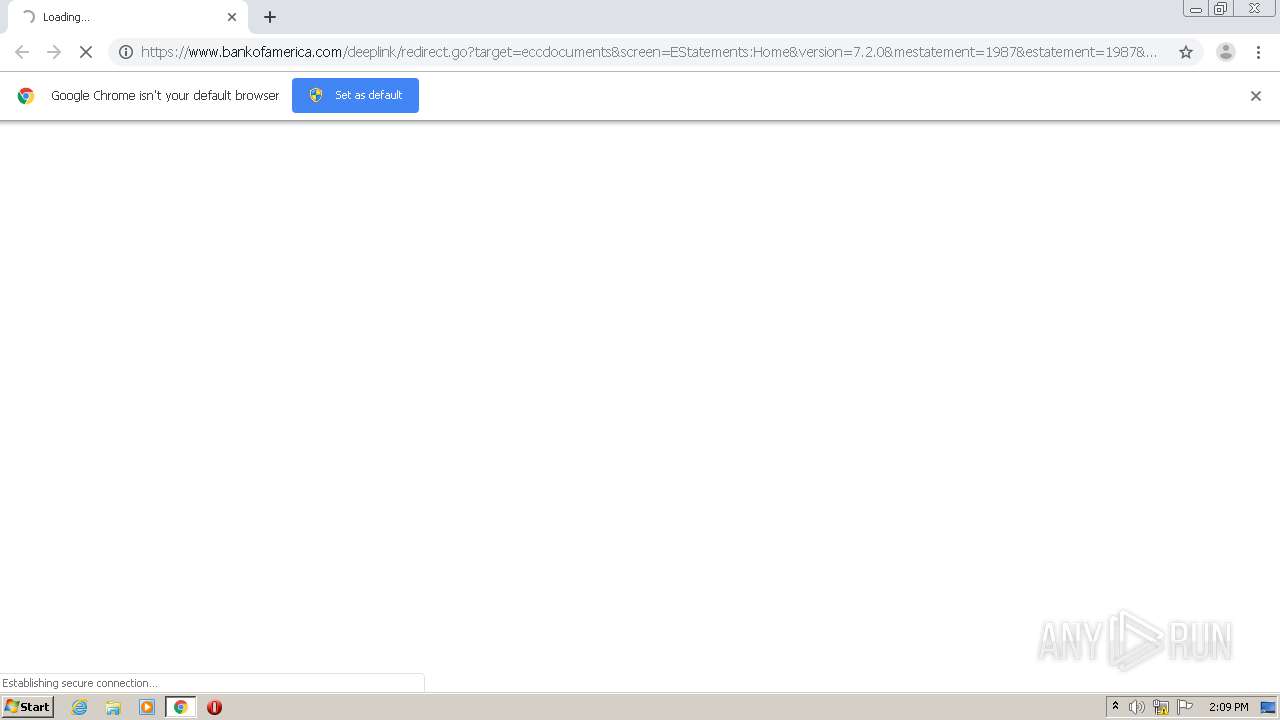
| URL: | https://www.bankofamerica.com/deeplink/redirect.go?target=eccdocuments&screen=EStatements:Home&version=7.2.0&mestatement=1987&estatement=1987&documentId=202011112020120122244396322610010010&popupFlag=y&documentReceivedDate=11302020&cm_mmc=OLB-eStatements-_-email-_-O524LT0001_email_ConsumerDepositStatements-_-EDCP&source=dep_stmt |
| Full analysis: | https://app.any.run/tasks/513d98d3-8a43-4028-bfa7-9575f5710807 |
| Verdict: | No threats detected |
| Analysis date: | December 07, 2020, 14:09:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A585053296EC38F9B892BBA48B3223F1 |
| SHA1: | 0B094CFC7F0E8275F3145343AB5DAFD35EA1421B |
| SHA256: | DC2D13BA93338713859E4F57DCE19CC54E23D0505D8094B9AD653C221FBEF563 |
| SSDEEP: | 6:2OLkHAhXYjXLMs94YRVFmZRRZRRBKJvGVMJ/NIxH8VtVaGYRCIAfrt2Kl4ApRCID:27nAERVFSRRZRR8/PmH8VtVGRLAR2KlR |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Application launched itself
- chrome.exe (PID: 2212)
Reads the hosts file
- chrome.exe (PID: 2512)
- chrome.exe (PID: 2212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
48
Monitored processes
12
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 628 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1048,5699848419021915196,14789827896469706216,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgACAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=6110338373482747164 --mojo-platform-channel-handle=1040 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 836 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,5699848419021915196,14789827896469706216,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3614228412722688641 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2136 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 964 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=2192 --on-initialized-event-handle=316 --parent-handle=320 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1016 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,5699848419021915196,14789827896469706216,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=7918155177631221315 --renderer-client-id=4 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2348 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1800 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,5699848419021915196,14789827896469706216,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17766556175076066234 --renderer-client-id=9 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2756 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2212 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://www.bankofamerica.com/deeplink/redirect.go?target=eccdocuments&screen=EStatements:Home&version=7.2.0&mestatement=1987&estatement=1987&documentId=202011112020120122244396322610010010&popupFlag=y&documentReceivedDate=11302020&cm_mmc=OLB-eStatements-_-email-_-O524LT0001_email_ConsumerDepositStatements-_-EDCP&source=dep_stmt" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2488 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,5699848419021915196,14789827896469706216,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=2219461076695858060 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3304 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2512 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,5699848419021915196,14789827896469706216,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=network --service-request-channel-token=12316267473485470687 --mojo-platform-channel-handle=1540 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2868 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1048,5699848419021915196,14789827896469706216,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=18137048156348462635 --mojo-platform-channel-handle=1924 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 3164 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1048,5699848419021915196,14789827896469706216,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=17305793459604779739 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2184 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
595
Read events
541
Write events
51
Delete events
3
Modification events
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (964) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | write | Name: | 2212-13251823773779000 |
Value: 259 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2212) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BrowserExitCodes |
| Operation: | delete value | Name: | 3252-13245750958665039 |
Value: 0 | |||
Executable files
0
Suspicious files
39
Text files
60
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5FCE379E-8A4.pma | — | |
MD5:— | SHA256:— | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\LOG.old~RF15aa72.TMP | — | |
MD5:— | SHA256:— | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\4c2db9e6-8f80-4a1e-93ec-8a5259d25ab8.tmp | — | |
MD5:— | SHA256:— | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\data_reduction_proxy_leveldb\000048.dbtmp | — | |
MD5:— | SHA256:— | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RF15aa63.TMP | text | |
MD5:C2DDBA63E4A2BD2E39A8B6C2C6384AAE | SHA256:6D5C1C78341C6F84911055D970ADDB0EC3499F8BF7FADE062122A22209CE67D9 | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Feature Engagement Tracker\EventDB\LOG.old | text | |
MD5:1C97B70A4BAD7C026F79467C7D496AFA | SHA256:C5A02E4984DE3F30DADFC0A89A93F45418C06653C3962EAA94C93909E51D272D | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:C2DDBA63E4A2BD2E39A8B6C2C6384AAE | SHA256:6D5C1C78341C6F84911055D970ADDB0EC3499F8BF7FADE062122A22209CE67D9 | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 2212 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\shared_proto_db\LOG.old~RF15acb4.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
29
DNS requests
18
Threats
10
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2512 | chrome.exe | GET | 200 | 184.24.10.146:80 | http://ocsp.entrust.net/MEUwQzBBMD8wPTAJBgUrDgMCGgUABBQsSqZpWQuWOxHU9pAda%2B7Lf6V20AQUaJDkZ6SmU4DHhmak8fdLQ%2FuEvW0CBFHTQEQ%3D | US | der | 1.53 Kb | whitelisted |
2512 | chrome.exe | GET | 200 | 184.24.10.146:80 | http://ocsp.entrust.net/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQnuEQcScL%2FkljKed%2BRzpzFYOq9kwQUw%2FfQtSowra8NkSFwOVTdvIlwxzoCEF17h6R1%2FJ9%2FchZ1HIYpmak%3D | US | der | 1.55 Kb | whitelisted |
2512 | chrome.exe | GET | 200 | 184.24.10.146:80 | http://ocsp.entrust.net/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQnuEQcScL%2FkljKed%2BRzpzFYOq9kwQUw%2FfQtSowra8NkSFwOVTdvIlwxzoCEGgu1ChalKokpbdrws6Cr4U%3D | US | der | 1.55 Kb | whitelisted |
2512 | chrome.exe | GET | 200 | 184.24.10.146:80 | http://ocsp.entrust.net/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQnuEQcScL%2FkljKed%2BRzpzFYOq9kwQUw%2FfQtSowra8NkSFwOVTdvIlwxzoCEAo7x5dx%2FACOdgqCW%2BYHhU8%3D | US | der | 1.55 Kb | whitelisted |
2512 | chrome.exe | GET | 200 | 184.24.10.146:80 | http://ocsp.entrust.net/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBQnuEQcScL%2FkljKed%2BRzpzFYOq9kwQUw%2FfQtSowra8NkSFwOVTdvIlwxzoCEQD2bMk7hsqhtgAAAABU0O1n | US | der | 1.55 Kb | whitelisted |
2512 | chrome.exe | GET | 200 | 184.24.10.146:80 | http://ocsp.entrust.net/MEUwQzBBMD8wPTAJBgUrDgMCGgUABBQsSqZpWQuWOxHU9pAda%2B7Lf6V20AQUaJDkZ6SmU4DHhmak8fdLQ%2FuEvW0CBFHTQEQ%3D | US | der | 1.53 Kb | whitelisted |
2512 | chrome.exe | GET | 200 | 184.24.10.146:80 | http://ocsp.entrust.net/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQnuEQcScL%2FkljKed%2BRzpzFYOq9kwQUw%2FfQtSowra8NkSFwOVTdvIlwxzoCEAwADgvqjyotNiN2j1u%2B%2FFs%3D | US | der | 1.55 Kb | whitelisted |
2512 | chrome.exe | GET | 200 | 184.24.10.146:80 | http://ocsp.entrust.net/MEUwQzBBMD8wPTAJBgUrDgMCGgUABBQsSqZpWQuWOxHU9pAda%2B7Lf6V20AQUaJDkZ6SmU4DHhmak8fdLQ%2FuEvW0CBFHTQEQ%3D | US | der | 1.53 Kb | whitelisted |
2512 | chrome.exe | GET | 200 | 184.24.10.146:80 | http://ocsp.entrust.net/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQnuEQcScL%2FkljKed%2BRzpzFYOq9kwQUw%2FfQtSowra8NkSFwOVTdvIlwxzoCEEaYqOZGezmAbCrvNq5zOg4%3D | US | der | 1.55 Kb | whitelisted |
2512 | chrome.exe | GET | 200 | 184.24.10.146:80 | http://ocsp.entrust.net/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQnuEQcScL%2FkljKed%2BRzpzFYOq9kwQUw%2FfQtSowra8NkSFwOVTdvIlwxzoCEAQXLCk02GztDUu%2BYyzNizE%3D | US | der | 1.55 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
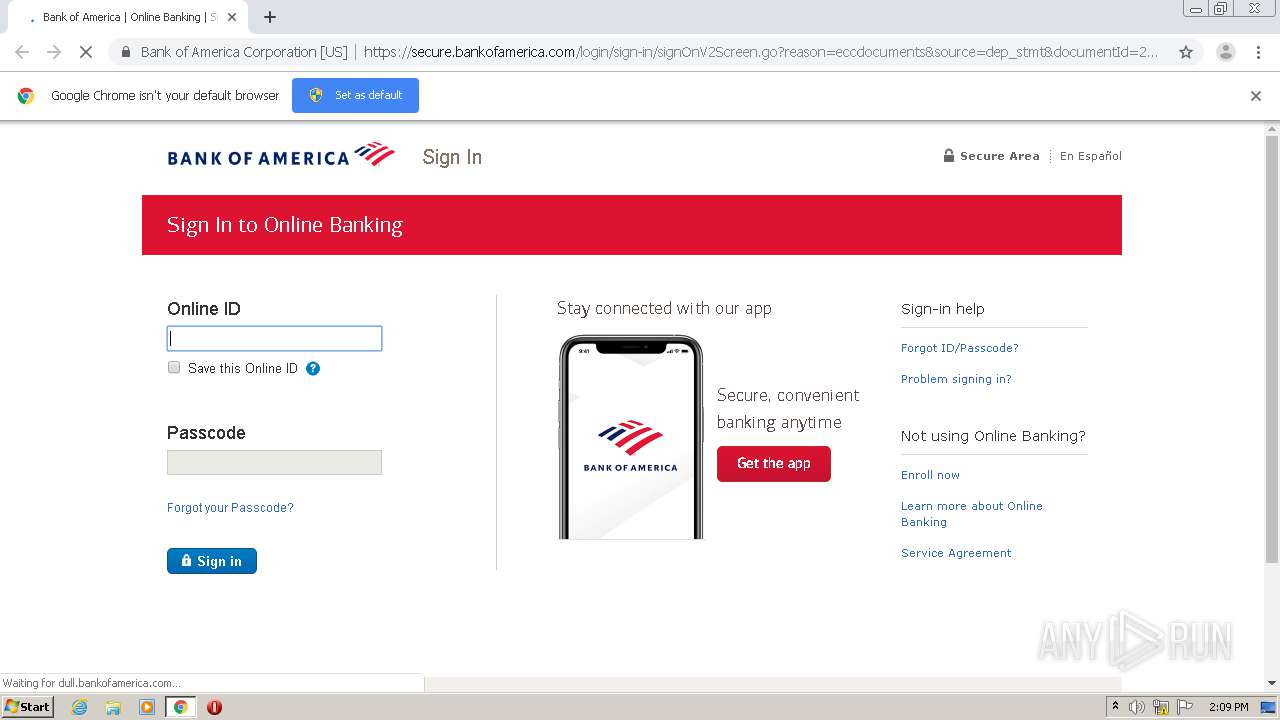
2512 | chrome.exe | 171.161.102.100:443 | www.bankofamerica.com | — | US | suspicious |
2512 | chrome.exe | 172.217.18.109:443 | accounts.google.com | Google Inc. | US | suspicious |
2512 | chrome.exe | 184.24.10.146:80 | ocsp.entrust.net | Bharti Airtel Ltd., Telemedia Services | US | unknown |
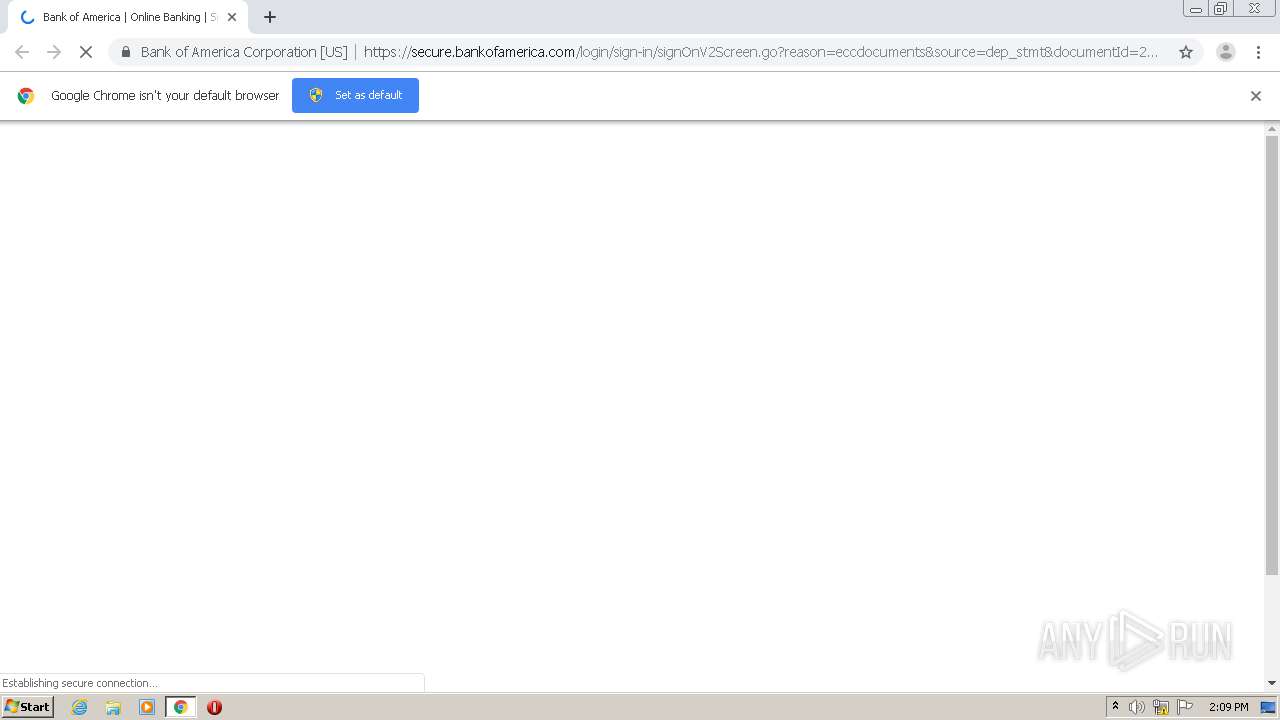
2512 | chrome.exe | 171.161.118.200:443 | secure.bankofamerica.com | — | US | unknown |
2512 | chrome.exe | 172.217.16.202:443 | safebrowsing.googleapis.com | Google Inc. | US | whitelisted |
2512 | chrome.exe | 3.250.252.43:443 | dpm.demdex.net | — | US | unknown |
2512 | chrome.exe | 52.71.213.209:443 | boss.bankofamerica.com | Amazon.com, Inc. | US | unknown |
2512 | chrome.exe | 52.201.76.21:443 | aero.bankofamerica.com | Amazon.com, Inc. | US | unknown |
2512 | chrome.exe | 52.213.168.74:443 | bankofamerica.tt.omtrdc.net | Amazon.com, Inc. | IE | unknown |
2512 | chrome.exe | 35.168.177.43:443 | dull.bankofamerica.com | Amazon.com, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bankofamerica.com |
| whitelisted |
accounts.google.com |
| shared |
ocsp.entrust.net |
| whitelisted |
secure.bankofamerica.com |
| suspicious |
safebrowsing.googleapis.com |
| whitelisted |
dpm.demdex.net |
| whitelisted |
bankofamerica.tt.omtrdc.net |
| whitelisted |
aero.bankofamerica.com |
| suspicious |
boss.bankofamerica.com |
| unknown |
dull.bankofamerica.com |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2512 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2512 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
2512 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2512 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
2512 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2512 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
2512 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2512 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |
2512 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Request) |
2512 | chrome.exe | Attempted User Privilege Gain | ET INFO Session Traversal Utilities for NAT (STUN Binding Response) |