| File name: | SKv1101015.msi |
| Full analysis: | https://app.any.run/tasks/c4087fec-18a0-44ca-be52-21bc0aca2652 |
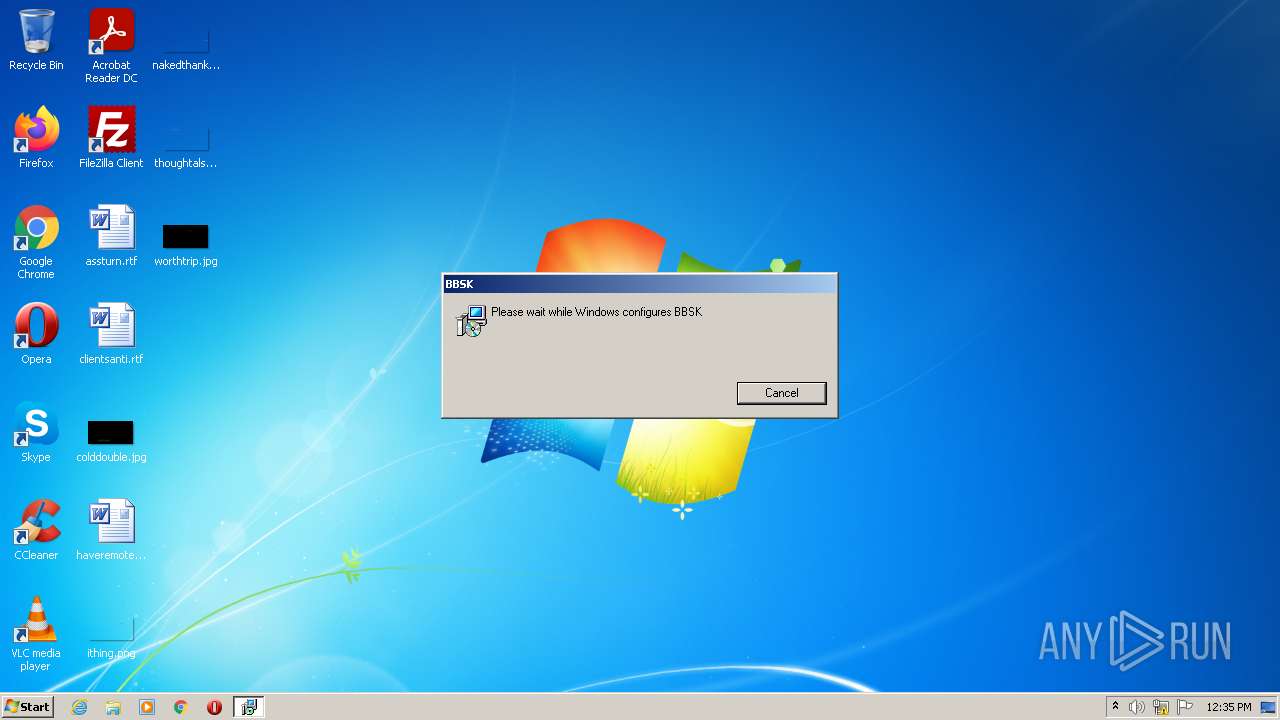
| Verdict: | Malicious activity |
| Analysis date: | March 23, 2022, 12:35:37 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-msi |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, MSI Installer, Last Printed: Fri Dec 11 11:47:44 2009, Create Time/Date: Fri Dec 11 11:47:44 2009, Last Saved Time/Date: Fri Dec 11 11:47:44 2009, Security: 0, Code page: 1252, Revision Number: {B240EF31-C639-4DDD-80B6-96D833D8EBD9}, Number of Words: 10, Subject: BBSK, Author: Drake Media Inc., Name of Creating Application: Advanced Installer 15.2 build 30c2e84376, Template: ;1033, Comments: This installer database contains the logic and data required to install BBSK., Title: Installation Database, Keywords: Installer, MSI, Database, Number of Pages: 200 |
| MD5: | 58322CC0D504DE7B8C105A1AD4835819 |
| SHA1: | A3EACAB0D427BE9C962D86E93C04CD59D6DC65AF |
| SHA256: | DC1982B083F3629E55D3BC6A057487C492A70ECA3DEB9306B30CAF70090B9F8C |
| SSDEEP: | 24576:tRCYL/jGiz0DDNgTFSA/iqZs6AUm25+rAoKH+VUTlJ33ojm1oNgHJrJ9CzS:tRCYXGiQnNgTFSA6qZs6AC5+rAllxEoQ |
MALICIOUS
Changes the autorun value in the registry
- msiexec.exe (PID: 2252)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 872)
Actions looks like stealing of personal data
- powershell.exe (PID: 2104)
SUSPICIOUS
Executed as Windows Service
- msiexec.exe (PID: 2252)
- vssvc.exe (PID: 2696)
Reads Windows owner or organization settings
- msiexec.exe (PID: 2824)
- msiexec.exe (PID: 2252)
Reads the Windows organization settings
- msiexec.exe (PID: 2824)
- msiexec.exe (PID: 2252)
Searches for installed software
- msiexec.exe (PID: 2252)
Application launched itself
- msiexec.exe (PID: 2252)
Executes PowerShell scripts
- MsiExec.exe (PID: 872)
- MSI4D9.tmp (PID: 3460)
Reads Environment values
- MsiExec.exe (PID: 872)
- powershell.exe (PID: 3912)
- MSI4D9.tmp (PID: 3460)
- vssvc.exe (PID: 2696)
- powershell.exe (PID: 2104)
- powershell.exe (PID: 700)
Reads the computer name
- powershell.exe (PID: 3912)
- MSI4D9.tmp (PID: 3460)
- powershell.exe (PID: 700)
- powershell.exe (PID: 2104)
Creates files in the user directory
- msiexec.exe (PID: 2252)
Checks supported languages
- powershell.exe (PID: 3912)
- MSI4D9.tmp (PID: 3460)
- powershell.exe (PID: 2104)
- powershell.exe (PID: 700)
Drops a file with a compile date too recent
- msiexec.exe (PID: 2252)
Drops a file that was compiled in debug mode
- msiexec.exe (PID: 2252)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2252)
Creates a software uninstall entry
- msiexec.exe (PID: 2252)
Drops a file with too old compile date
- msiexec.exe (PID: 2252)
INFO
Checks supported languages
- vssvc.exe (PID: 2696)
- msiexec.exe (PID: 2824)
- MsiExec.exe (PID: 872)
- msiexec.exe (PID: 2252)
Checks Windows Trust Settings
- msiexec.exe (PID: 2252)
- msiexec.exe (PID: 2824)
- powershell.exe (PID: 3912)
- powershell.exe (PID: 700)
- powershell.exe (PID: 2104)
Reads settings of System Certificates
- msiexec.exe (PID: 2824)
- msiexec.exe (PID: 2252)
- powershell.exe (PID: 3912)
- powershell.exe (PID: 700)
Reads the computer name
- msiexec.exe (PID: 2252)
- vssvc.exe (PID: 2696)
- MsiExec.exe (PID: 872)
- msiexec.exe (PID: 2824)
Starts application with an unusual extension
- msiexec.exe (PID: 2252)
Application was dropped or rewritten from another process
- MSI4D9.tmp (PID: 3460)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msi | | | Microsoft Windows Installer (81.9) |
|---|---|---|
| .mst | | | Windows SDK Setup Transform Script (9.2) |
| .msp | | | Windows Installer Patch (7.6) |
| .msi | | | Microsoft Installer (100) |
EXIF
FlashPix
| Pages: | 200 |
|---|---|
| Keywords: | Installer, MSI, Database |
| Title: | Installation Database |
| Comments: | This installer database contains the logic and data required to install BBSK. |
| Template: | ;1033 |
| Software: | Advanced Installer 15.2 build 30c2e84376 |
| LastModifiedBy: | - |
| Author: | Drake Media Inc. |
| Subject: | BBSK |
| Words: | 10 |
| RevisionNumber: | {B240EF31-C639-4DDD-80B6-96D833D8EBD9} |
| CodePage: | Windows Latin 1 (Western European) |
| Security: | None |
| ModifyDate: | 2009:12:11 11:47:44 |
| CreateDate: | 2009:12:11 11:47:44 |
| LastPrinted: | 2009:12:11 11:47:44 |
Total processes
48
Monitored processes
8
Malicious processes
3
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 700 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss4D7.ps1" | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 872 | C:\Windows\system32\MsiExec.exe -Embedding 38D9A4B1DB568EFCBC24F8D0DFDDFDE8 | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2104 | "C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe" -noninteractive -ExecutionPolicy bypass -c "[Reflection.Assembly]::Load([System.IO.File]::ReadAllBytes('SK.Driver.dll'));[Reflection.Assembly]::Load([System.IO.File]::ReadAllBytes('S.dll'));[sk.S]::Start()" | C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe | MSI4D9.tmp | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 2252 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2696 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft� Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2824 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\SKv1101015.msi" | C:\Windows\System32\msiexec.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows� installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3460 | "C:\Windows\Installer\MSI4D9.tmp" /DontWait /HideWindow /dir "C:\Users\admin\AppData\Roaming\BBSK\" C:\Windows\SysWOW64\WindowsPowerShell\v1.0\powershell.exe -noninteractive -ExecutionPolicy bypass -c "[Reflection.Assembly]::Load([System.IO.File]::ReadAllBytes('SK.Driver.dll'));[Reflection.Assembly]::Load([System.IO.File]::ReadAllBytes('S.dll'));[sk.S]::Start()" | C:\Windows\Installer\MSI4D9.tmp | — | msiexec.exe | |||||||||||
User: admin Company: Caphyon LTD Integrity Level: MEDIUM Description: File that launches another file Exit code: 4294967295 Version: 15.2.0.0 Modules
| |||||||||||||||
| 3912 | -NoProfile -Noninteractive -ExecutionPolicy Bypass -File "C:\Users\admin\AppData\Local\Temp\pss10.ps1" | C:\Windows\system32\WindowsPowerShell\v1.0\powershell.exe | MsiExec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
Total events
17 040
Read events
16 707
Write events
321
Delete events
12
Modification events
| (PID) Process: | (2824) msiexec.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2252) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SystemRestore |
| Operation: | write | Name: | SrCreateRp (Enter) |
Value: 4000000000000000CEBD8F82B23ED801CC080000600D0000D5070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2252) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppCreate (Enter) |
Value: 4000000000000000CEBD8F82B23ED801CC080000600D0000D0070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2252) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\SPP |
| Operation: | write | Name: | LastIndex |
Value: 69 | |||
| (PID) Process: | (2252) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\SPP |
| Operation: | write | Name: | SppGatherWriterMetadata (Enter) |
Value: 40000000000000005A44D782B23ED801CC080000600D0000D3070000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2252) msiexec.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\VssapiPublisher |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000005A44D782B23ED801CC080000F40B0000E8030000010000000000000000000000CF6D06D115F1C04D879A8AC62CF1F0280000000000000000 | |||
| (PID) Process: | (2696) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Shadow Copy Optimization Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000007692E582B23ED801880A00003C0A0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2696) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\Registry Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000007692E582B23ED801880A00005C0E0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2696) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\ASR Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000007692E582B23ED801880A000028020000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2696) vssvc.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\VSS\Diag\COM+ REGDB Writer |
| Operation: | write | Name: | IDENTIFY (Enter) |
Value: 40000000000000007692E582B23ED801880A0000380D0000E8030000010000000100000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
14
Suspicious files
12
Text files
10
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2252 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 872 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\pss10.ps1 | text | |
MD5:— | SHA256:— | |||
| 2252 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFDAB2BF29ED61C813.TMP | gmc | |
MD5:— | SHA256:— | |||
| 2252 | msiexec.exe | C:\System Volume Information\SPP\OnlineMetadataCache\{d1066dcf-f115-4dc0-879a-8ac62cf1f028}_OnDiskSnapshotProp | binary | |
MD5:— | SHA256:— | |||
| 2252 | msiexec.exe | C:\Windows\Installer\13fe3b.ipi | binary | |
MD5:— | SHA256:— | |||
| 2252 | msiexec.exe | C:\Windows\Installer\MSI1.tmp | executable | |
MD5:F0E3167159D38491B01A23BAE32647CA | SHA256:15FB0BDA4E4644D5769B90108C87A469CC75F74113D03240236F272396AA49FB | |||
| 872 | MsiExec.exe | C:\Users\admin\AppData\Local\Temp\pssFFFF.ps1 | text | |
MD5:C601F894AE26402F106645992FF5BE53 | SHA256:D4FE52F4EA0B2F07058900C29B36755AE5305193B9E8D55F510336EFC8FF3CFF | |||
| 3912 | powershell.exe | C:\Users\admin\AppData\Local\Temp\bokb5jdu.0zd.psm1 | binary | |
MD5:C4CA4238A0B923820DCC509A6F75849B | SHA256:— | |||
| 2252 | msiexec.exe | C:\Windows\Installer\MSI21.tmp | executable | |
MD5:F0E3167159D38491B01A23BAE32647CA | SHA256:15FB0BDA4E4644D5769B90108C87A469CC75F74113D03240236F272396AA49FB | |||
| 2252 | msiexec.exe | C:\Windows\Installer\MSIFFA1.tmp | executable | |
MD5:882E26BCE2987A04B0E50EF204466CBE | SHA256:E50A65D4C06F025E07860D535EE73FFBD6EEF209599D26B8E0BE1E624F65C1B3 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
6
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | powershell.exe | POST | 200 | 52.24.177.168:80 | http://logs-01.loggly.com/inputs/1f667d94-35d0-4958-aa21-54e5d3fd784d/tag/bbsk/ | US | binary | 19 b | whitelisted |
2104 | powershell.exe | GET | 404 | 99.86.7.72:80 | http://bsk968.com/ext/fhg?key= | US | html | 1.76 Kb | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3912 | powershell.exe | 52.24.177.168:443 | logs-01.loggly.com | Amazon.com, Inc. | US | suspicious |
2104 | powershell.exe | 52.24.177.168:80 | logs-01.loggly.com | Amazon.com, Inc. | US | suspicious |
700 | powershell.exe | 52.24.177.168:443 | logs-01.loggly.com | Amazon.com, Inc. | US | suspicious |
2104 | powershell.exe | 99.86.7.72:80 | bsk968.com | AT&T Services, Inc. | US | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
logs-01.loggly.com |
| whitelisted |
bsk968.com |
| malicious |