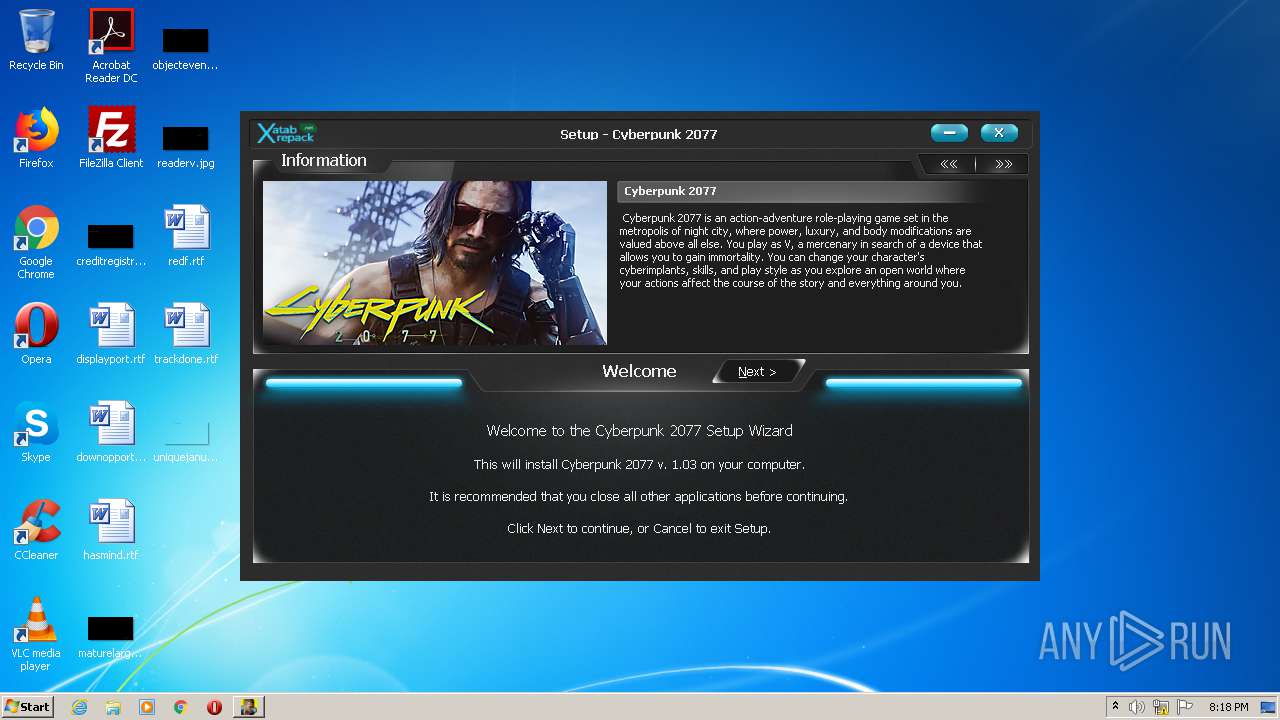
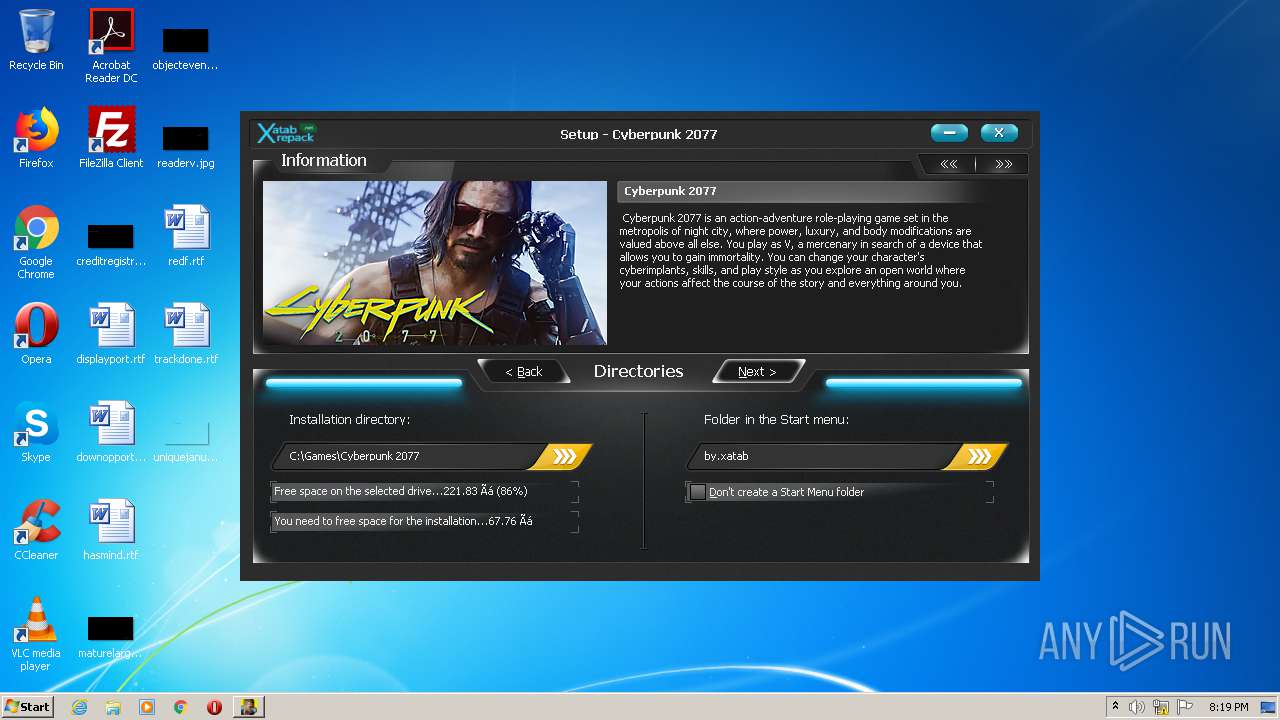
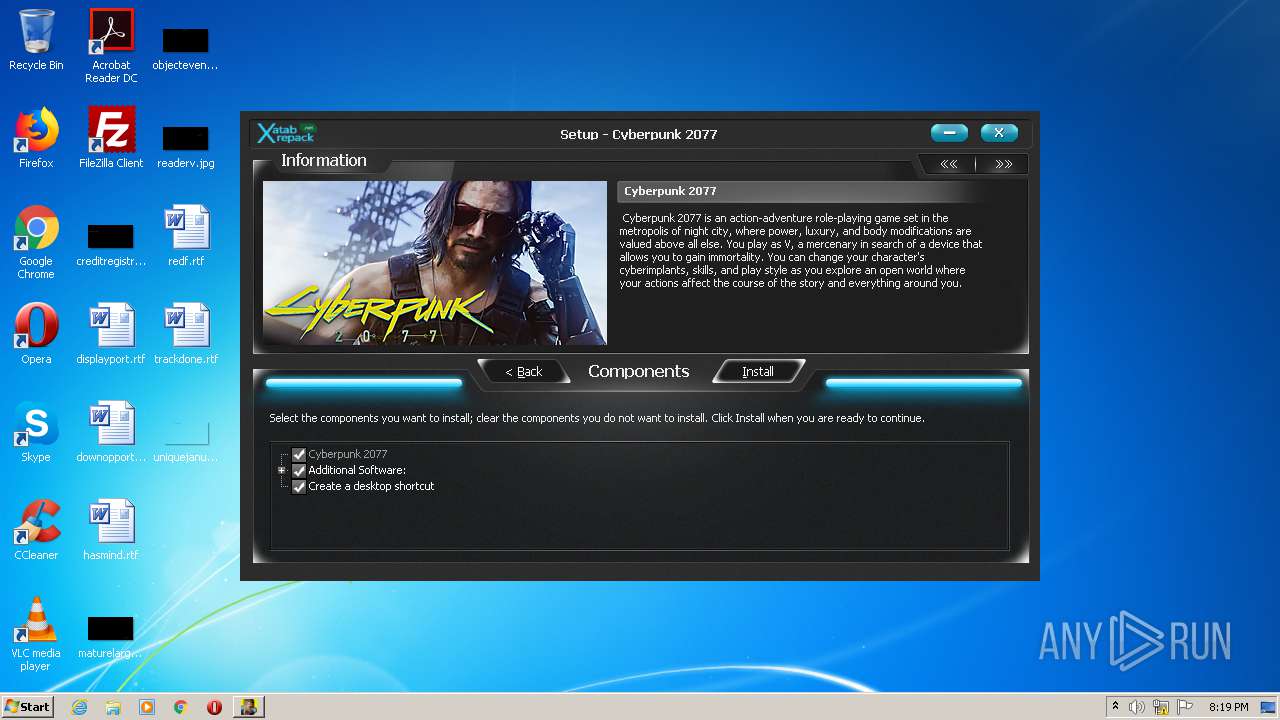
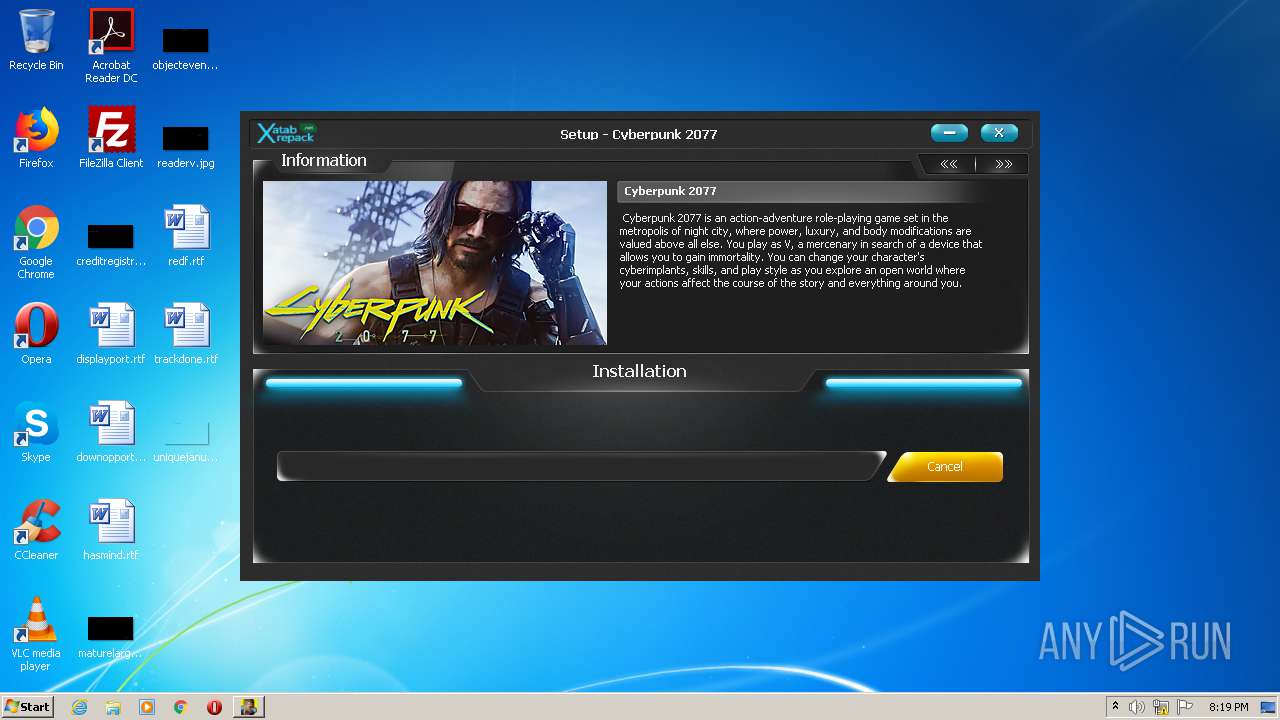
| File name: | setup.exe |
| Full analysis: | https://app.any.run/tasks/0611f008-1a82-4a0c-af82-87788babe35f |
| Verdict: | Malicious activity |
| Analysis date: | December 12, 2020, 20:17:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8A5EFB4CB8924F14E144C6A68B8757A8 |
| SHA1: | A6959DCB0C447EAE6A685199DFC52F921E728B39 |
| SHA256: | DC0757E9827610BDA5D7C10D926474D9571CEBD4466A96702FFC08BE02F624A7 |
| SSDEEP: | 98304:J6lThL07I0X3nb3czb2ZElKMnQEdKutIxKCCgN:UtLiI0XbD9MnJcuixfCQ |
MALICIOUS
Drops executable file immediately after starts
- setup.exe (PID: 2688)
- setup.tmp (PID: 3092)
Application was dropped or rewritten from another process
- _iu14D2N.tmp (PID: 2144)
- unins000.exe (PID: 2400)
SUSPICIOUS
Executable content was dropped or overwritten
- setup.exe (PID: 2688)
- setup.tmp (PID: 3092)
Drops a file that was compiled in debug mode
- setup.tmp (PID: 3092)
Reads Windows owner or organization settings
- setup.tmp (PID: 3092)
Drops a file with too old compile date
- setup.tmp (PID: 3092)
Reads the Windows organization settings
- setup.tmp (PID: 3092)
Starts application with an unusual extension
- unins000.exe (PID: 2400)
Starts itself from another location
- unins000.exe (PID: 2400)
INFO
Loads dropped or rewritten executable
- setup.tmp (PID: 3092)
Application was dropped or rewritten from another process
- setup.tmp (PID: 3092)
Creates a software uninstall entry
- setup.tmp (PID: 3092)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (81.5) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10.5) |
| .exe | | | Win32 Executable (generic) (3.3) |
| .exe | | | Win16/32 Executable Delphi generic (1.5) |
| .exe | | | Generic Win/DOS Executable (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:10:02 07:04:04+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 86016 |
| InitializedDataSize: | 630784 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x16478 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
| FileDescription: | Cyberpunk 2077 Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | Cyberpunk 2077 |
| ProductVersion: |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 02-Oct-2012 05:04:04 |
| Detected languages: |
|
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | - |
| FileDescription: | Cyberpunk 2077 Setup |
| FileVersion: | - |
| LegalCopyright: | - |
| ProductName: | Cyberpunk 2077 |
| ProductVersion: | - |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0050 |
| Pages in file: | 0x0002 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x000F |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x001A |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000100 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 8 |
| Time date stamp: | 02-Oct-2012 05:04:04 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000143F8 | 0x00014400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4822 |
.itext | 0x00016000 | 0x00000BE8 | 0x00000C00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.01516 |
.data | 0x00017000 | 0x00000D9C | 0x00000E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.66929 |
.bss | 0x00018000 | 0x00005750 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.idata | 0x0001E000 | 0x00000F9E | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.96778 |
.tls | 0x0001F000 | 0x00000008 | 0x00000000 | IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rdata | 0x00020000 | 0x00000018 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 0.190489 |
.rsrc | 0x00021000 | 0x00097E88 | 0x00098000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.90021 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.1535 | 1582 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 6.41331 | 1720 | Latin 1 / Western European | English - United States | RT_ICON |
3 | 6.48772 | 2440 | Latin 1 / Western European | English - United States | RT_ICON |
4 | 6.53104 | 4264 | Latin 1 / Western European | English - United States | RT_ICON |
5 | 6.4721 | 6760 | Latin 1 / Western European | English - United States | RT_ICON |
6 | 6.49709 | 9640 | Latin 1 / Western European | English - United States | RT_ICON |
7 | 6.50902 | 13032 | Latin 1 / Western European | English - United States | RT_ICON |
8 | 6.51772 | 16936 | Latin 1 / Western European | English - United States | RT_ICON |
9 | 6.48401 | 21640 | Latin 1 / Western European | English - United States | RT_ICON |
10 | 6.49085 | 26600 | Latin 1 / Western European | English - United States | RT_ICON |
Imports
advapi32.dll |
comctl32.dll |
kernel32.dll |
oleaut32.dll |
user32.dll |
Total processes
41
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2144 | "C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp" /SECONDPHASE="C:\Games\Cyberpunk 2077\unins000.exe" /FIRSTPHASEWND=$20182 /VERYSILENT | C:\Users\admin\AppData\Local\Temp\_iu14D2N.tmp | — | unins000.exe | |||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 | |||||||||||||||
| 2400 | "C:\Games\Cyberpunk 2077\unins000.exe" /VERYSILENT | C:\Games\Cyberpunk 2077\unins000.exe | — | setup.tmp | |||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 | |||||||||||||||
| 2688 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Cyberpunk 2077 Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2988 | "C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\setup.exe | — | explorer.exe | |||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Cyberpunk 2077 Setup Exit code: 3221226540 Version: Modules
| |||||||||||||||
| 3092 | "C:\Users\admin\AppData\Local\Temp\is-2JNEC.tmp\setup.tmp" /SL5="$60138,2420149,717824,C:\Users\admin\AppData\Local\Temp\setup.exe" | C:\Users\admin\AppData\Local\Temp\is-2JNEC.tmp\setup.tmp | setup.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.1052.0.0 Modules
| |||||||||||||||
Total events
71
Read events
30
Write events
41
Delete events
0
Modification events
| (PID) Process: | (3092) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 140C0000904207EBC3D0D601 | |||
| (PID) Process: | (3092) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: 2984E6B2BC8D5CB7ACE2DD2294FDB56A82B163B5C76189AA9593B2CE2BA8B252 | |||
| (PID) Process: | (3092) setup.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3092) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\GOG.com\Games\1423049311 |
| Operation: | write | Name: | installer_language |
Value: russian | |||
| (PID) Process: | (3092) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\GOG.com\Games\1423049311 |
| Operation: | write | Name: | gameName |
Value: Cyberpunk 2077 | |||
| (PID) Process: | (3092) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\GOG.com\Games\1423049311 |
| Operation: | write | Name: | gameID |
Value: 1423049311 | |||
| (PID) Process: | (3092) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\GOG.com\Games\1423049311 |
| Operation: | write | Name: | productID |
Value: 1423049311 | |||
| (PID) Process: | (3092) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\GOG.com\Games\1423049311 |
| Operation: | write | Name: | language |
Value: russian | |||
| (PID) Process: | (3092) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\GOG.com\Games\1423049311 |
| Operation: | write | Name: | lang_code |
Value: ru-RU | |||
| (PID) Process: | (3092) setup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\GOG.com\Games\1423049311 |
| Operation: | write | Name: | path |
Value: C:\Games\Cyberpunk 2077 | |||
Executable files
16
Suspicious files
0
Text files
12
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3092 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-3JRMK.tmp\isskin.dll | executable | |
MD5:92C2E247392E0E02261DEA67E1BB1A5E | SHA256:25FDB94E386F8A41F10ABA00ED092A91B878339F8E256A7252B11169122B0A68 | |||
| 3092 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-3JRMK.tmp\ISDone.dll | executable | |
MD5:4FEAFA8B5E8CDB349125C8AF0AC43974 | SHA256:BB8A0245DCC5C10A1C7181BAD509B65959855009A8105863EF14F2BB5B38AC71 | |||
| 3092 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-3JRMK.tmp\b2p.dll | executable | |
MD5:DAE5ED5F828C64E0A2ADC0A98A08CA46 | SHA256:89FF2808EC92B072F347C10D30D1CDE0441925EE626D0C192EC4BA86F0E8398E | |||
| 3092 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-3JRMK.tmp\unarc.dll | executable | |
MD5:56A2BCECBD3CDDD6F4A35361BF4920D6 | SHA256:5FCFAC18758A12E0E717A5189F379922A32B5AC12F26491E638D70B54AE1DCAB | |||
| 3092 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-3JRMK.tmp\cls.ini | text | |
MD5:CFD9F12C9D0CF664D5B672A222F8DA49 | SHA256:EFB80E03B818B9FE848DFD0C7B0D3F3812A5CACC4B4A0AF913BA13801921E5AB | |||
| 3092 | setup.tmp | C:\Games\Cyberpunk 2077\is-990VR.tmp | — | |
MD5:— | SHA256:— | |||
| 3092 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-3JRMK.tmp\WizImg1.bmp | image | |
MD5:911567C946619B4883DC497B7EAE8854 | SHA256:752334102550456F8B381DEDAE4E00DC50DED1DCA4BB0DCA8A6199534067807F | |||
| 3092 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-3JRMK.tmp\WizImg3.bmp | image | |
MD5:5C323B9884ADACAF956A720FA9770564 | SHA256:9050BE4E5859036B9DF2A891DCAC21FFEAB2AC6C1F4F86420F35269CB86E5016 | |||
| 3092 | setup.tmp | C:\Users\admin\AppData\Local\Temp\is-3JRMK.tmp\WizImg2.bmp | image | |
MD5:E2E6E55E3FE56ACB3EA8866B6B3707D2 | SHA256:90810B38EFBC2A21B90412CD696FCC8D9F91F8811754B8CEBEB2685285666D5E | |||
| 2688 | setup.exe | C:\Users\admin\AppData\Local\Temp\is-2JNEC.tmp\setup.tmp | executable | |
MD5:58330B30BF798C37CEAA3EF585FC2DEC | SHA256:6DB6E235A6F5613CC5845A2BD391EB1D82EFA9F64164B9FF34D6D309B903D794 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report