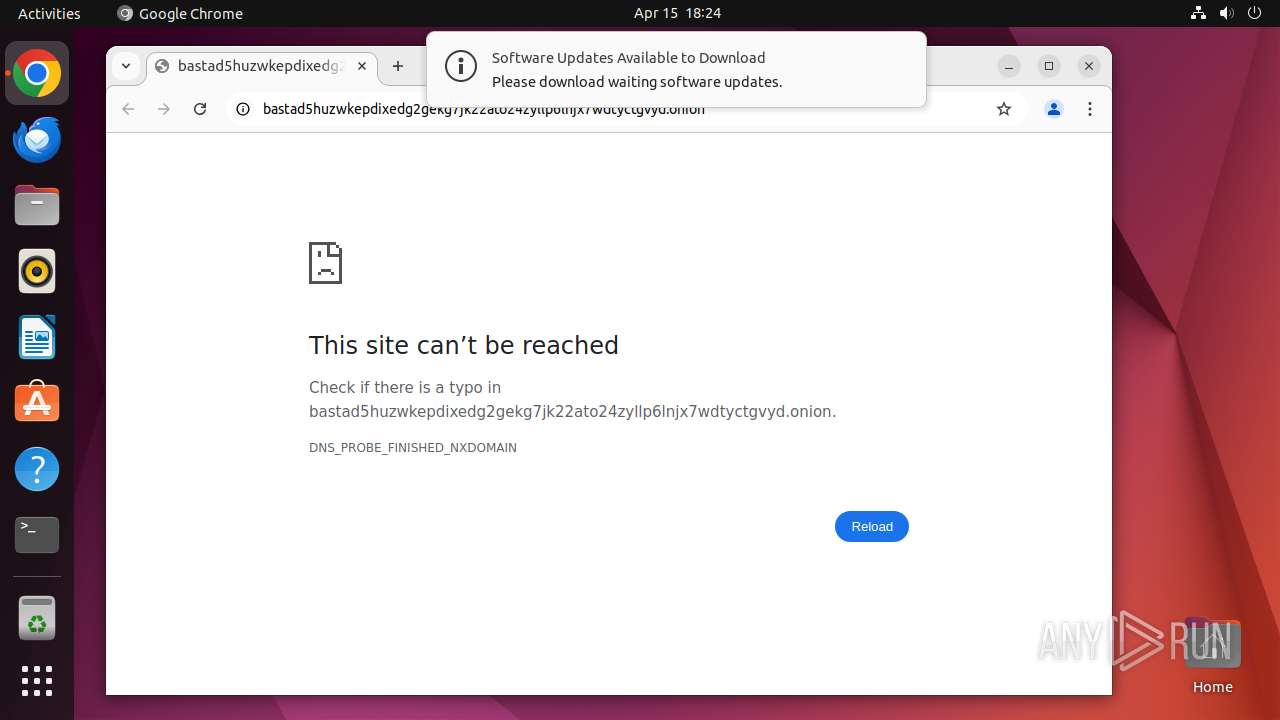
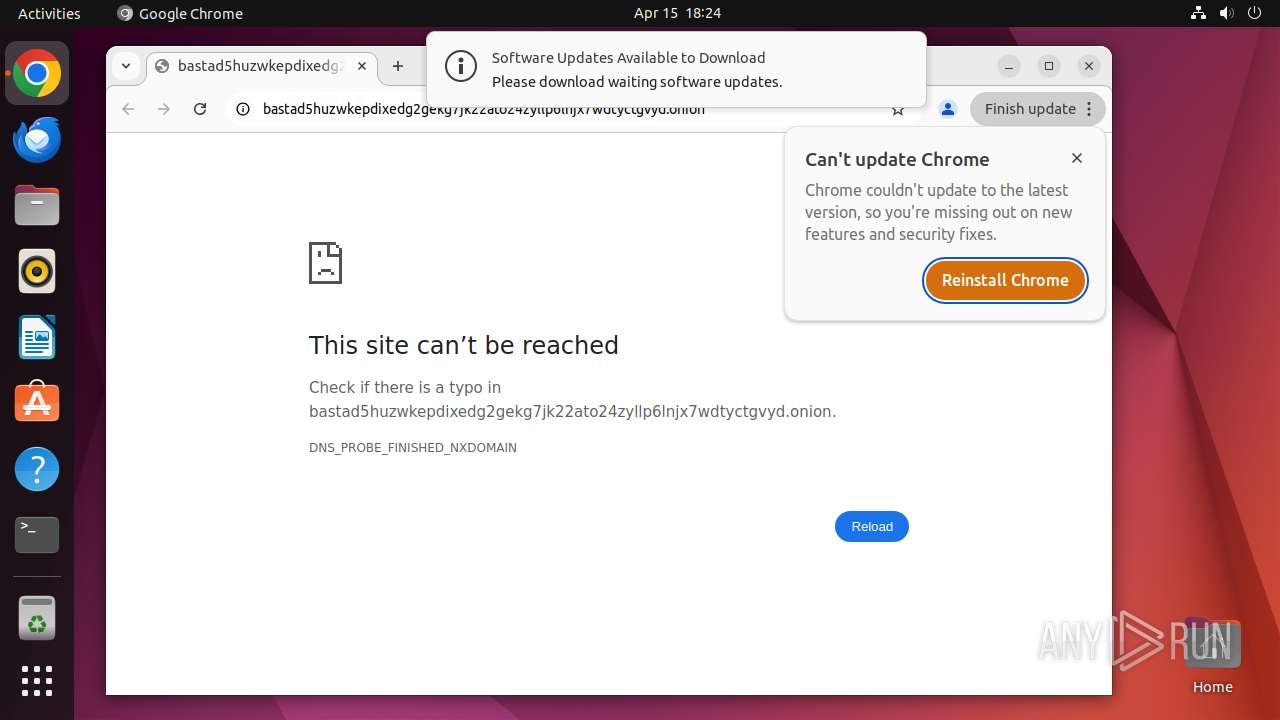
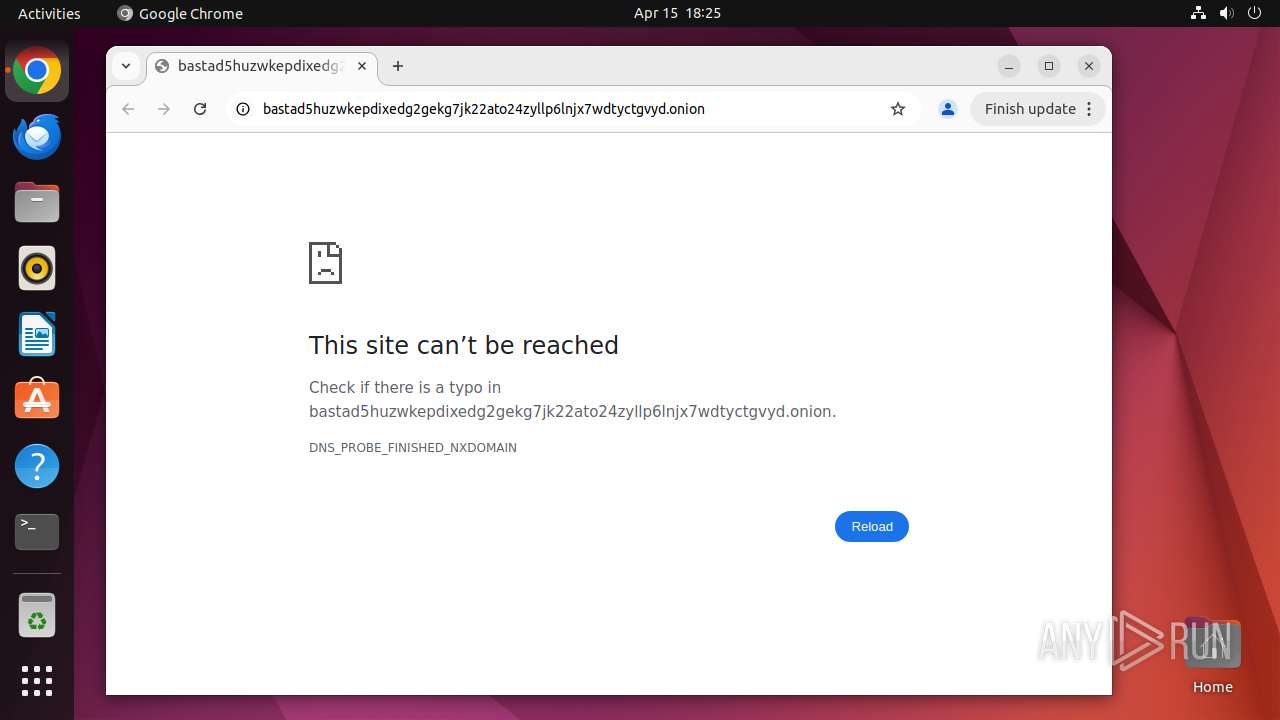
| URL: | https://bastad5huzwkepdixedg2gekg7jk22ato24zyllp6lnjx7wdtyctgvyd.onion/ |
| Full analysis: | https://app.any.run/tasks/33edccb2-a393-4f42-830a-64d501181047 |
| Verdict: | Malicious activity |
| Analysis date: | April 15, 2025, 17:24:40 |
| OS: | Ubuntu 22.04.2 |
| MD5: | 0B9CC54B47BC95514AAF50F2544DD8BD |
| SHA1: | 3E0036EC4BE6A67DB662D81B0253757E9E0982C0 |
| SHA256: | DC24A5764AC51521F460D13EFE7F262A78245B51D501FBF964C99E48B87FA277 |
| SSDEEP: | 3:N8MjABCXCrgBf4bFjcGawFn:2oXCUWFj3RFn |
MALICIOUS
No malicious indicators.SUSPICIOUS
Executes commands using command-line interpreter
- sudo (PID: 40656)
- chrome (PID: 40657)
Potential Corporate Privacy Violation
- systemd-resolved (PID: 445)
INFO
Checks timezone
- chrome (PID: 40657)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
333
Monitored processes
114
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 445 | /lib/systemd/systemd-resolved | /usr/lib/systemd/systemd-resolved | systemd | |
User: systemd-resolve Integrity Level: UNKNOWN | ||||
| 40655 | /bin/sh -c "DISPLAY=:0 sudo -iu user google-chrome https://bastad5huzwkepdixedg2gekg7jk22ato24zyllp6lnjx7wdtyctgvyd\.onion/ " | /usr/bin/dash | — | any-guest-agent |
User: root Integrity Level: UNKNOWN | ||||
| 40656 | sudo -iu user google-chrome https://bastad5huzwkepdixedg2gekg7jk22ato24zyllp6lnjx7wdtyctgvyd.onion/ | /usr/bin/sudo | — | dash |
User: root Integrity Level: UNKNOWN | ||||
| 40657 | /usr/bin/google-chrome https://bastad5huzwkepdixedg2gekg7jk22ato24zyllp6lnjx7wdtyctgvyd.onion/ | /opt/google/chrome/chrome | sudo | |
User: user Integrity Level: UNKNOWN | ||||
| 40658 | /usr/bin/locale-check C.UTF-8 | /usr/bin/locale-check | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40659 | readlink -f /usr/bin/google-chrome | /usr/bin/readlink | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40660 | dirname /opt/google/chrome/google-chrome | /usr/bin/dirname | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40661 | mkdir -p /home/user/.local/share/applications | /usr/bin/mkdir | — | chrome |
User: user Integrity Level: UNKNOWN Exit code: 0 | ||||
| 40662 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
| 40663 | cat | /usr/bin/cat | — | chrome |
User: user Integrity Level: UNKNOWN | ||||
Executable files
12
Suspicious files
220
Text files
20
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 40657 | chrome | /home/user/.config/google-chrome/ShaderCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 40657 | chrome | /home/user/.config/google-chrome/ShaderCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 40657 | chrome | /home/user/.config/google-chrome/ShaderCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 40657 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_3 | binary | |
MD5:— | SHA256:— | |||
| 40657 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_2 | binary | |
MD5:— | SHA256:— | |||
| 40657 | chrome | /home/user/.config/google-chrome/Default/GPUCache/data_0 | binary | |
MD5:— | SHA256:— | |||
| 40700 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 40779 | chrome | /home/user/.cache/mesa_shader_cache/index | binary | |
MD5:— | SHA256:— | |||
| 40657 | chrome | /home/user/.config/google-chrome/Default/History | binary | |
MD5:— | SHA256:— | |||
| 40657 | chrome | /home/user/.config/google-chrome/Default/DawnWebGPUCache/data_3 | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
14
TCP/UDP connections
36
DNS requests
243
Threats
216
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
40703 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adnwswi5bi3pd3idmkzwee46s2gq_2025.3.26.1143/ggkkehgbnfjpeggfpleeakpidbkibbmn_2025.3.26.1143_all_k7ciobm2xv32lbqoijkr6ievde.crx3 | unknown | — | — | whitelisted |
— | — | GET | 204 | 91.189.91.98:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
— | — | GET | 204 | 91.189.91.98:80 | http://connectivity-check.ubuntu.com/ | unknown | — | — | whitelisted |
40703 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aclxnidwwkj5di3vduduj2gqpgpq_4.10.2891.0/oimompecagnajdejgnnjijobebaeigek_4.10.2891.0_linux_b4hin3q5s66ws2322cyyfp35lu.crx3 | unknown | — | — | whitelisted |
40703 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adp7lmscefogeldj4te6xerqth3a_9.55.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.55.0_all_ocm7dvbavb37zglvqhfr5kszse.crx3 | unknown | — | — | whitelisted |
40703 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/acs377hx5nmoxskleksnzmwt6fca_500/lmelglejhemejginpboagddgdfbepgmp_500_all_ZZ_acltzyywp2rl2nsp5dezar5dk4oa.crx3 | unknown | — | — | whitelisted |
40703 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/p4hk7t7ztumoqzhiq26rtjdhc4_3068/jflookgnkcckhobaglndicnbbgbonegd_3068_all_lvzxw5k2be7wzytqtigjjre2qy.crx3 | unknown | — | — | whitelisted |
40703 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adpfsmx3jx54vc56xzsioflc3uiq_1283/efniojlnjndmcbiieegkicadnoecjjef_1283_all_oox2w4oahqh2damefcaxtqzrzu.crx3 | unknown | — | — | whitelisted |
40703 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ngifsy4k4mu7bcrdyhc4vjaocy_2025.4.2.0/gonpemdgkjcecdgbnaabipppbmgfggbe_2025.04.02.00_all_adnkhxd45xqajkfutwmwv6agl33q.crx3 | unknown | — | — | whitelisted |
40703 | chrome | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/m5jeg4otebjue2x5zve5fxse7i_2025.4.14.1/jflhchccmppkfebkiaminageehmchikm_2025.04.14.01_all_gw3lyksyqcxidjes5zuqycb36q.crx3 | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 91.189.91.98:80 | — | Canonical Group Limited | US | unknown |
484 | avahi-daemon | 224.0.0.251:5353 | — | — | — | unknown |
— | — | 37.19.194.81:443 | odrs.gnome.org | Datacamp Limited | DE | whitelisted |
512 | snapd | 185.125.188.58:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
512 | snapd | 185.125.188.54:443 | api.snapcraft.io | Canonical Group Limited | GB | whitelisted |
40703 | chrome | 172.217.16.131:443 | clientservices.googleapis.com | GOOGLE | US | whitelisted |
40703 | chrome | 142.250.185.170:443 | safebrowsingohttpgateway.googleapis.com | GOOGLE | US | whitelisted |
40703 | chrome | 142.250.153.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
40703 | chrome | 151.101.129.91:443 | google-ohttp-relay-safebrowsing.fastly-edge.com | FASTLY | US | unknown |
40703 | chrome | 172.217.18.3:443 | update.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
odrs.gnome.org |
| whitelisted |
api.snapcraft.io |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
safebrowsingohttpgateway.googleapis.com |
| whitelisted |
bastad5huzwkepdixedg2gekg7jk22ato24zyllp6lnjx7wdtyctgvyd.onion |
| unknown |
accounts.google.com |
| whitelisted |
google-ohttp-relay-safebrowsing.fastly-edge.com |
| unknown |
update.googleapis.com |
| whitelisted |
8.100.168.192.in-addr.arpa |
| unknown |
Threats
PID | Process | Class | Message |
|---|---|---|---|
445 | systemd-resolved | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
445 | systemd-resolved | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
445 | systemd-resolved | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
445 | systemd-resolved | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
445 | systemd-resolved | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
445 | systemd-resolved | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
445 | systemd-resolved | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
445 | systemd-resolved | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
445 | systemd-resolved | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |
445 | systemd-resolved | Potential Corporate Privacy Violation | ET INFO DNS Query for TOR Hidden Domain .onion Accessible Via TOR |