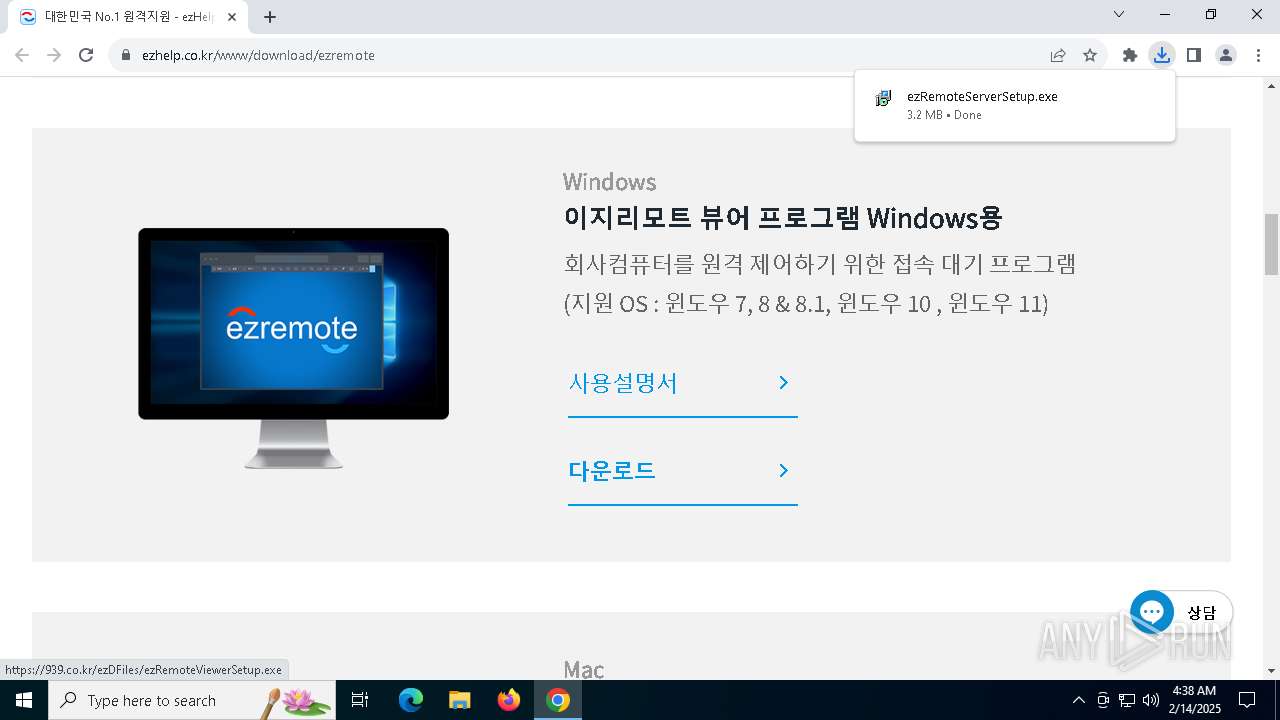
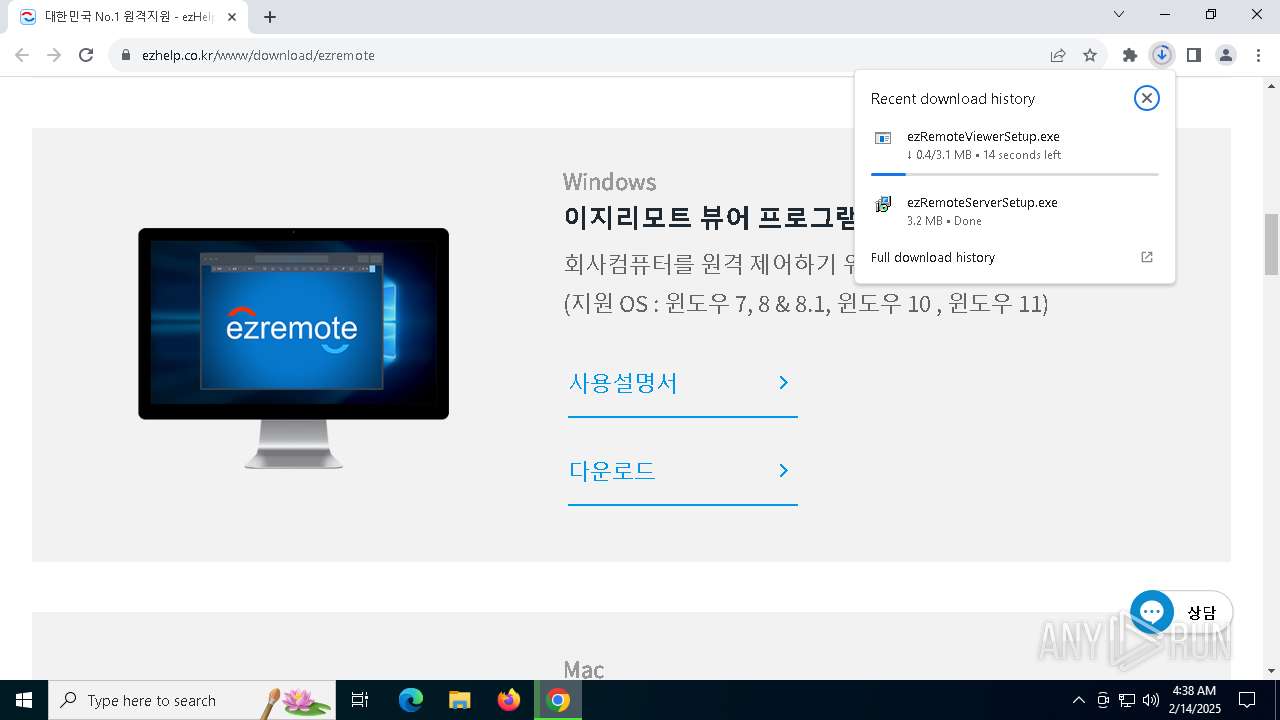
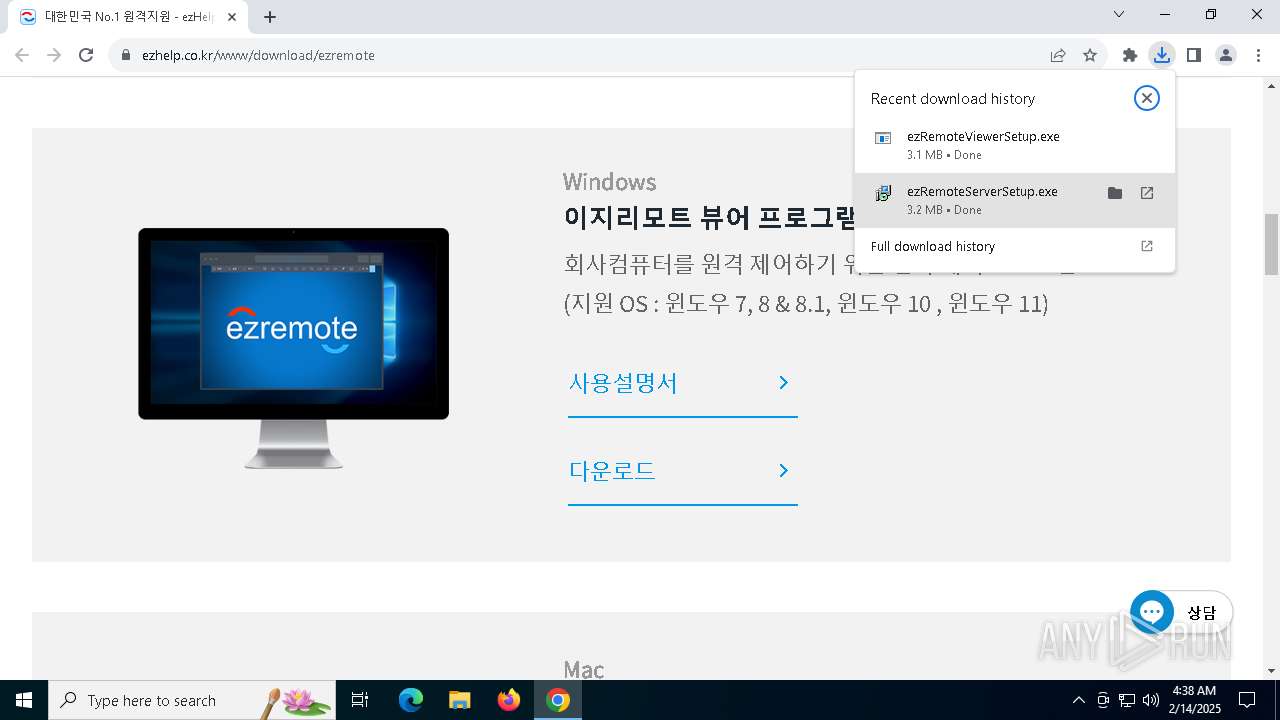
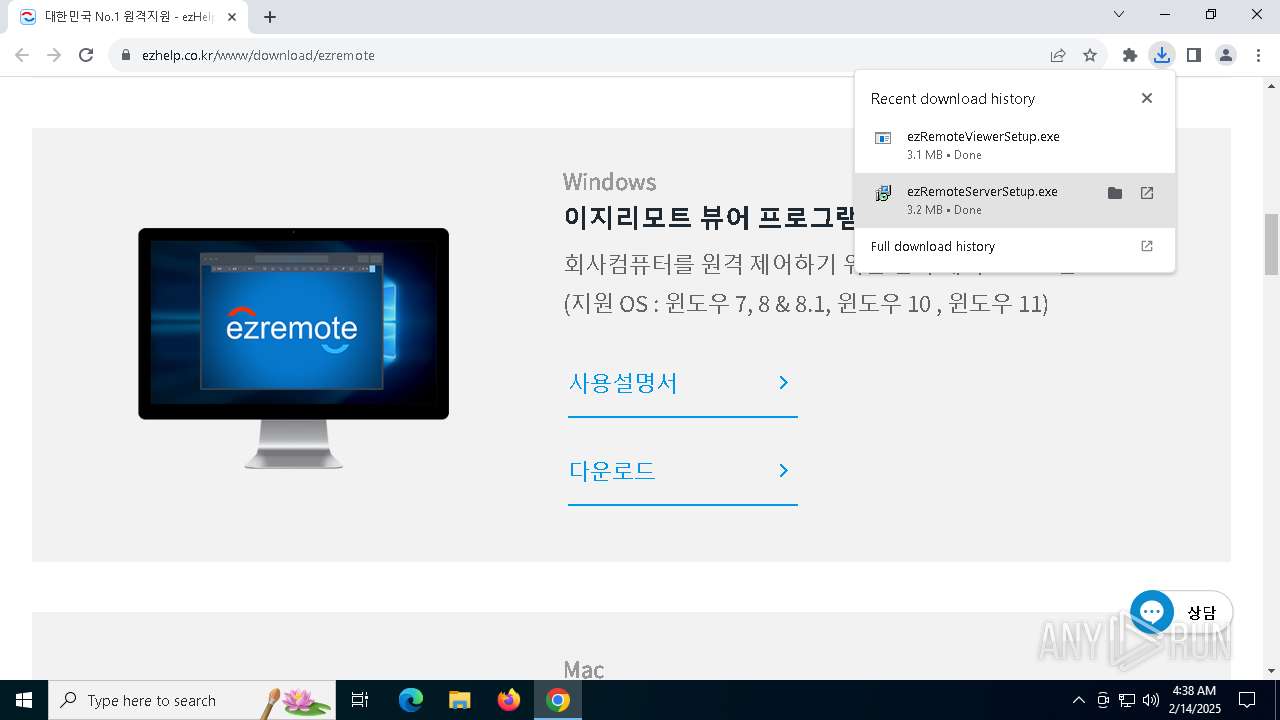
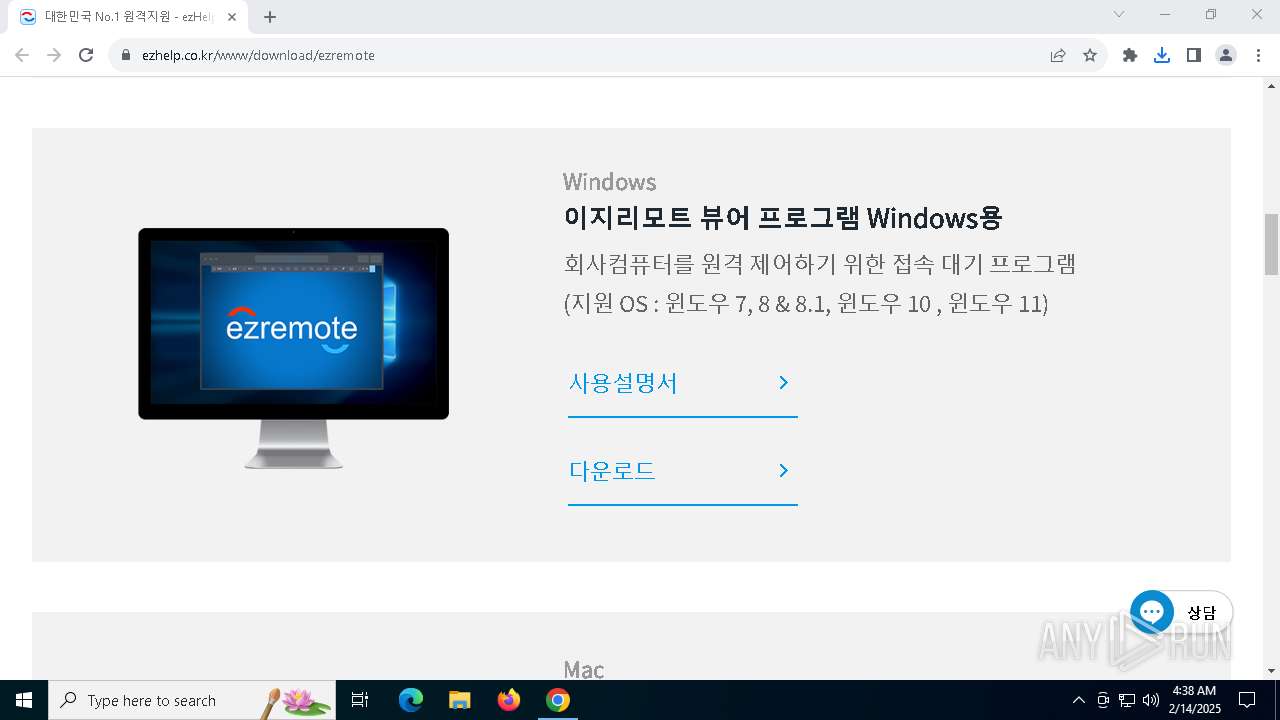
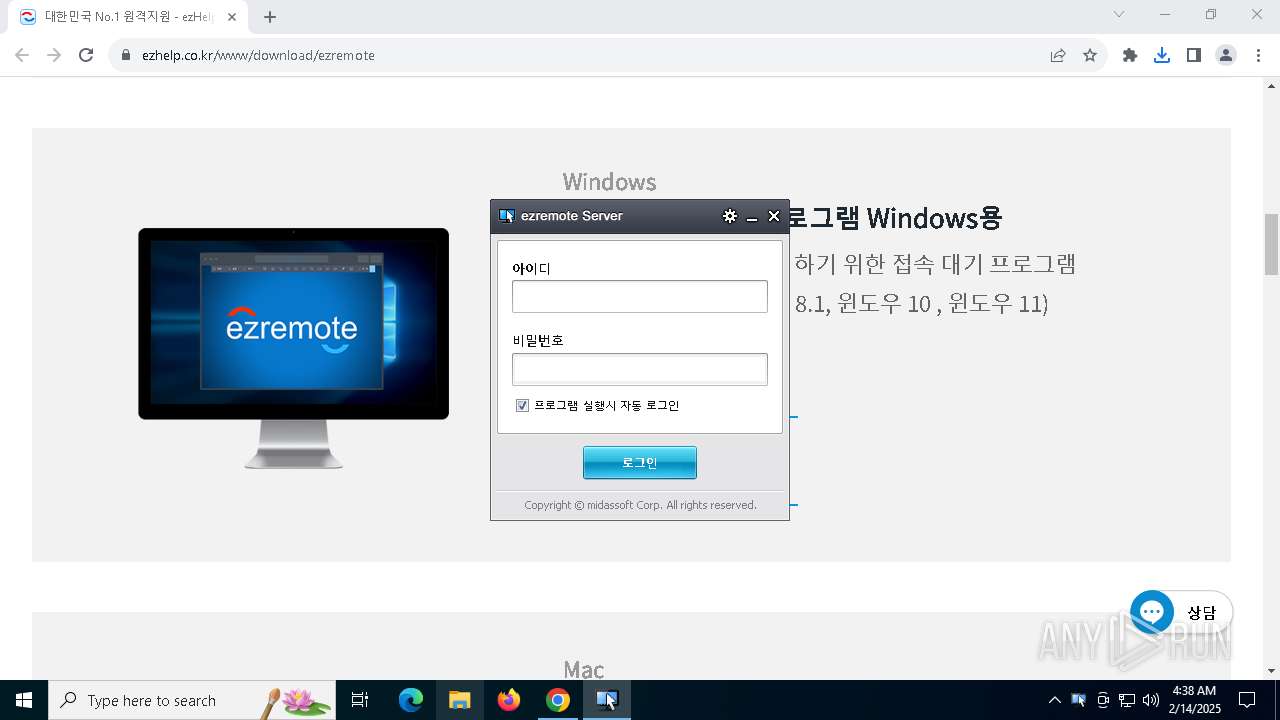
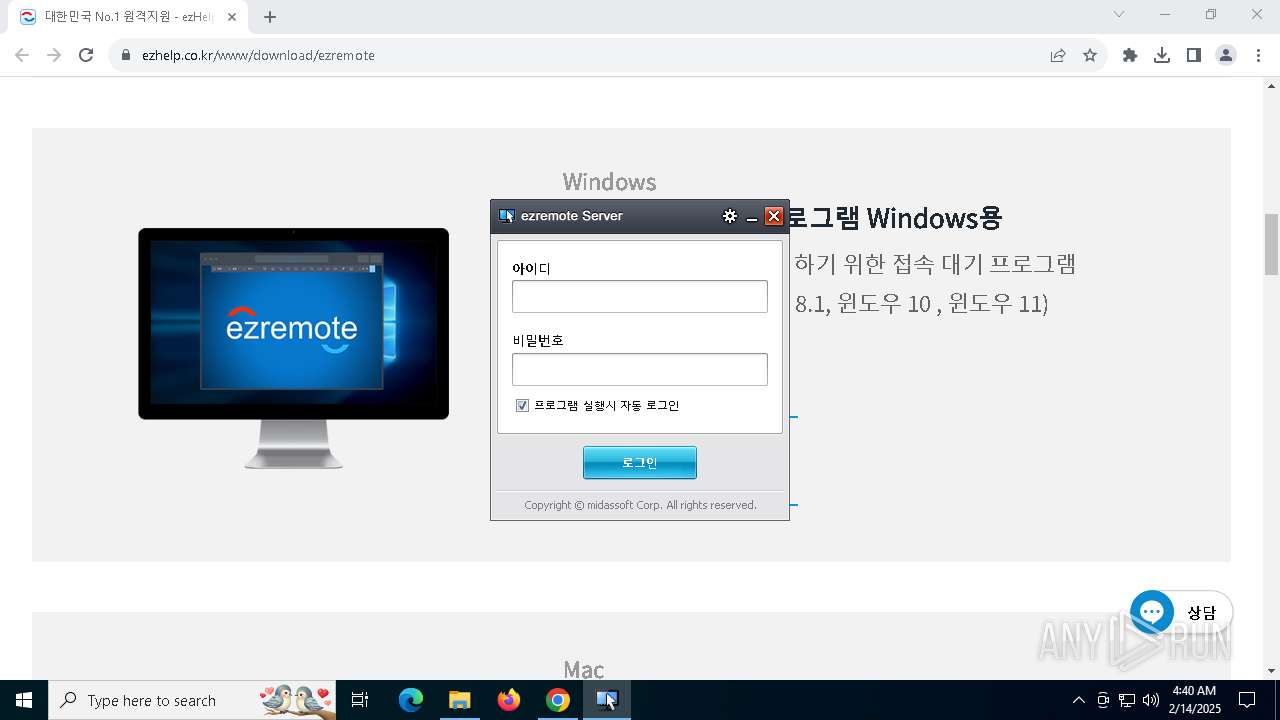
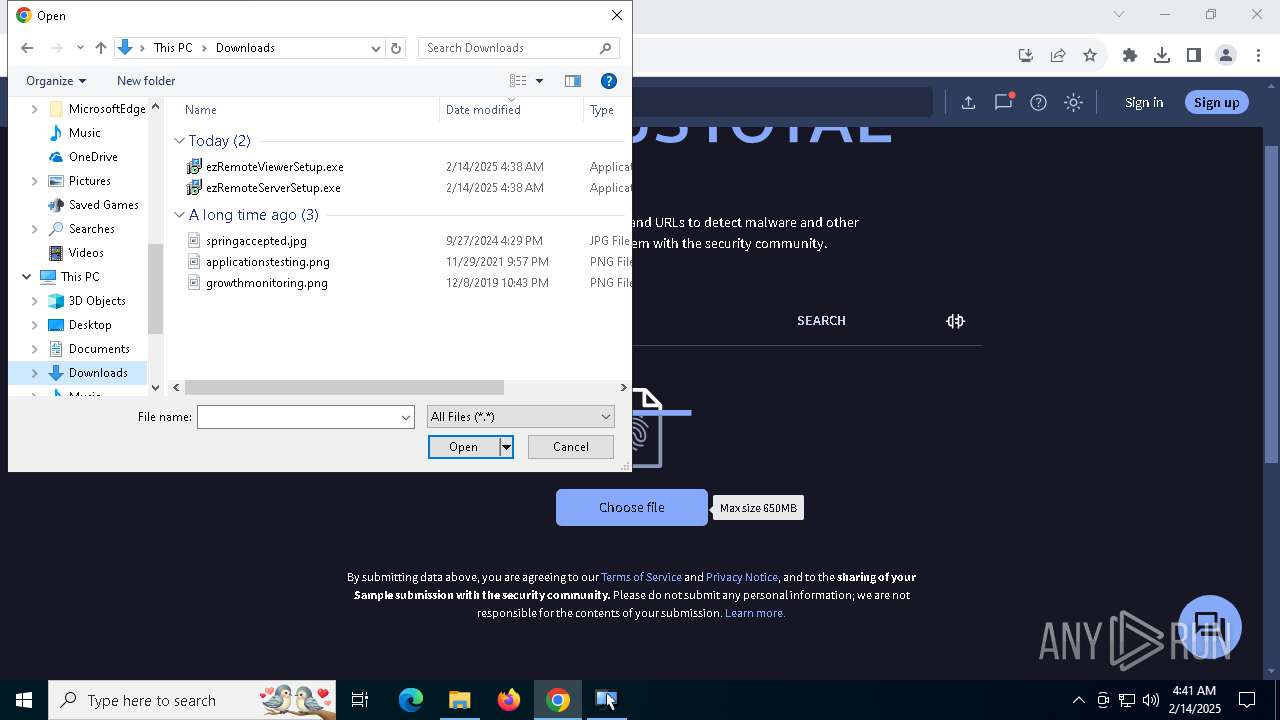
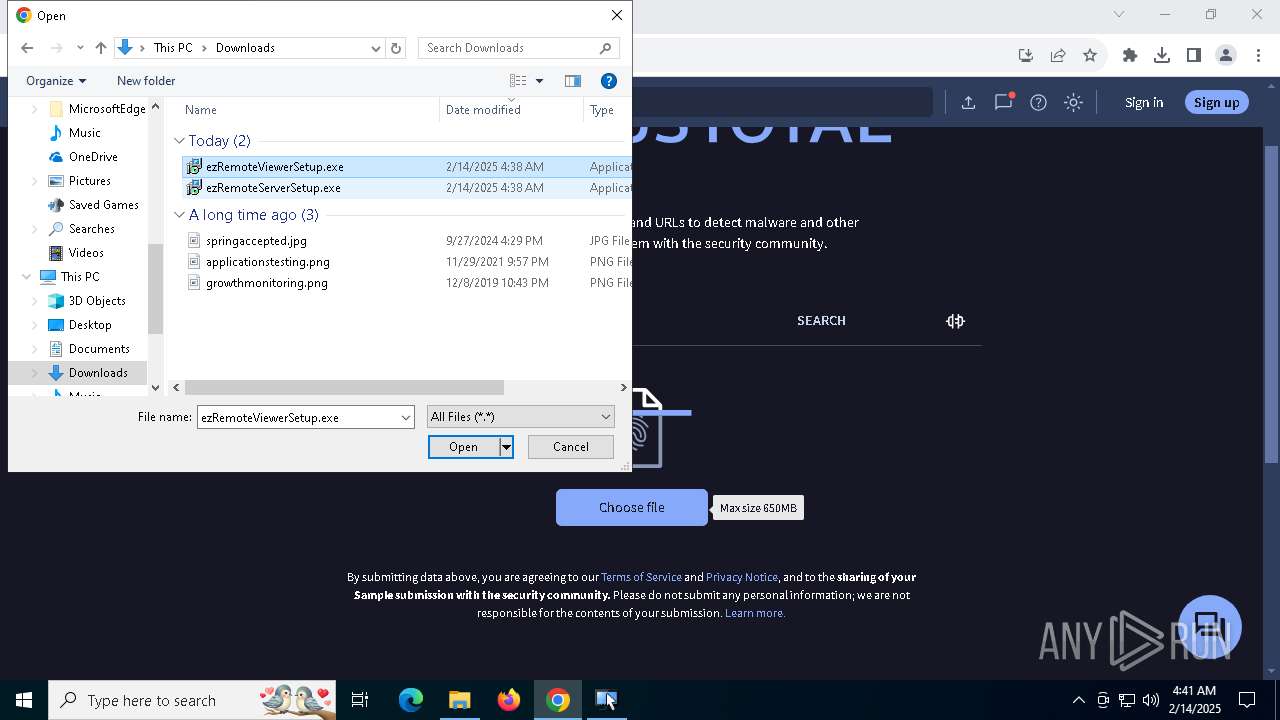
| URL: | https://www.ezhelp.co.kr/www/download/ezremote |
| Full analysis: | https://app.any.run/tasks/0f7f11de-f922-4550-b3dd-32321c62efcb |
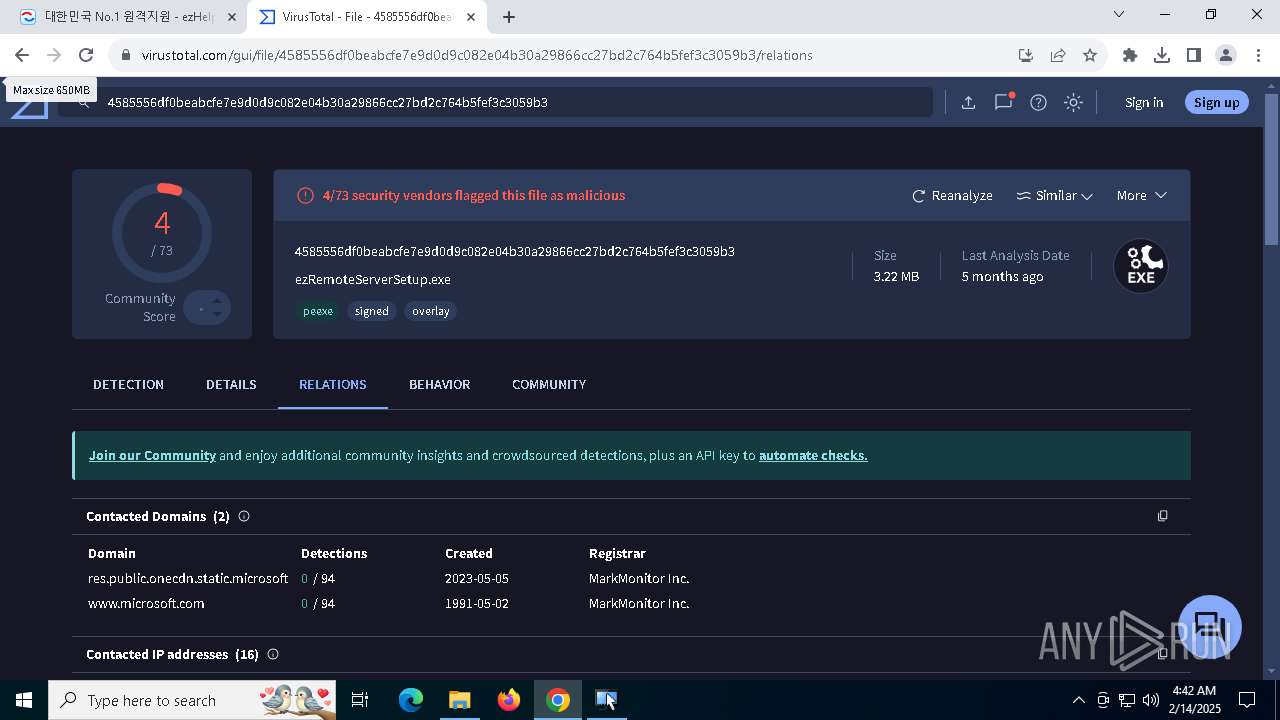
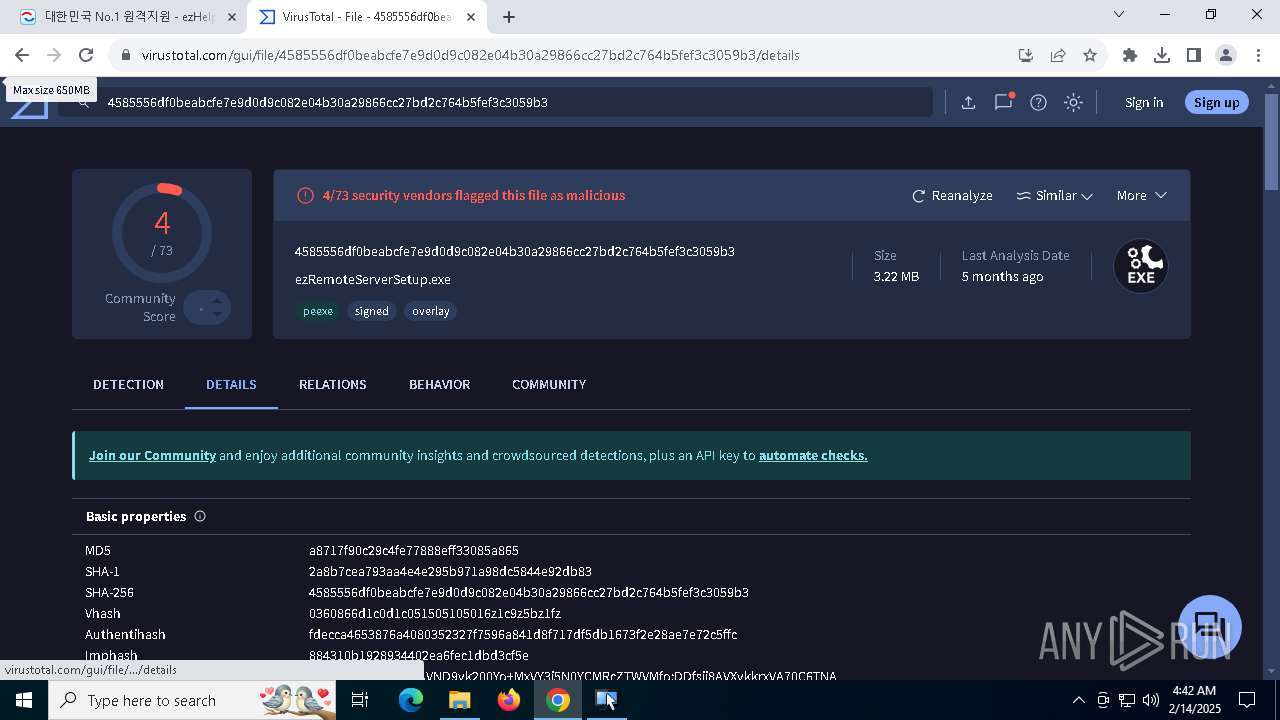
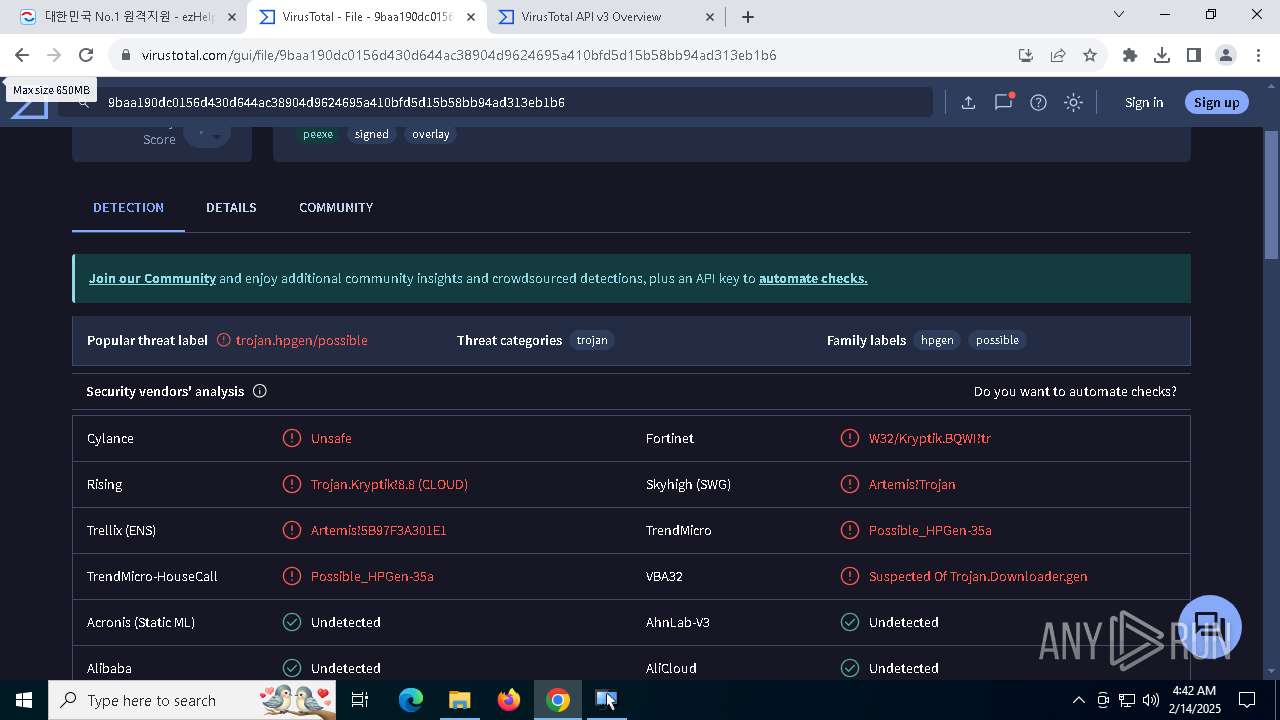
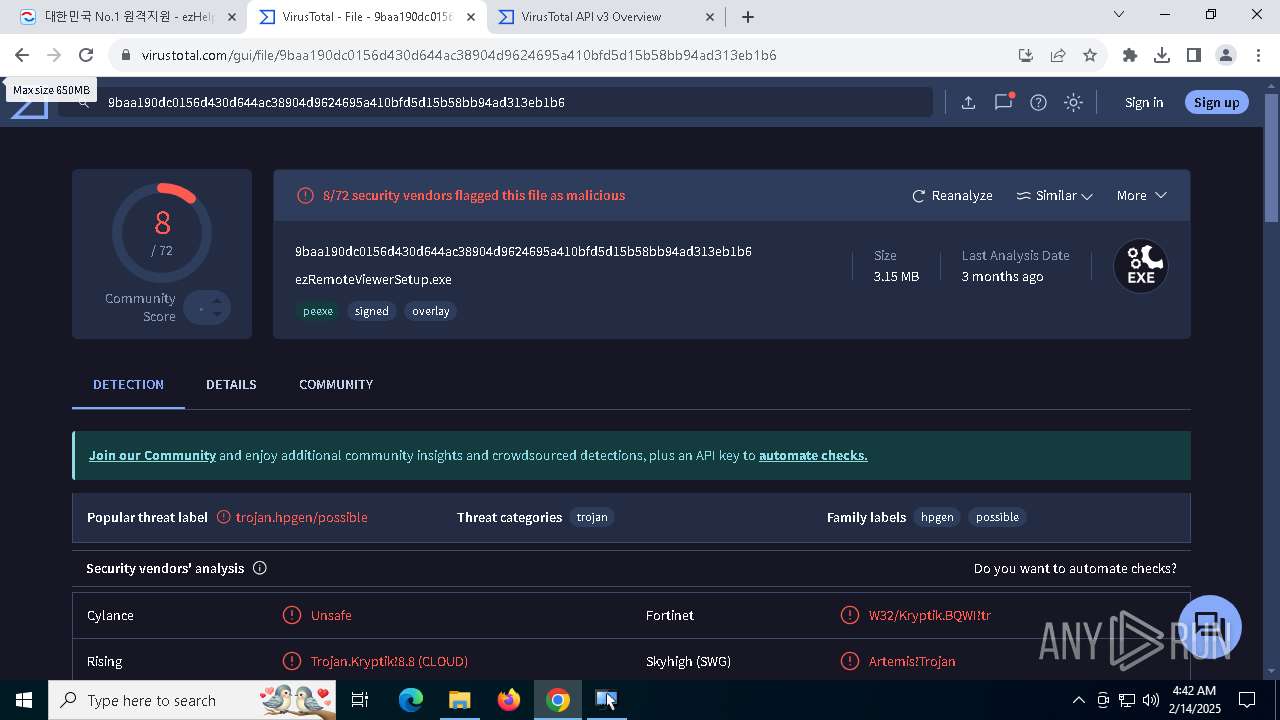
| Verdict: | Malicious activity |
| Analysis date: | February 14, 2025, 04:37:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
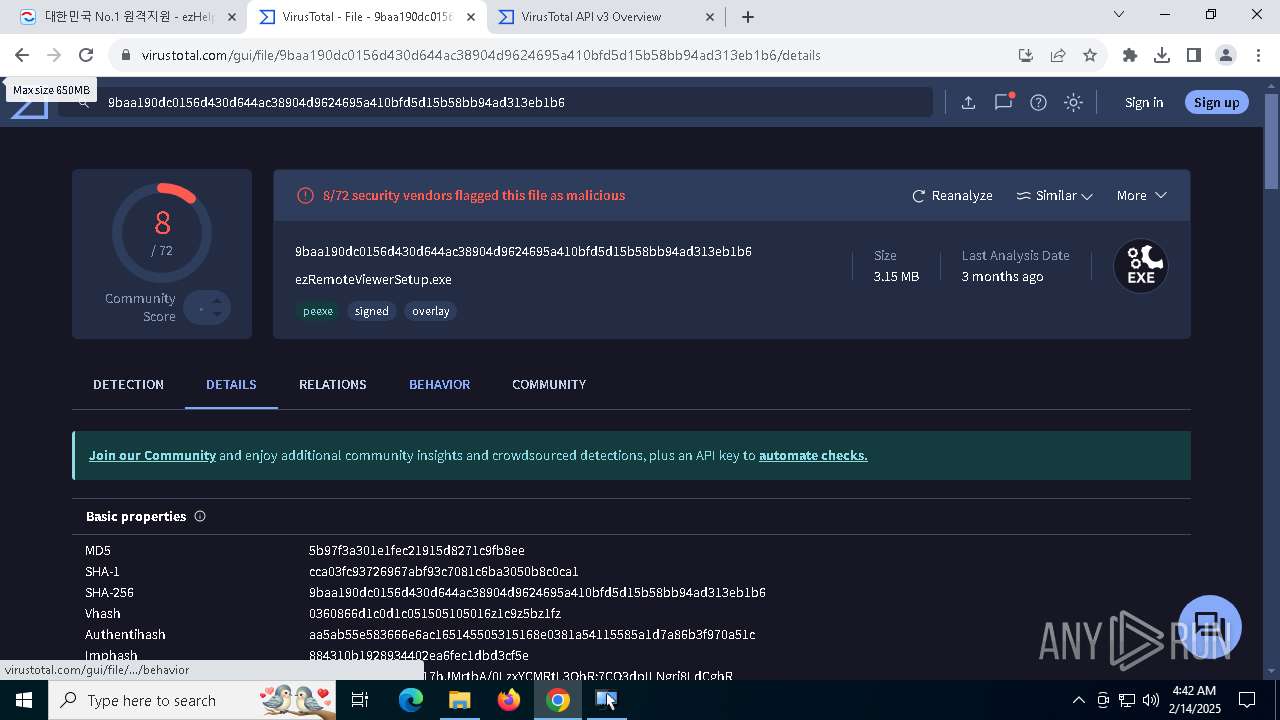
| MD5: | 123A87393A9E7E6E2D9D65F3308811B5 |
| SHA1: | 816F00E078BA66647ED25B1DF0AEBE9966308E85 |
| SHA256: | DBFED723CCC3FA928EBAF3C21A254805B520F333969E6CEFF505E936393E9349 |
| SSDEEP: | 3:N8DSL5VZ6aShKZk6hn:2OL5VZn5 |
MALICIOUS
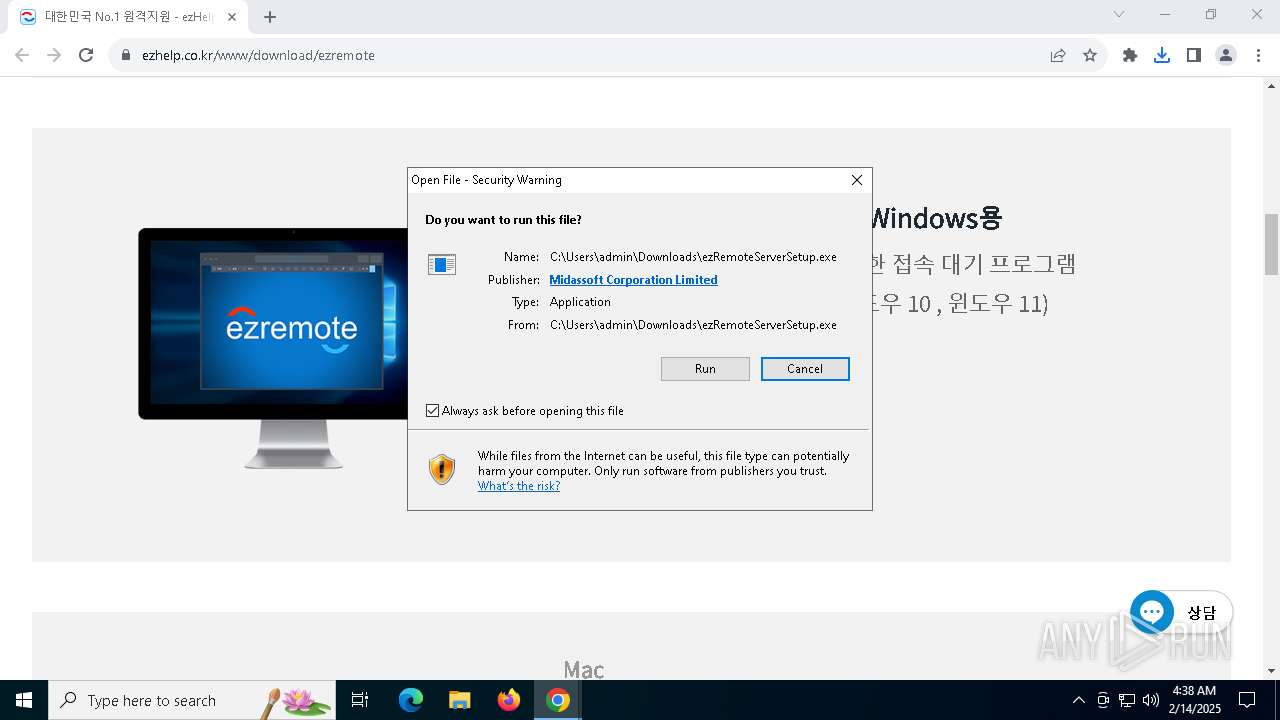
Executing a file with an untrusted certificate
- InstallDriver.exe (PID: 6084)
- ServiceControl.exe (PID: 7096)
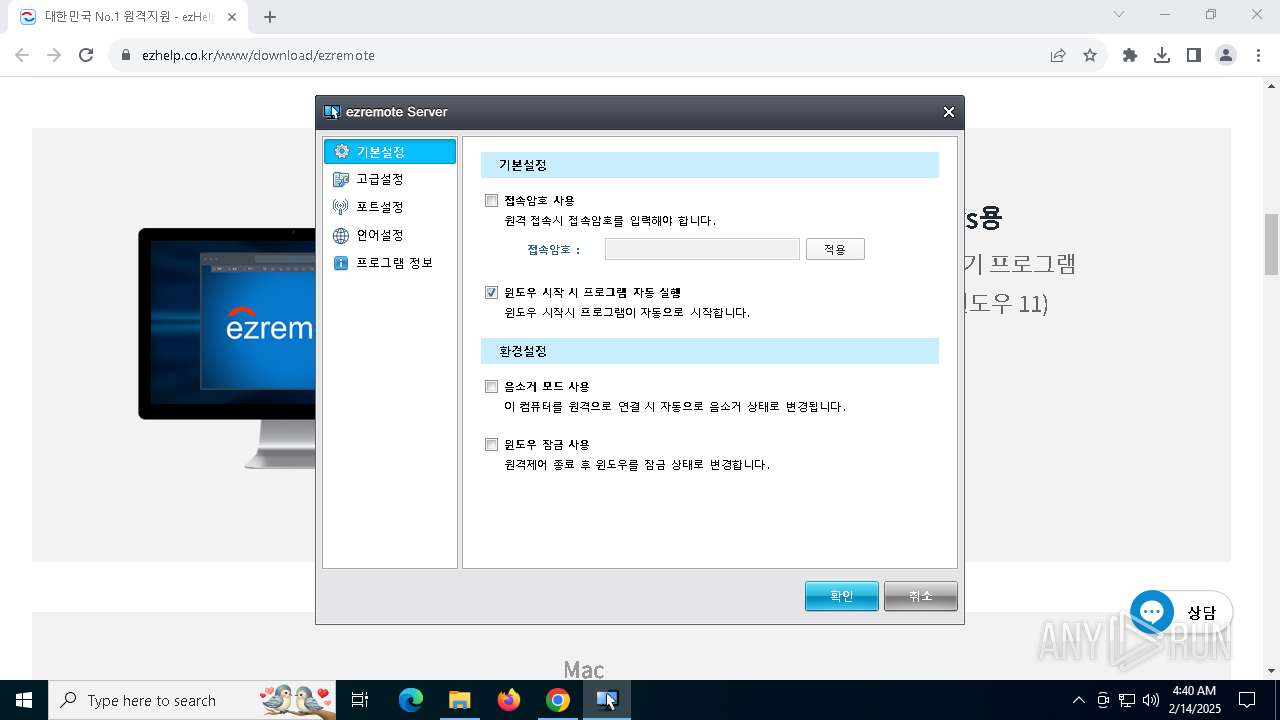
Changes the autorun value in the registry
- ezRemoteServer.exe (PID: 2008)
SUSPICIOUS
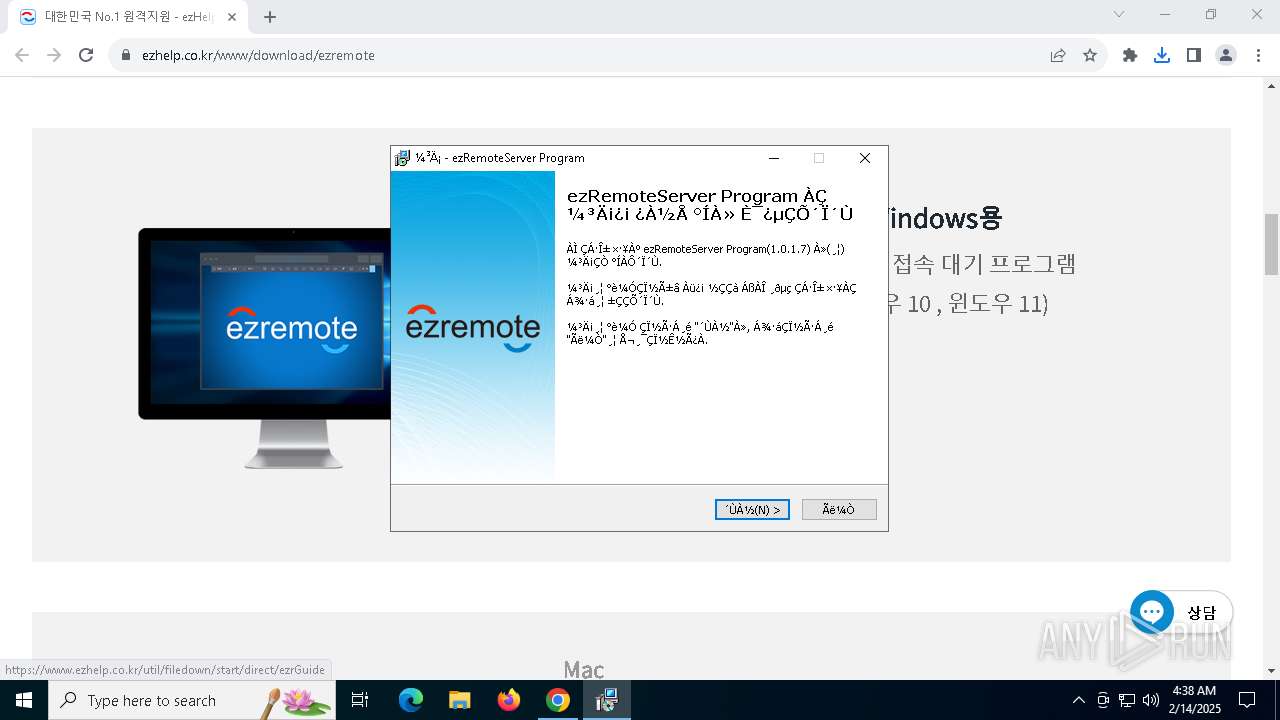
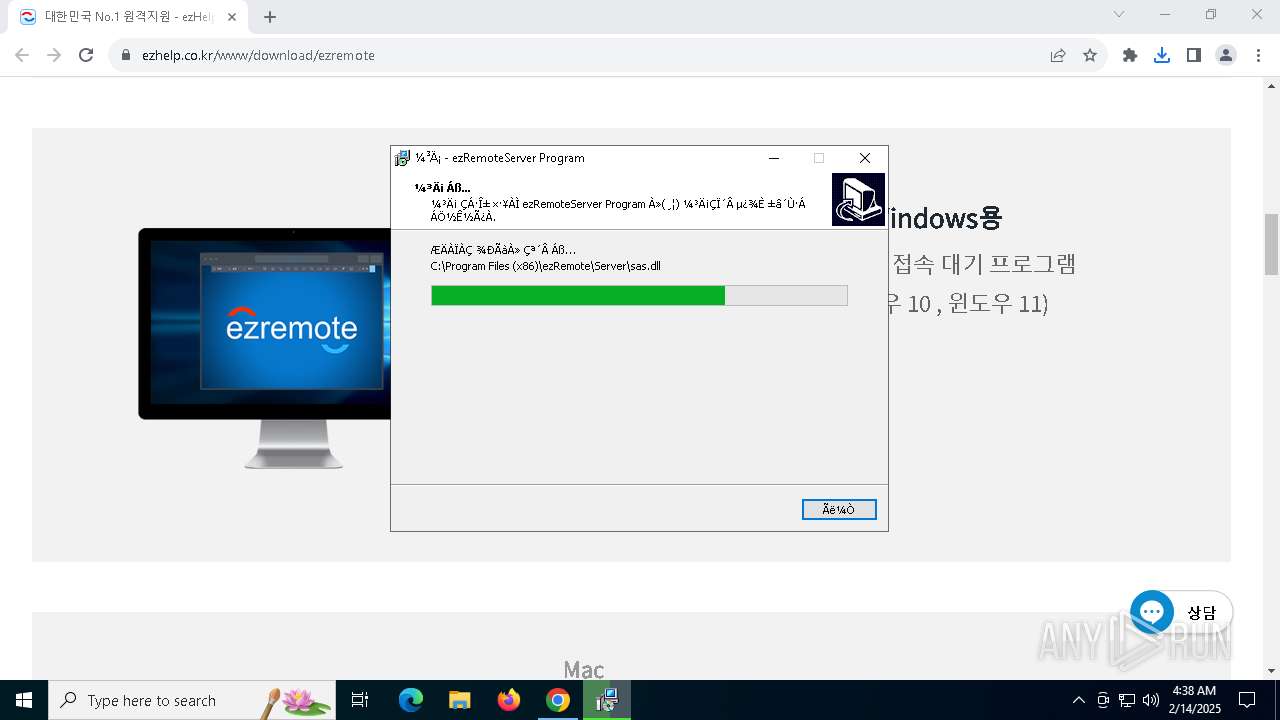
Executable content was dropped or overwritten
- ezRemoteServerSetup.exe (PID: 7020)
- ezRemoteServerSetup.exe (PID: 5980)
- ezRemoteServerSetup.tmp (PID: 5972)
- ezRemoteServerLauncher.exe (PID: 1988)
- InstallDriver.exe (PID: 6084)
- drvinst.exe (PID: 5040)
- drvinst.exe (PID: 5404)
Reads security settings of Internet Explorer
- ezRemoteServerSetup.tmp (PID: 7040)
- ezRemoteServerSetup.tmp (PID: 5972)
- ezRemoteServerUpdater.exe (PID: 6996)
- ezRemoteServerLauncher.exe (PID: 5640)
- InstallDriver.exe (PID: 6084)
- ezRemoteServer.exe (PID: 7136)
Reads the Windows owner or organization settings
- ezRemoteServerSetup.tmp (PID: 5972)
Process drops legitimate windows executable
- ezRemoteServerSetup.tmp (PID: 5972)
Checks Windows Trust Settings
- ezRemoteServerUpdater.exe (PID: 6996)
- InstallDriver.exe (PID: 6084)
- drvinst.exe (PID: 5040)
Application launched itself
- ezRemoteServerLauncher.exe (PID: 5640)
- ezRemoteServer.exe (PID: 7136)
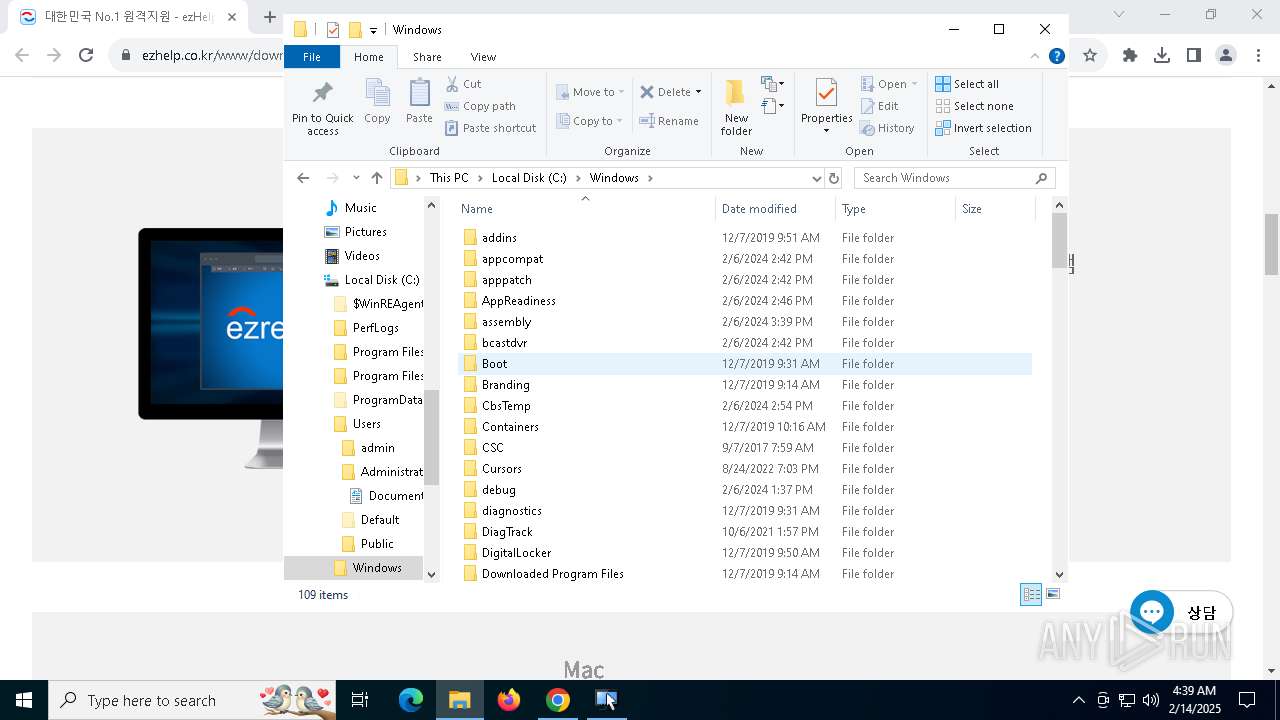
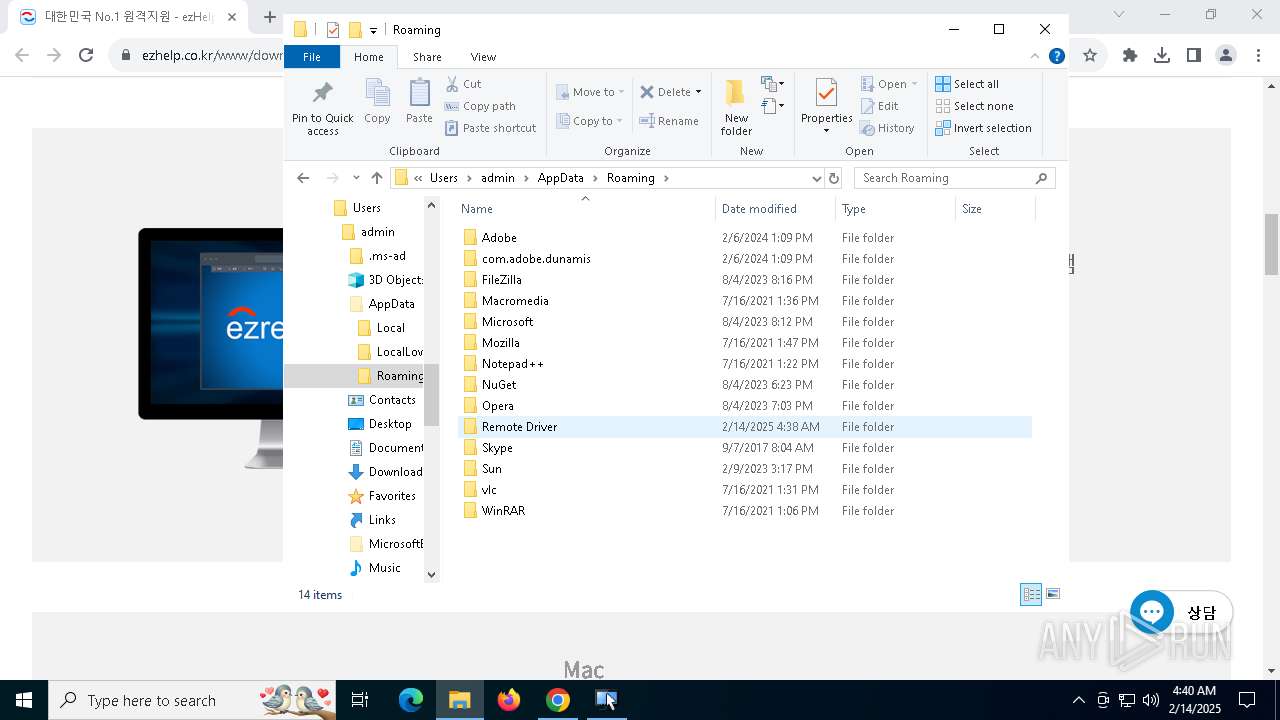
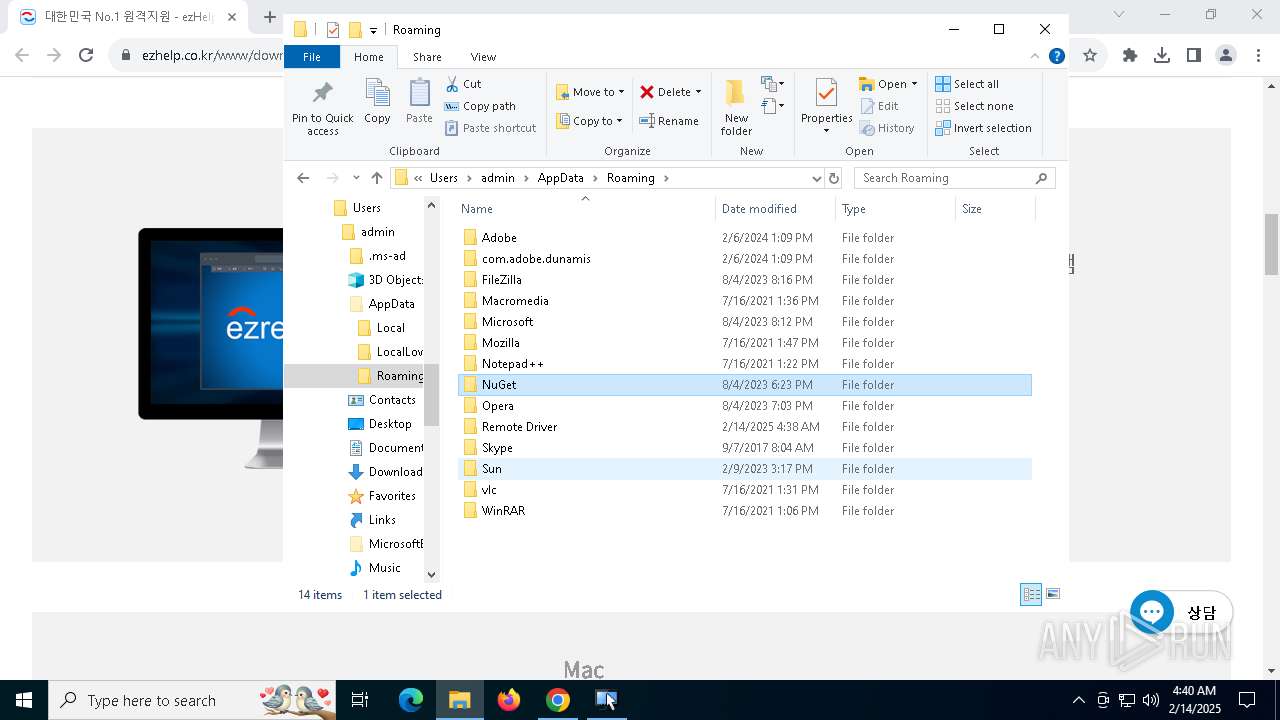
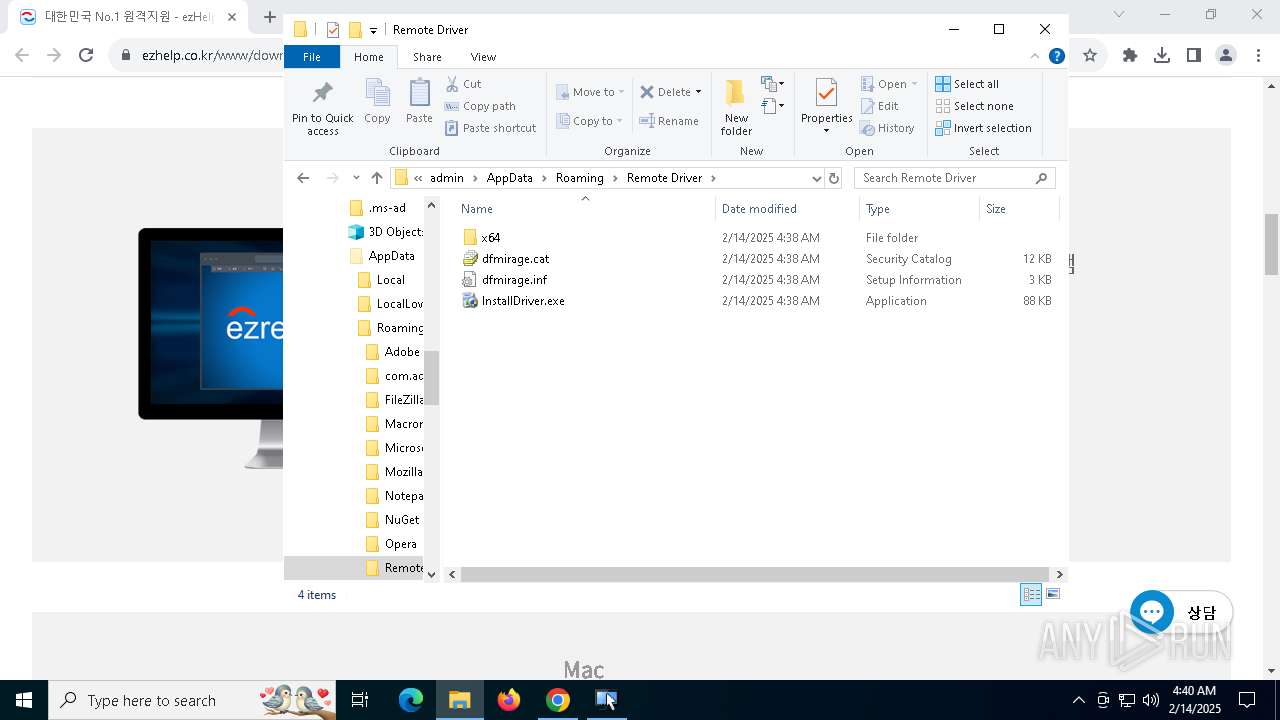
Drops a system driver (possible attempt to evade defenses)
- drvinst.exe (PID: 5040)
- InstallDriver.exe (PID: 6084)
- ezRemoteServerLauncher.exe (PID: 1988)
- drvinst.exe (PID: 5404)
Creates files in the driver directory
- drvinst.exe (PID: 5040)
- drvinst.exe (PID: 5404)
Creates or modifies Windows services
- drvinst.exe (PID: 5404)
Executes as Windows Service
- ezRemoteServer.exe (PID: 4864)
There is functionality for taking screenshot (YARA)
- ezRemoteServer.exe (PID: 4864)
- ezRemoteServer.exe (PID: 1412)
Connects to unusual port
- ezRemoteServerUpdater.exe (PID: 6996)
INFO
Application launched itself
- chrome.exe (PID: 3812)
Checks supported languages
- ezRemoteServerSetup.exe (PID: 7020)
- ezRemoteServerSetup.tmp (PID: 7040)
- ezRemoteServerSetup.exe (PID: 5980)
- ezRemoteServerSetup.tmp (PID: 5972)
- ezRemoteServerUpdater.exe (PID: 6996)
- ezRemoteServerLauncher.exe (PID: 5640)
- ezRemoteServerLauncher.exe (PID: 1988)
- ezRemoteServer.exe (PID: 2008)
- InstallDriver.exe (PID: 6084)
- drvinst.exe (PID: 5040)
- drvinst.exe (PID: 5404)
- ezRemoteServer.exe (PID: 7136)
- ServiceControl.exe (PID: 7096)
- ezRemoteServer.exe (PID: 4864)
- ezRemoteServer.exe (PID: 1412)
Create files in a temporary directory
- ezRemoteServerSetup.exe (PID: 7020)
- ezRemoteServerSetup.exe (PID: 5980)
- ezRemoteServerSetup.tmp (PID: 5972)
- InstallDriver.exe (PID: 6084)
Executable content was dropped or overwritten
- chrome.exe (PID: 3812)
- chrome.exe (PID: 7004)
Connects to unusual port
- chrome.exe (PID: 6352)
Reads the computer name
- ezRemoteServerSetup.tmp (PID: 7040)
- ezRemoteServerSetup.tmp (PID: 5972)
- ezRemoteServerUpdater.exe (PID: 6996)
- ezRemoteServerLauncher.exe (PID: 5640)
- ezRemoteServerLauncher.exe (PID: 1988)
- InstallDriver.exe (PID: 6084)
- ezRemoteServer.exe (PID: 2008)
- drvinst.exe (PID: 5040)
- drvinst.exe (PID: 5404)
- ezRemoteServer.exe (PID: 7136)
- ServiceControl.exe (PID: 7096)
- ezRemoteServer.exe (PID: 4864)
- ezRemoteServer.exe (PID: 1412)
Process checks computer location settings
- ezRemoteServerSetup.tmp (PID: 7040)
- ezRemoteServerSetup.tmp (PID: 5972)
- ezRemoteServerUpdater.exe (PID: 6996)
- ezRemoteServerLauncher.exe (PID: 5640)
- ezRemoteServer.exe (PID: 7136)
The sample compiled with english language support
- ezRemoteServerSetup.tmp (PID: 5972)
- chrome.exe (PID: 7004)
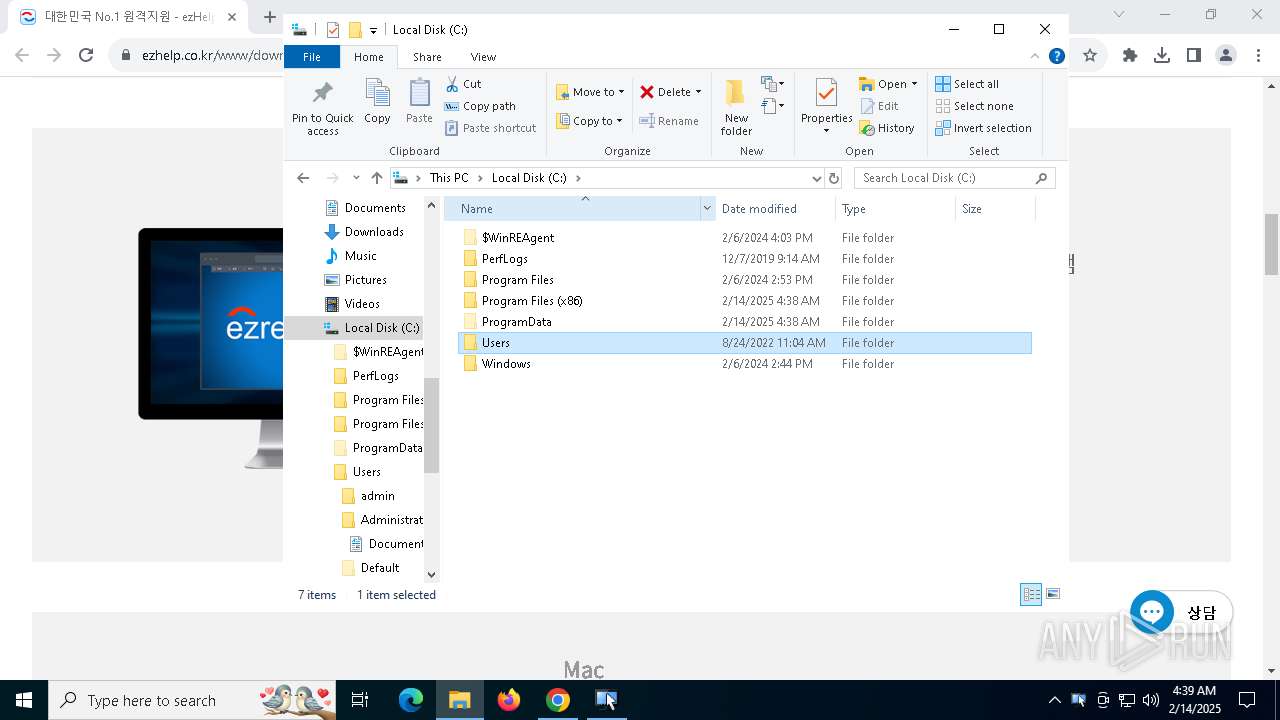
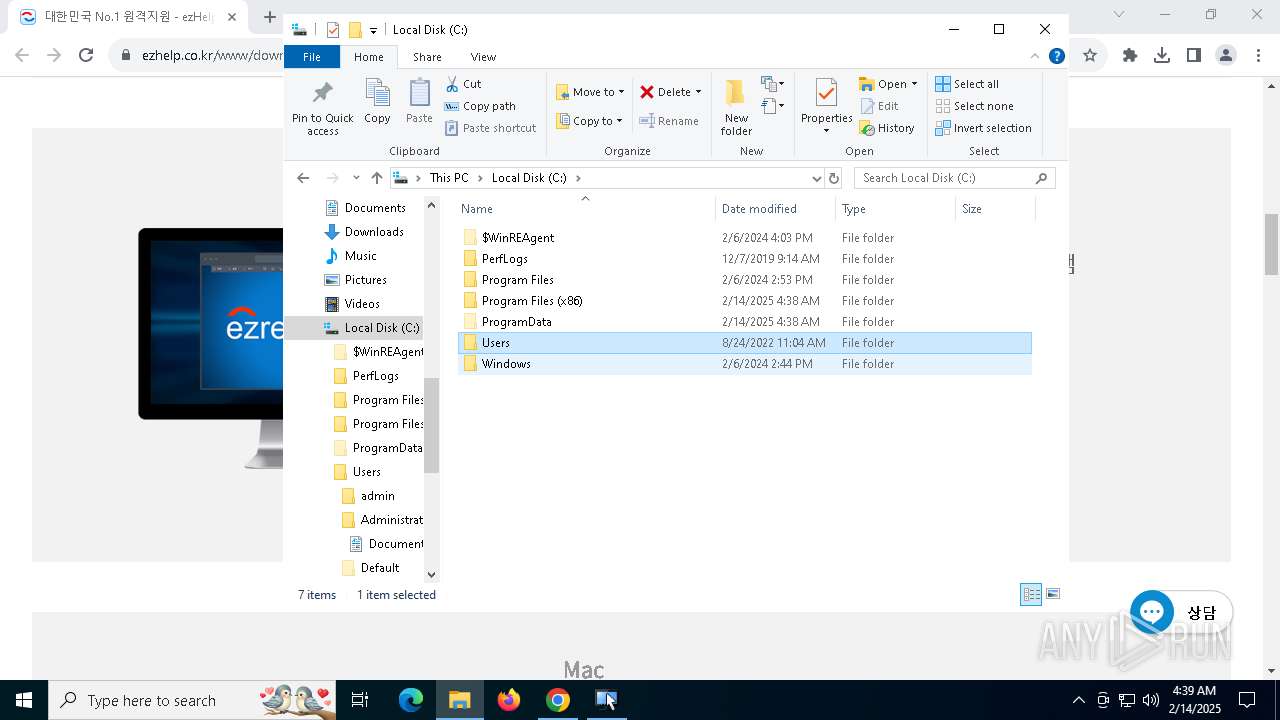
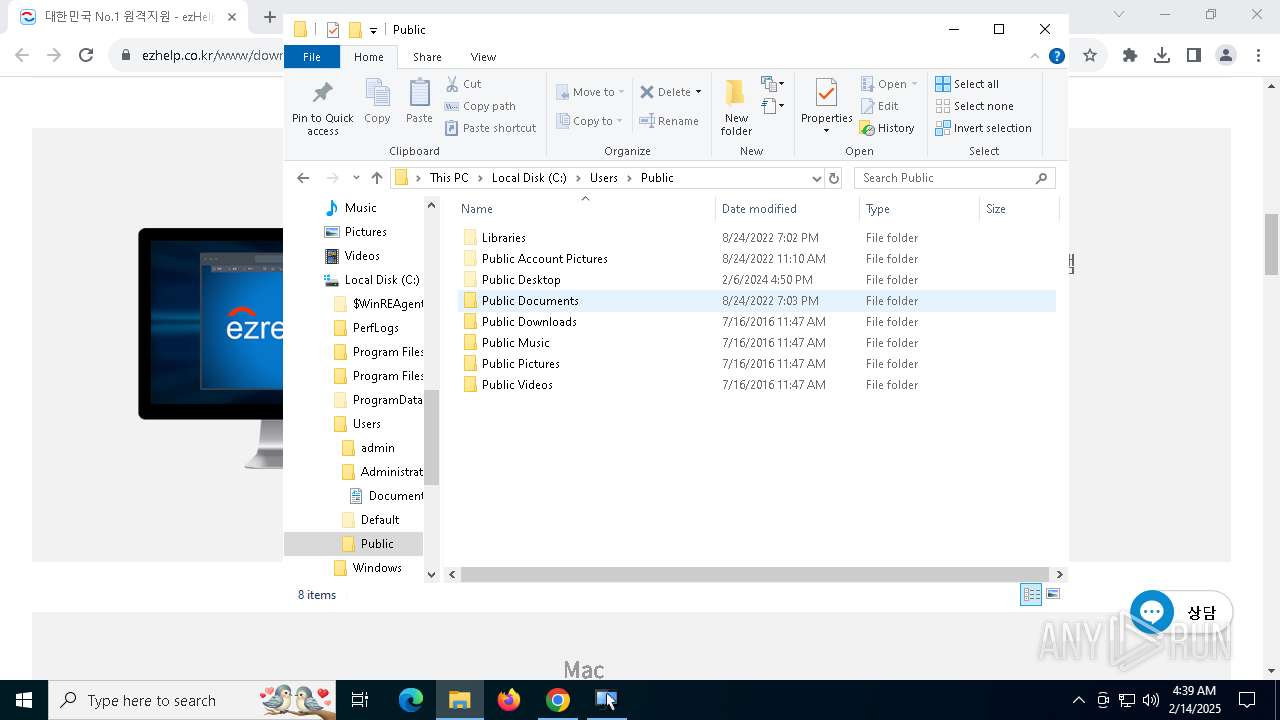
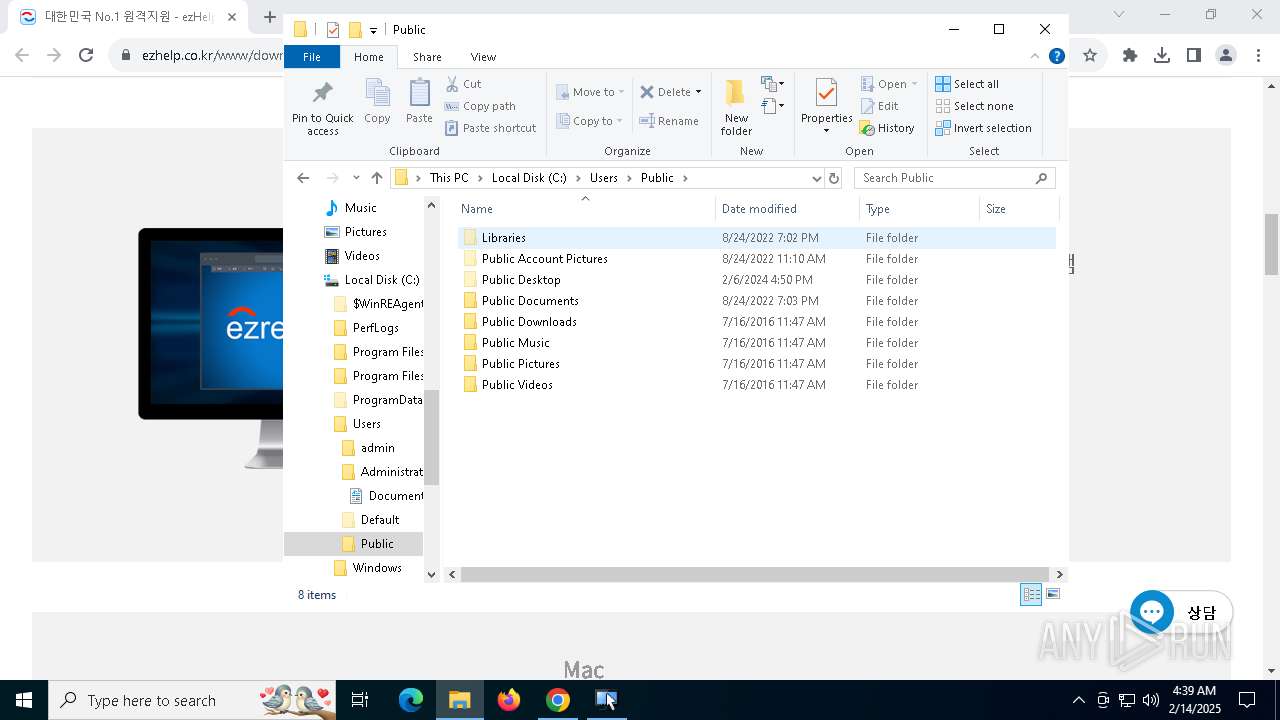
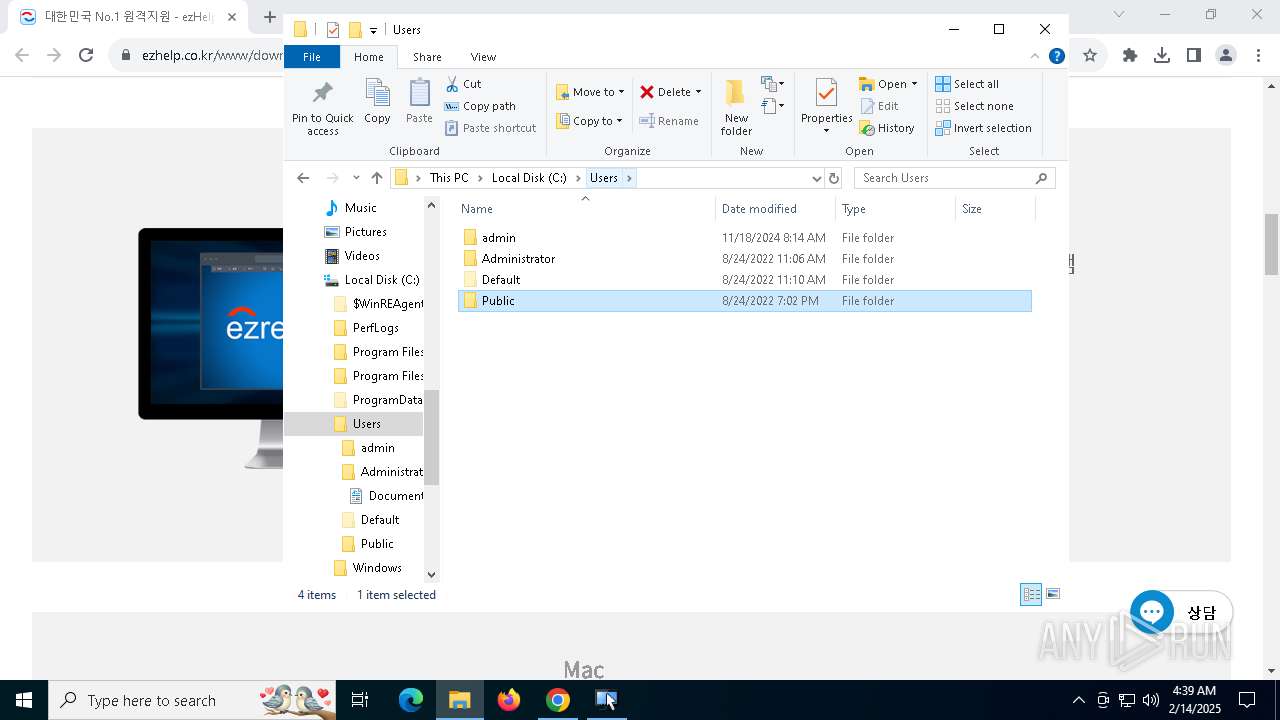
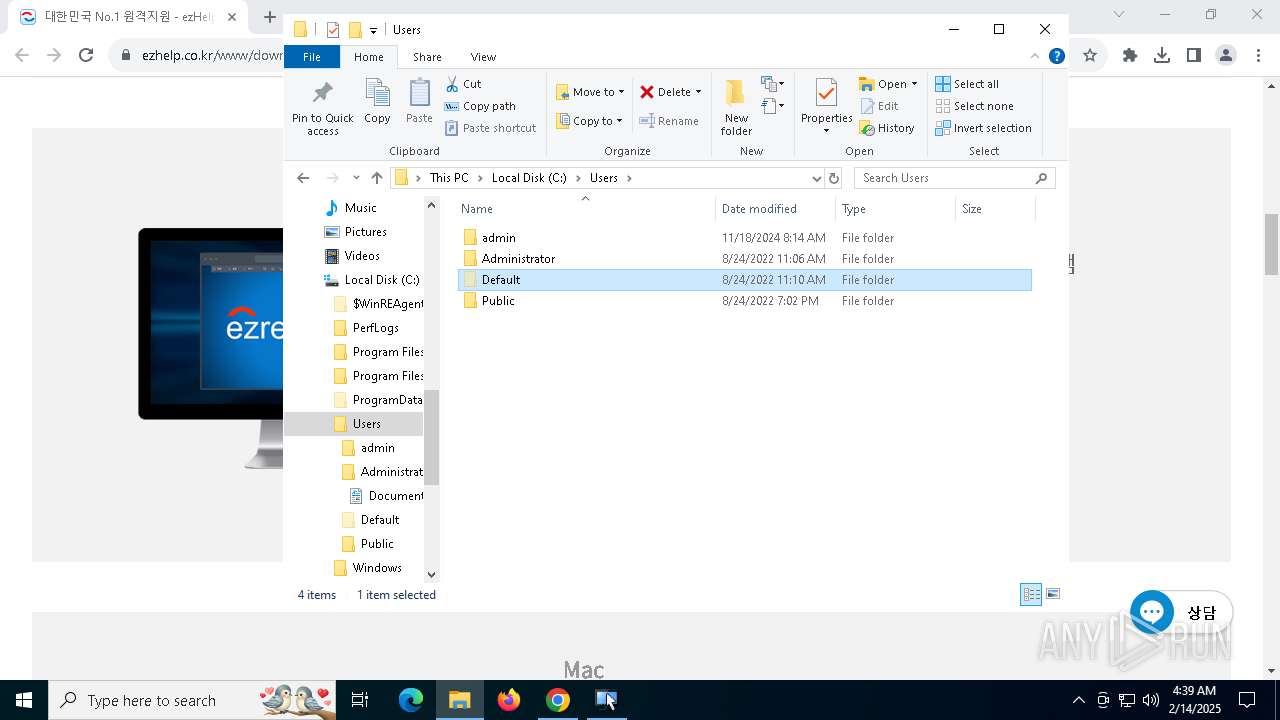
Creates files in the program directory
- ezRemoteServerSetup.tmp (PID: 5972)
- ezRemoteServerLauncher.exe (PID: 1988)
- ezRemoteServer.exe (PID: 2008)
- ezRemoteServer.exe (PID: 7136)
- ezRemoteServer.exe (PID: 4864)
Reads the machine GUID from the registry
- ezRemoteServerUpdater.exe (PID: 6996)
- InstallDriver.exe (PID: 6084)
- drvinst.exe (PID: 5040)
- ezRemoteServerLauncher.exe (PID: 1988)
The sample compiled with korean language support
- ezRemoteServerSetup.tmp (PID: 5972)
- ezRemoteServerLauncher.exe (PID: 1988)
Creates a software uninstall entry
- ezRemoteServerSetup.tmp (PID: 5972)
Reads the software policy settings
- ezRemoteServerUpdater.exe (PID: 6996)
- InstallDriver.exe (PID: 6084)
- drvinst.exe (PID: 5040)
Checks proxy server information
- ezRemoteServerUpdater.exe (PID: 6996)
Process checks whether UAC notifications are on
- ezRemoteServerLauncher.exe (PID: 1988)
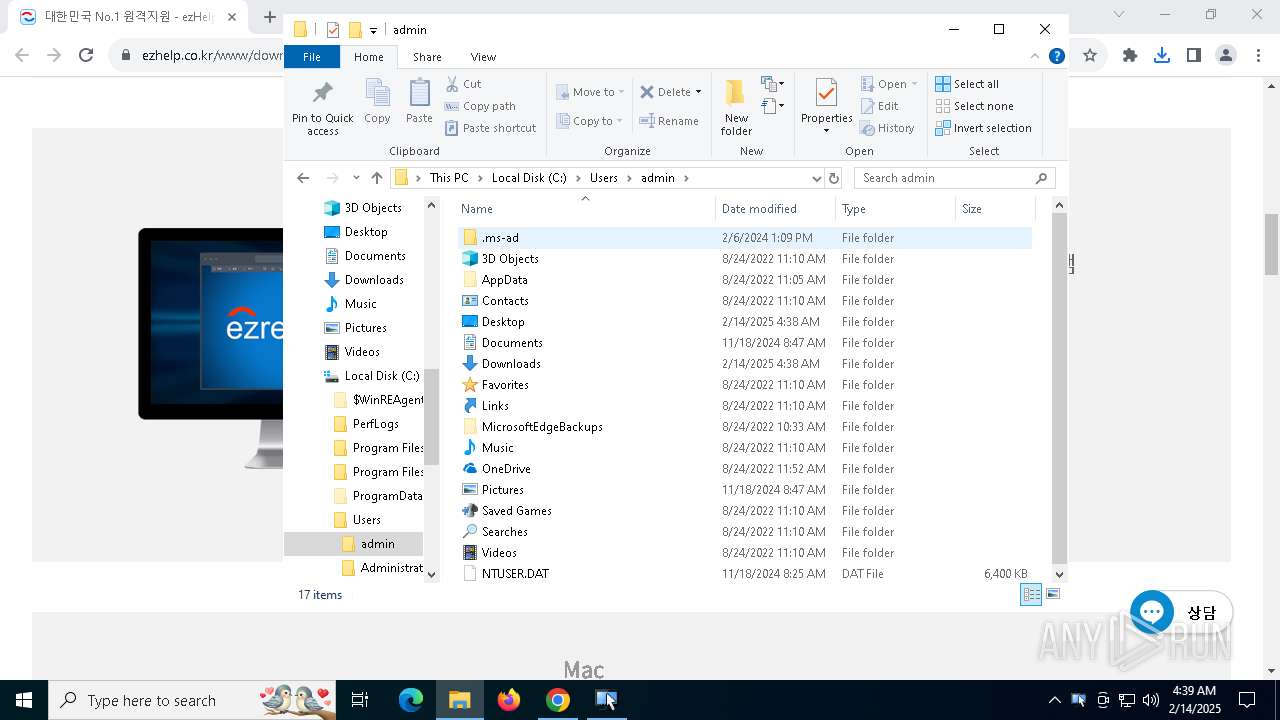
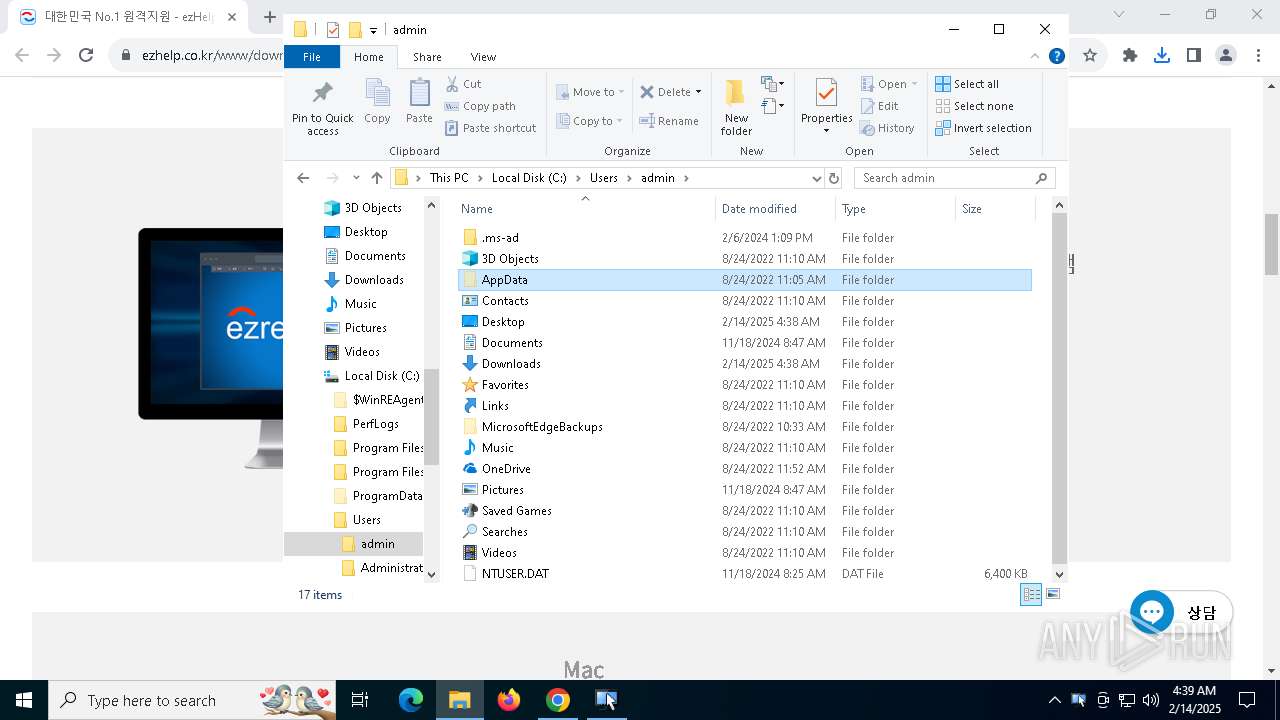
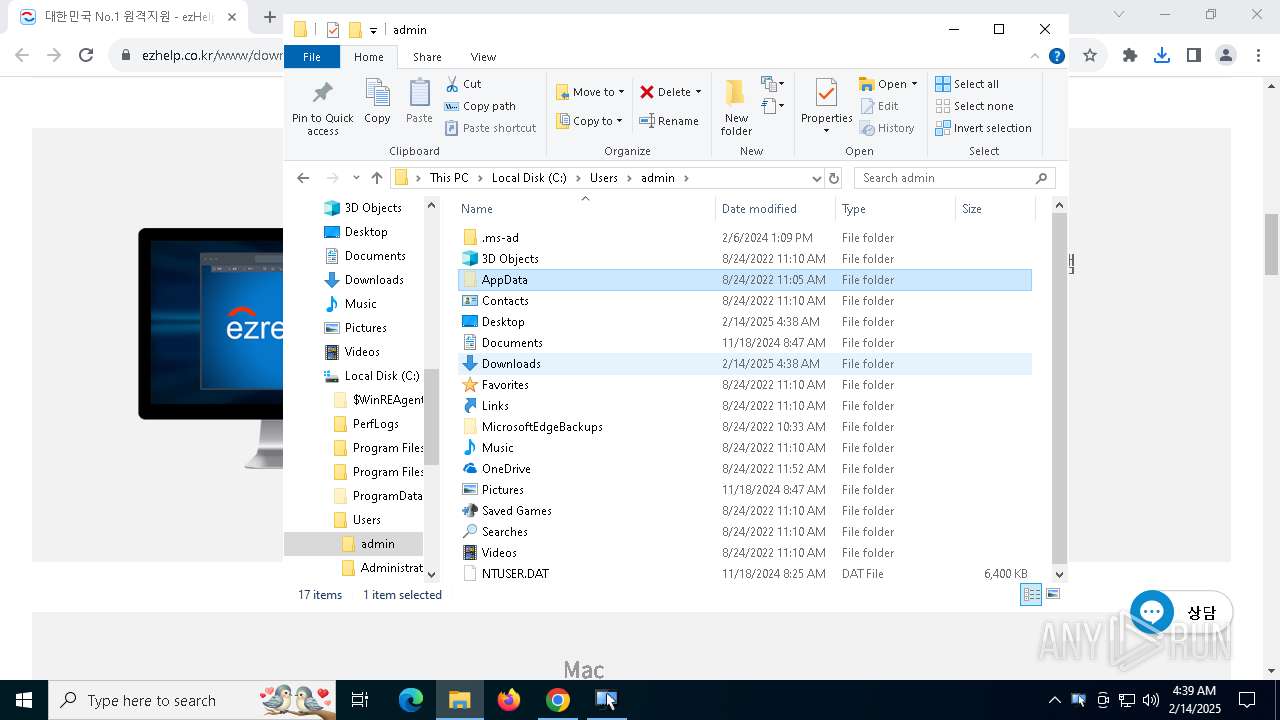
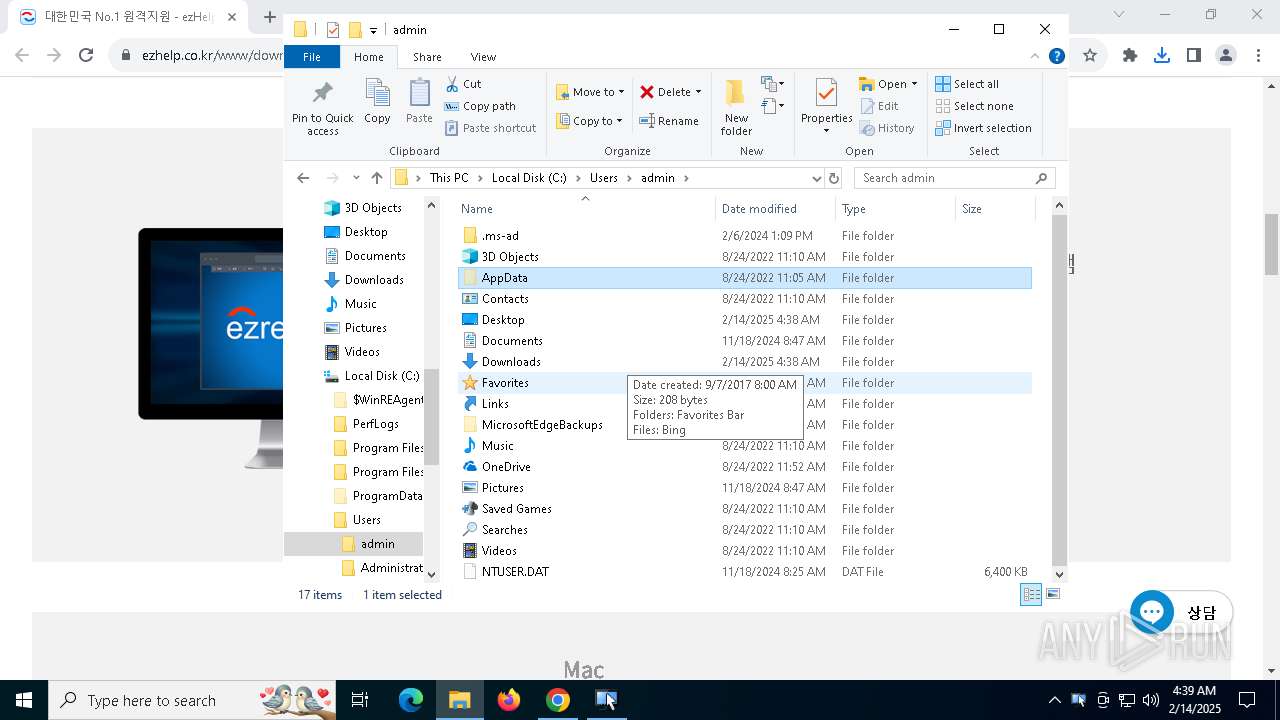
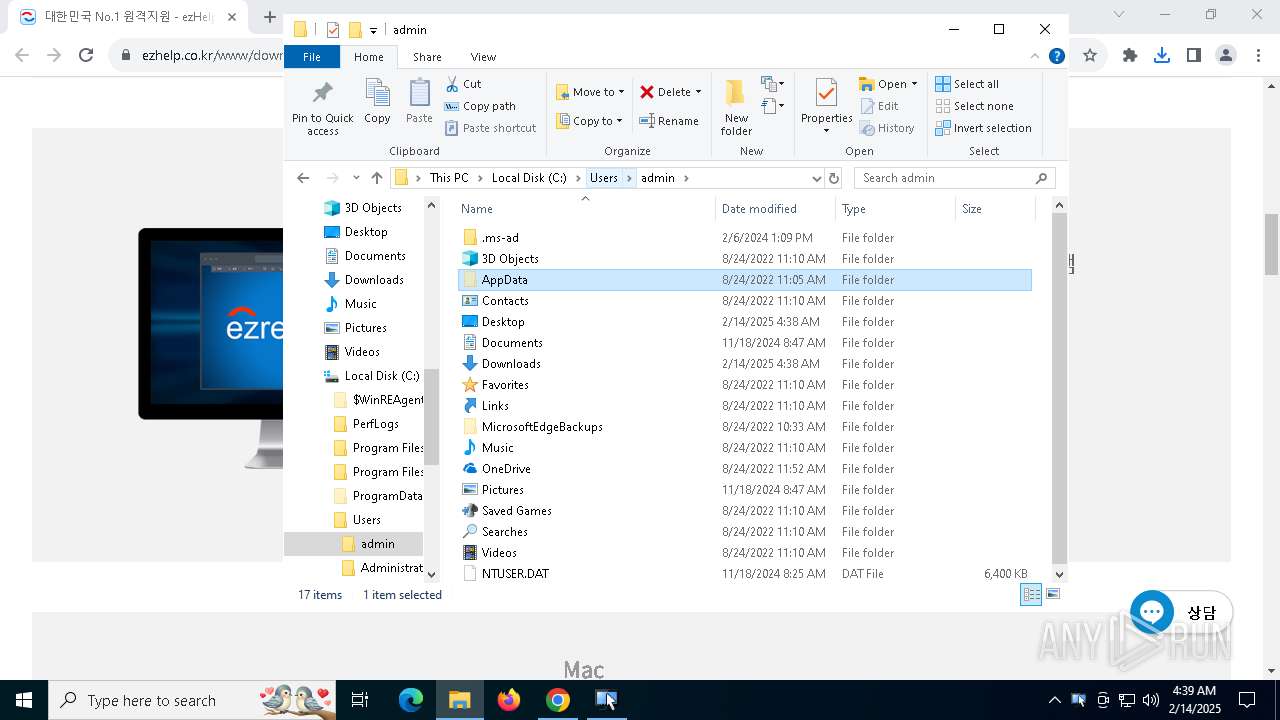
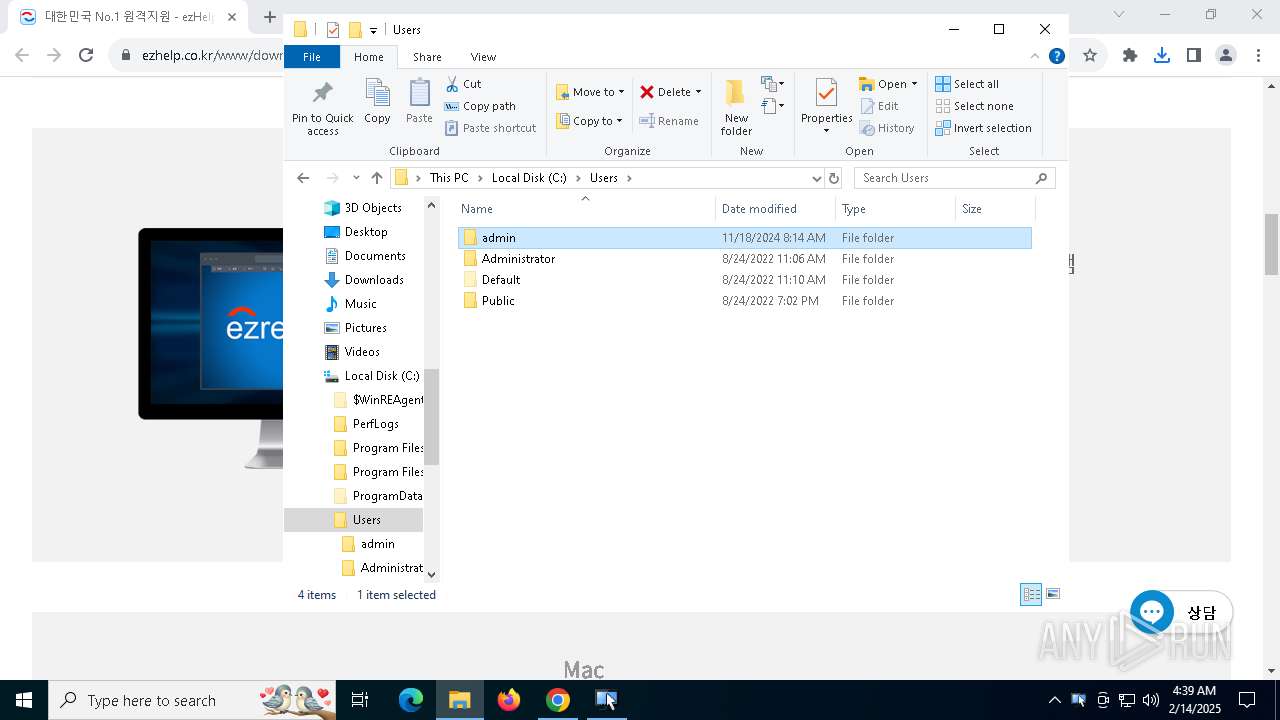
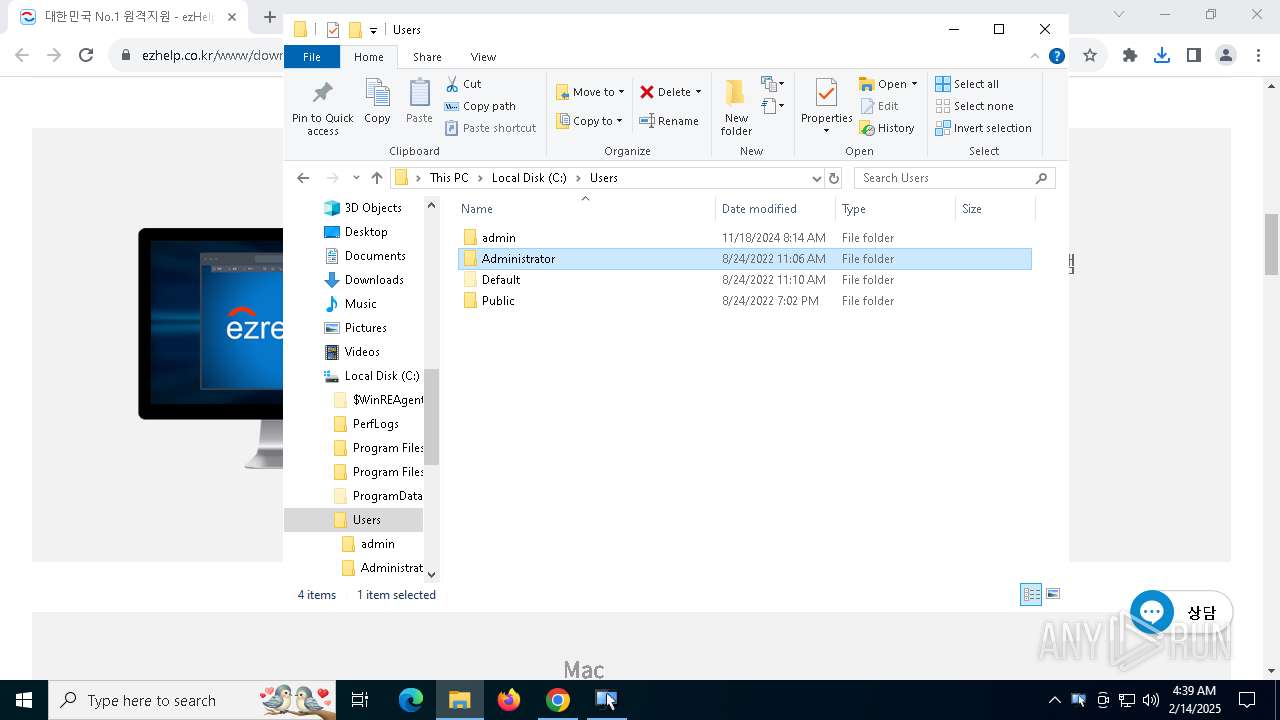
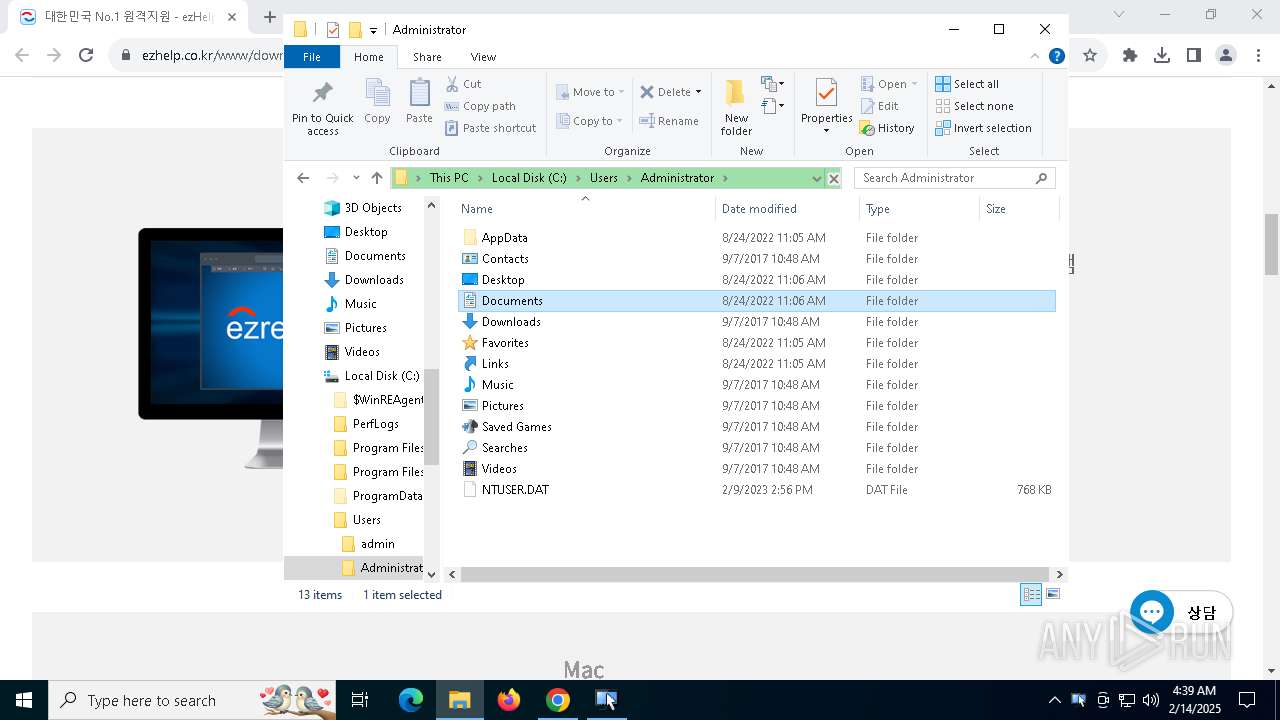
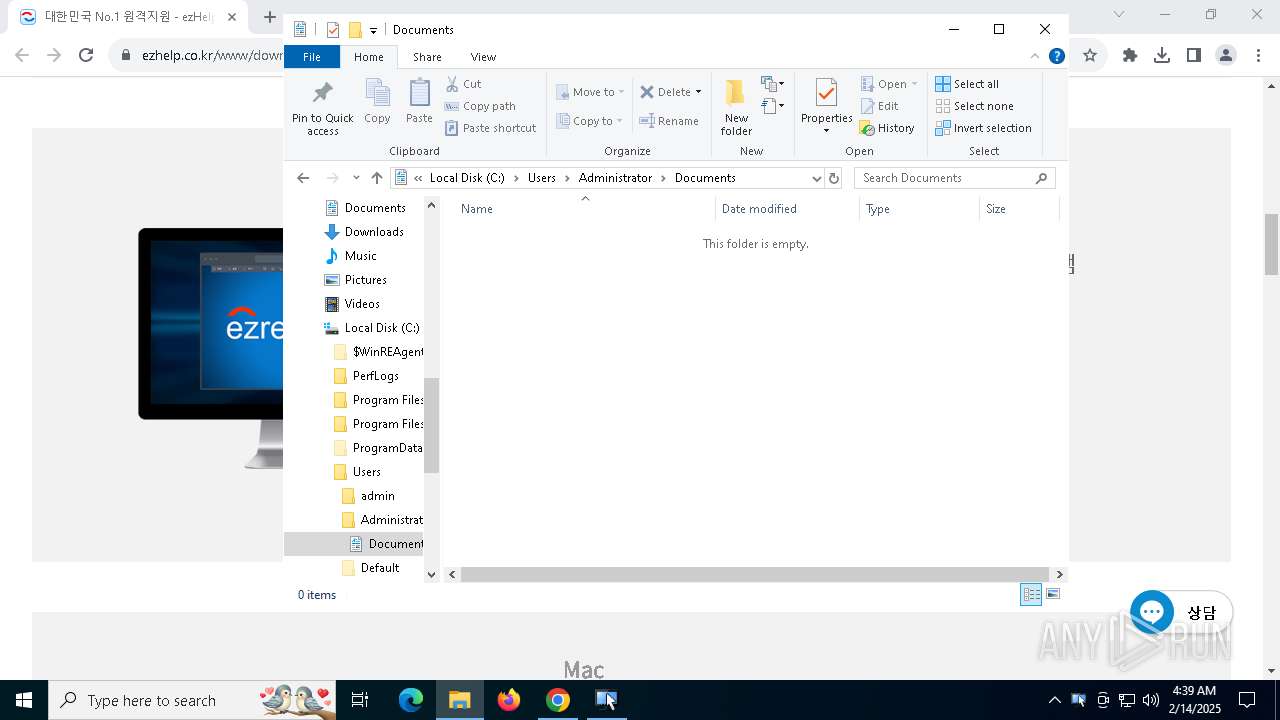
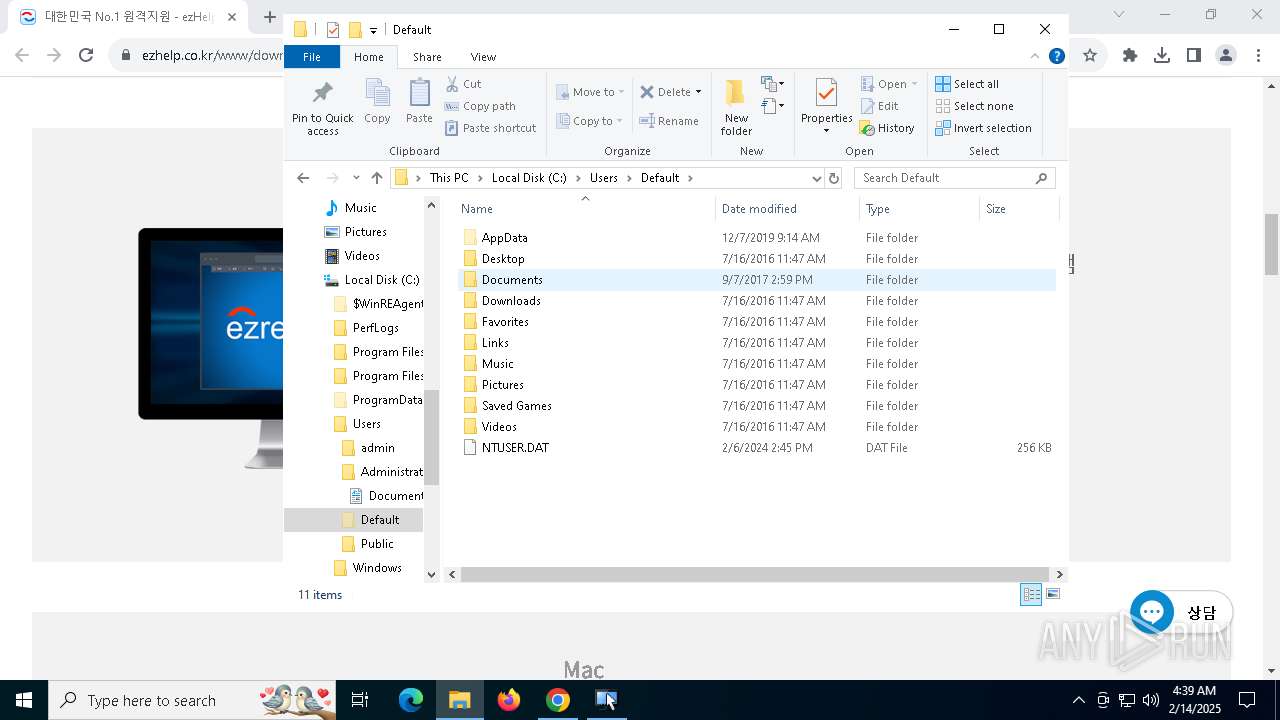
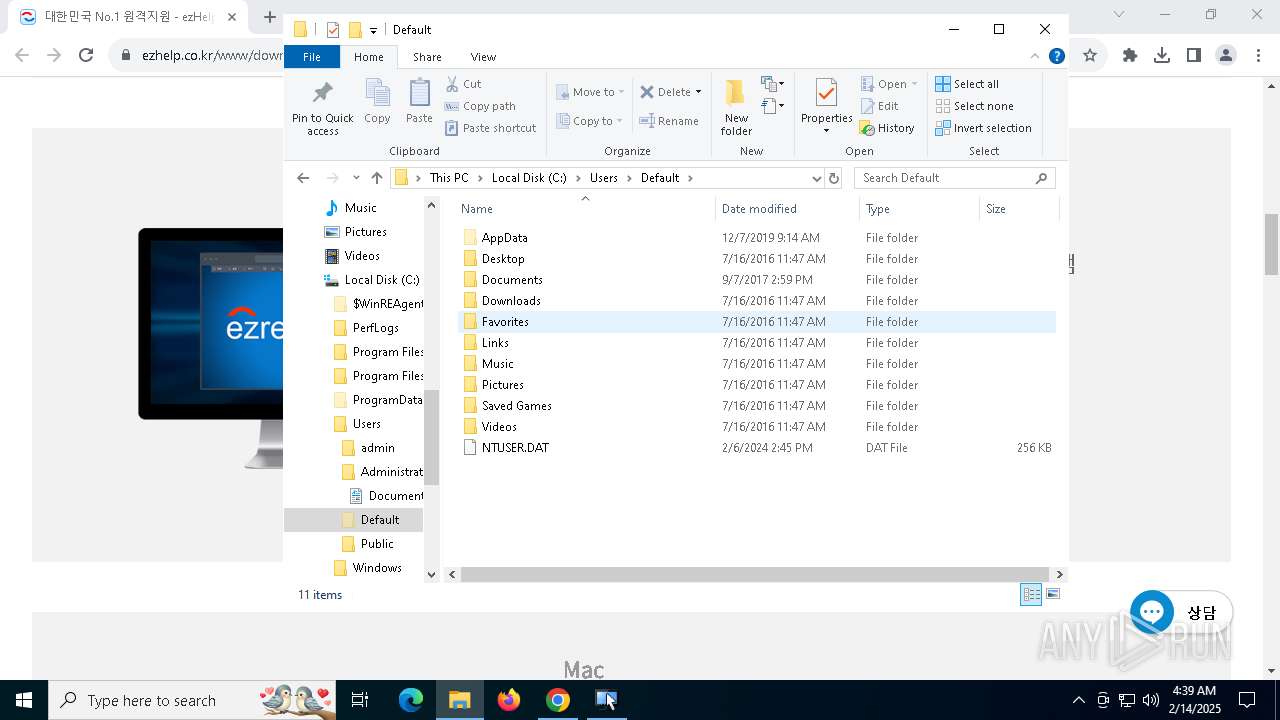
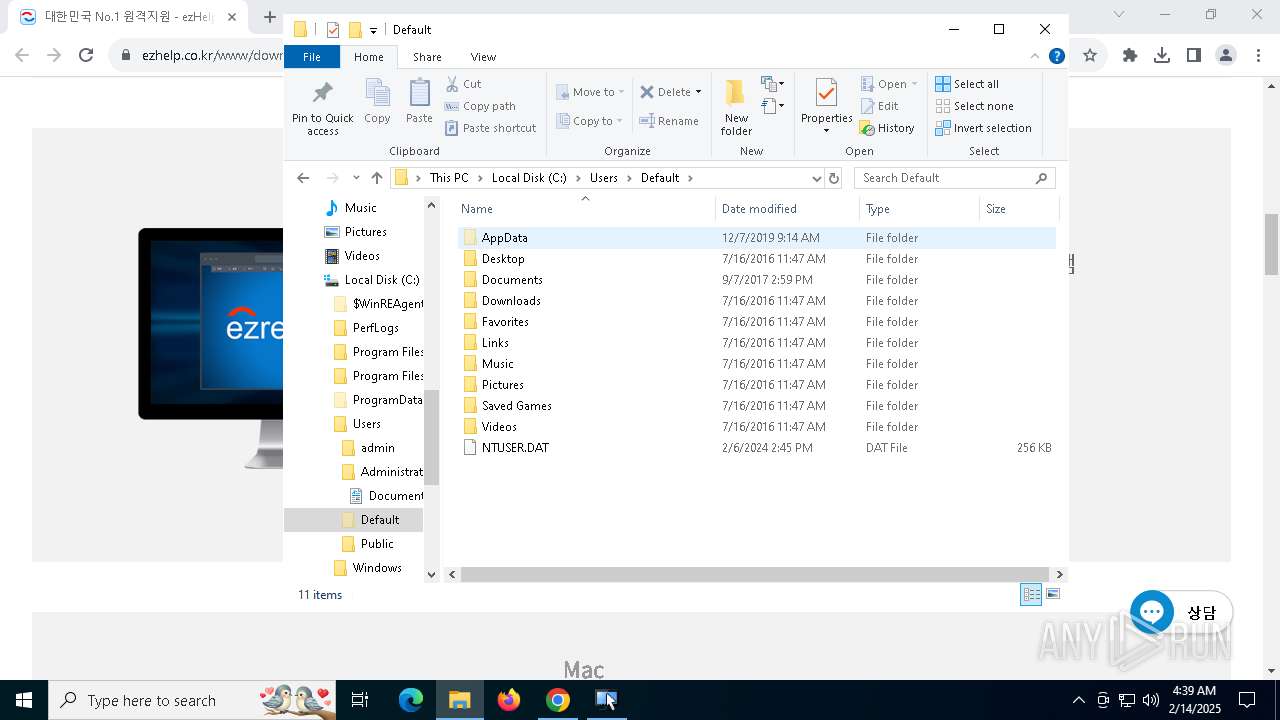
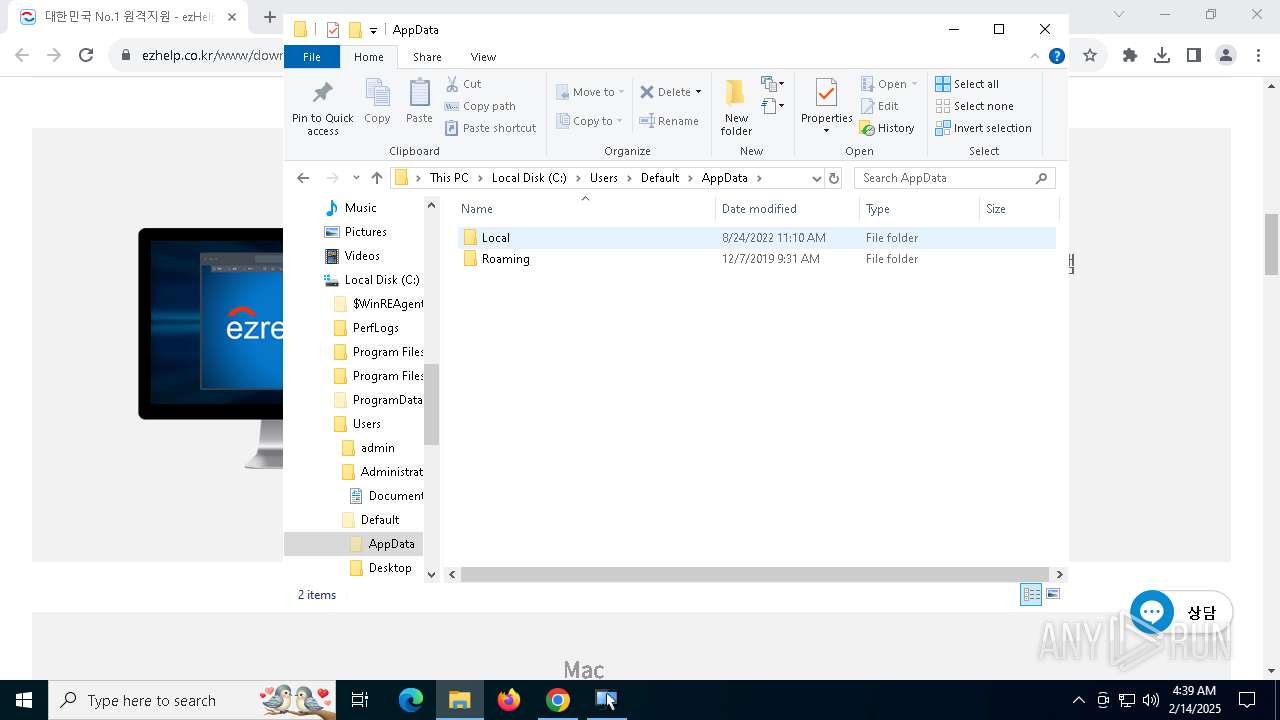
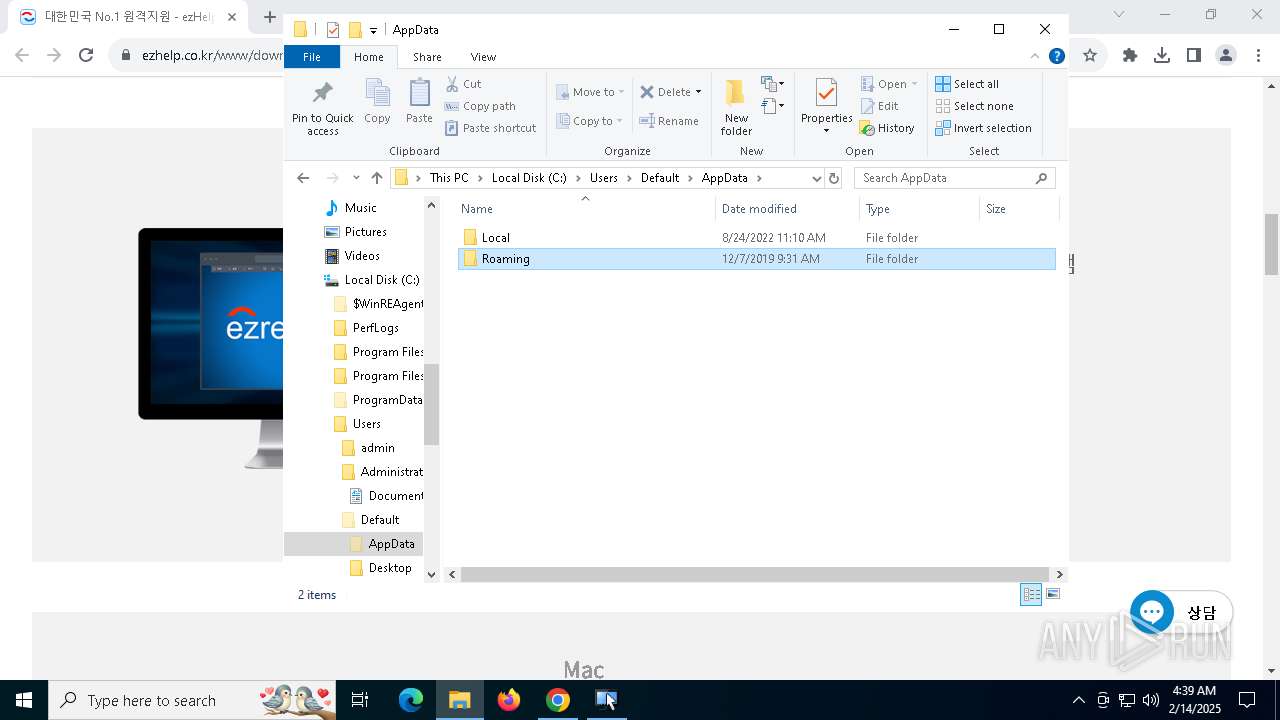
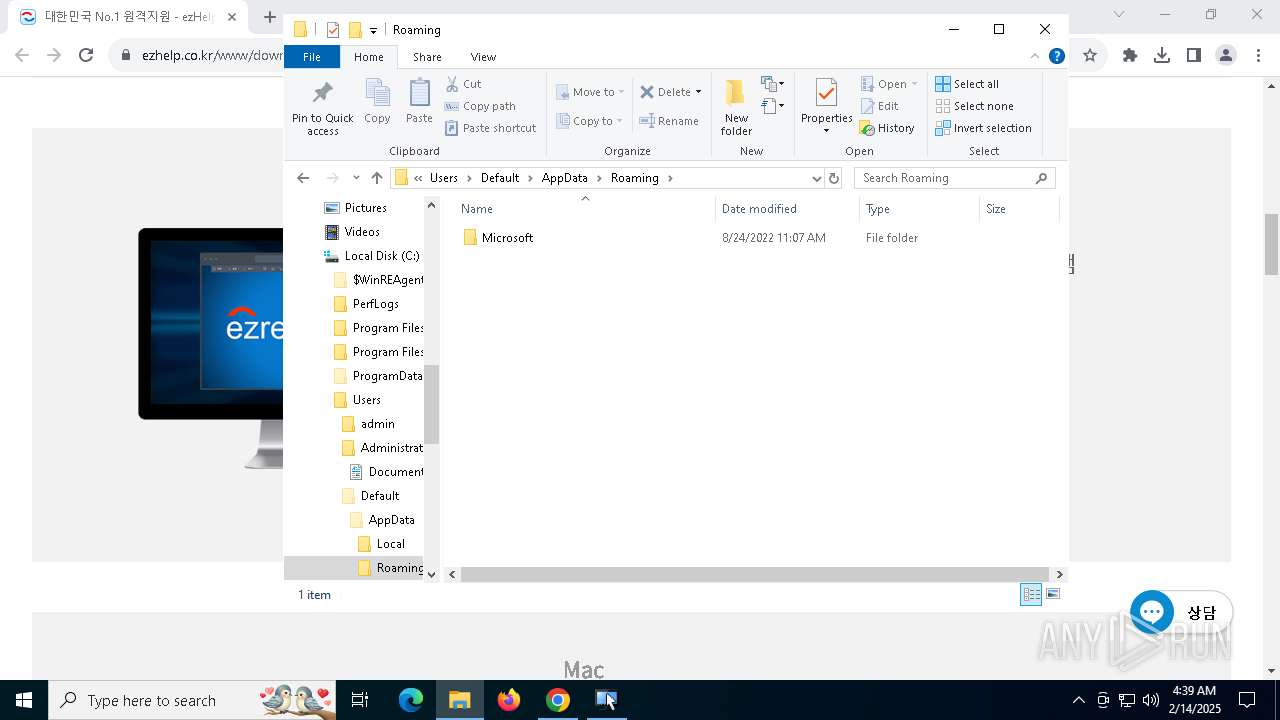
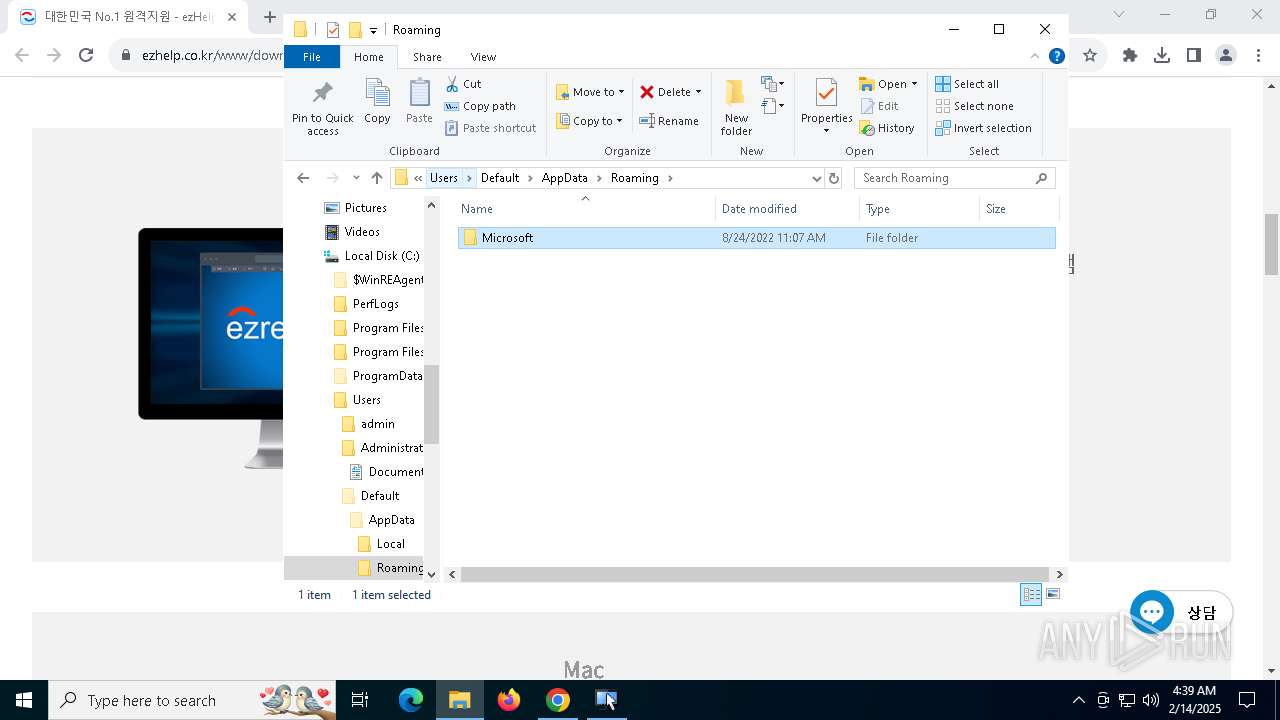
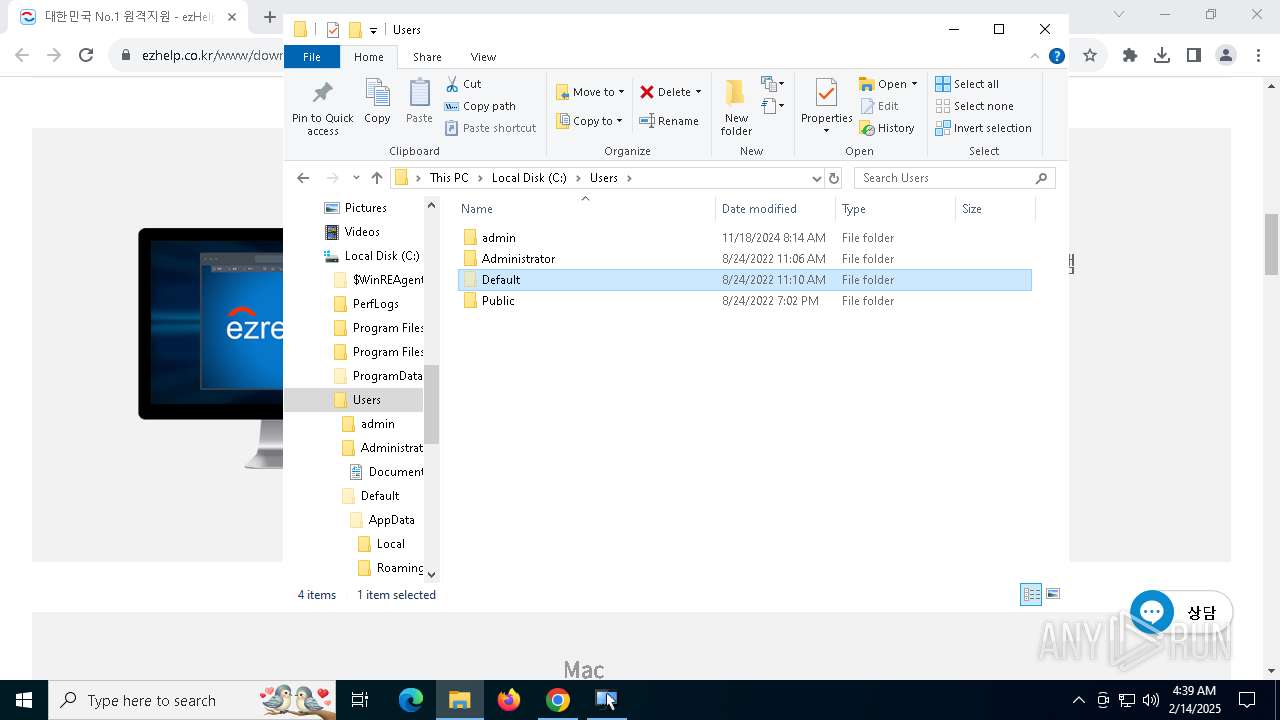
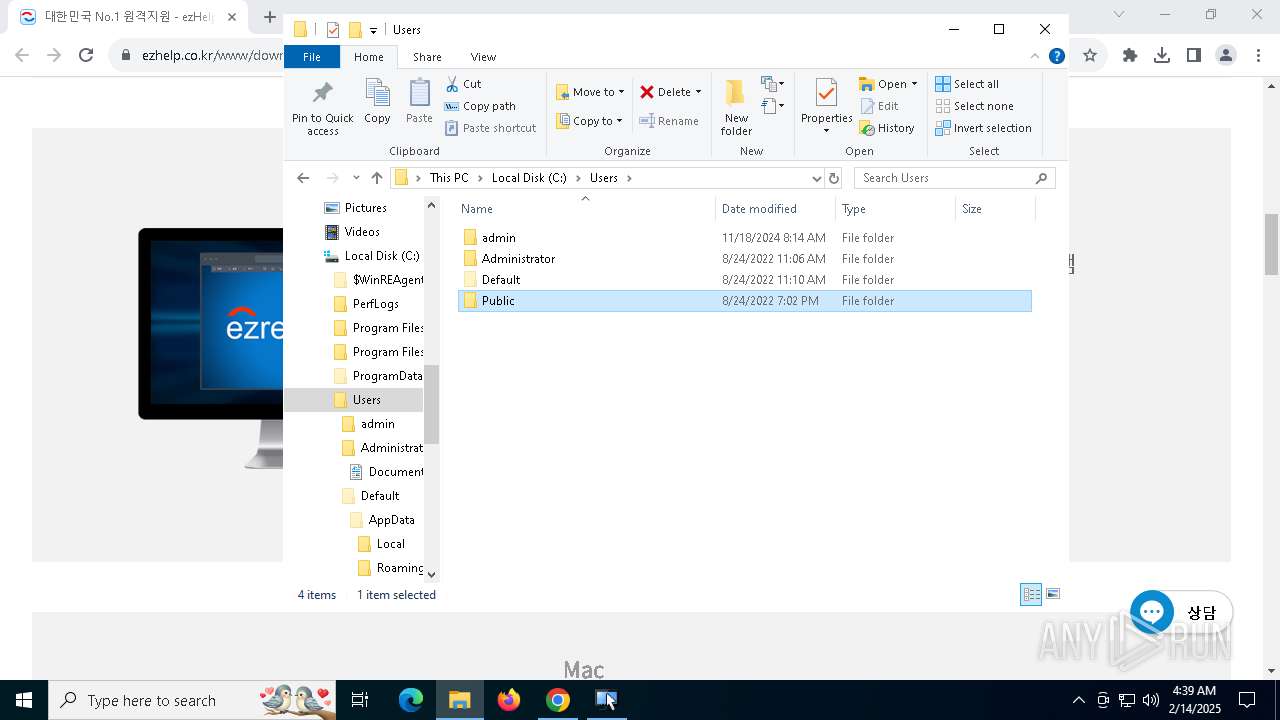
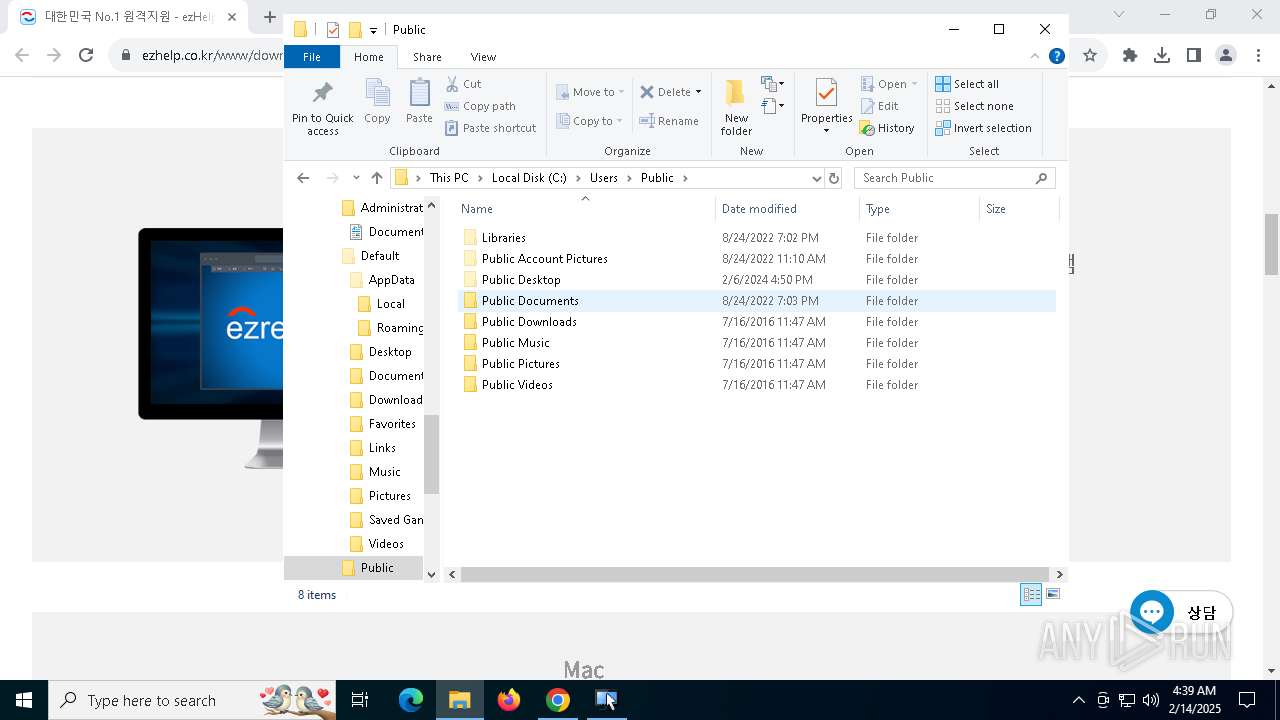
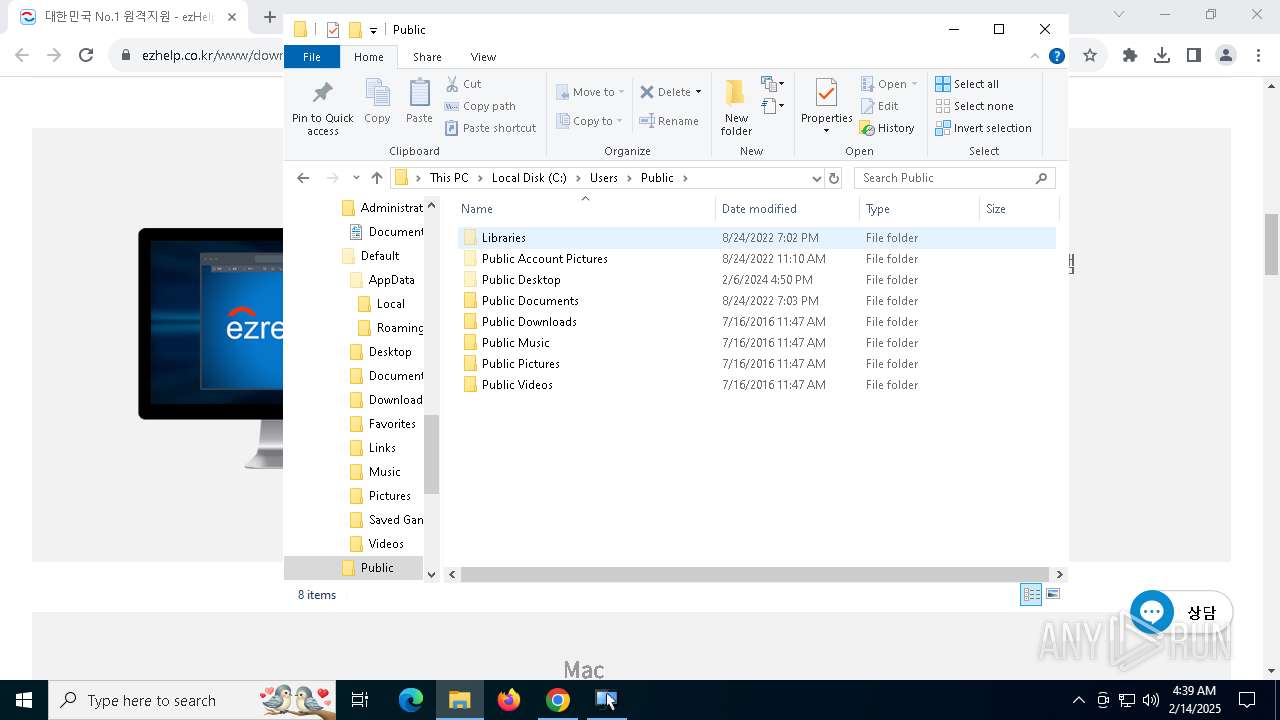
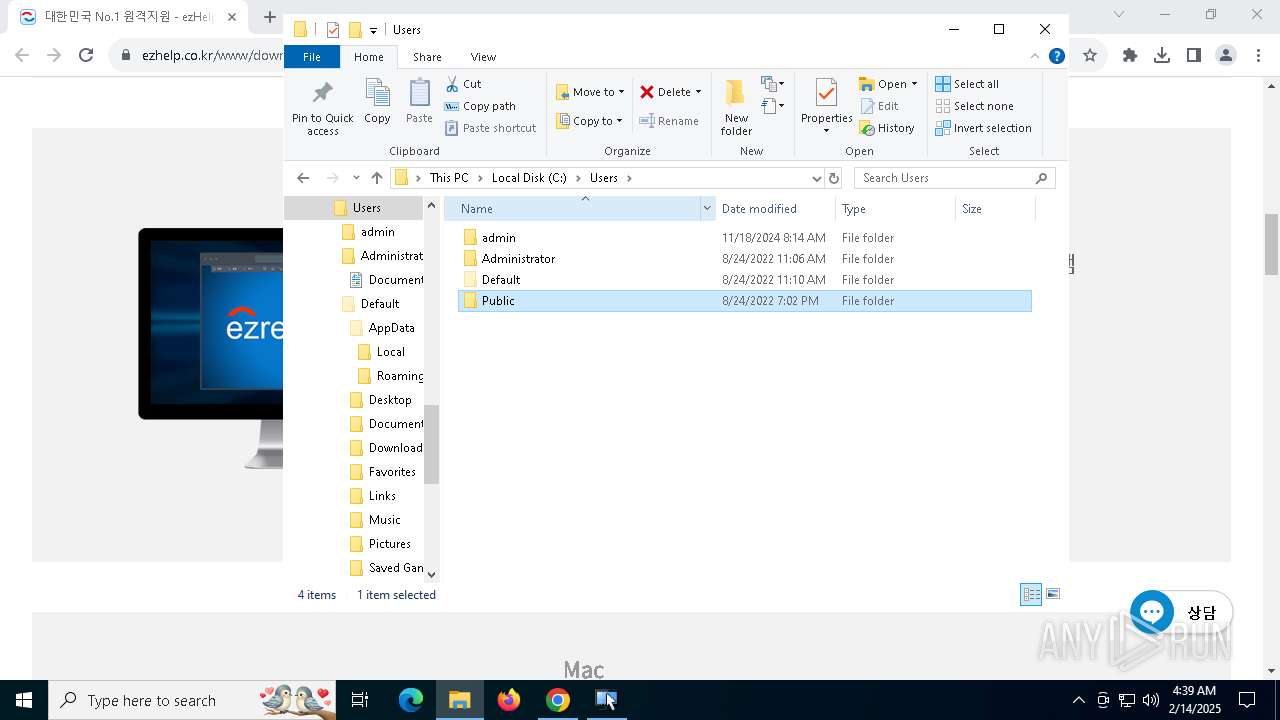
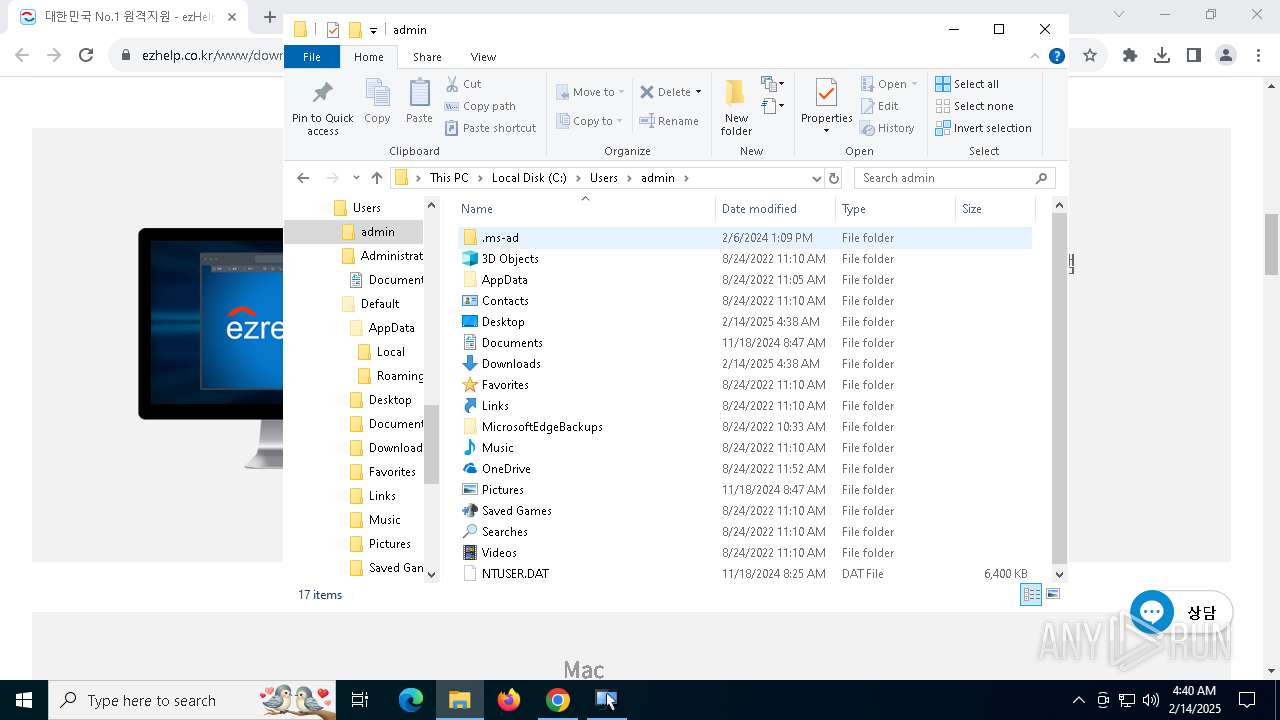
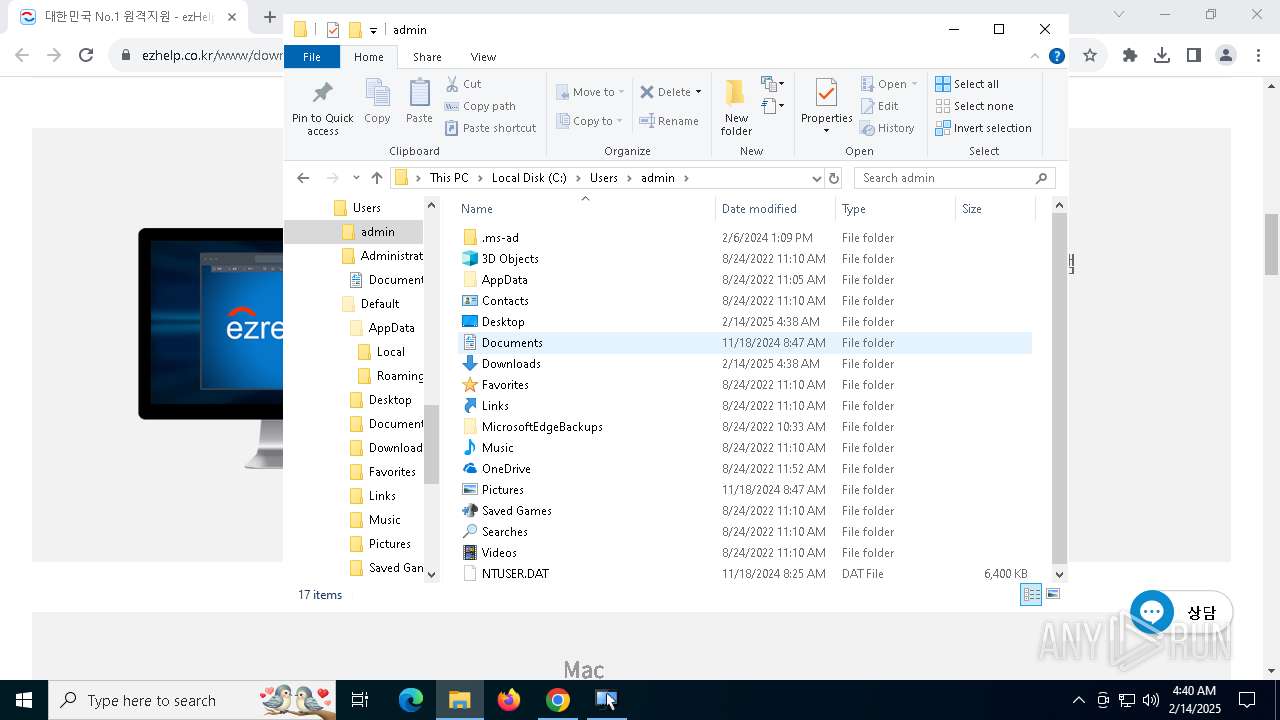
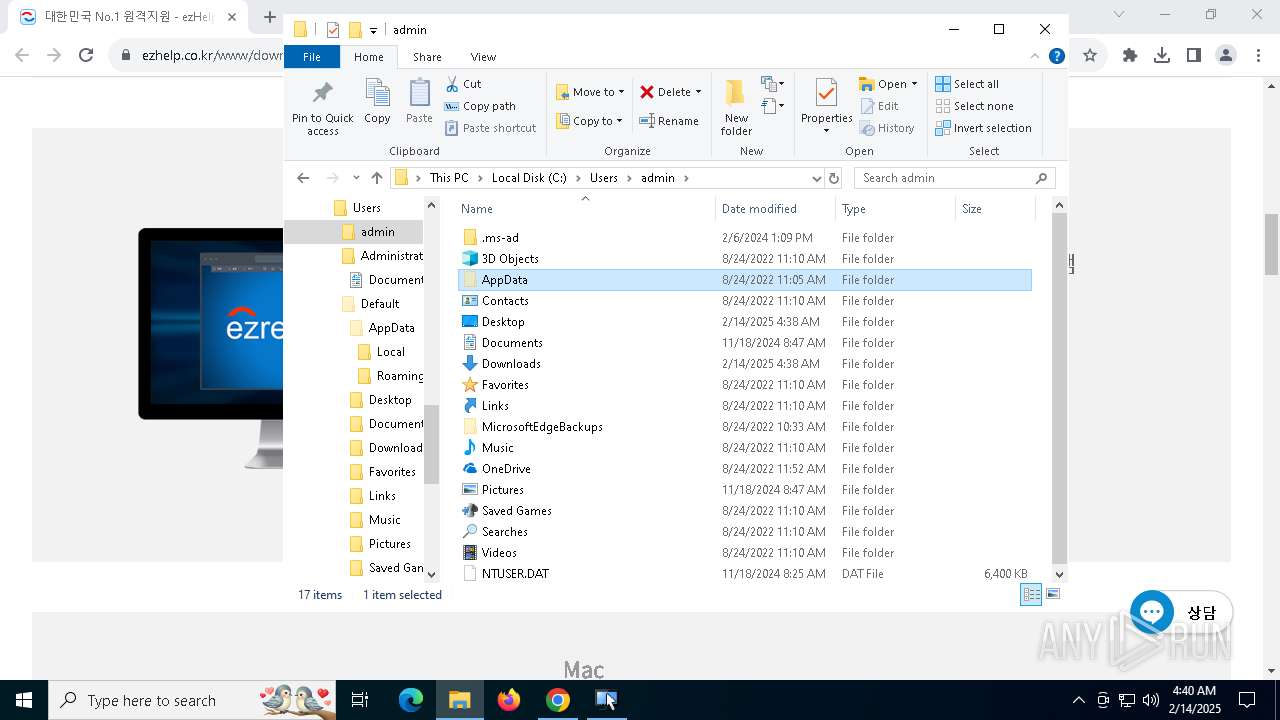
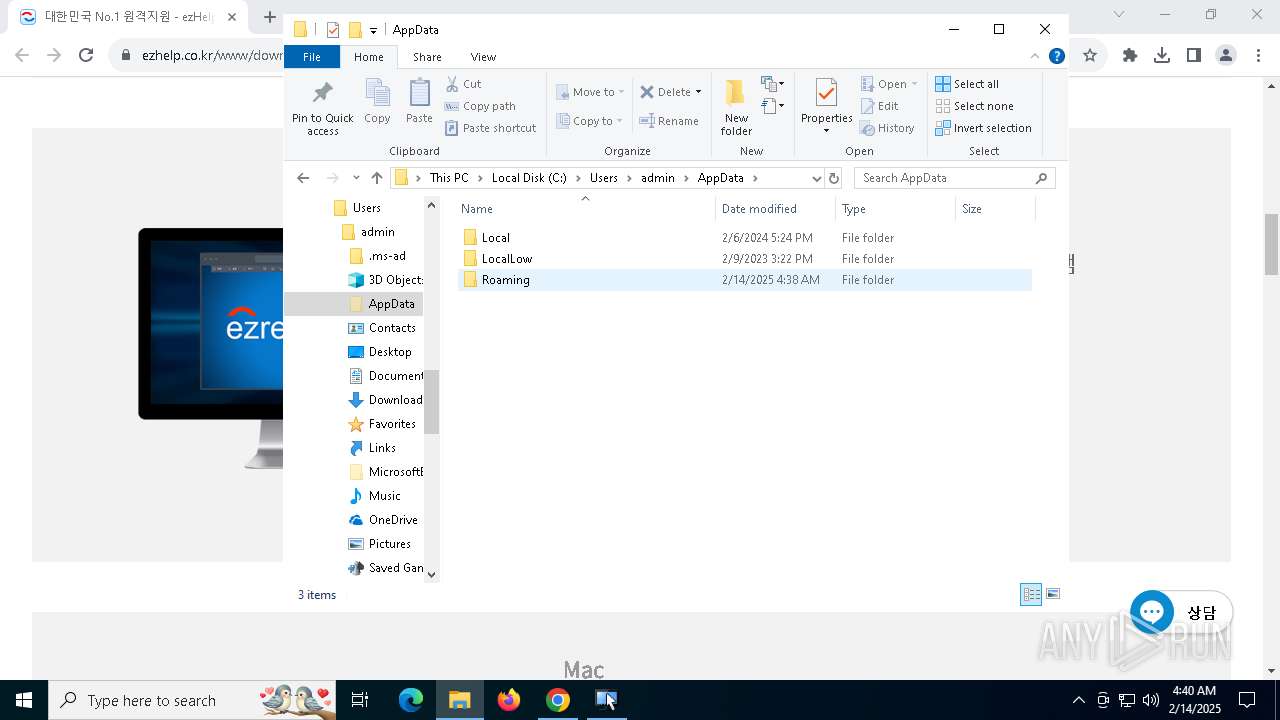
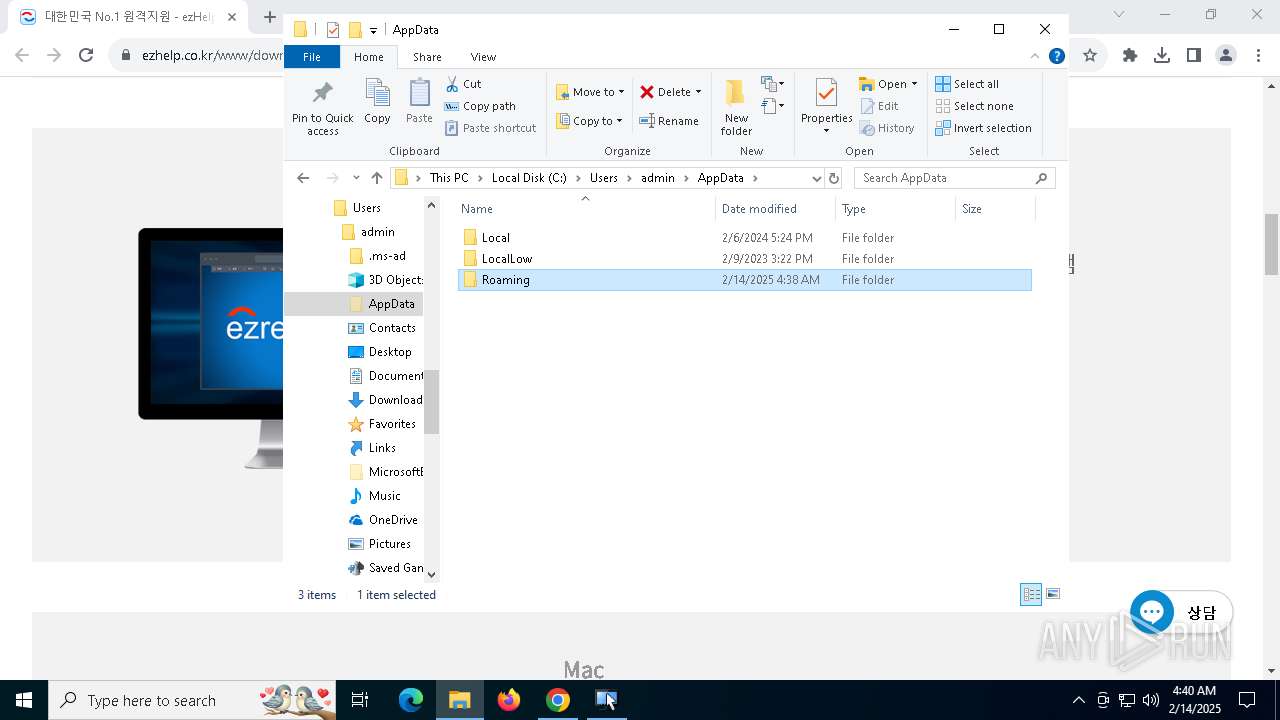
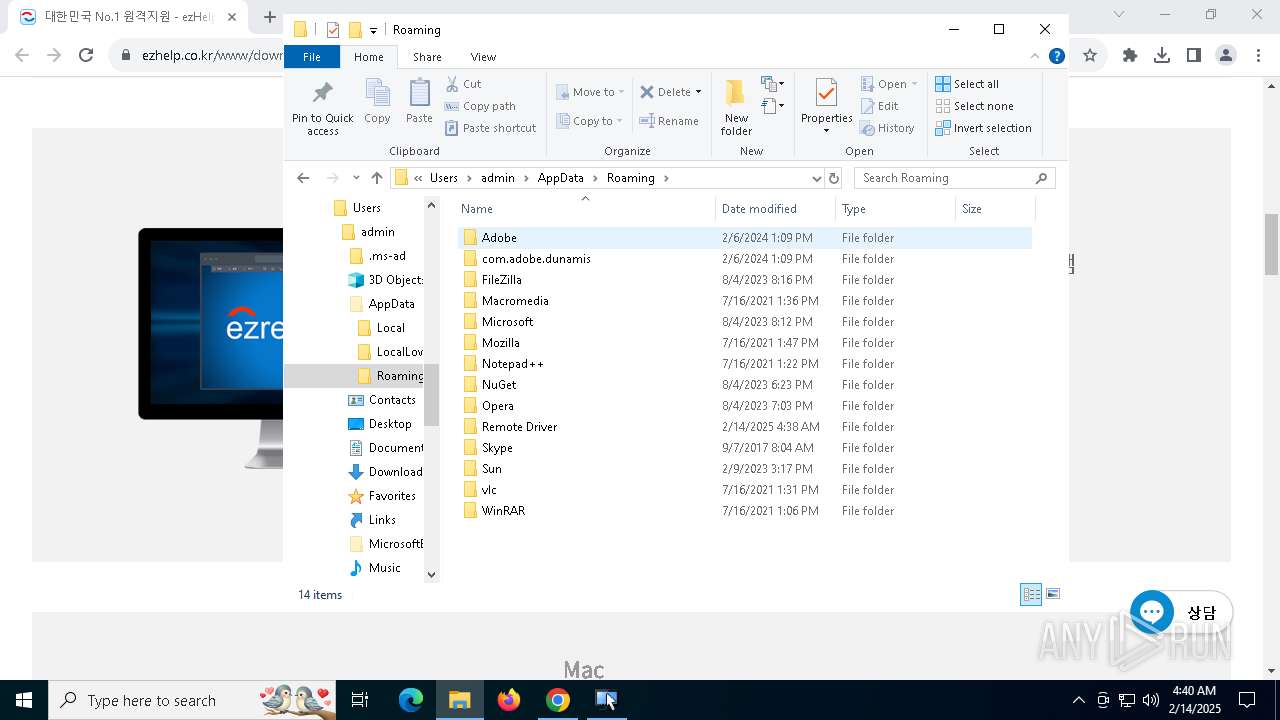
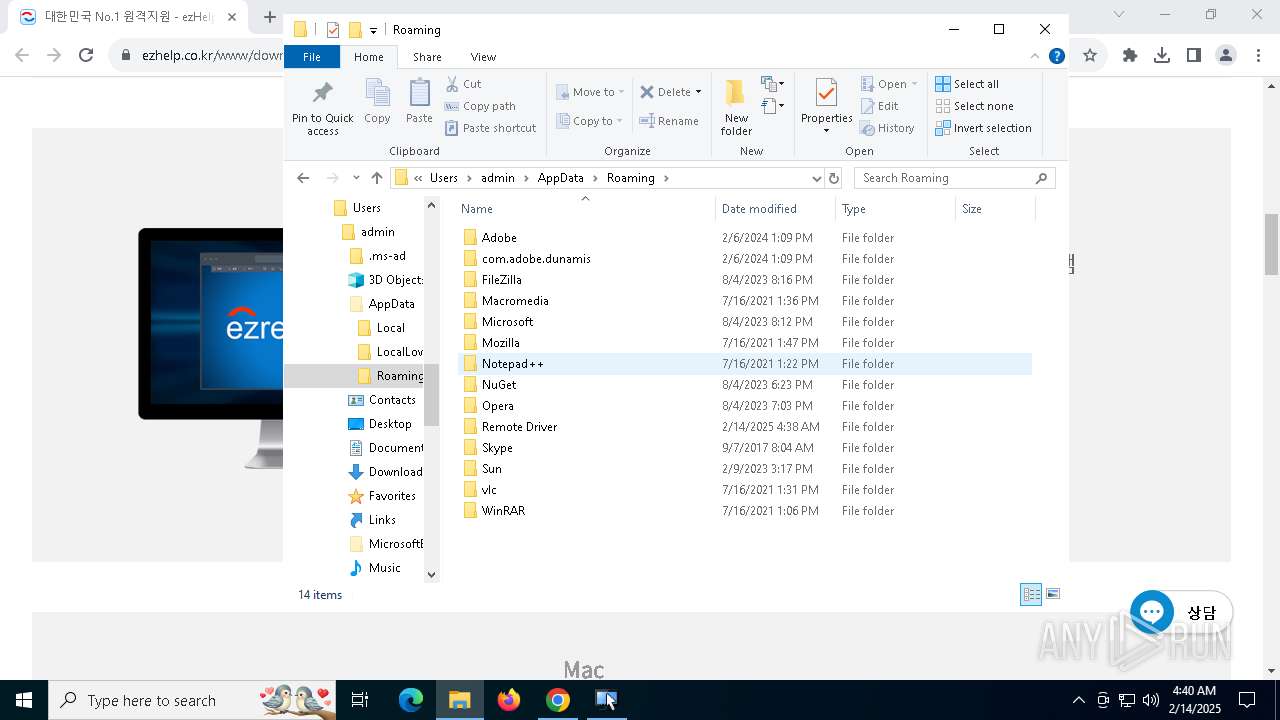
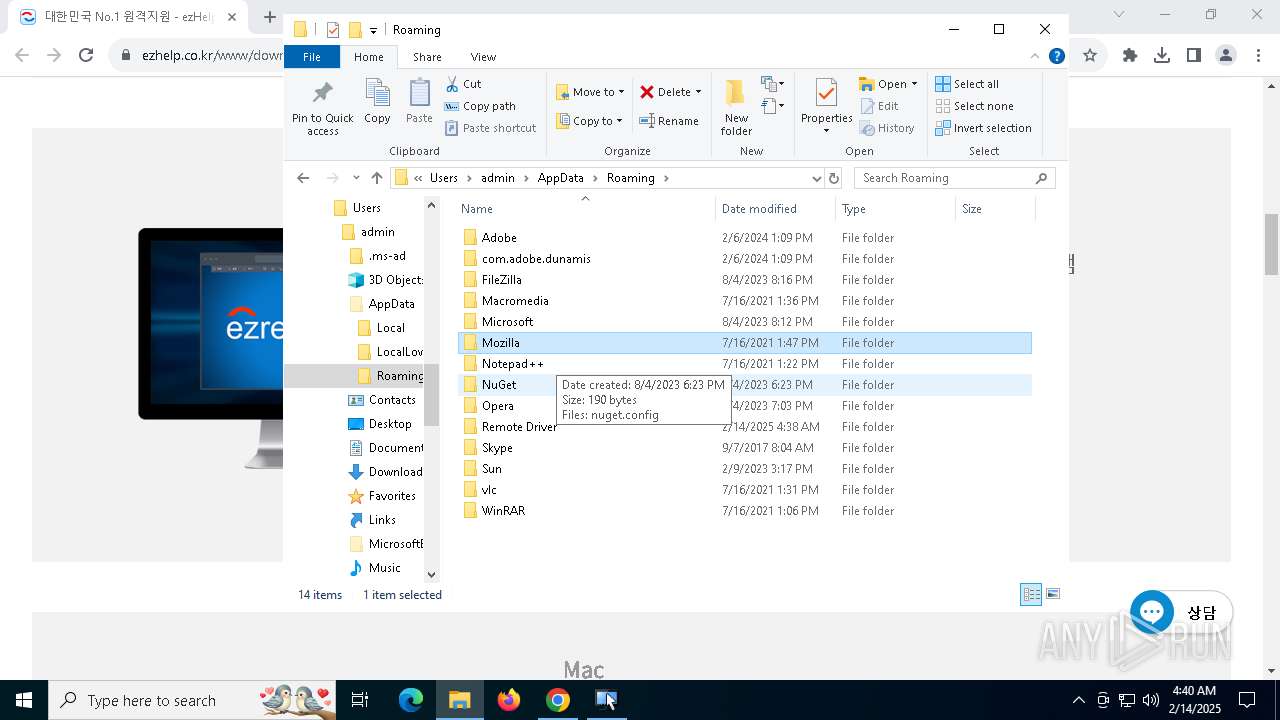
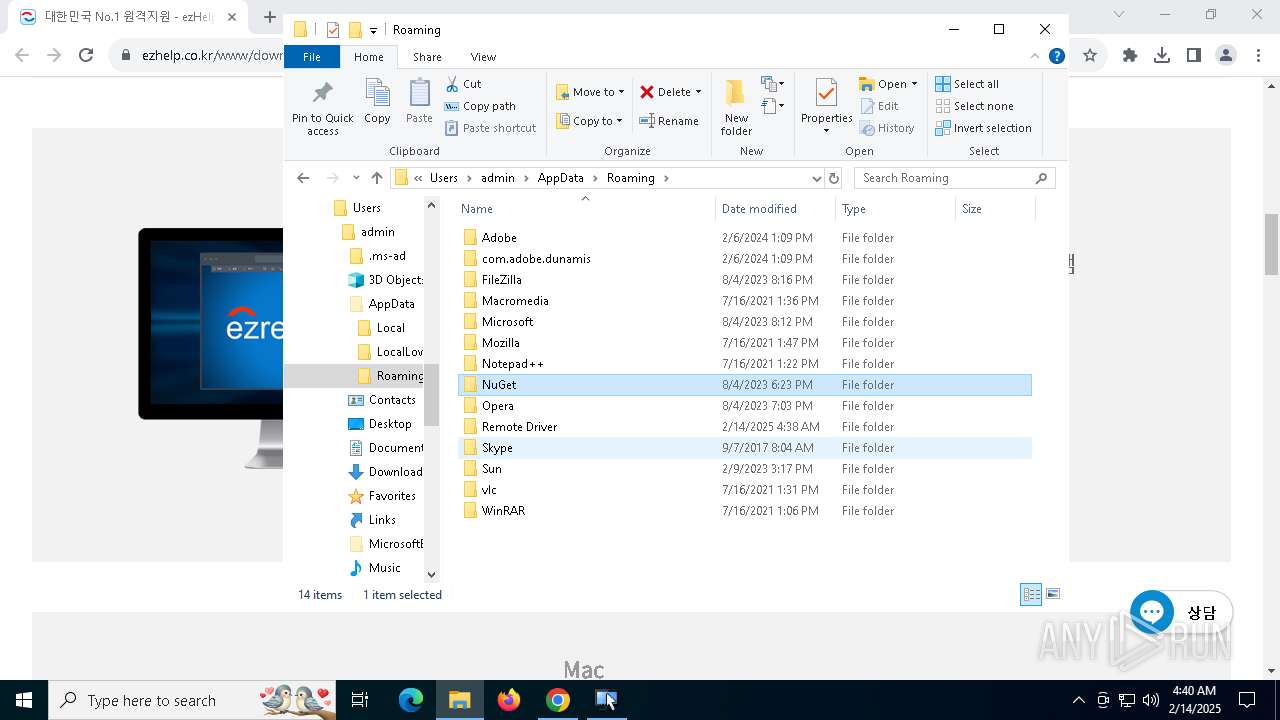
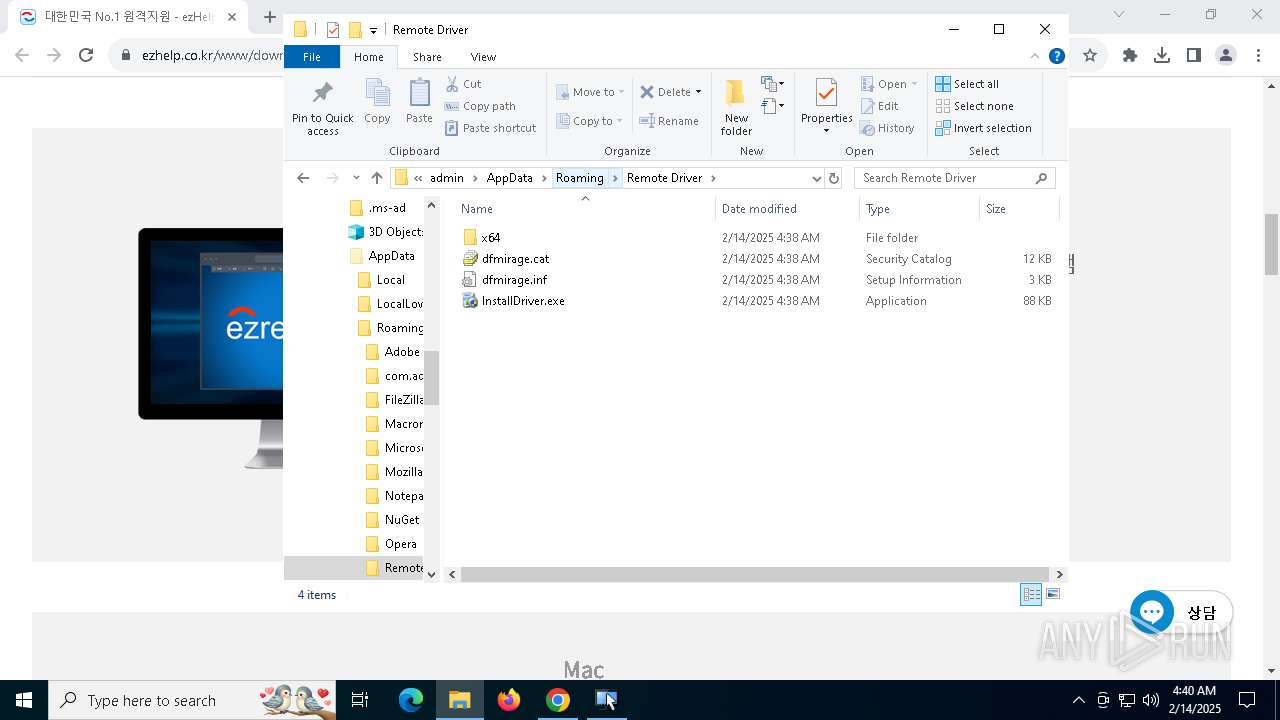
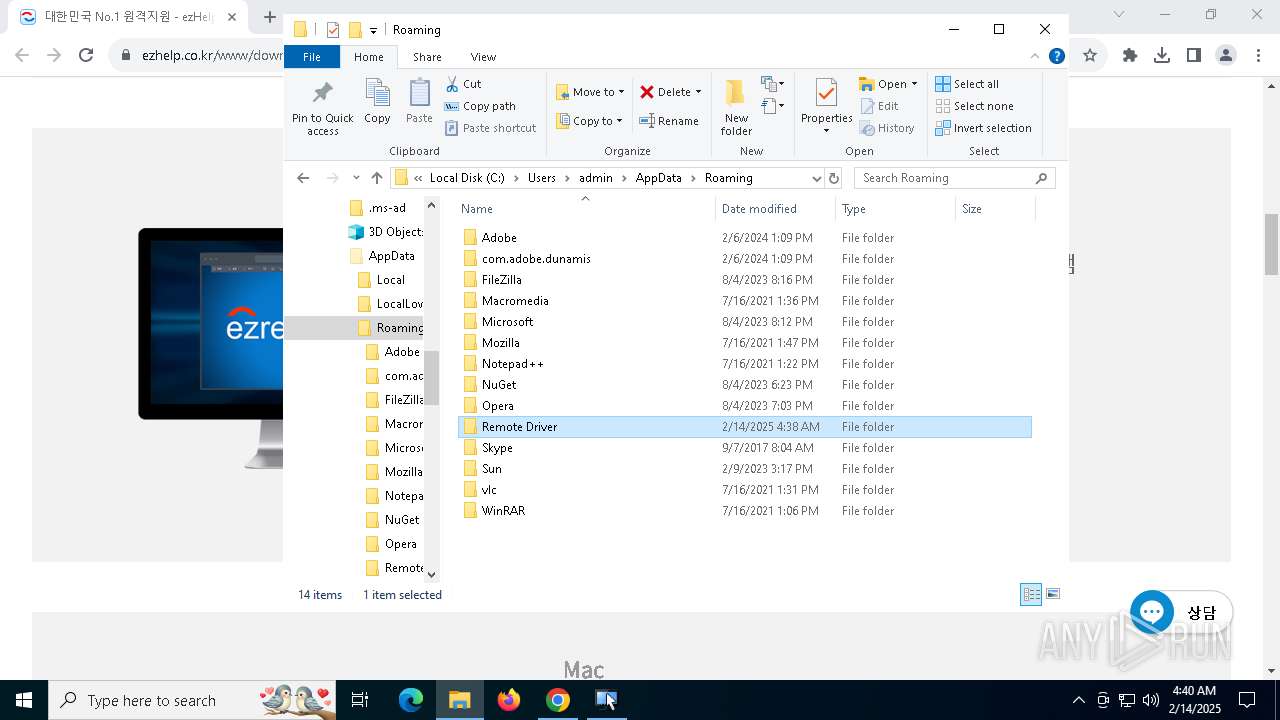
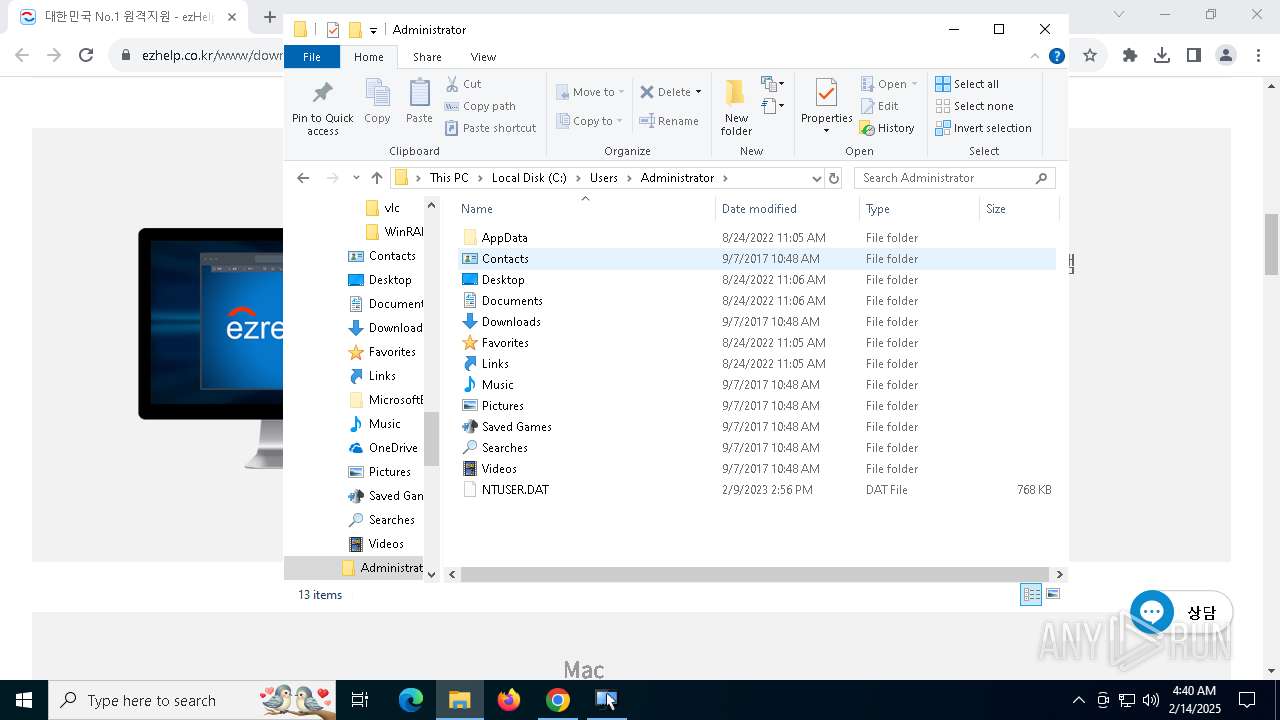
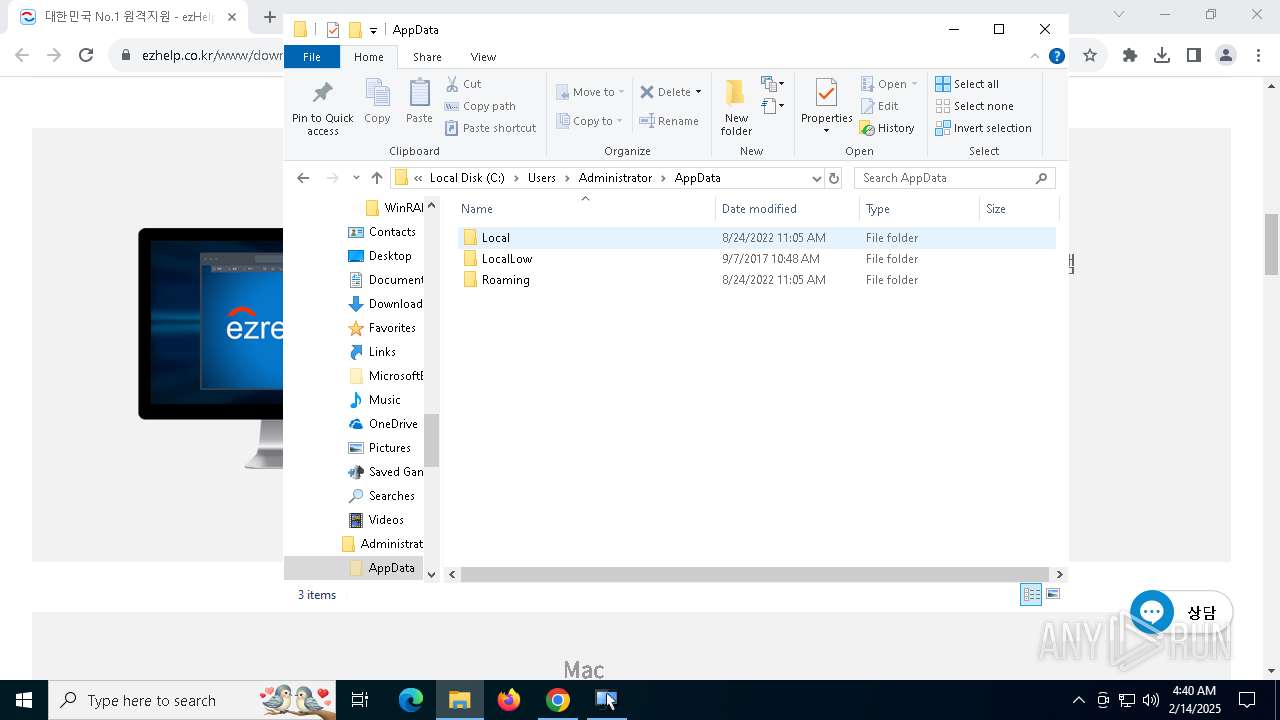
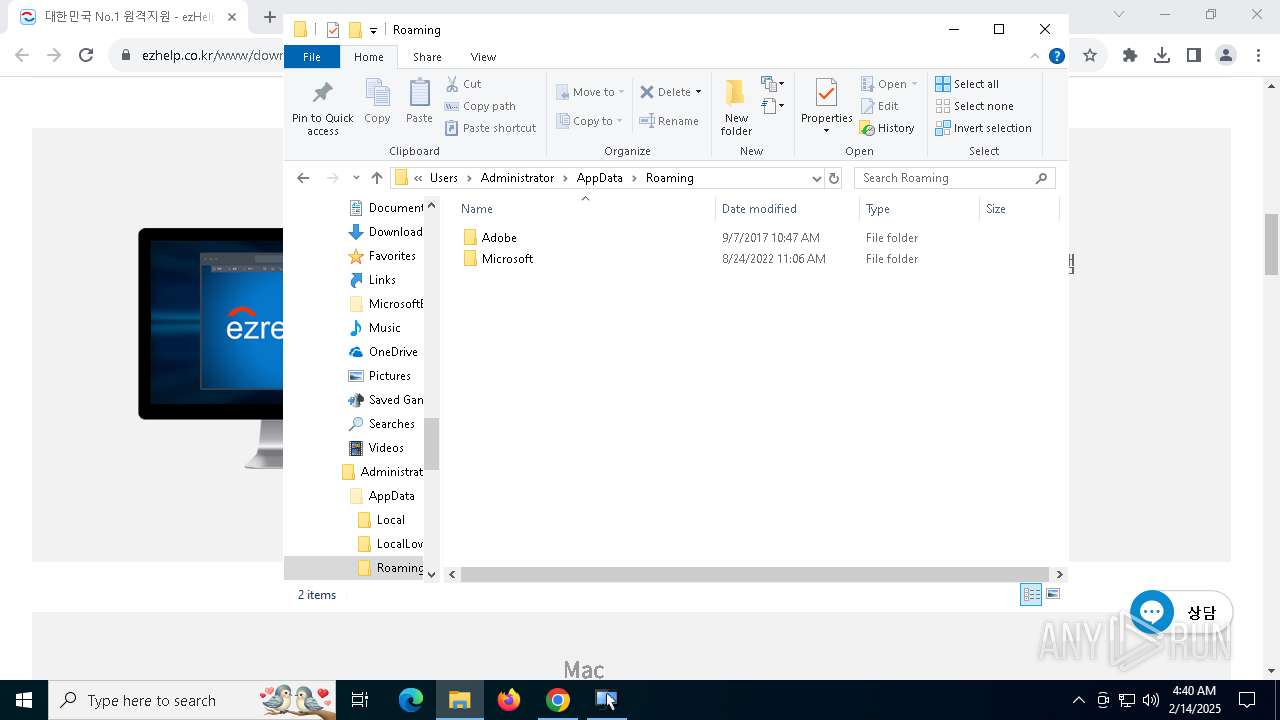
Creates files or folders in the user directory
- ezRemoteServerLauncher.exe (PID: 1988)
UPX packer has been detected
- ezRemoteServer.exe (PID: 1412)
- ezRemoteServer.exe (PID: 4864)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
200
Monitored processes
60
Malicious processes
7
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 736 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=31 --mojo-platform-channel-handle=6064 --field-trial-handle=1852,i,16118224236973201867,4265857413816128442,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=34 --mojo-platform-channel-handle=6092 --field-trial-handle=1852,i,16118224236973201867,4265857413816128442,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1140 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=6064 --field-trial-handle=1852,i,16118224236973201867,4265857413816128442,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1144 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=39 --mojo-platform-channel-handle=6764 --field-trial-handle=1852,i,16118224236973201867,4265857413816128442,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1328 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=30 --mojo-platform-channel-handle=5212 --field-trial-handle=1852,i,16118224236973201867,4265857413816128442,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1412 | "C:\Program Files (x86)\ezRemote\Server\ezRemoteServer.exe" -controlservice -slave | C:\Program Files (x86)\ezRemote\Server\ezRemoteServer.exe | ezRemoteServer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 2.1.0.5 Modules
| |||||||||||||||
| 1792 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=3508 --field-trial-handle=1852,i,16118224236973201867,4265857413816128442,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1988 | "C:\Program Files (x86)\ezRemote\Server\ezRemoteServerLauncher.exe" elevation | C:\Program Files (x86)\ezRemote\Server\ezRemoteServerLauncher.exe | ezRemoteServerLauncher.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.4.2 Modules
| |||||||||||||||
| 2008 | ezRemoteServer -install | C:\Program Files (x86)\ezRemote\Server\ezRemoteServer.exe | ezRemoteServerLauncher.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 2.1.0.5 Modules
| |||||||||||||||
| 2072 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5052 --field-trial-handle=1852,i,16118224236973201867,4265857413816128442,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
29 461
Read events
29 248
Write events
196
Delete events
17
Modification events
| (PID) Process: | (3812) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3812) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3812) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3812) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3812) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5404) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000D764E8439A7EDB01 | |||
| (PID) Process: | (5972) ezRemoteServerSetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\ezRemoteServer Program_is1 |
| Operation: | write | Name: | Inno Setup: Setup Version |
Value: 5.5.3 (a) | |||
| (PID) Process: | (5972) ezRemoteServerSetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\ezRemoteServer Program_is1 |
| Operation: | write | Name: | Inno Setup: App Path |
Value: C:\Program Files (x86)\ezRemote\Server | |||
| (PID) Process: | (5972) ezRemoteServerSetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\ezRemoteServer Program_is1 |
| Operation: | write | Name: | InstallLocation |
Value: C:\Program Files (x86)\ezRemote\Server\ | |||
| (PID) Process: | (5972) ezRemoteServerSetup.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\Windows\CurrentVersion\Uninstall\ezRemoteServer Program_is1 |
| Operation: | write | Name: | Inno Setup: Icon Group |
Value: ezRemote | |||
Executable files
67
Suspicious files
450
Text files
60
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF13737e.TMP | — | |
MD5:— | SHA256:— | |||
| 3812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF13737e.TMP | — | |
MD5:— | SHA256:— | |||
| 3812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF13737e.TMP | — | |
MD5:— | SHA256:— | |||
| 3812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF13737e.TMP | — | |
MD5:— | SHA256:— | |||
| 3812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF13739d.TMP | — | |
MD5:— | SHA256:— | |||
| 3812 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
49
TCP/UDP connections
207
DNS requests
170
Threats
4
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5040 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
5040 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
5040 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
5040 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/aculsbfvftdtqcjji5o6a743svfq_9.54.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.54.0_all_fjvhh4h55icwcaan3v3j6mksxa.crx3 | unknown | — | — | whitelisted |
5040 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | unknown | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
6352 | chrome.exe | GET | 200 | 151.101.66.133:80 | http://secure.globalsign.com/cacert/gsgccr6alphasslca2023.crt | unknown | — | — | whitelisted |
3812 | chrome.exe | GET | 200 | 151.101.66.133:80 | http://ocsp.globalsign.com/codesigningrootr45/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQVFZP5vqhCrtRN5SWf40Rn6NM1IAQUHwC%2FRoAK%2FHg5t6W0Q9lWULvOljsCEHe9DgW3WQu2HUdhUx4%2Fde0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4712 | MoUsoCoreWorker.exe | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 104.126.37.144:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
5064 | SearchApp.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
3812 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6352 | chrome.exe | 142.250.110.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
6352 | chrome.exe | 182.252.178.53:443 | www.ezhelp.co.kr | abcle | KR | suspicious |
6352 | chrome.exe | 142.250.186.35:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
www.ezhelp.co.kr |
| unknown |
accounts.google.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
cdnjs.cloudflare.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6352 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6352 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Cloudflare content delivery network (cdnjs .cloudflare .com) |
6352 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
6352 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] An application monitoring request to sentry .io |
Process | Message |
|---|---|
ezRemoteServerUpdater.exe | Updater : ¼ºñ½º°¡ Á¸ÀçÇÏÁö ¾Ê´Â´Ù.
|
ezRemoteServerUpdater.exe | Updater : Server IP = 182.252.178.40 |
ezRemoteServerLauncher.exe | launcher :
Local group(s):
|
ezRemoteServerLauncher.exe | launcher :
Entries enumerated: 1
|
ezRemoteServerLauncher.exe | launcher :
Local group(s):
|
ezRemoteServerLauncher.exe | launcher :
Entries enumerated: 1
|
ezRemoteServerLauncher.exe | launcher : First = html , Second = images , File = chat2_bubblebbg1.jpg , Size = 7027
|
ezRemoteServerLauncher.exe | launcher : UAC On |
ezRemoteServerLauncher.exe | launcher : First = html , Second = , File = chat.css , Size = 777
|
ezRemoteServerLauncher.exe | launcher : First = html , Second = , File = chat.html , Size = 1171
|