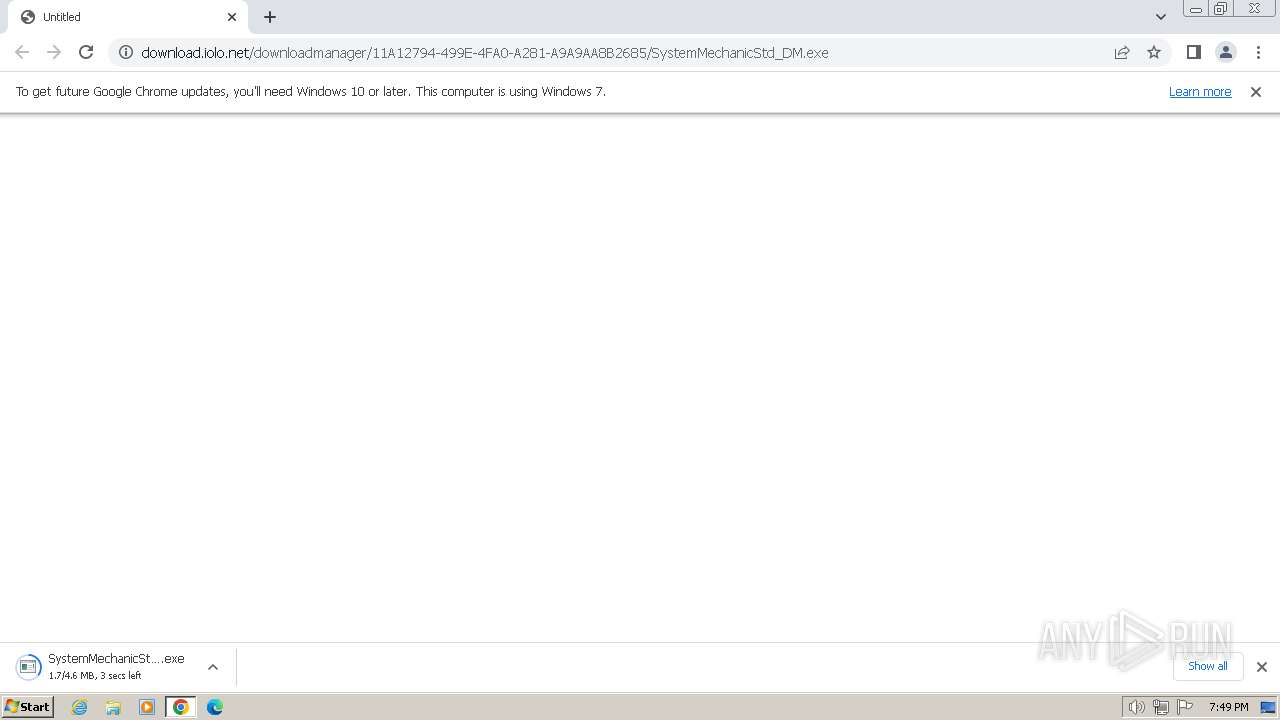
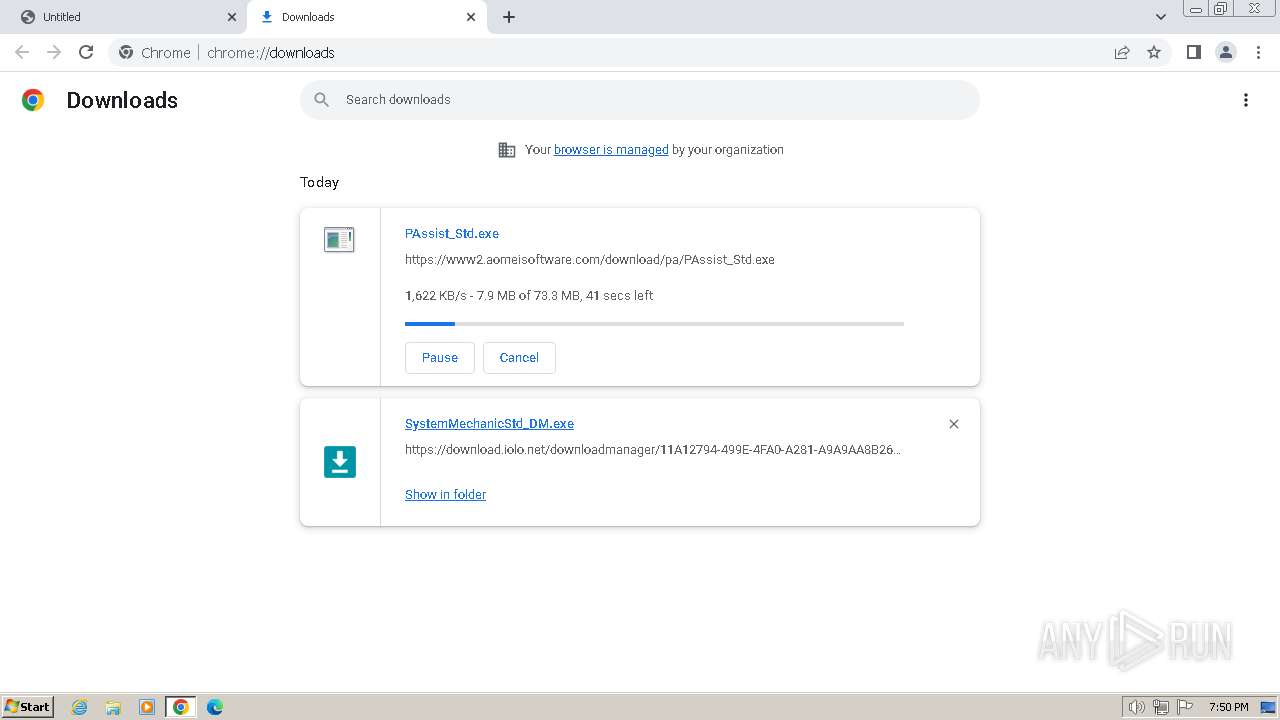
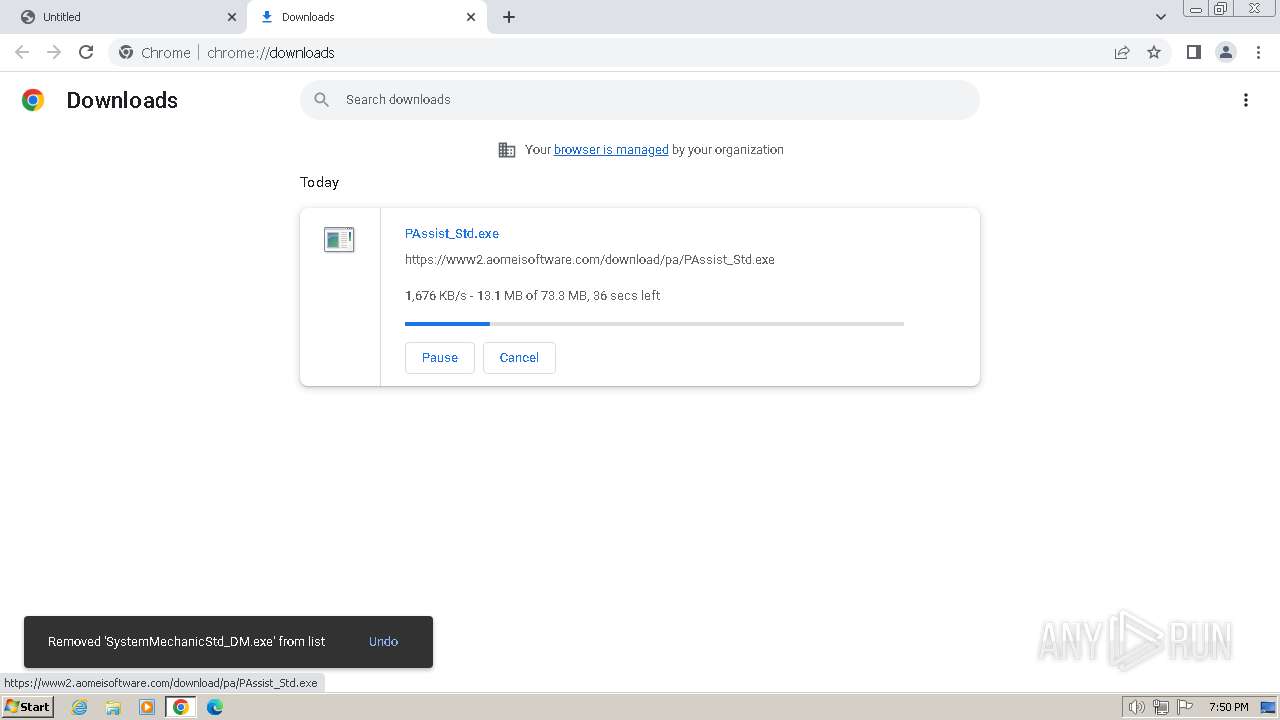
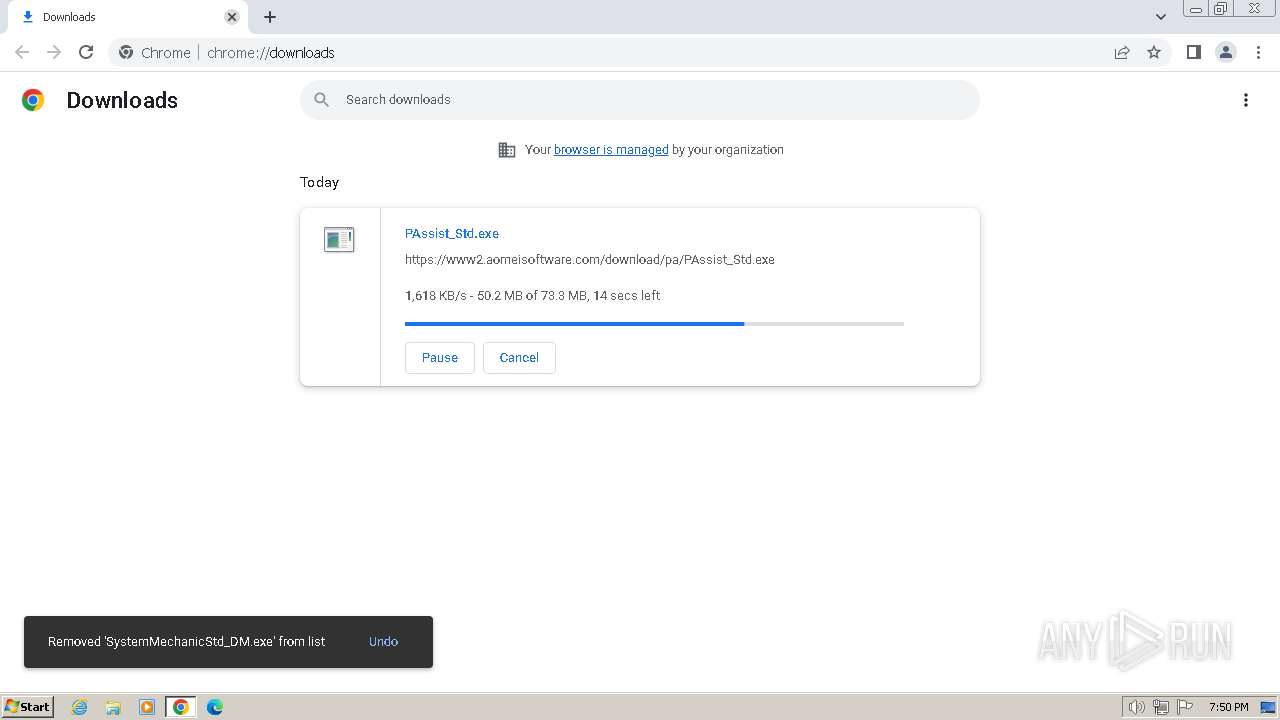
| URL: | https://download.iolo.net/downloadmanager/11A12794-499E-4FA0-A281-A9A9AA8B2685/SystemMechanicStd_DM.exe |
| Full analysis: | https://app.any.run/tasks/f9a38725-343b-4695-bde3-82cc28dbadd2 |
| Verdict: | Malicious activity |
| Analysis date: | March 05, 2024, 19:49:28 |
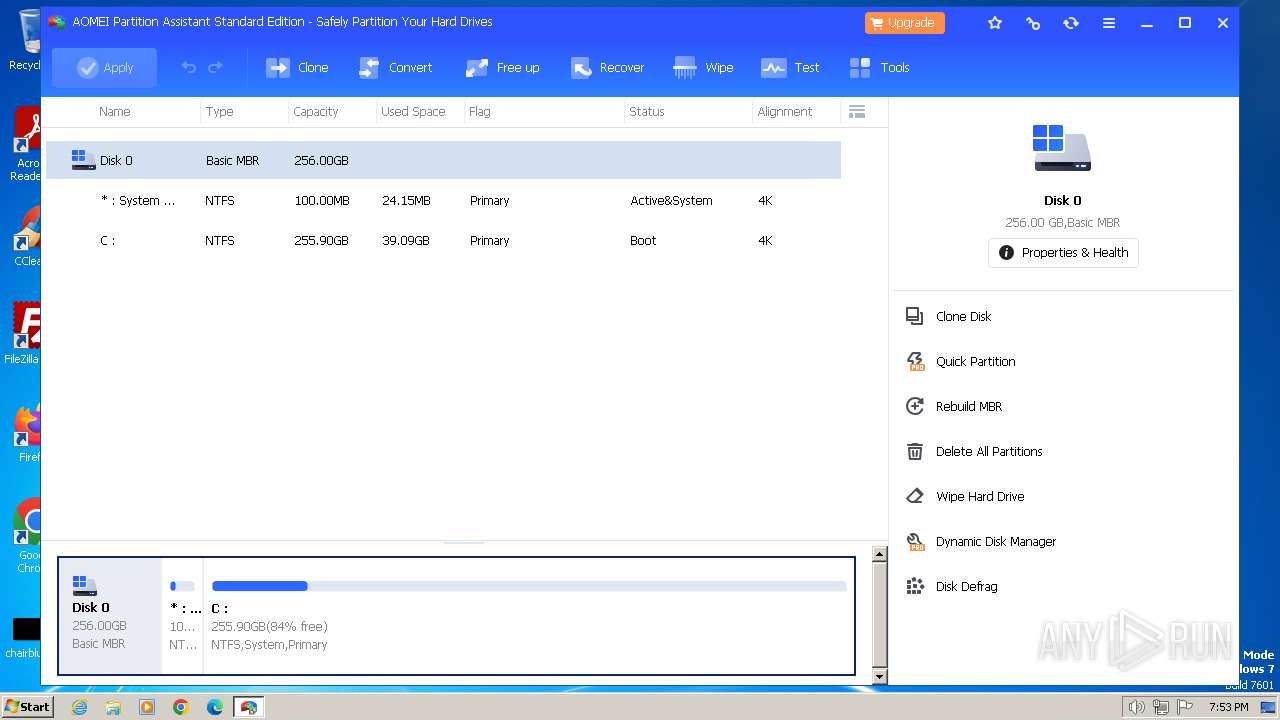
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 7C5C66A311EE9C5ACAA7A6F8B6EE6F2D |
| SHA1: | E470E9ACC146BF94D831DEC049DB995FA24800F7 |
| SHA256: | DC1429BA15491851C45A38AA690169F9DA6737A8C0B3E3B23AC7F32E3ACE4BF3 |
| SSDEEP: | 3:N8SElW0PJELUXP9UXShFYztrKLGW4AW4An:2SKBPKwXuXSEVKyW1An |
MALICIOUS
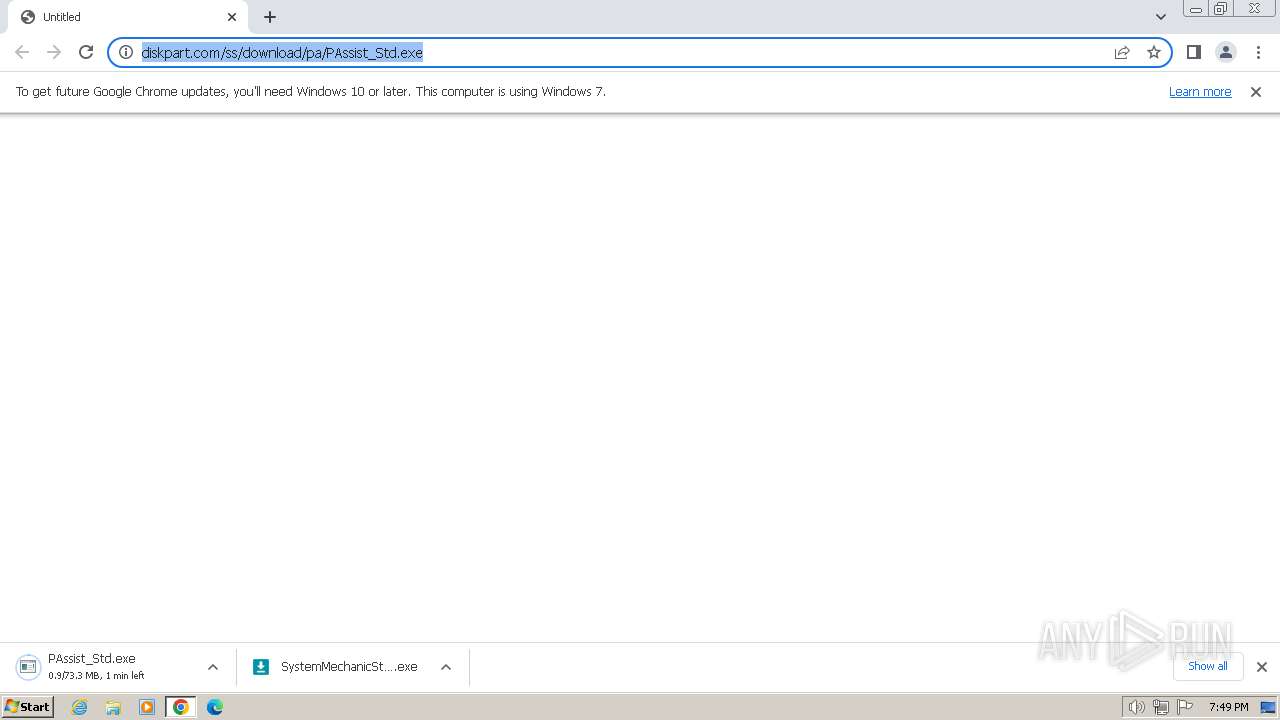
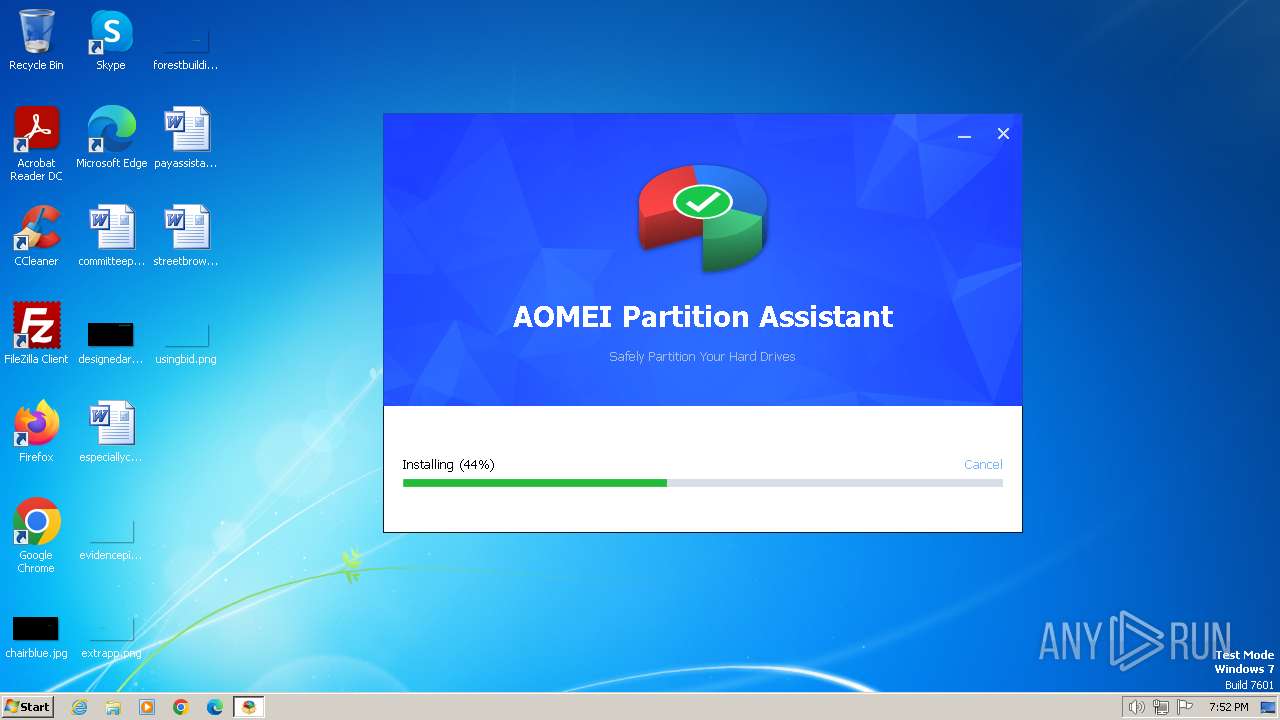
Drops the executable file immediately after the start
- PAssist_Std.exe (PID: 3356)
- PAssist_Std.tmp (PID: 2540)
- SetupGreen32.exe (PID: 324)
Creates a writable file in the system directory
- PAssist_Std.tmp (PID: 2540)
- SetupGreen32.exe (PID: 324)
Actions looks like stealing of personal data
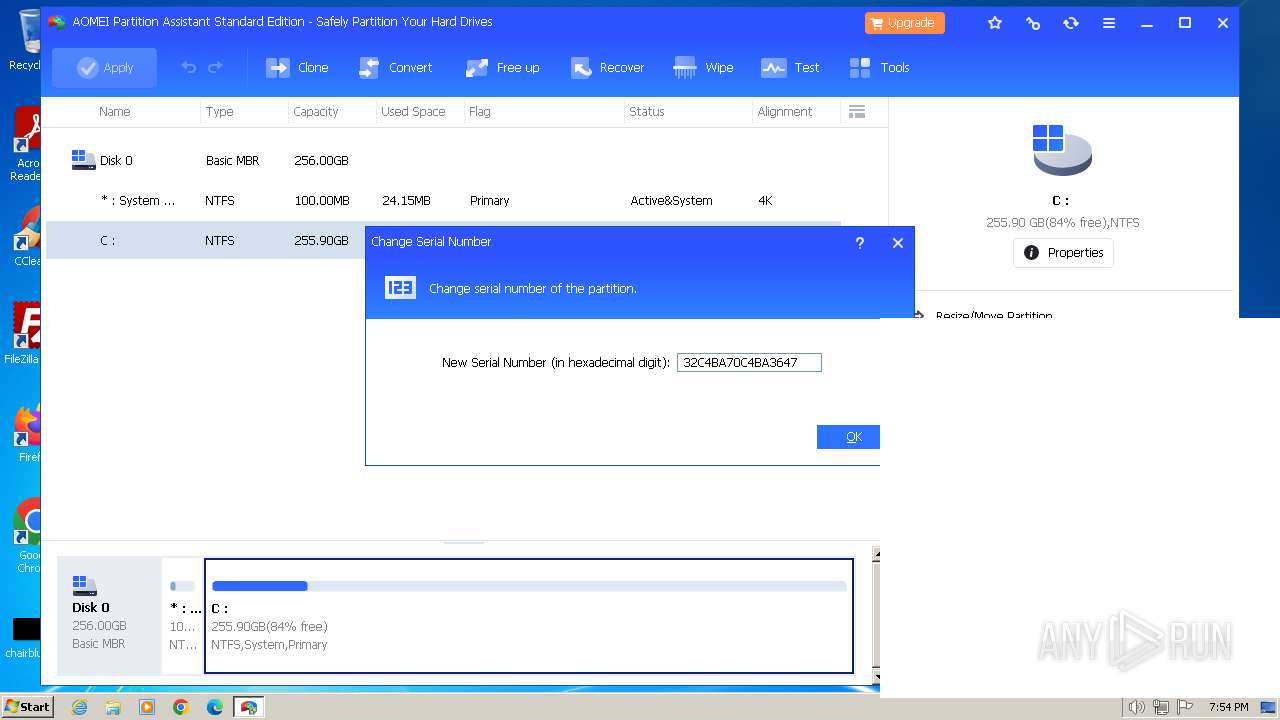
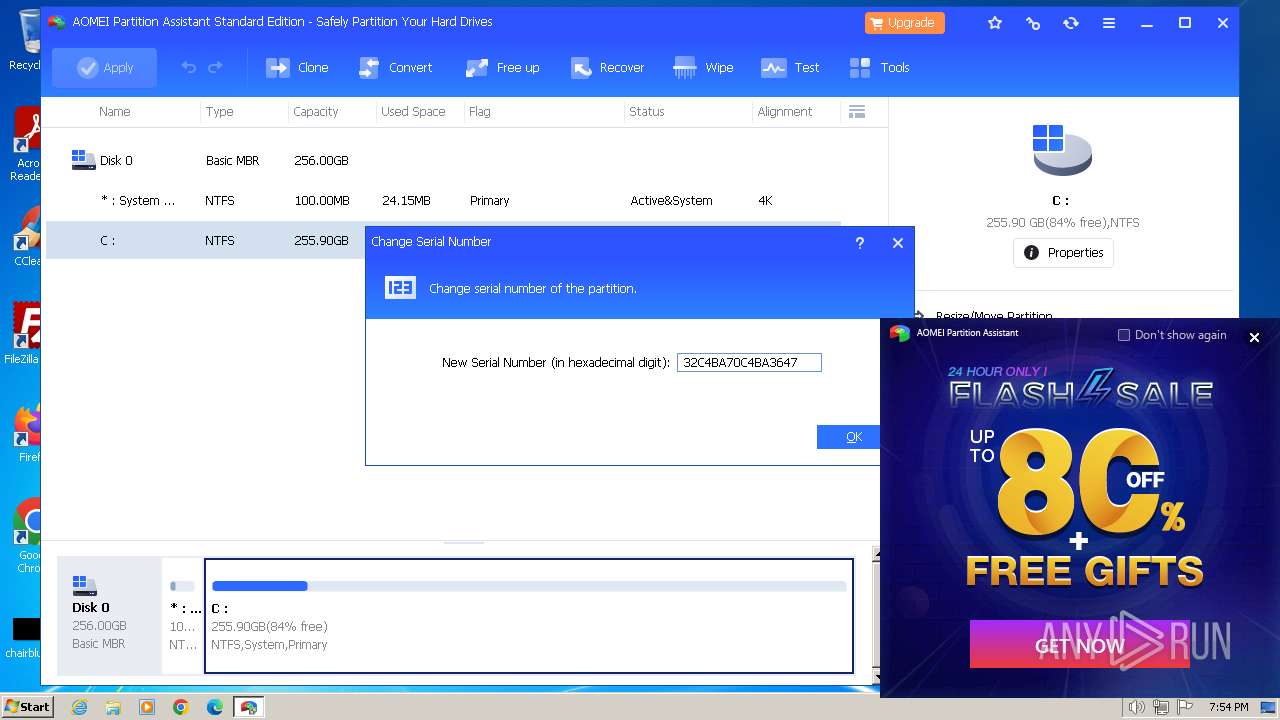
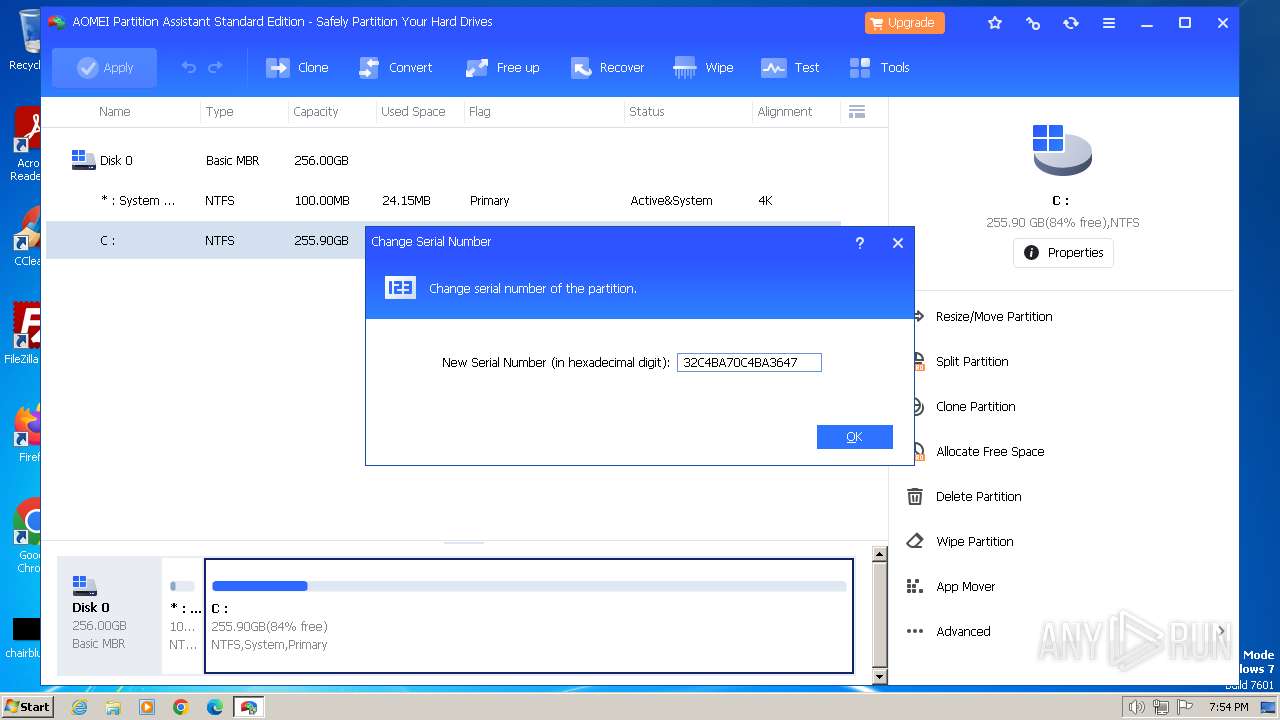
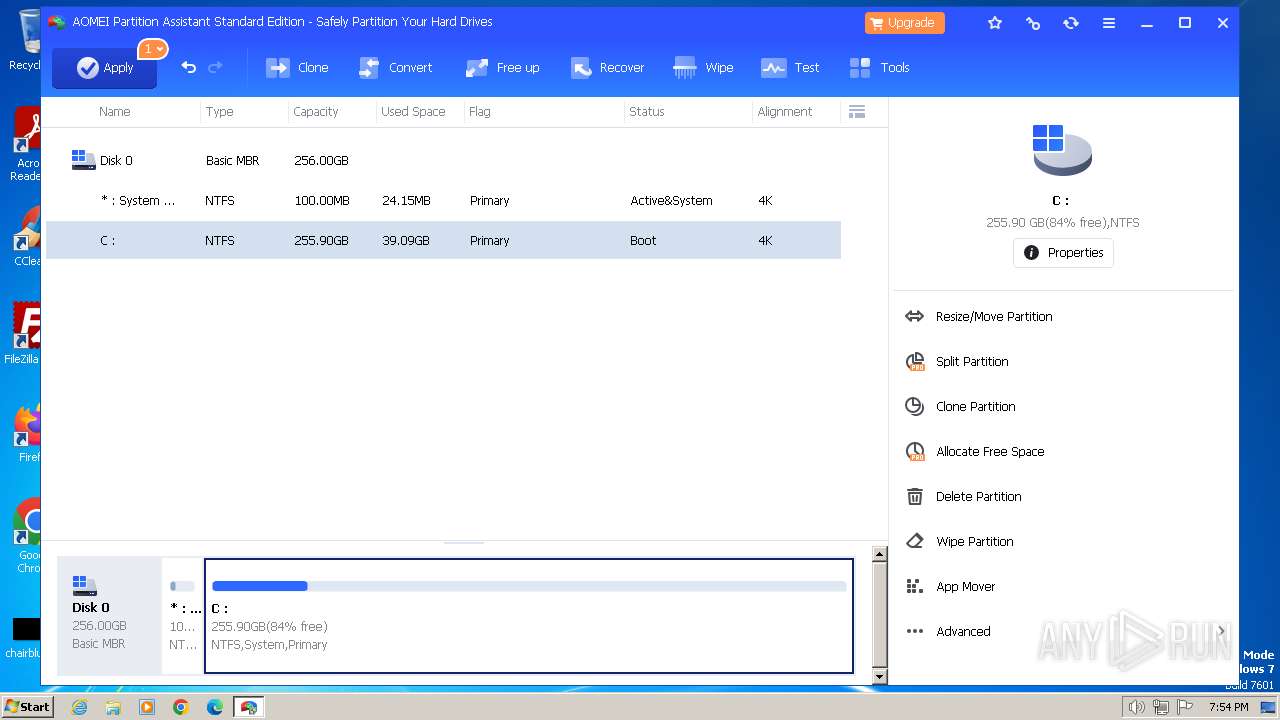
- PartAssist.exe (PID: 2248)
SUSPICIOUS
Executable content was dropped or overwritten
- PAssist_Std.exe (PID: 3356)
- PAssist_Std.tmp (PID: 2540)
- SetupGreen32.exe (PID: 324)
Reads the Windows owner or organization settings
- PAssist_Std.tmp (PID: 2540)
Reads security settings of Internet Explorer
- PAssist_Std.tmp (PID: 2540)
- PartAssist.exe (PID: 2248)
- ga4.exe (PID: 3212)
- amanhlp.exe (PID: 2888)
- panotify.exe (PID: 3452)
- amanhlp.exe (PID: 2004)
- amanhlp.exe (PID: 3292)
Reads the Internet Settings
- PAssist_Std.tmp (PID: 2540)
- PartAssist.exe (PID: 2248)
- ga4.exe (PID: 3212)
- amanhlp.exe (PID: 2888)
- panotify.exe (PID: 3452)
- amanhlp.exe (PID: 2004)
- amanhlp.exe (PID: 3292)
The process drops C-runtime libraries
- PAssist_Std.tmp (PID: 2540)
Reads Microsoft Outlook installation path
- PAssist_Std.tmp (PID: 2540)
- PartAssist.exe (PID: 2248)
- panotify.exe (PID: 3452)
Reads Internet Explorer settings
- PAssist_Std.tmp (PID: 2540)
- PartAssist.exe (PID: 2248)
- panotify.exe (PID: 3452)
Drops a system driver (possible attempt to evade defenses)
- PAssist_Std.tmp (PID: 2540)
- SetupGreen32.exe (PID: 324)
Creates or modifies Windows services
- PAssist_Std.tmp (PID: 2540)
Starts CMD.EXE for commands execution
- PAssist_Std.tmp (PID: 2540)
Process drops legitimate windows executable
- PAssist_Std.tmp (PID: 2540)
Reads settings of System Certificates
- PartAssist.exe (PID: 2248)
- GaHlp.exe (PID: 2096)
- ga4.exe (PID: 3212)
- amanhlp.exe (PID: 2888)
- amanhlp.exe (PID: 2004)
Checks Windows Trust Settings
- PartAssist.exe (PID: 2248)
- ga4.exe (PID: 3212)
- amanhlp.exe (PID: 2888)
- amanhlp.exe (PID: 2004)
Drops 7-zip archiver for unpacking
- PAssist_Std.tmp (PID: 2540)
Searches for installed software
- PartAssist.exe (PID: 2248)
- PAssist_Std.tmp (PID: 2540)
INFO
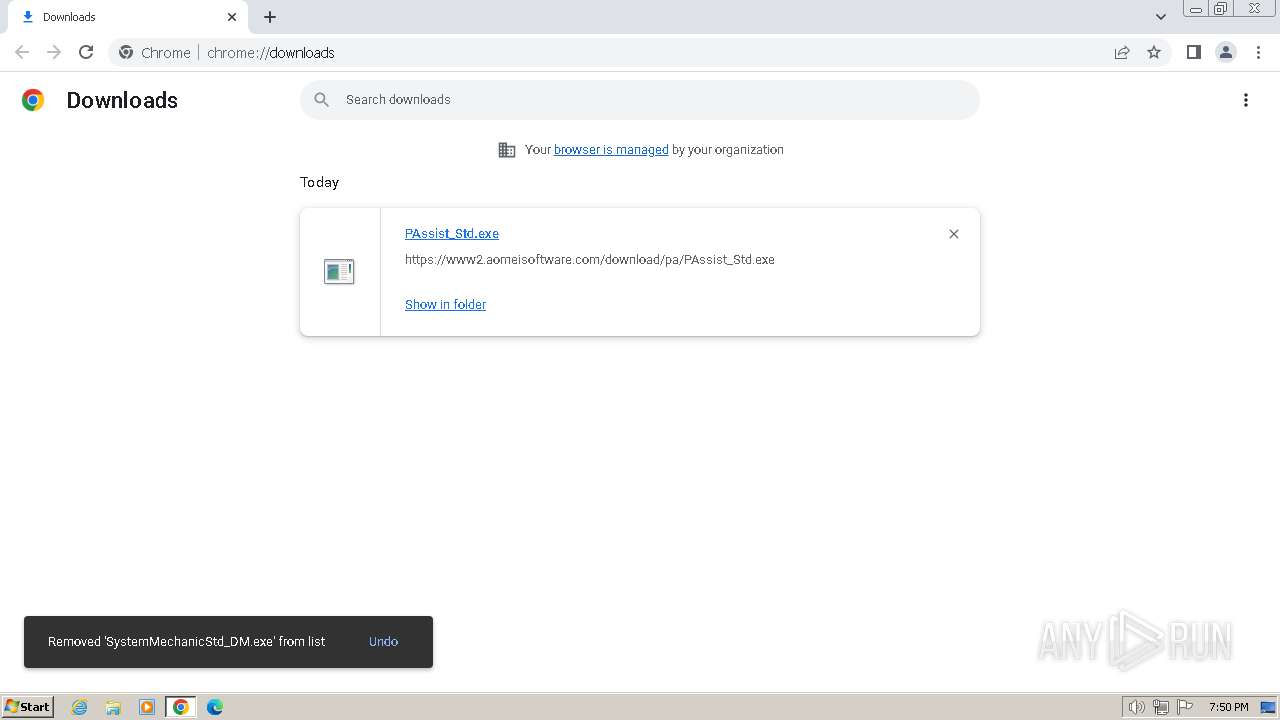
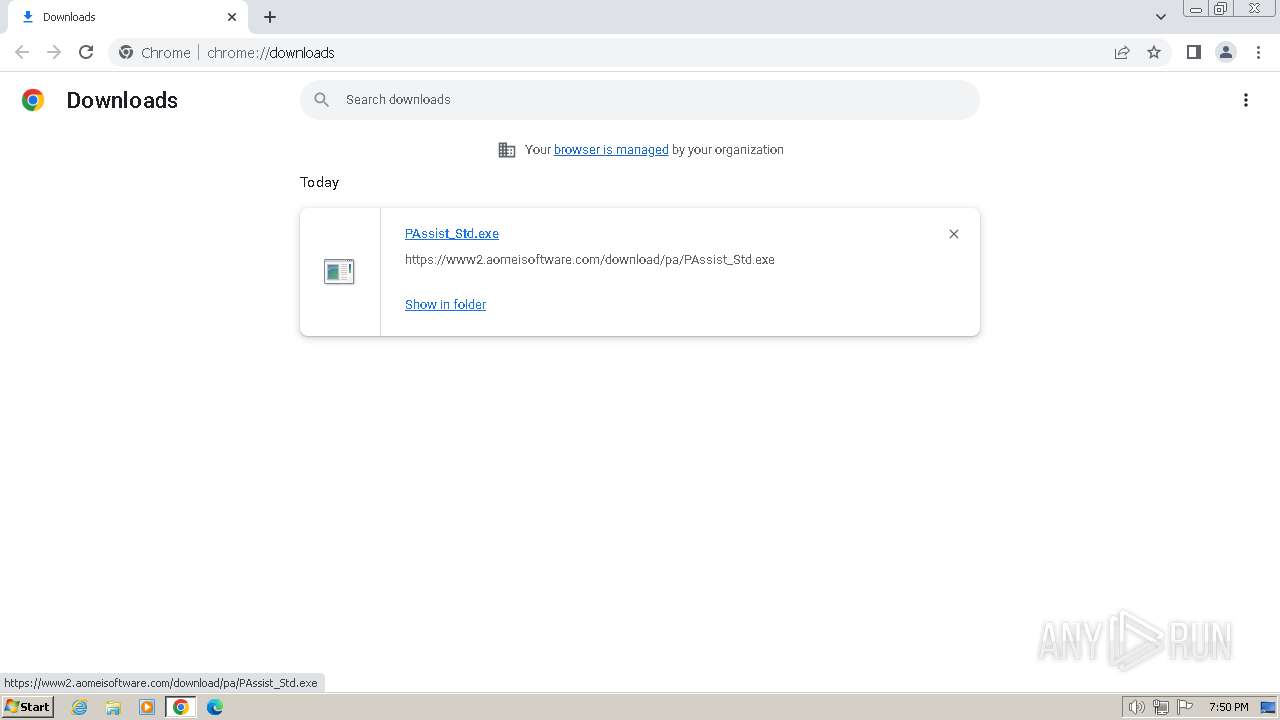
Drops the executable file immediately after the start
- chrome.exe (PID: 3240)
The process uses the downloaded file
- chrome.exe (PID: 3240)
- chrome.exe (PID: 2244)
- chrome.exe (PID: 1504)
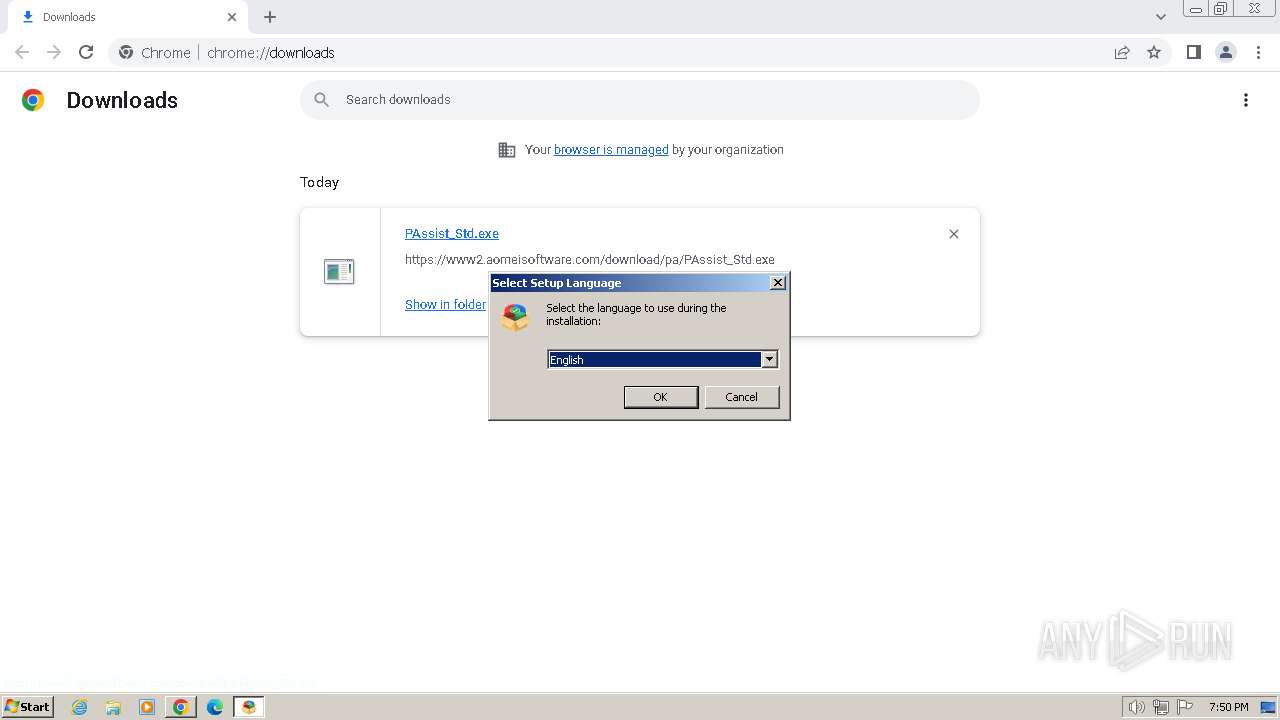
Checks supported languages
- PAssist_Std.exe (PID: 3356)
- PAssist_Std.tmp (PID: 2540)
- aman.exe (PID: 3560)
- loaddrv.exe (PID: 2384)
- loaddrv.exe (PID: 1624)
- loaddrv.exe (PID: 3800)
- loaddrv.exe (PID: 3088)
- ga4.exe (PID: 2112)
- GaHlp.exe (PID: 2096)
- aman.exe (PID: 1348)
- SetupGreen32.exe (PID: 324)
- LoadDrv_Win32.exe (PID: 480)
- ga4.exe (PID: 3940)
- ga4.exe (PID: 3212)
- amanhlp.exe (PID: 2888)
- PartAssist.exe (PID: 2248)
- amanhlp.exe (PID: 2004)
- SetupGreen32.exe (PID: 1604)
- panotify.exe (PID: 3452)
- amanhlp.exe (PID: 3292)
- LoadDrv_Win32.exe (PID: 3688)
Executable content was dropped or overwritten
- chrome.exe (PID: 3240)
Create files in a temporary directory
- PAssist_Std.exe (PID: 3356)
- PAssist_Std.tmp (PID: 2540)
- ga4.exe (PID: 2112)
- aman.exe (PID: 1348)
- ga4.exe (PID: 3940)
- ga4.exe (PID: 3212)
Reads the computer name
- PAssist_Std.tmp (PID: 2540)
- loaddrv.exe (PID: 2384)
- loaddrv.exe (PID: 3088)
- GaHlp.exe (PID: 2096)
- ga4.exe (PID: 2112)
- PartAssist.exe (PID: 2248)
- loaddrv.exe (PID: 1624)
- LoadDrv_Win32.exe (PID: 3688)
- loaddrv.exe (PID: 3800)
- LoadDrv_Win32.exe (PID: 480)
- ga4.exe (PID: 3940)
- ga4.exe (PID: 3212)
- amanhlp.exe (PID: 2888)
- panotify.exe (PID: 3452)
- amanhlp.exe (PID: 3292)
- amanhlp.exe (PID: 2004)
Application launched itself
- chrome.exe (PID: 3240)
- msedge.exe (PID: 2484)
- msedge.exe (PID: 2320)
Checks proxy server information
- PAssist_Std.tmp (PID: 2540)
- PartAssist.exe (PID: 2248)
- ga4.exe (PID: 3212)
- amanhlp.exe (PID: 2888)
- panotify.exe (PID: 3452)
- amanhlp.exe (PID: 2004)
- amanhlp.exe (PID: 3292)
Creates files in the program directory
- PAssist_Std.tmp (PID: 2540)
- aman.exe (PID: 3560)
- cmd.exe (PID: 844)
- ga4.exe (PID: 2112)
- aman.exe (PID: 1348)
- PartAssist.exe (PID: 2248)
- ga4.exe (PID: 3940)
- panotify.exe (PID: 3452)
Creates a software uninstall entry
- PAssist_Std.tmp (PID: 2540)
Dropped object may contain TOR URL's
- PAssist_Std.tmp (PID: 2540)
Reads product name
- PAssist_Std.tmp (PID: 2540)
- GaHlp.exe (PID: 2096)
- ga4.exe (PID: 2112)
- aman.exe (PID: 1348)
- PartAssist.exe (PID: 2248)
- ga4.exe (PID: 3940)
- ga4.exe (PID: 3212)
Reads Environment values
- PAssist_Std.tmp (PID: 2540)
- GaHlp.exe (PID: 2096)
- ga4.exe (PID: 2112)
- aman.exe (PID: 1348)
- PartAssist.exe (PID: 2248)
- ga4.exe (PID: 3940)
- ga4.exe (PID: 3212)
Reads the machine GUID from the registry
- ga4.exe (PID: 2112)
- PartAssist.exe (PID: 2248)
- PAssist_Std.tmp (PID: 2540)
- GaHlp.exe (PID: 2096)
- ga4.exe (PID: 3940)
- ga4.exe (PID: 3212)
- panotify.exe (PID: 3452)
- amanhlp.exe (PID: 3292)
- amanhlp.exe (PID: 2004)
- amanhlp.exe (PID: 2888)
Manual execution by a user
- msedge.exe (PID: 2320)
Reads the software policy settings
- PartAssist.exe (PID: 2248)
- GaHlp.exe (PID: 2096)
- ga4.exe (PID: 3212)
- amanhlp.exe (PID: 2888)
- amanhlp.exe (PID: 2004)
Creates files or folders in the user directory
- PartAssist.exe (PID: 2248)
- ga4.exe (PID: 3212)
- panotify.exe (PID: 3452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
129
Monitored processes
69
Malicious processes
10
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
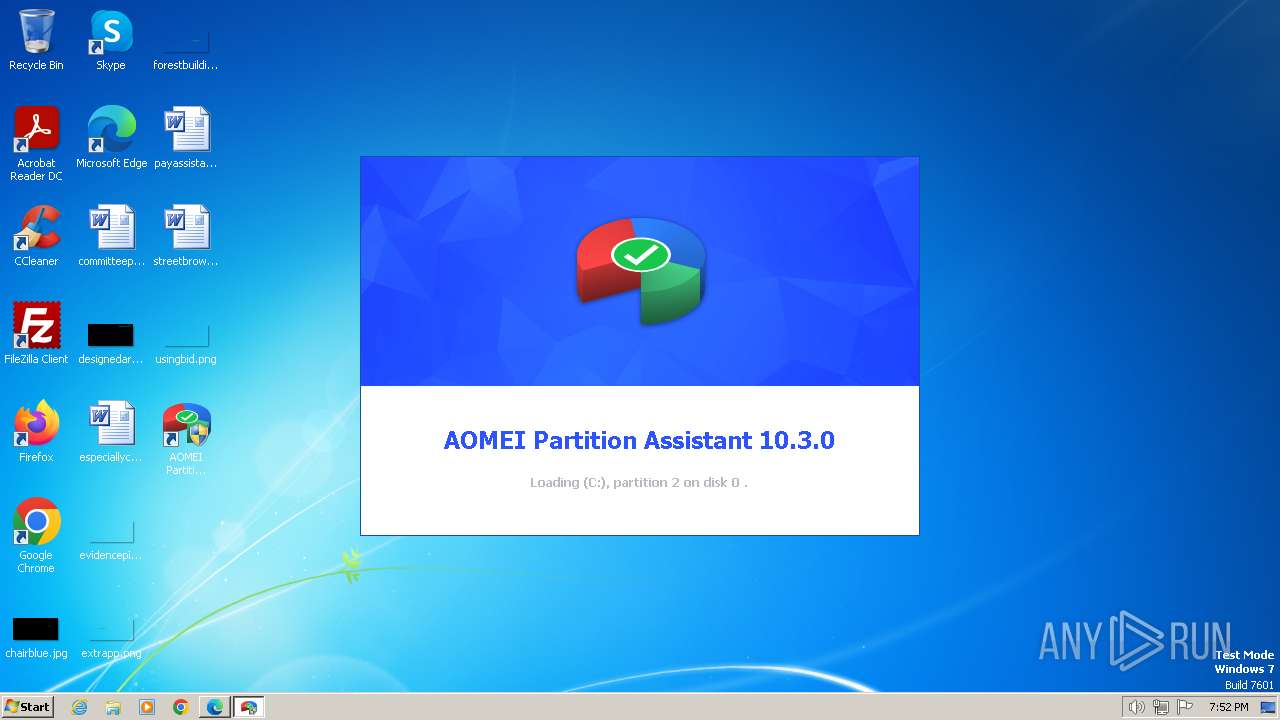
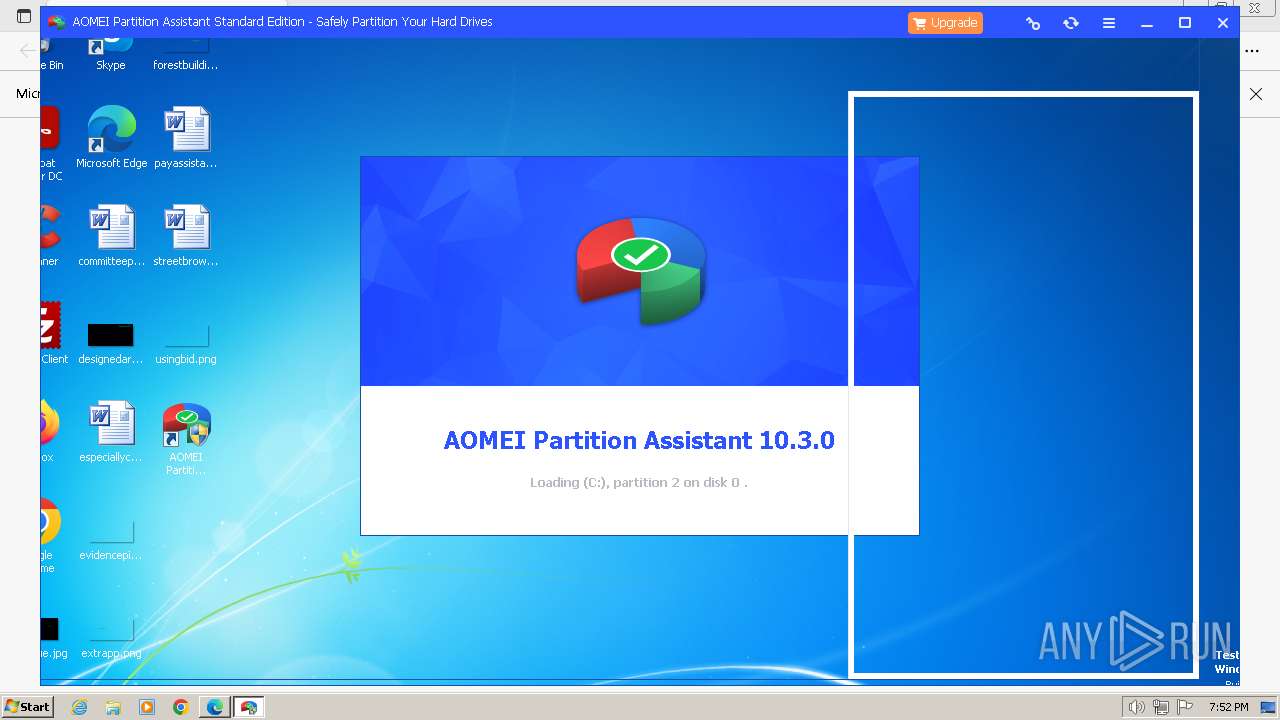
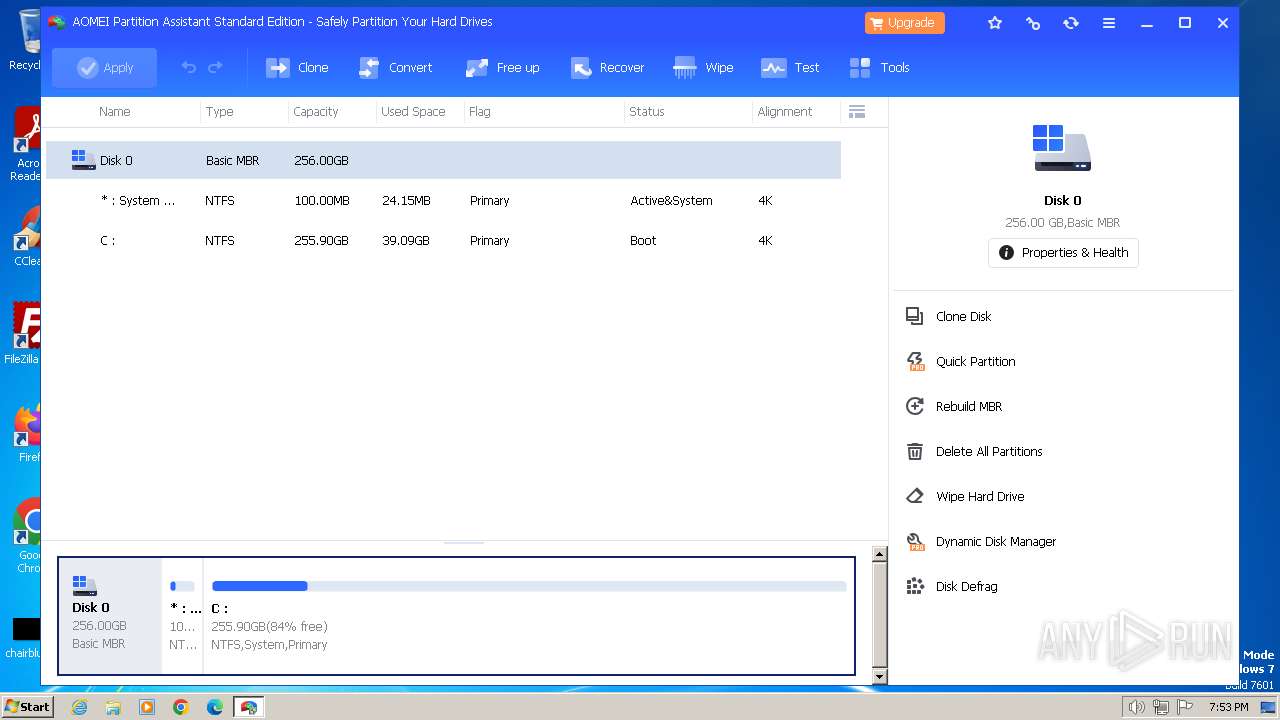
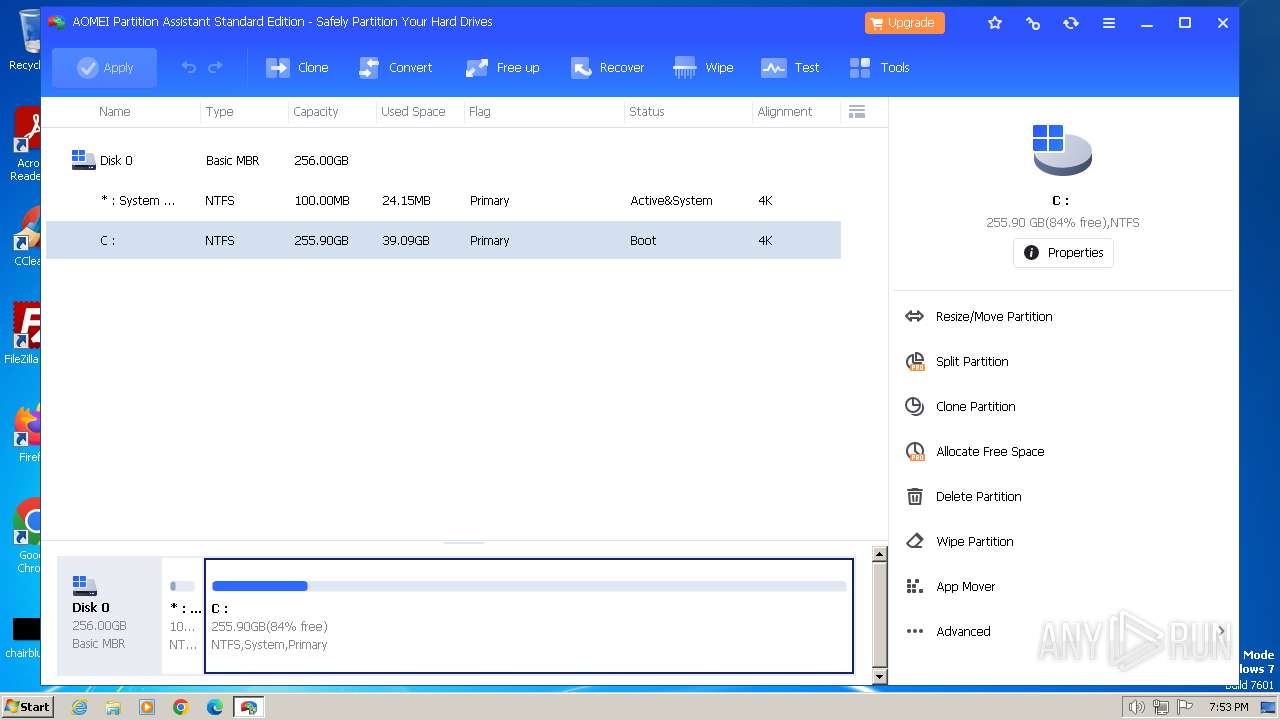
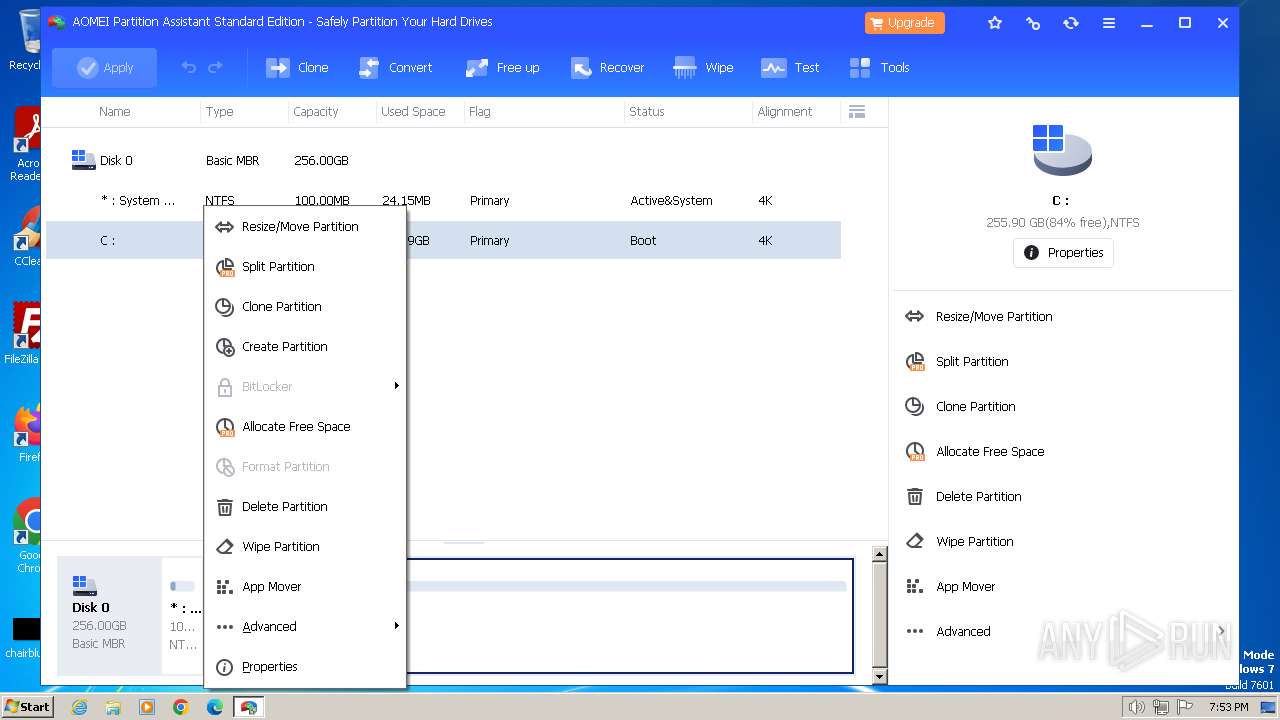
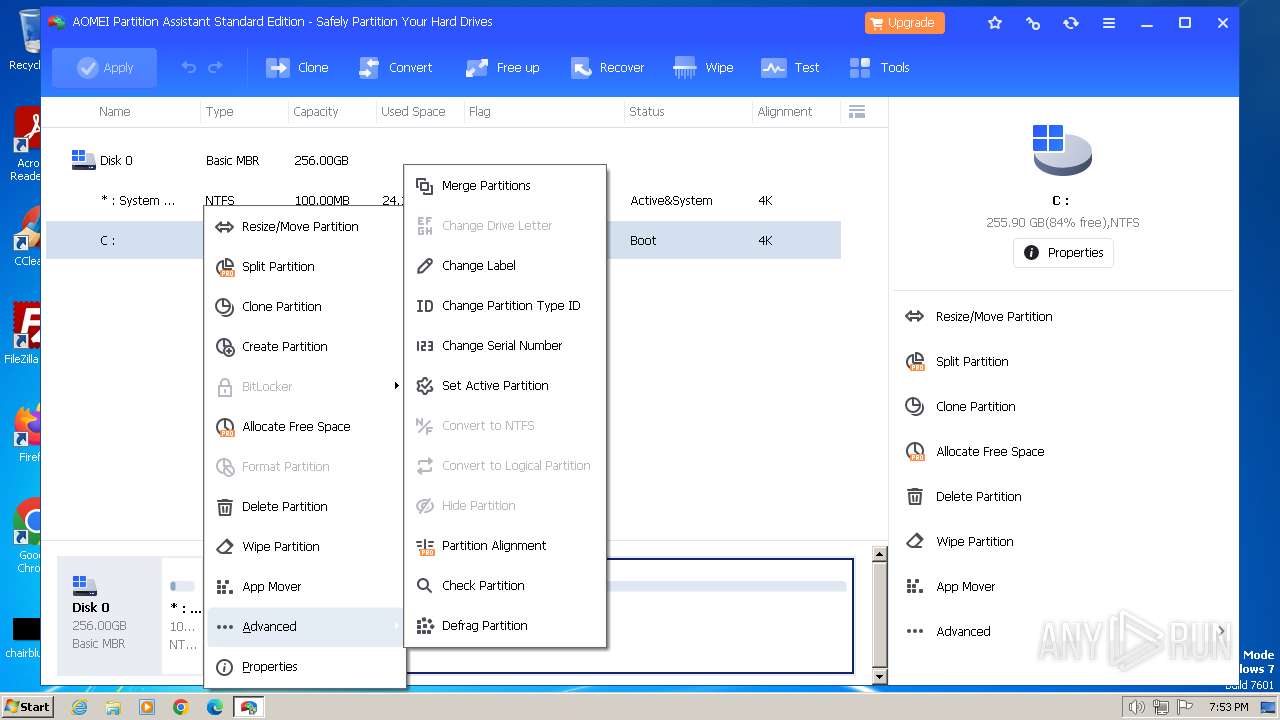
| 324 | "C:\Program Files\AOMEI Partition Assistant\SetupGreen32.exe" | C:\Program Files\AOMEI Partition Assistant\SetupGreen32.exe | PartAssist.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 480 | "C:\Program Files\AOMEI Partition Assistant\LoadDrv_Win32.exe" | C:\Program Files\AOMEI Partition Assistant\LoadDrv_Win32.exe | PartAssist.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 560 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=4140 --field-trial-handle=1340,i,16765496286488863375,8209079176426043986,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 712 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3884 --field-trial-handle=1160,i,6774299423258577892,4431281002639406160,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 844 | "C:\Windows\system32\cmd.exe" /c echo [UserExperience] >"C:\Program Files\AOMEI Partition Assistant\Other.ini"&&echo ExperienceValue=1 >>"C:\Program Files\AOMEI Partition Assistant\Other.ini | C:\Windows\System32\cmd.exe | — | PAssist_Std.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=3868 --field-trial-handle=1160,i,6774299423258577892,4431281002639406160,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1168 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=entity_extraction_service.mojom.PageScreenshotProcessor --lang=en-US --service-sandbox-type=entity_extraction --mojo-platform-channel-handle=3624 --field-trial-handle=1340,i,16765496286488863375,8209079176426043986,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1172 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilReadIcon --lang=en-US --service-sandbox-type=icon_reader --disable-quic --mojo-platform-channel-handle=1968 --field-trial-handle=1160,i,6774299423258577892,4431281002639406160,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1308 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1076 --field-trial-handle=1160,i,6774299423258577892,4431281002639406160,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 1348 | "C:\Users\admin\AppData\Local\Temp\is-P352R.tmp\aman.exe" -Commit_install "en" "0" 2 | C:\Users\admin\AppData\Local\Temp\is-P352R.tmp\aman.exe | PAssist_Std.tmp | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
52 727
Read events
51 598
Write events
490
Delete events
639
Modification events
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (3240) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
698
Suspicious files
109
Text files
1 412
Unknown types
72
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17fa8c.TMP | — | |
MD5:— | SHA256:— | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old | text | |
MD5:AD0DB8476493577A67FA94A162B646C4 | SHA256:304FB5B4FD83D4A9FF1EF4CF20232A1783169C148297BFE37ED24A1D22A74F2B | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Local Storage\leveldb\LOG.old~RF17fba6.TMP | text | |
MD5:C383FD120B14BB0E98E99C1BCC9B43F6 | SHA256:56A3A5EACBD28BEE1CF8C1D0052321A5C27EE858BEF7B2FA1DE20806A0823CC1 | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old~RF17fcbf.TMP | text | |
MD5:0272AD43ECEA4DC6C694BE6D918B5BA7 | SHA256:530F5A3F46B293038FEBEF2035CFA622F05B202363ABFAF9E40E105BD1472432 | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old~RF17fd2c.TMP | — | |
MD5:— | SHA256:— | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old | text | |
MD5:ECD3386BCC950E73B86EB128A5F57622 | SHA256:C9A068EAFBC587EDFC89392F64DDD350EEB96C5CF195CDB030BAB8F6DD33833B | |||
| 3240 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Extension State\LOG.old | text | |
MD5:BF244CDEBD39A0D20444C1578C0200BE | SHA256:CC7E247D7764DA50D4137E894838F918281D4915FE0823B4FC0CB763BF582F4D | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
61
DNS requests
63
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
856 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
856 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvYTBmQUFZUHRkSkgtb01uSGNvRHZ2Tm5HQQ/1.0.0.15_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | binary | 3.07 Kb | unknown |
2248 | PartAssist.exe | GET | 304 | 23.73.137.235:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?960962806711390c | unknown | — | — | unknown |
2248 | PartAssist.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gsr1/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS3V7W2nAf4FiMTjpDJKg6%2BMgGqMQQUYHtmGkUNl8qJUC99BM00qP%2F8%2FUsCEHe9DWzbNvka6iEPxPBY0w0%3D | unknown | binary | 1.41 Kb | unknown |
2248 | PartAssist.exe | GET | 200 | 104.26.10.118:80 | http://account.aomeitech.com/ini/recommend/pa/cfg.ini | unknown | text | 119 b | unknown |
2248 | PartAssist.exe | GET | 200 | 172.66.43.9:80 | http://www2.aomeisoftware.com/download/Autoupgrade/PAaotoupgrade/PAupgrade.ini | unknown | text | 18.6 Kb | unknown |
2248 | PartAssist.exe | GET | 200 | 104.26.10.118:80 | http://account.aomeitech.com/ini/popup/pa/Notifycfg.ini | unknown | text | 345 b | unknown |
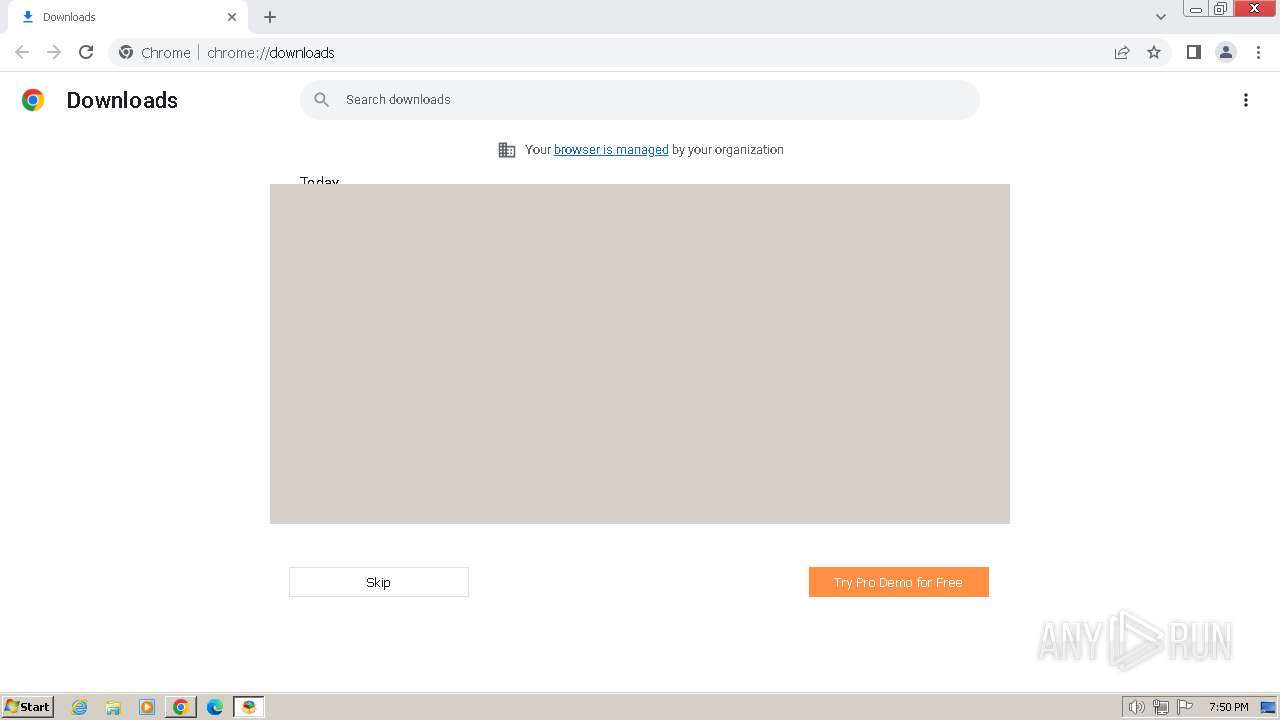
2248 | PartAssist.exe | GET | 200 | 172.66.40.247:80 | http://www.aomeisoftware.com/ini/recommend/pa/rec.html?v=20230719115247 | unknown | html | 7.76 Kb | unknown |
3212 | ga4.exe | GET | 200 | 142.250.184.195:80 | http://ocsp.pki.goog/gtsr1/ME4wTDBKMEgwRjAJBgUrDgMCGgUABBQwkcLWD4LqGJ7bE7B1XZsEbmfwUAQU5K8rJnEaK0gnhS9SZizv8IkTcT4CDQIDvFNZazTHGPUBUGY%3D | unknown | binary | 724 b | unknown |
3452 | panotify.exe | GET | 200 | 172.66.43.9:80 | http://www2.aomeisoftware.com/popup/pa/24hour-flash-sale-a-pa.html?lang=en¬interest=1 | unknown | html | 377 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3228 | chrome.exe | 173.194.76.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
3240 | chrome.exe | 239.255.255.250:1900 | — | — | — | unknown |
3228 | chrome.exe | 138.199.37.227:443 | download.iolo.net | Datacamp Limited | DE | unknown |
3240 | chrome.exe | 224.0.0.251:5353 | — | — | — | unknown |
3228 | chrome.exe | 142.250.186.174:443 | sb-ssl.google.com | GOOGLE | US | whitelisted |
3228 | chrome.exe | 142.250.185.132:443 | www.google.com | GOOGLE | US | whitelisted |
3228 | chrome.exe | 142.250.185.74:443 | safebrowsing.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
accounts.google.com |
| shared |
download.iolo.net |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
www.google.com |
| whitelisted |
safebrowsing.googleapis.com |
| whitelisted |
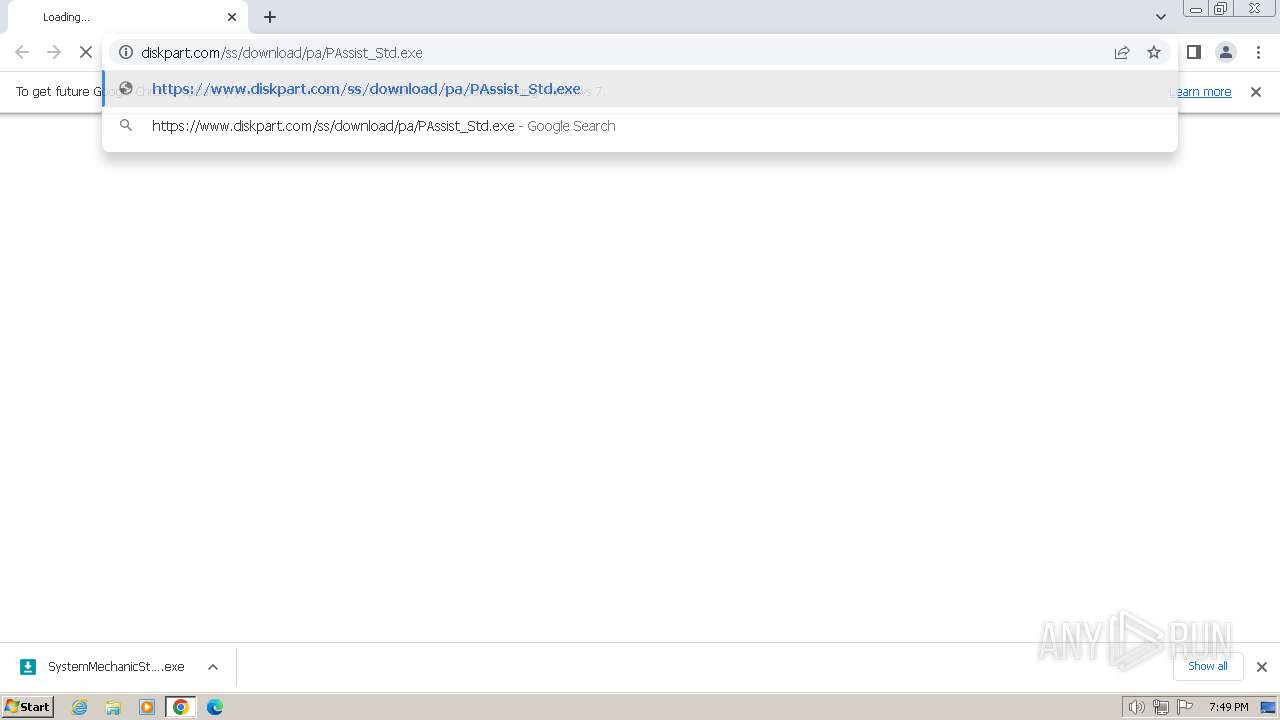
www.diskpart.com |
| unknown |
www2.aomeisoftware.com |
| unknown |
www.googleapis.com |
| whitelisted |
update.googleapis.com |
| whitelisted |
edgedl.me.gvt1.com |
| whitelisted |
Threats
Process | Message |
|---|---|
loaddrv.exe | ------------Uninstall AMPA Drive-----------------
|
loaddrv.exe | OpenSCManager() ok !
|
loaddrv.exe | OpenService() Faild !
|
loaddrv.exe | Failed to Uninstall drive.
|
loaddrv.exe | ------------Install AMPA Drive-----------------
|
loaddrv.exe | OpenSCManager() ok !
|
loaddrv.exe | CrateService() ok !
|
loaddrv.exe | StartService() Faild!
|
loaddrv.exe | Failed to Install drive.
|
loaddrv.exe | ------------Uninstall Drive-----------------
|