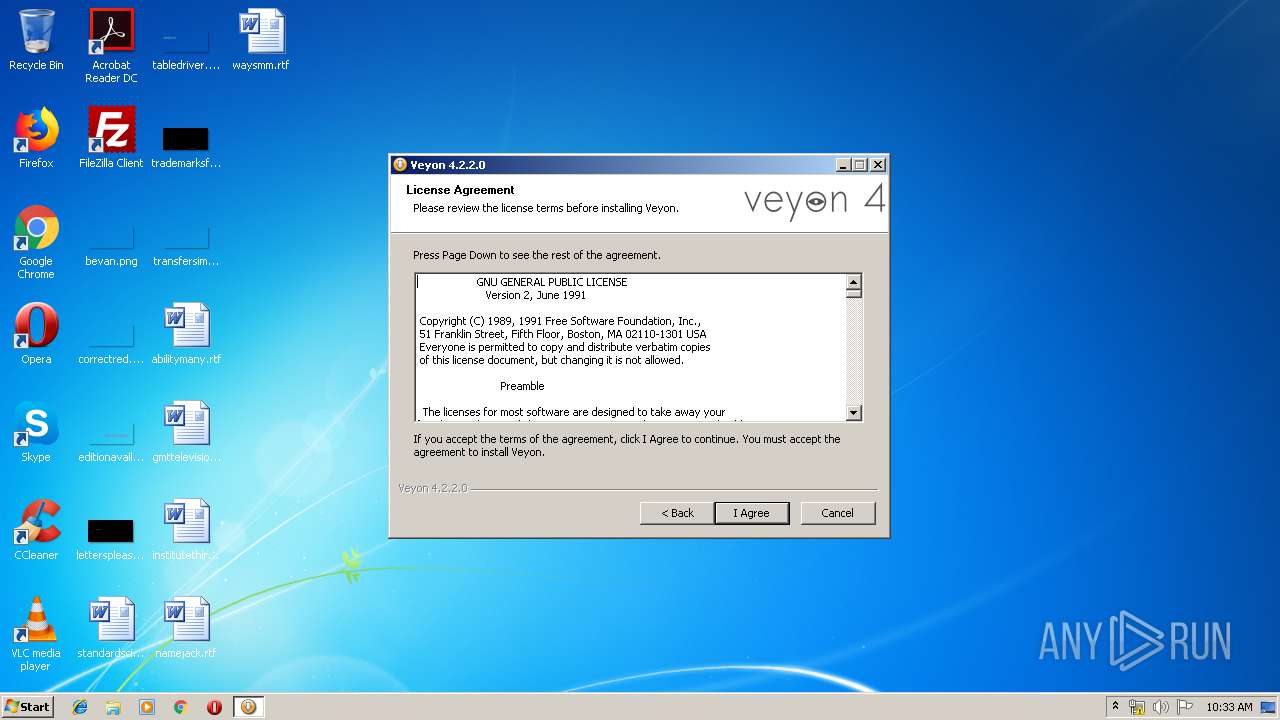
| File name: | veyon-4.2.2.0-win32-setup.exe |
| Full analysis: | https://app.any.run/tasks/24270841-fb31-45d1-a147-8d7fe5b09086 |
| Verdict: | Malicious activity |
| Analysis date: | June 28, 2019, 09:32:47 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 (stripped to external PDB), for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | A664ABE0255831729D3EDC6F5BA661BB |
| SHA1: | F7EC51DEE08D2417399F918D8382CC3C3FC929C7 |
| SHA256: | DC0B1490C5DD1443402E26F3662F12586F51A3D17CBB164F169FC636AD2E5482 |
| SSDEEP: | 196608:vMcM/K6w0HJcqw1Uc0jCJhMSEKS0BMq82SUMSo3gPGTDbD1l4:vRoXvaqwWc0jshMxKS0yINHeP/I |
MALICIOUS
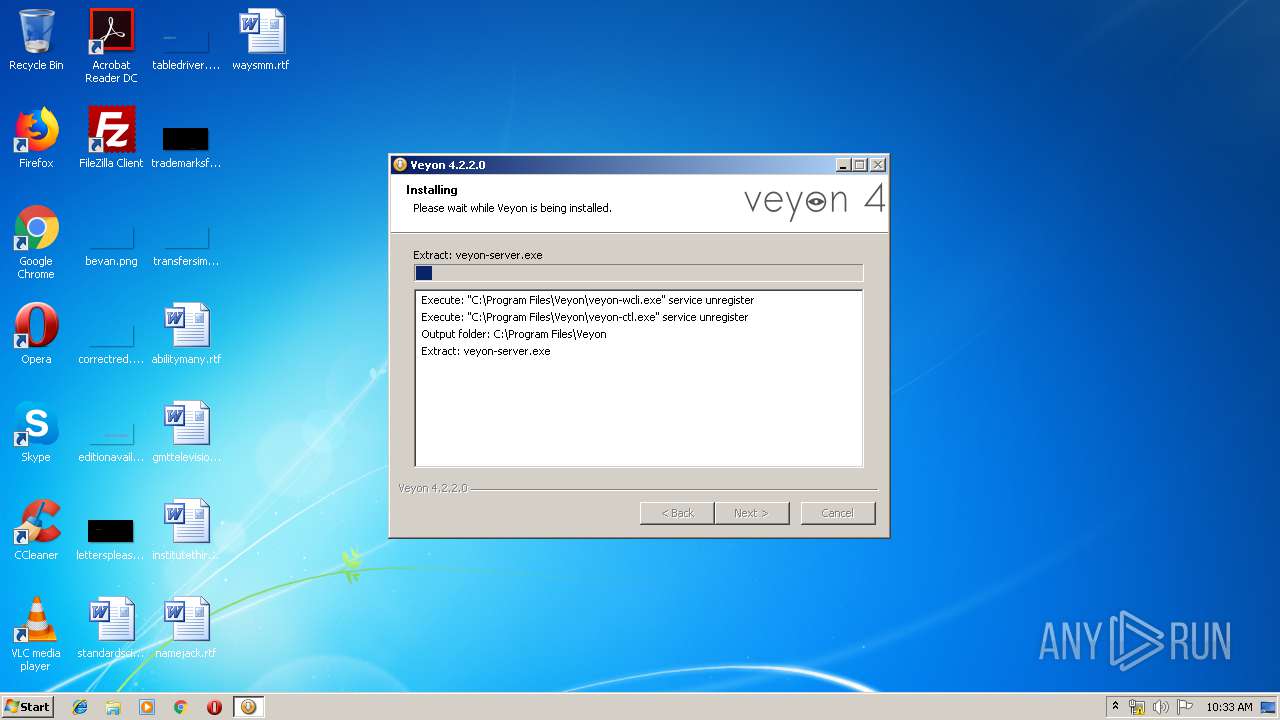
Loads dropped or rewritten executable
- veyon-wcli.exe (PID: 2724)
- veyon-wcli.exe (PID: 3816)
- veyon-wcli.exe (PID: 3772)
- veyon-wcli.exe (PID: 2504)
- veyon-4.2.2.0-win32-setup.exe (PID: 3740)
- veyon-service.exe (PID: 2360)
- veyon-server.exe (PID: 2984)
- veyon-master.exe (PID: 2872)
- veyon-worker.exe (PID: 3796)
- veyon-configurator.exe (PID: 2668)
Application was dropped or rewritten from another process
- veyon-wcli.exe (PID: 3772)
- veyon-wcli.exe (PID: 2504)
- veyon-wcli.exe (PID: 2724)
- veyon-wcli.exe (PID: 3816)
- veyon-service.exe (PID: 2360)
- veyon-server.exe (PID: 2984)
- veyon-configurator.exe (PID: 2668)
- veyon-worker.exe (PID: 3796)
- veyon-master.exe (PID: 2872)
SUSPICIOUS
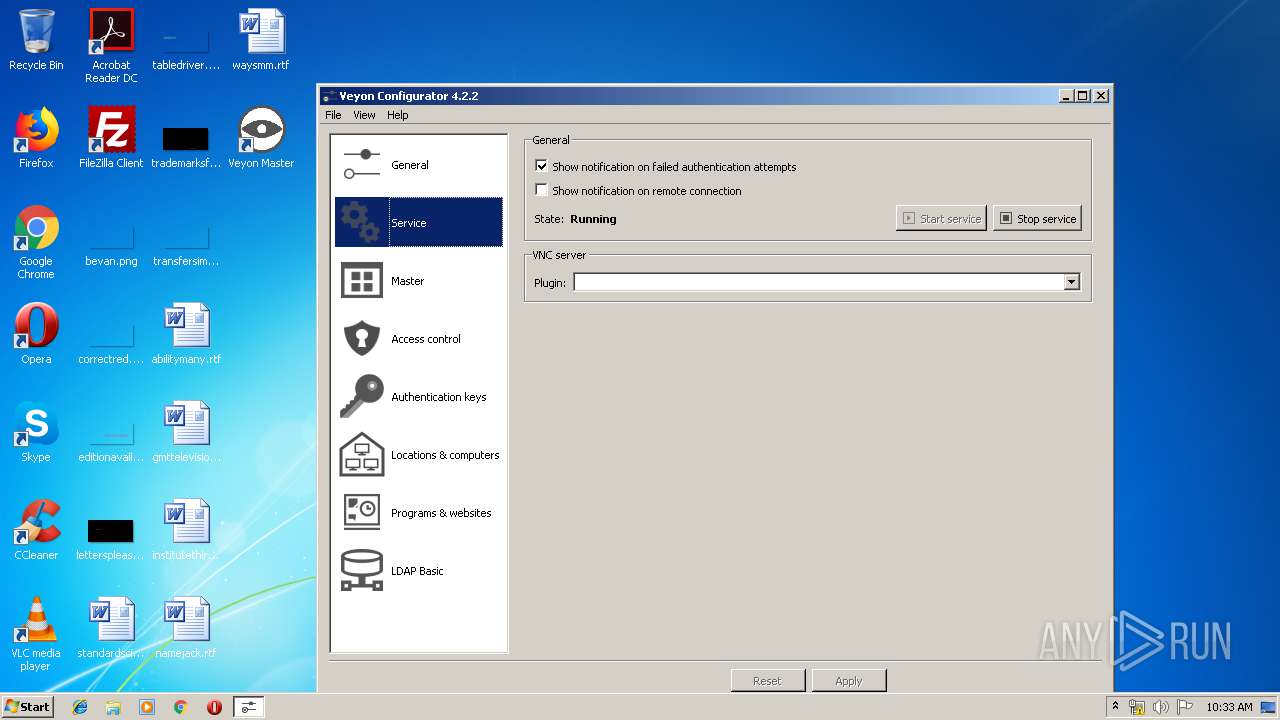
Executed as Windows Service
- veyon-service.exe (PID: 2360)
Executable content was dropped or overwritten
- veyon-4.2.2.0-win32-setup.exe (PID: 3740)
Creates files in the Windows directory
- veyon-server.exe (PID: 2984)
- veyon-service.exe (PID: 2360)
Creates a software uninstall entry
- veyon-4.2.2.0-win32-setup.exe (PID: 3740)
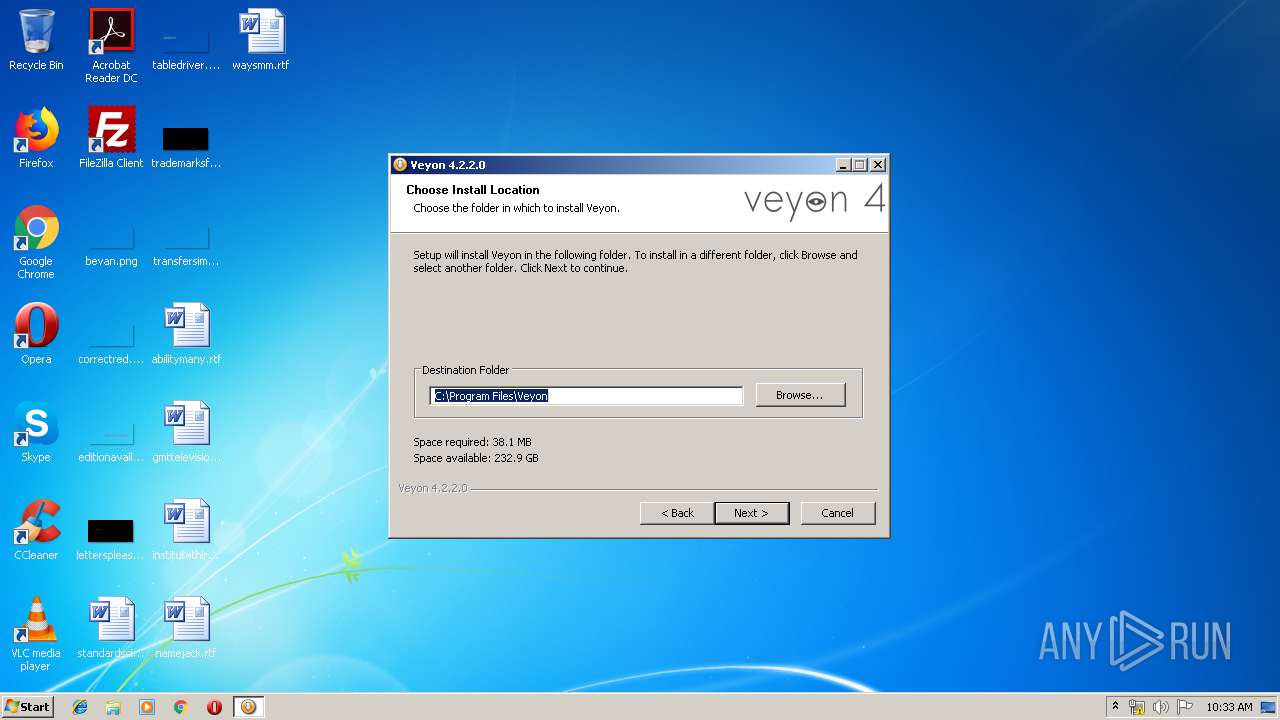
Creates files in the program directory
- veyon-4.2.2.0-win32-setup.exe (PID: 3740)
INFO
Dropped object may contain Bitcoin addresses
- veyon-4.2.2.0-win32-setup.exe (PID: 3740)
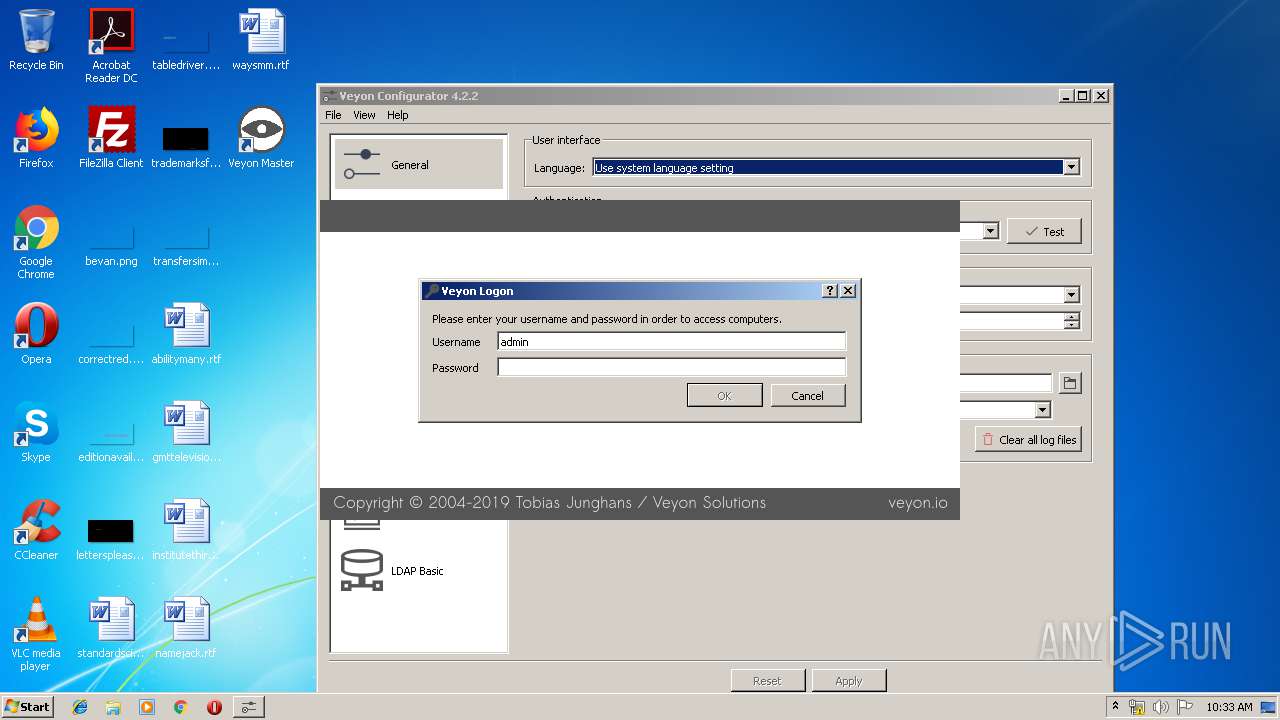
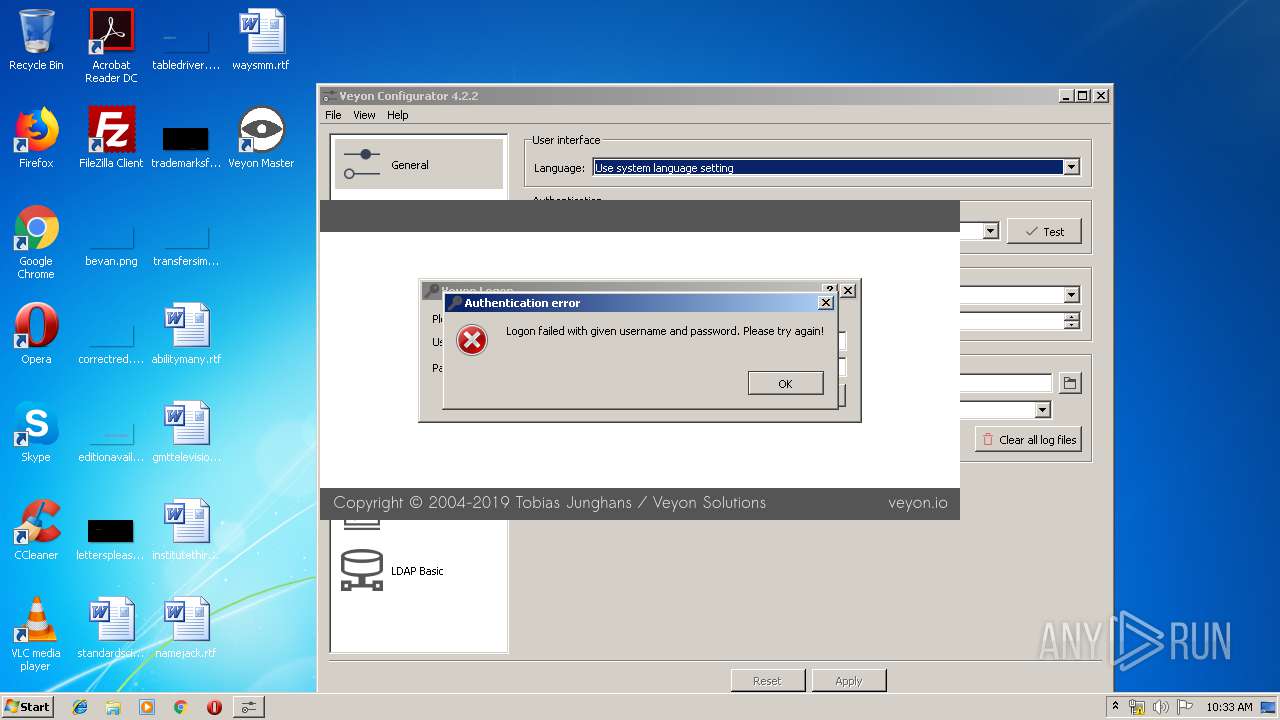
Manual execution by user
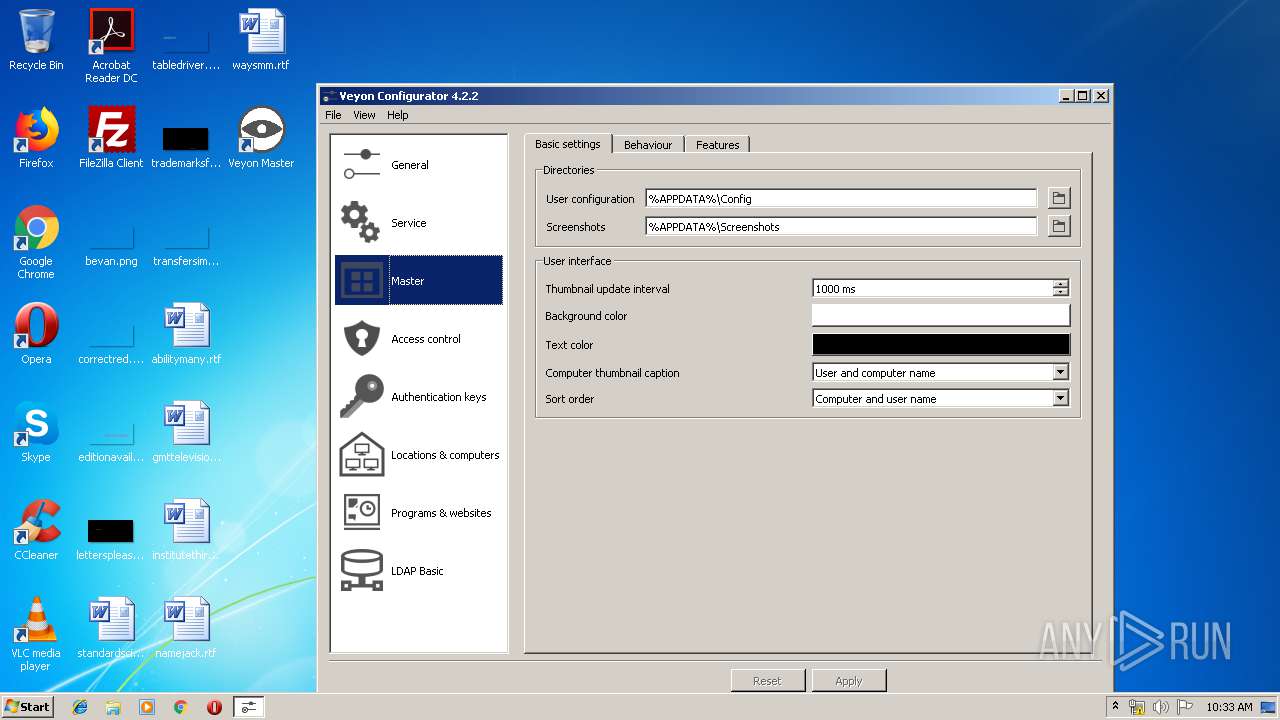
- veyon-master.exe (PID: 2872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:01:07 10:11:30+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.31 |
| CodeSize: | 36864 |
| InitializedDataSize: | 38912 |
| UninitializedDataSize: | 108032 |
| EntryPoint: | 0x4344 |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 4.2.2.0 |
| ProductVersionNumber: | 4.2.2.0 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Windows, Latin1 |
| CompanyName: | Veyon Solutions |
| FileDescription: | Veyon Installer |
| FileVersion: | 4.2.2.0 |
| LegalCopyright: | 2004-2019 Tobias Junghans / Veyon Solutions |
| ProductName: | Veyon |
| ProductVersion: | 4.2.2.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 07-Jan-2019 09:11:30 |
| Detected languages: |
|
| CompanyName: | Veyon Solutions |
| FileDescription: | Veyon Installer |
| FileVersion: | 4.2.2.0 |
| LegalCopyright: | 2004-2019 Tobias Junghans / Veyon Solutions |
| ProductName: | Veyon |
| ProductVersion: | 4.2.2.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 07-Jan-2019 09:11:30 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00008E8C | 0x00009000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.95358 |
.data | 0x0000A000 | 0x000000C0 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.42446 |
.rdata | 0x0000B000 | 0x00006C1C | 0x00006E00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.23655 |
.bss | 0x00012000 | 0x0001A500 | 0x00000000 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_2048BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_8BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0002D000 | 0x00001354 | 0x00001400 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.32256 |
.ndata | 0x0002F000 | 0x00018000 | 0x00000200 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00047000 | 0x0000BD80 | 0x0000BE00 | IMAGE_SCN_ALIGN_1024BYTES, IMAGE_SCN_ALIGN_16BYTES, IMAGE_SCN_ALIGN_1BYTES, IMAGE_SCN_ALIGN_256BYTES, IMAGE_SCN_ALIGN_2BYTES, IMAGE_SCN_ALIGN_32BYTES, IMAGE_SCN_ALIGN_4096BYTES, IMAGE_SCN_ALIGN_4BYTES, IMAGE_SCN_ALIGN_512BYTES, IMAGE_SCN_ALIGN_64BYTES, IMAGE_SCN_ALIGN_8192BYTES, IMAGE_SCN_ALIGN_MASK, IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.97989 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.28905 | 1072 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.61959 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 4.84061 | 3752 | UNKNOWN | English - United States | RT_ICON |
4 | 6.16608 | 2216 | UNKNOWN | English - United States | RT_ICON |
5 | 3.91942 | 1640 | UNKNOWN | English - United States | RT_ICON |
6 | 5.42186 | 1384 | UNKNOWN | English - United States | RT_ICON |
7 | 5.58096 | 1128 | UNKNOWN | English - United States | RT_ICON |
8 | 3.74963 | 744 | UNKNOWN | English - United States | RT_ICON |
9 | 3.01957 | 296 | UNKNOWN | English - United States | RT_ICON |
102 | 2.71813 | 180 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.DLL |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
46
Monitored processes
11
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2360 | "C:\Program Files\Veyon\veyon-service.exe" | C:\Program Files\Veyon\veyon-service.exe | — | services.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2504 | "C:\Program Files\Veyon\veyon-wcli.exe" config set Windows/SoftwareSASEnabled 1 | C:\Program Files\Veyon\veyon-wcli.exe | — | veyon-4.2.2.0-win32-setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
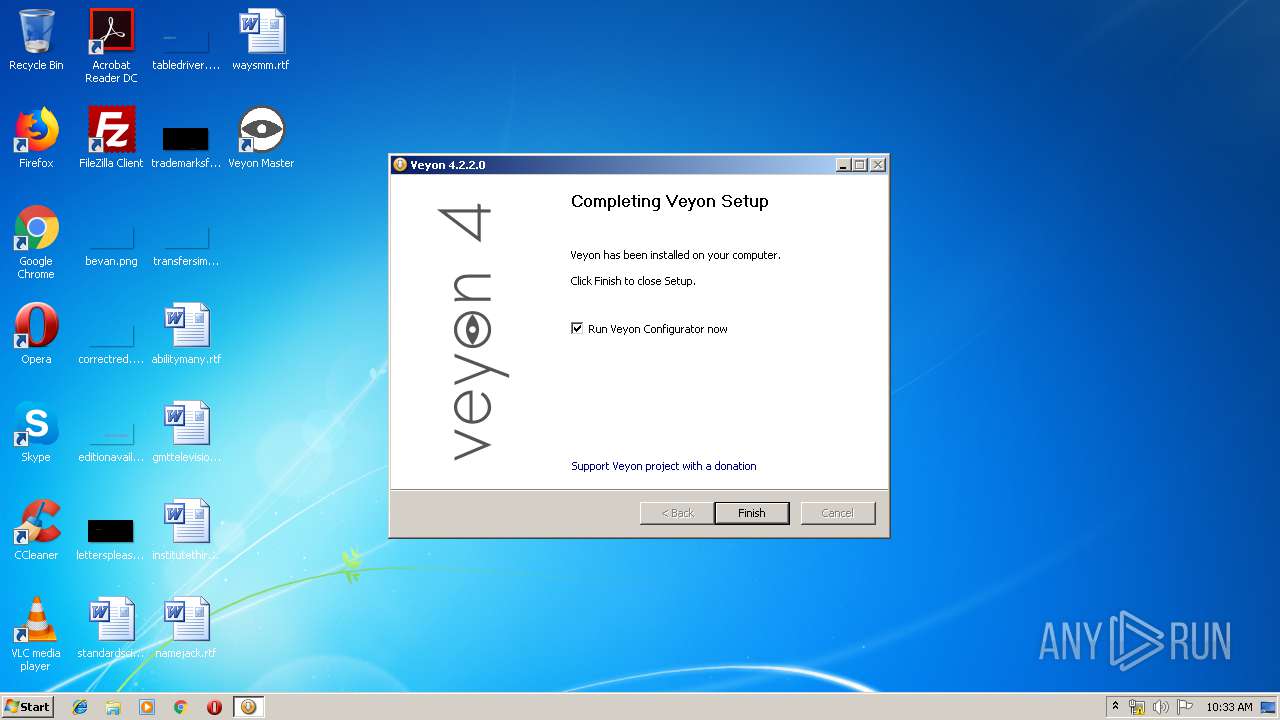
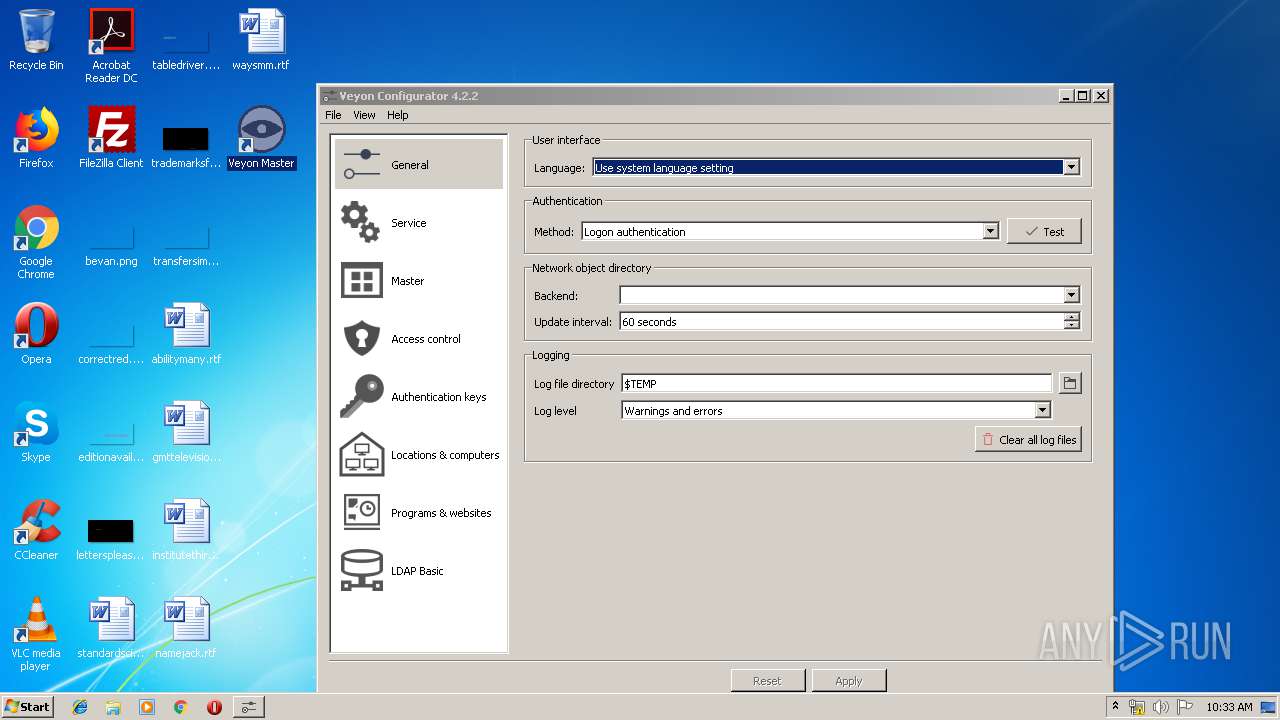
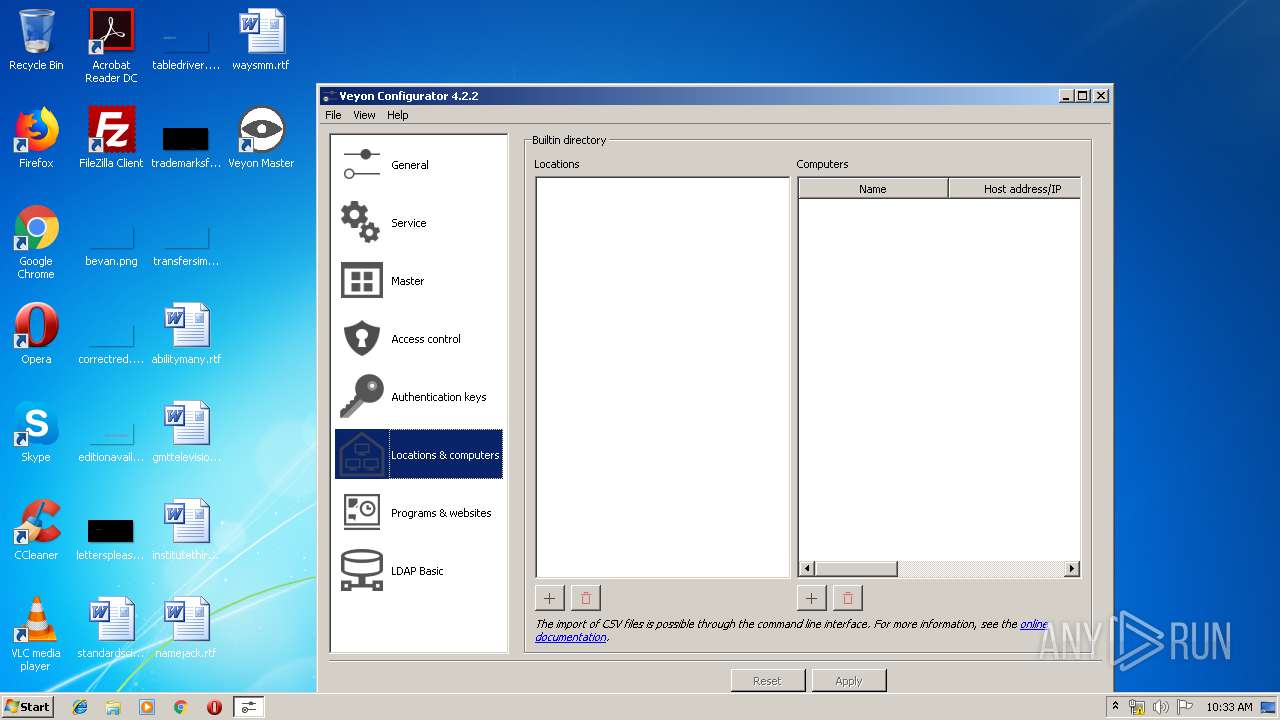
| 2668 | "C:\Program Files\Veyon\veyon-configurator.exe" | C:\Program Files\Veyon\veyon-configurator.exe | — | veyon-4.2.2.0-win32-setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
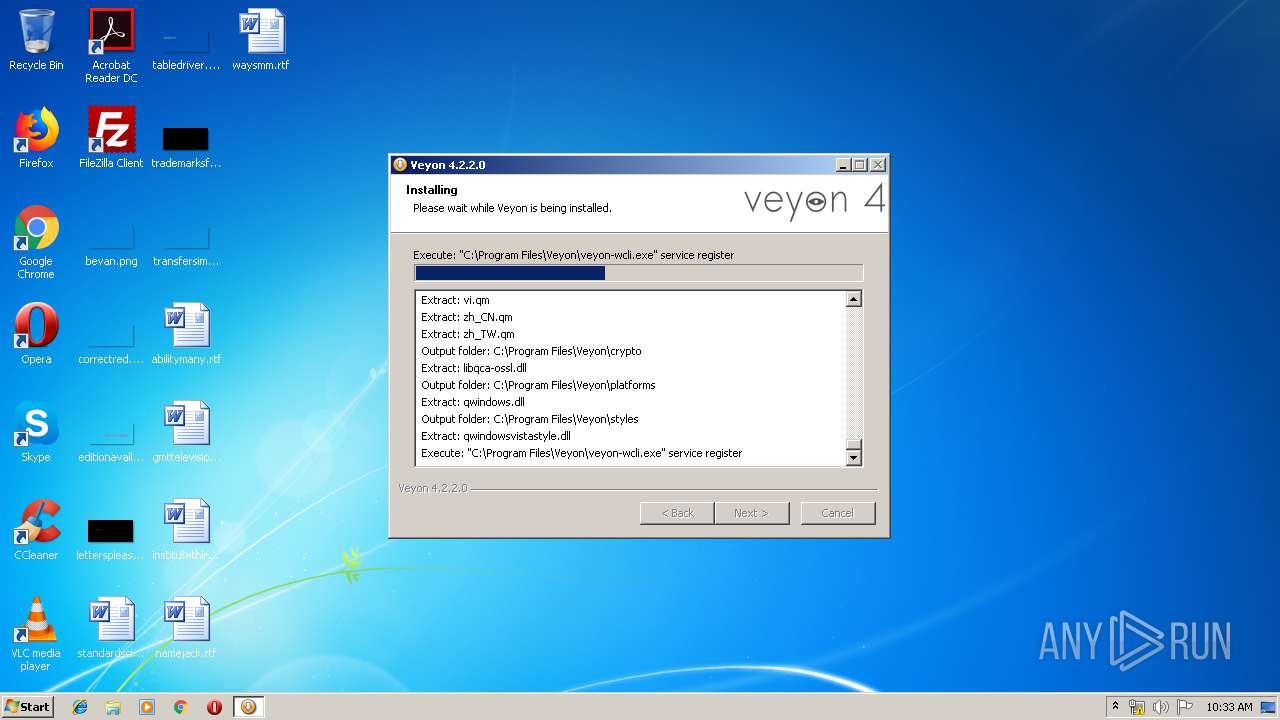
| 2724 | "C:\Program Files\Veyon\veyon-wcli.exe" service register | C:\Program Files\Veyon\veyon-wcli.exe | veyon-4.2.2.0-win32-setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2788 | "C:\Users\admin\AppData\Local\Temp\veyon-4.2.2.0-win32-setup.exe" | C:\Users\admin\AppData\Local\Temp\veyon-4.2.2.0-win32-setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Veyon Solutions Integrity Level: MEDIUM Description: Veyon Installer Exit code: 3221226540 Version: 4.2.2.0 Modules
| |||||||||||||||
| 2872 | "C:\Program Files\Veyon\veyon-master.exe" | C:\Program Files\Veyon\veyon-master.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 4294967295 Modules
| |||||||||||||||
| 2984 | "C:\Program Files\Veyon\veyon-server.exe" | C:\Program Files\Veyon\veyon-server.exe | — | veyon-service.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 3740 | "C:\Users\admin\AppData\Local\Temp\veyon-4.2.2.0-win32-setup.exe" | C:\Users\admin\AppData\Local\Temp\veyon-4.2.2.0-win32-setup.exe | explorer.exe | ||||||||||||
User: admin Company: Veyon Solutions Integrity Level: HIGH Description: Veyon Installer Exit code: 0 Version: 4.2.2.0 Modules
| |||||||||||||||
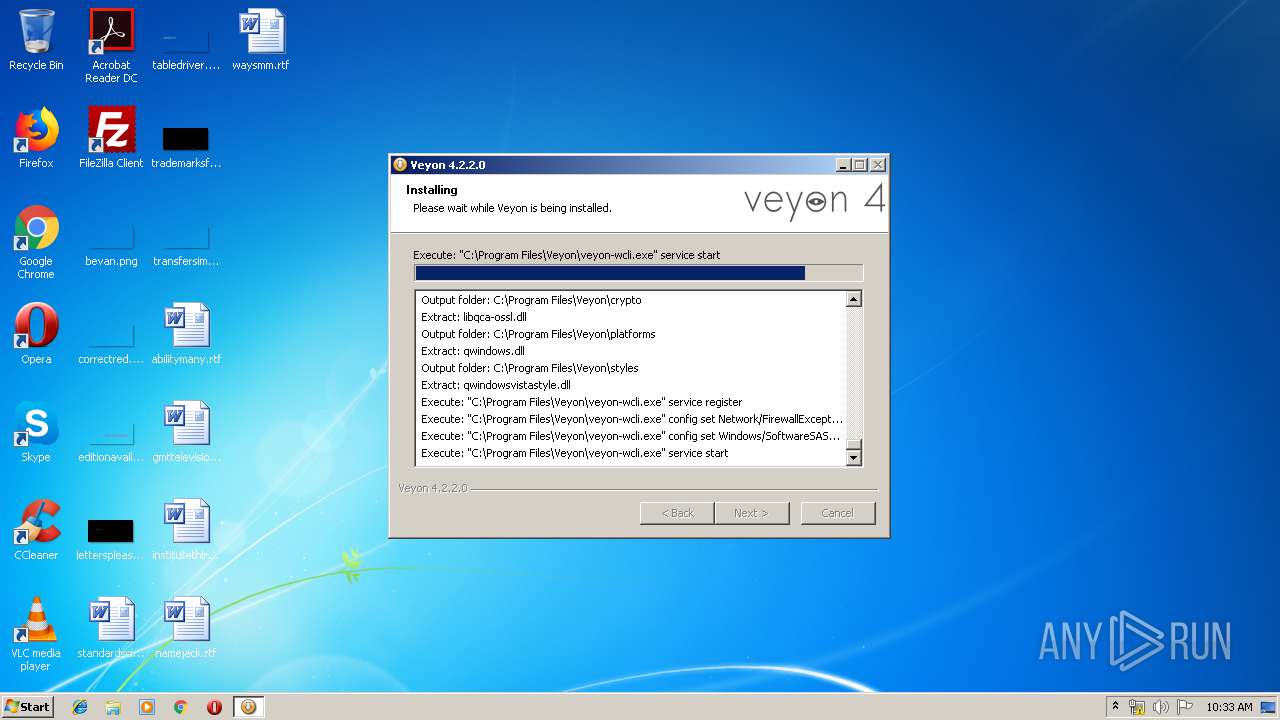
| 3772 | "C:\Program Files\Veyon\veyon-wcli.exe" config set Network/FirewallExceptionEnabled 1 | C:\Program Files\Veyon\veyon-wcli.exe | — | veyon-4.2.2.0-win32-setup.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3796 | "C:\Program Files\Veyon\veyon-worker.exe" {8e997d84-ebb9-430f-8f72-d45d9821963d} | C:\Program Files\Veyon\veyon-worker.exe | veyon-server.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
493
Read events
431
Write events
58
Delete events
4
Modification events
| (PID) Process: | (2724) veyon-wcli.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application\CLI |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Program Files\Veyon\veyon-wcli.exe | |||
| (PID) Process: | (2724) veyon-wcli.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application\CLI |
| Operation: | write | Name: | TypesSupported |
Value: 31 | |||
| (PID) Process: | (3772) veyon-wcli.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application\CLI |
| Operation: | write | Name: | EventMessageFile |
Value: C:\Program Files\Veyon\veyon-wcli.exe | |||
| (PID) Process: | (3772) veyon-wcli.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\services\eventlog\Application\CLI |
| Operation: | write | Name: | TypesSupported |
Value: 31 | |||
| (PID) Process: | (3772) veyon-wcli.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Veyon Solutions\Veyon\Core |
| Operation: | write | Name: | ApplicationVersion |
Value: 2 | |||
| (PID) Process: | (3772) veyon-wcli.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Veyon Solutions\Veyon\Core |
| Operation: | write | Name: | InstallationID |
Value: 1fb7338e-7d96-439b-af38-9dc5ab84b662 | |||
| (PID) Process: | (3772) veyon-wcli.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Veyon Solutions\Veyon\Core |
| Operation: | write | Name: | PluginVersions |
Value: @@JsonValue(eyJvIjp7InsxNGJhY2FhYS1lYmU1LTQ0OWMtYjg4MS01YjM4MmY5NTI1NzF9IjoiMS4xIiwiezFiMDgyNjViLTM0OGYtNDk3OC1hY2FhLTQ1ZDRmNmI5MGJkOX0iOiIxLjEiLCJ7MWJhYTAxZTAtMDJkNi00NDk0LWE3NjYtNzg4ZjViMjI1OTkxfSI6IjEuMSIsInsxYmRiMGQxYy1mOGViLTRkMjEtYTA5My1kNTU1YTEwZjM5NzV9IjoiMS4xIiwiezI5MTdjZGViLWFjMTMtNDA5OS04NzE1LTIwMzY4MjU0YTM2N30iOiIxLjEiLCJ7MmFkOThjY2ItZTlhNS00M2VmLThjNGMtODc2YWM1ZWZiY2IxfSI6IjEuMSIsInszODdhMGM0My0xMzU1LTRmZjYtOWUxZi1kMDk4ZTljZTUxMjd9IjoiMS4xIiwiezM5ZDdhMDdmLTk0ZGItNDkxMi1hYTFhLWM0ZGY4YWVlMzg3OX0iOiIxLjEiLCJ7NDEyMmU4Y2EtYjYxNy00ZTM2LWI4NTEtOGUwNTBlZDJkODJlfSI6IjEuMiIsIns0NzkwYmFkOC00YzU2LTQwZDUtODM2MS0wOTlhNjhmMGMyNGJ9IjoiMS4xIiwiezY3ZGZjMWMxLThmMzctNDUzOS1hMjk4LTE2ZTc0ZTM0ZmQ4Yn0iOiIxLjEiLCJ7NmYwYTQ5MWUtYzFjNi00MzM4LTgyNDQtZjgyM2IwYmY4NjcwfSI6IjEuMiIsIns4NWY2YzYzMS1lNzVhLTRjNzgtOGNiMi1hN2YzZjUwMjAxNWF9IjoiMS4xIiwiezhhZTY2NjhiLTljMTItNGIyOS05YmZjLWZmODlmNjYwNDE2NH0iOiIxLjEiLCJ7YTU0ZWUwMTgtNDJiZi00NTY5LTkwYzctMGQ4NDcwMTI1Y2NmfSI6IjEuMSIsIntiNDdiY2FlMC0yNGZmLTRiZjUtODY5Yy00ODRkNjRhZjVjNGN9IjoiMS4xIiwie2Q0YmI5YzQyLTllZWYtNGVjYi04ZGQ1LWRmZDg0YjM1NTQ4MX0iOiIxLjAiLCJ7ZWUzMjI1MjEtZjRmYi00ODJkLWIwODItODJhNzkwMDNhZmE3fSI6IjEuMSJ9fQ==) | |||
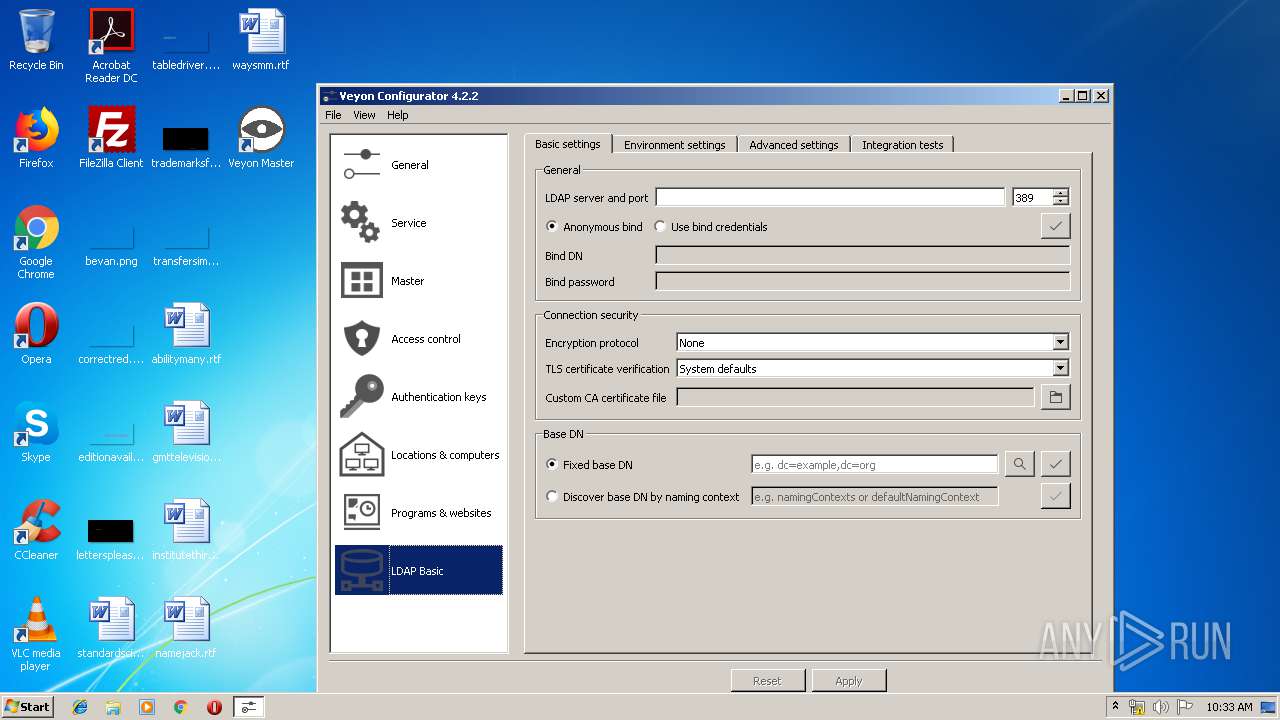
| (PID) Process: | (3772) veyon-wcli.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Veyon Solutions\Veyon\LDAP |
| Operation: | write | Name: | ComputerLocationAttribute |
Value: | |||
| (PID) Process: | (3772) veyon-wcli.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Veyon Solutions\Veyon\LDAP |
| Operation: | write | Name: | ComputerLocationsByAttribute |
Value: false | |||
| (PID) Process: | (3772) veyon-wcli.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Veyon Solutions\Veyon\LDAP |
| Operation: | write | Name: | ComputerLocationsByContainer |
Value: false | |||
Executable files
59
Suspicious files
0
Text files
9
Unknown types
66
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3740 | veyon-4.2.2.0-win32-setup.exe | C:\Program Files\Veyon\veyon-cli.exe | executable | |
MD5:69ECF1C538F6C1AAB1FA9393D1C0A7DD | SHA256:4F546A64A6062732155DB90AFB7AB5E5119C506D5052F0661E7BCBF4B56B6D58 | |||
| 3740 | veyon-4.2.2.0-win32-setup.exe | C:\Program Files\Veyon\veyon-server.exe | executable | |
MD5:EADDB26B0E0D2FB98E6458C10285094E | SHA256:AF10E90F1B4AD28E39FBFC6F66B6F84F8FBF3BCC0E94387889A38562A3E3A736 | |||
| 3740 | veyon-4.2.2.0-win32-setup.exe | C:\Program Files\Veyon\Qt5Concurrent.dll | executable | |
MD5:86E8AF5459F71625F8465D54CC2DF9B7 | SHA256:B85C7E7149626066E6205DFA17F79DC693F48E647A43285A568134D2ACC243E7 | |||
| 3740 | veyon-4.2.2.0-win32-setup.exe | C:\Program Files\Veyon\veyon-configurator.exe | executable | |
MD5:CC80BF12F1A7C1EFEC1018C3A8F57260 | SHA256:65F702B6C477384EA72A16EB541C6369CB383A81A4042AD0D4DFD596483CF4B9 | |||
| 3740 | veyon-4.2.2.0-win32-setup.exe | C:\Program Files\Veyon\veyon-worker.exe | executable | |
MD5:1AF78E87C7A890FA2C0599E4D4CB570C | SHA256:FD6B0E06E30F5A7C6BD2FACF808ED0696094D6A907548A41C8E3B98D63FE439E | |||
| 3740 | veyon-4.2.2.0-win32-setup.exe | C:\Program Files\Veyon\veyon-service.exe | executable | |
MD5:D89A747FE98772CA6574E2069440AF2C | SHA256:B7902F2DE645C9258D1069D701D81640FF4B4D763A1AA3E227A8D1623FB69543 | |||
| 3740 | veyon-4.2.2.0-win32-setup.exe | C:\Program Files\Veyon\ddengine.dll | executable | |
MD5:A9F077D1EB81FFE4FFC2A774E988ECC5 | SHA256:BD044BF280D3DFFED9D8B0B1A65505CD7BA212879F0171D1207B2003068E6746 | |||
| 3740 | veyon-4.2.2.0-win32-setup.exe | C:\Program Files\Veyon\Qt5Widgets.dll | executable | |
MD5:748E76A7F0E2DDD3C4451097867912A3 | SHA256:0B41038CC480CB5FD21F4EA3A23FC5F1D365F344FC4CB541D88AAE73D3AC9B61 | |||
| 3740 | veyon-4.2.2.0-win32-setup.exe | C:\Program Files\Veyon\Qt5Gui.dll | executable | |
MD5:ED4A7FD7F1CDA0254D2C3207C3F03419 | SHA256:802C313BCF6A236207F6D12F2AD50A495F0AB0BD97521E5597589D250AF2FD6C | |||
| 3740 | veyon-4.2.2.0-win32-setup.exe | C:\Program Files\Veyon\libgcc_s_sjlj-1.dll | executable | |
MD5:64D36A7334F4A512B1F67CB2B15B968A | SHA256:456F4B31A7A7B8507BFA9E2ACD01B6FB7DD3B33741D308BF36E756D943CF2B91 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
veyon-wcli.exe | QWaitCondition: Destroyed while threads are still waiting
|
veyon-wcli.exe | QWaitCondition: Destroyed while threads are still waiting
|