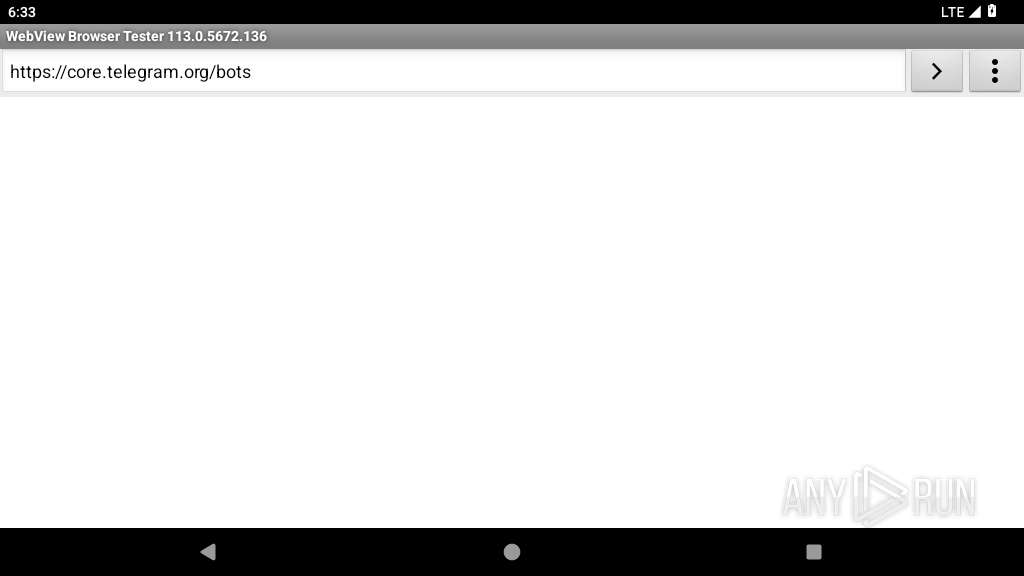
| URL: | api.telegram.org |
| Full analysis: | https://app.any.run/tasks/921e314b-d991-43d9-8930-ed01a9cb39ea |
| Verdict: | Malicious activity |
| Analysis date: | March 27, 2025, 06:33:12 |
| OS: | Android 14 |
| Tags: | |
| Indicators: | |
| MD5: | EB2E97935491BC186DB68B66FEC5619A |
| SHA1: | 9E2E447EA2FCCE6DF6BC988B1F11DF9E6D8643D3 |
| SHA256: | DBF6F39373592D863930B506019FBB9C3E096A85874A51575AF8DCEBB64233F5 |
| SSDEEP: | 3:8Mavn:8Mav |
MALICIOUS
No malicious indicators.SUSPICIOUS
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- app_process64 (PID: 2222)
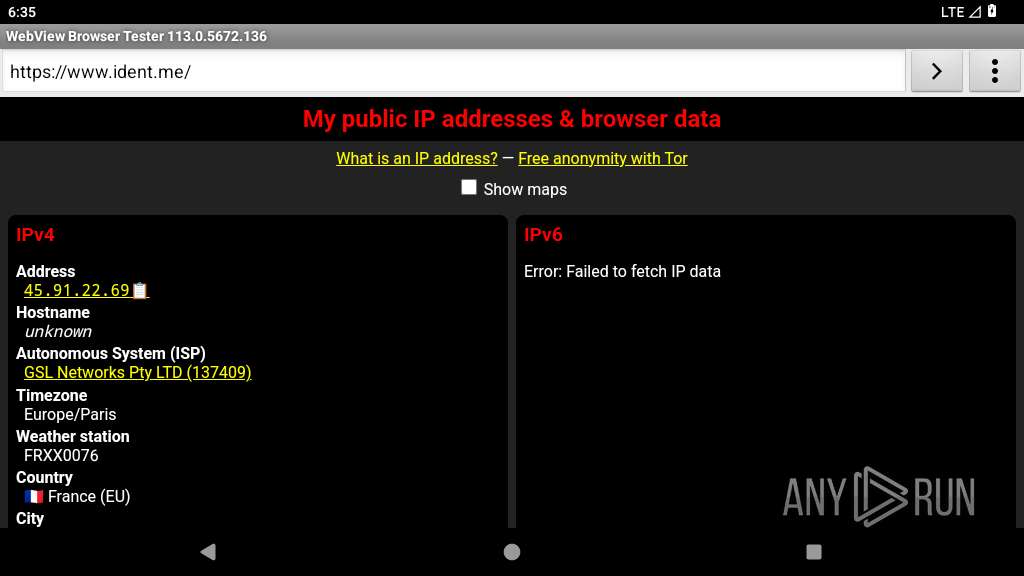
Checks for external IP
- app_process64 (PID: 2222)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
127
Monitored processes
5
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process |
|---|---|---|---|---|
| 343 | /system/bin/netd | /system/bin/netd | init | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2222 | org.chromium.webview_shell | /system/bin/app_process64 | app_process64 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2247 | zygote | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2264 | webview_zygote | /system/bin/app_process32 | — | app_process32 |
User: webview_zygote Integrity Level: UNKNOWN Exit code: 0 | ||||
| 2300 | zygote | /system/bin/app_process32 | app_process32 | |
User: root Integrity Level: UNKNOWN Exit code: 0 | ||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
48
DNS requests
4
Threats
7
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 204 | 142.250.75.227:80 | http://connectivitycheck.gstatic.com/generate_204 | unknown | — | — | whitelisted |
2222 | app_process64 | GET | 301 | 104.26.13.28:80 | http://lol.com/ | unknown | — | — | unknown |
2222 | app_process64 | GET | 301 | 65.108.151.63:80 | http://ident.me/ | unknown | — | — | whitelisted |
2222 | app_process64 | GET | 301 | 149.154.167.220:80 | http://api.telegram.org/ | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
447 | mdnsd | 224.0.0.251:5353 | — | — | — | unknown |
343 | netd | 8.8.8.8:443 | — | — | — | malicious |
— | — | 8.8.8.8:853 | — | GOOGLE | US | malicious |
— | — | 216.239.35.12:123 | time.android.com | — | — | whitelisted |
— | — | 142.250.75.227:80 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
— | — | 142.250.179.100:443 | www.google.com | GOOGLE | US | whitelisted |
— | — | 142.251.168.81:443 | — | GOOGLE | US | unknown |
2222 | app_process64 | 149.154.167.220:80 | — | Telegram Messenger Inc | GB | unknown |
2247 | app_process32 | 142.250.75.227:443 | connectivitycheck.gstatic.com | GOOGLE | US | whitelisted |
2300 | app_process32 | 142.250.201.163:443 | — | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
connectivitycheck.gstatic.com |
| whitelisted |
kScXmx-dnsotls-ds.metric.gstatic.com |
| whitelisted |
www.google.com |
| whitelisted |
time.android.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Misc activity | ET INFO Android Device Connectivity Check |
2222 | app_process64 | Misc activity | ET HUNTING Observed Telegram API Domain (api .telegram .org in TLS SNI) |
2222 | app_process64 | Misc activity | ET INFO Observed Cloudflare Page Developer Domain (pages .dev in TLS SNI) |
2222 | app_process64 | Device Retrieving External IP Address Detected | ET INFO Observed External IP Lookup Domain (ident .me) in TLS SNI |
2222 | app_process64 | Device Retrieving External IP Address Detected | ET INFO Observed External IP Lookup Domain (ident .me) in TLS SNI |
2222 | app_process64 | Device Retrieving External IP Address Detected | ET INFO Observed External IP Lookup Domain (ident .me) in TLS SNI |
2222 | app_process64 | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |