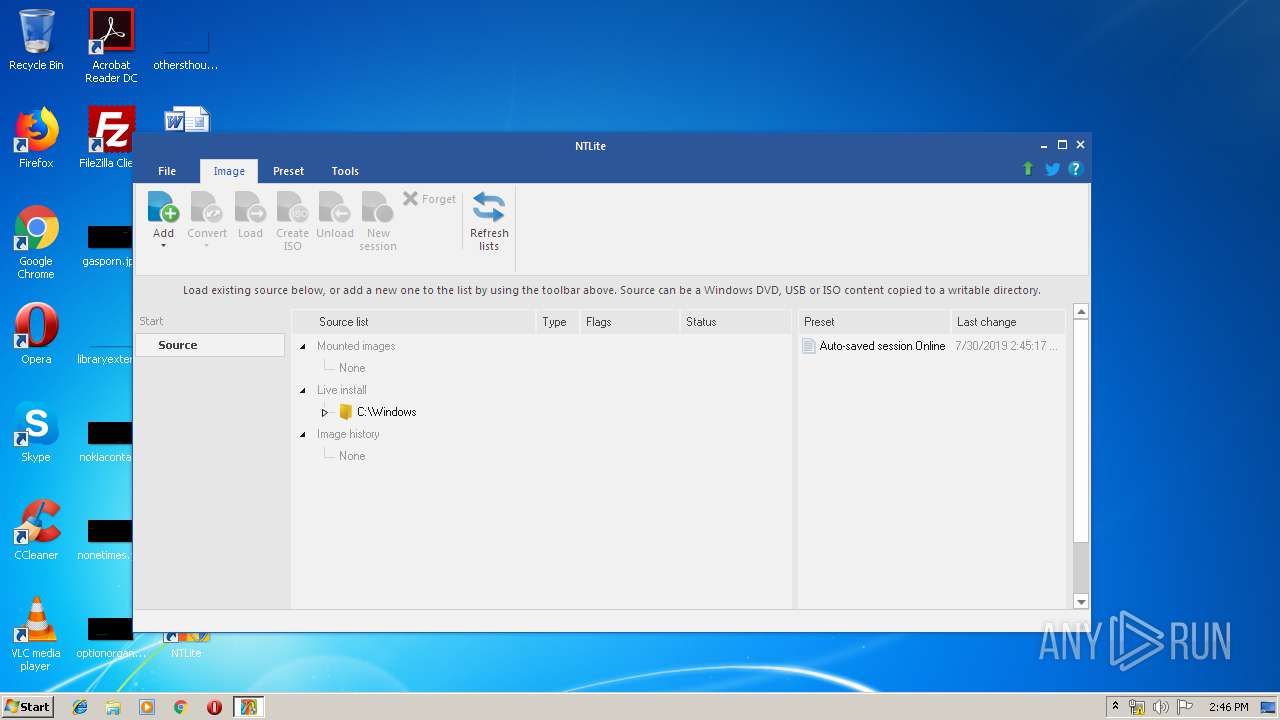
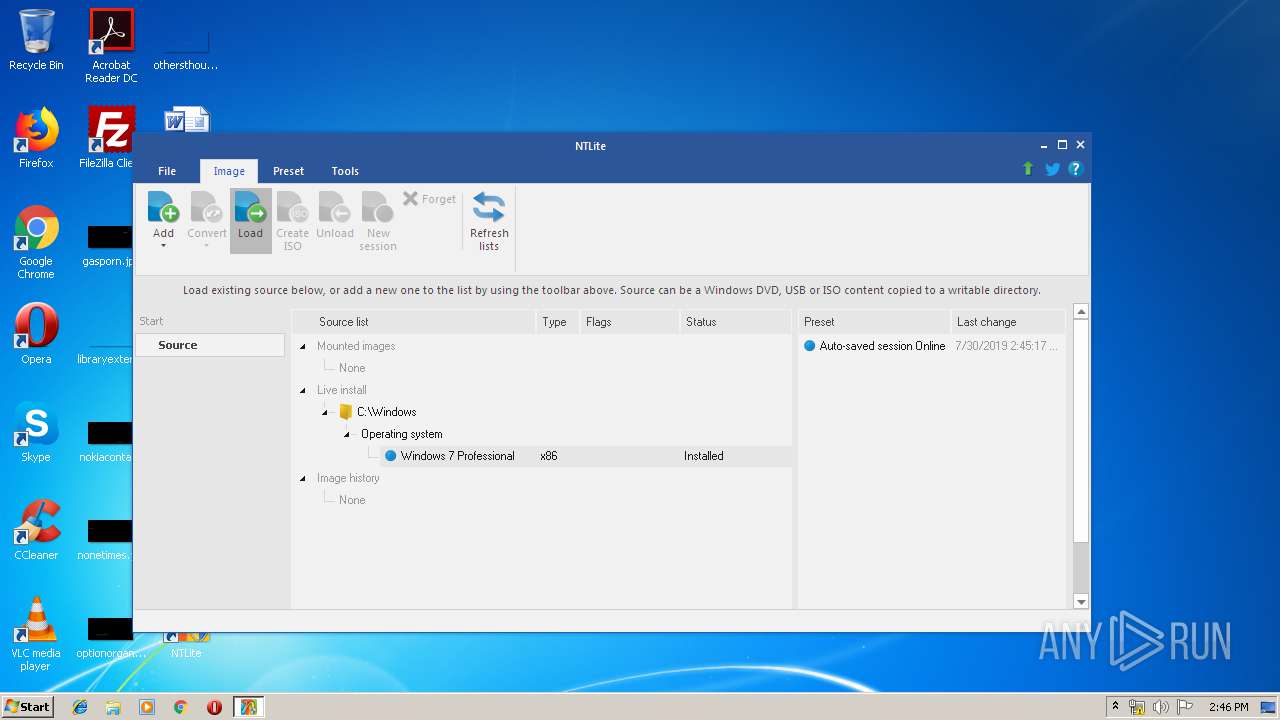
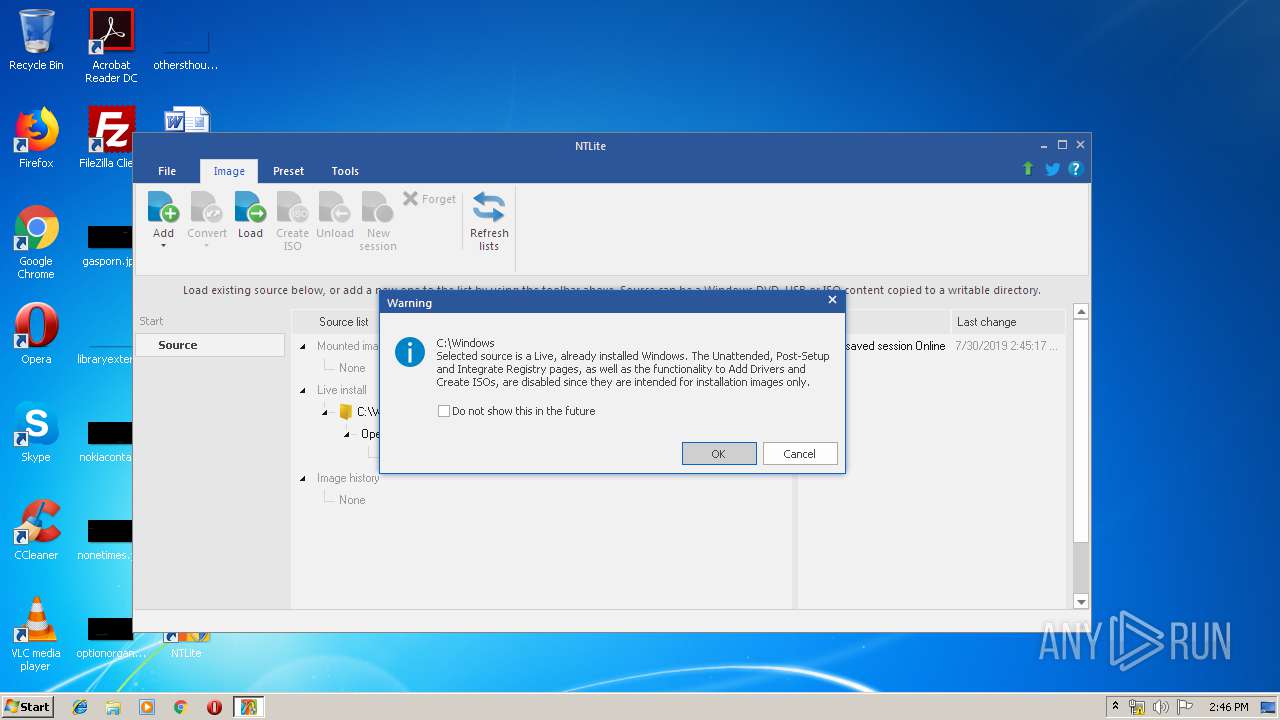
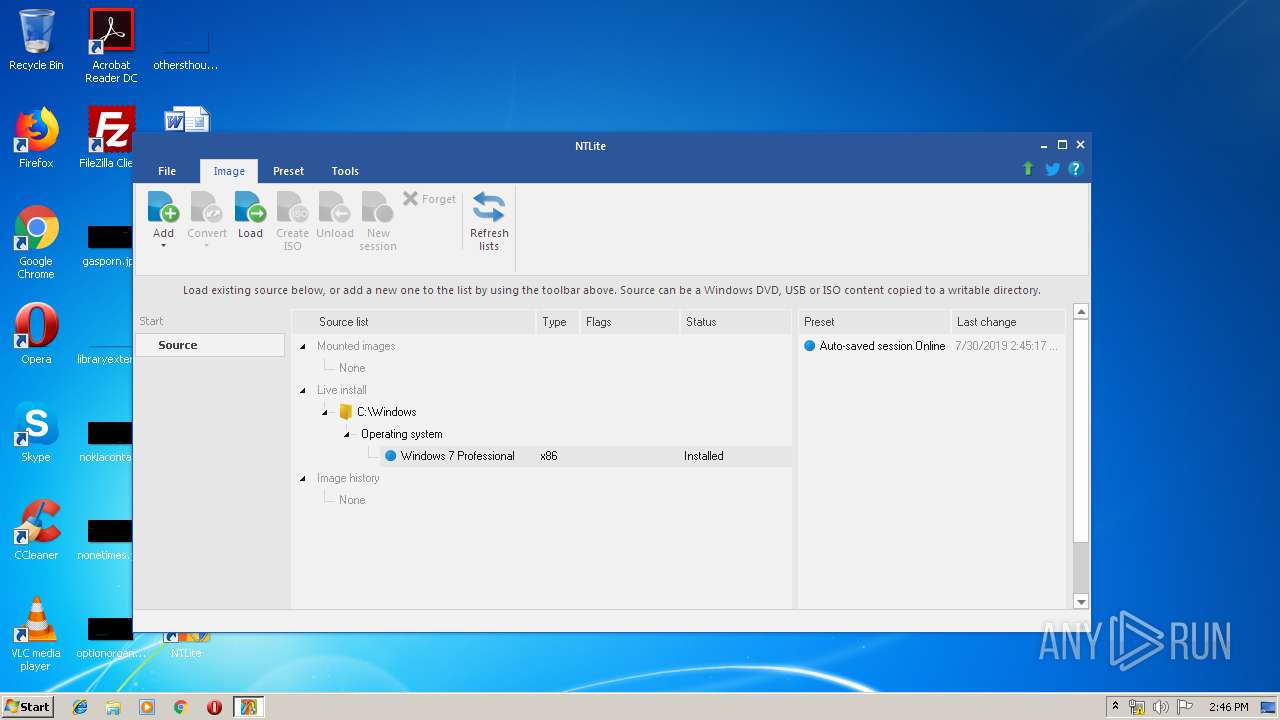
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 58199E9A84DFCA8DC6DC01685C7F829D |
| SHA1: | 2A7380EAC84C6866D4186084DDF95C12B3D9772D |
| SHA256: | DC397221DE19248C478A23CFC35CC3B16AFD0D6CE49E702744DFA8D6910F64D7 |
| SSDEEP: | 196608:+GumX0IABs+cZ4pl8Faj7HZBr3RtObk2HISlfdc5pPmJJSzRYd:HNXsBO4pl+q7LrhtObk2HIYlc5QJJSVi |
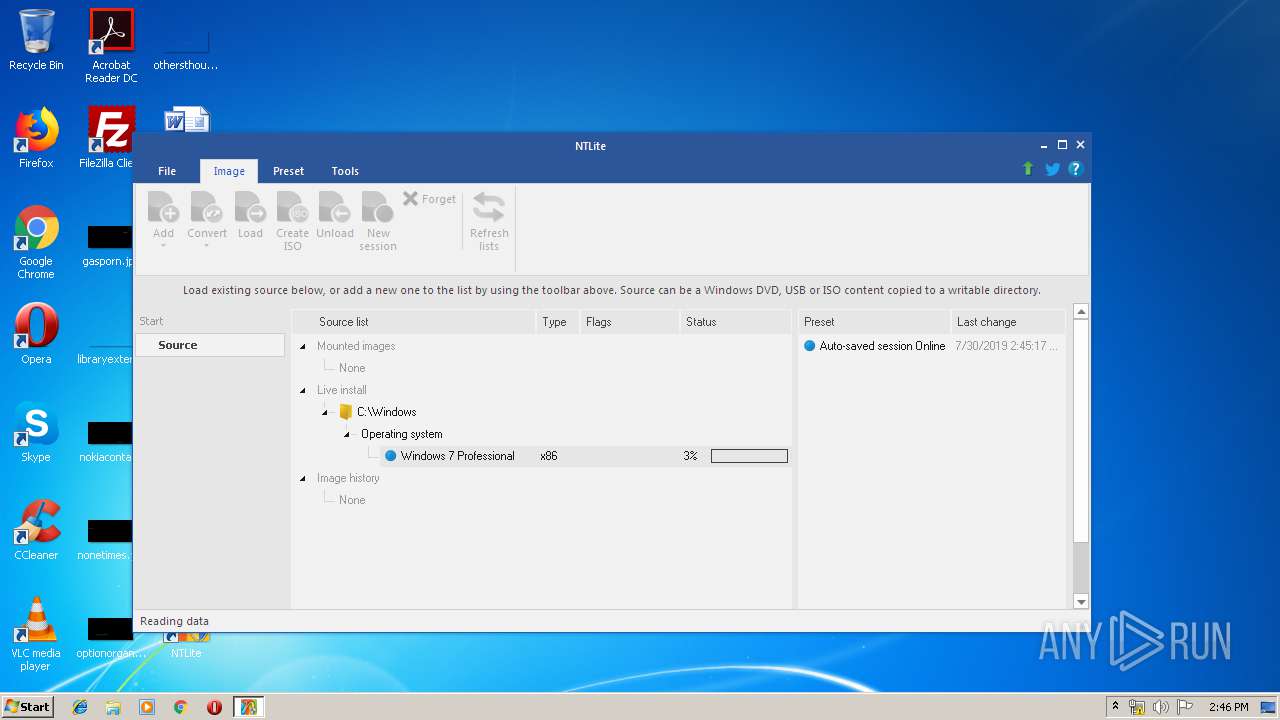
MALICIOUS
Application was dropped or rewritten from another process
- NTLite.exe (PID: 2368)
- NTLite.exe (PID: 2984)
- NTLite.exe (PID: 3636)
Loads dropped or rewritten executable
- NTLite.exe (PID: 2368)
- Dism.exe (PID: 3360)
- dismhost.exe (PID: 2996)
- Dism.exe (PID: 3020)
- dismhost.exe (PID: 1480)
- Dism.exe (PID: 3928)
- TrustedInstaller.exe (PID: 2296)
- Dism.exe (PID: 3660)
- Dism.exe (PID: 1008)
- dismhost.exe (PID: 2504)
- Dism.exe (PID: 2812)
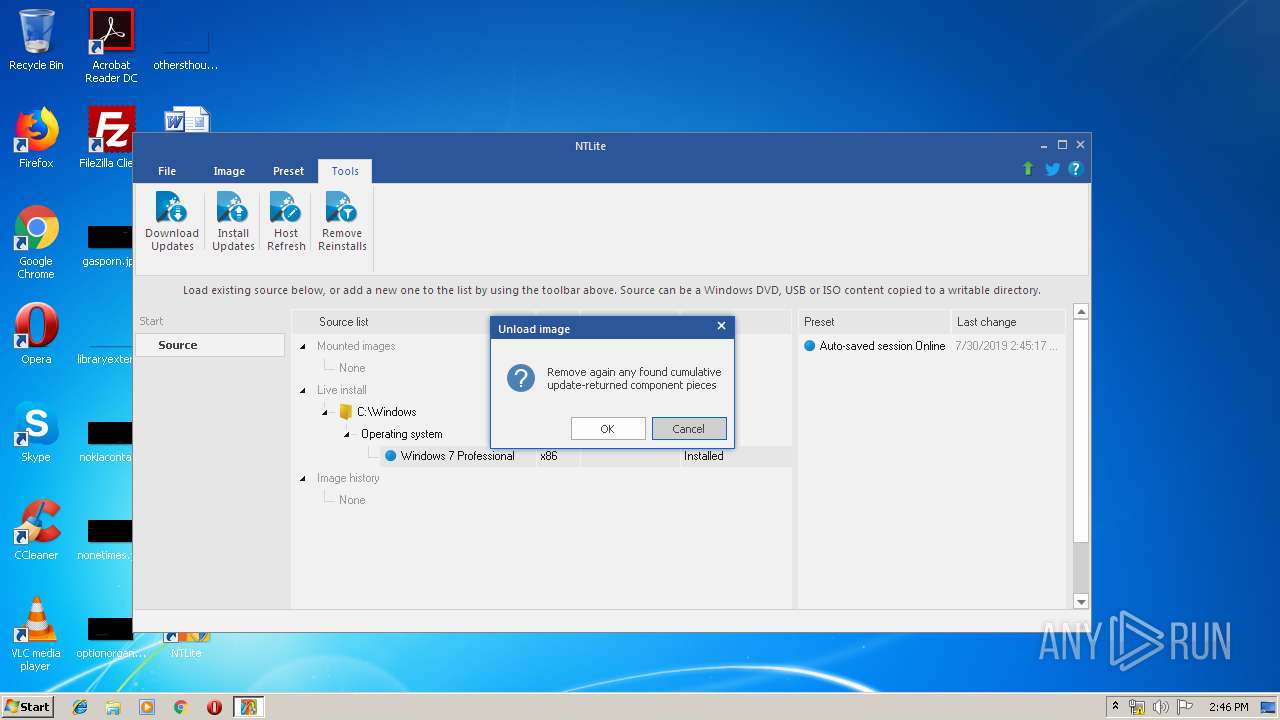
SUSPICIOUS
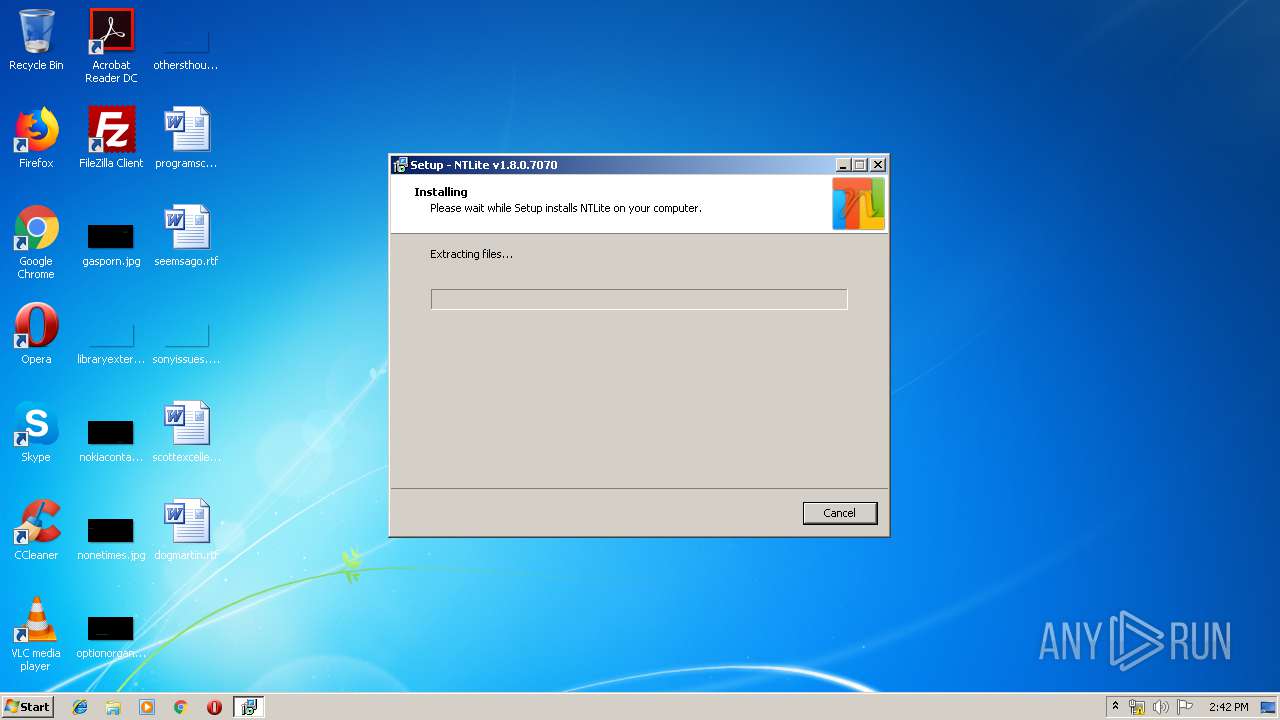
Executable content was dropped or overwritten
- NTLite_setup_x86.exe (PID: 4008)
- NTLite_setup_x86.exe (PID: 2796)
- NTLite_setup_x86.tmp (PID: 3392)
- NTLite.exe (PID: 2368)
- Dism.exe (PID: 3360)
- Dism.exe (PID: 3660)
- Dism.exe (PID: 3928)
Reads Windows owner or organization settings
- NTLite_setup_x86.tmp (PID: 3392)
Reads the Windows organization settings
- NTLite_setup_x86.tmp (PID: 3392)
Low-level read access rights to disk partition
- NTLite.exe (PID: 2368)
- NTLite.exe (PID: 2984)
Checks Windows language
- NTLite.exe (PID: 2368)
- NTLite.exe (PID: 2984)
Creates files in the user directory
- NTLite.exe (PID: 2368)
- NTLite.exe (PID: 2984)
Checks supported languages
- NTLite.exe (PID: 2368)
- NTLite.exe (PID: 2984)
Creates files in the Windows directory
- NTLite.exe (PID: 2368)
- TrustedInstaller.exe (PID: 2296)
- NTLite.exe (PID: 2984)
Reads Environment values
- NTLite.exe (PID: 2368)
- NTLite.exe (PID: 2984)
Removes files from Windows directory
- NTLite.exe (PID: 2368)
- TrustedInstaller.exe (PID: 2296)
Creates files in the program directory
- NTLite.exe (PID: 2368)
INFO
Application was dropped or rewritten from another process
- NTLite_setup_x86.tmp (PID: 3756)
- NTLite_setup_x86.tmp (PID: 3392)
Creates a software uninstall entry
- NTLite_setup_x86.tmp (PID: 3392)
Creates files in the program directory
- NTLite_setup_x86.tmp (PID: 3392)
Reads settings of System Certificates
- NTLite.exe (PID: 2368)
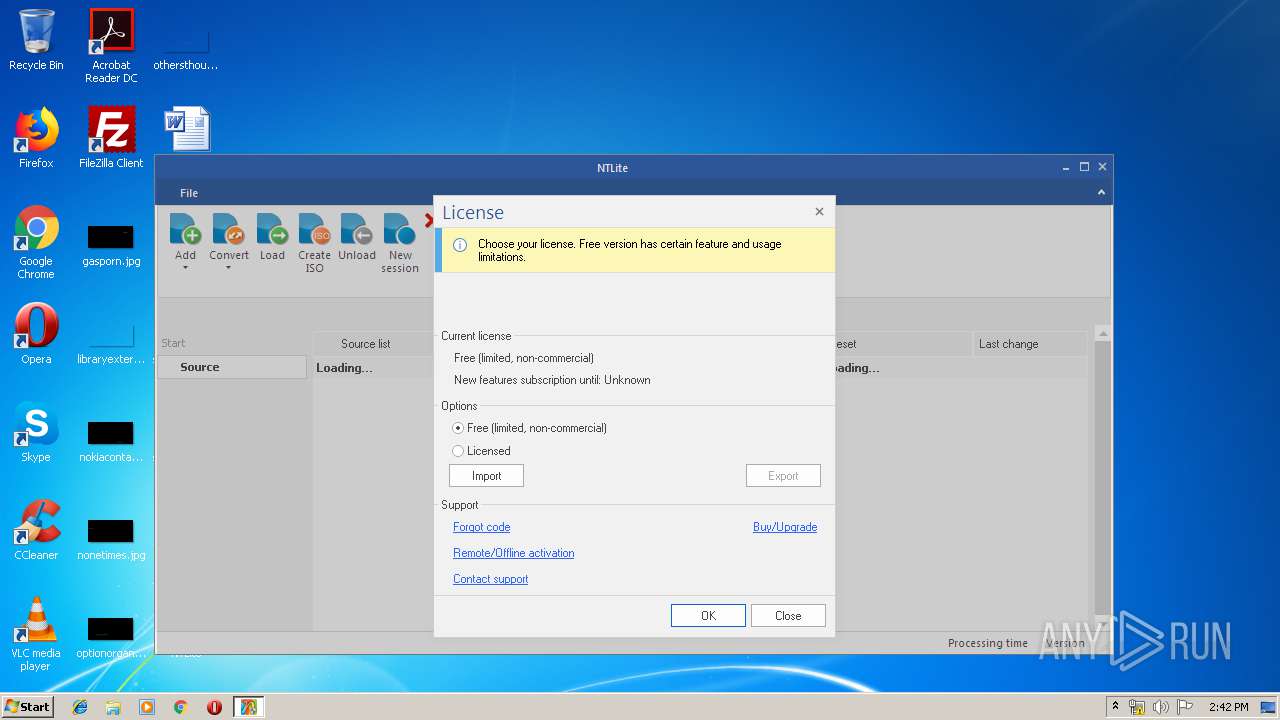
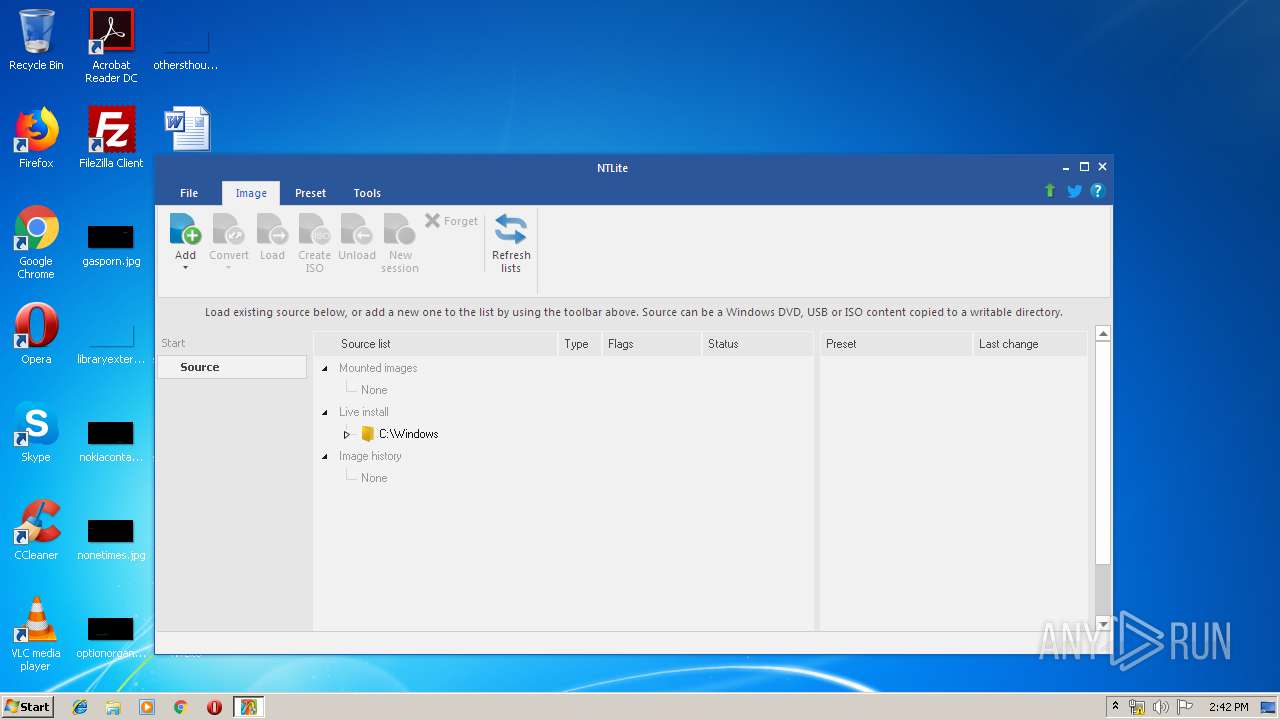
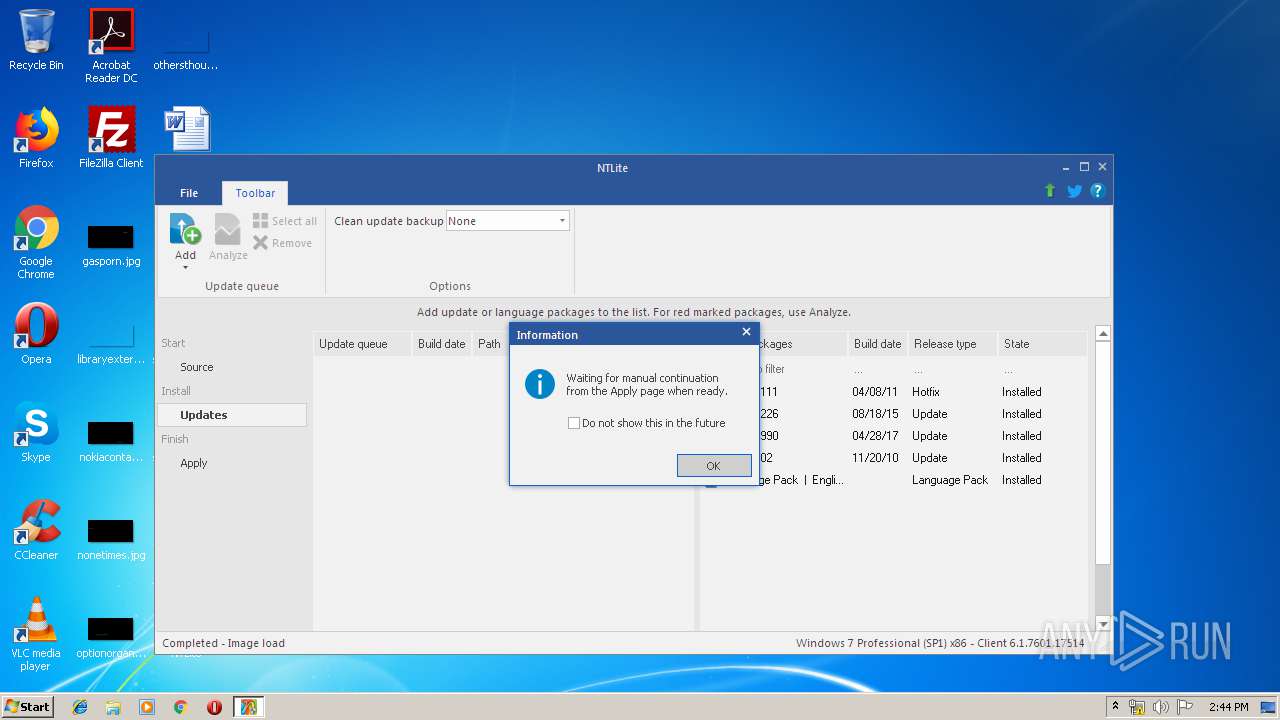
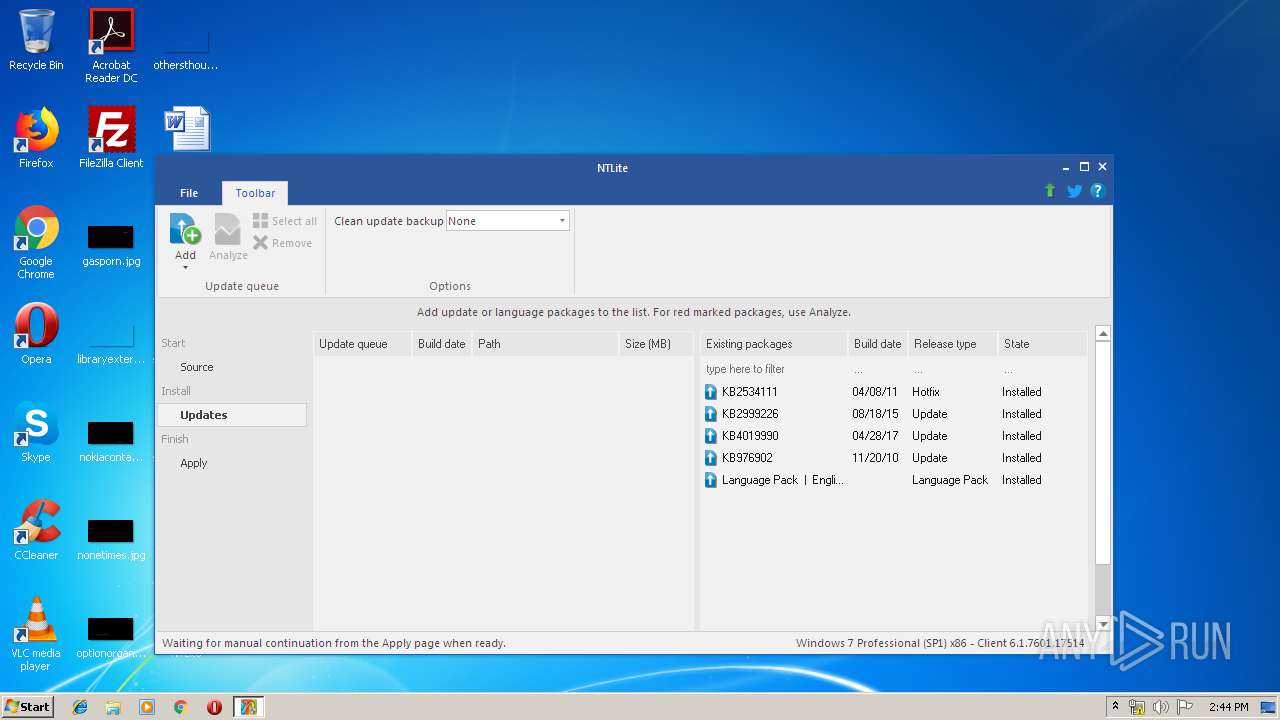
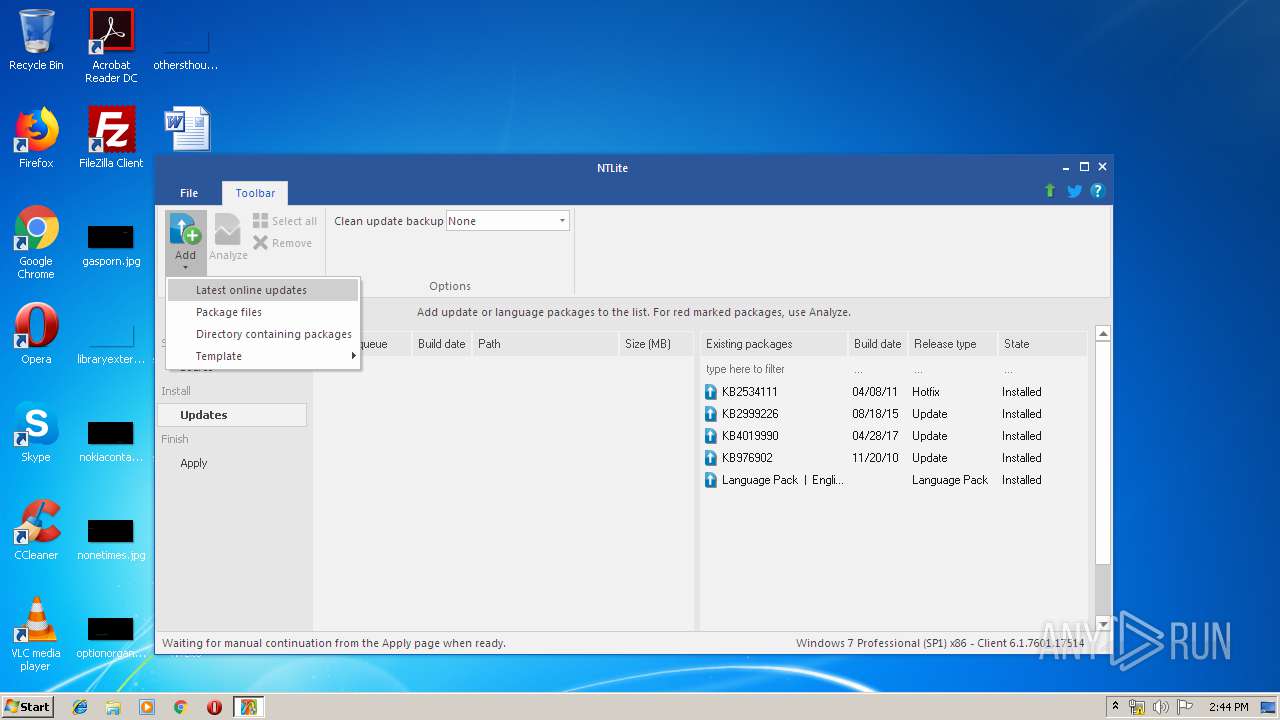
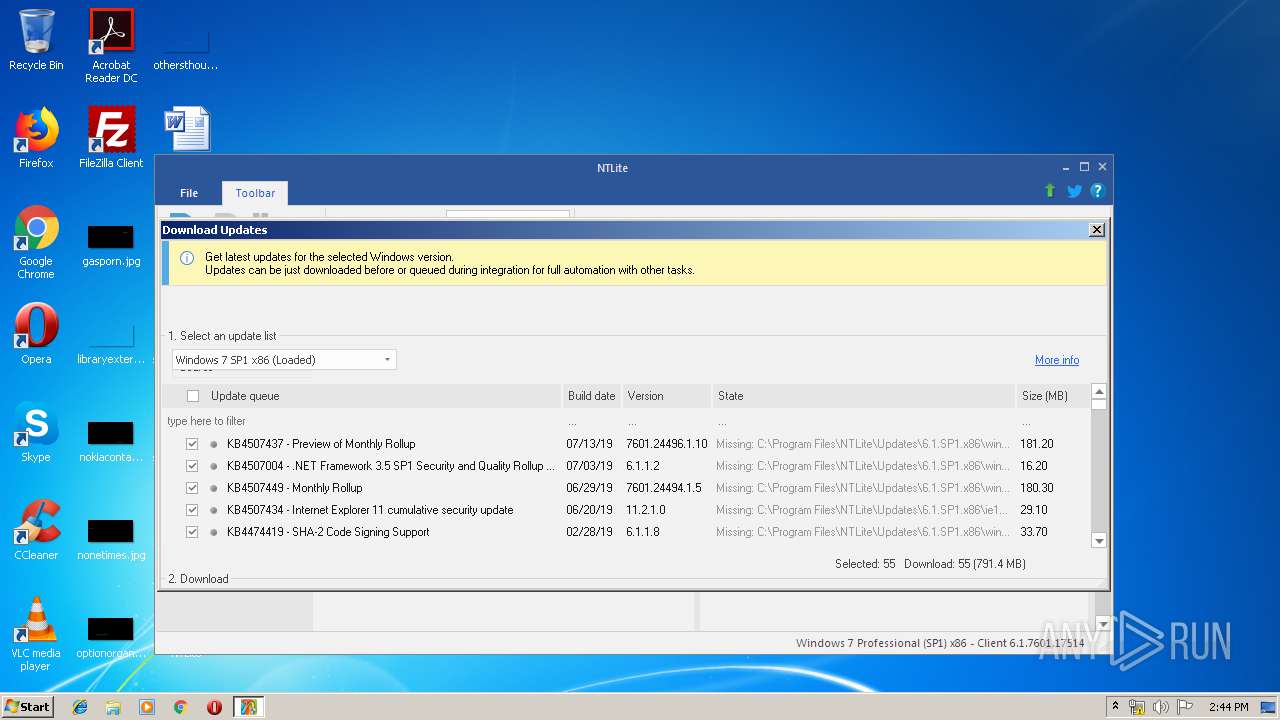
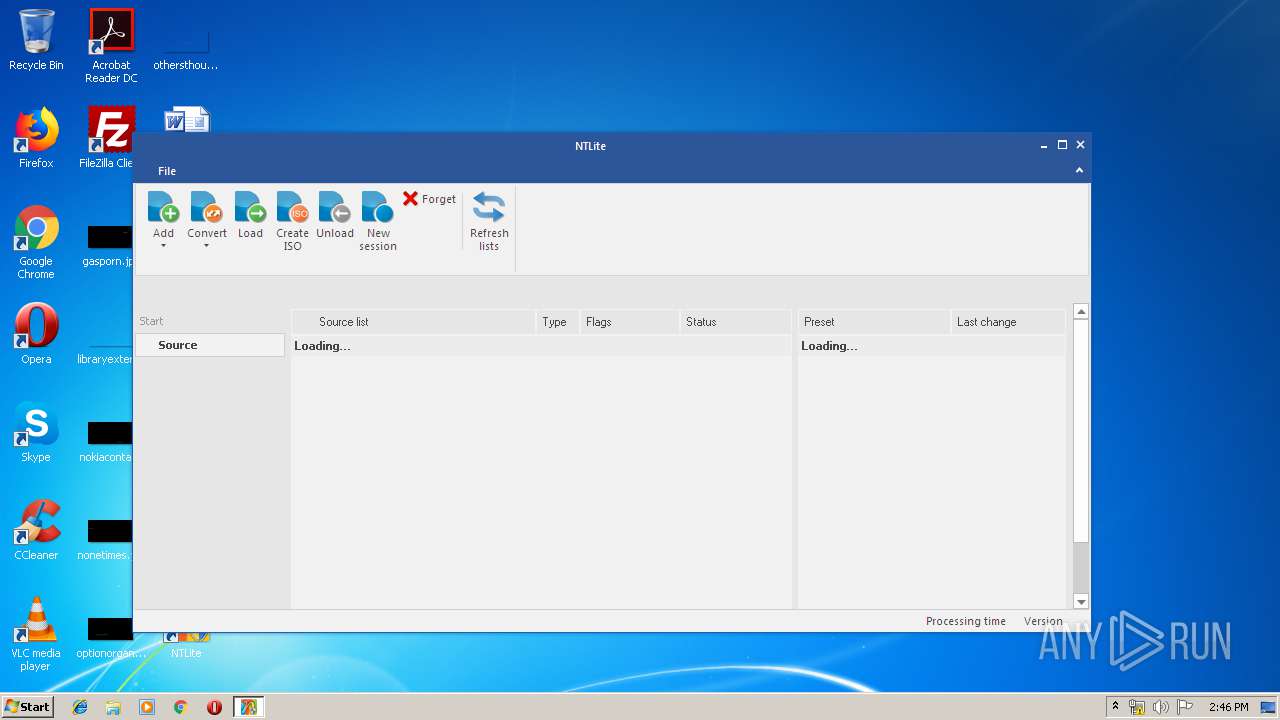
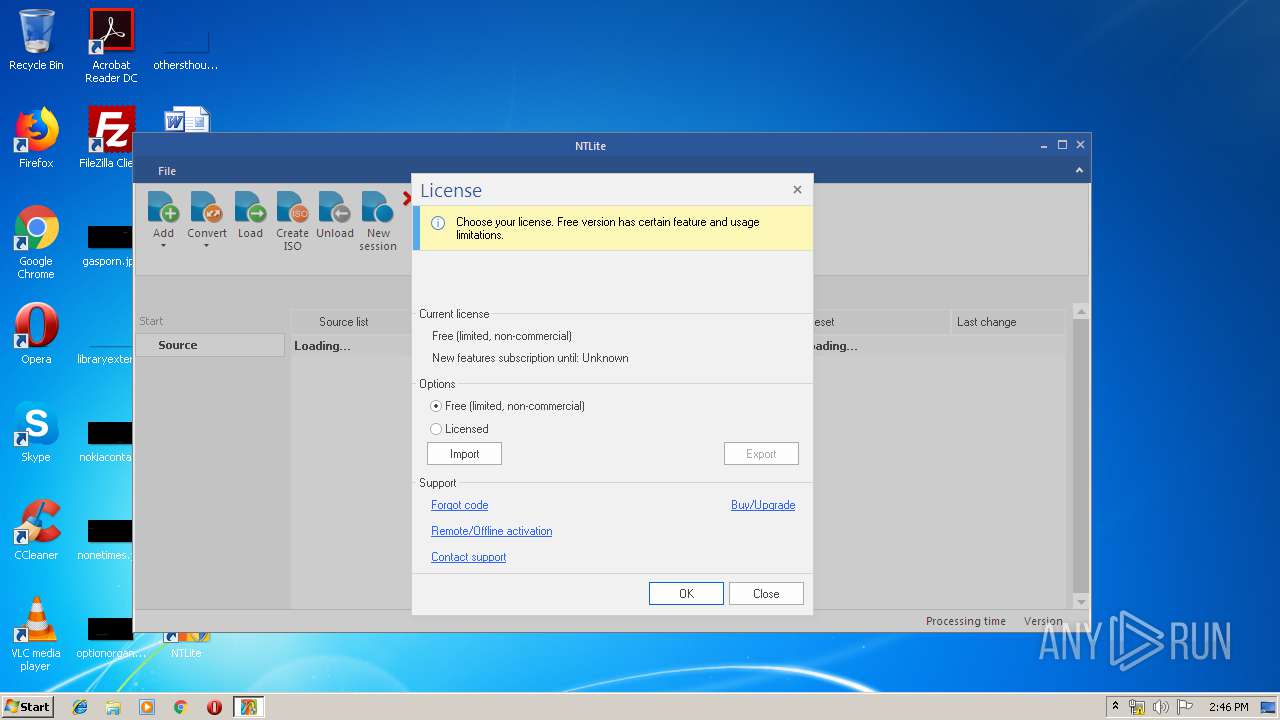
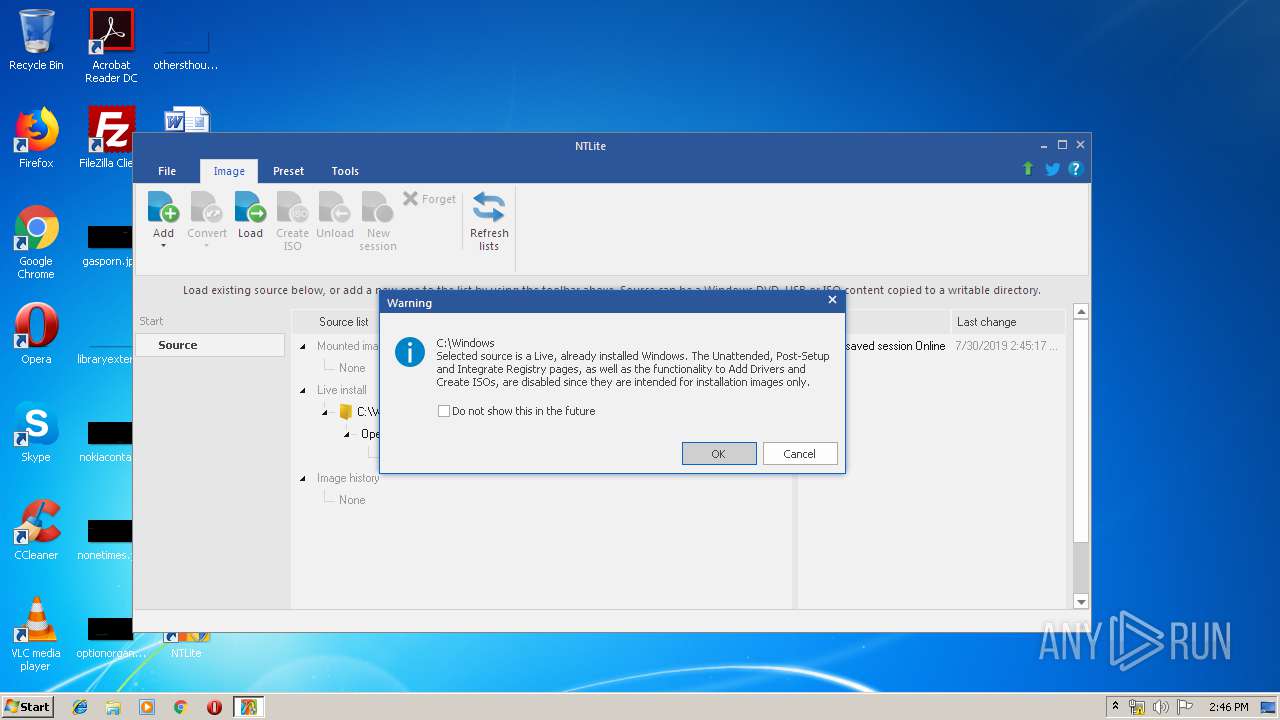
Manual execution by user
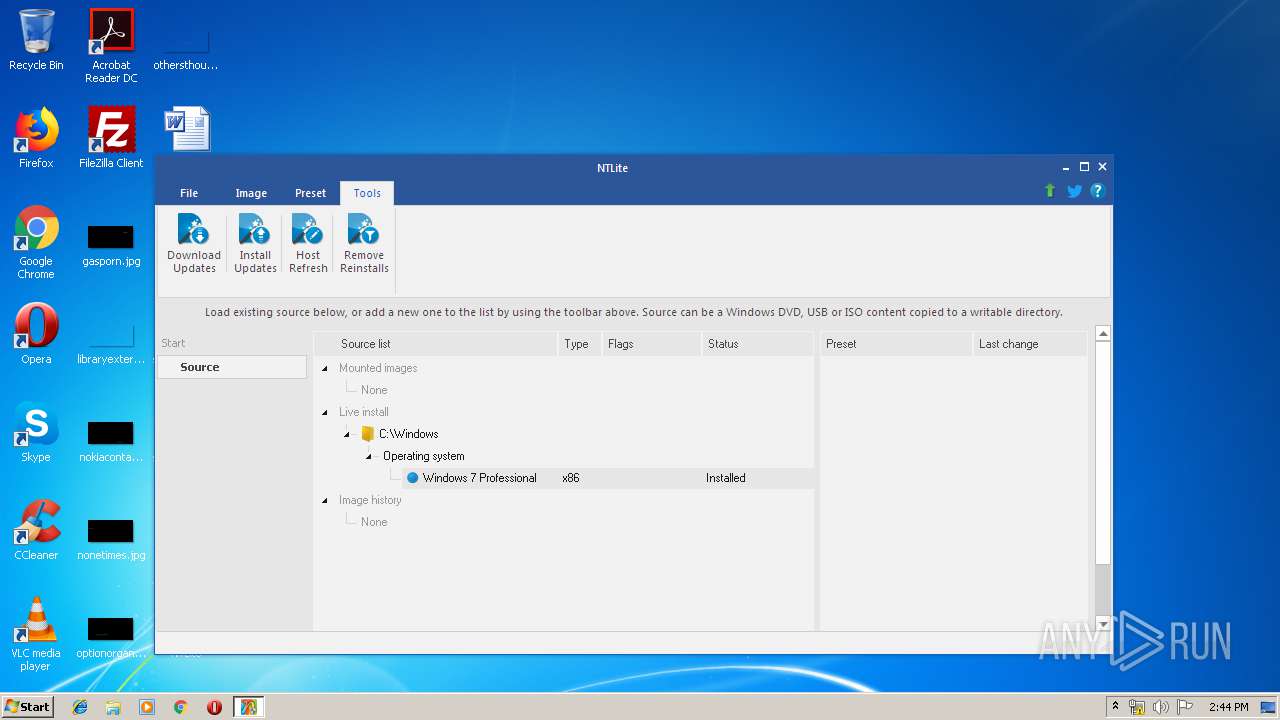
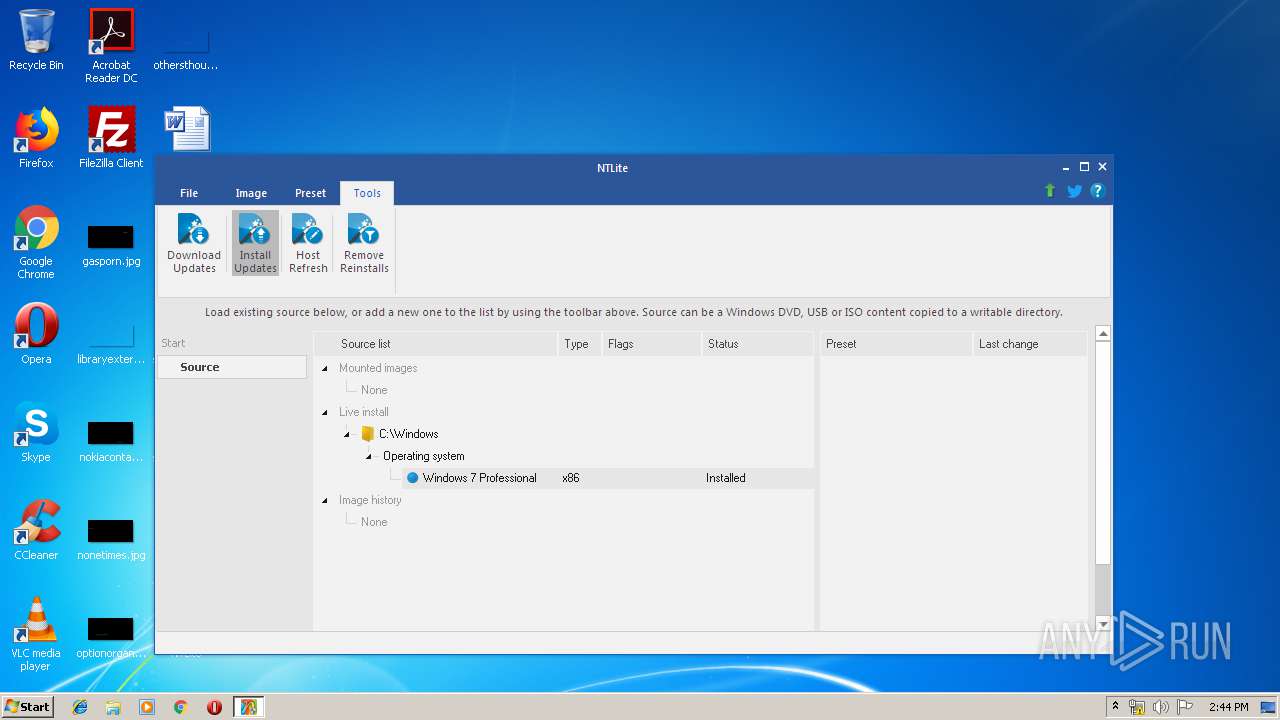
- NTLite.exe (PID: 2984)
- NTLite.exe (PID: 3636)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (51.8) |
|---|---|---|
| .exe | | | InstallShield setup (20.3) |
| .exe | | | Win32 EXE PECompact compressed (generic) (19.6) |
| .dll | | | Win32 Dynamic Link Library (generic) (3.1) |
| .exe | | | Win32 Executable (generic) (2.1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:04:27 10:22:11+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 682496 |
| InitializedDataSize: | 37888 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xa7ed0 |
| OSVersion: | 6 |
| ImageVersion: | 6 |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
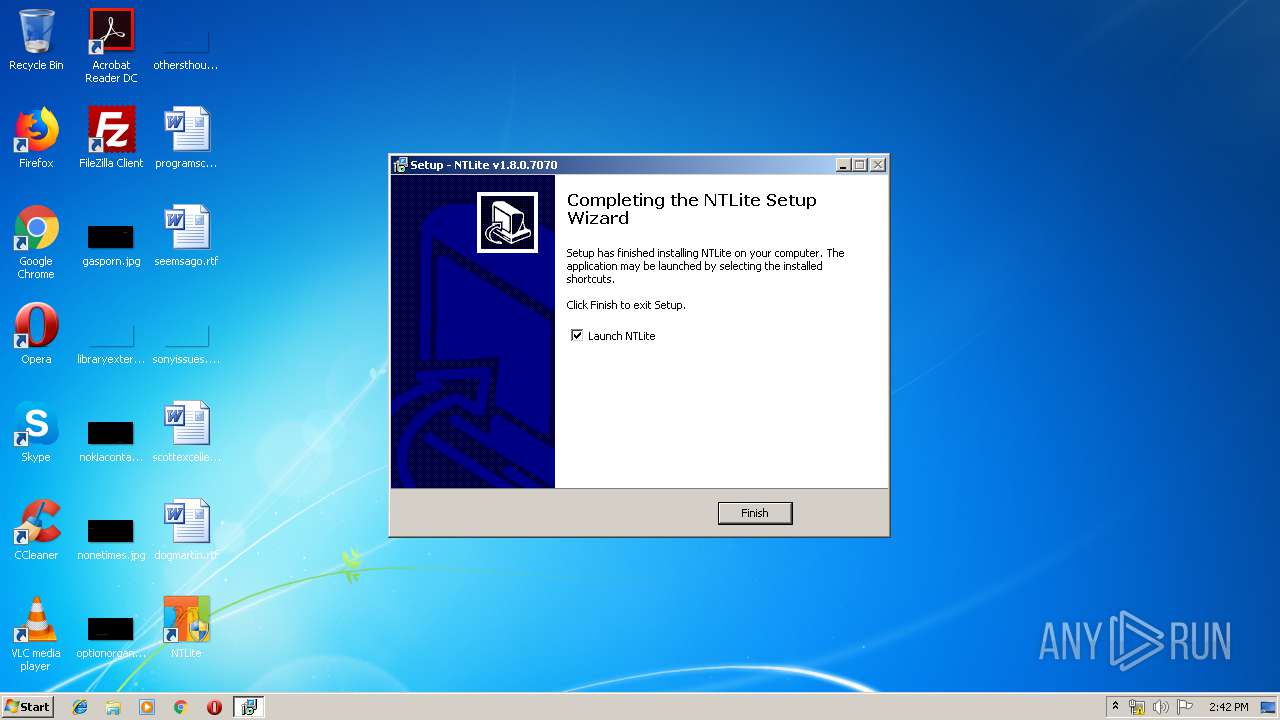
| FileVersionNumber: | 1.8.0.7070 |
| ProductVersionNumber: | 1.8.0.7070 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Nlitesoft |
| FileDescription: | NTLite Setup |
| FileVersion: | 1.8.0.7070 |
| LegalCopyright: | © 2014-2019 Nlitesoft. All rights reserved. |
| OriginalFileName: | |
| ProductName: | NTLite |
| ProductVersion: | 1.8.0.7070 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 27-Apr-2019 08:22:11 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | Nlitesoft |
| FileDescription: | NTLite Setup |
| FileVersion: | 1.8.0.7070 |
| LegalCopyright: | © 2014-2019 Nlitesoft. All rights reserved. |
| OriginalFileName: | - |
| ProductName: | NTLite |
| ProductVersion: | 1.8.0.7070 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 10 |
| Time date stamp: | 27-Apr-2019 08:22:11 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000A50E0 | 0x000A5200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.36825 |
.itext | 0x000A7000 | 0x00001668 | 0x00001800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.95049 |
.data | 0x000A9000 | 0x000037A4 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.02787 |
.bss | 0x000AD000 | 0x0000676C | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x000B4000 | 0x00000F1C | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.79161 |
.didata | 0x000B5000 | 0x000001A4 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.74582 |
.edata | 0x000B6000 | 0x0000009A | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.88107 |
.tls | 0x000B7000 | 0x00000018 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x000B8000 | 0x0000005D | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 1.36974 |
.rsrc | 0x000B9000 | 0x00004600 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.45286 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.13965 | 1580 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.47151 | 1384 | UNKNOWN | Dutch - Netherlands | RT_ICON |
3 | 3.91708 | 744 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4 | 3.91366 | 2216 | UNKNOWN | Dutch - Netherlands | RT_ICON |
4086 | 3.16547 | 864 | UNKNOWN | UNKNOWN | RT_STRING |
4087 | 3.40938 | 608 | UNKNOWN | UNKNOWN | RT_STRING |
4088 | 3.31153 | 1116 | UNKNOWN | UNKNOWN | RT_STRING |
4089 | 3.33977 | 1036 | UNKNOWN | UNKNOWN | RT_STRING |
4090 | 3.36723 | 724 | UNKNOWN | UNKNOWN | RT_STRING |
4091 | 3.33978 | 184 | UNKNOWN | UNKNOWN | RT_STRING |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
kernel32.dll (delay-loaded) |
netapi32.dll |
oleaut32.dll |
user32.dll |
version.dll |
Exports
Title | Ordinal | Address |
|---|---|---|
dbkFCallWrapperAddr | 1 | 0x000B063C |
__dbk_fcall_wrapper | 2 | 0x0000D3DC |
TMethodImplementationIntercept | 3 | 0x00053ABC |
Total processes
64
Monitored processes
17
Malicious processes
14
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1008 | "C:\Windows\System32\Dism.exe" | C:\Windows\System32\Dism.exe | NTLite.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1480 | \\?\C:\Users\admin\AppData\Local\Temp\NLTmpScratch\NLTmpS01\530A85A7-199B-4BEC-96C8-D3B1F2BD697C\dismhost.exe {1ECFB792-9145-4576-B9DC-017DF108423E} | C:\Users\admin\AppData\Local\Temp\NLTmpScratch\NLTmpS01\530A85A7-199B-4BEC-96C8-D3B1F2BD697C\dismhost.exe | Dism.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Host Servicing Process Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2296 | C:\Windows\servicing\TrustedInstaller.exe | C:\Windows\servicing\TrustedInstaller.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Modules Installer Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2368 | "C:\Program Files\NTLite\NTLite.exe" | C:\Program Files\NTLite\NTLite.exe | NTLite_setup_x86.tmp | ||||||||||||
User: admin Company: Nlitesoft d.o.o. Integrity Level: HIGH Description: NTLite Exit code: 3765269347 Version: 1.8.0.7070 Modules
| |||||||||||||||
| 2504 | \\?\C:\Users\admin\AppData\Local\Temp\NLTmpScratch\NLTmpS01\FCA41781-85E0-43D8-9711-656924200C18\dismhost.exe {BCABB5BF-CED2-4C49-8D04-AE654F0F15A7} | C:\Users\admin\AppData\Local\Temp\NLTmpScratch\NLTmpS01\FCA41781-85E0-43D8-9711-656924200C18\dismhost.exe | Dism.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Host Servicing Process Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2796 | "C:\Users\admin\Downloads\NTLite_setup_x86.exe" /SPAWNWND=$801CC /NOTIFYWND=$8019E | C:\Users\admin\Downloads\NTLite_setup_x86.exe | NTLite_setup_x86.tmp | ||||||||||||
User: admin Company: Nlitesoft Integrity Level: HIGH Description: NTLite Setup Exit code: 0 Version: 1.8.0.7070 Modules
| |||||||||||||||
| 2812 | "C:\Windows\System32\Dism.exe" | C:\Windows\System32\Dism.exe | NTLite.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2984 | "C:\Program Files\NTLite\NTLite.exe" | C:\Program Files\NTLite\NTLite.exe | explorer.exe | ||||||||||||
User: admin Company: Nlitesoft d.o.o. Integrity Level: HIGH Description: NTLite Exit code: 0 Version: 1.8.0.7070 Modules
| |||||||||||||||
| 2996 | \\?\C:\Users\admin\AppData\Local\Temp\NLTmpScratch\NLTmpS01\77F83205-B2A0-45CE-BE10-26B422D1236B\dismhost.exe {3AE3877C-2D95-4167-9823-ADA4BB1C66C6} | C:\Users\admin\AppData\Local\Temp\NLTmpScratch\NLTmpS01\77F83205-B2A0-45CE-BE10-26B422D1236B\dismhost.exe | Dism.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Host Servicing Process Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3020 | "C:\Windows\System32\Dism.exe" | C:\Windows\System32\Dism.exe | NTLite.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Dism Image Servicing Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
15 451
Read events
15 030
Write events
415
Delete events
6
Modification events
| (PID) Process: | (3392) NTLite_setup_x86.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 400D000042ED39A6DC46D501 | |||
| (PID) Process: | (3392) NTLite_setup_x86.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 1F4AAEC6AC15D9D93F997486627EBC1F5153443DF60CC7F051052B07EA5E6002 | |||
| (PID) Process: | (3392) NTLite_setup_x86.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3392) NTLite_setup_x86.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFiles0000 |
Value: C:\Program Files\NTLite\NTLite.exe | |||
| (PID) Process: | (3392) NTLite_setup_x86.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | RegFilesHash |
Value: AAAF6FBB2985E72E1E60772C42F7108738576A1697E36899D6831174CA02761B | |||
| (PID) Process: | (3392) NTLite_setup_x86.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NTLite_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 6.0.2 (u) | |||
| (PID) Process: | (3392) NTLite_setup_x86.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NTLite_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files\NTLite | |||
| (PID) Process: | (3392) NTLite_setup_x86.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NTLite_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files\NTLite\ | |||
| (PID) Process: | (3392) NTLite_setup_x86.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NTLite_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: NTLite | |||
| (PID) Process: | (3392) NTLite_setup_x86.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\NTLite_is1 |
| Operation: | write | Name: | Inno Setup: User |
Value: admin | |||
Executable files
115
Suspicious files
66
Text files
334
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3392 | NTLite_setup_x86.tmp | C:\Program Files\NTLite\is-28ICF.tmp | — | |
MD5:— | SHA256:— | |||
| 3392 | NTLite_setup_x86.tmp | C:\Program Files\NTLite\is-MEFNH.tmp | — | |
MD5:— | SHA256:— | |||
| 3392 | NTLite_setup_x86.tmp | C:\Program Files\NTLite\is-9RTS4.tmp | — | |
MD5:— | SHA256:— | |||
| 3392 | NTLite_setup_x86.tmp | C:\Program Files\NTLite\HWLists\is-G3LLA.tmp | — | |
MD5:— | SHA256:— | |||
| 3392 | NTLite_setup_x86.tmp | C:\Program Files\NTLite\HWLists\is-0B9UH.tmp | — | |
MD5:— | SHA256:— | |||
| 3392 | NTLite_setup_x86.tmp | C:\Program Files\NTLite\HWLists\is-39A4P.tmp | — | |
MD5:— | SHA256:— | |||
| 3392 | NTLite_setup_x86.tmp | C:\Program Files\NTLite\HWLists\is-1MOTC.tmp | — | |
MD5:— | SHA256:— | |||
| 3392 | NTLite_setup_x86.tmp | C:\Program Files\NTLite\Tools\ApiWrappers\is-3GFMH.tmp | — | |
MD5:— | SHA256:— | |||
| 3392 | NTLite_setup_x86.tmp | C:\Program Files\NTLite\Tools\ApiWrappers\is-C7ABL.tmp | — | |
MD5:— | SHA256:— | |||
| 3392 | NTLite_setup_x86.tmp | C:\Program Files\NTLite\Tools\ApiWrappers\is-8HA3I.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
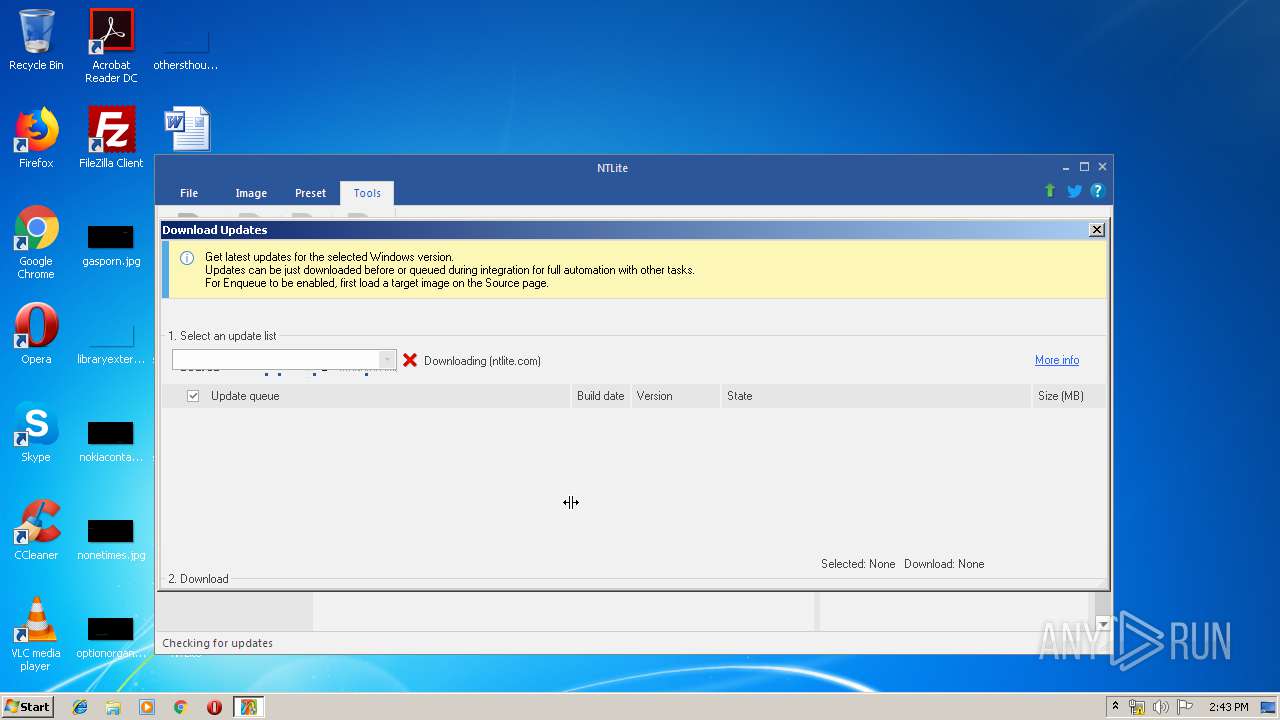
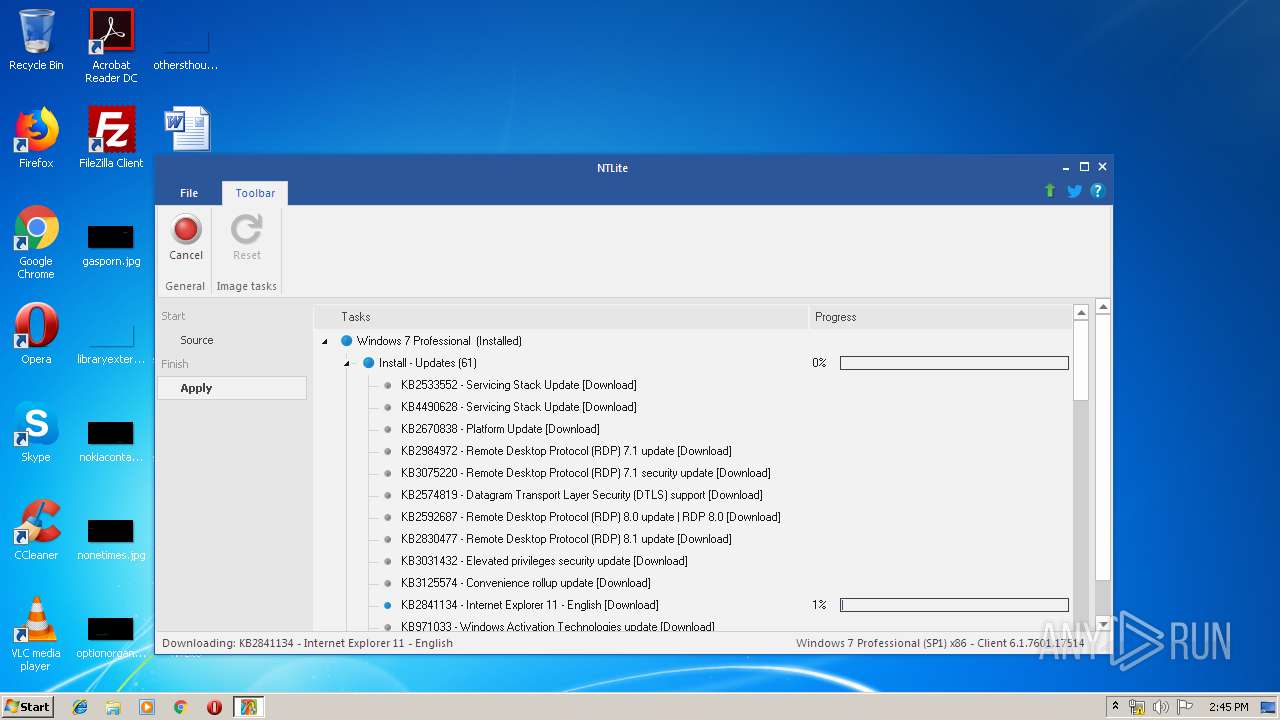
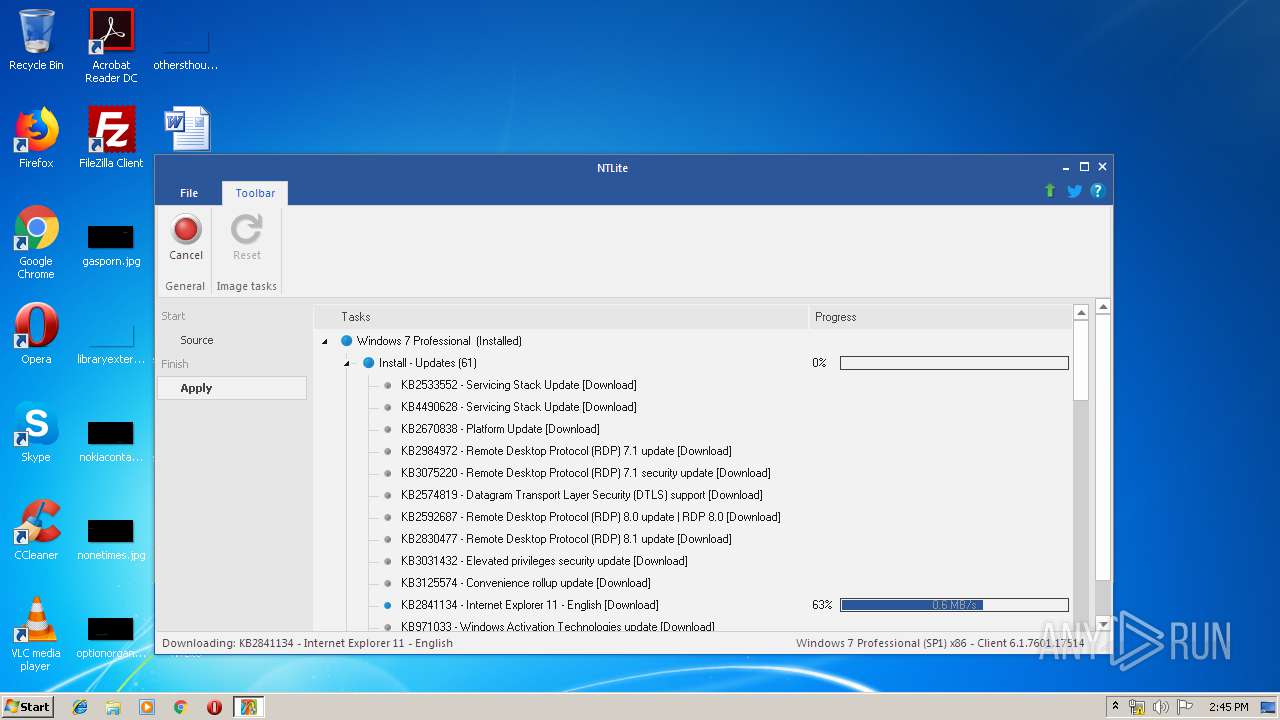
HTTP(S) requests
62
TCP/UDP connections
60
DNS requests
7
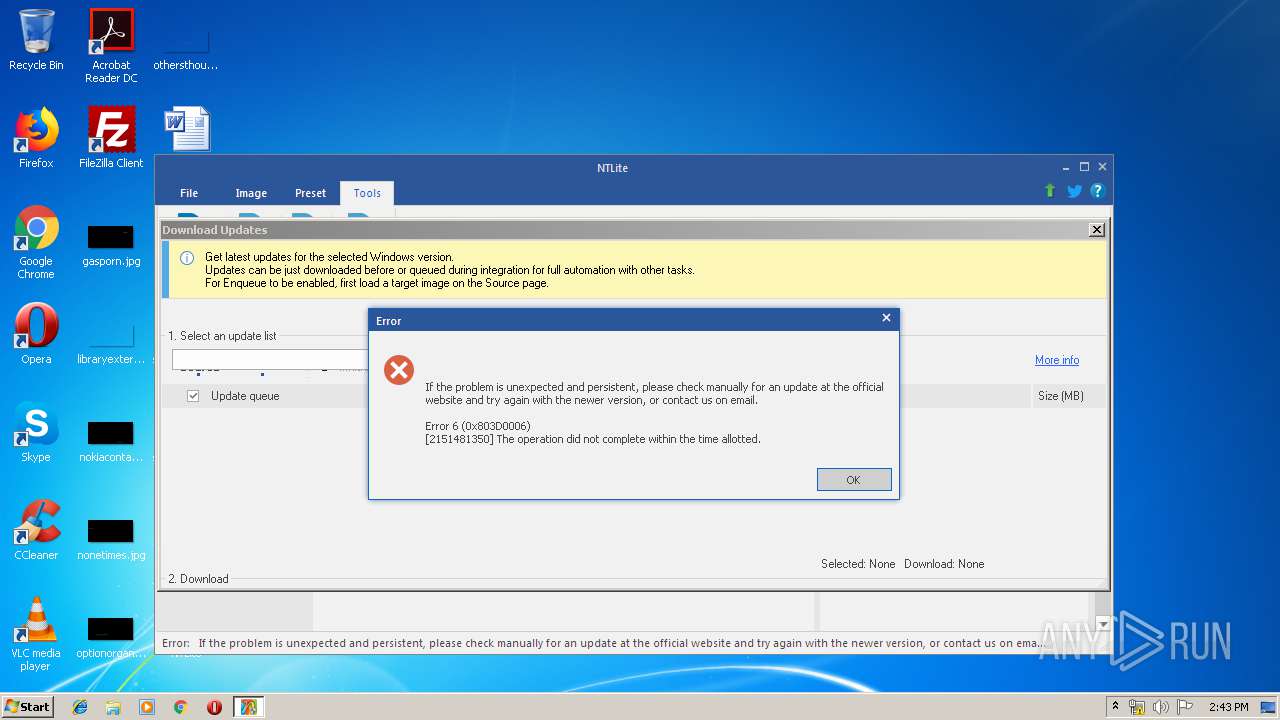
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
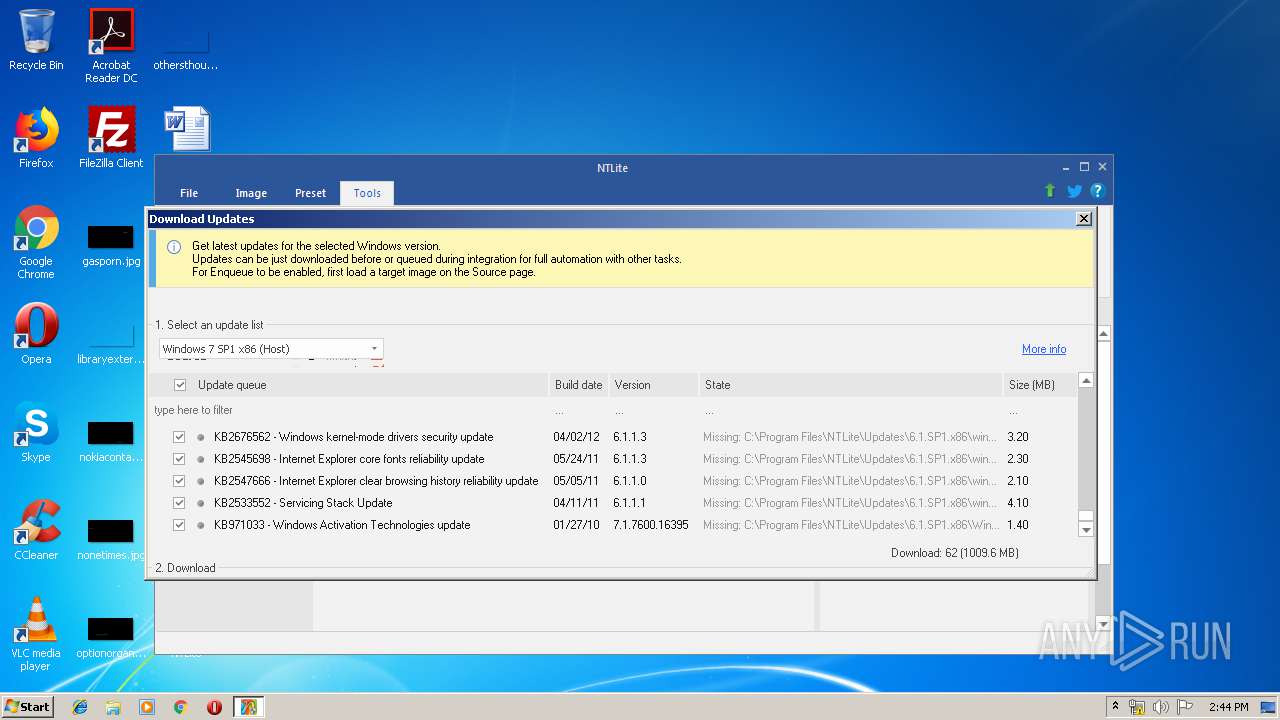
2368 | NTLite.exe | GET | — | 8.241.9.254:80 | http://download.windowsupdate.com/c/msdownload/update/software/updt/2013/06/windows6.1-kb2574819-v2-x86_219ef0b5d7e89489e3f0f01e264ec576cc3d66ad.msu | US | — | — | whitelisted |
2368 | NTLite.exe | GET | — | 8.241.9.254:80 | http://download.windowsupdate.com/msdownload/update/software/ftpk/2013/02/windows6.1-kb2670838-x86_984b8d122a688d917f81c04155225b3ef31f012e.msu | US | — | — | whitelisted |
2368 | NTLite.exe | GET | — | 8.241.9.254:80 | http://download.windowsupdate.com/msdownload/update/software/updt/2012/10/windows6.1-kb2592687-x86_4c11d26c8e1824643ce1caf60c30693d6536d0a2.msu | US | — | — | whitelisted |
— | — | GET | — | 13.107.4.50:80 | http://www.download.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab | US | — | — | whitelisted |
2368 | NTLite.exe | GET | — | 2.18.233.19:80 | http://download.microsoft.com/download/9/2/F/92FC119C-3BCD-476C-B425-038A39625558/IE11-Windows6.1-x86-en-us.exe | unknown | — | — | whitelisted |
2368 | NTLite.exe | GET | — | 8.241.9.254:80 | http://download.windowsupdate.com/msdownload/update/software/crup/2011/05/windows6.1-kb2533552-x86_f2061d1c40b34f88efbe55adf6803d278aa67064.msu | US | — | — | whitelisted |
2368 | NTLite.exe | GET | — | 92.122.213.217:80 | http://download.windowsupdate.com/c/msdownload/update/software/secu/2016/09/ie11-windows6.1-kb3185319-x86_cd4081249bd098b0244fef6e9dfb8ee5674f1fcd.msu | unknown | — | — | whitelisted |
2368 | NTLite.exe | GET | — | 8.241.9.254:80 | http://download.windowsupdate.com/msdownload/update/software/updt/2012/11/windows6.1-kb2685813-x86_d2c51b6b97d4ffcb069bcaafbff3135e96fe18e5.msu | US | — | — | whitelisted |
2368 | NTLite.exe | GET | — | 8.241.9.254:80 | http://download.windowsupdate.com/msdownload/update/software/updt/2012/09/windows6.1-kb2729094-v2-x86_565e7f2a6562ace748c5b6165aa342a11c96aa98.msu | US | — | — | whitelisted |
2368 | NTLite.exe | GET | — | 8.241.9.254:80 | http://download.windowsupdate.com/msdownload/update/software/updt/2013/01/windows6.1-kb2773072-x86_2e4f322442fe5f2ca2819f0052b164e9bbcd0f36.msu | US | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2368 | NTLite.exe | 93.104.208.59:443 | licensing.ntlite.com | M-net Telekommunikations GmbH | DE | unknown |
— | — | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
2368 | NTLite.exe | 2.18.233.19:80 | download.microsoft.com | Akamai International B.V. | — | whitelisted |
2368 | NTLite.exe | 13.107.4.50:80 | www.download.windowsupdate.com | Microsoft Corporation | US | whitelisted |
2368 | NTLite.exe | 8.241.9.254:80 | download.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
2368 | NTLite.exe | 92.122.213.217:80 | download.windowsupdate.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
licensing.ntlite.com |
| suspicious |
www.download.windowsupdate.com |
| whitelisted |
download.microsoft.com |
| whitelisted |
download.windowsupdate.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2368 | NTLite.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
Process | Message |
|---|---|
NTLite.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
NTLite.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
NTLite.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
NTLite.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
Dism.exe | PID=3020 Instantiating the Provider Store. - CDISMImageSession::get_ProviderStore |
Dism.exe | PID=3020 Initializing a provider store for the LOCAL session type. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=3020 Attempting to initialize the logger from the Image Session. - CDISMProviderStore::Final_OnConnect |
Dism.exe | PID=3020 Provider has not previously been encountered. Attempting to initialize the provider. - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=3020 Loading Provider from location C:\Windows\System32\Dism\LogProvider.dll - CDISMProviderStore::Internal_GetProvider |
Dism.exe | PID=3020 Getting Provider OSServices - CDISMProviderStore::GetProvider |